Brivo Single Sign-On (SSO)
Brivo takes access control fully into the cloud, with a state-of-the-art IP system that reduces nearly all hardware and manages your system from anywhere. Brivo's main access contribution is centred through its mobile platform, this interprets the setup and management of the system.
miniOrange provides a ready to use solution for Brivo. This solution ensures that you are ready to roll out secure access to Brivo to your employees within minutes.
For web applications that do not provide support for federated single sign-on, we have miniOrange Secure Single Sign-On browser plugins for SSO. Here, it is enabled on an application, where end users see an icon on their home pages and browsers, through this users can set and update their credentials. ( In the secure store for that application only).
miniOrange Supports all Browser Extension
- miniOrange Secure Single Sign-On Plugins for SSO support all popular web browsers like Chrome, Firefox, Safari, Internet Explorer and Microsoft Edge.
- Browser plugin a secure driven post to the application login page, signing in the user automatically on their behalf. - The plug-in does not store the credentials anywhere and they are discarded once the user has signed into the application.
- Users credentials are stored in an encrypted format by using AES encryption with the combination of a customer-specific private key. When a user clicks the application icon, miniOrange securely posts the username/password to the app login page over SSL and the user is automatically logged in.
Connect with External Source of Users
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
Get Free Installation Help - Book a Slot
miniOrange offers free help through a consultation call with our System Engineers to Install or Setup Brivo SSO solution in your environment with 30 days trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you setting it up in no time.
Get Help
Follow the Step-by-Step Guide given below for Brivo Portal Single Sign-On (SSO)
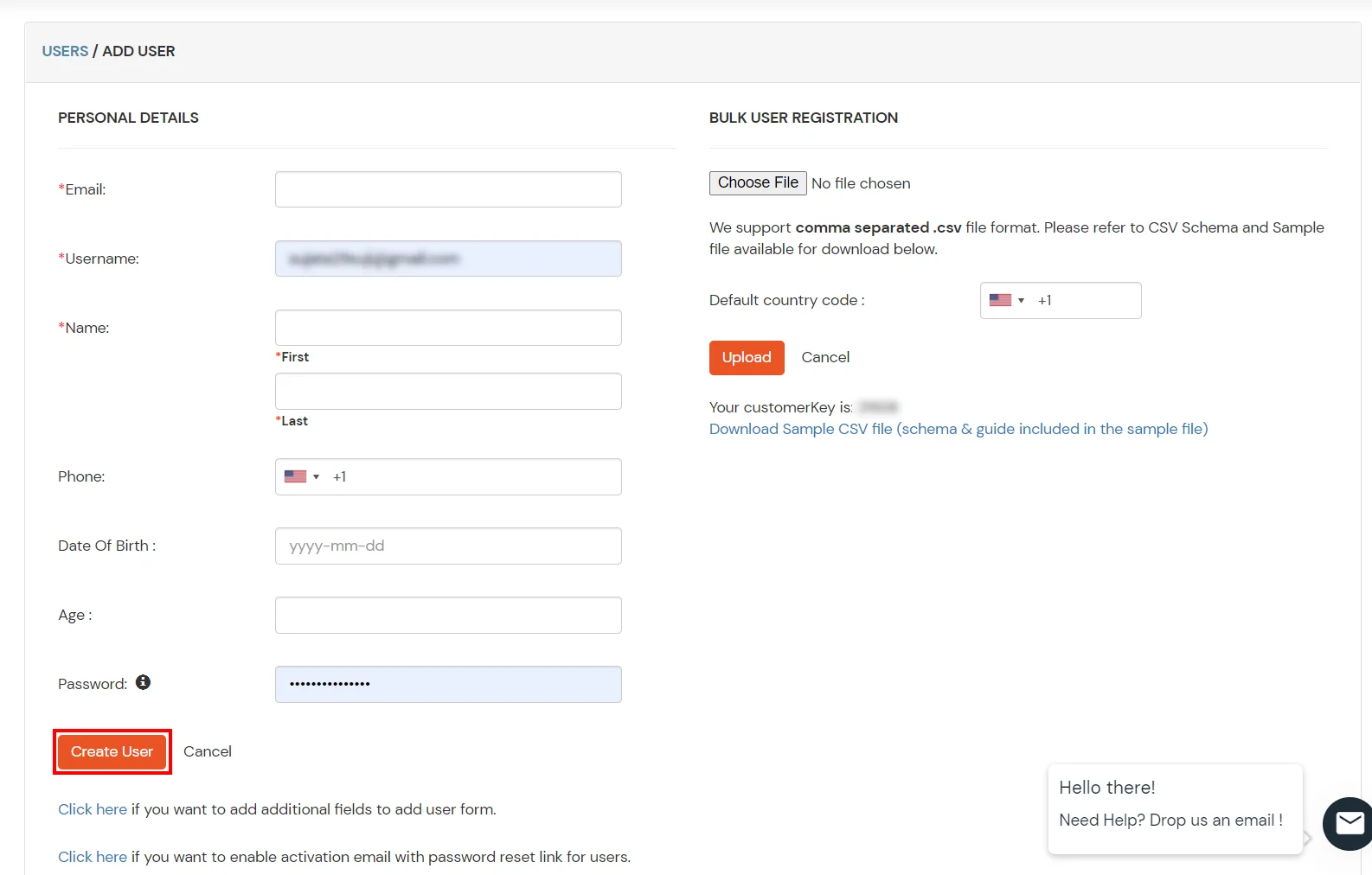
1. Configure Brivo in miniOrange
- Log into miniOrange Admin Console.
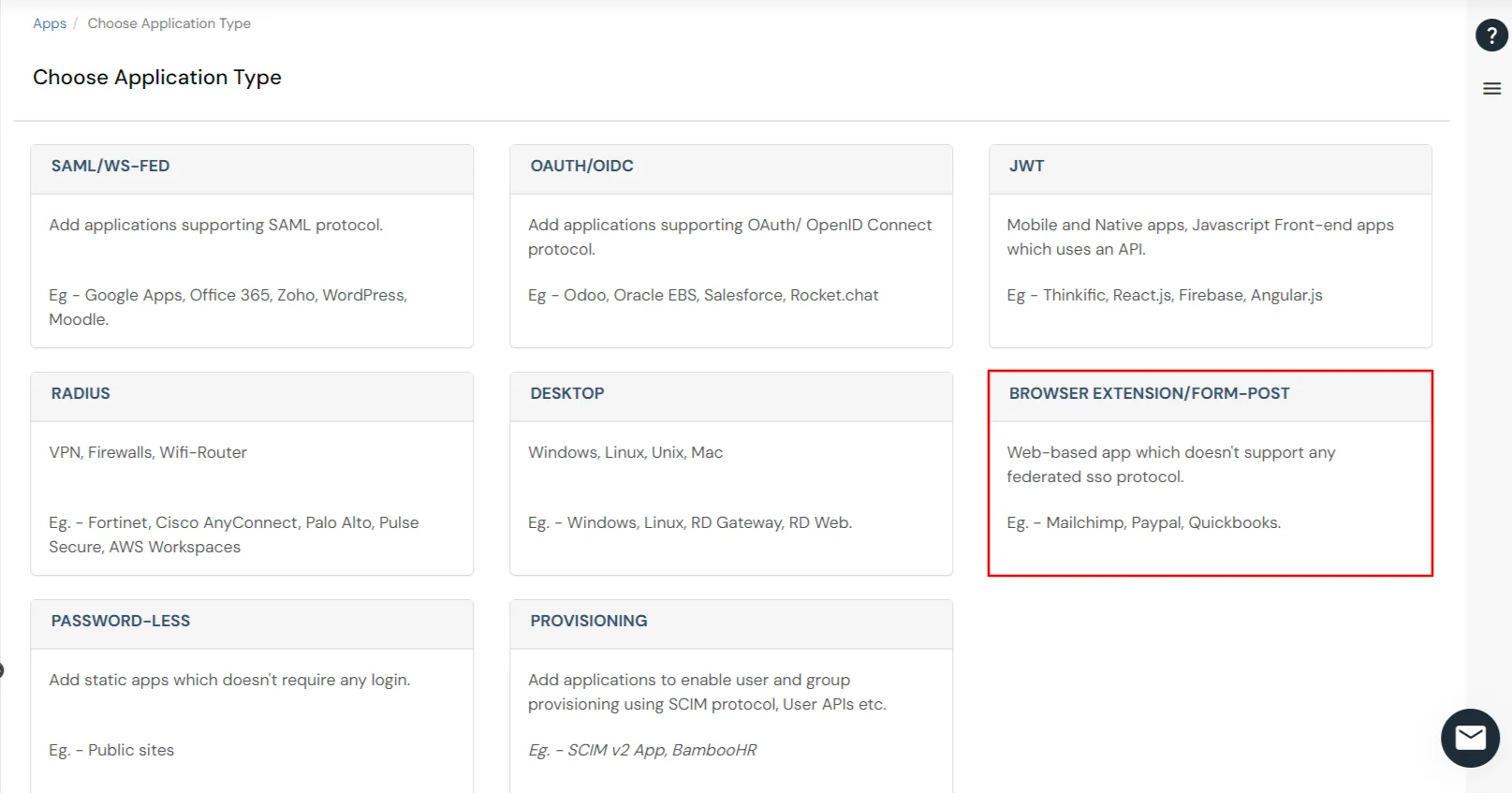
- Go to Apps >> click Add Application button.

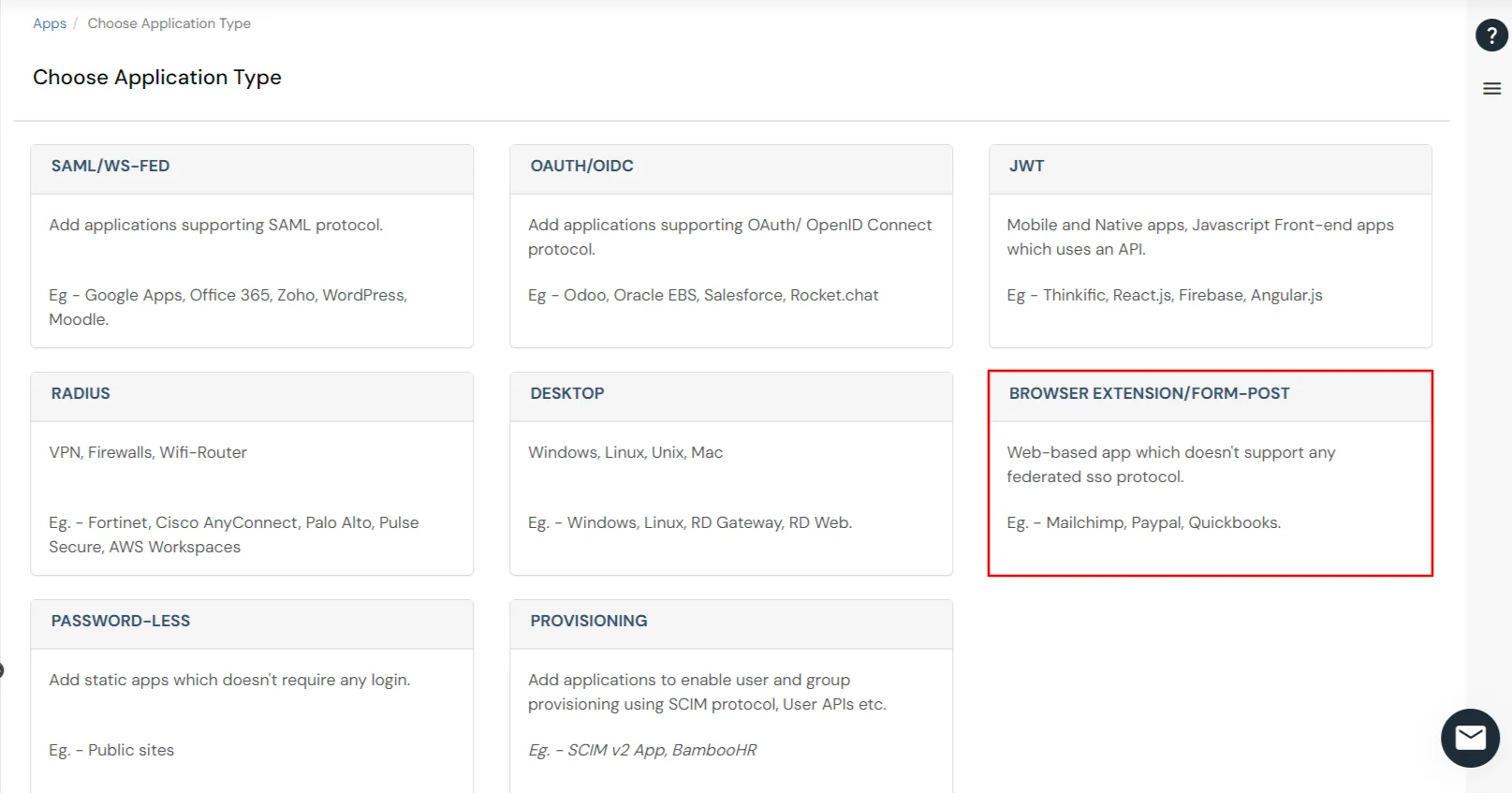
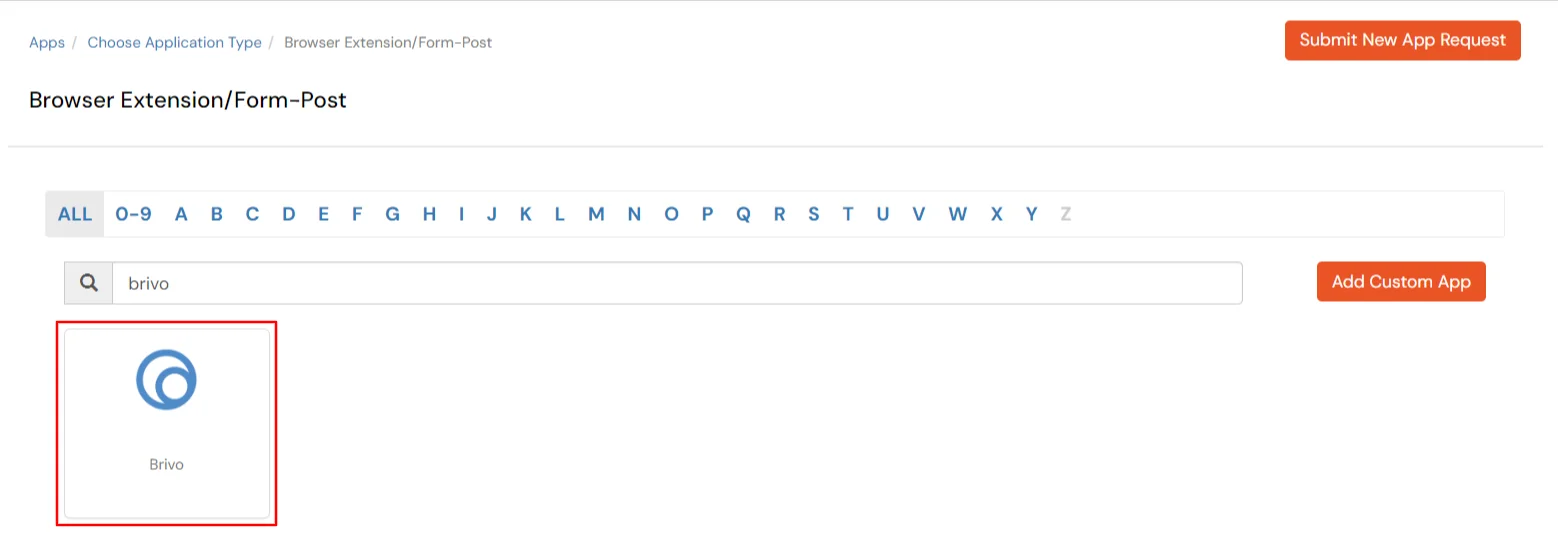
- In Choose Application Type click on BROWSER EXTENSION/FORM-POST as application type.
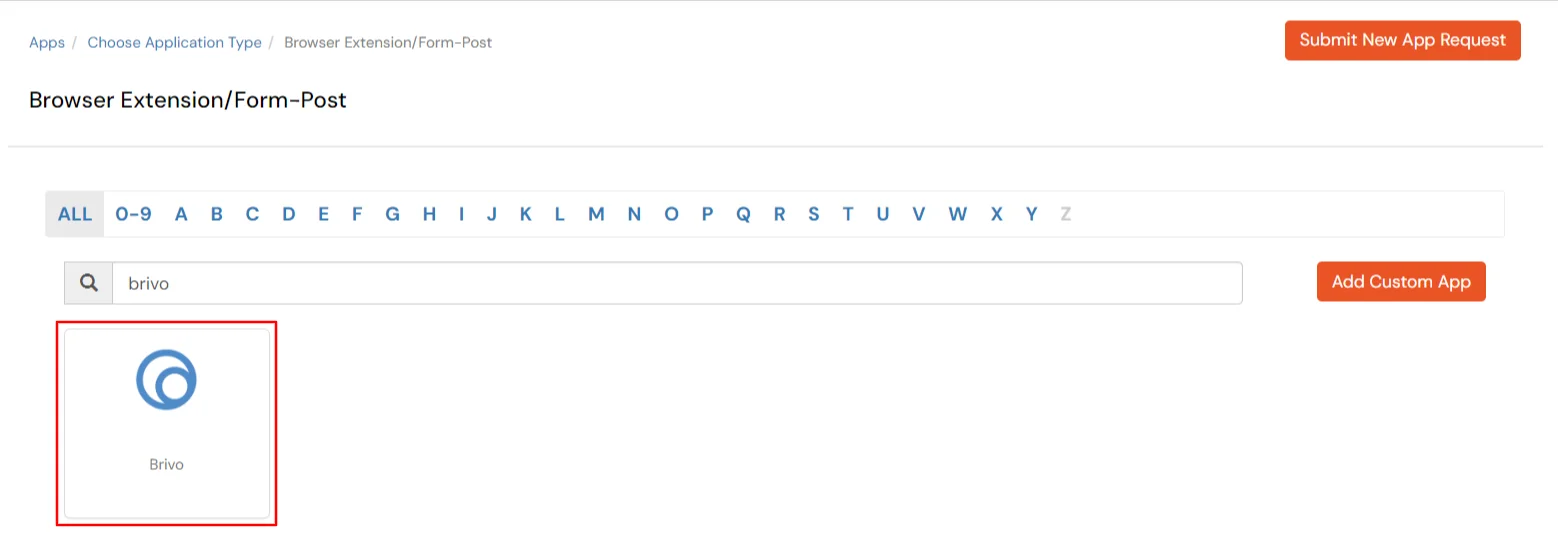
- Search for Brivo in the list, if you don't find Brivo in the list then, click on Add Custom App button.
