Overview
In modern workplaces, ensuring secure access to cloud applications is more challenging than ever. With employees using a mix of company-owned and personal devices nowadays, the risk of unauthorized access increases. Traditional security methods often fall short when it comes to managing these diverse devices and safeguarding sensitive data. Unauthorized logins from insecure devices can lead to data breaches, compromised credentials, and non-compliance with critical regulations.
To tackle these concerns, miniOrange’s IAM and MDM solution offers a centralized approach to control and monitor device access. By enforcing strict policies, only authorized devices, whether BYOD or company-owned, can access cloud applications, ensuring secure login and maintaining compliance with industry standards.
Problem Statement
An organization managing a hybrid workforce faced the following security challenges in ensuring secure access control and login to cloud applications:
- Uncontrolled Device Access: Employees were accessing critical cloud applications from both company-owned and personal devices, many of which were not enrolled in the security management system.
This created a significant risk, as the organization had no way to verify whether the devices used to access sensitive data were secure or compliant with company policies. Unauthorized or compromised devices could easily bypass security measures.
- Lack of Device Enrollment Enforcement: Employees were able to log in from devices that hadn’t been properly enrolled, leaving sensitive data vulnerable to unauthorized access.
Devices that were not part of the approved list could potentially bypass the required security configurations, increasing the risk of data leaks and non-compliance with industry regulations.
- Limited User Access Control: The organization lacked strong identity governance around who could access which cloud applications and under what conditions.
User authentication was not tightly integrated with device posture checks, and access decisions were not consistently tied to verified work identities. There was limited enforcement of strong authentication methods such as MFA, and no clear mapping between user identity, role, and the device being used. This increased the risk of credential misuse, unauthorized access, and excessive privileges across critical cloud applications.
Solution
To address these security challenges, miniOrange implemented a unified IAM and MDM solution with a focus on three core protection layers:
1. Device Access Control (Enrolled Device Verification)
Capabilities:
- Enforced Device Enrollment: Only devices enrolled in the MDM system are allowed to access cloud applications. Admins can specify that only devices with specific security profiles (e.g., encryption, up-to-date OS) are permitted to log in.
- Device Compliance Monitoring: Continuous monitoring ensures devices comply with security policies before they can access sensitive applications.
Benefits:
- Prevents unauthorized devices from accessing cloud applications, mitigating risks from unsecured or non-compliant devices.
- Ensures full control over which devices are allowed access, maintaining organizational security standards.
2. Centralized Authentication and Access Control (IAM Integration)
Capabilities:
- User Authentication: Ensures only authorized users, through their work IDs, can log in to cloud applications. Multi-factor authentication (MFA) is enforced for added security.
- Device Authentication: The system verifies that users are logging in only from registered devices, blocking access from any unapproved or unregistered device.
Benefits:
- Protects against unauthorized logins by verifying both user identity and device authenticity.
- Ensures that users can only access critical applications from secure, enrolled devices, keeping sensitive data protected.
3. Comprehensive Device and Activity Monitoring (MDM Integration)
Capabilities:
- Real-Time Device Monitoring: Tracks all enrolled devices in real time, ensuring they meet compliance standards (e.g., encryption, up-to-date software).
- Access Logs and Alerts: Provides detailed logs of device access to cloud applications, with immediate alerts for any suspicious or unauthorized login attempts.
Benefits:
- Protects against unauthorized logins by verifying both user identity and device authenticity.Provides visibility into which devices are accessing cloud applications, enabling a quick response to any unauthorized activity.
- Helps maintain compliance with regulatory standards by ensuring that only secure, authorized devices are used for accessing sensitive data.
Implementation Details
1. Policy Configuration
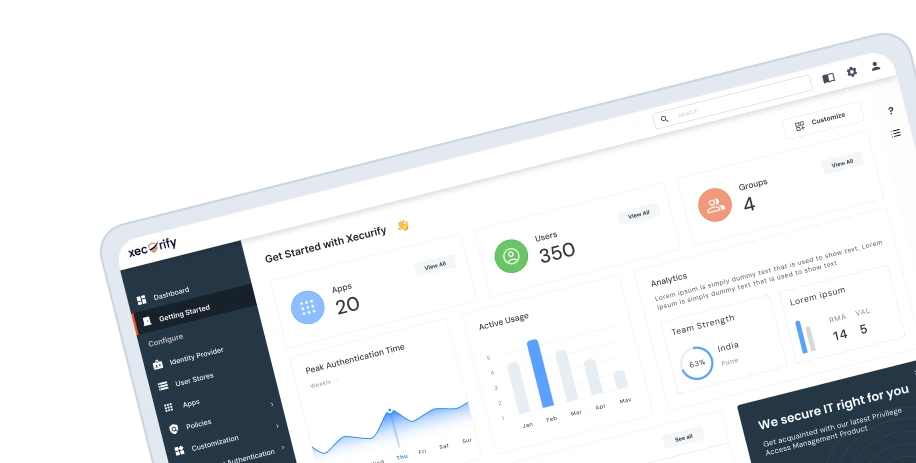
On the IAM and MDM dashboard, administrators can define specific access policies for different device groups.
- Policies can be customized for company-owned devices and BYOD devices to ensure that only compliant devices are granted access.
- Admins can set up rules that enforce device enrollment and compliance checks before granting cloud application access.
- Notifications are configured for policy violations, such as unauthorized device logins or failed compliance checks.
2. Endpoint Enrollment & Device Management
A lightweight agent is deployed on all enrolled devices (both company-owned and BYOD).
- The agent silently monitors and enforces device policies, ensuring that each device meets the security standards required to access cloud applications.
- Even when devices are offline, the agent continues to enforce key security policies, such as restricting access to sensitive data or applications from non-compliant devices.
3. Centralized Reporting & Alerts
Admins have access to real-time reporting and alerting features.
- Immediate alerts are sent for unauthorized login attempts, policy violations, or when a device is detected trying to access cloud applications without proper enrollment.
- Detailed reports allow admins to monitor access patterns across different device groups, ensuring compliance with security policies and regulations.
Key Outcomes & Benefits
1. Regulatory Compliance
Ensures compliance with industry standards such as GDPR, HIPAA, and other data protection regulations by enforcing strict device and access controls.
2. Complete Visibility and Control
Admins gain full visibility over which devices are accessing cloud applications and ensure that only authorized, compliant devices are granted access. Real-time activity tracking allows for quick identification of unauthorized access attempts.
3. Enhanced Security and Threat Prevention
Proactively blocks unauthorized access from insecure devices, reducing the risk of data breaches. It educates users by notifying them if they attempt to access applications from non-compliant devices, thus minimizing the likelihood of security incidents.
Enable Secure Cloud Access with IAM + MDM
Allow cloud access only from authorized users and compliant devices.
Start Free Trial
Book a Demo
Conclusion
By implementing miniOrange’s IAM and MDM solution, organizations can ensure that only authorized devices, whether company-owned or BYOD, are granted access to sensitive cloud applications. The solution provides comprehensive control over device access, enabling organizations to enforce strict security policies, track user activity, and maintain compliance with industry regulations.
With robust device enrollment, continuous compliance monitoring, and real-time reporting, businesses can safeguard their data from unauthorized access and prevent potential security breaches. This solution ensures that sensitive information remains protected while offering full visibility and control over how devices interact with cloud resources.