Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
×
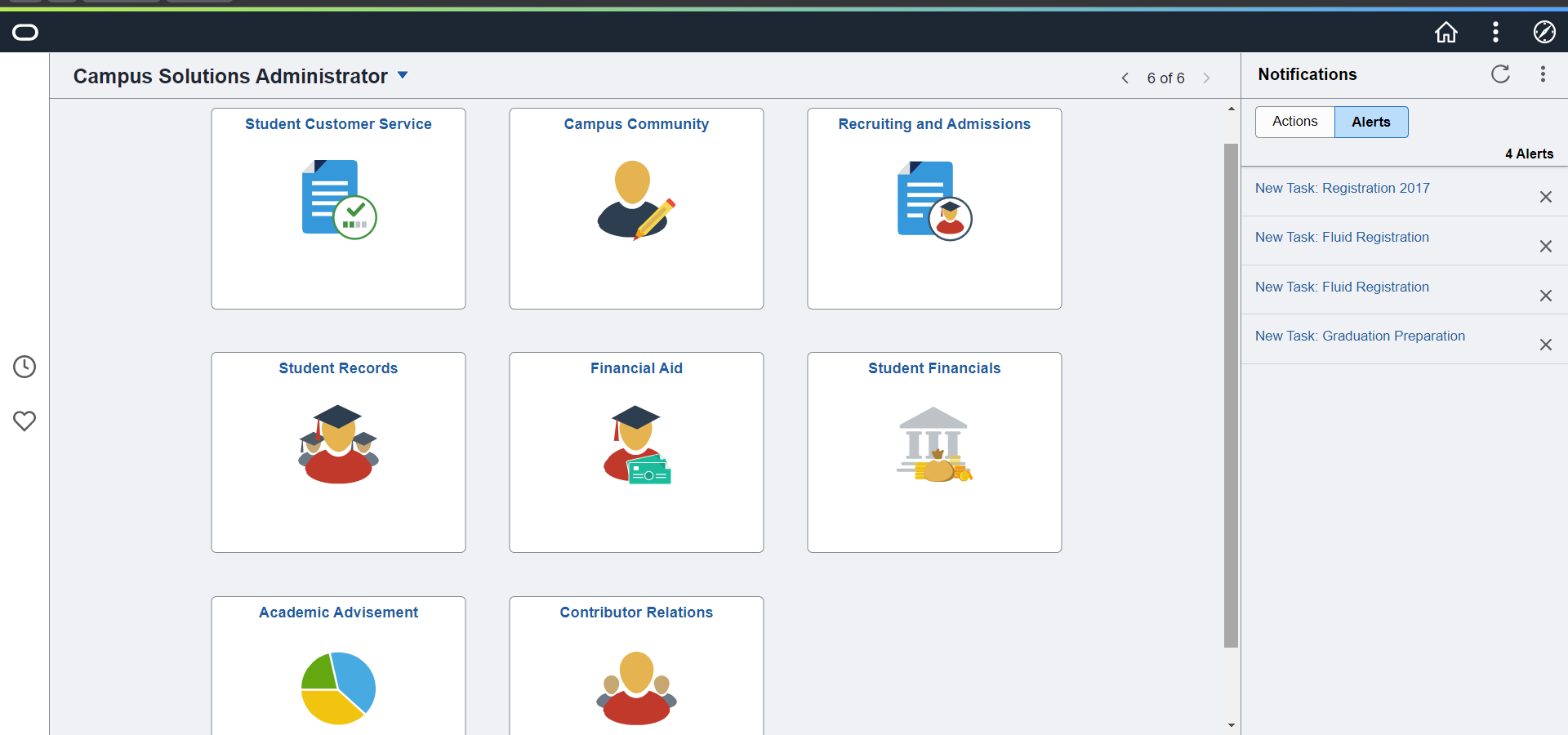
PeopleSoft, developed by Oracle, is a suite of business applications for human resource management, financials, supply chain management, and other core business functions. Adding MFA to PeopleSoft applications helps organizations protect against unauthorized access, thereby enhancing the security of their data and systems.
PeopleSoft Multi-Factor Authentication (MFA) refers to a security enhancement for PeopleSoft applications that requires users to provide two or more verification factors to gain access to a resource, such as an application or online account. This is an extra layer of security designed to ensure that you're the only person who can access your account, even if someone else knows your password.
