Cisco Spark Single Sign-On SSO
Cisco Spark Platform provide the platform with SAASPASS multi-factor authentication (MFA) and secure single sign-on (SSO) and integrate it with SAML without any time limitation and code. You have to just log into your Cisco Spark Platform services securely to your both desktop / laptop and mobile with SAASPASS Instant Login (Proximity, Scan Barcode, On-Device Login and Remote Login). Here no need to remember passwords for the same.
Single Sign-on(SSO) solution for Cisco Spark is a cloud based service. With this service you need only one password for all your web & SaaS apps including Cisco Spark. miniOrange provides secure access and full control to Cisco Spark for enterprises and applications. With the help of the given guide you can configure Cisco Spark easily.
miniOrange and Cisco Spark Single Sign-On (SSO) integration supports the following features:
- SP Initiated Single Sign-On (SSO)
- IdP Initiated Single Sign-On (SSO)
Connect with External Source of Users
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
Follow the Step-by-Step Guide given below for Cisco Spark Single Sign-On (SSO)
1. Configure Cisco Spark Platform in miniOrange
- Login into miniOrange Admin Console.
- Go to Apps and click on Add Application button.

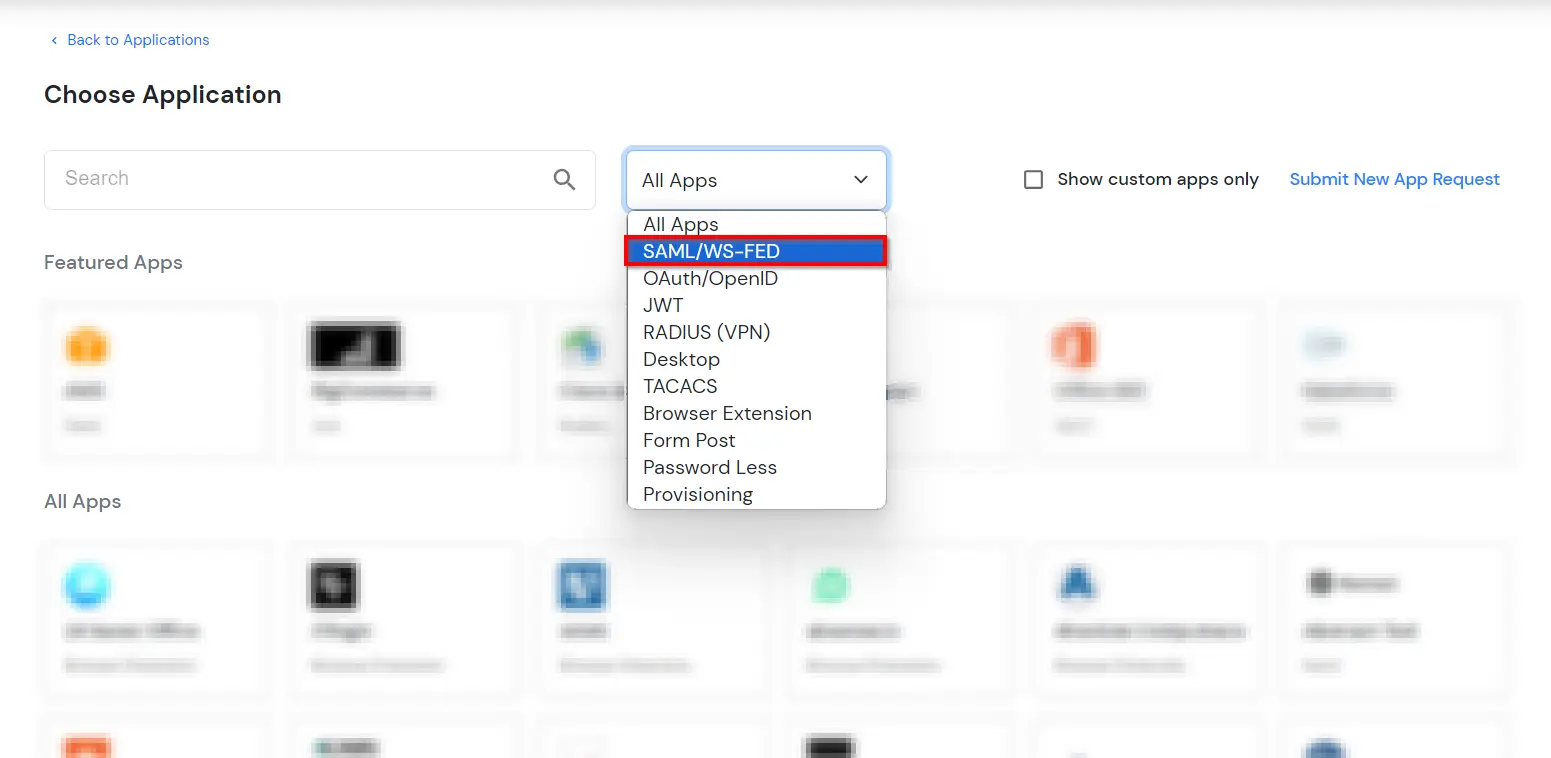
- In Choose Application Type, select SAML/WS-FED from the All Apps dropdown.
