Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
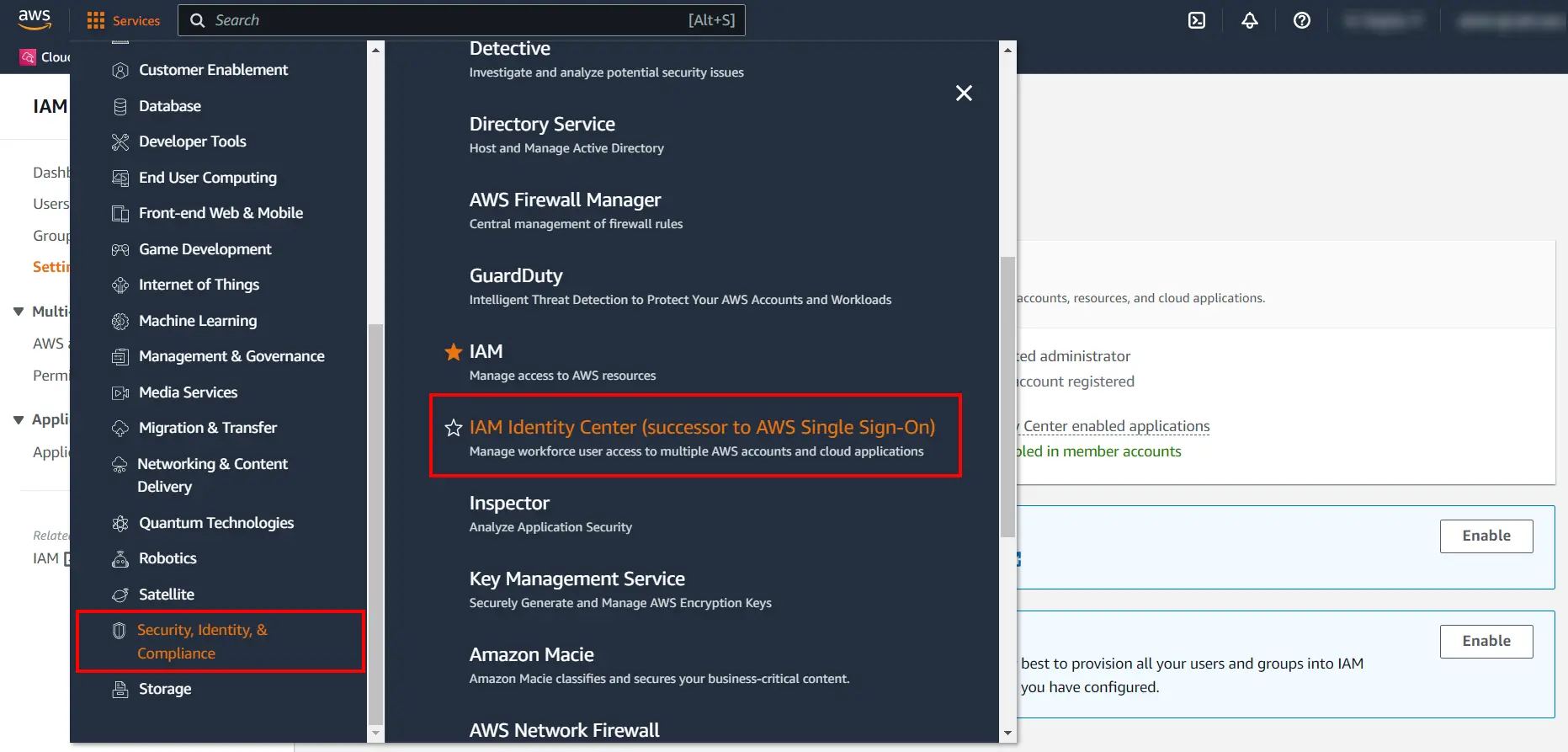
×Amazon Web Service (AWS) Single Sign-on (SSO) service is a cloud based Single Sign-On (SSO) solution which provides a simplified and secure access for users/groups to Amazon web services and full access to multiple cloud Applications along with AWS management console with one set of login credentials. Specifically, it helps you manage SSO access and user permissions across all your AWS accounts as well as custom applications that support Security Assertion Markup Language (SAML) 2.0.
miniOrange provides secure access to AWS SSO via the miniOrange Identity Provider (IDP) wherein users and groups can be authenticated, thus providing seamless access to your AWS resources.
With miniOrange AWS SSO, you can:
miniOrange offers free help through a consultation call with our System Engineers to Install or Setup AWS SSO solution in your environment with 30-day free trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you in no time.
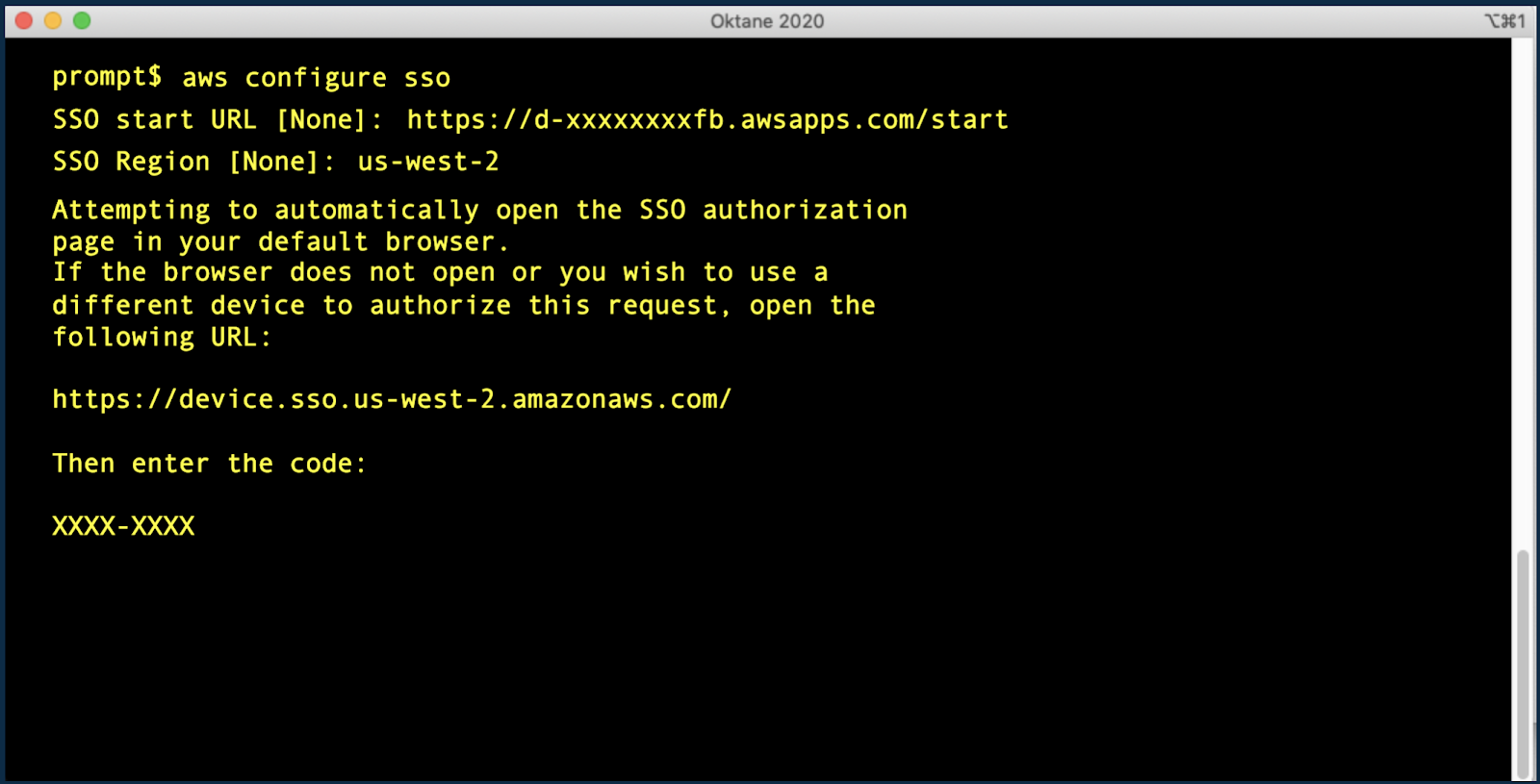
In this flow, a person tries to login to the Serivce Provider (AWS account) directly. The request is redirected to the Identity Provider for authentication. On sucessfull authentication from the Identity provider, the person is given access to the application (AWS account).