Multi-Factor Authentication typically involves a combination of something you know (like a password or PIN), something you have (such as a smartphone app to approve authentication requests or a security token), and something you are (like a fingerprint or other biometric method). By requiring two or more of these authentication methods, PeopleSoft MFA makes it significantly harder for unauthorized users to access sensitive information and systems.
miniOrange offers 1 hour free help through a consultation call with our System Engineers to Install or Setup PeopleSoft SSO SAML solution in your environment with 30 days free trial. For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you setting it up in no time.
miniOrange provides 15+ authentication methods and solutions for various use cases. Organizations can set up specific authentication and configuration options in addition to security, including
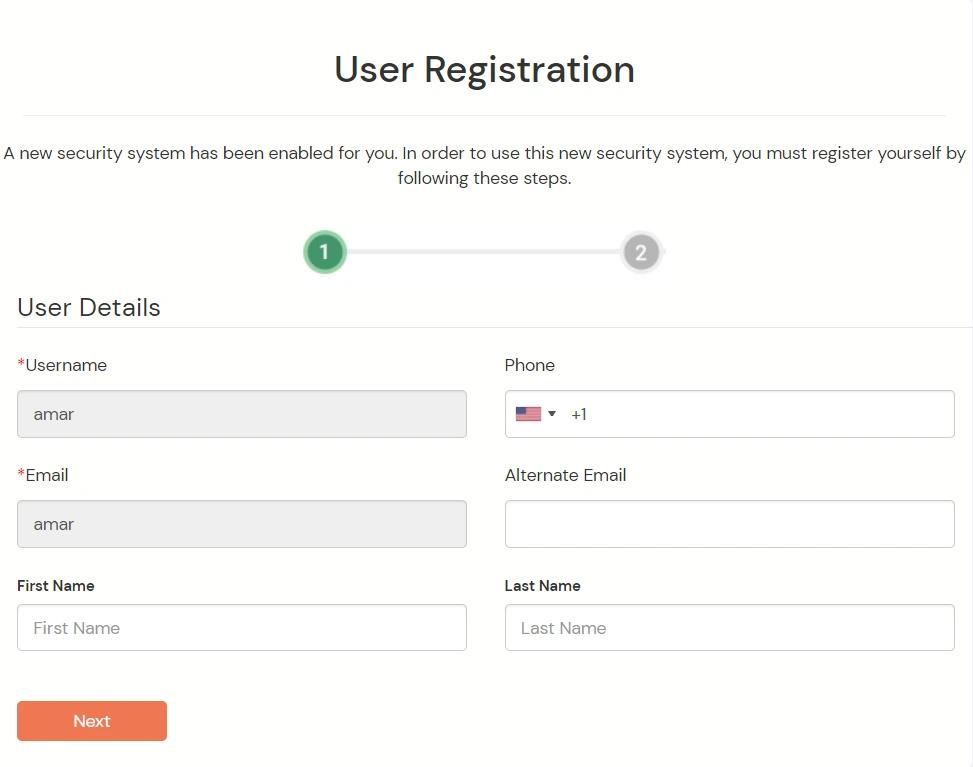
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
1. Applications involved in the deployment
2. Port Configuration

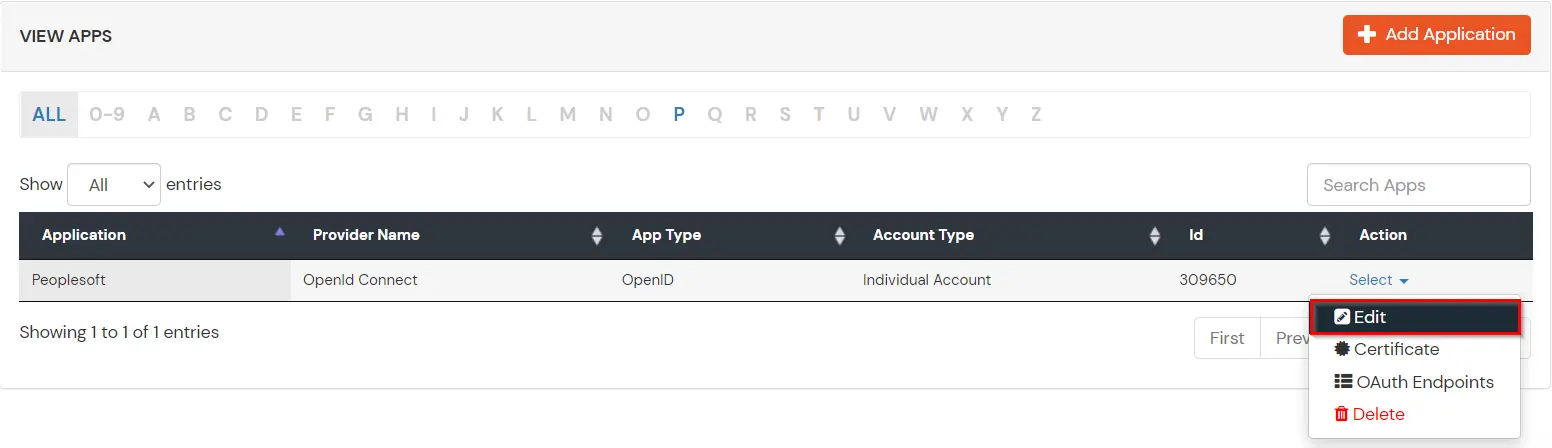
You can edit Application by using the following steps:
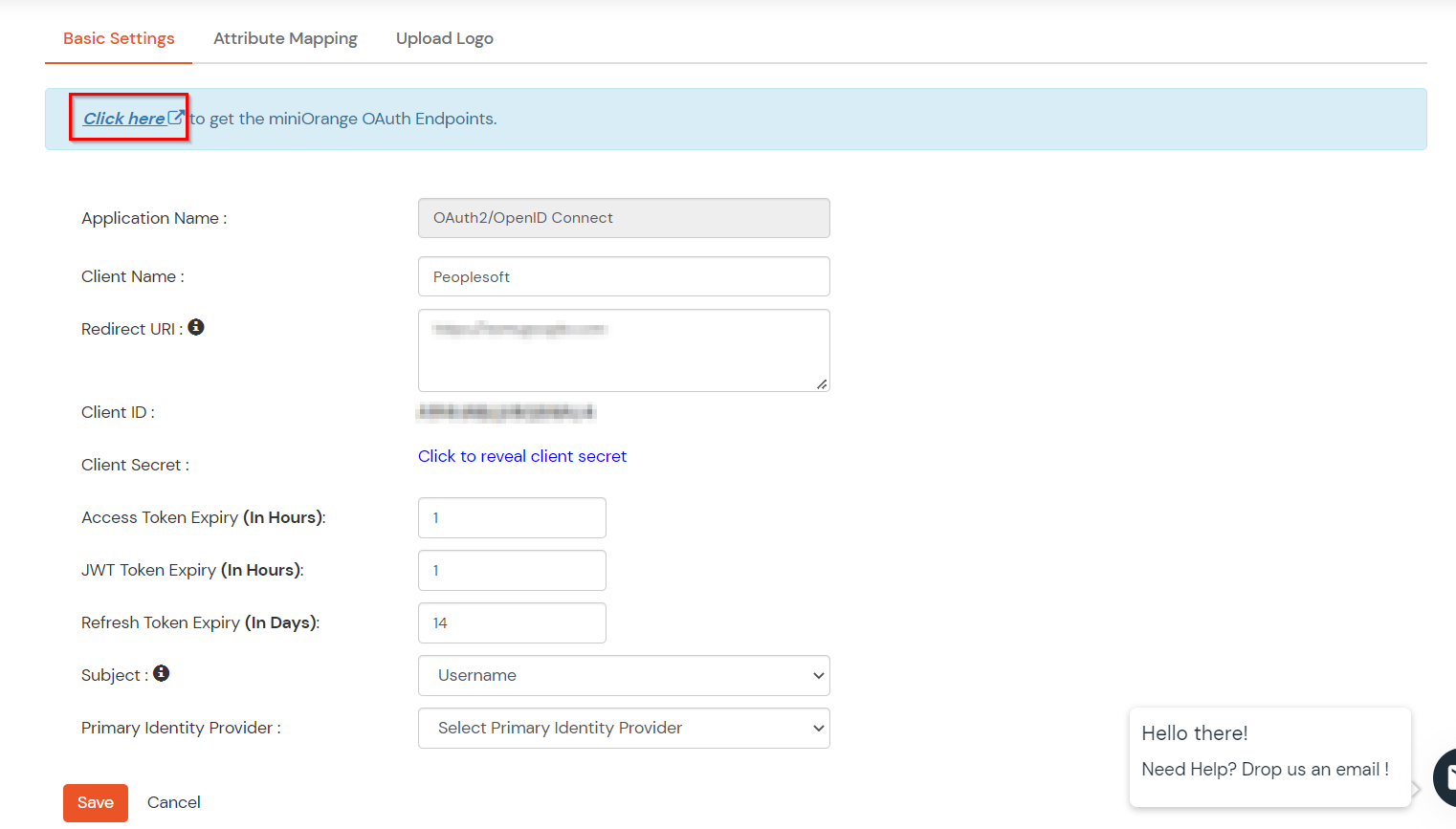
| Authorization Endpoint: | https://login.xecurify.com/moas/idp/openidsso (Note: Use this endpoint only if you want to use miniorange as oauth identity server.) https://login.xecurify.com/moas/broker/login/oauth/260174 (Note: Use this enpoint only if you are configuring any Identity Provider in Identity Providers Menu and not using miniorange as IDP.) |
| Token Endpoint: | https://login.xecurify.com/moas/rest/oauth/token |
| User Info Endpoint: | https://login.xecurify.com/moas/rest/oauth/getuserinfo |
| Introspection Endpoint: | https://login.xecurify.com/moas/rest/oauth/introspect |