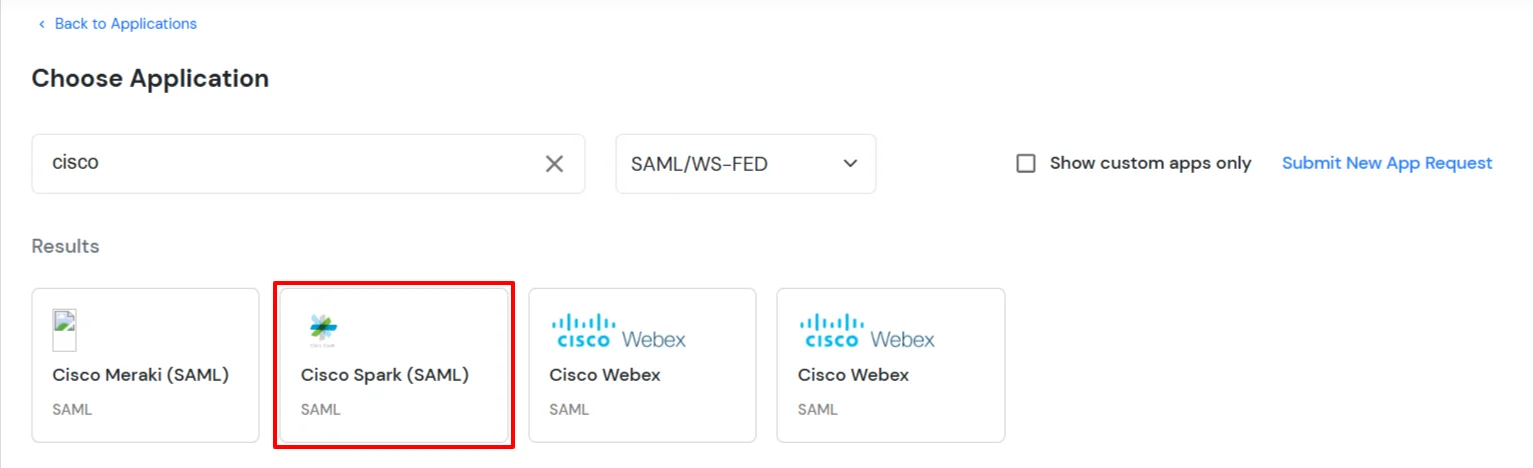
- Search for Cisco Spark Platform in the list, if you don't find Cisco Spark Platform in the list then, search for custom and you can set up your application in Custom SAML App.
2. Configure SSO in Cisco Spark
- Login to the Cisco Webex Control Hub at as an administrator.
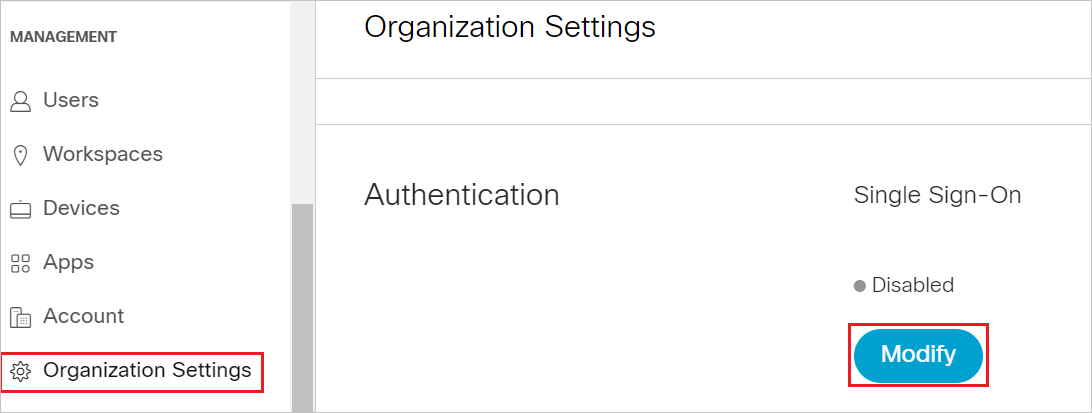
- Click on Settings >> Authentication >> Modify.