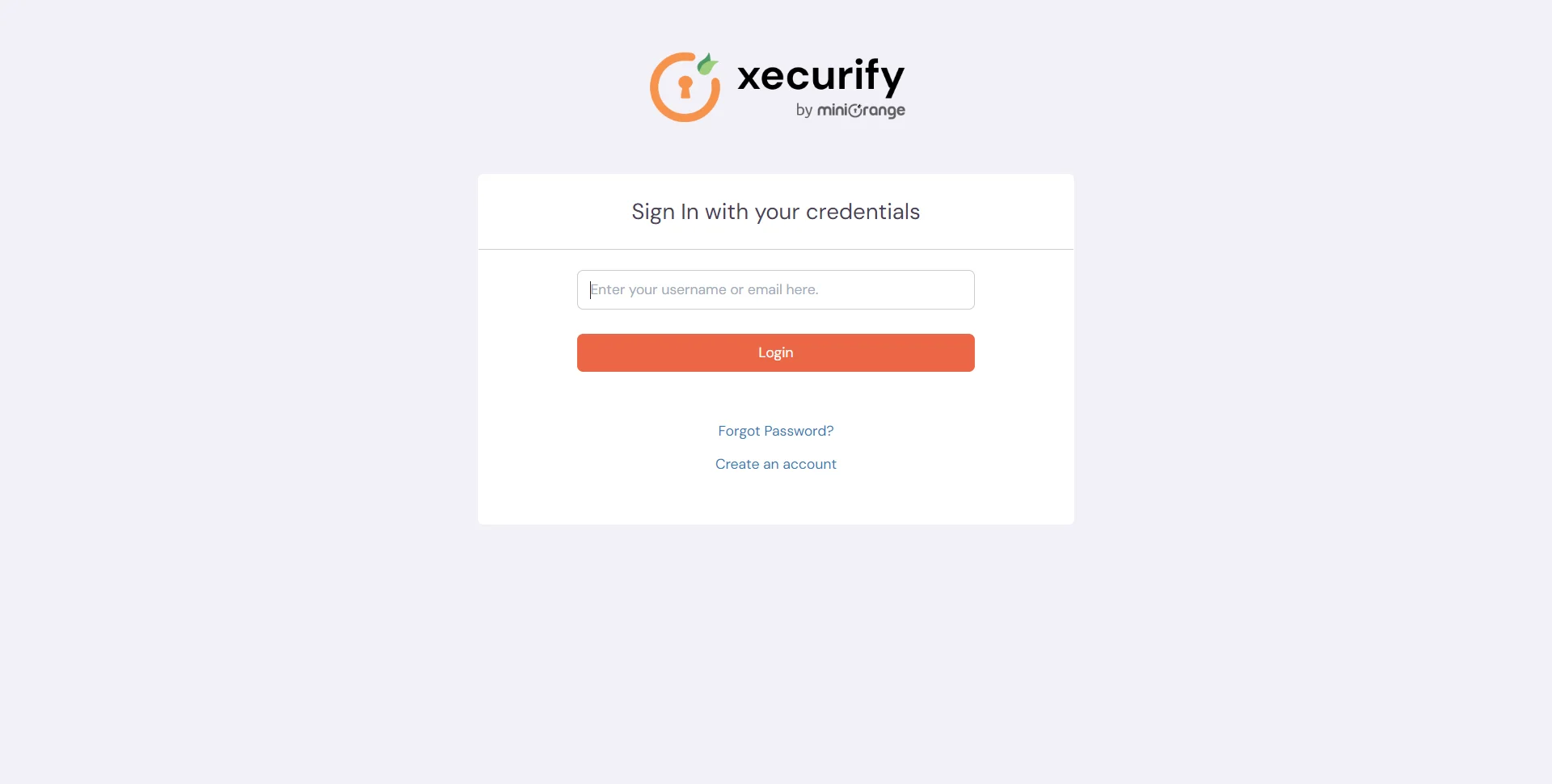
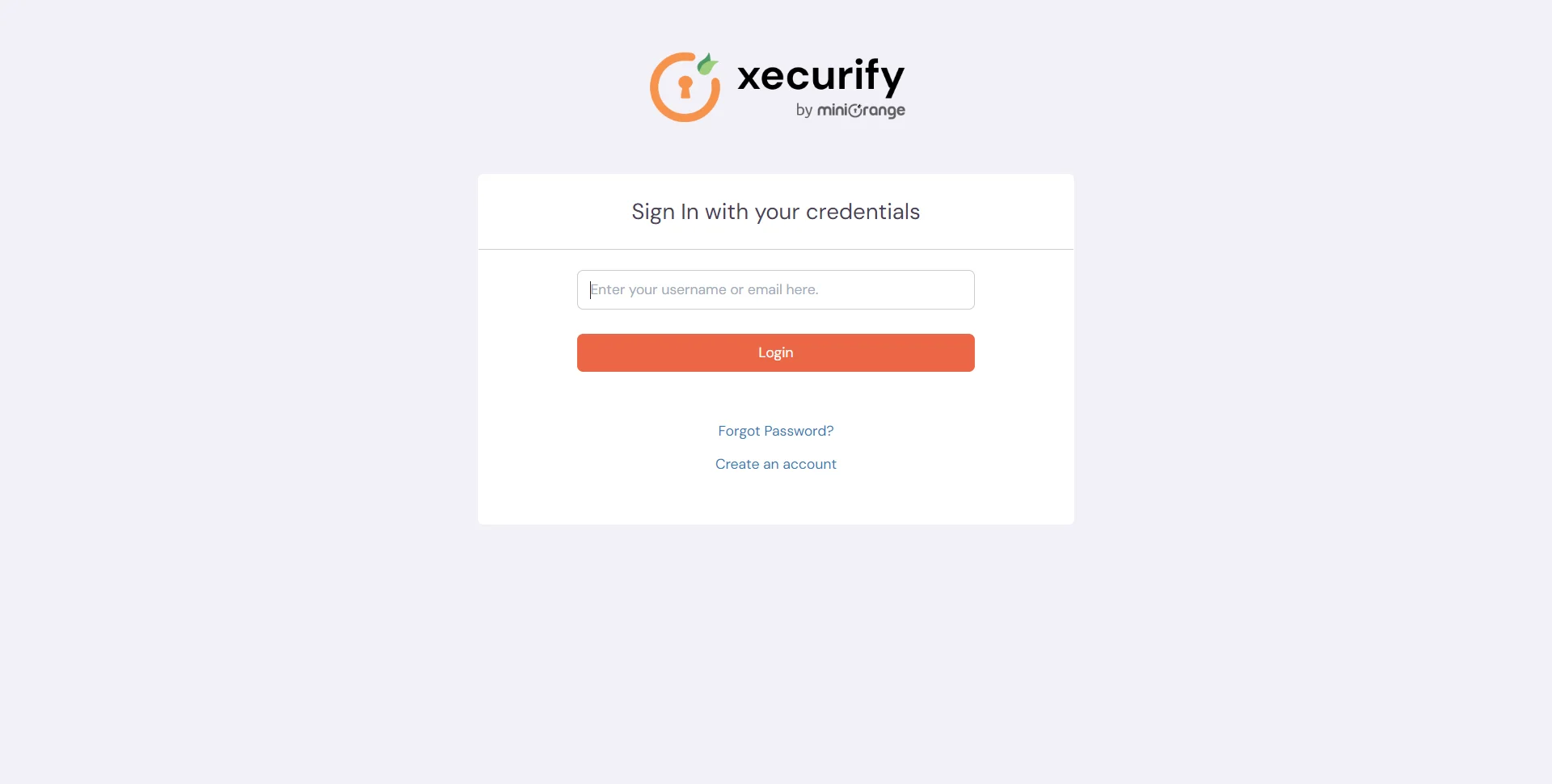
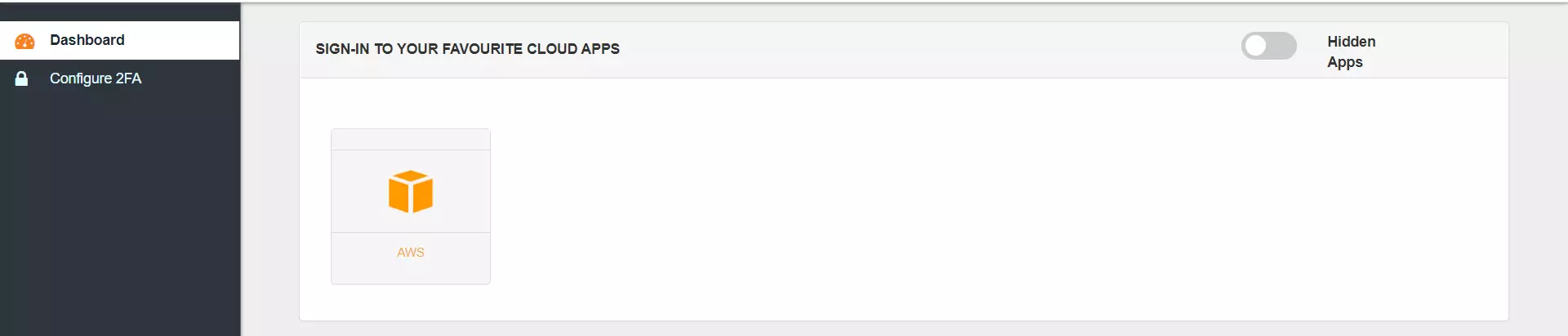
In this flow, a person logs in to the Identity Provider using his credentials. Now the person can access any of the configured Service Providers (AWS account, etc.) through the Identity Provider Dashboard without having to enter the credentials agian.