| Revoke Endpoint: | https://login.xecurify.com/moas/rest/oauth/revoke |
| OpenID Single Logout Endpoint: | https://login.xecurify.com/moas/idp/oidc/logout?post_logout_redirect_uri=<YOUR-APP-LOGOUT-URL> |
| email: | View email address of the user |
| profile: | View profile attributes of the user account |
| openid: | Retrieve JWT token for OpenID Connect |
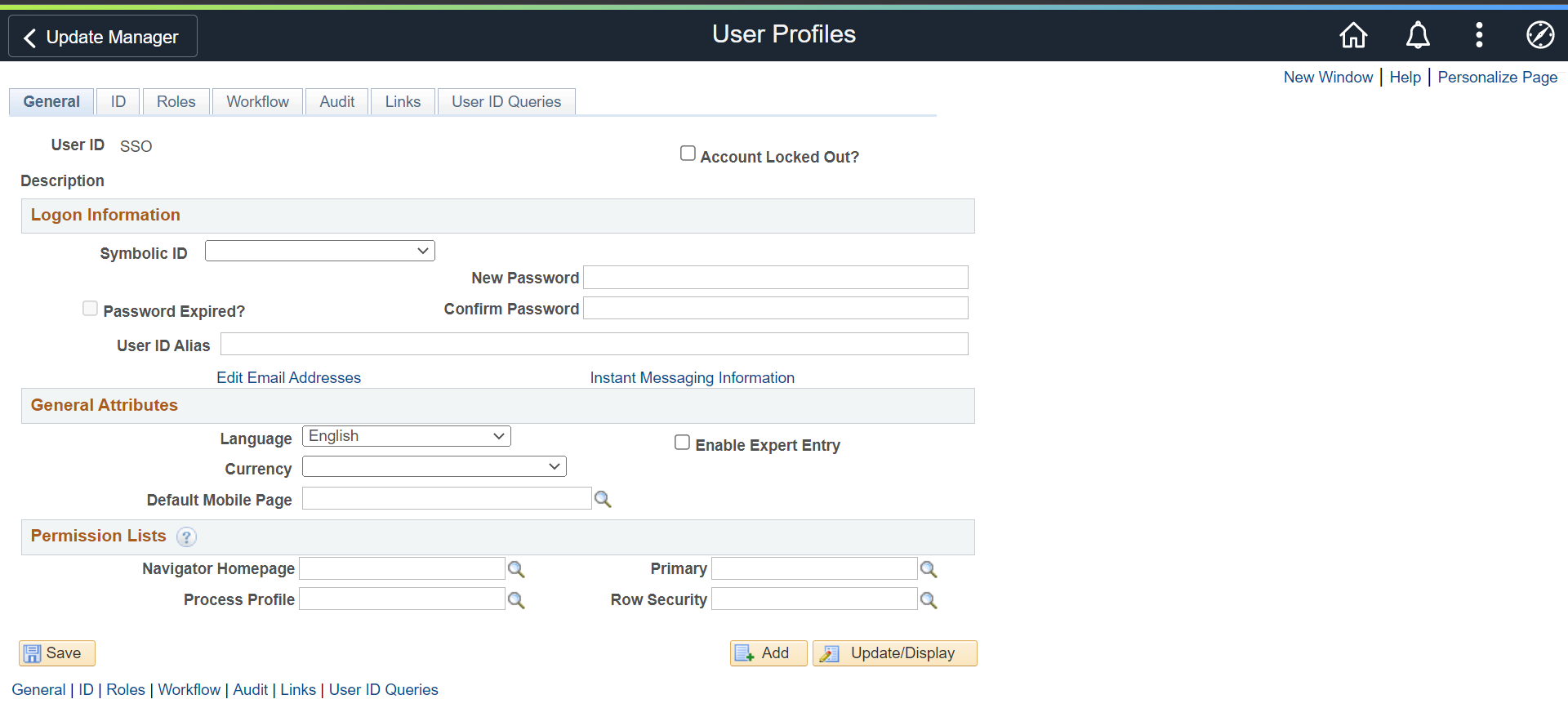
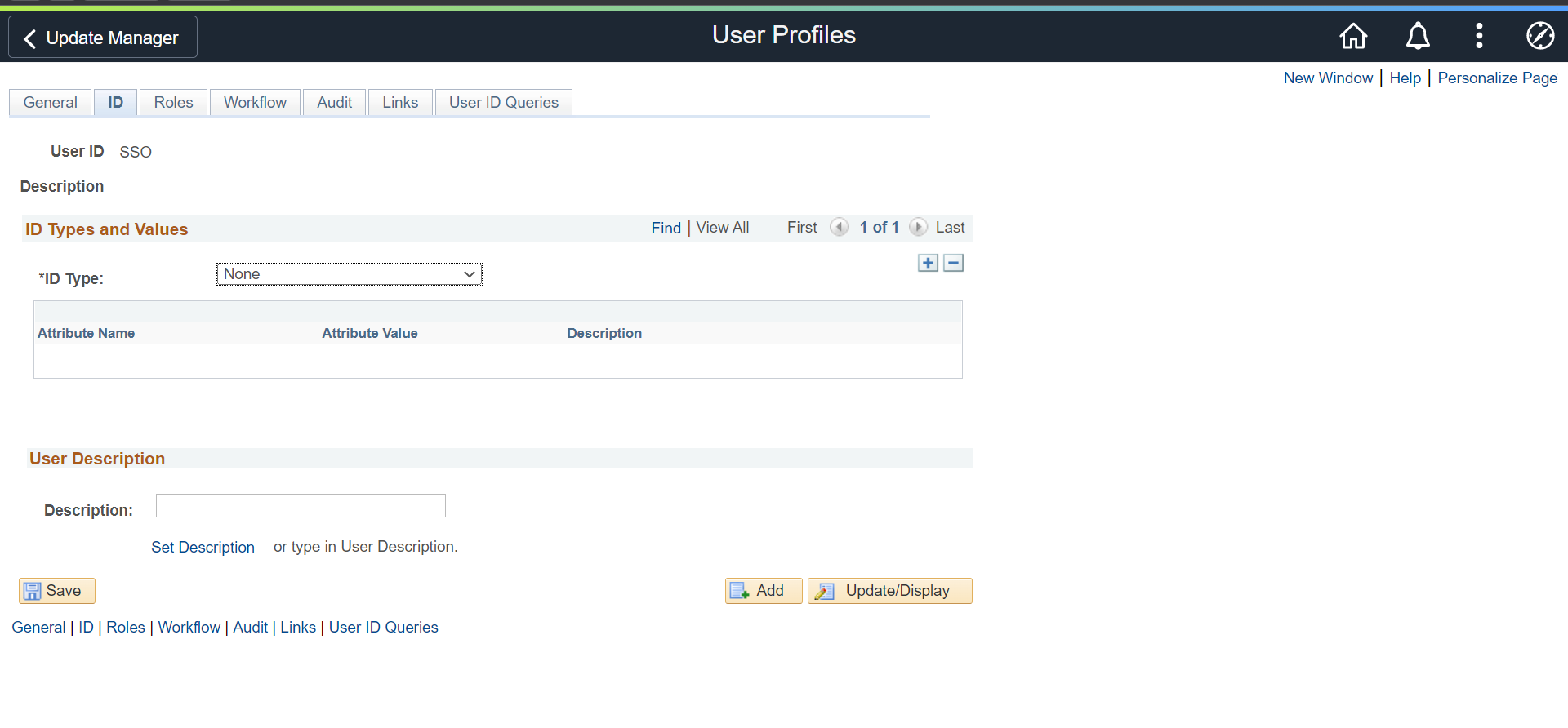
| User ID | SSO |
| Symbolic ID | Blank |
| ID Type | None |
| Role | PeopleSoft User |
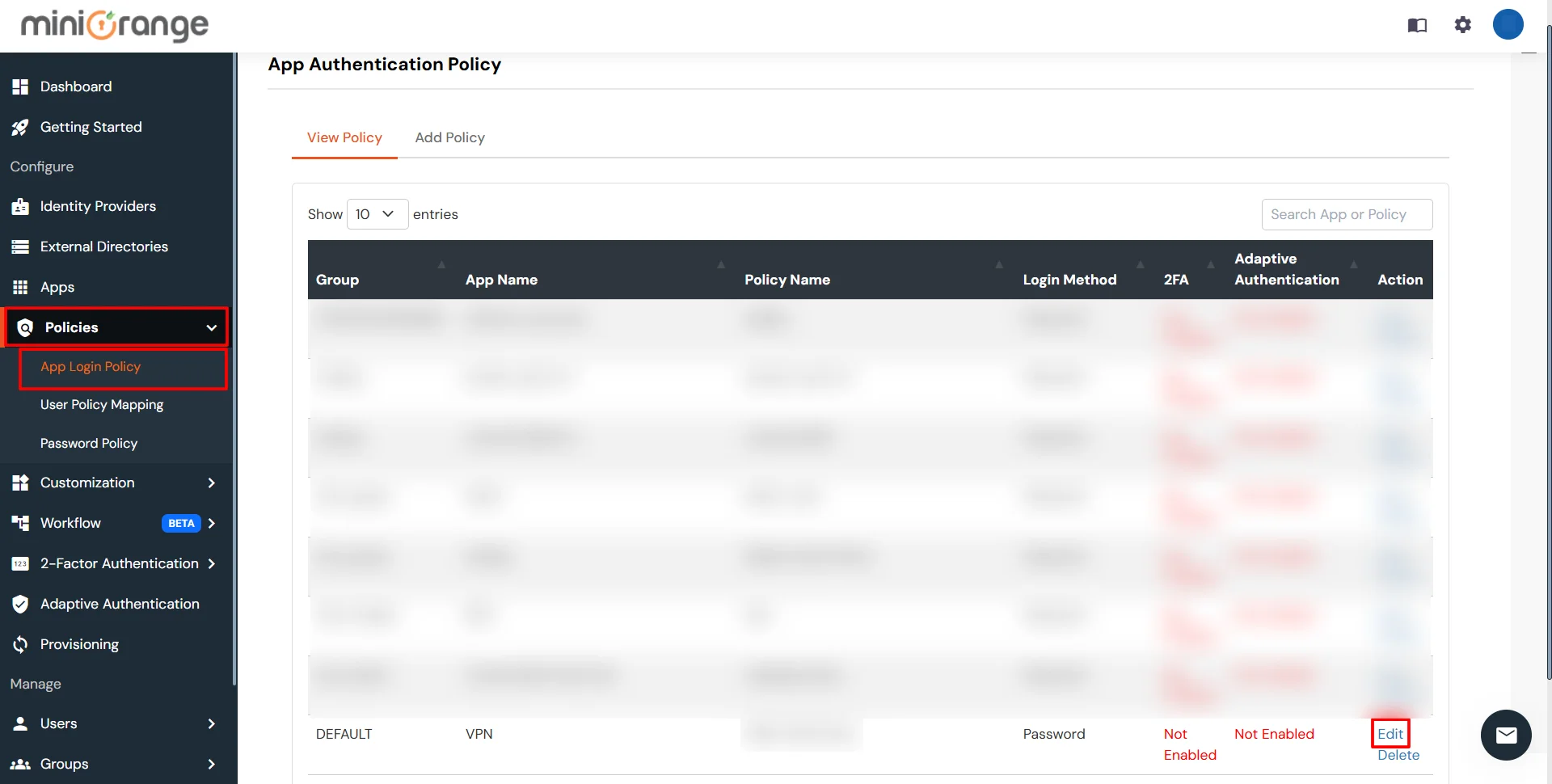
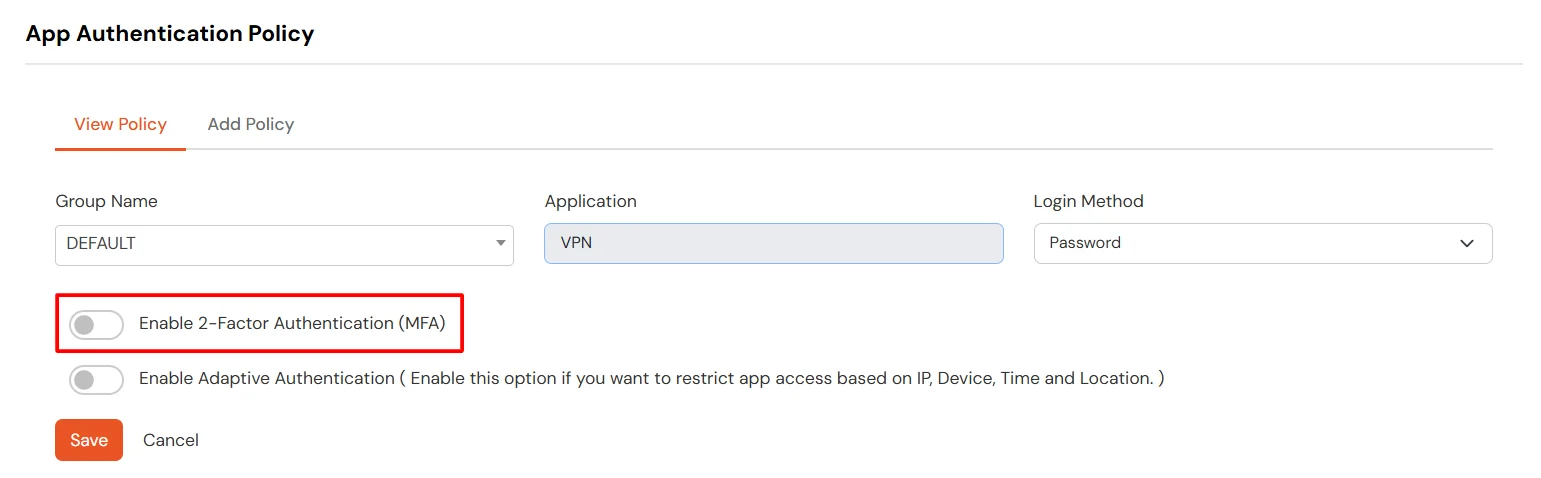
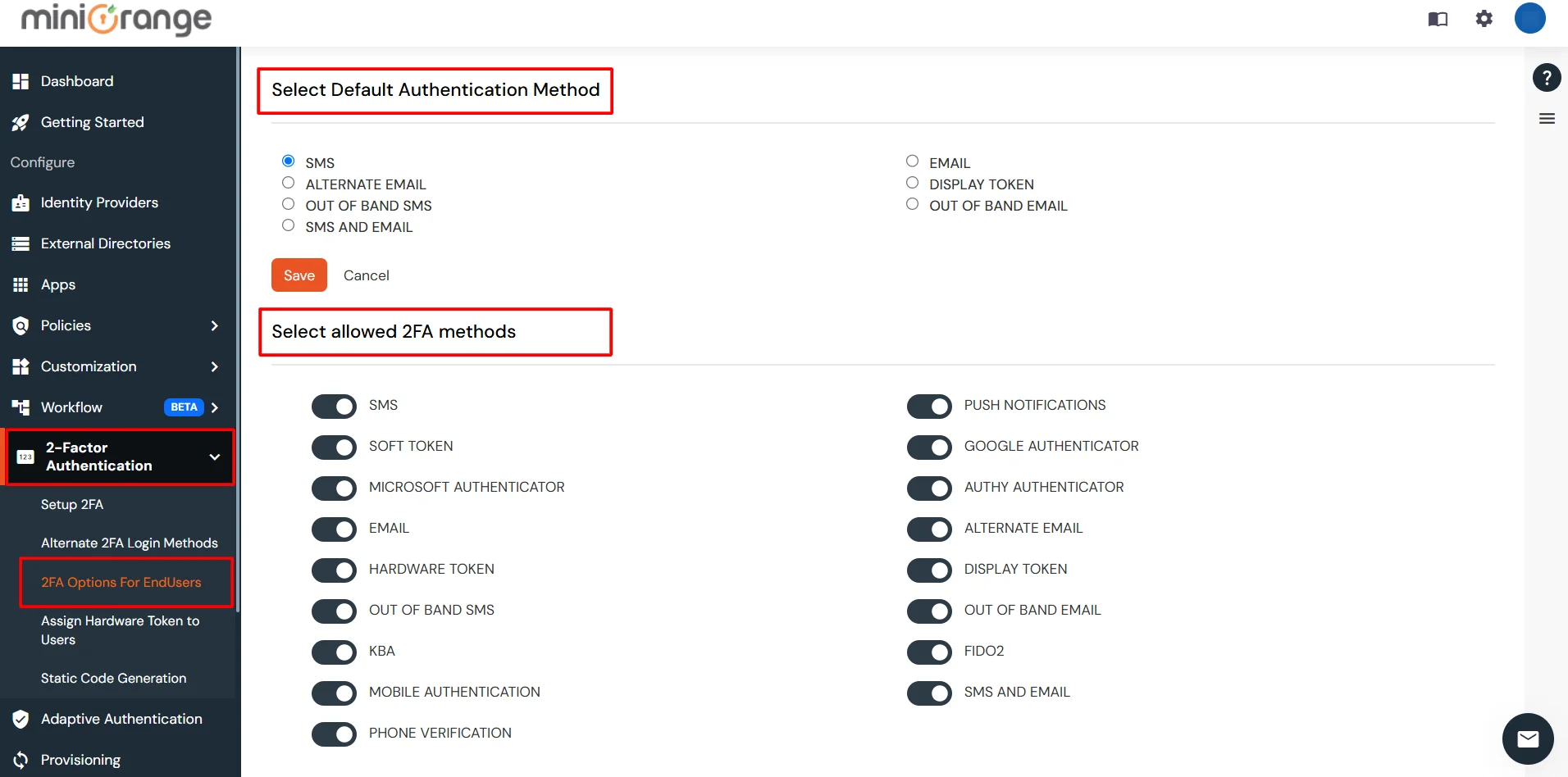
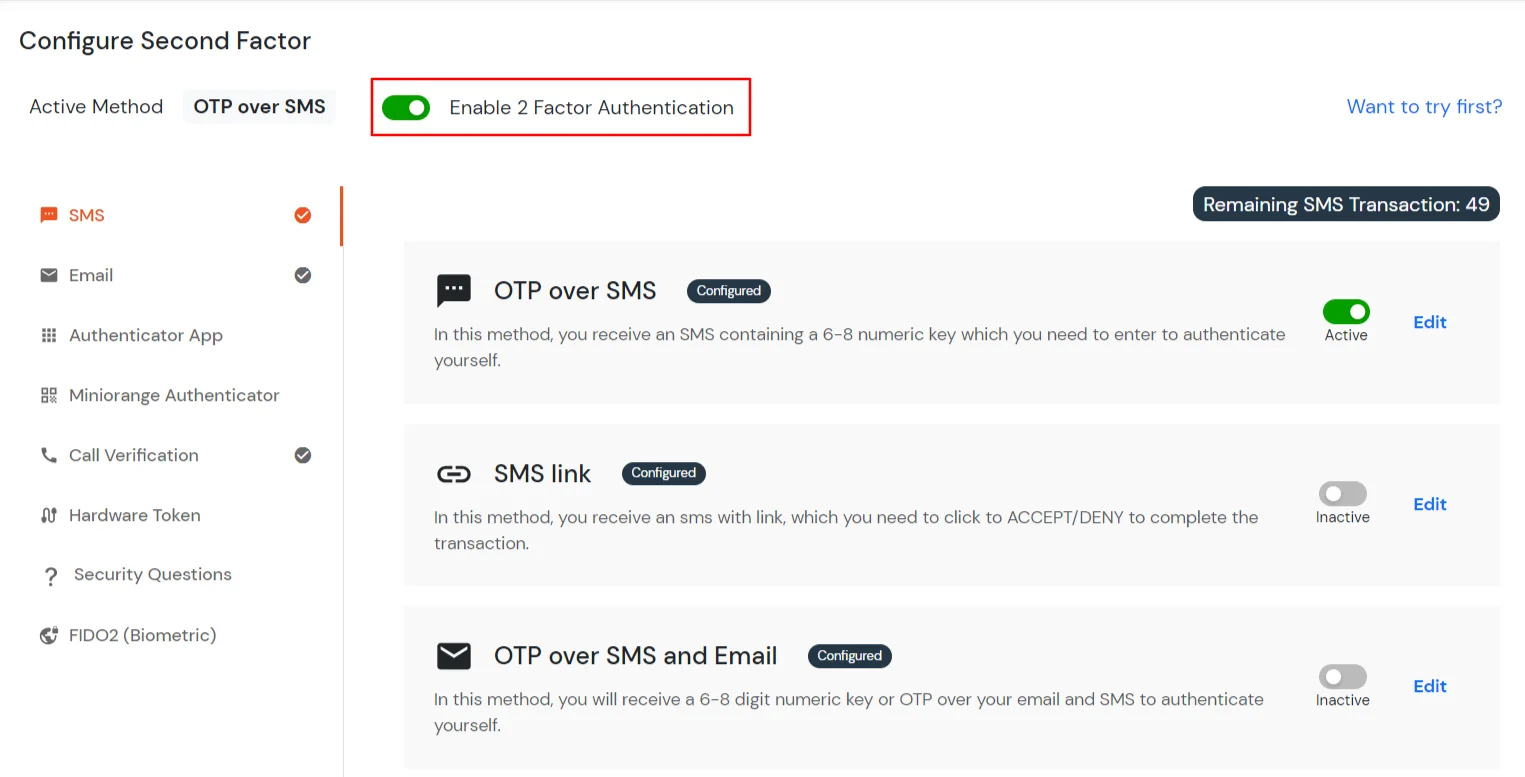
3.1: Enable 2FA for Users of PeopleSoft app
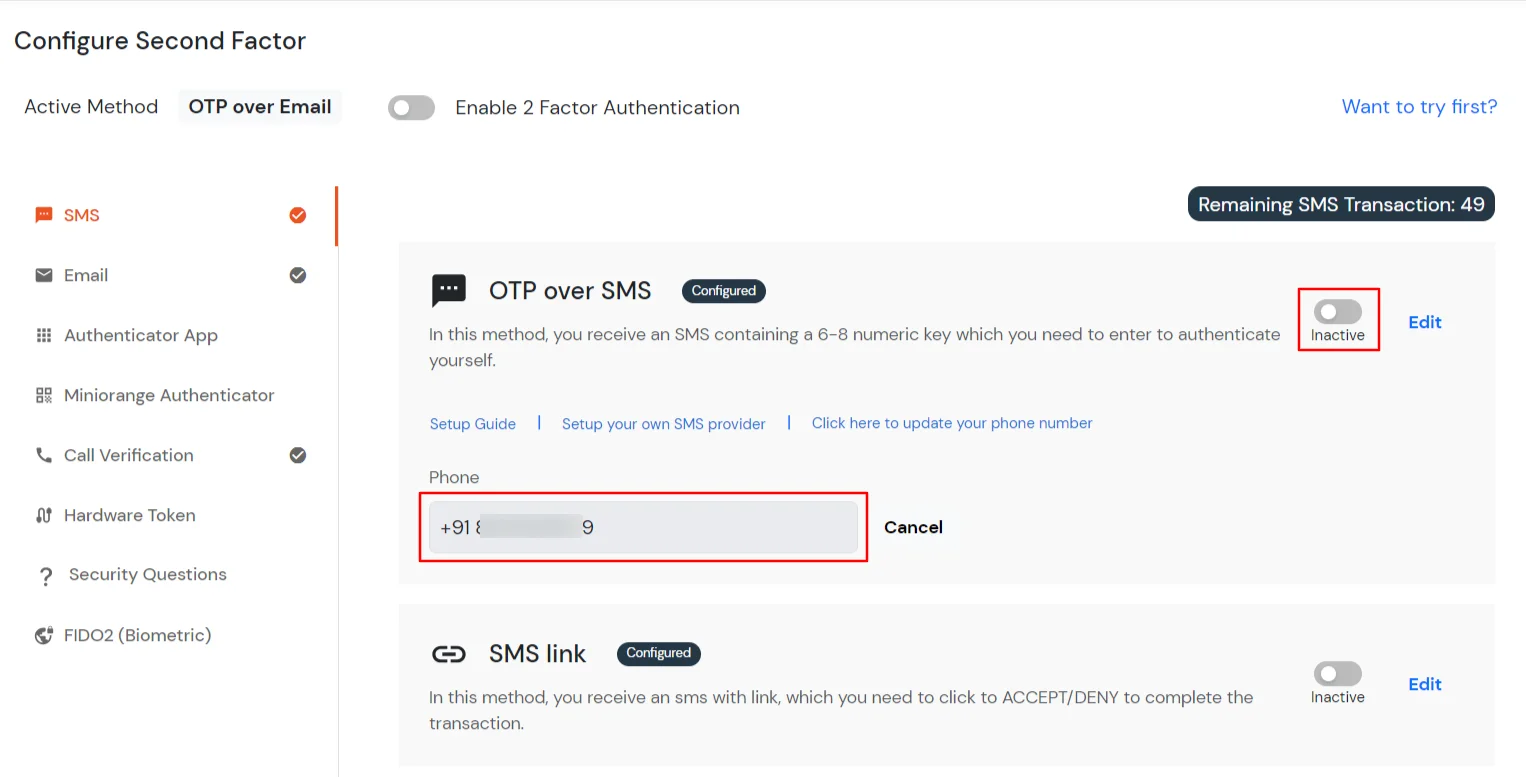
3.2: Configure 2FA for your Endusers
