Need Help? We are right here!
Search Results:
×Unrestricted peripheral access creates major security gaps. Without proper endpoint security device control,
sensitive data and compliance are at risk.

Employees or contractors can copy confidential data onto removable media within seconds. Intellectual property, financial reports, and source code can be exfiltrated without detection.

Malicious insiders may intentionally transfer sensitive files to unauthorized devices. Accidental insiders may unknowingly violate compliance rules by using personal storage devices.

Infected USB drives remain a common attack vector. Malware introduced through external devices can bypass perimeter defenses and spread laterally across networks.

Unapproved hardware such as portable SSDs, modems, smartphones, and external storage can create hidden attack surfaces.

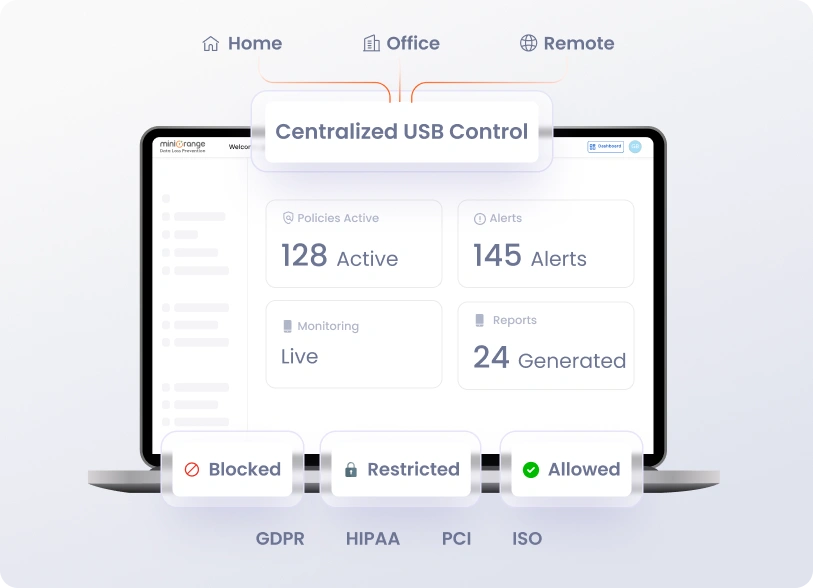
Without centralized monitoring, IT teams can’t track connected devices or data transfers, creating security gaps and compliance risks.

All remote control communications are fully encrypted, ensuring that data in transit remains secure and confidential during every remote session
miniOrange device control software provides layered protection across endpoints using granular policies and centralized governance.

Block or allow USB storage devices and external drives with granular access control rules. Monitor file transfers and prevent unauthorized copying to protect sensitive data.

Get real-time insight into all connected peripherals. Track device usage, generate audit logs, and detect suspicious activity across endpoints.
Simplify onboarding with zero-touch enrollment and automated provisioning. Pre-configure devices, assign users, and enforce corporate policies during the setup process.

Deploy, update, and manage corporate apps across all devices from a single dashboard. Enforce app compliance, whitelist/blacklist applications, and prevent data leakage.

Gain insights into device compliance, usage trends, and operational risks. Generate detailed reports to support audits and maintain enterprise security standards.