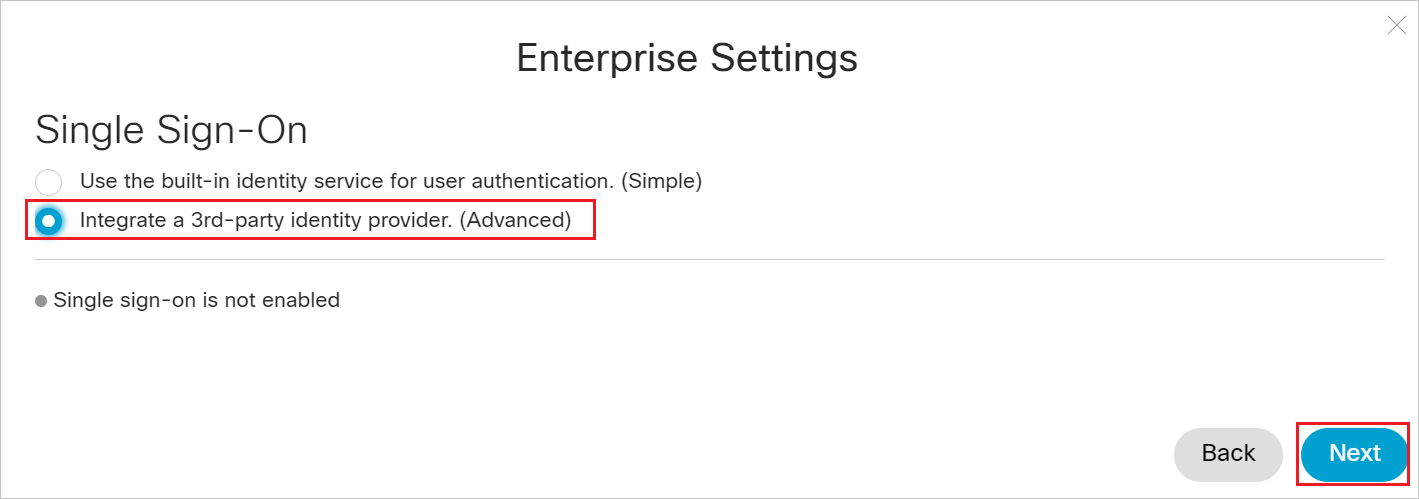
- Select option Integrate a 3rd-party provider. (Advanced) and click on Next.
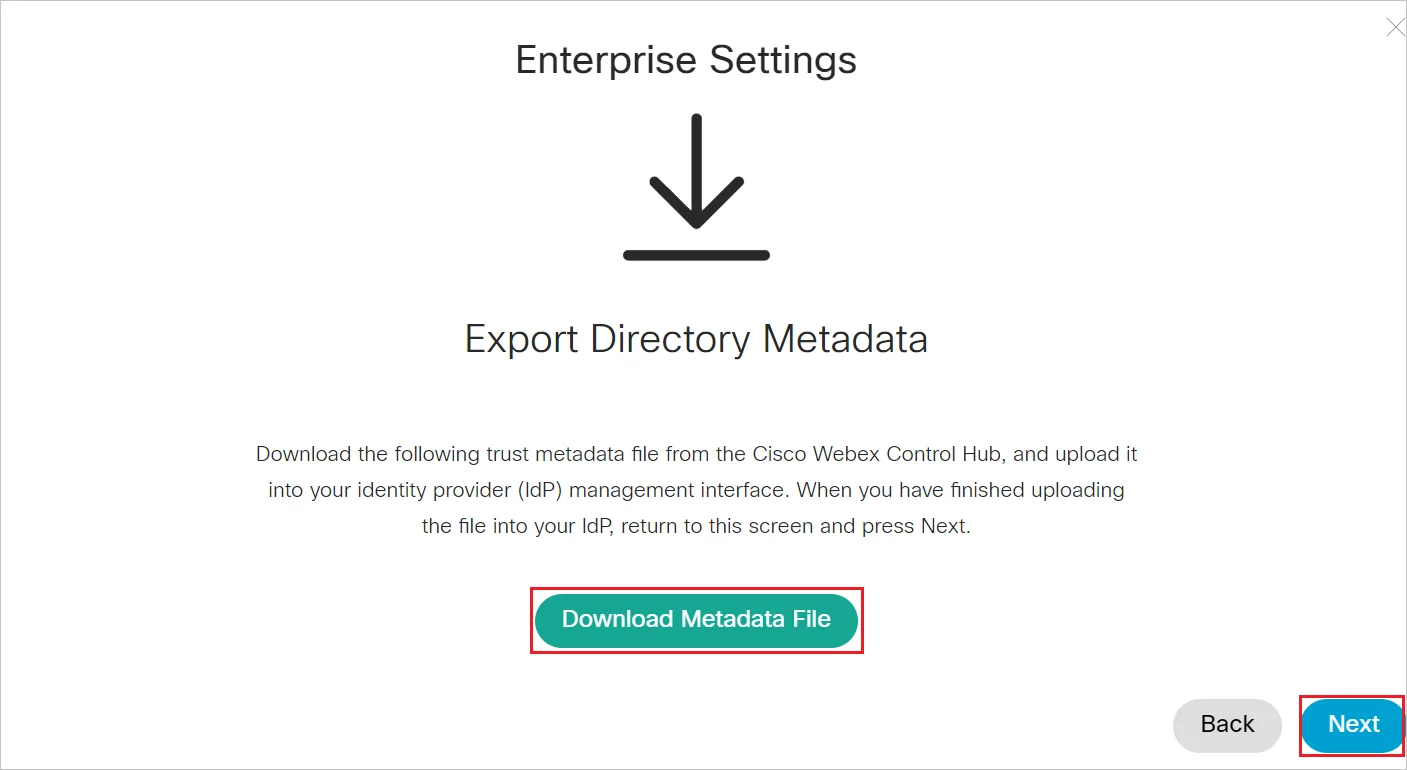
- Click on Download Metadata File to download the Service Provider Metadata file and keep it handy, click on Next.