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
You will need the following pre requisites to setup SSO for AWS organization:
1. AWS organization admin account.
2. Set up AWS organization service.
3. Download the signed certificate from the AWS console or organization.
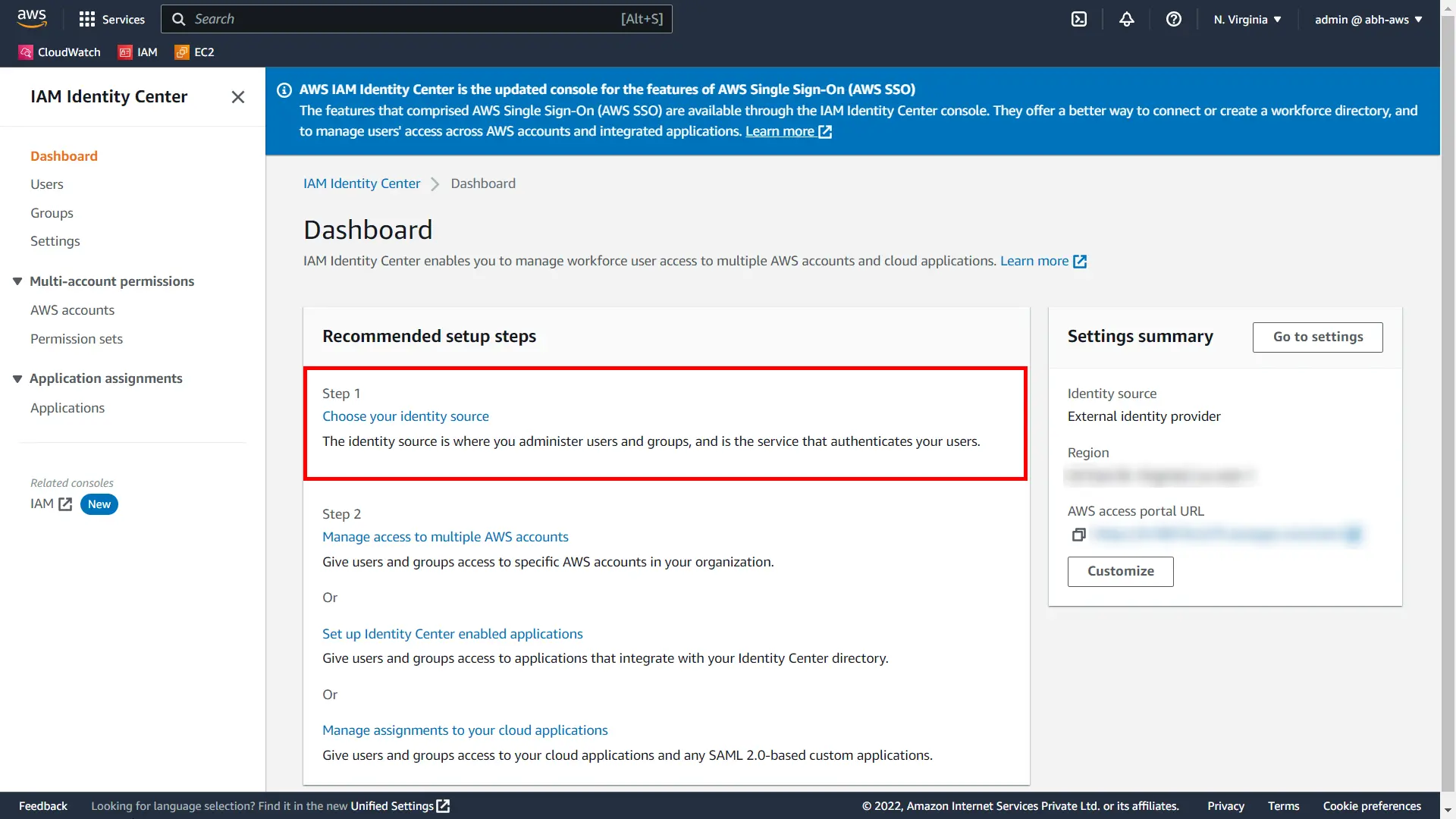
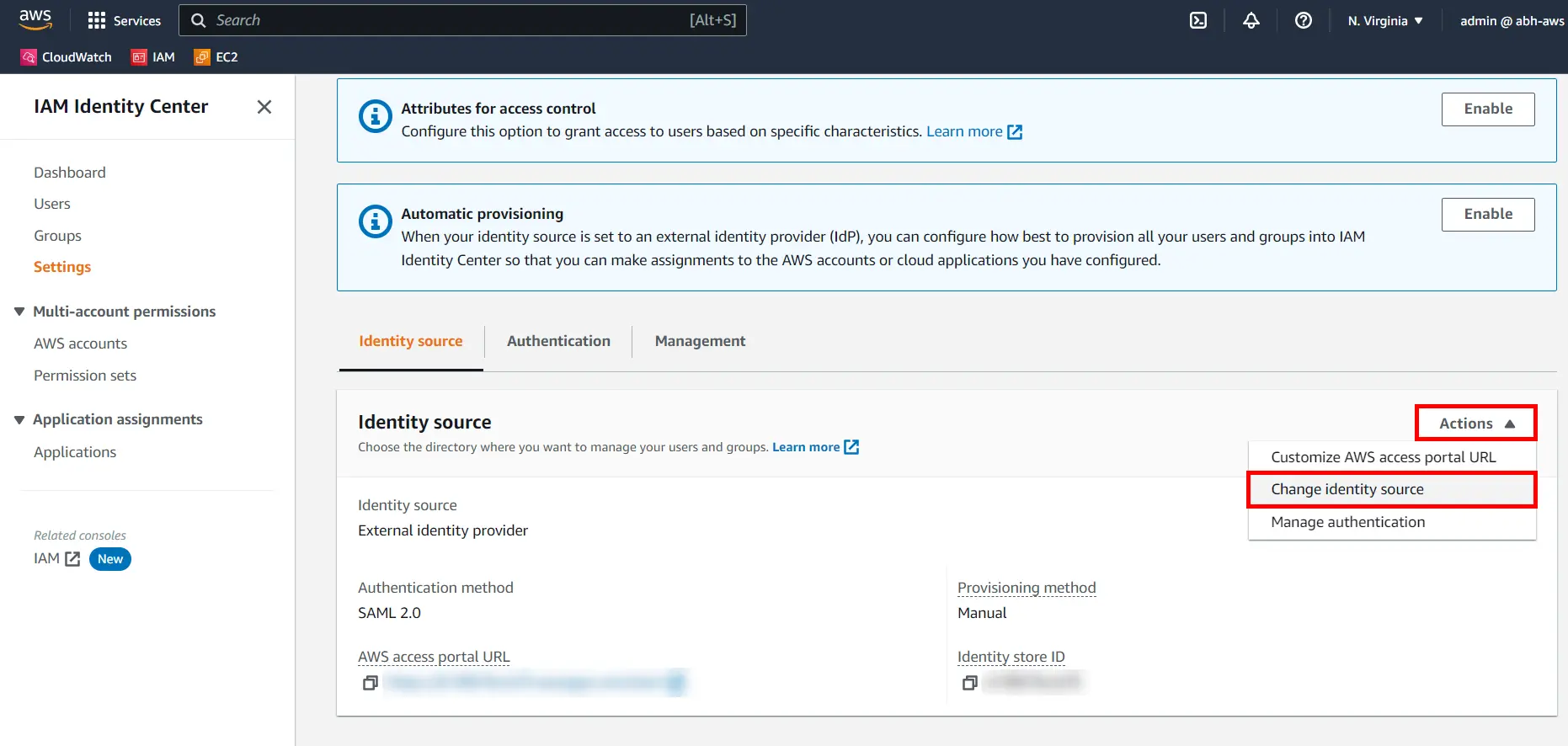
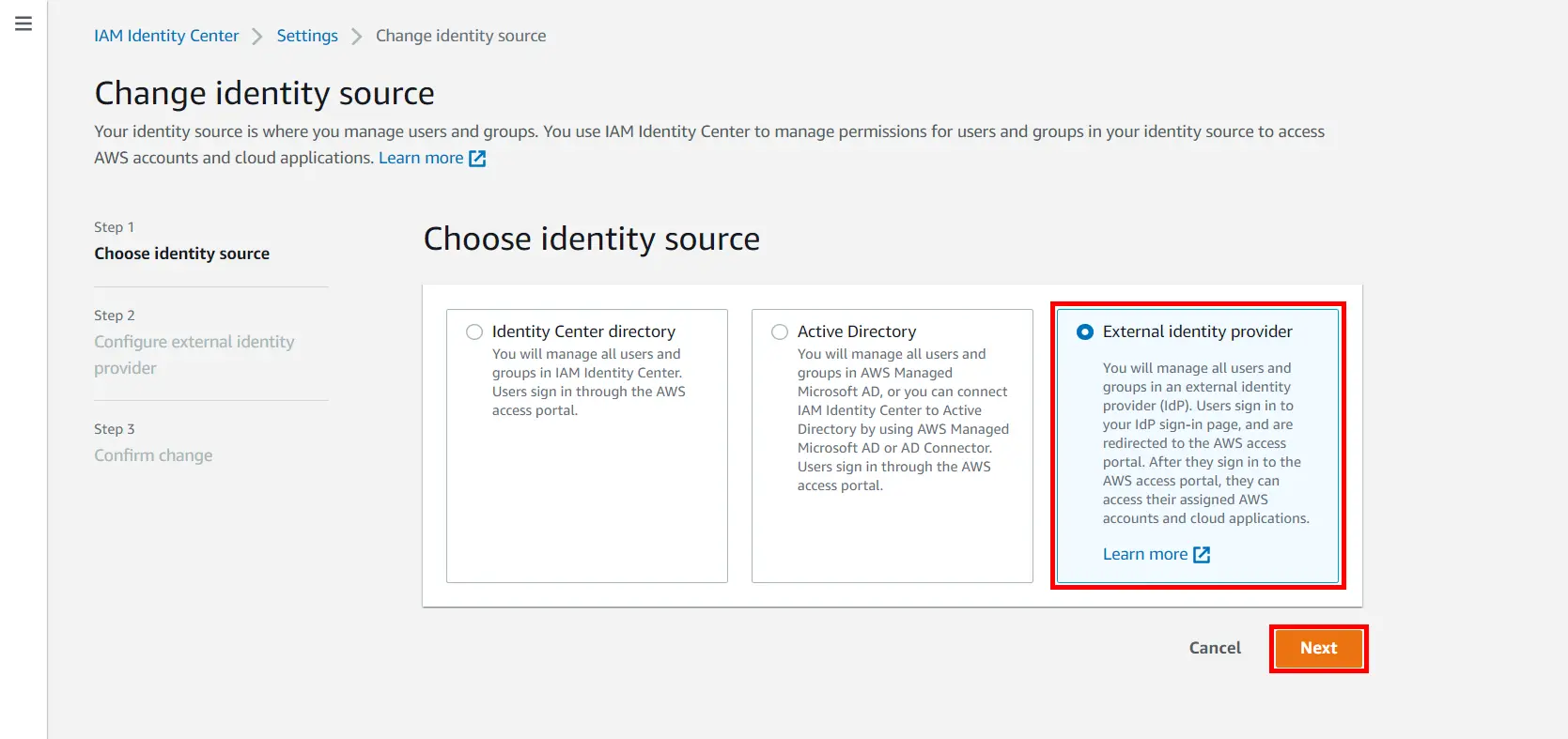
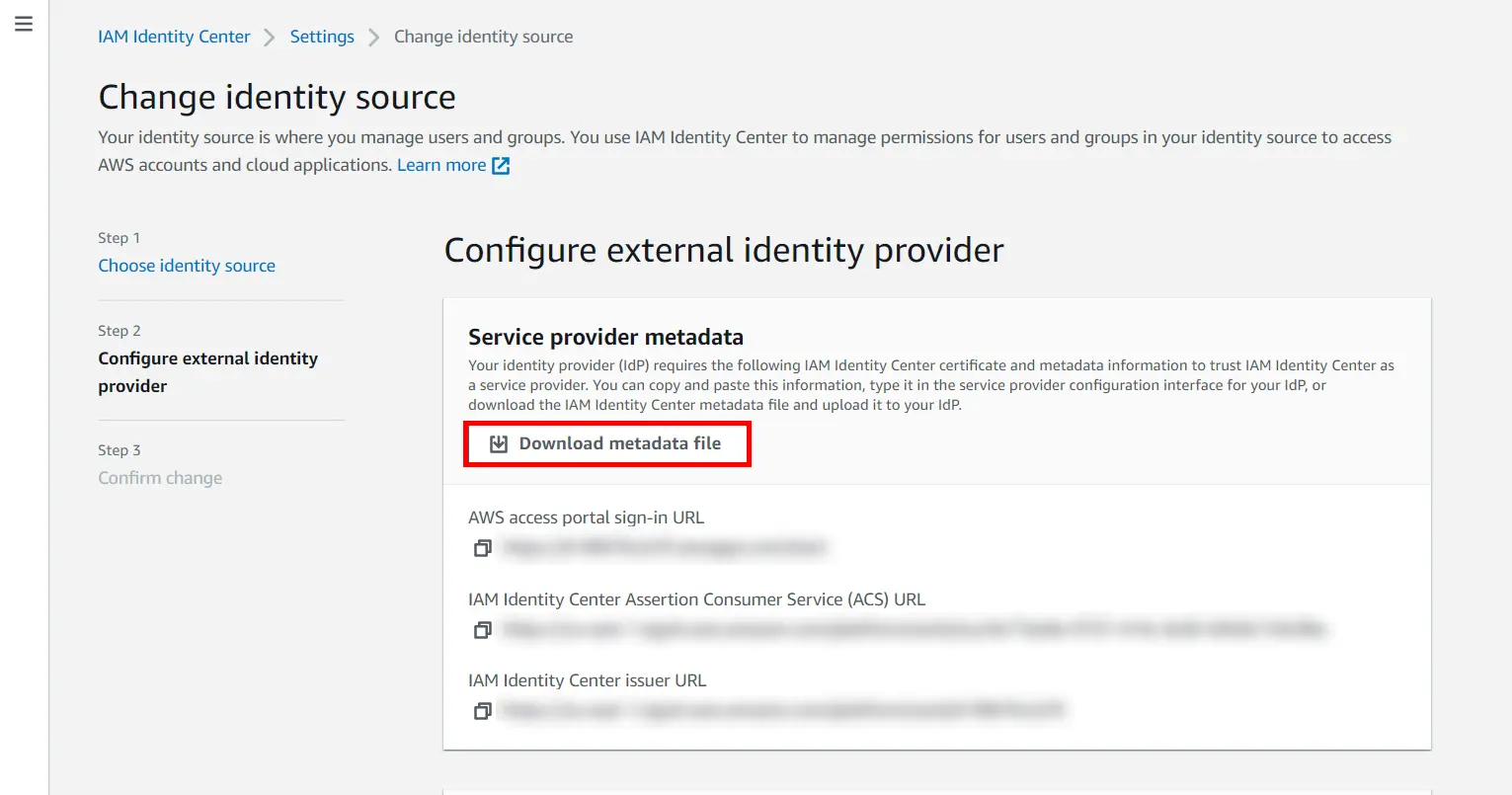

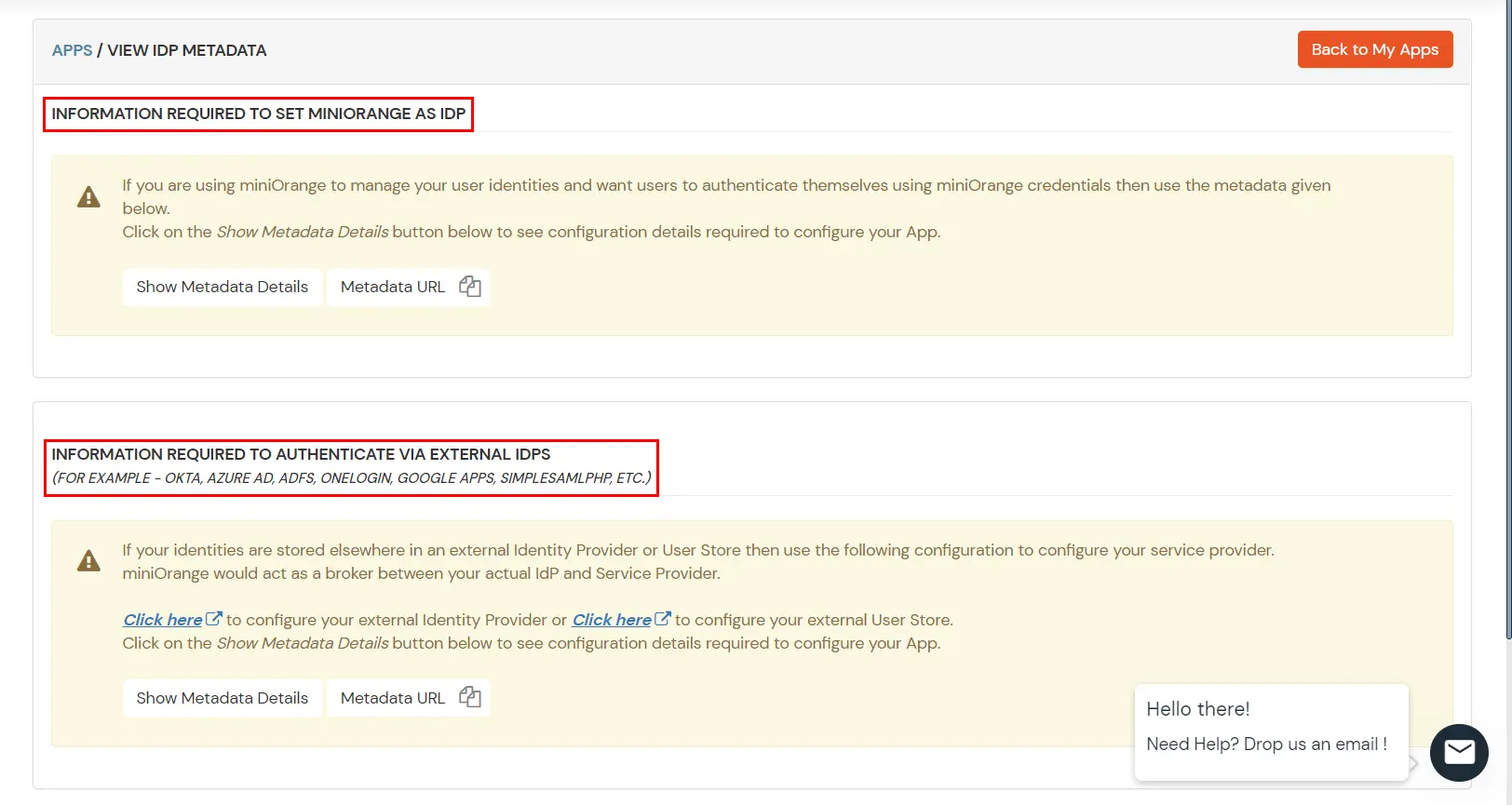