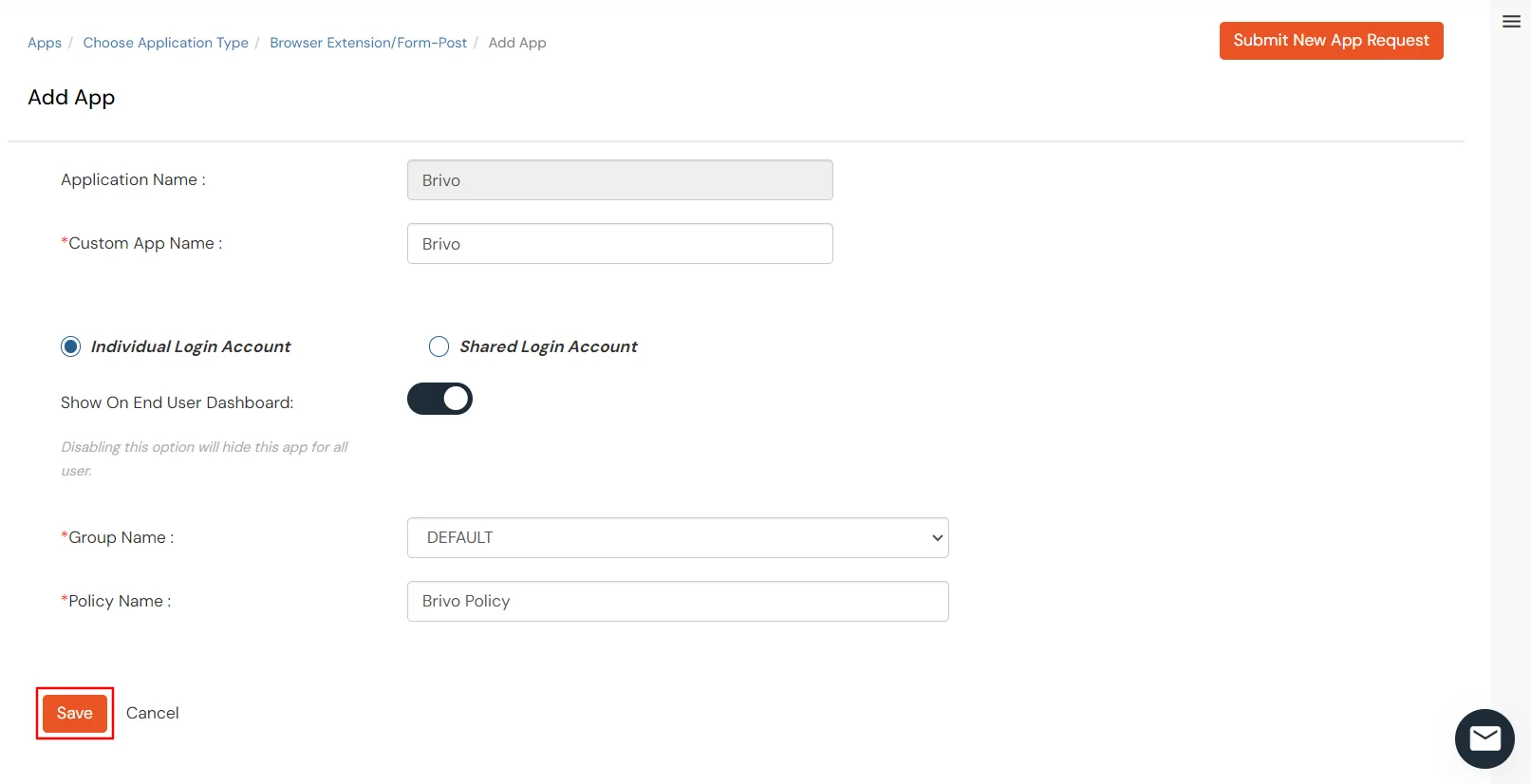
- Enter the following details in fields below:
| App details |
Description |
| Group Name |
Select Group name as default.(This will allow all your added groups to access this service) |
| Policy Name |
Select Policy Name the same as your application name. |
| Individual Login |
If each user has a different username and password for the app, admin should choose an Individual Login Account option, so that users can save their username and password from the user portal themselves. |
| Shared Login |
If multiple users are allowed to access the app via the same credentials assigned by admin, admin should choose share Login Account option. |
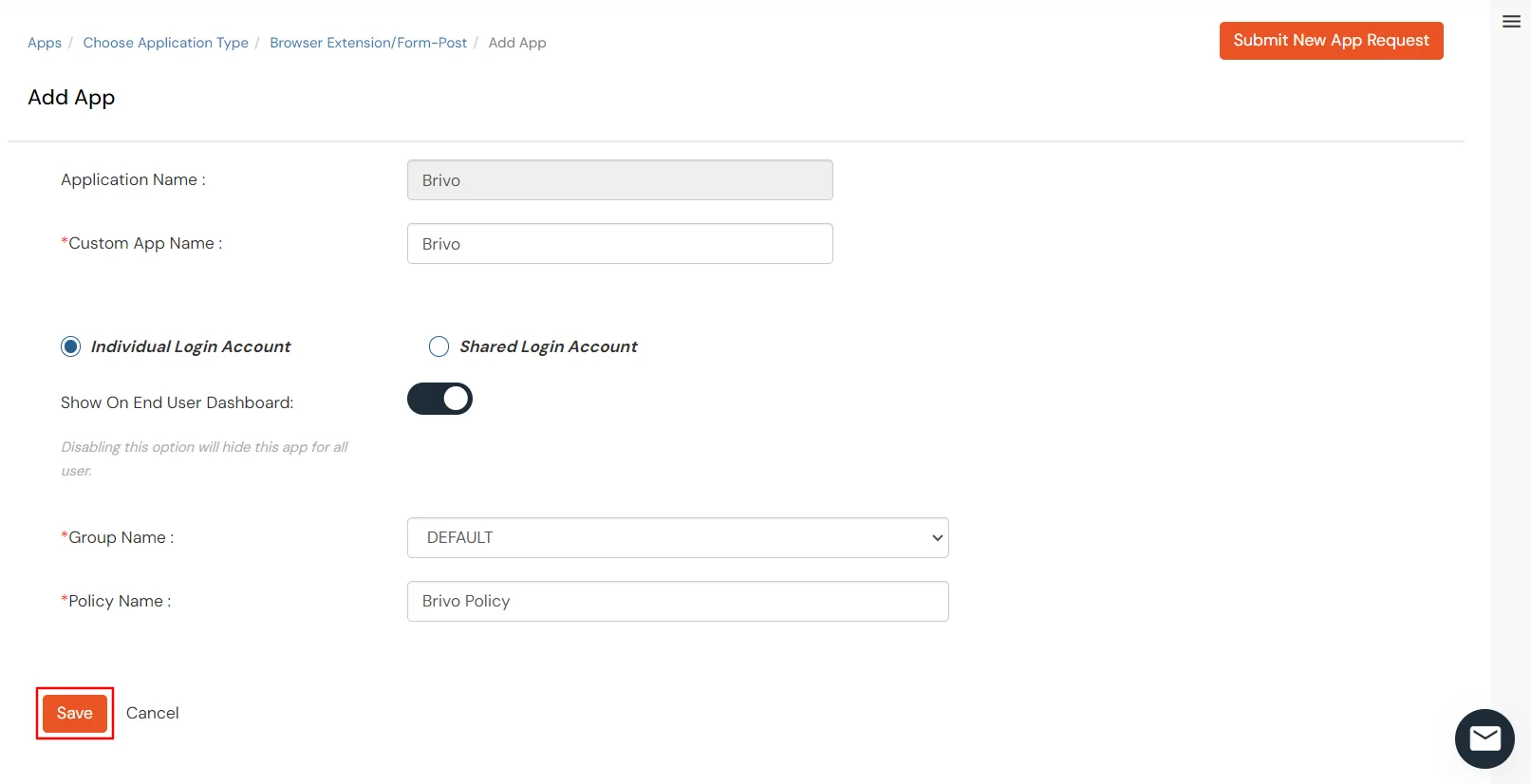
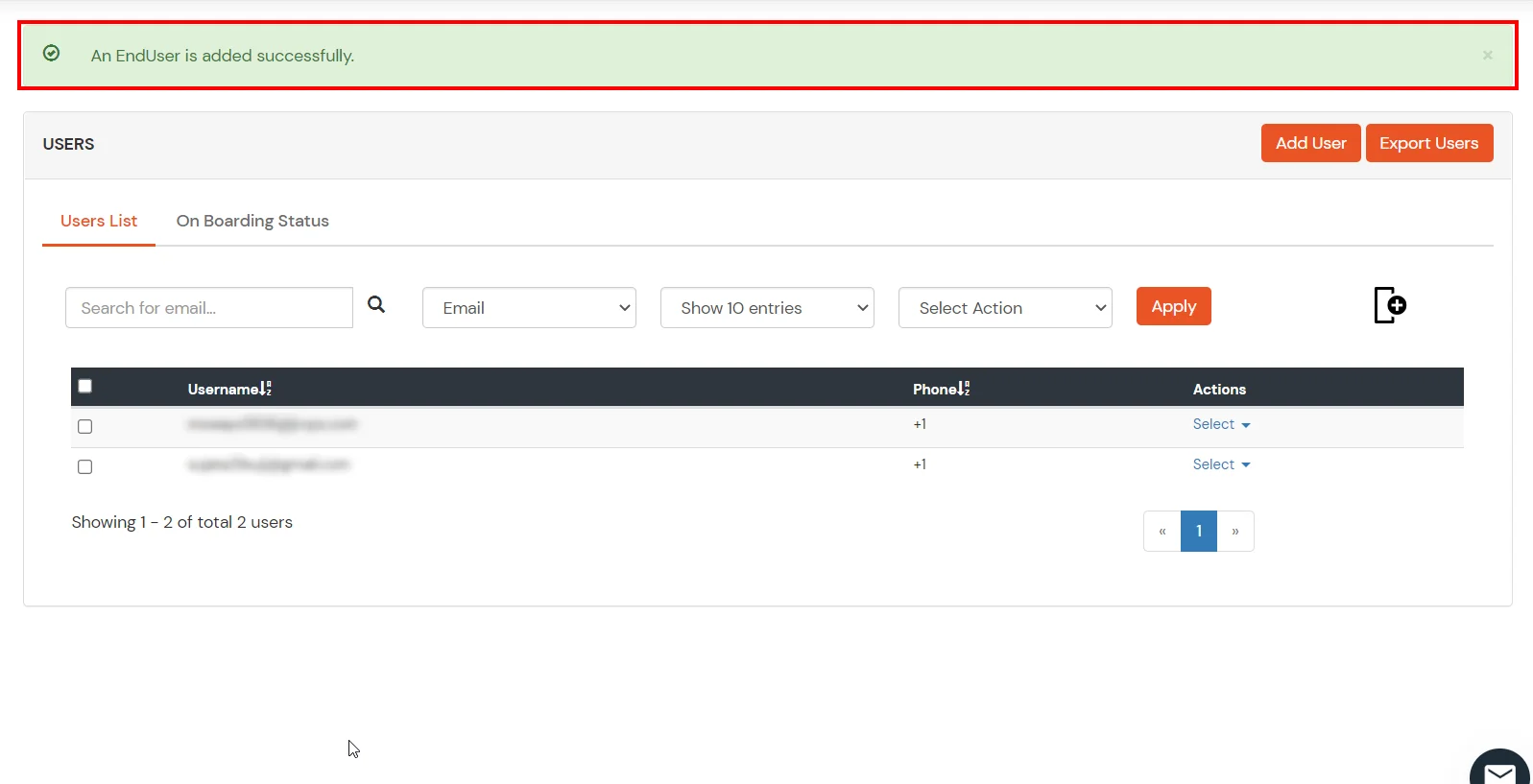
- Select your login type and click on the Save button.
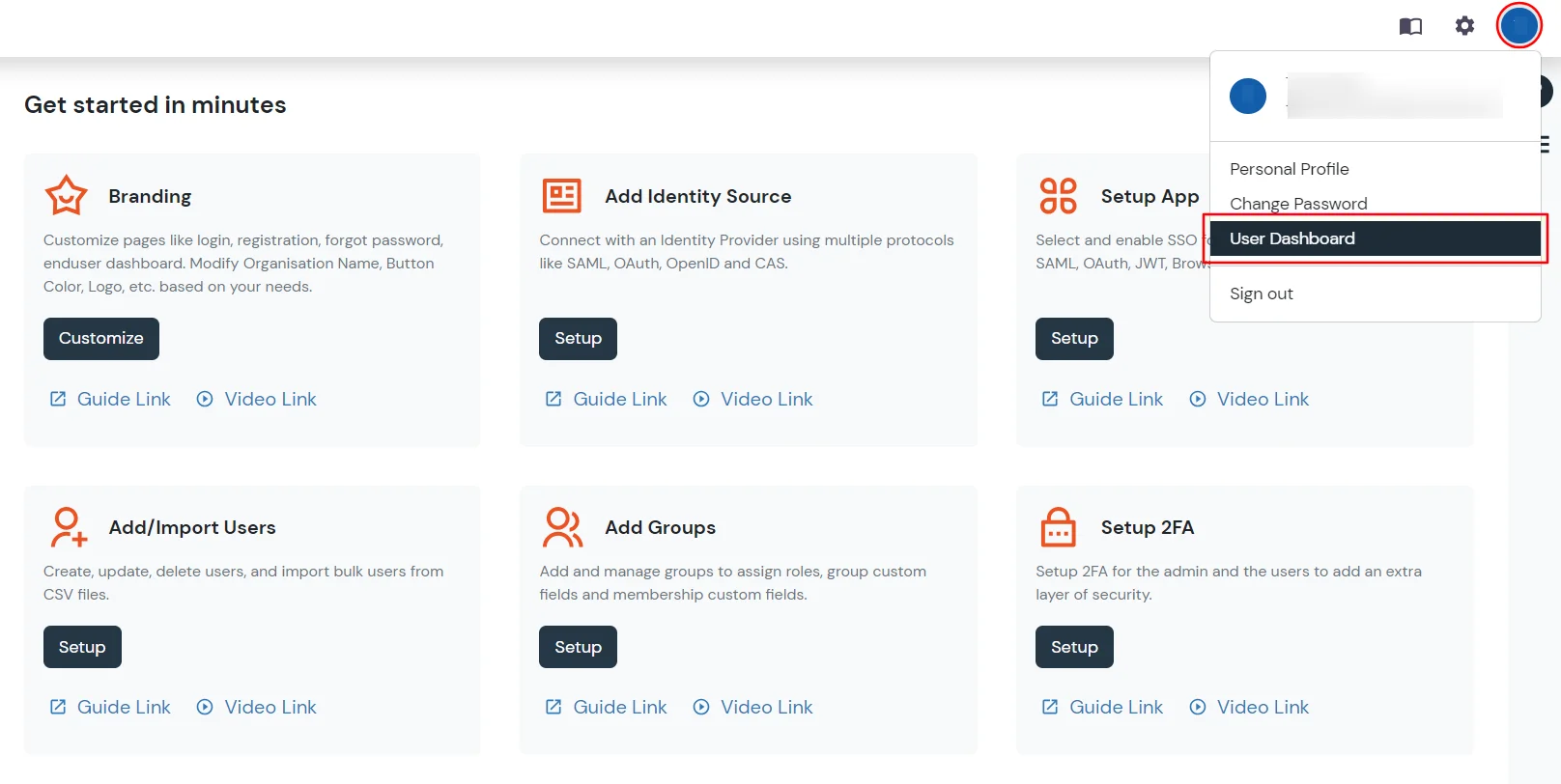
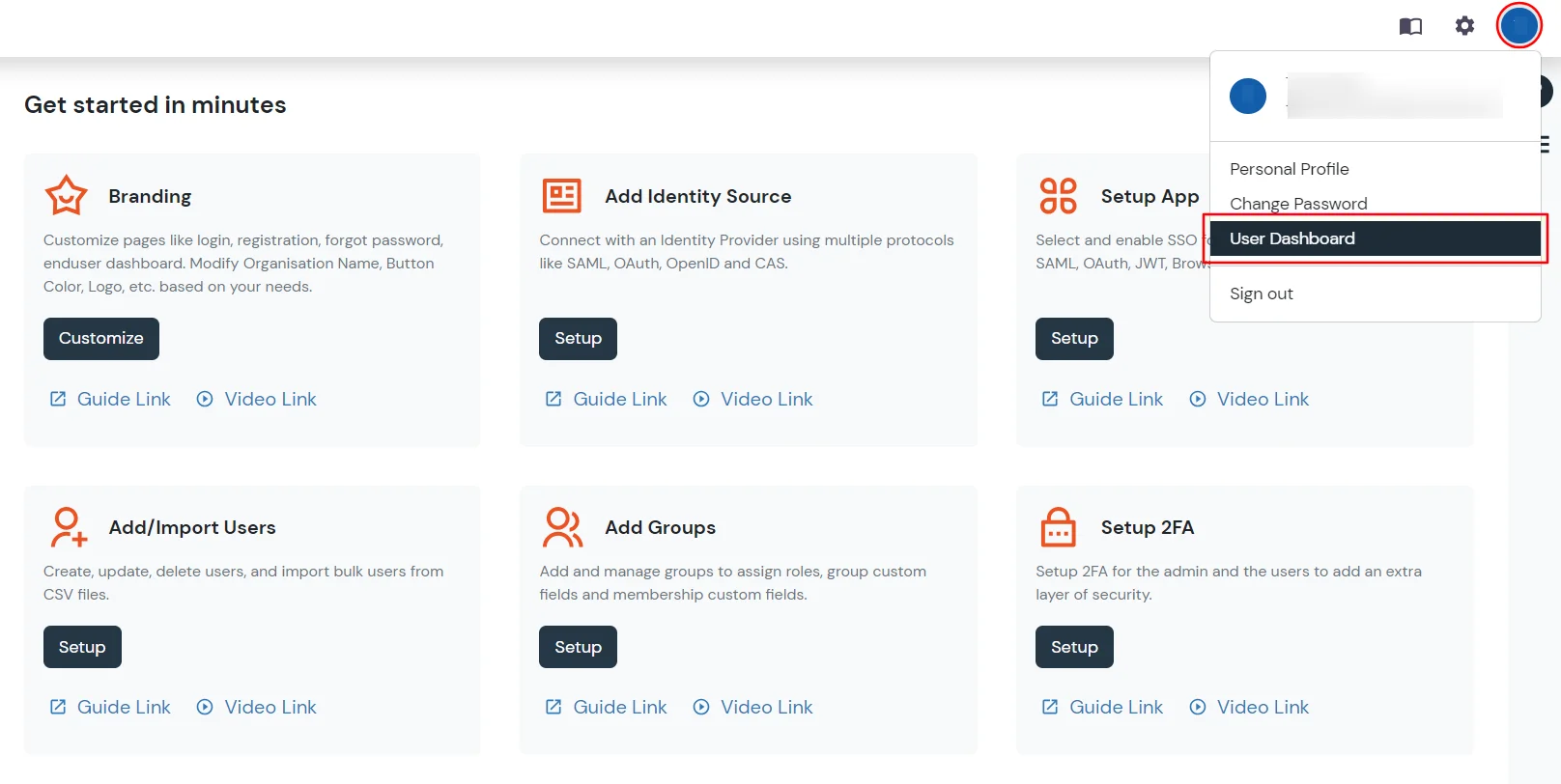
- From the top right side click Profile >> and then User Dashboard.