Define granular permissions for IT admins, managers, and support staff. Assign responsibilities based on roles to ensure secure and accountable device management.
miniOrange’s cross-platform mobile device management ensures IT teams can manage all operating systems from a single dashboard without switching tools.
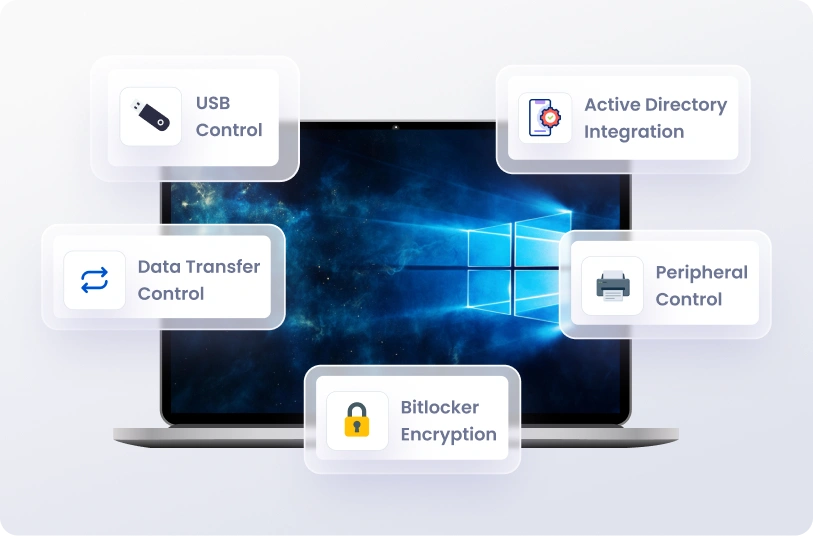
Our device control for Windows ensures granular protection for all corporate endpoints.
Secure Apple endpoints with precise endpoint device control.

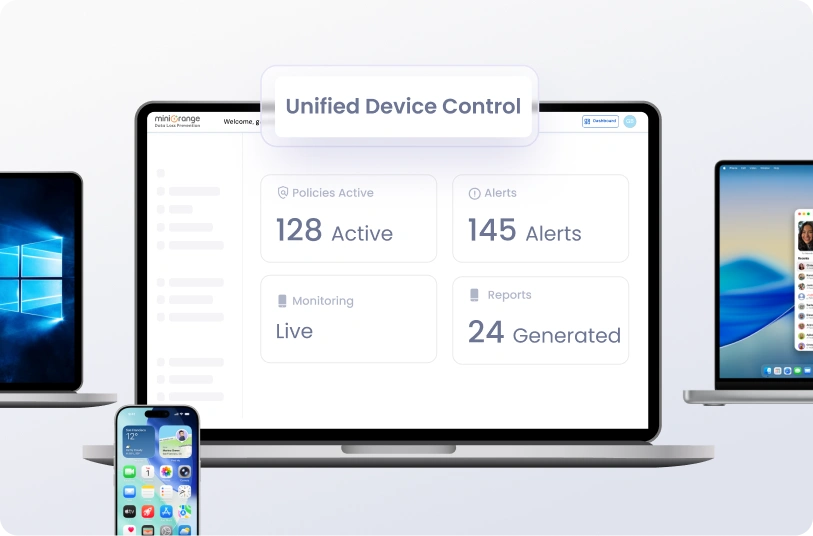
Manage all endpoints with a unified, enterprise-grade endpoint device control system.
Protect sensitive data and maintain compliance across remote and hybrid teams with endpoint device control.
Enterprise device control is critical across industries handling sensitive data.
Protect customer financial data, prevent fraud, and maintain regulatory compliance.

Secure patient records and prevent unauthorized PHI transfers.

Safeguard classified data and restrict external media usage.

Control student device access and prevent data leakage from institutional systems.
Uncontrolled USB and peripheral devices create direct pathways for malware and data theft. Device control software blocks unauthorized removable media and reduces external attack vectors across endpoints.
Employees can intentionally or accidentally transfer sensitive data to external devices. Enterprise device control enforces strict access policies and continuous monitoring to reduce insider-driven security incidents.
Regulations require visibility into data movement. Device control provides detailed logs, policy enforcement, and centralized reporting to support audit and compliance requirements.
Modern security frameworks demand verification of every connected device. Device control enforces default-deny policies and role-based permissions to secure endpoint interactions.
Device control works alongside DLP and endpoint security solutions to add hardware-level enforcement, creating layered protection across the enterprise.
Get answers to the most common Device Control security questions.