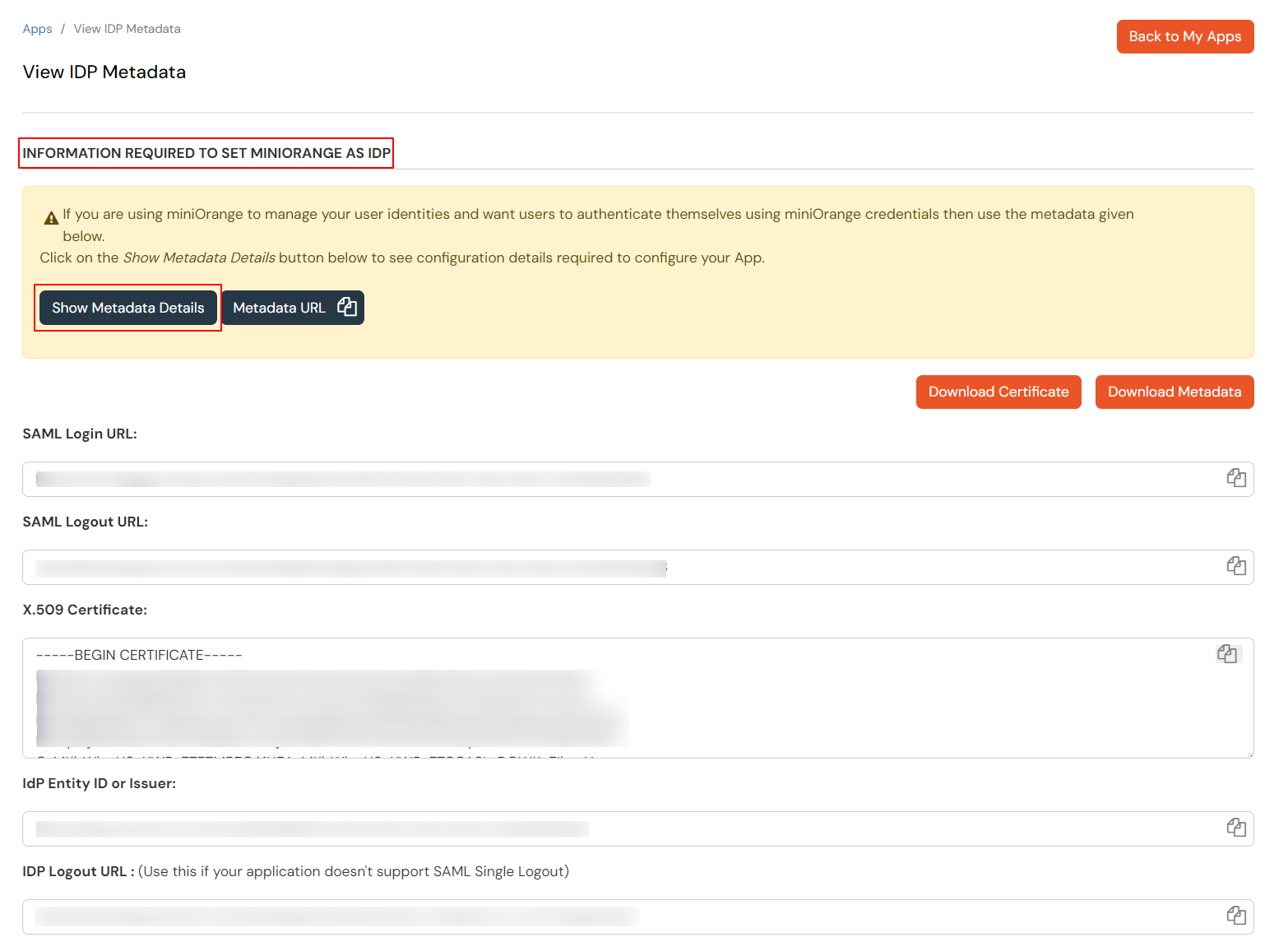
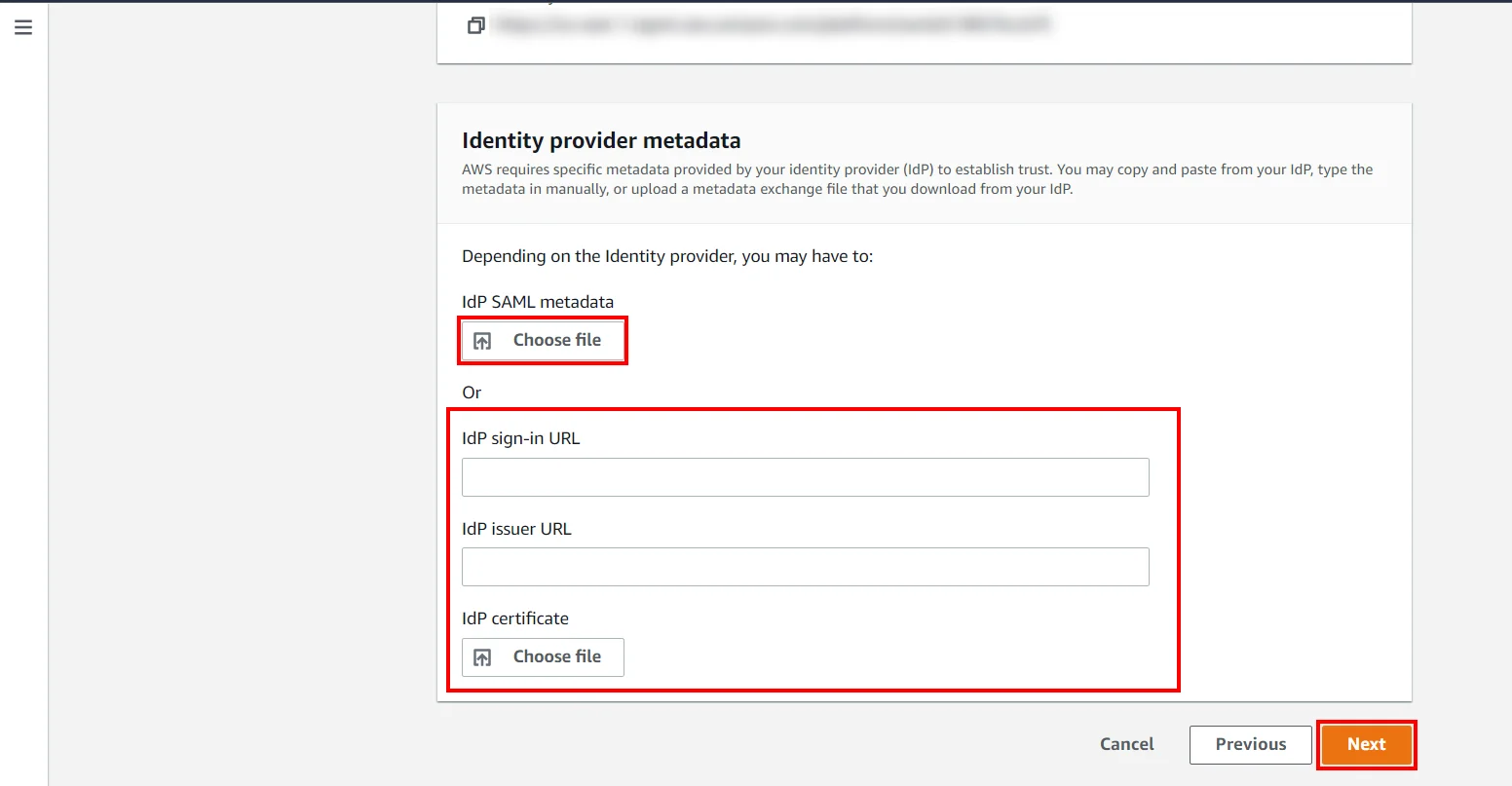
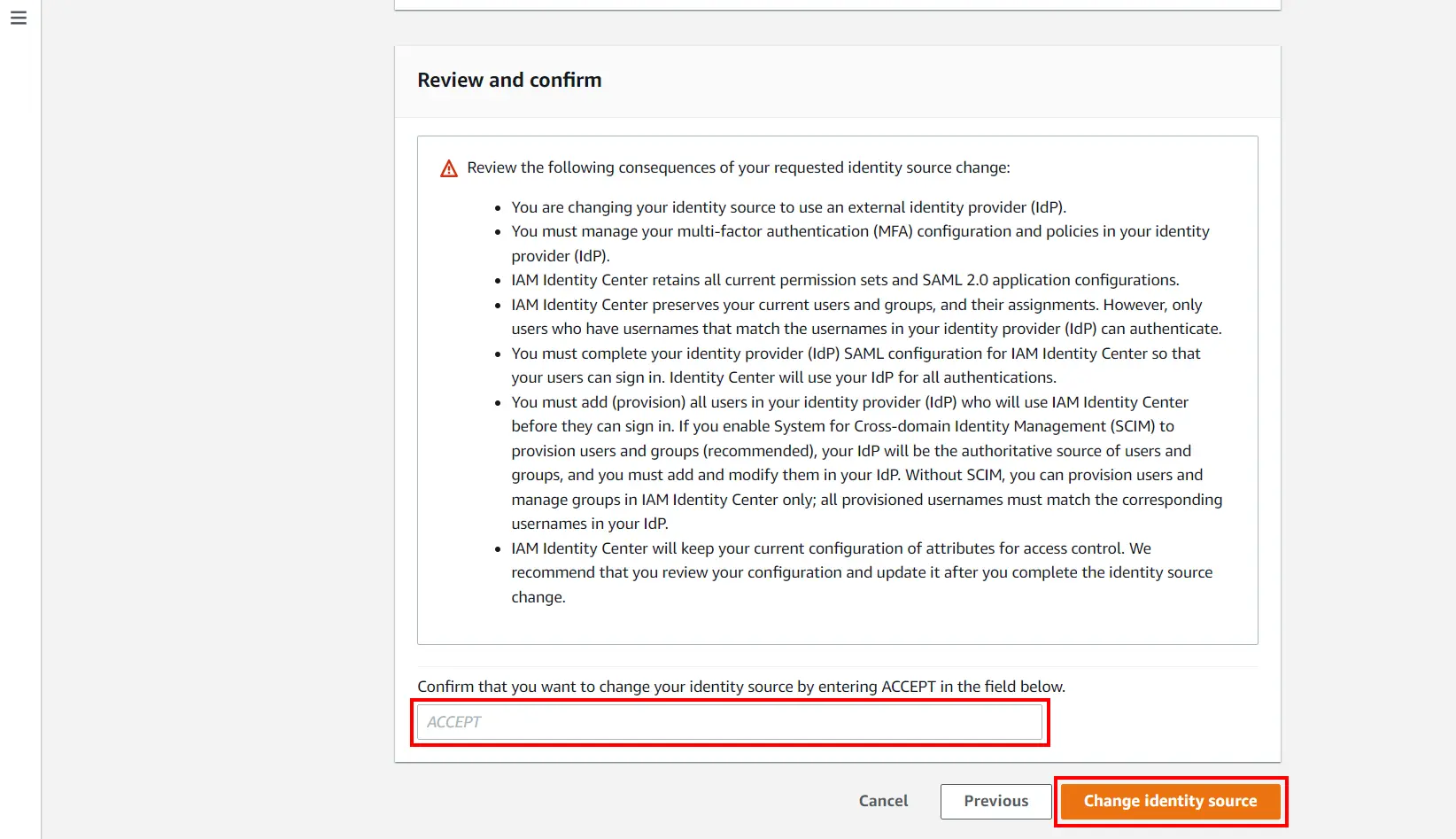
Get IdP Metadata Details to upload to AWS Console:
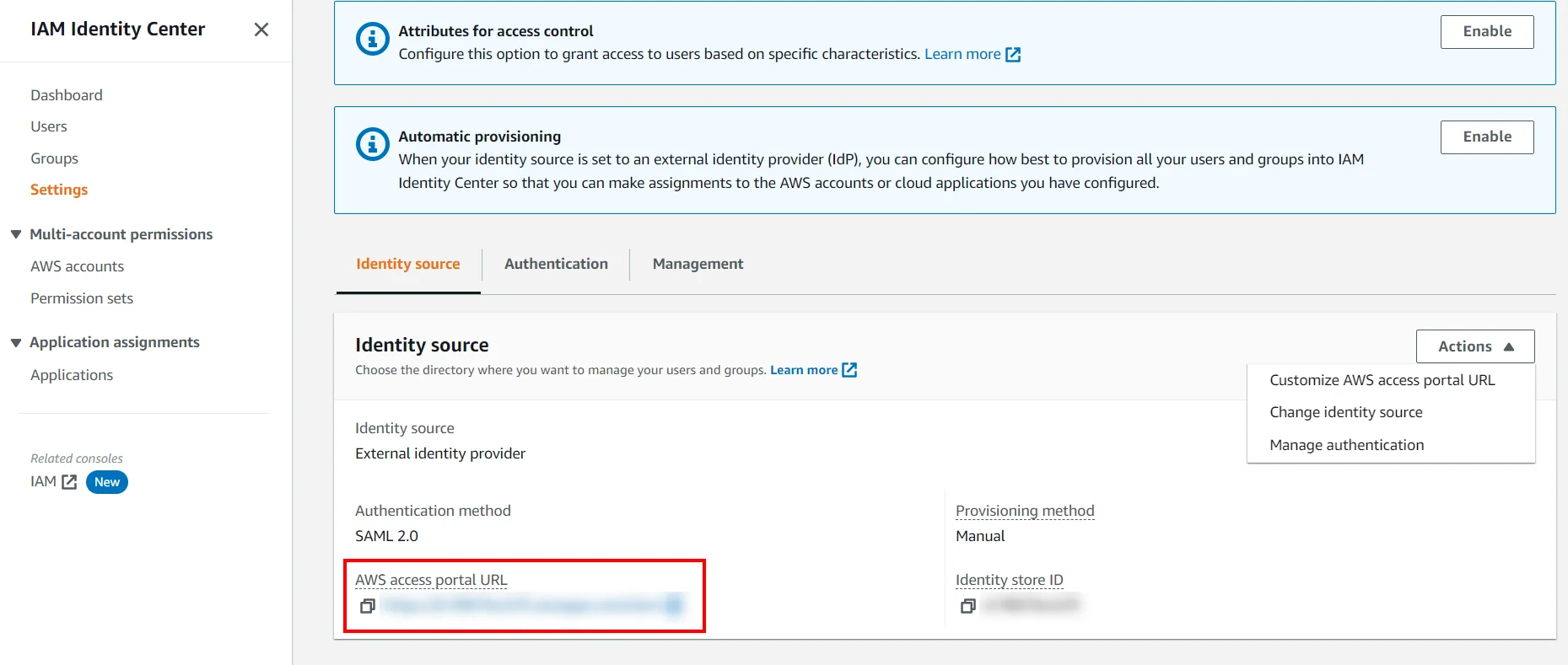
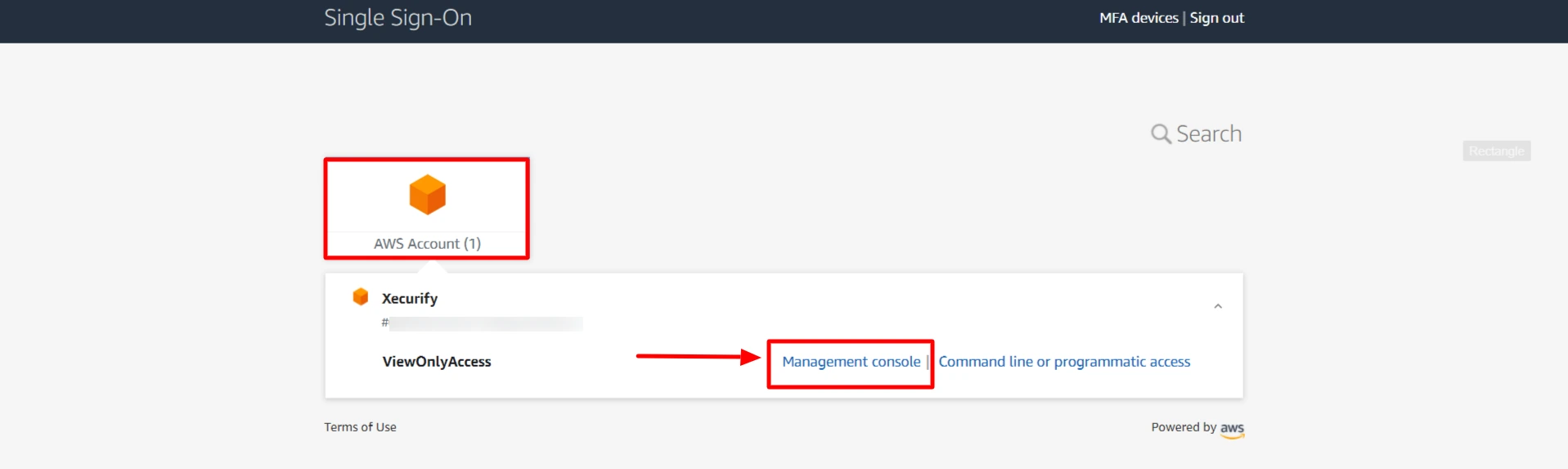