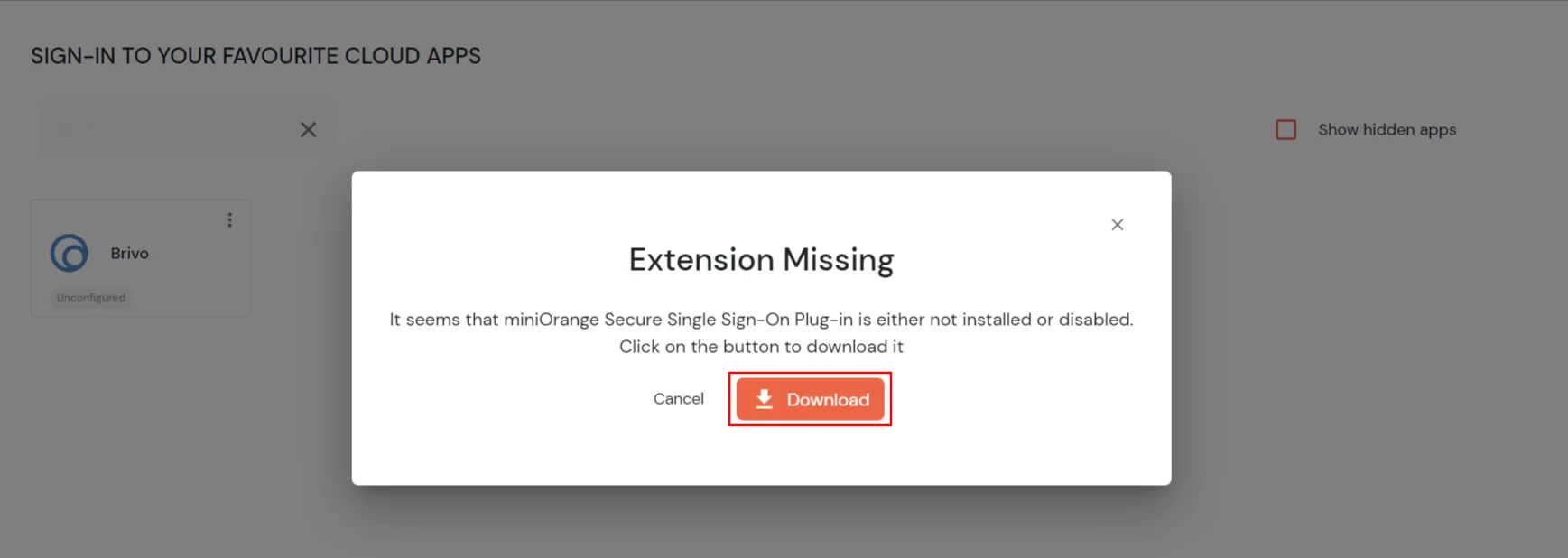
- Under the "SIGN-IN TO YOUR FAVOURITE CLOUD APPS" section search for Brivo app. Click on Brivo app icon then, click Download symbol.
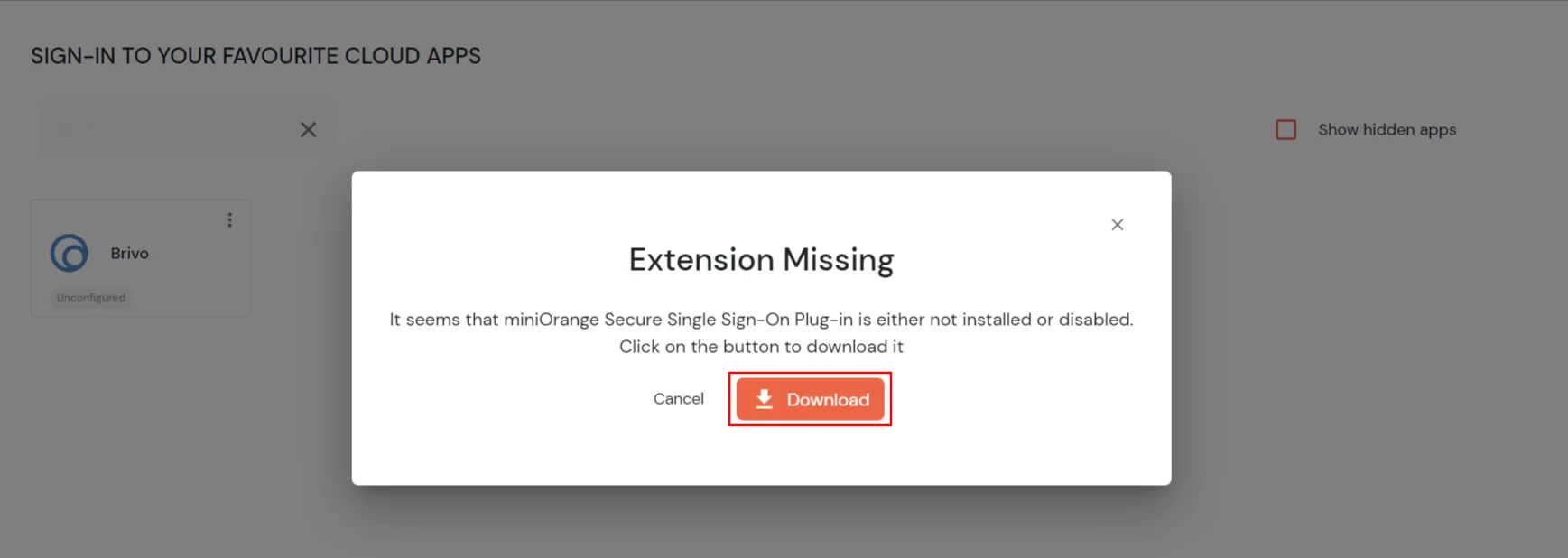
- It will redirect you to add extension page. Now, click on the Add to Chrome.

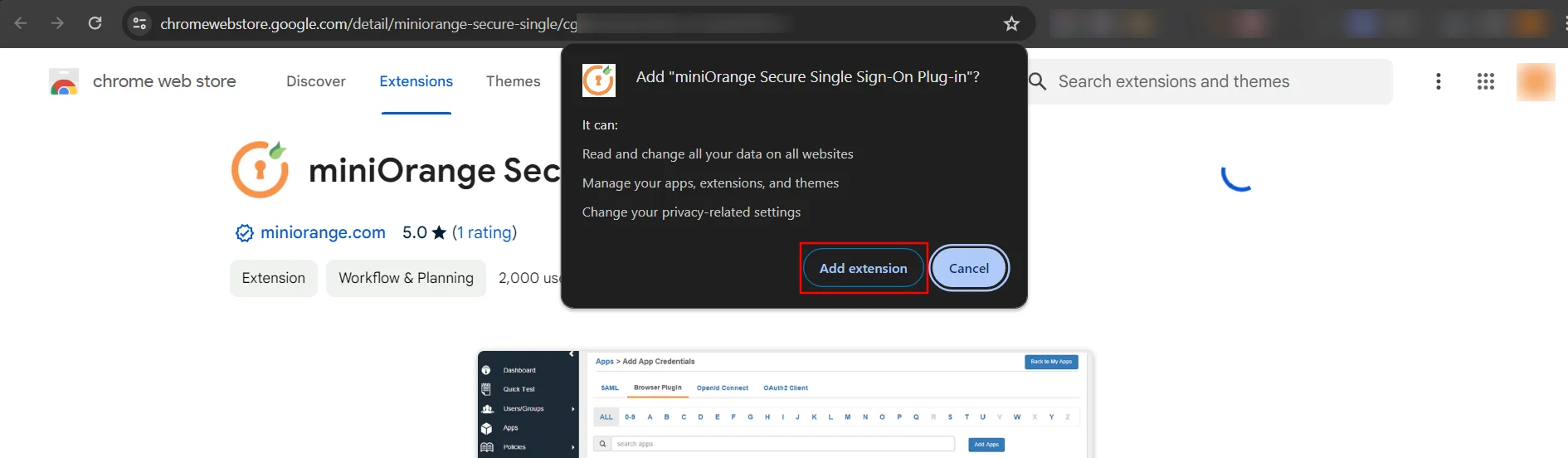
- Click on Add extension.
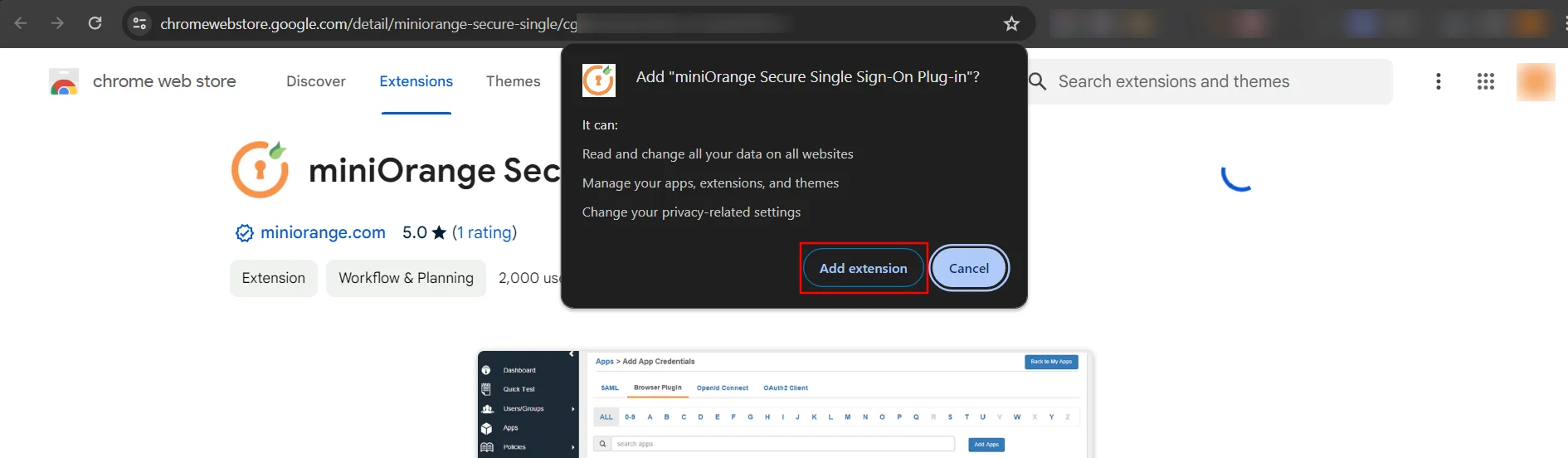
- Now, miniOrange extension is added in your extension
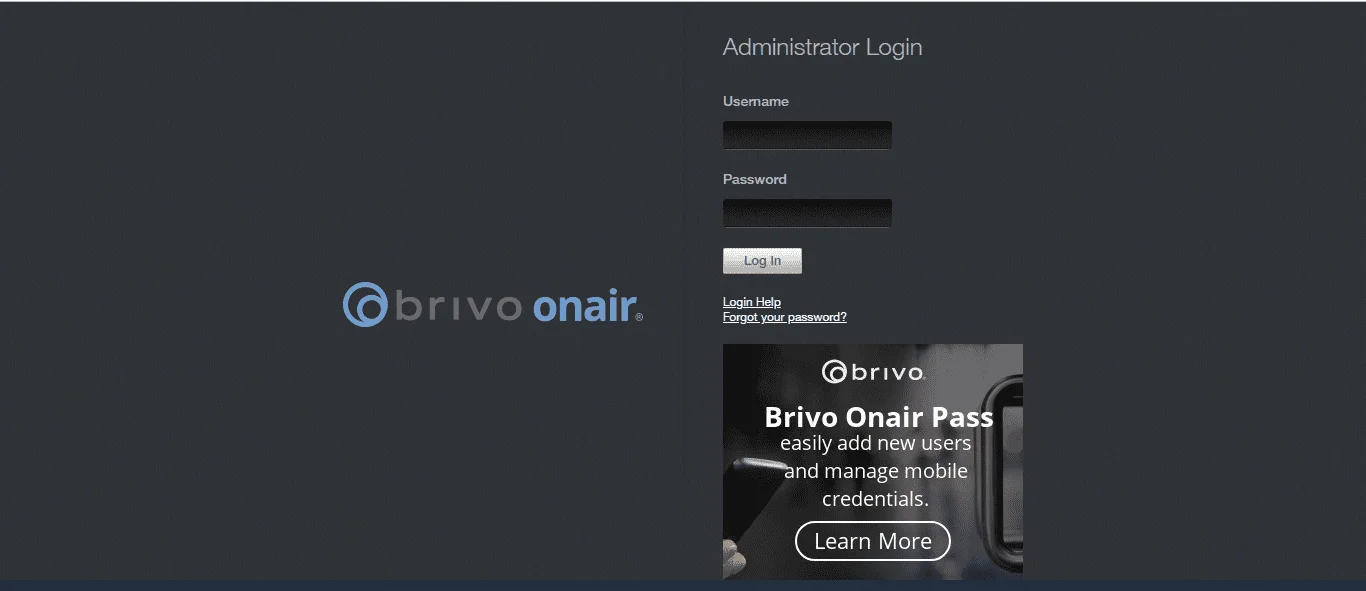
- Click on the app icon from miniOrange user portal, you will be redirected to Brivo login page.
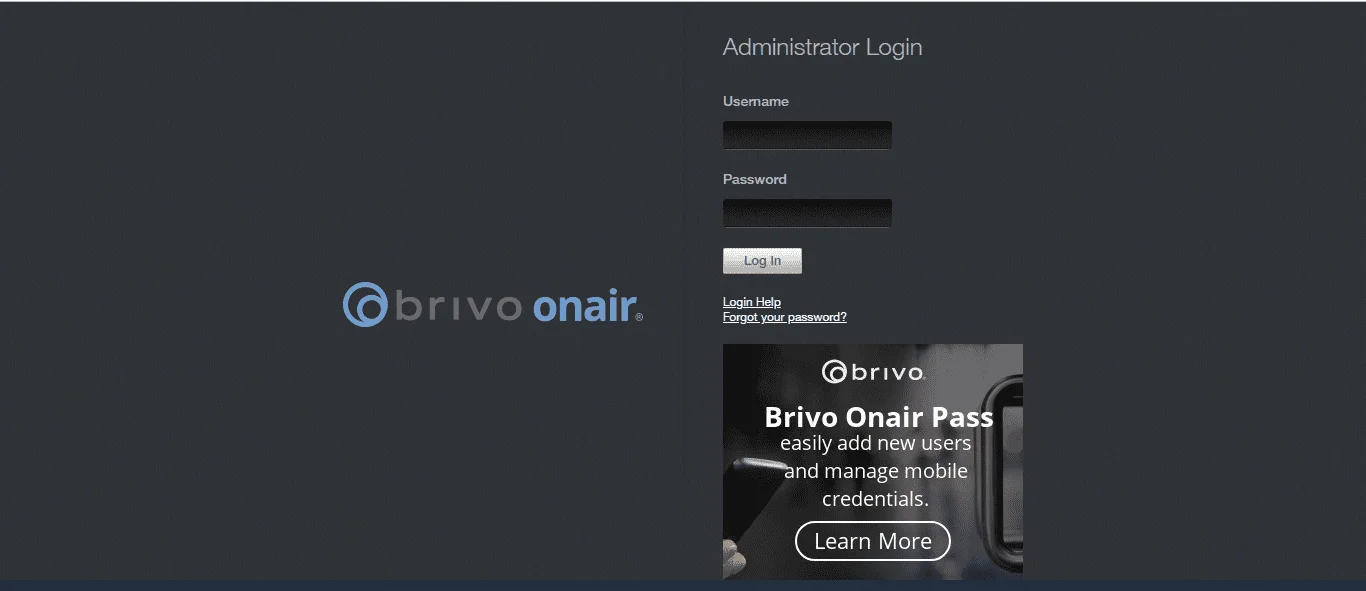
- Now browser extension will fill the username and password credentials automatically. Once enabled, end users can see an icon on their browser which auto-fills username and password on the application login page and submit the page automatically to let user access the app.
