Overview
Password-based authentication continues to be one of the largest attack surfaces across SaaS platforms. Applications like Zendesk Guides offer native login controls, but enterprises often require a higher level of authentication governance.
Security teams today need:
- Centralized MFA enforcement
- API-driven identity validation
- Dynamic user attribute integration
- Centralized audit visibility
- High-availability IAM infrastructure
Native SaaS authentication mechanisms are not always designed to meet these enterprise-grade security and compliance demands.
The Enterprise Requirement
The organization needed to:
- Enforce Multi-Factor Authentication (MFA) for Zendesk Guides
- Dynamically retrieve user phone numbers via API
- Avoid storing user PII within the MFA platform
- Introduce an authentication enforcement layer at the application boundary
- Validate the solution with a controlled pilot group
The deployment required only minimal configuration adjustments within Zendesk to support secure proxy-based authentication.
The objective was clear: Establish policy-driven MFA enforcement before SaaS session creation.
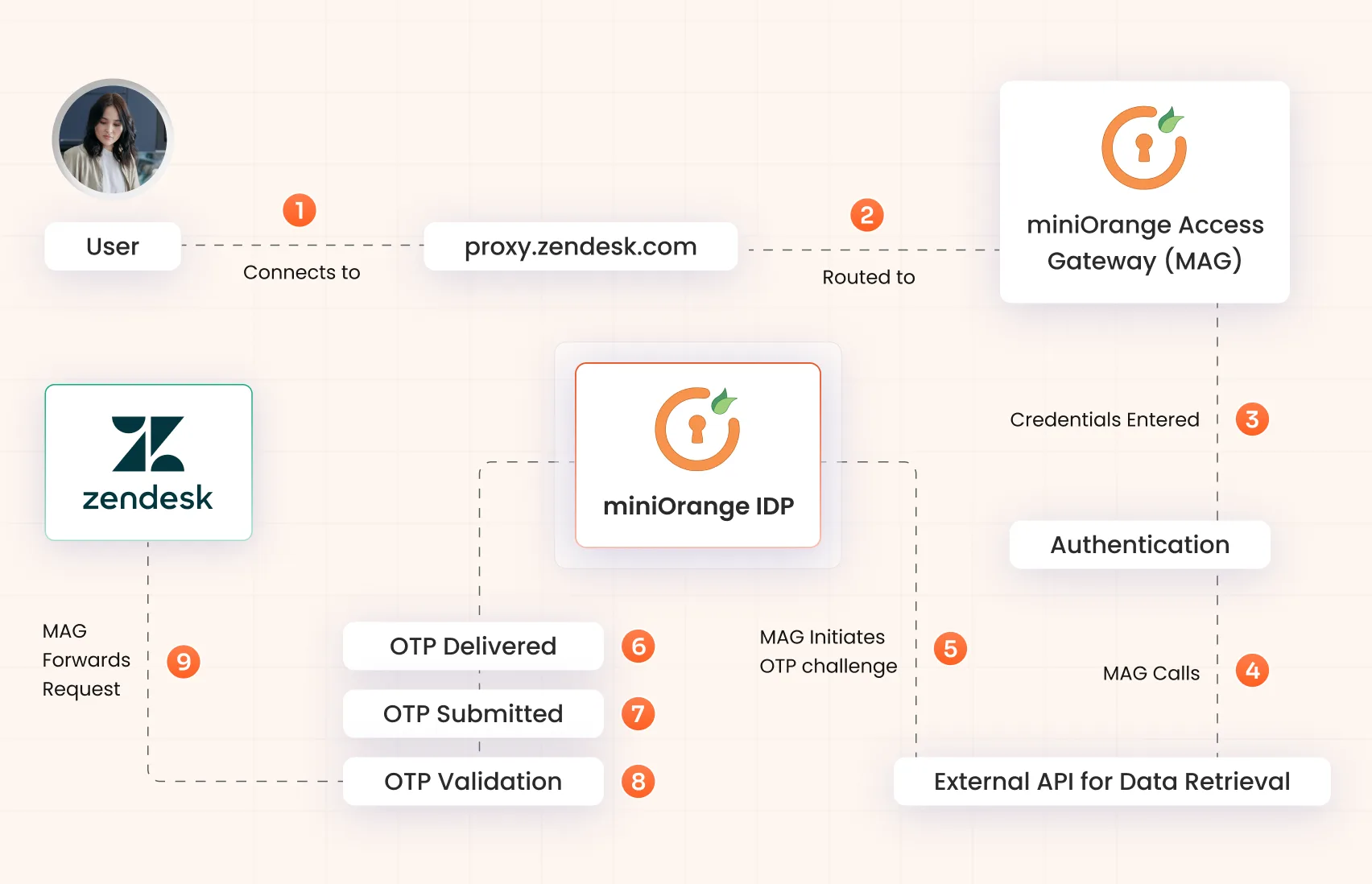
The Solution: A Reverse Proxy Enforcement Layer
miniOrange Access Gateway (MAG) was deployed as a reverse proxy in front of Zendesk, creating a secure authentication control point before traffic reaches the application.
Instead of relying solely on SaaS-native controls, authentication is intercepted and validated at the gateway layer.
No authenticated session is forwarded to Zendesk until MFA validation is successfully completed.
Core Components