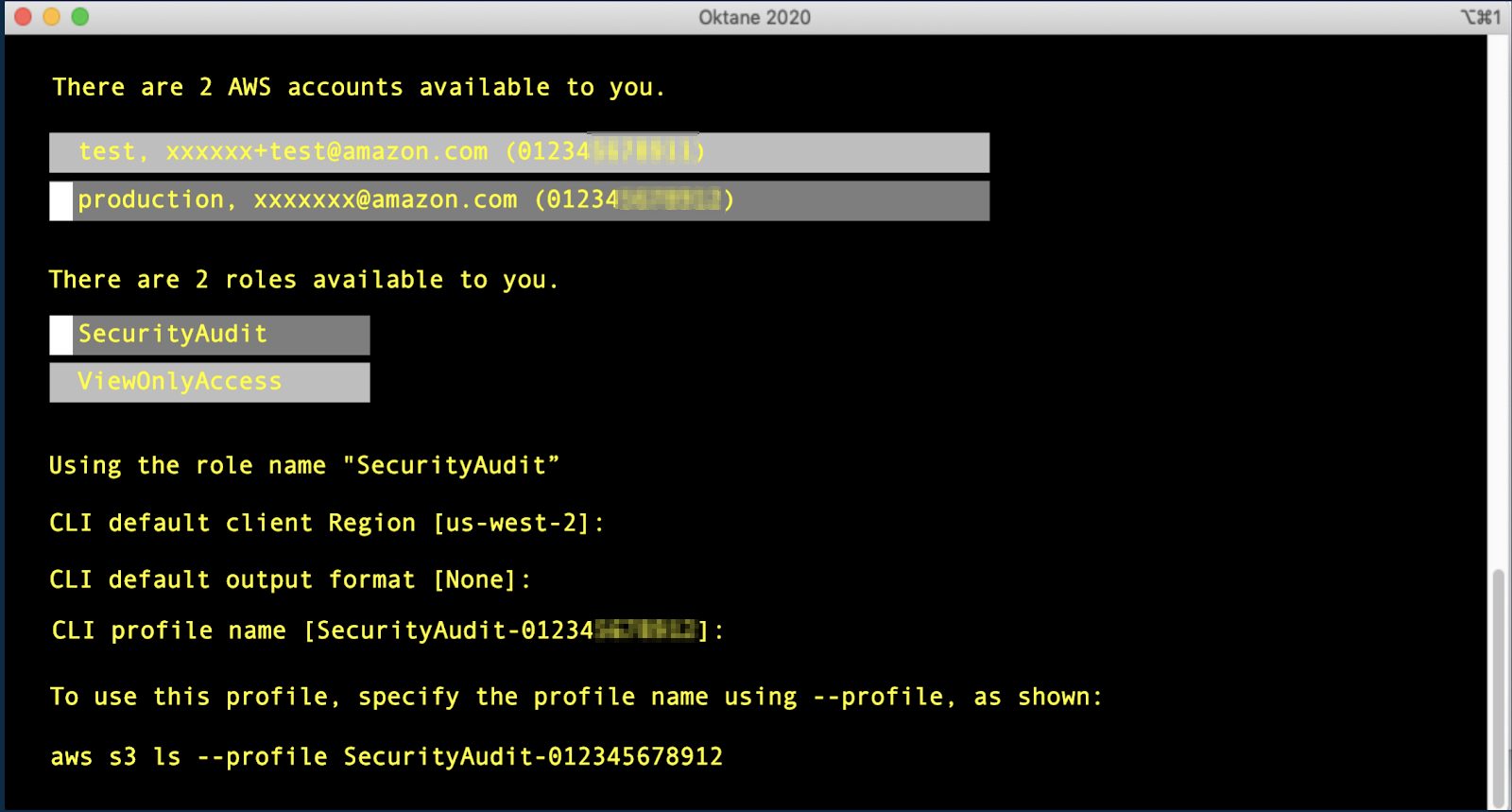
Test SSO login to your AWS account with miniOrange IdP:
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.
Test SSO login to your AWS account using with miniOrange IdP:
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.