- Now, you can see the homepage of the app.
2. Embed Brivo application link in your Website/User Portal
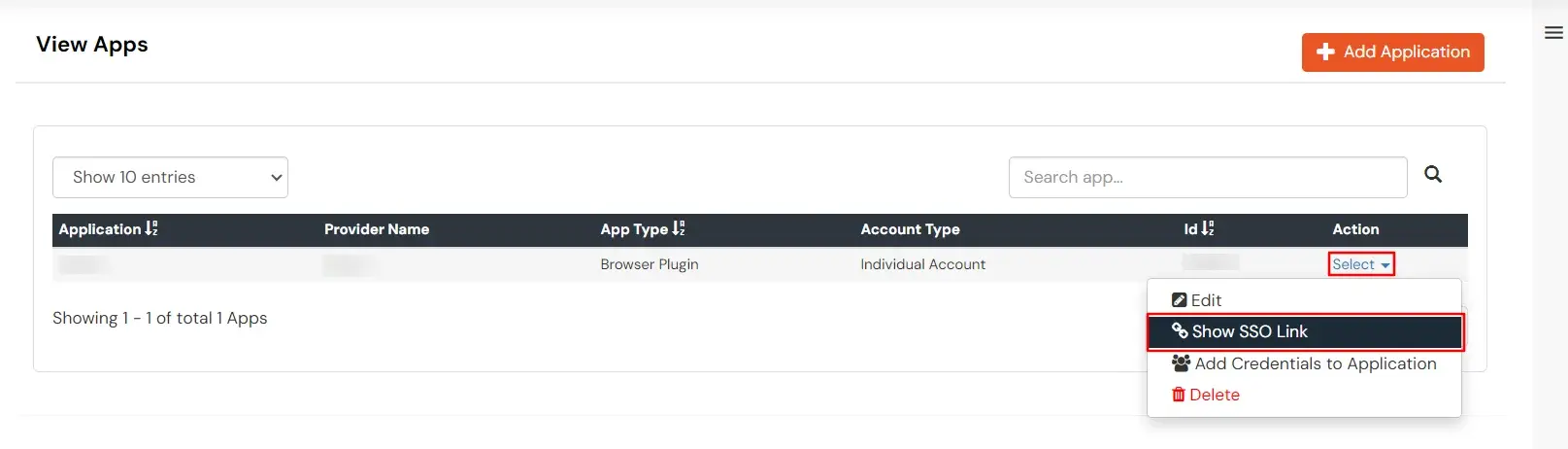
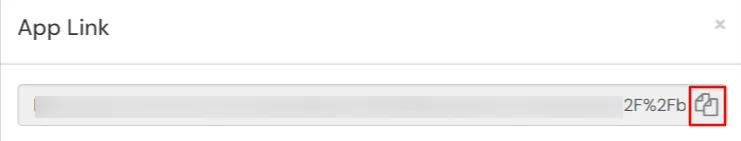
- Go to Admin Dashboard >> Apps >> search for Brivo app.
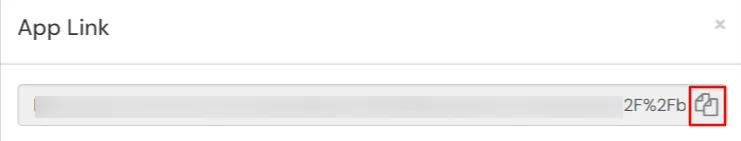
- Click on Select in Action menu against Brivo app. Select Show SSO link option from dropdown.
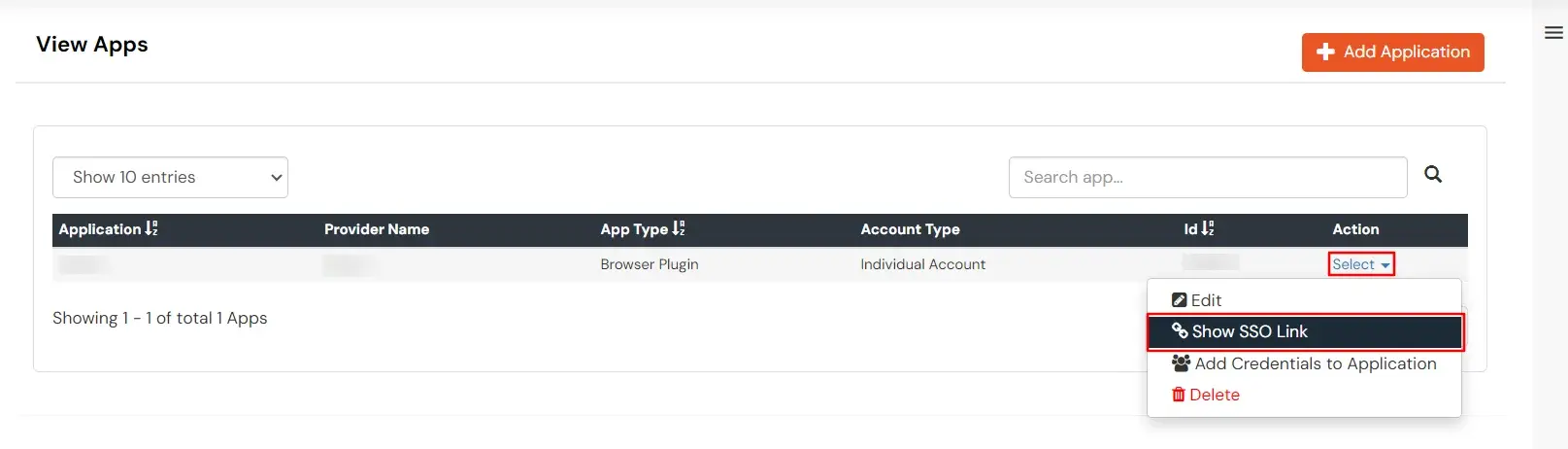
- Copy the app link and paste it anywhere on your website - User portal/ Apps Dashboard /Menu, etc.
3. Configure Your User Directory (Optional)
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
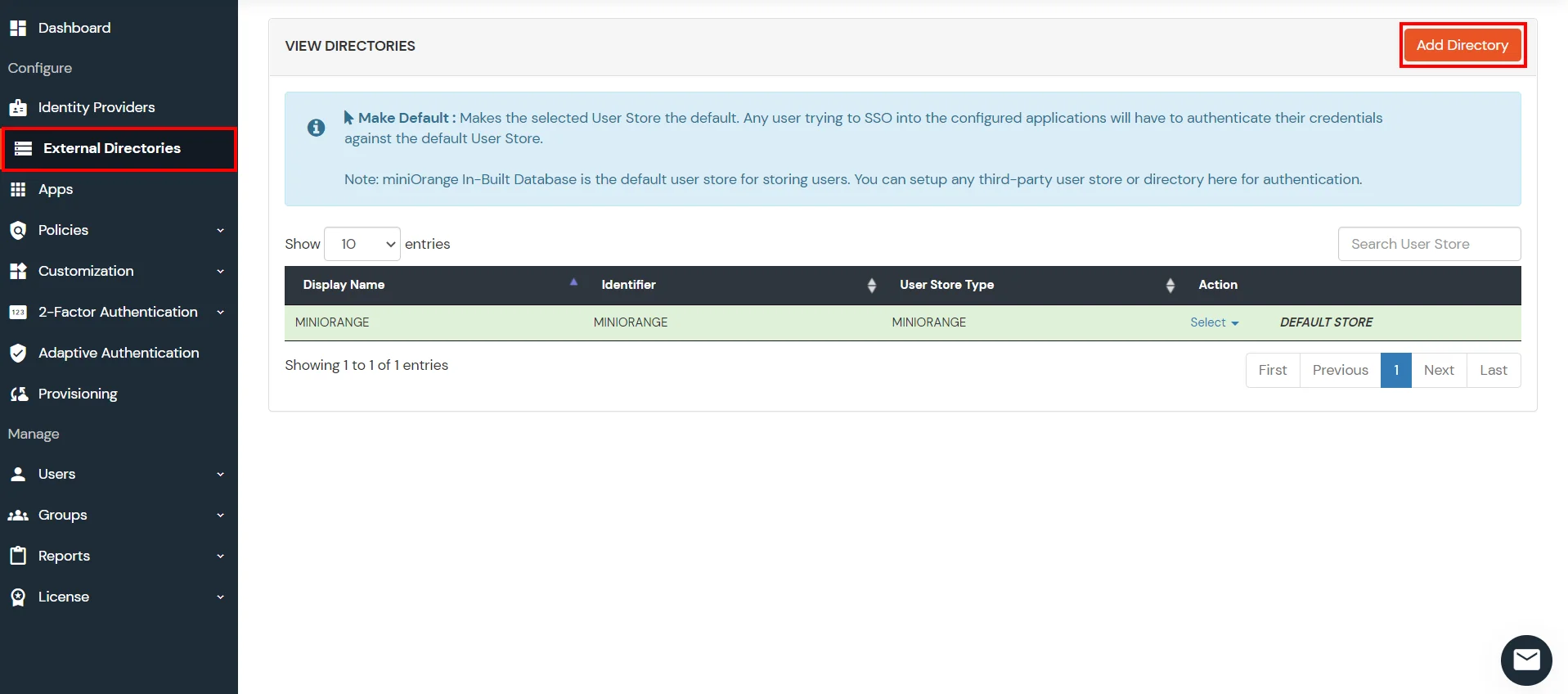
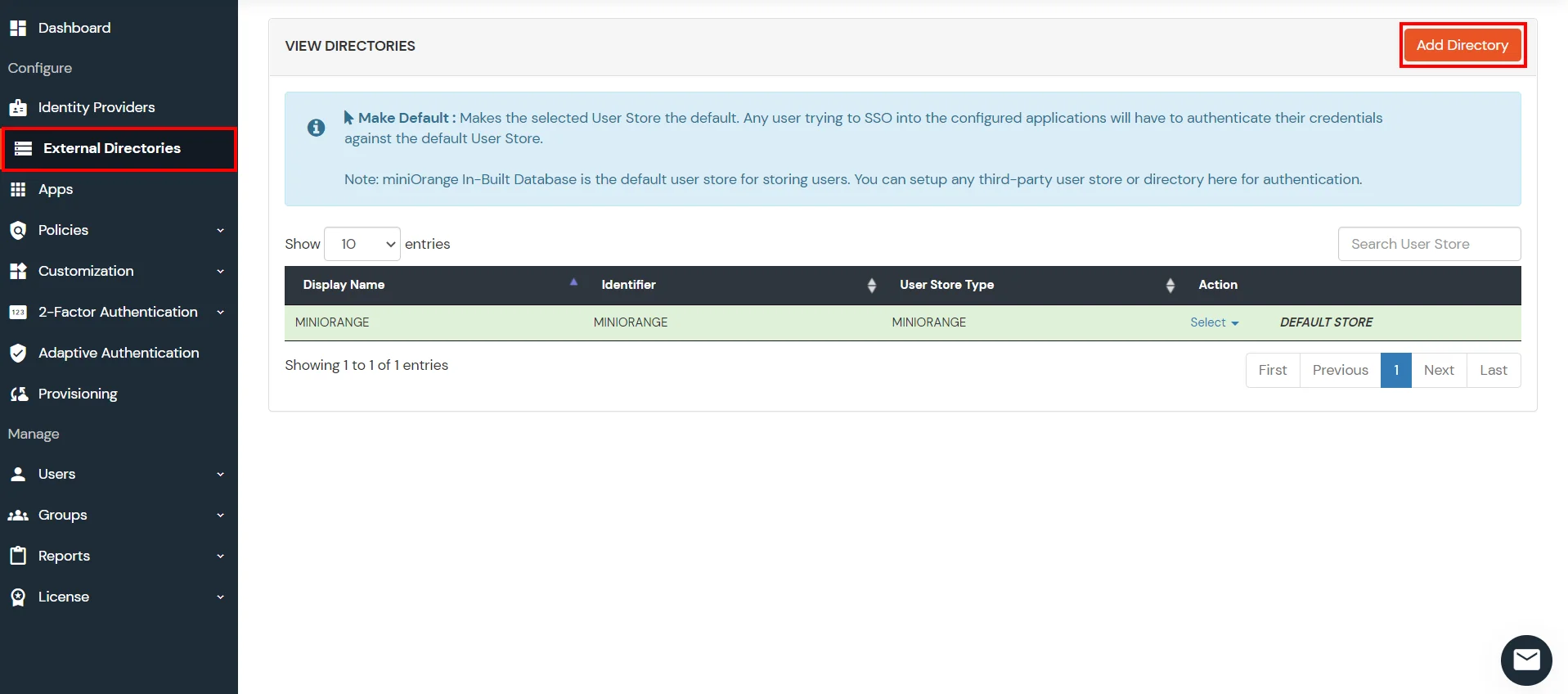
- Click on External Directories >> Add Directory in the left menu of the dashboard.
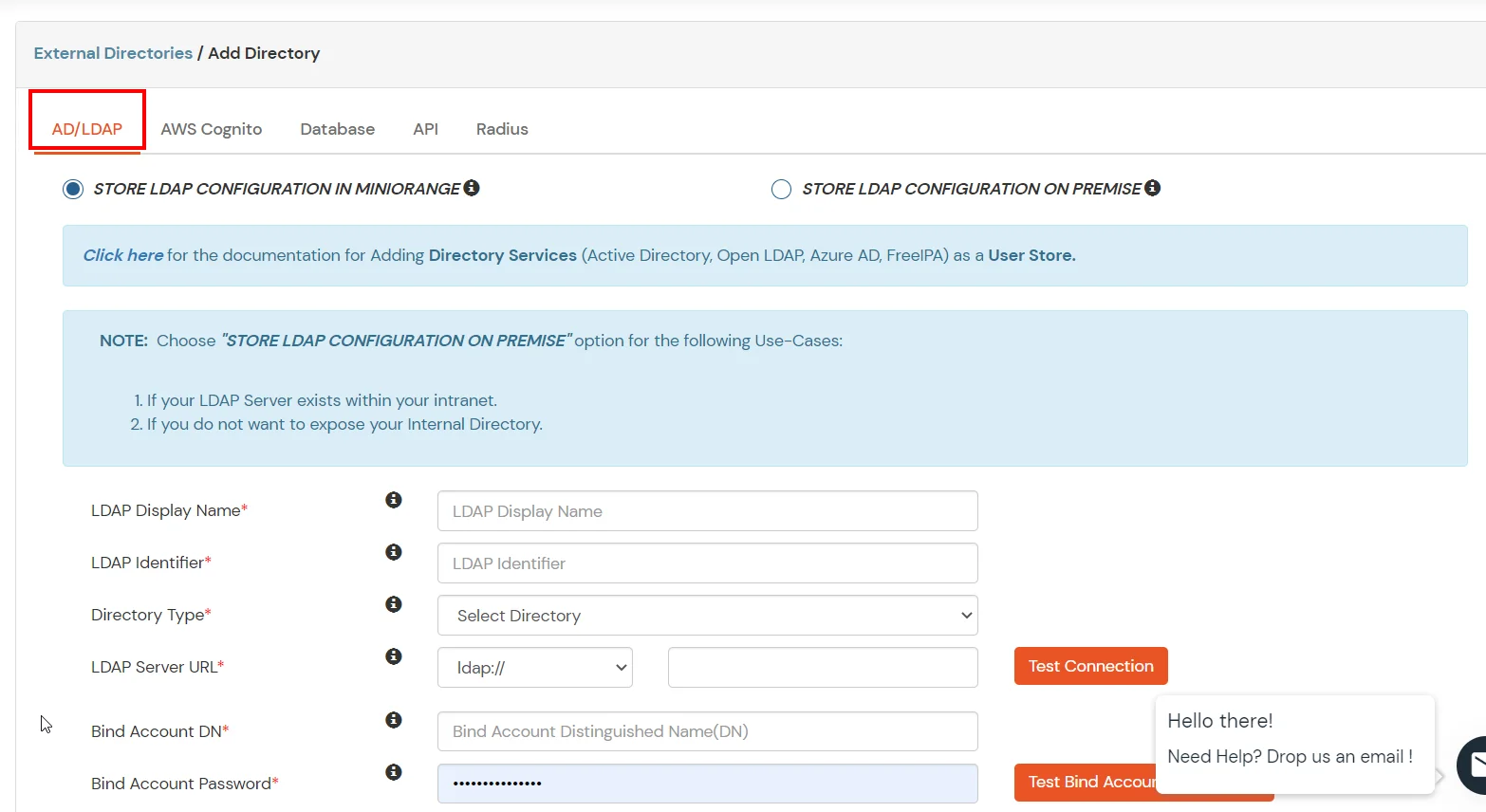
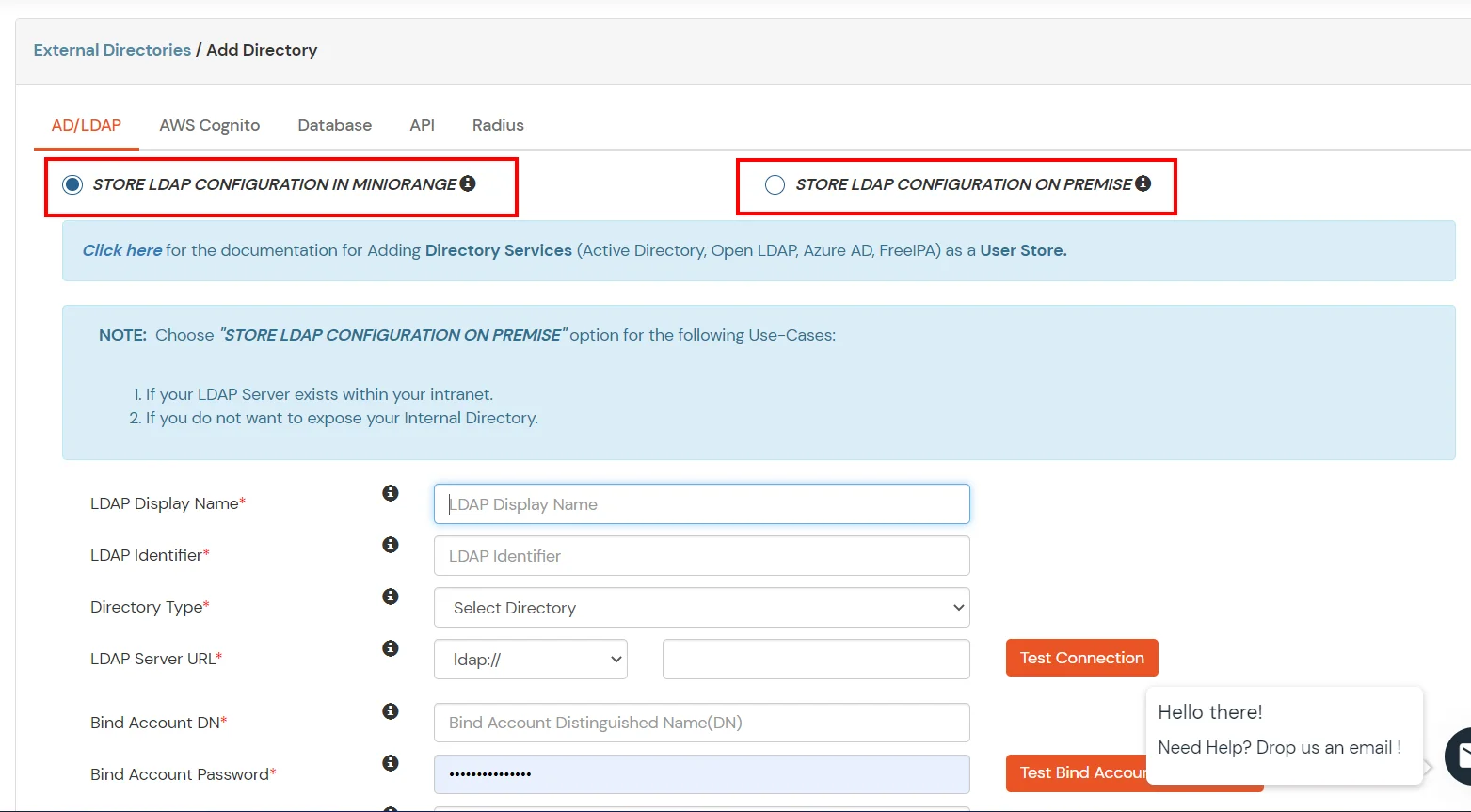
- Select Directory type as AD/LDAP.