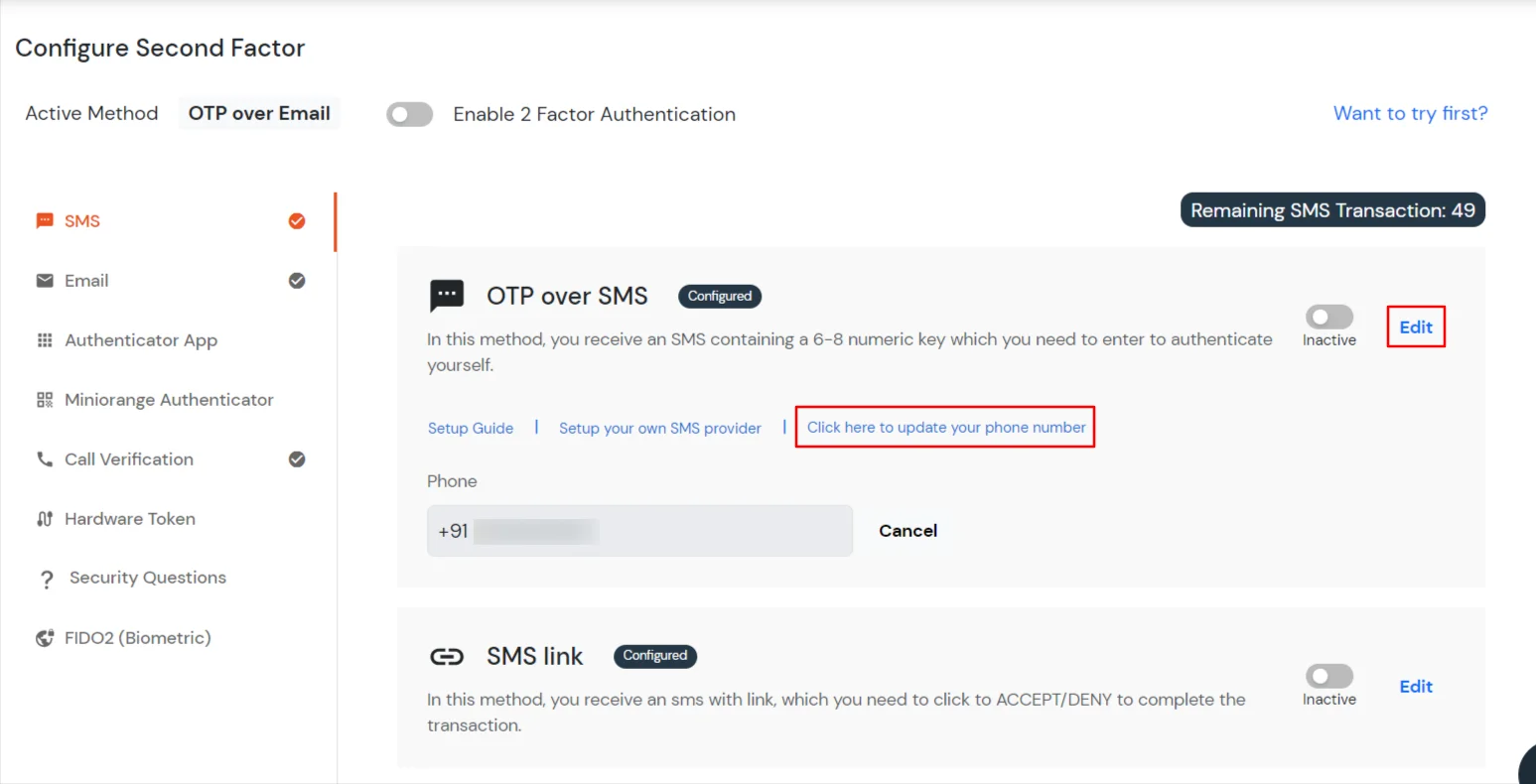
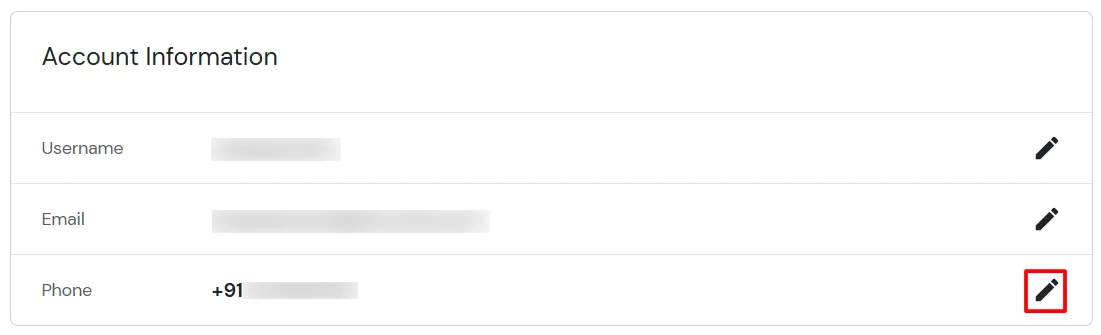
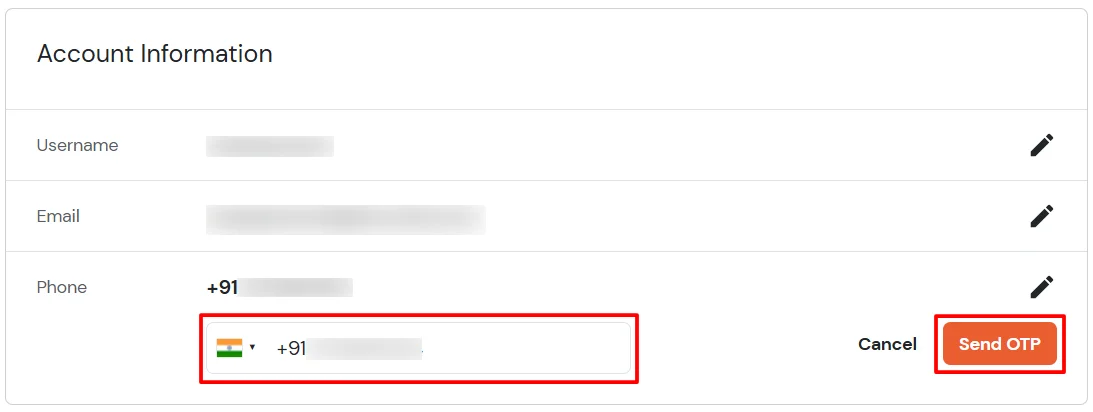
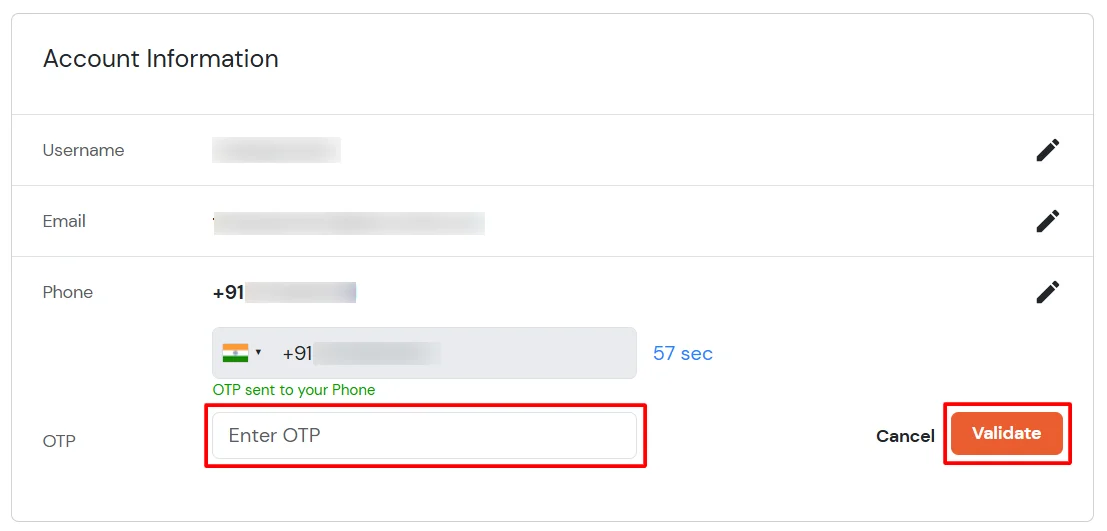
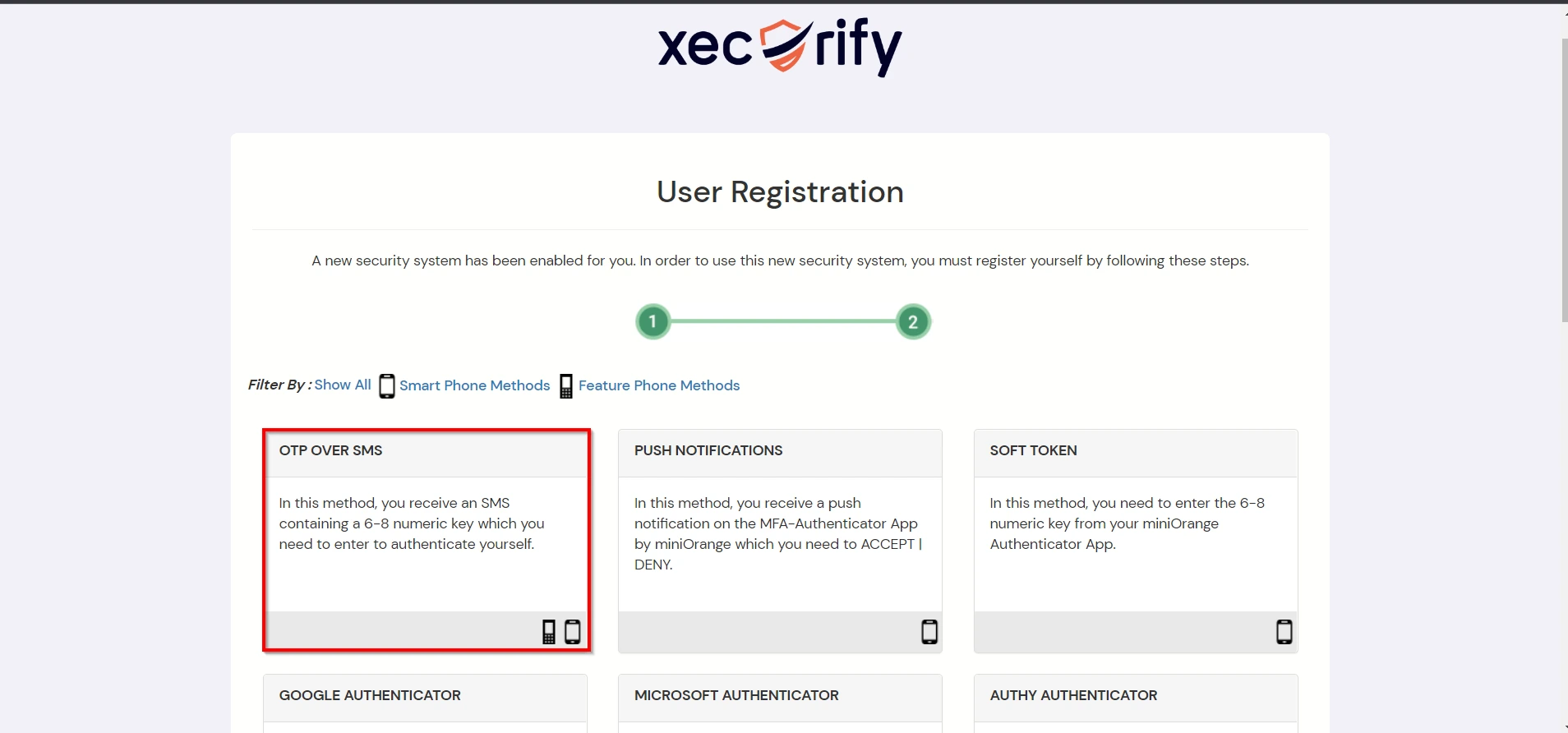
3.3: Enduser 2FA Setup
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.
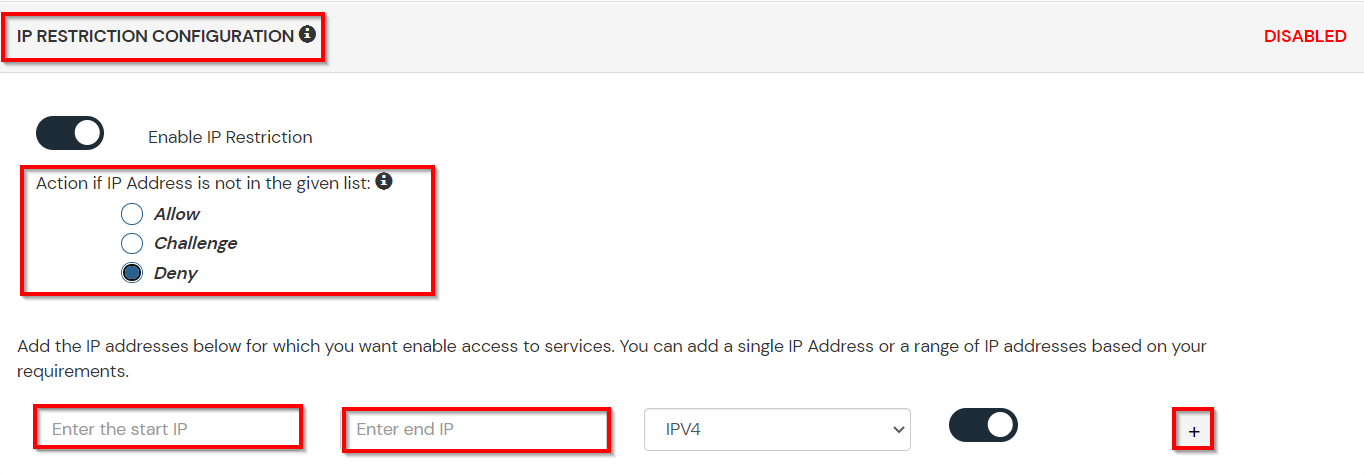
A. Restricting access to PeopleSoft with IP Configuration
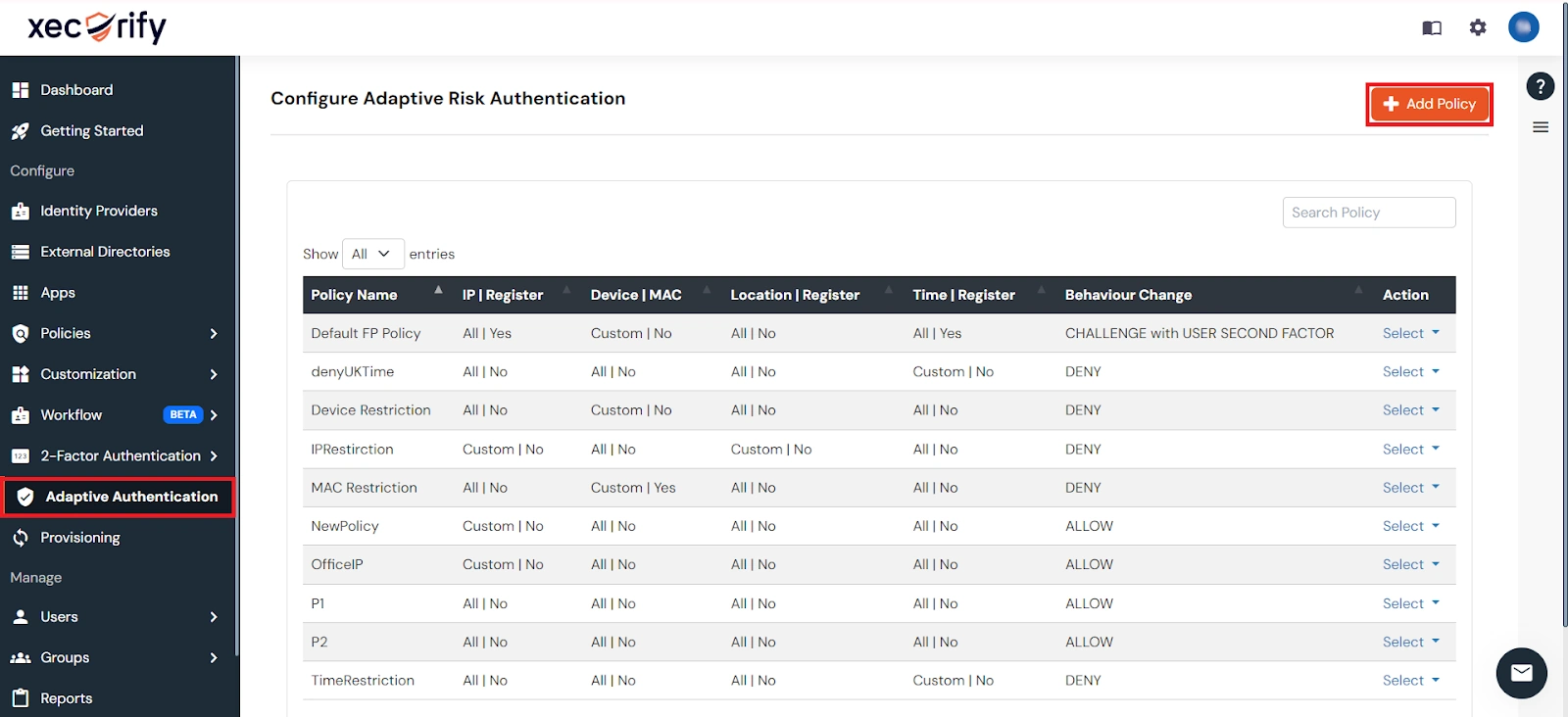
You can use adaptive authentication with PeopleSoft Single Sign-On (SSO) to improve the security and functionality of Single Sign-On. You can allow a IP Address in certain range for SSO or you can deny it based your requirements and you can also challenge the user to verify his authenticity. Adaptive authentication manages the user authentication bases on different factors such as Device ID, Location, Time of Access, IP Address and many more.