miniOrange Access Gateway (MAG)
Reverse proxy and policy enforcement point

miniOrange Identity Provider (IDP)
OTP generation and validation engine

External API Source
Secure retrieval of user phone numbers
How the Authentication Flow Works
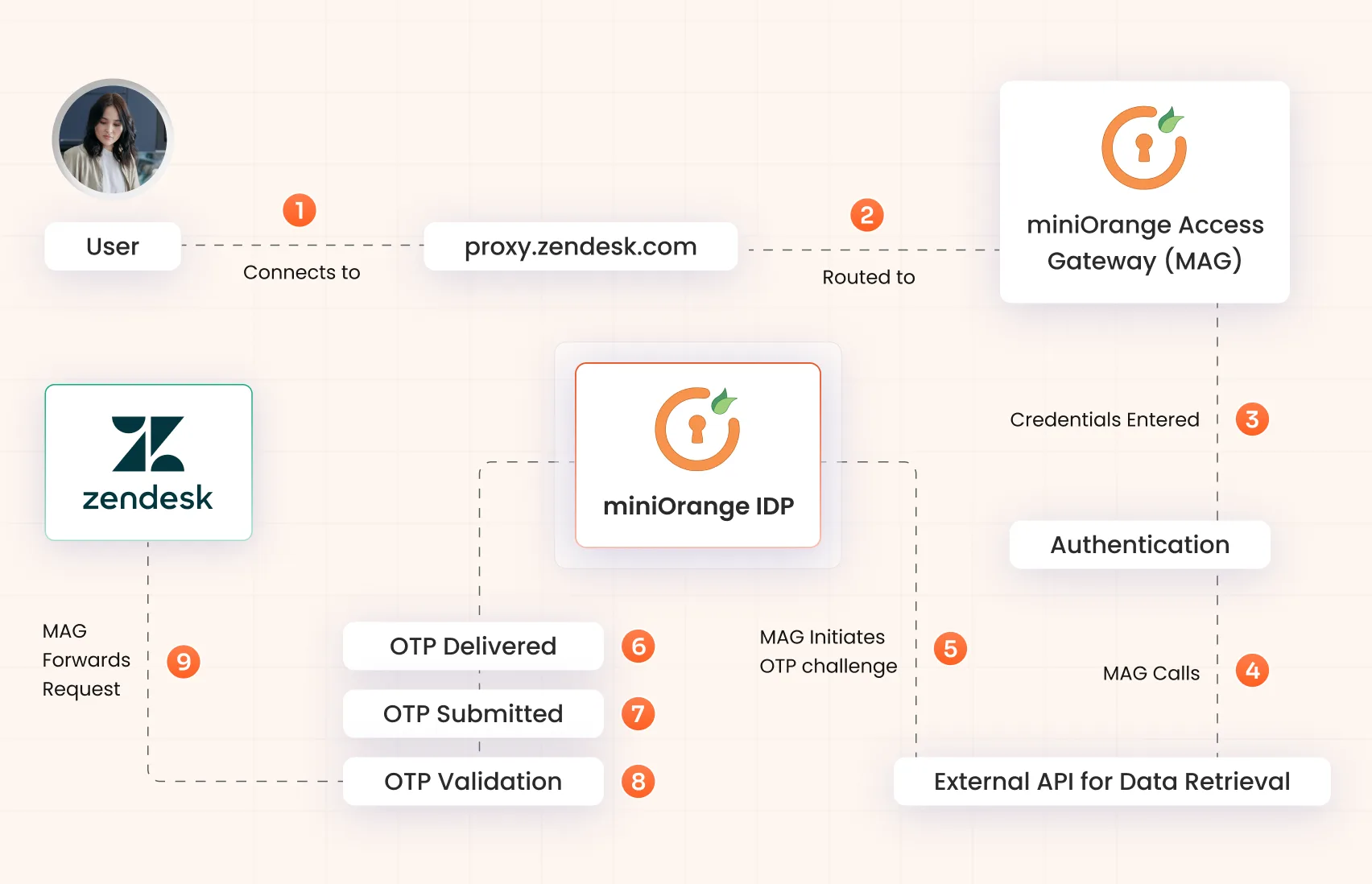
- User connects to proxy.zendesk.com
- Request is routed to miniOrange Access Gateway
- User completes primary authentication
- MAG securely calls an external API to retrieve the user’s phone number
- MAG initiates an OTP challenge via miniOrange IDP
- OTP is delivered via SMS or Authenticator App
- User submits OTP at the IDP Prompt
- IDP validates the OTP and issues a secure session token
- MAG forwards the authenticated request to app.zendesk.com
MFA enforcement occurs inline — before Zendesk session establishment.
Ready to Secure Your Enterprise Applications?
See how miniOrange Access Gateway can work in your environment.
Start Free Trial
Book a Demo
Why Native SaaS MFA Was Not Sufficient
- Limited external attribute integration
- No authentication enforcement layer at the application edge
- Restricted flexibility in policy-driven MFA
- Inconsistent centralized audit visibility
- Limited control over authentication boundary
By inserting a reverse proxy enforcement layer, the organization gained centralized authentication governance while maintaining Zendesk’s core architecture with minimal configuration changes.
Security & Operational Outcomes
- Inline MFA enforcement before Zendesk session creation
- Minimal configuration updates required within Zendesk
- No storage of user PII within miniOrange
- Secure API-driven user attribute retrieval
- Centralized authentication and MFA event logging
- Controlled authentication boundary at the application edge
- Pilot successfully validated within 8–12 days
- Production-ready scalable architecture demonstrated
Production-Ready Architecture
The validated deployment supports enterprise-scale expansion with:
- High-availability Identity Servers
- Load-balanced Access Gateway nodes
- PostgreSQL clustered database architecture
- Redis and MQ for performance optimization
- Data center and disaster recovery readiness
- Hardened RedHat 9 infrastructure
The pilot validated both functional performance and architectural scalability for full production rollout.
Ideal For Organizations That
- Require centralized MFA enforcement for SaaS applications
- Cannot store user PII in third-party systems
- Need dynamic API-based identity integration
- Operate in regulated or security-sensitive environments
- Want authentication enforcement independent of SaaS limitations