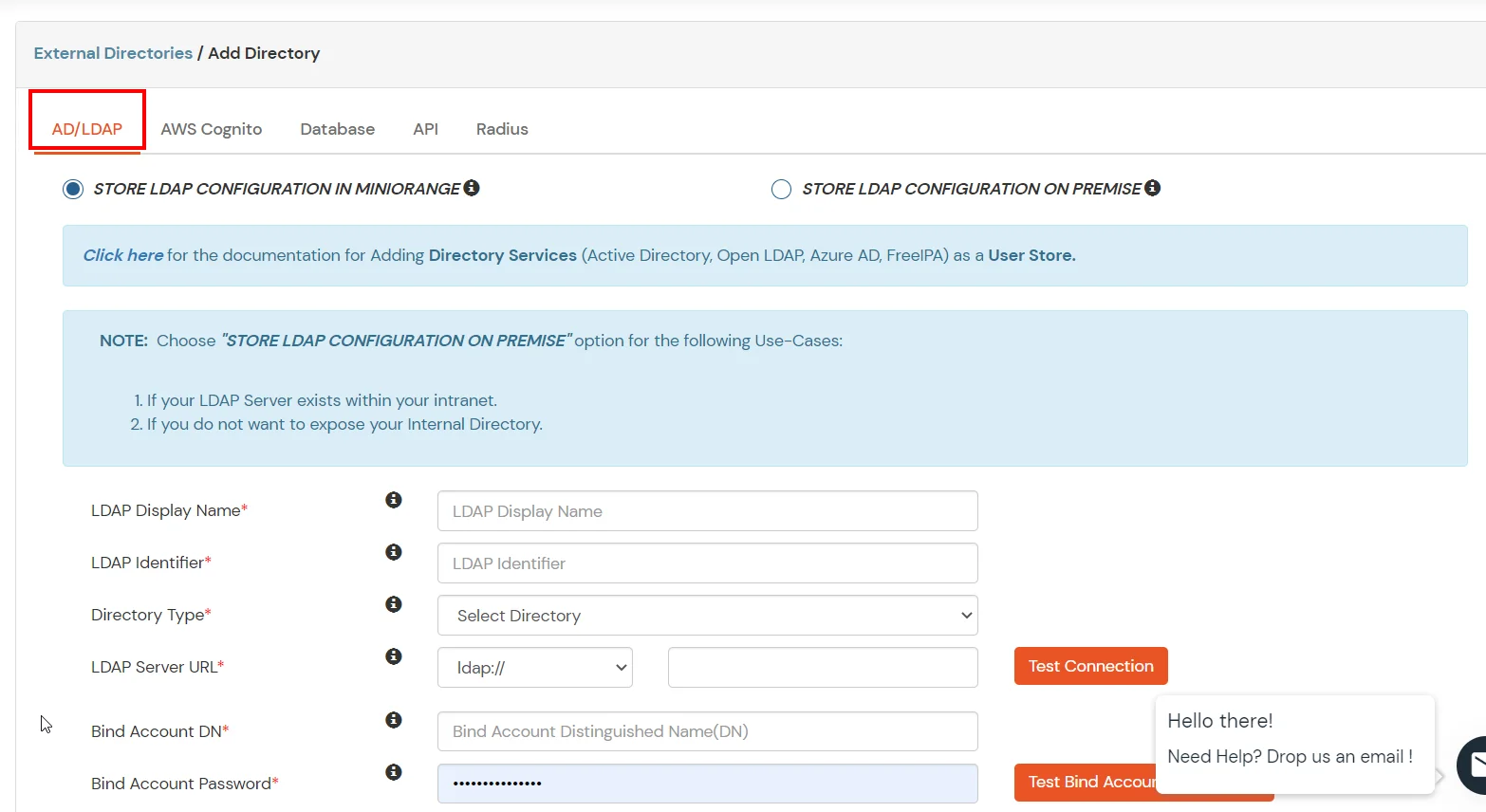
- STORE LDAP CONFIGURATION IN MINIORANGE: Choose this option if you want to keep your configuration in miniOrange. If active directory is behind a firewall, you will need to open the firewall to allow incoming requests to your AD.
- STORE LDAP CONFIGURATION ON PREMISE: Choose this option if you want to keep your configuration in your premise and only allow access to AD inside premises. You will have to download and install miniOrange gateway in your premise.
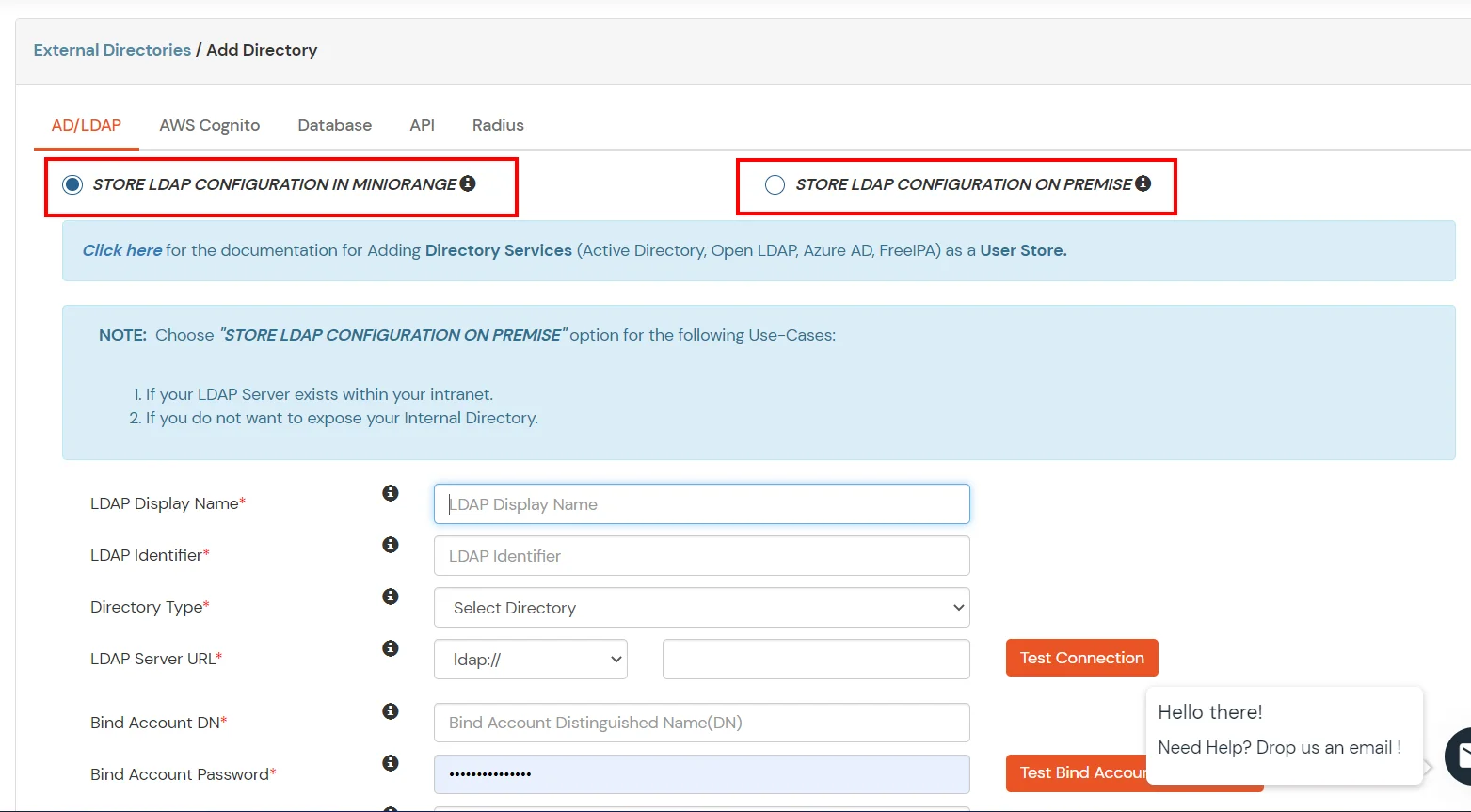
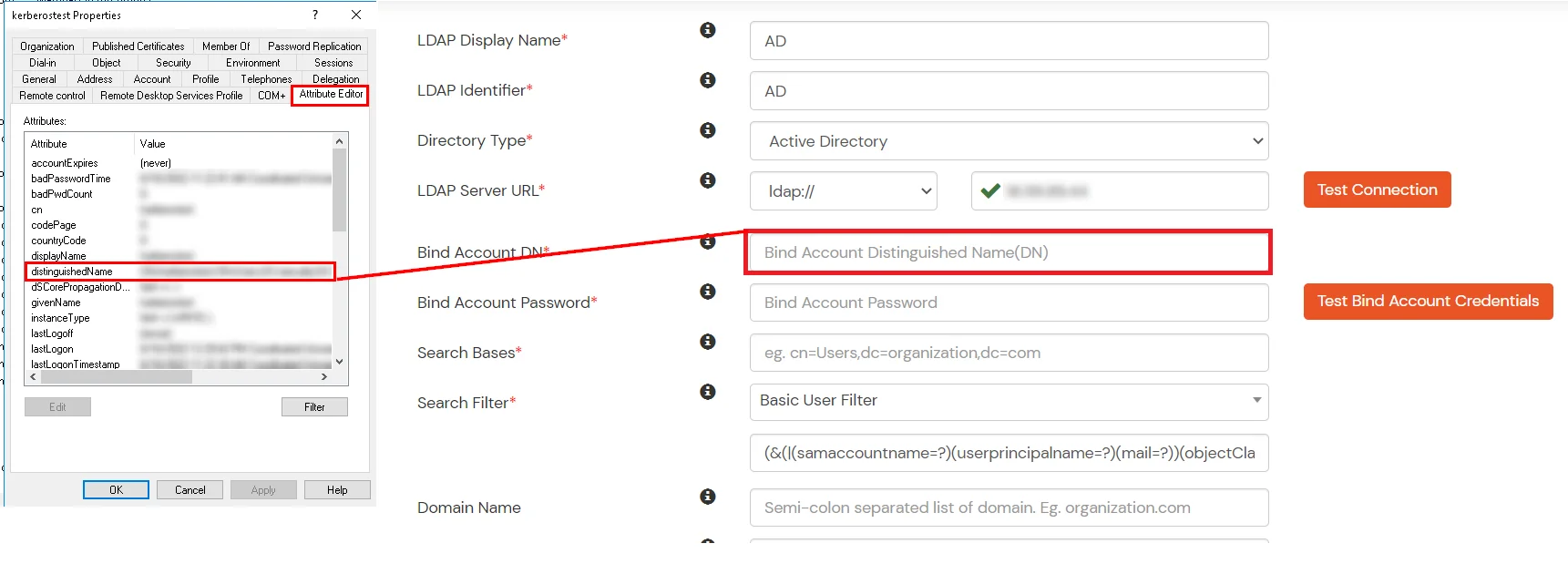
- Enter LDAP Display Name and LDAP Identifier name.
- Select Directory Type as Active Directory.
- Enter the LDAP Server URL or IP Address against LDAP Server URL field.
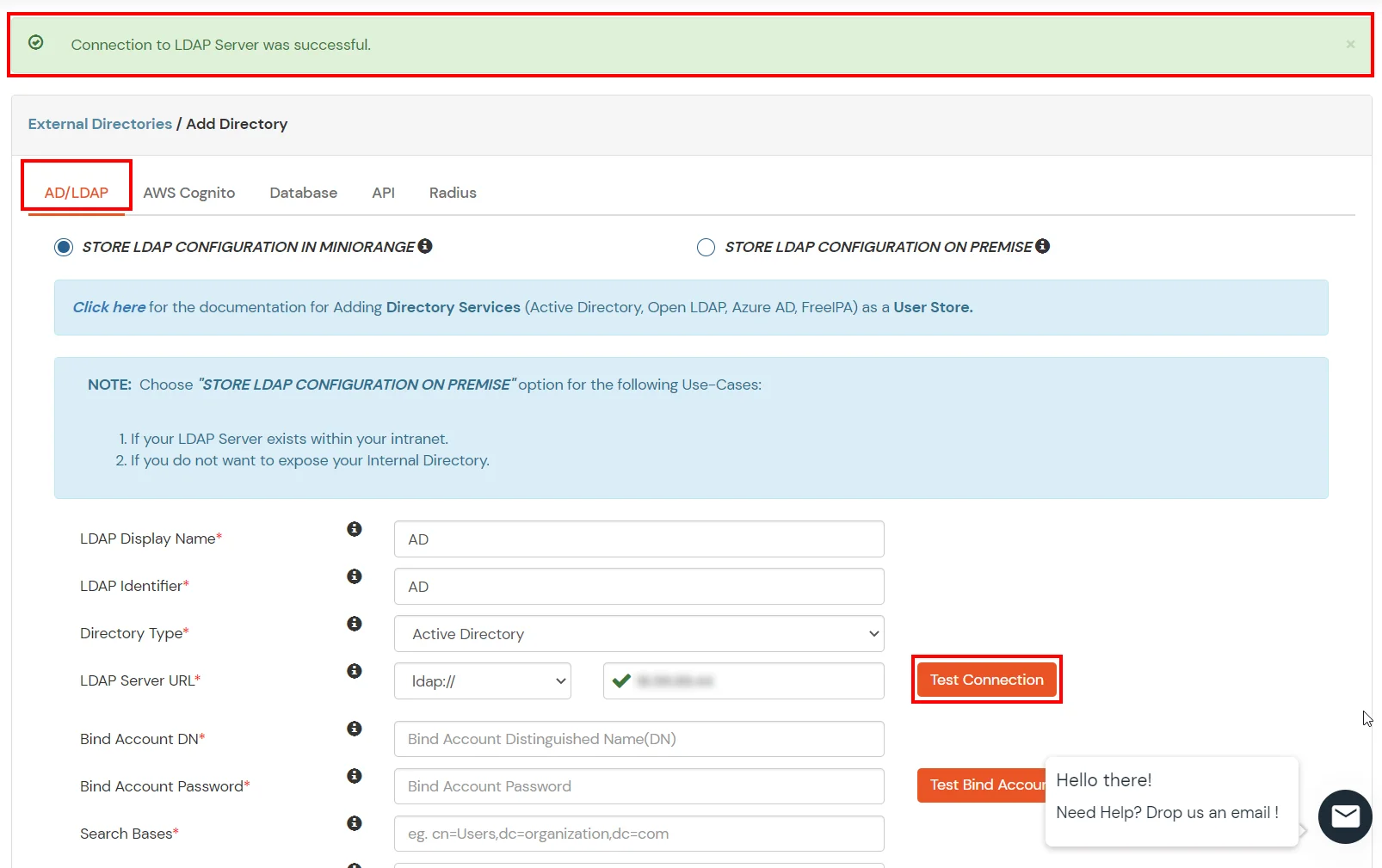
- Click on Test Connection button to verify if you have made a successful connection with your LDAP server.