You can configure Adaptive Authentication with IP Blocking in following way :
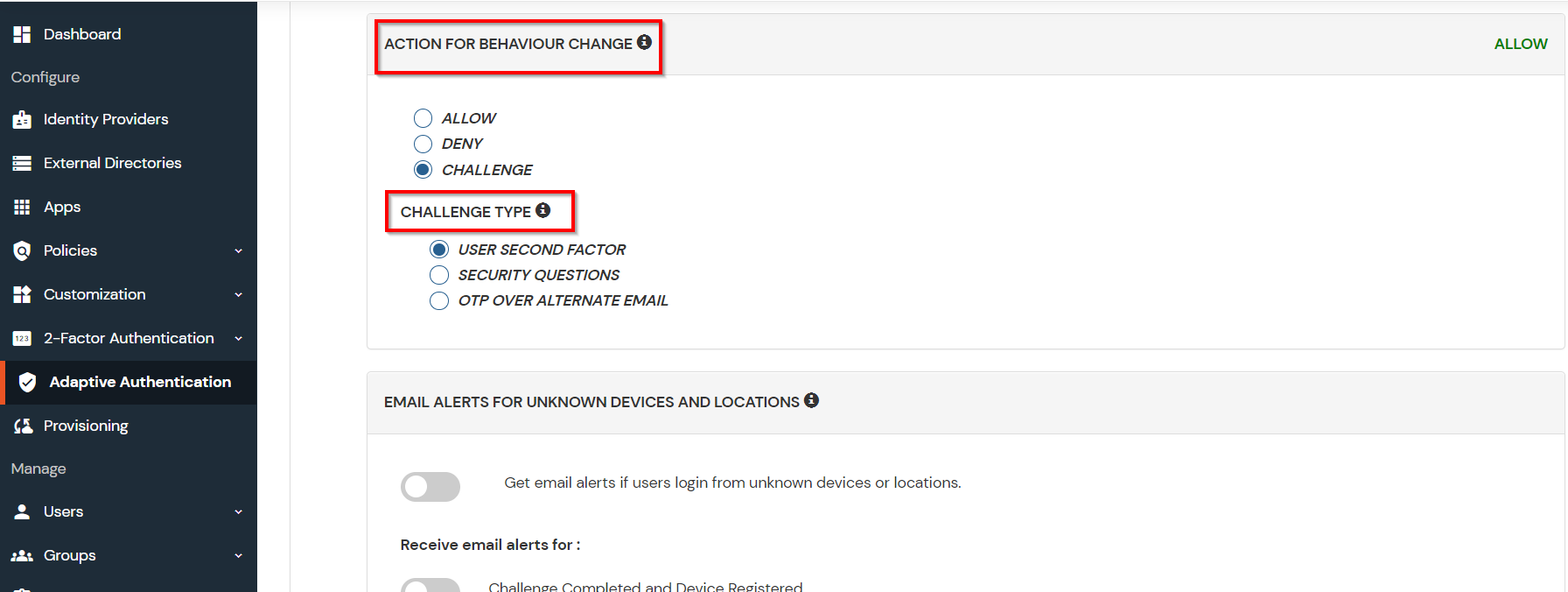
| Attribute | Description |
|---|---|
| Allow | Allow users to authenticate and use services if Adaptive authentication condition is true. |
| Deny | Deny user authentications and access to services if Adaptive authentication condition is true. |
| Challenge | Challenge users with one of the three methods mentioned below for verifying user authenticity. |
| Attribute | Description |
|---|---|
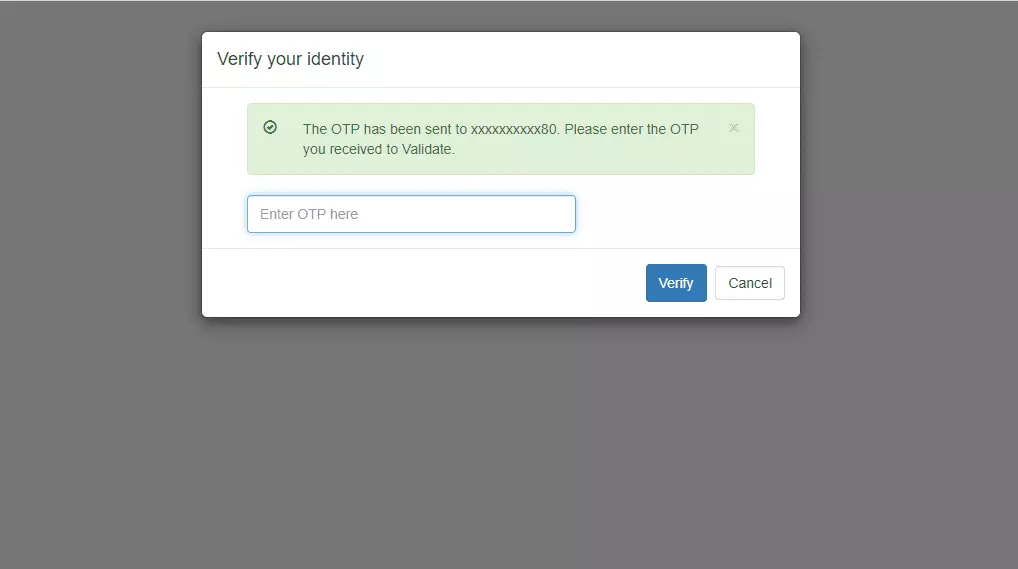
| User second Factor | The User needs to authenticate using the second factor he has opted or assigned for such as
|
| KBA (Knowledge-based authentication) | The System will ask the user for 2 of 3 questions he has configured in his Self-Service Console. Only after the right answer to both questions is the user allowed to proceed further. |
| OTP over Alternate Email | User will receive an OTP on the alternate email they have configured through the Self Service Console. Once the user provides the correct OTP, they are allowed to proceed further. |
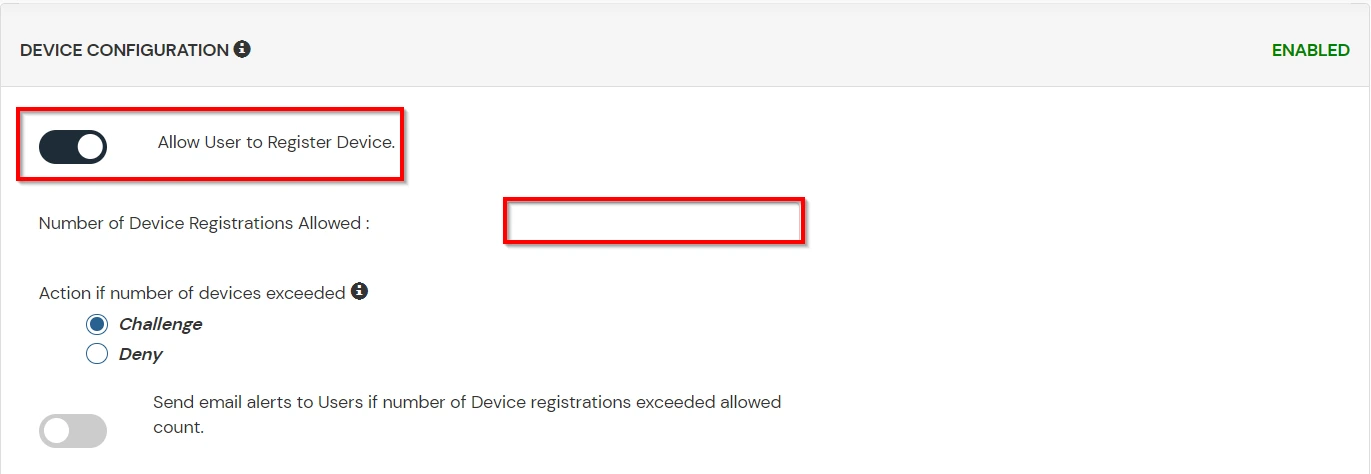
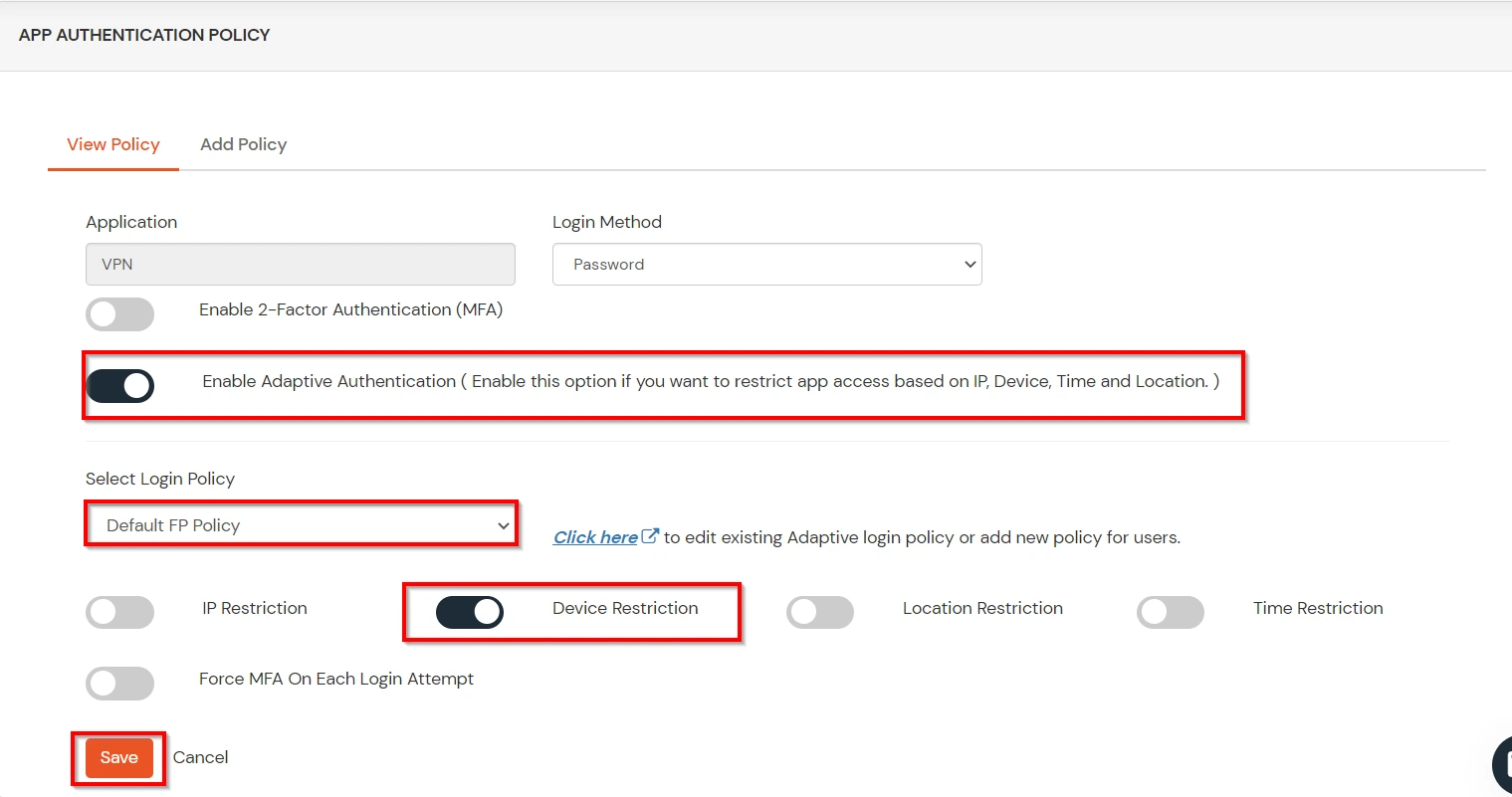
B. Adaptive Authentication with Limiting number of devices
Using Adaptive Authentication you can also restrict the number of devices the end user can access the Services on. You can allow end users to access services on a fixed no. of devices. The end users will be able to access services provided by us on this fixed no. of devices.