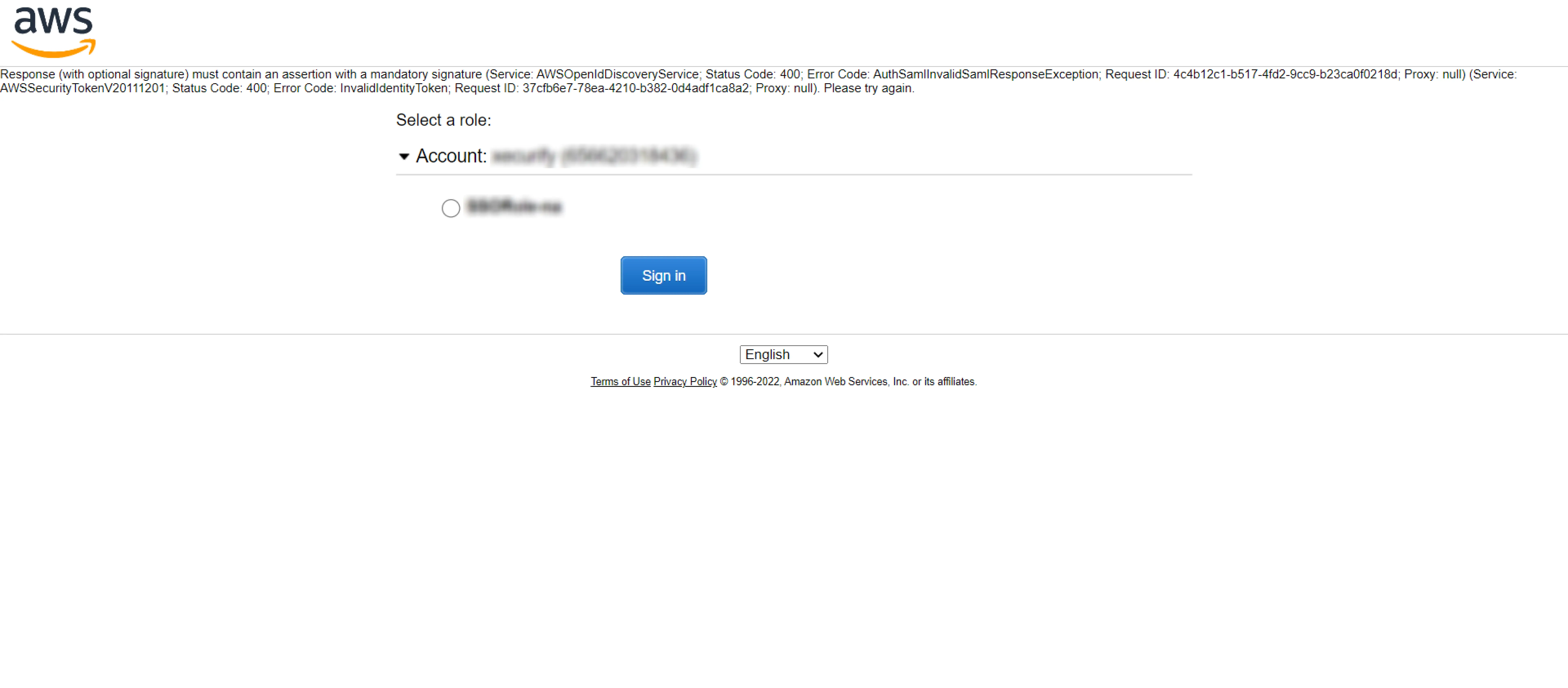
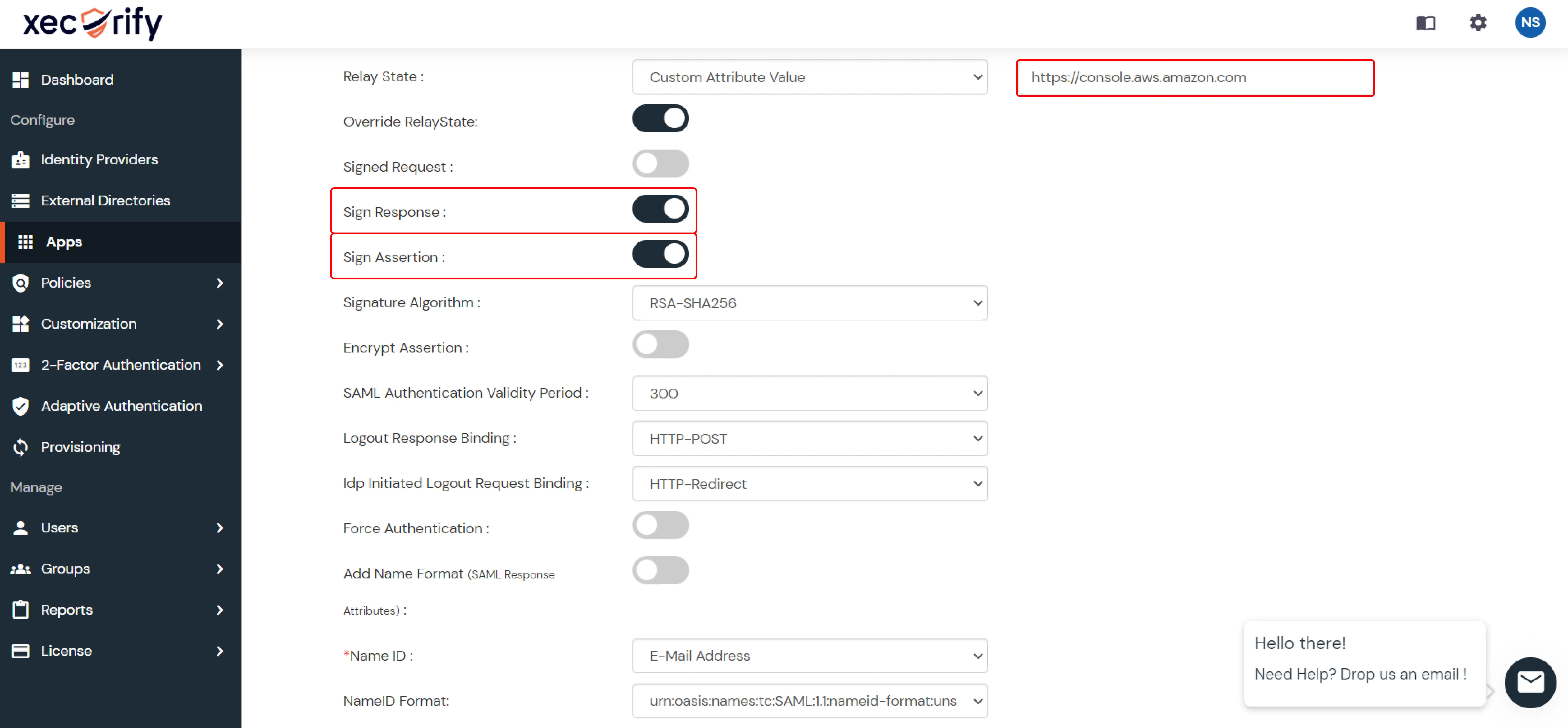
1. BAD REQUEST (Status Code: 400):
2. IDP Initiated
3. Troubleshoot other common errors HERE.
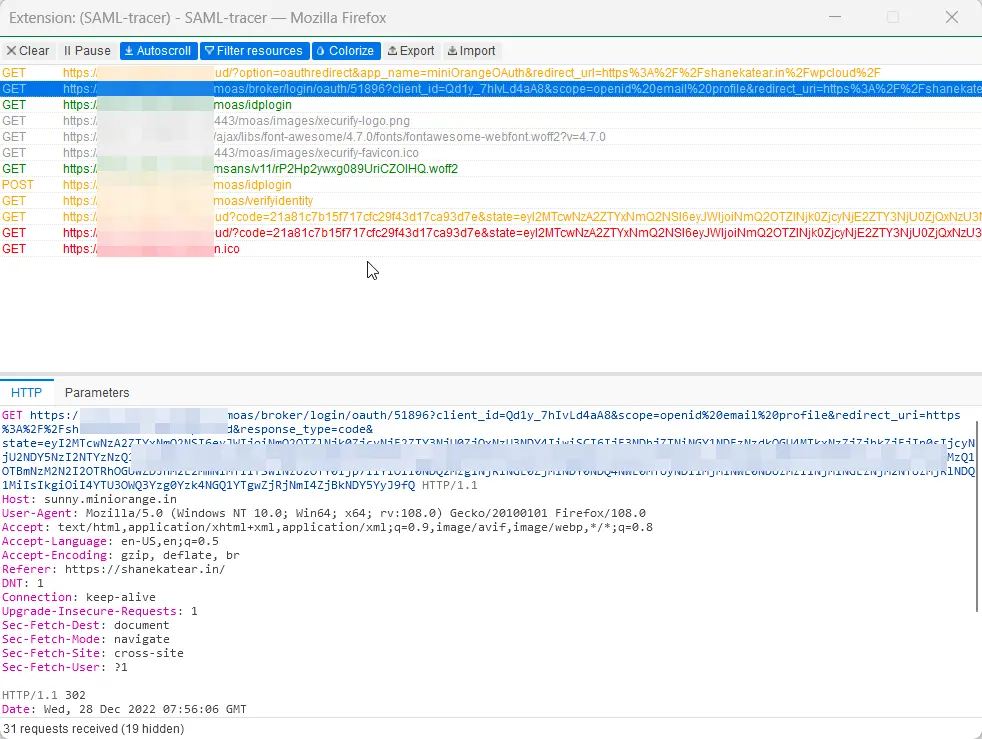