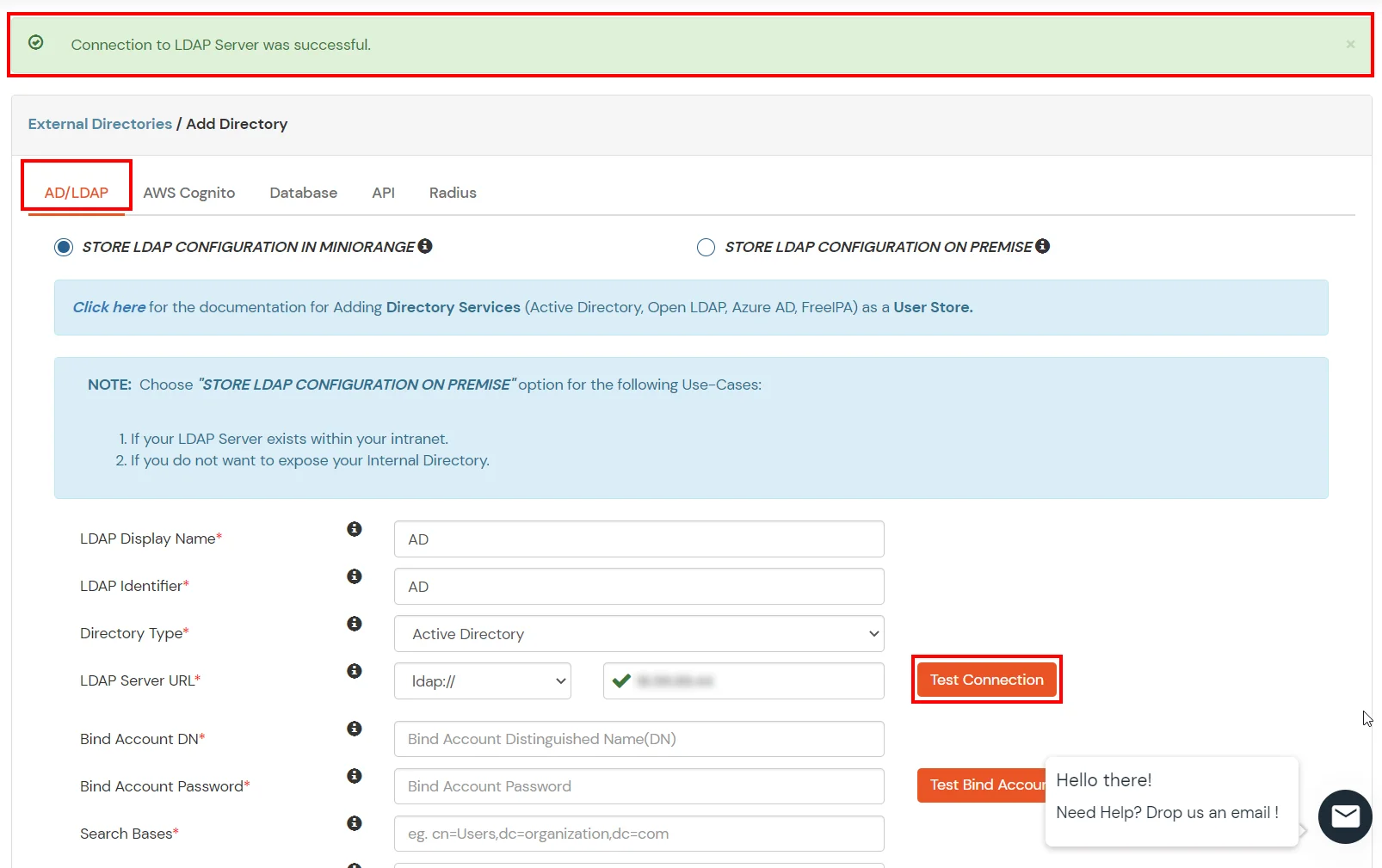
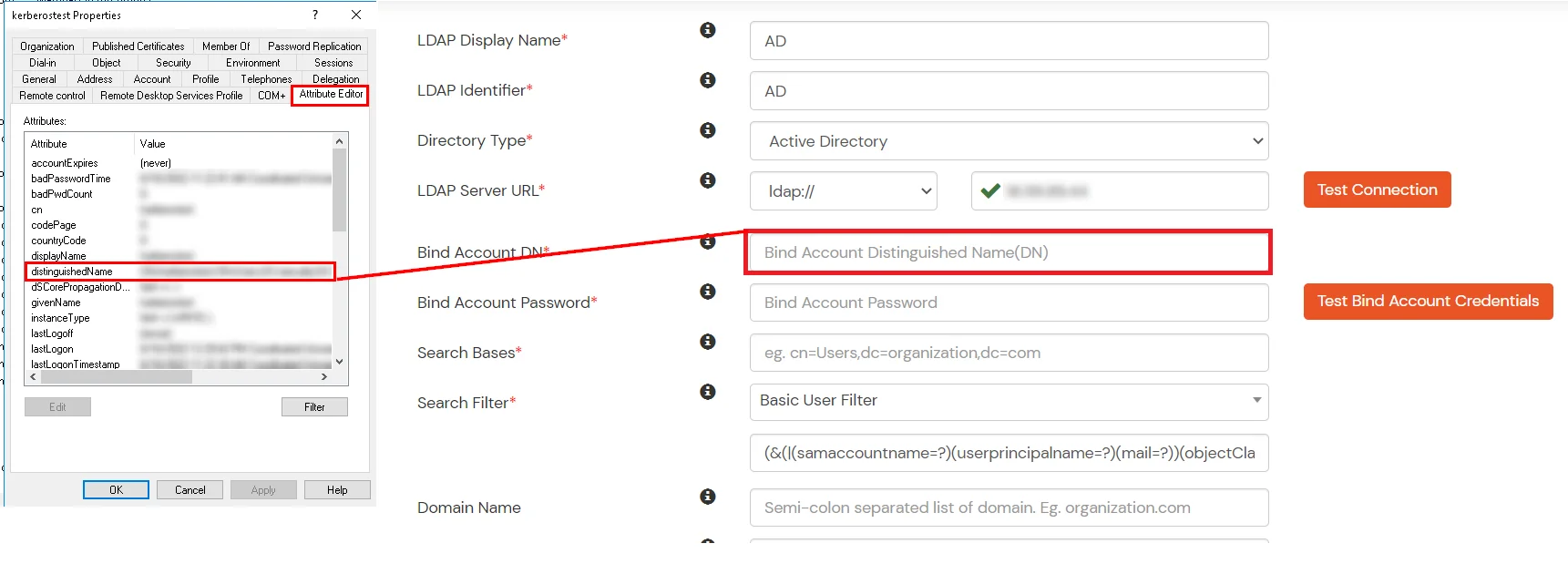
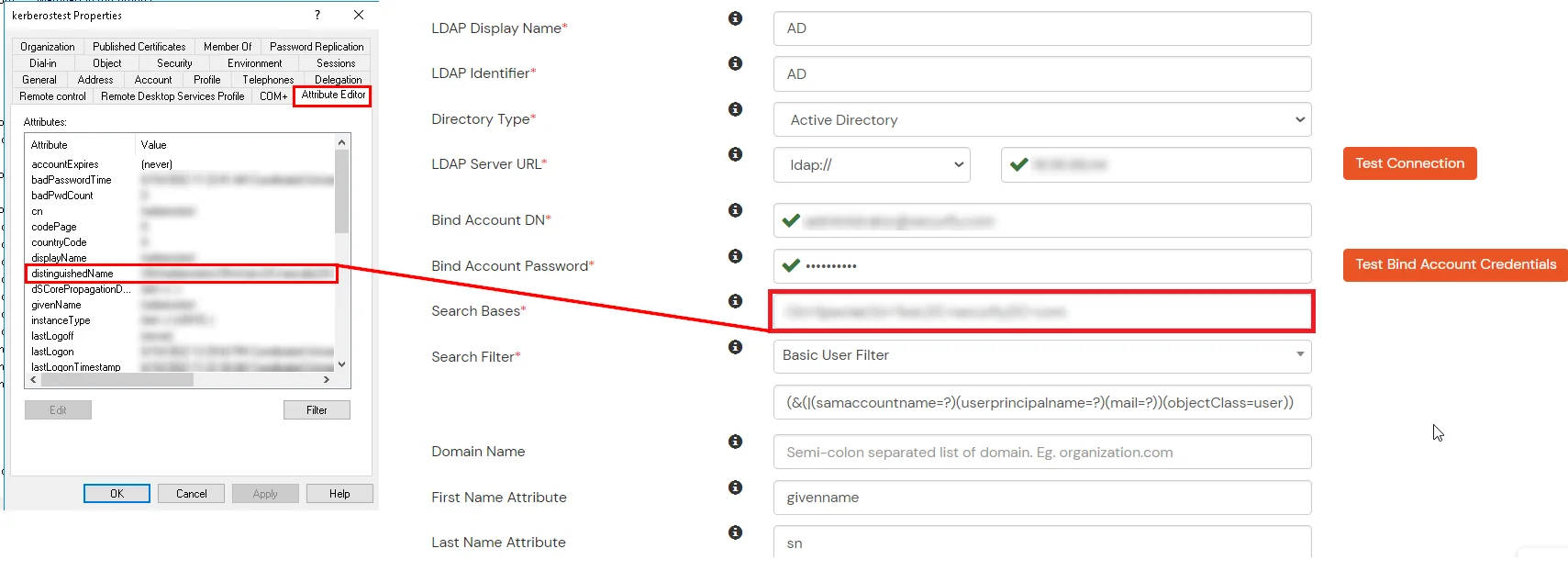
- In Active Directory, go to the properties of user containers/OU's and search for Distinguished Name attribute.
- Enter the valid Bind account Password.
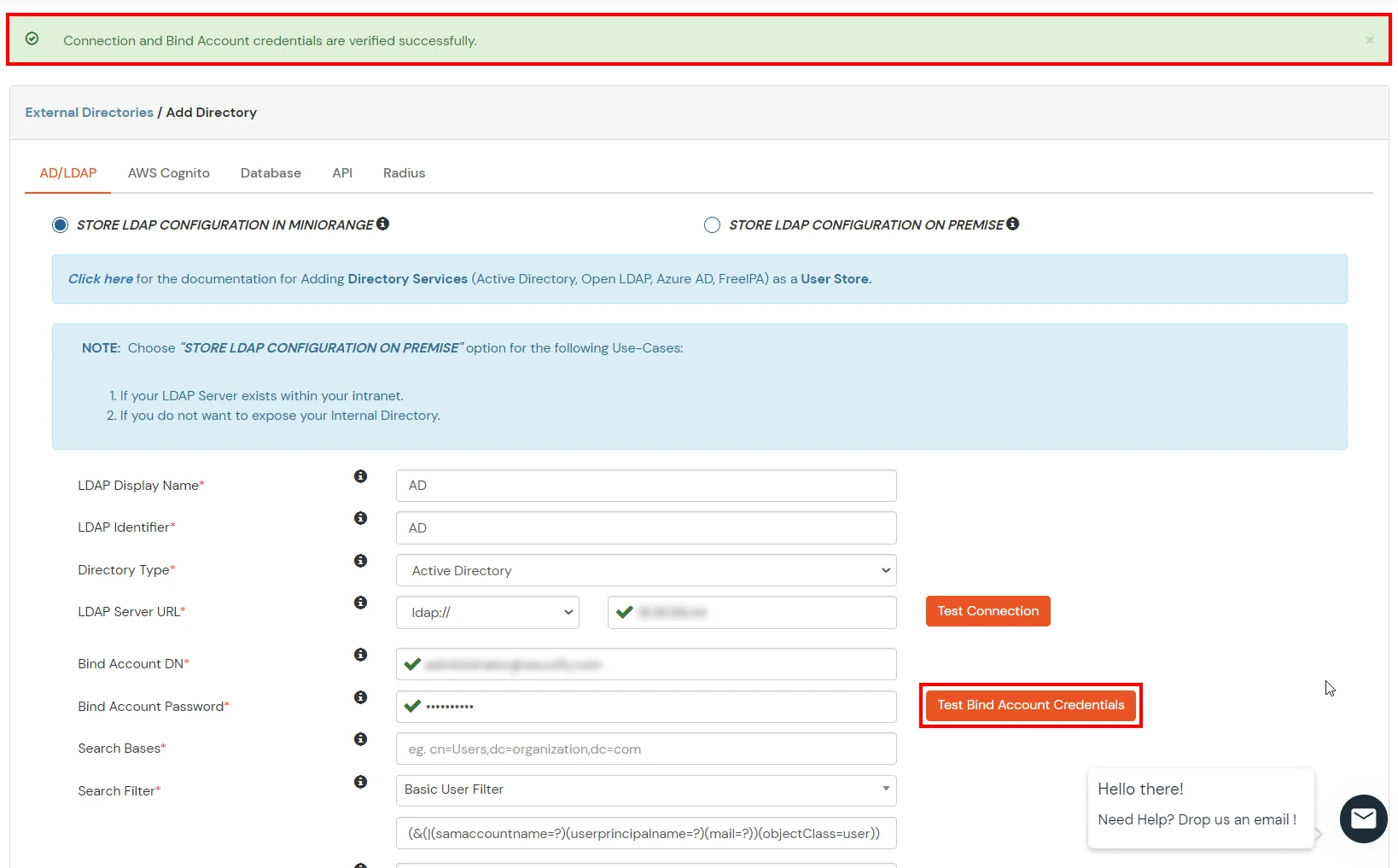
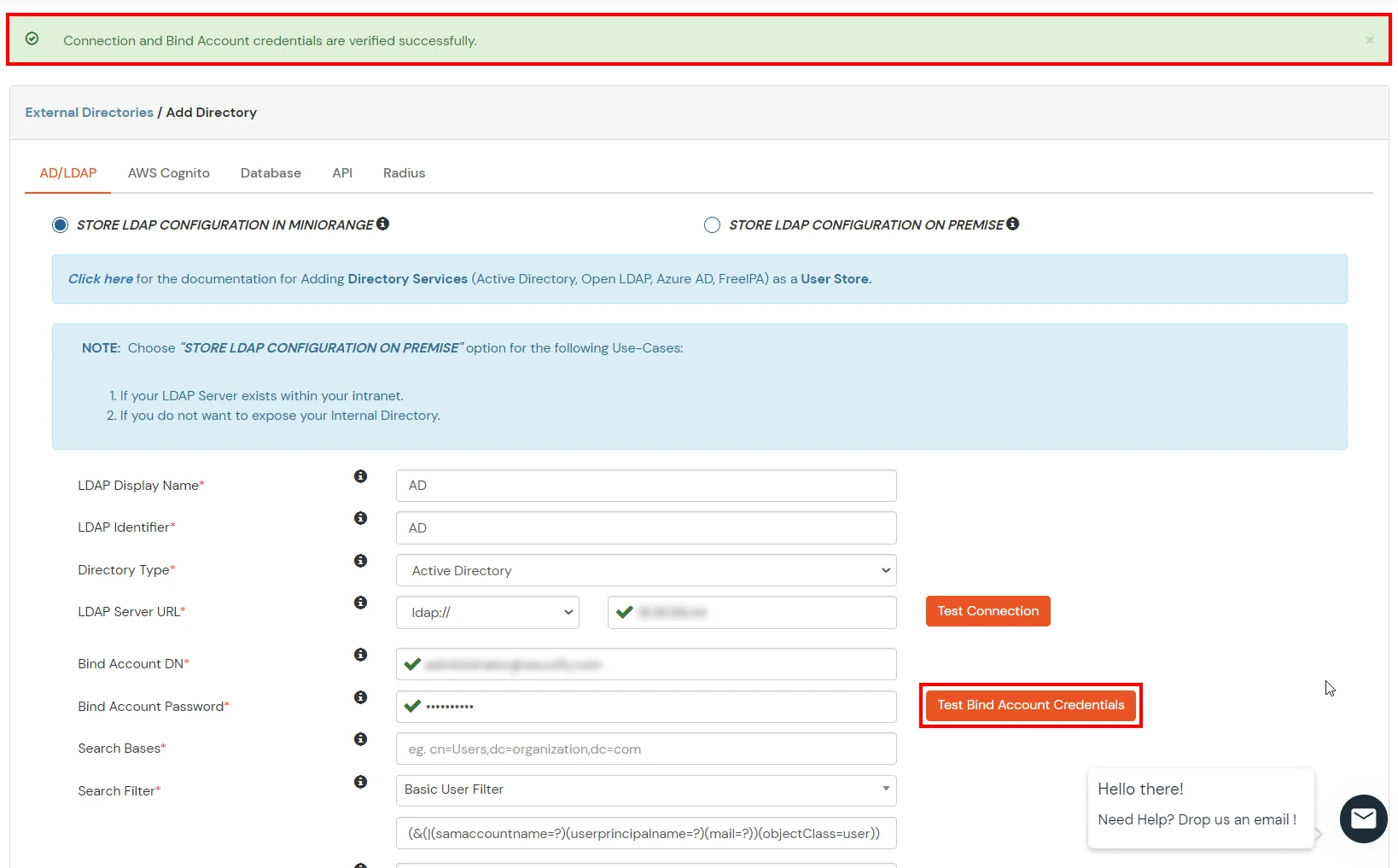
- Click on Test Bind Account Credentials button to verify your LDAP Bind credentials for LDAP connection.