You can configure Adaptive Authentication with Device Restriction in following way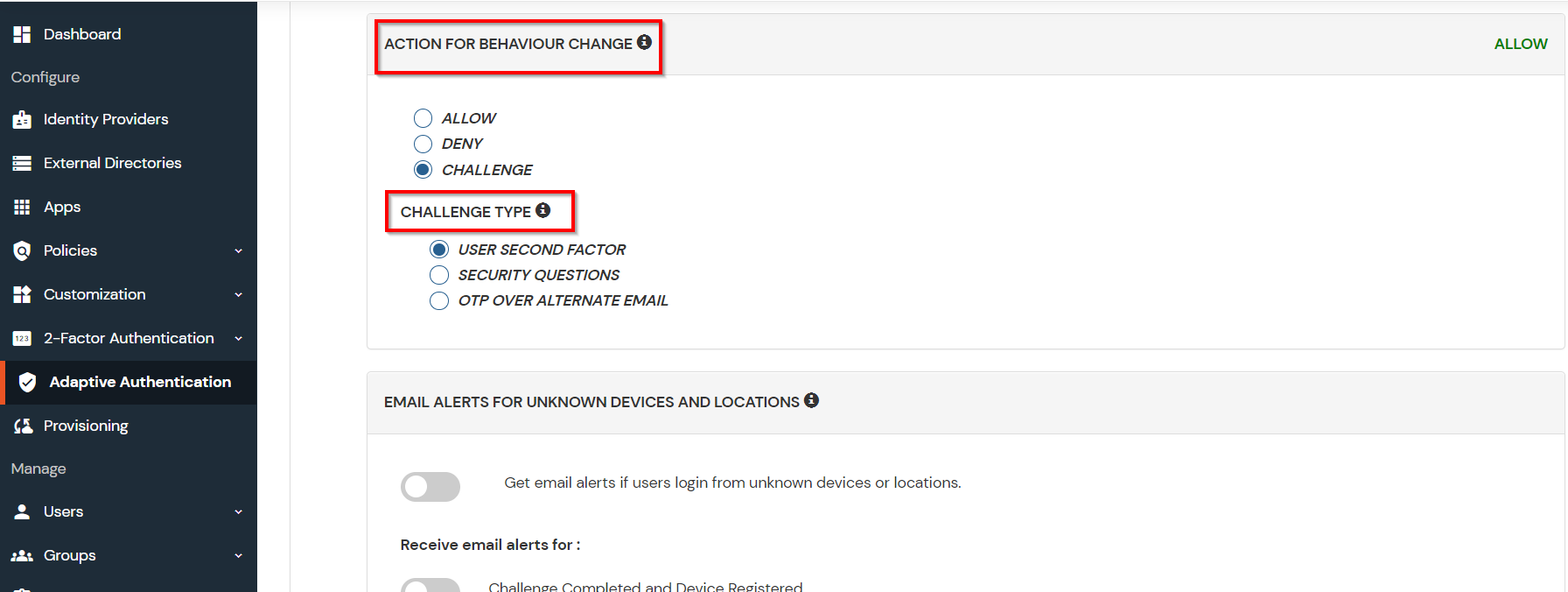
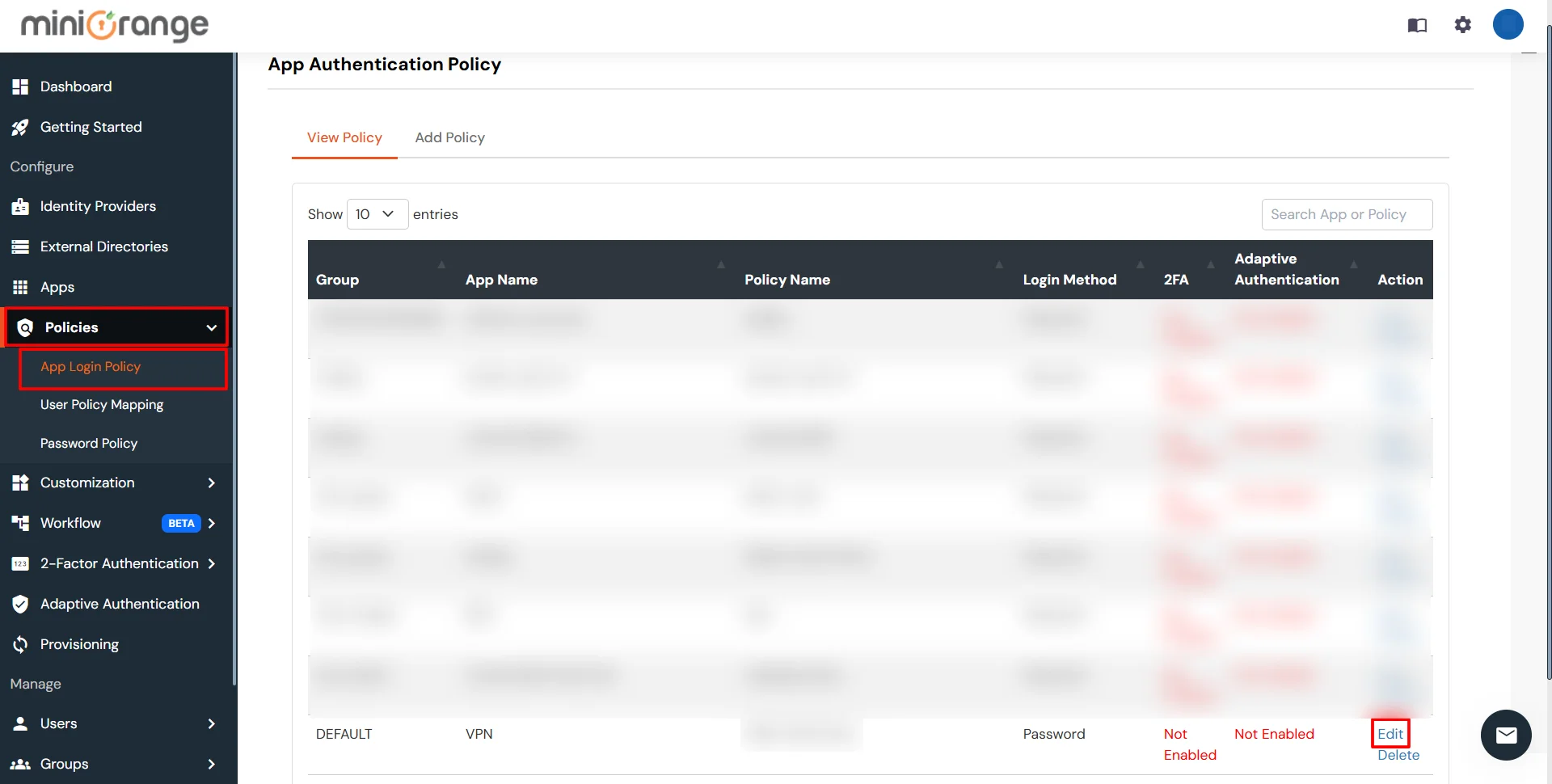
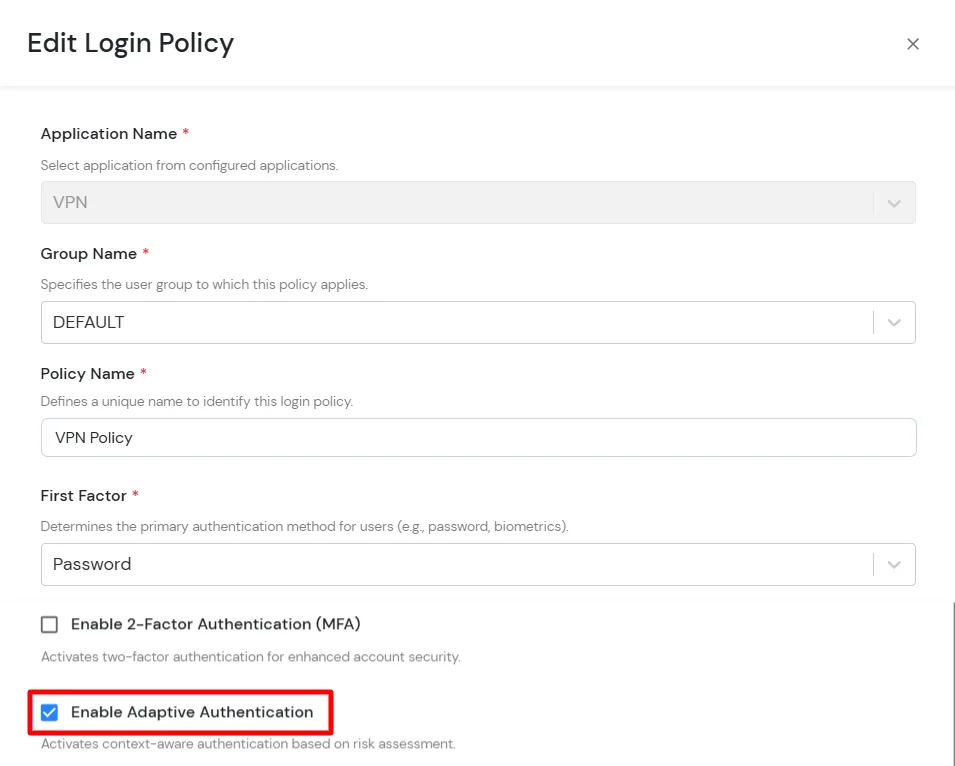
C. Add Adaptive Authentication policy to PeopleSoft
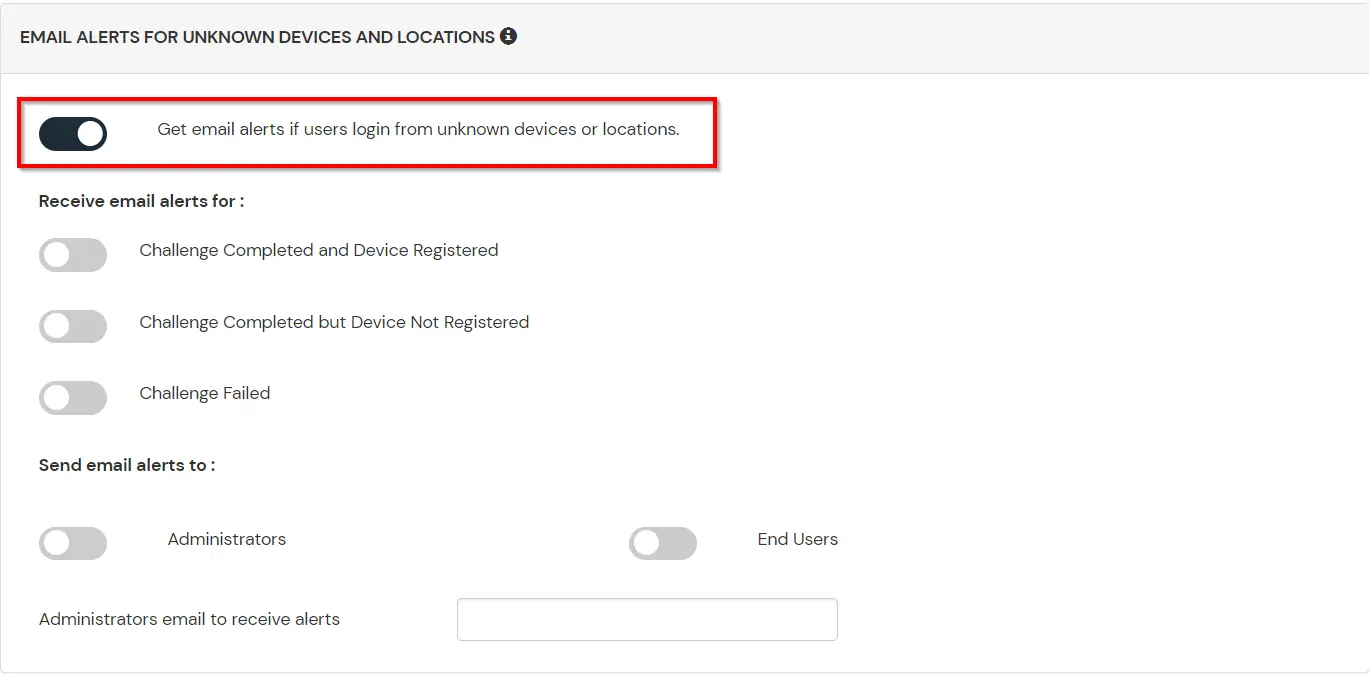
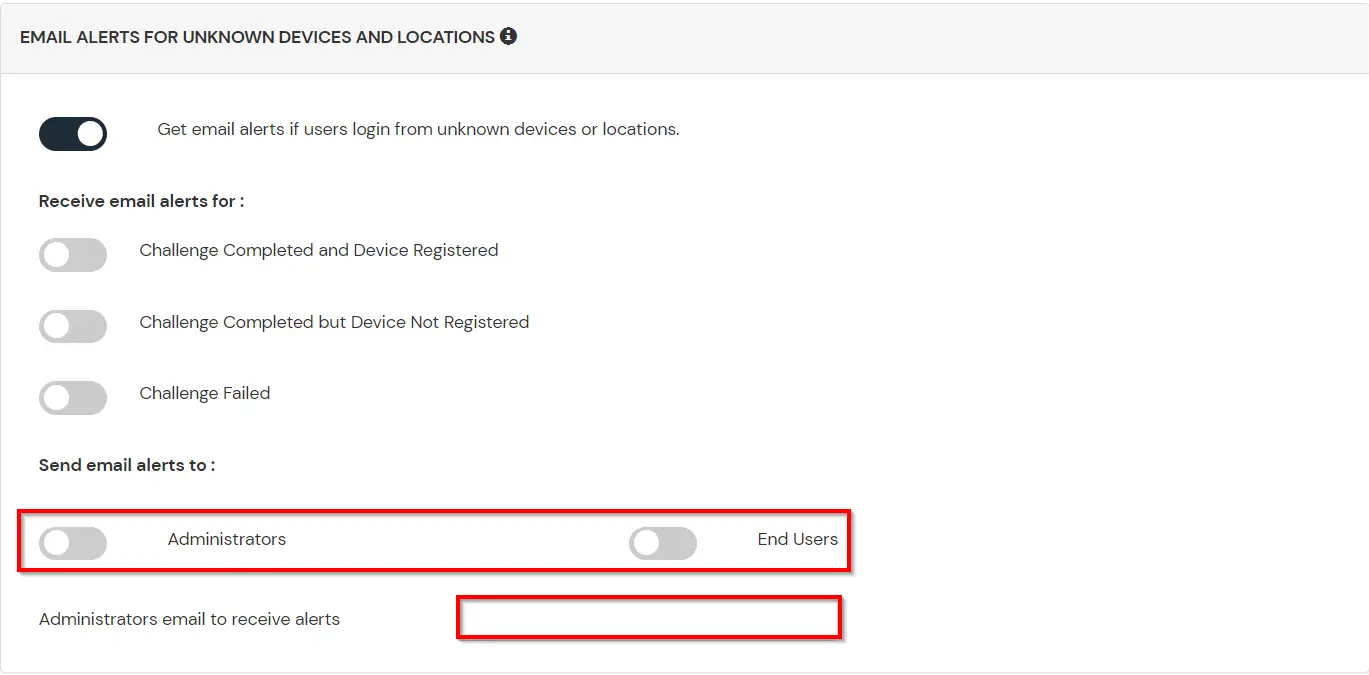
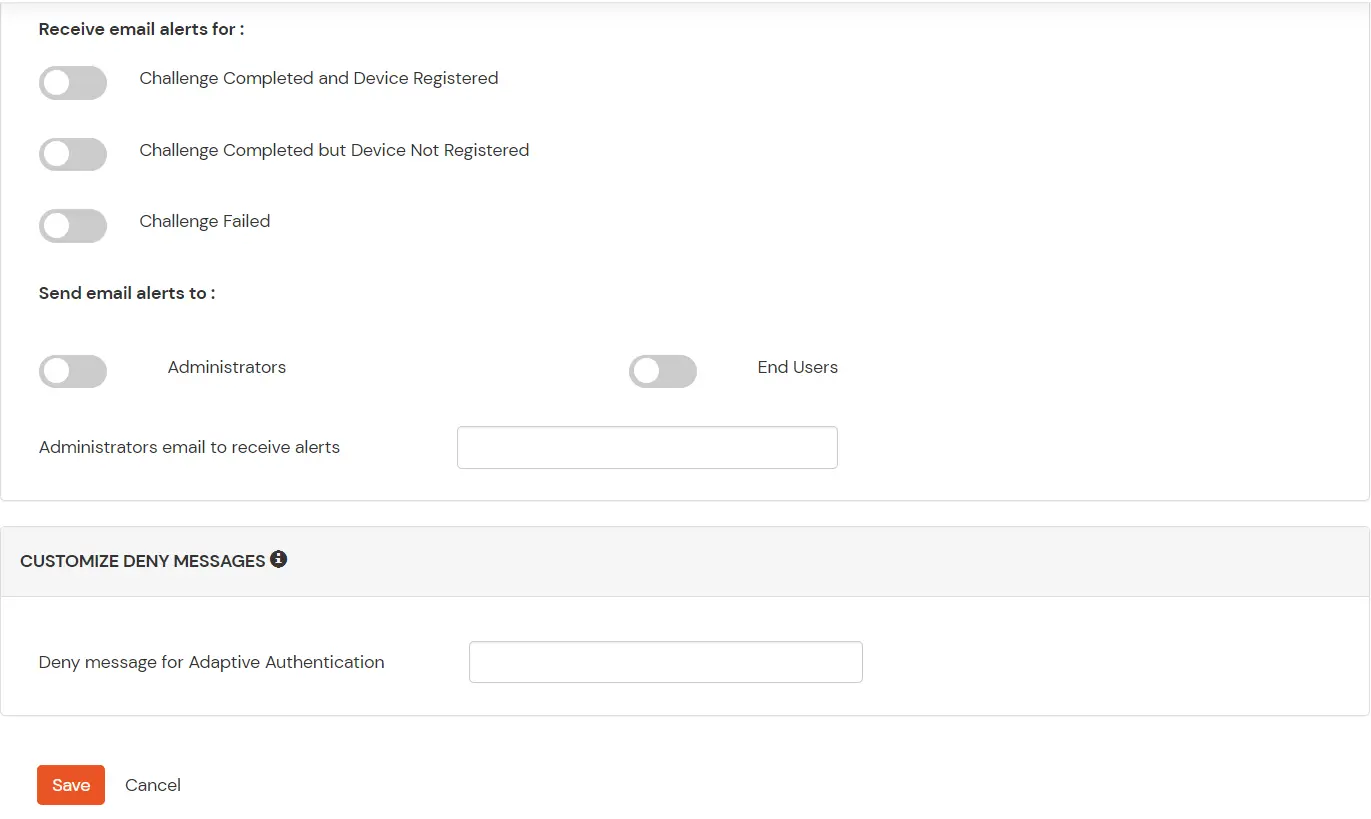
D. Notification and Alert Message.
This section handles the notifications and alerts related to Adaptive Authentication. It provides the following options :
| Option | Description |
|---|---|
| Users login from unknown IP addresses, devices or locations | Enabling this option allows you to login from unknown IP addresses or devices and even locations. |
| Number of Device registrations exceeded allowed count | This option will allow you to register more devices than the devices you have numbered. |
| Challenge Completed and Device Registered | Enabling this option allows you to send an email alert when an end-user completes a challenge and registers a device. |
| Challenge Completed but Device Not Registered | Enabling this option allows you to send an email alert when an end-user completes a challenge but do not registers the device. |
| Challenge Failed | Enabling this option allows you to send an email alert when an end-user fails to complete the challenge. |
Note: Oracle and Java are registered trademarks of Oracle and/or its affiliates. miniOrange is a separate entity.