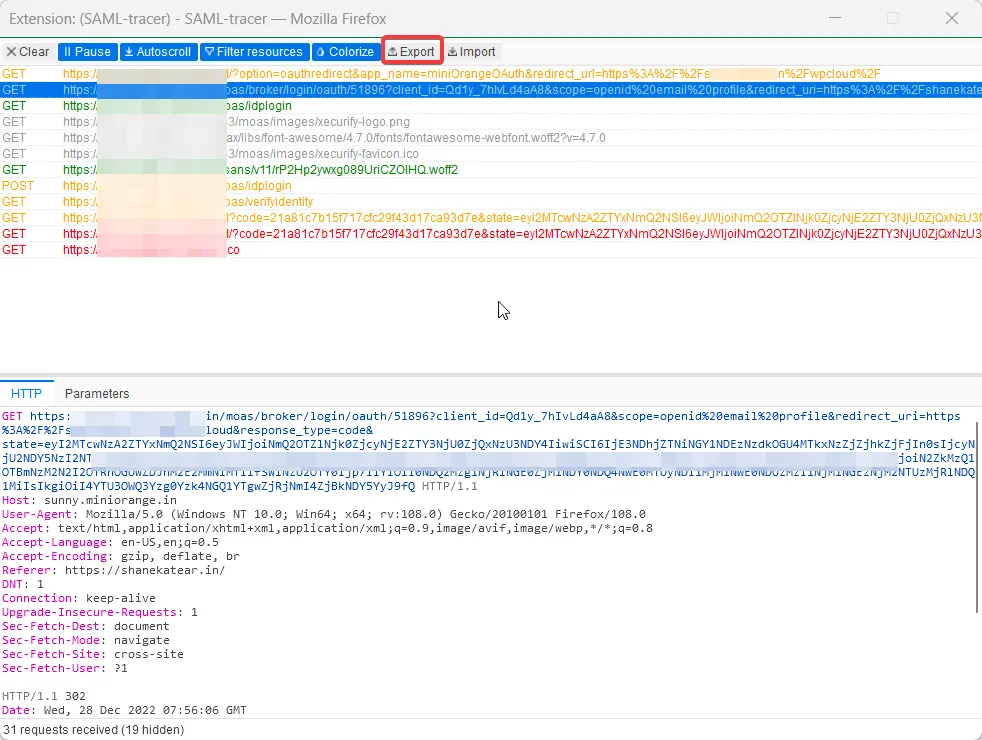
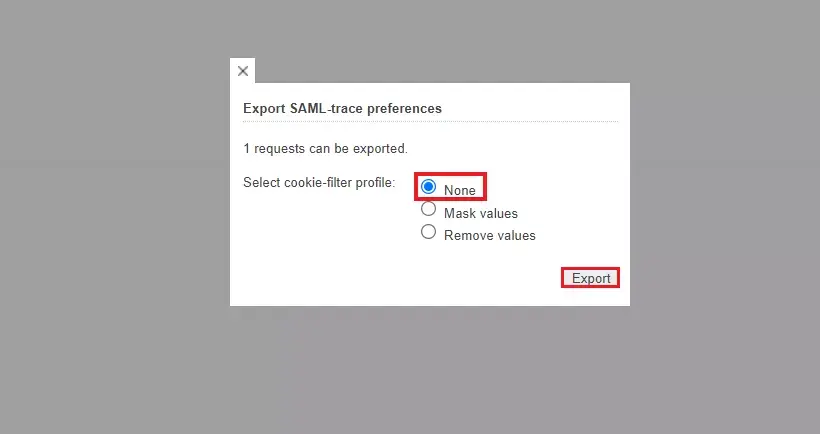
For Firefox: Add SAML tracer Add-On from the Firefox marketplace.
For Chrome / Edge or Chromium-based browsers: Install the SAML tracer extension from Chrome Webstore.