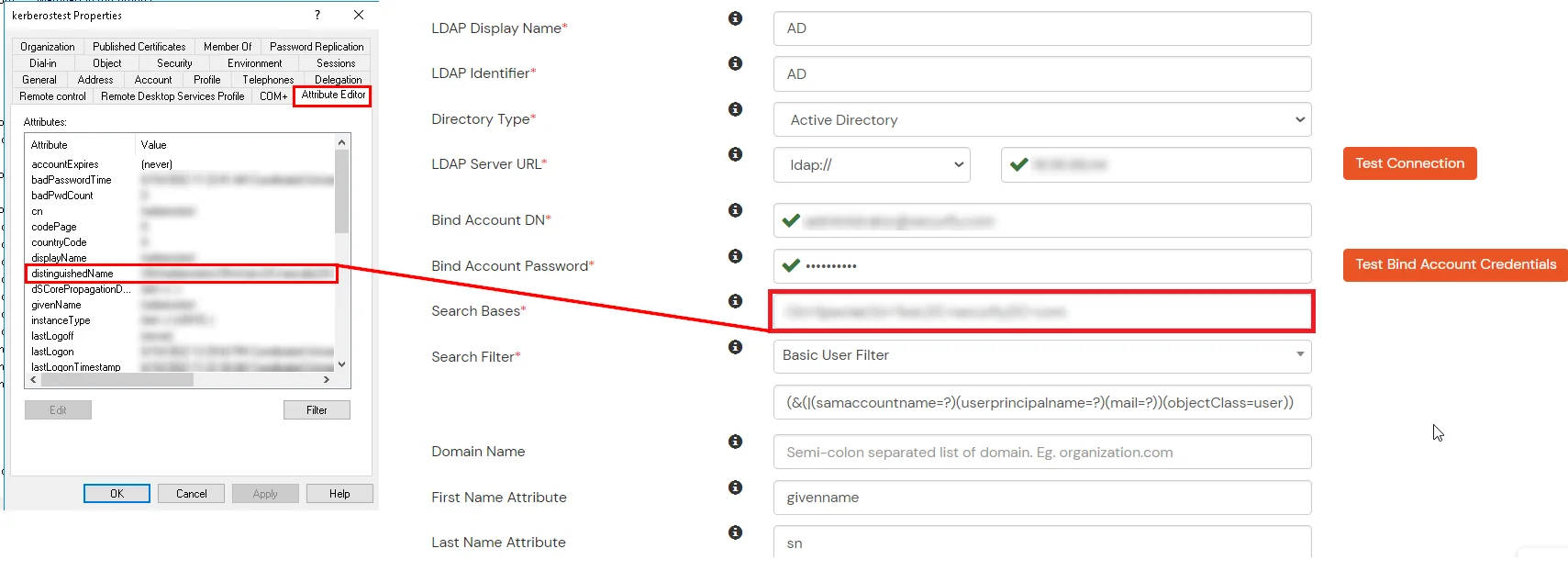
- Search Base is the location in the directory where the search for a user begins. You will get this from the same place you got your Distinguished name.
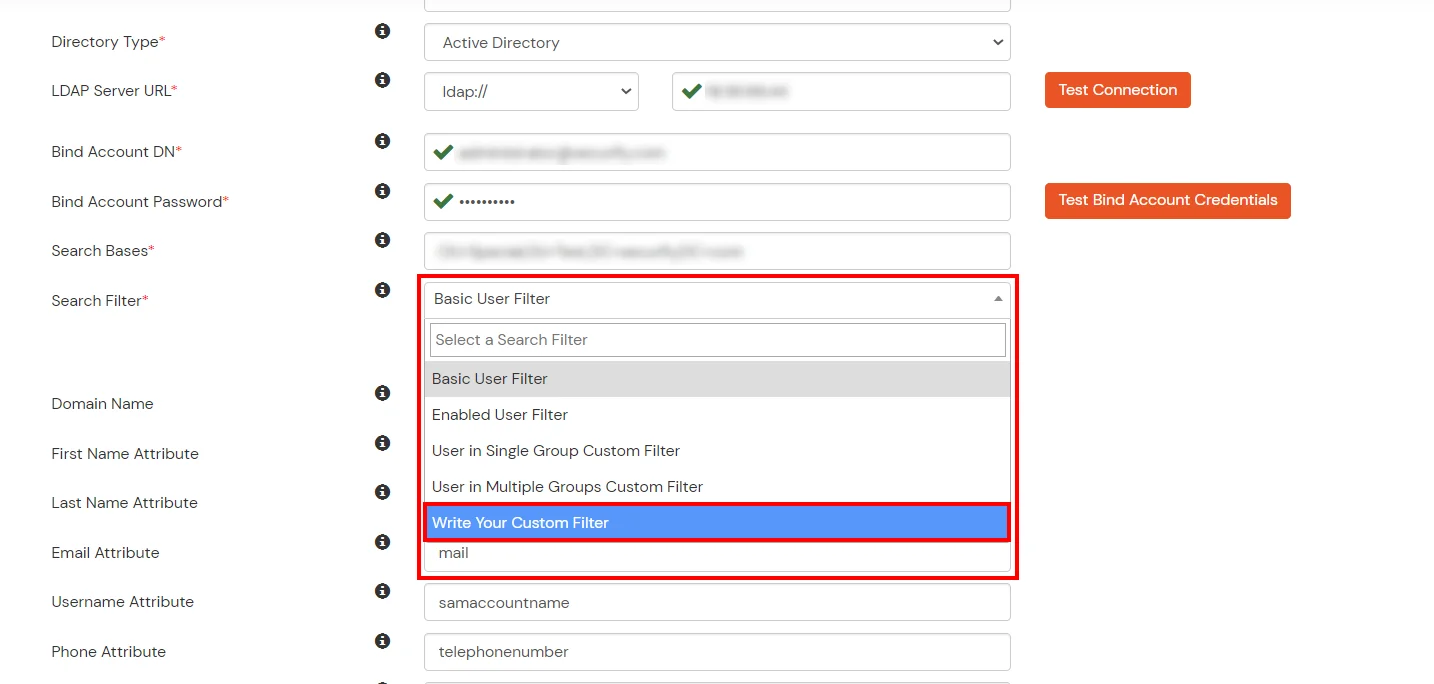
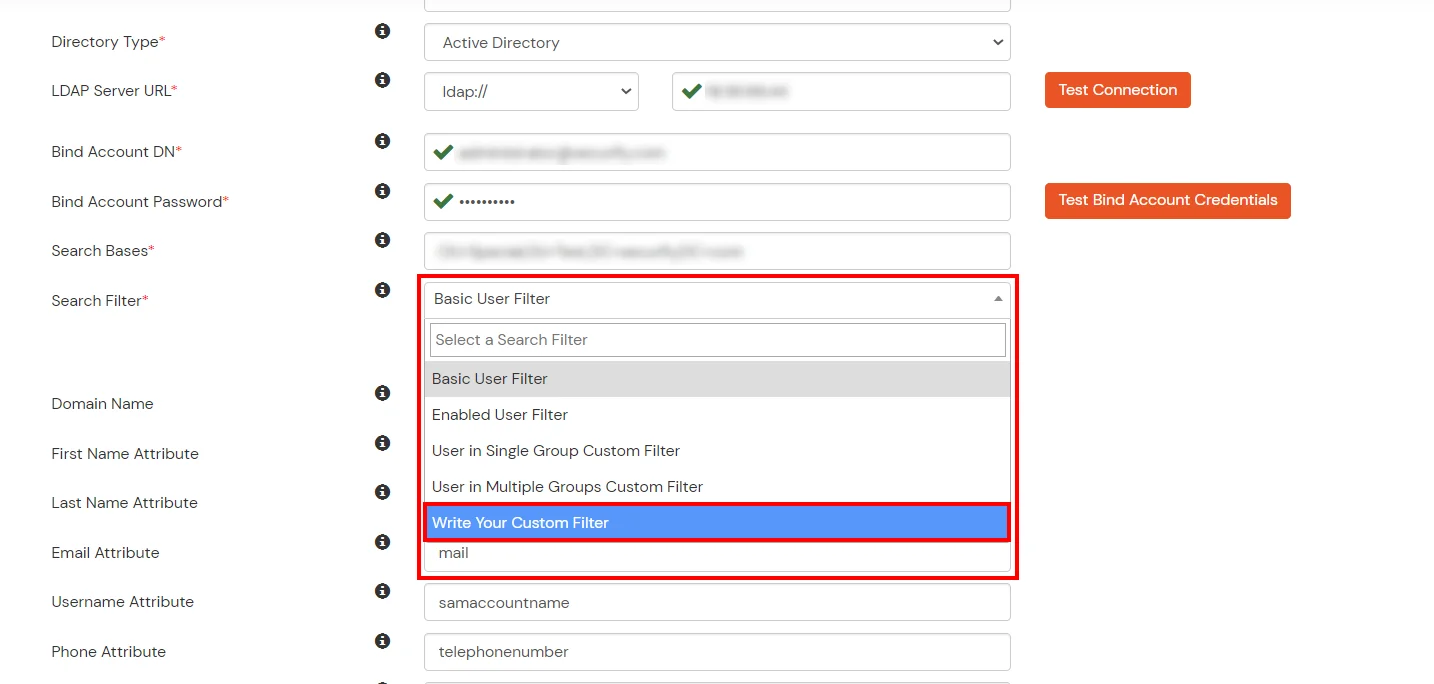
- Select a suitable Search filter from the drop-down menu. If you use User in Single Group Filter or User in Multiple Group Filter, replace the <group-dn> in the search filter with the distinguished name of the group in which your users are present. To use custom Search Filter select "Write your Custom Filter" option and customize it accordingly.
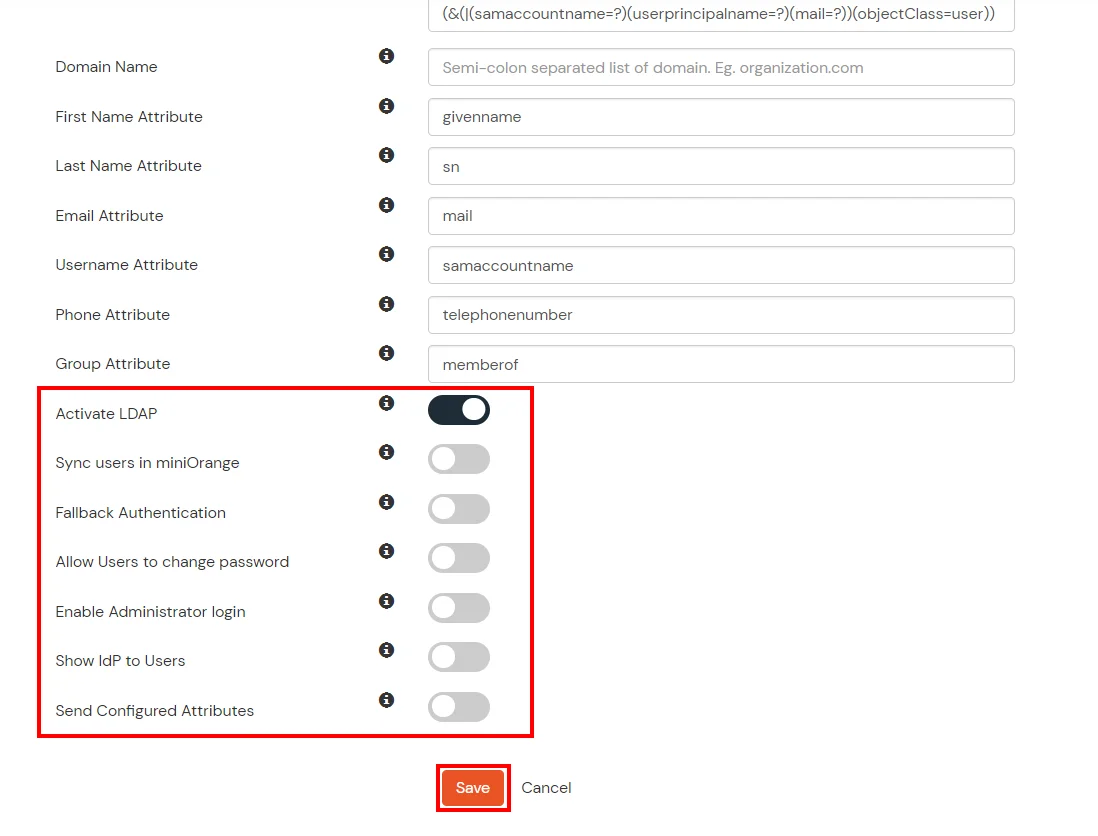
- You can also configure following options while setting up AD. Enable Activate LDAP in order to authenticate users from AD/LDAP. Click on the Save button to add user store.
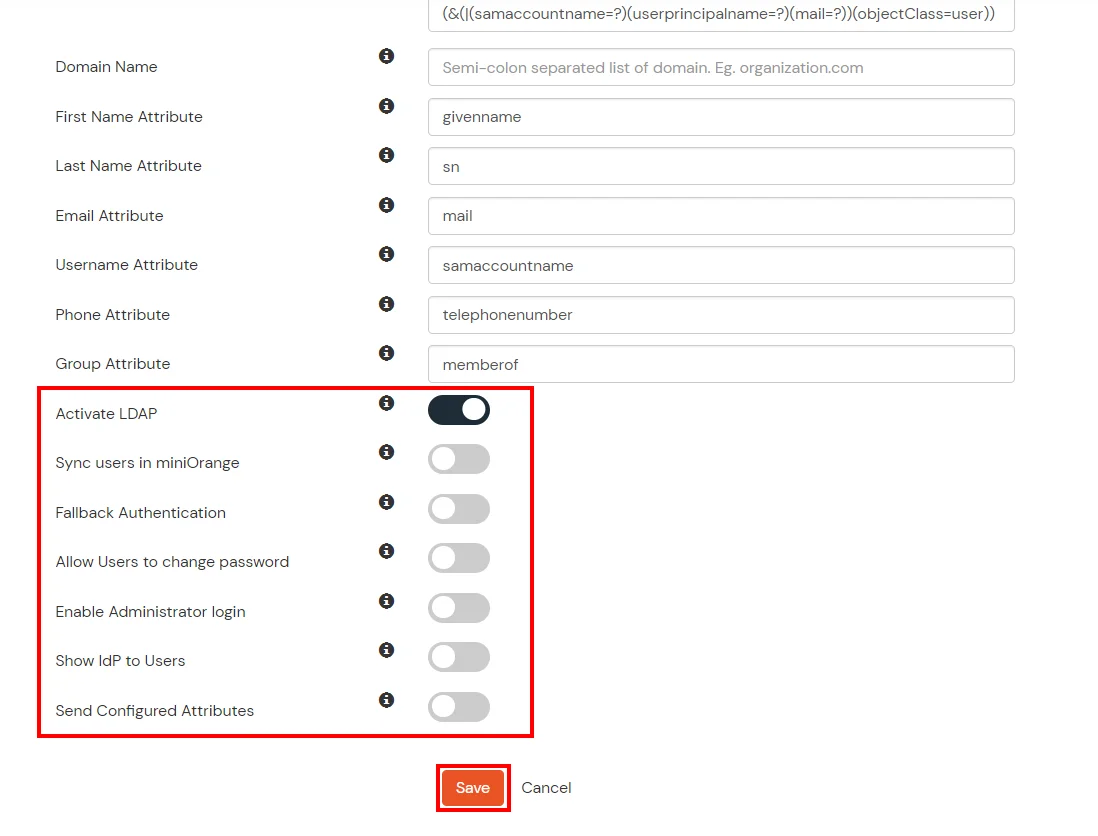
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute |
Description |
| Activate LDAP |
All user authentications will be done with LDAP credentials if you Activate it |
| Sync users in miniOrange |
Users will be created in miniOrange after authentication with LDAP |
| Fallback Authentication |
If LDAP credentials fail then user will be authenticated through miniOrange |
| Allow users to change password |
This allows your users to change their password. It updates the new credentials in your LDAP server |
| Enable administrator login |
On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users |
If you enable this option, this IdP will be visible to users |
| Send Configured Attributes |
If you enable this option, then only the attributes configured below will be sent in attributes at the time of login |
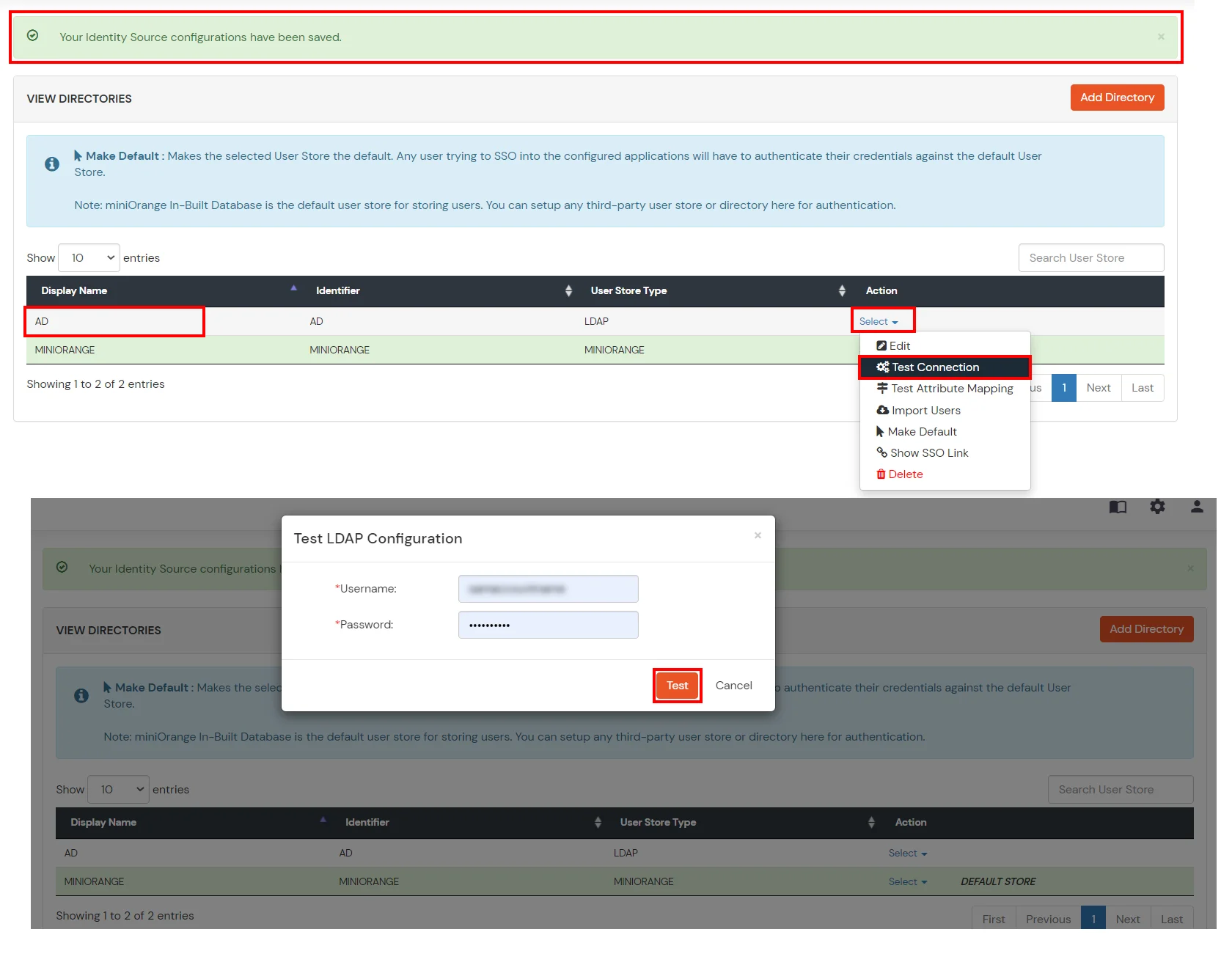
- Click on Save. After this, it will show you the list of User stores. Click on Test Connection to check whether you have enter valid details. For that, it will ask for username and password.