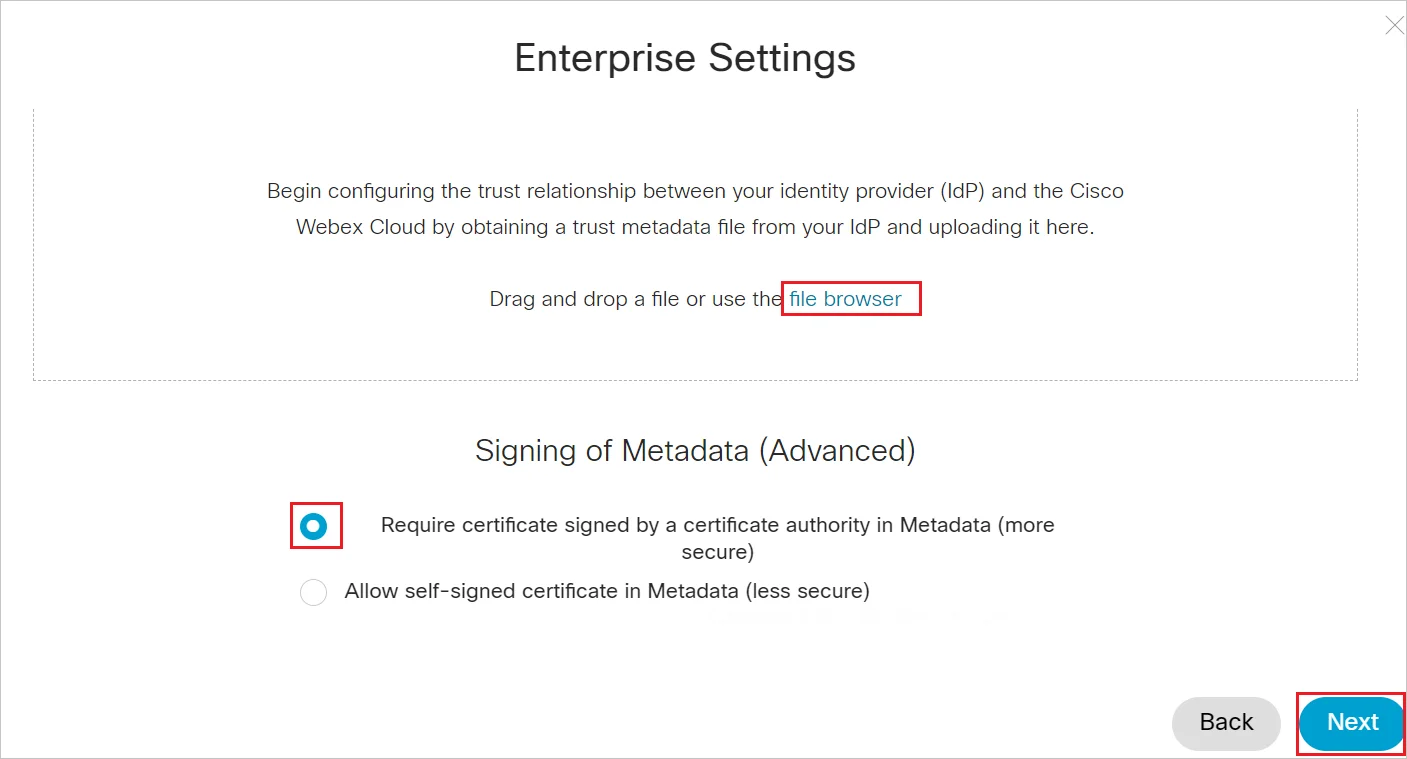
- Click on file browser option to locate and upload the miniOrange metadata file. Then, select Require certificate signed by a certificate authority in Metadata (more secure) and click Next.
- Click Save.
3. Test SSO Configuration
Test SSO login to your Cisco Spark Platform account with miniOrange IdP:
External References