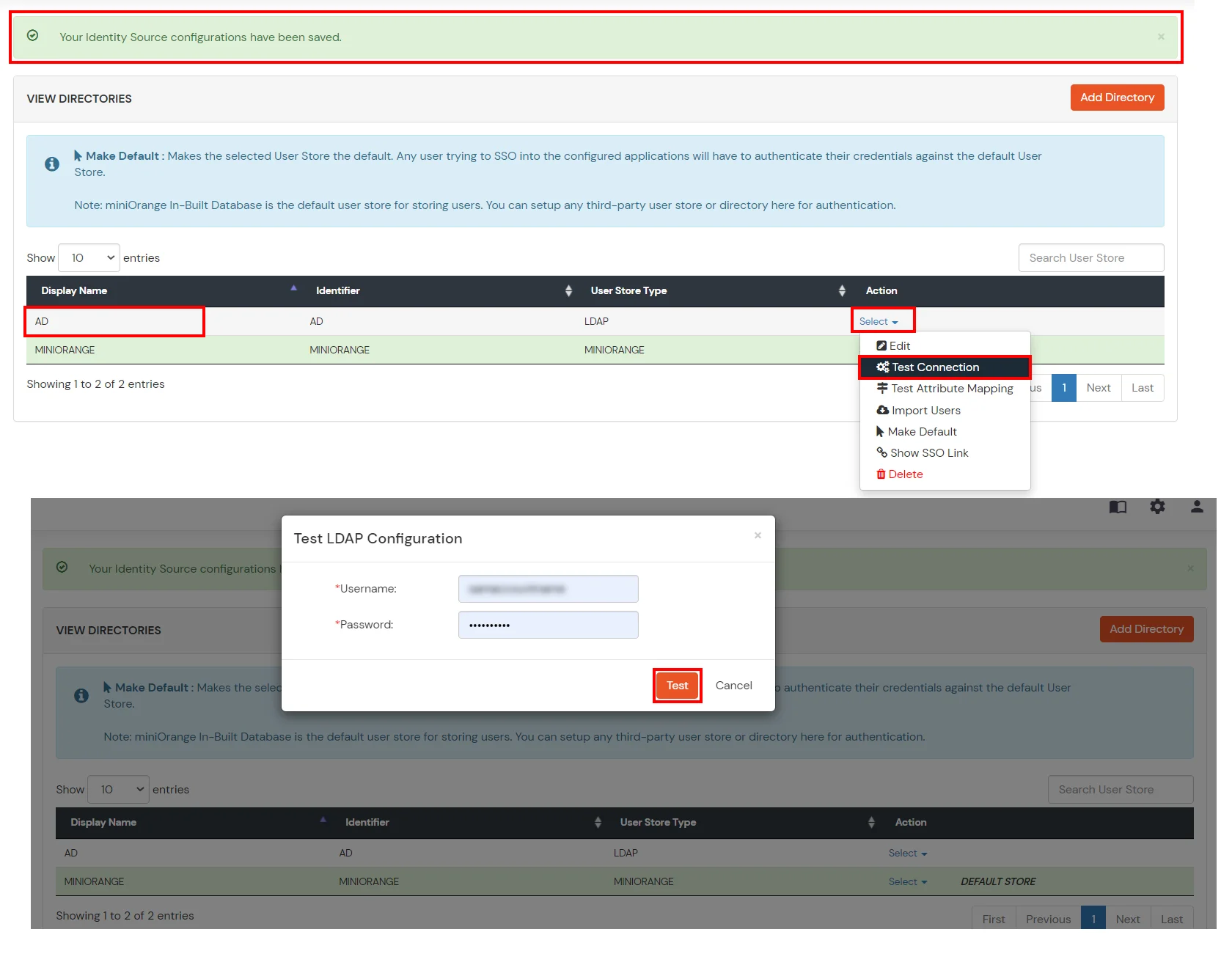
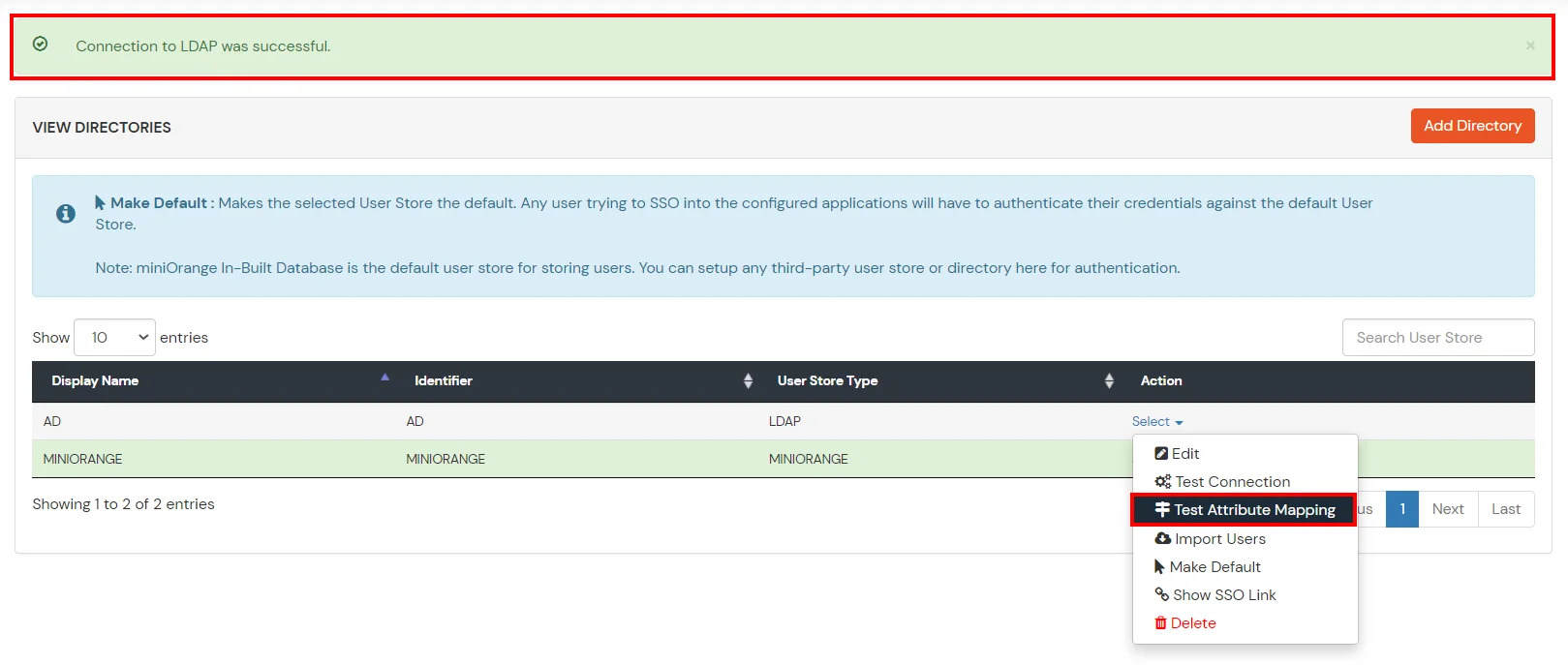
- On Successful connection with LDAP Server, a success message is shown.
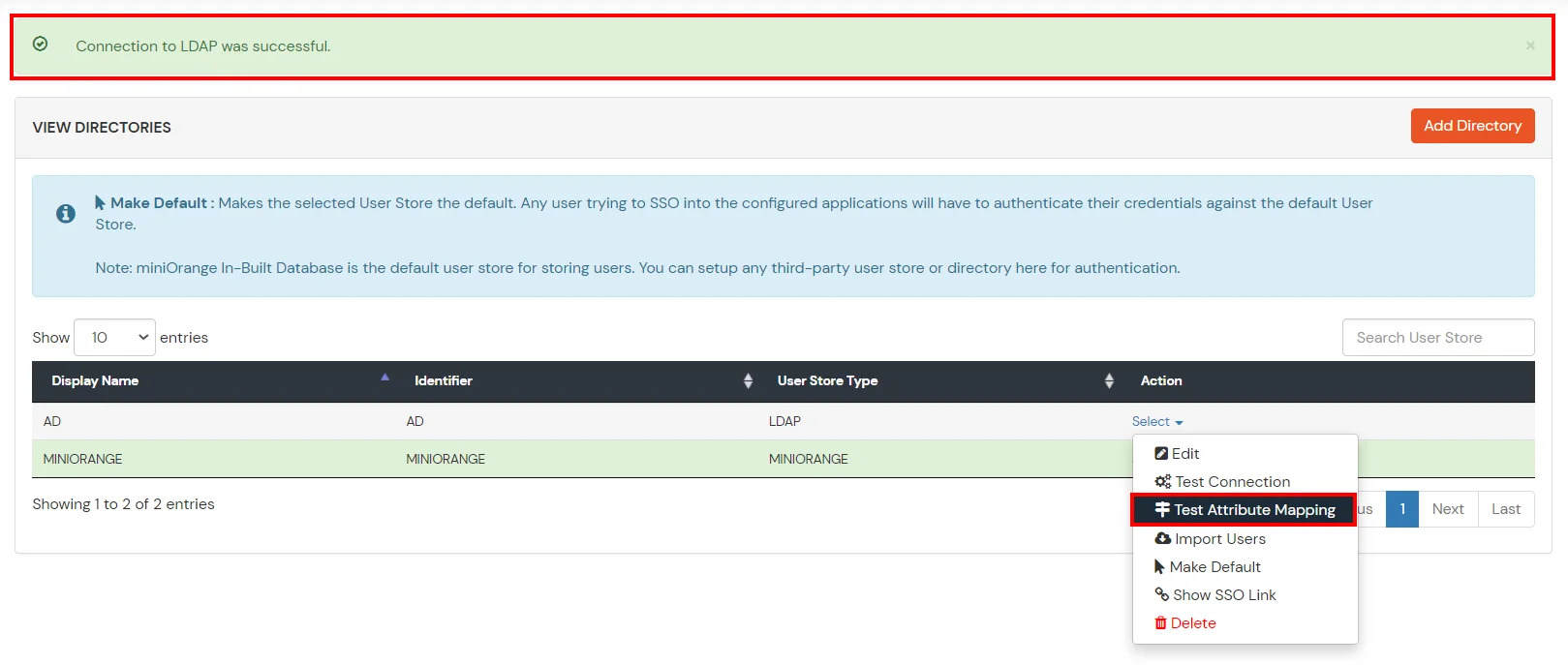
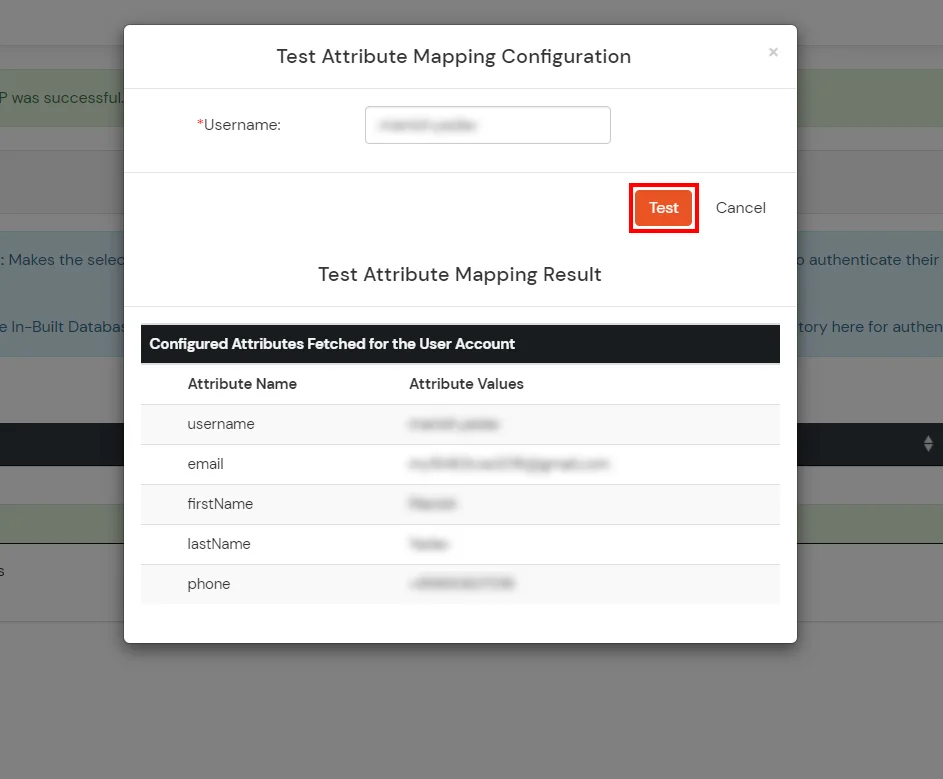
- Click on Test Attribute Mapping.
- Enter a valid Username. Then, click on Test. Mapped Attributes corresponding to the user are fetched.
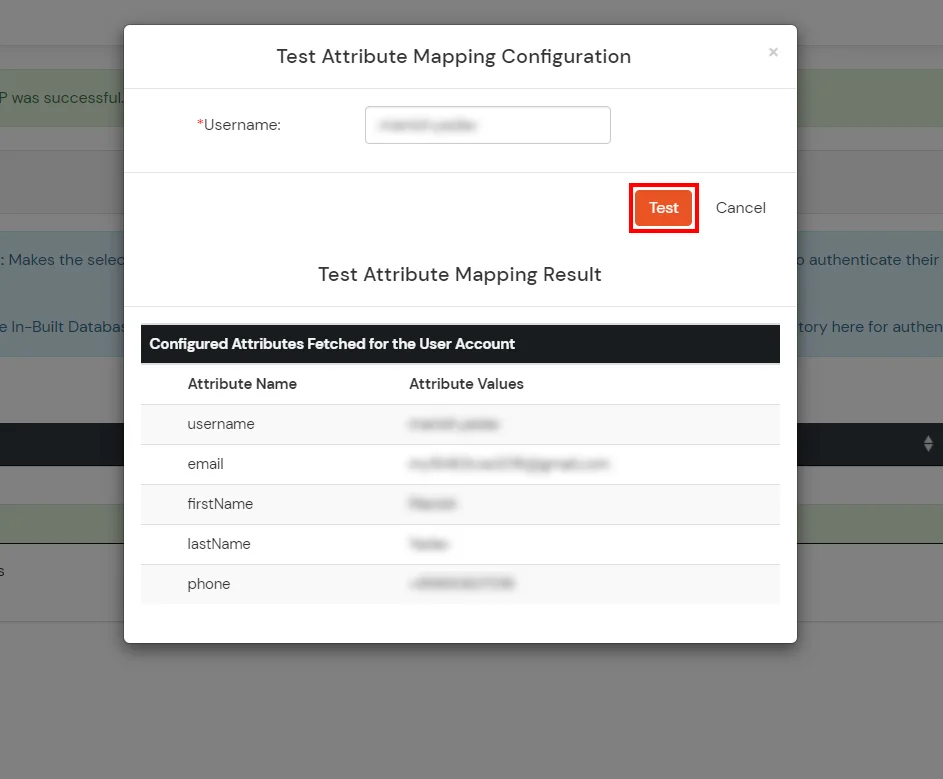
- After successful Attribute Mapping Configuration, go back to the ldap configuration and enable Activate LDAP in order to authenticate users from AD/LDAP.
Refer our guide to setup LDAPS on windows server.
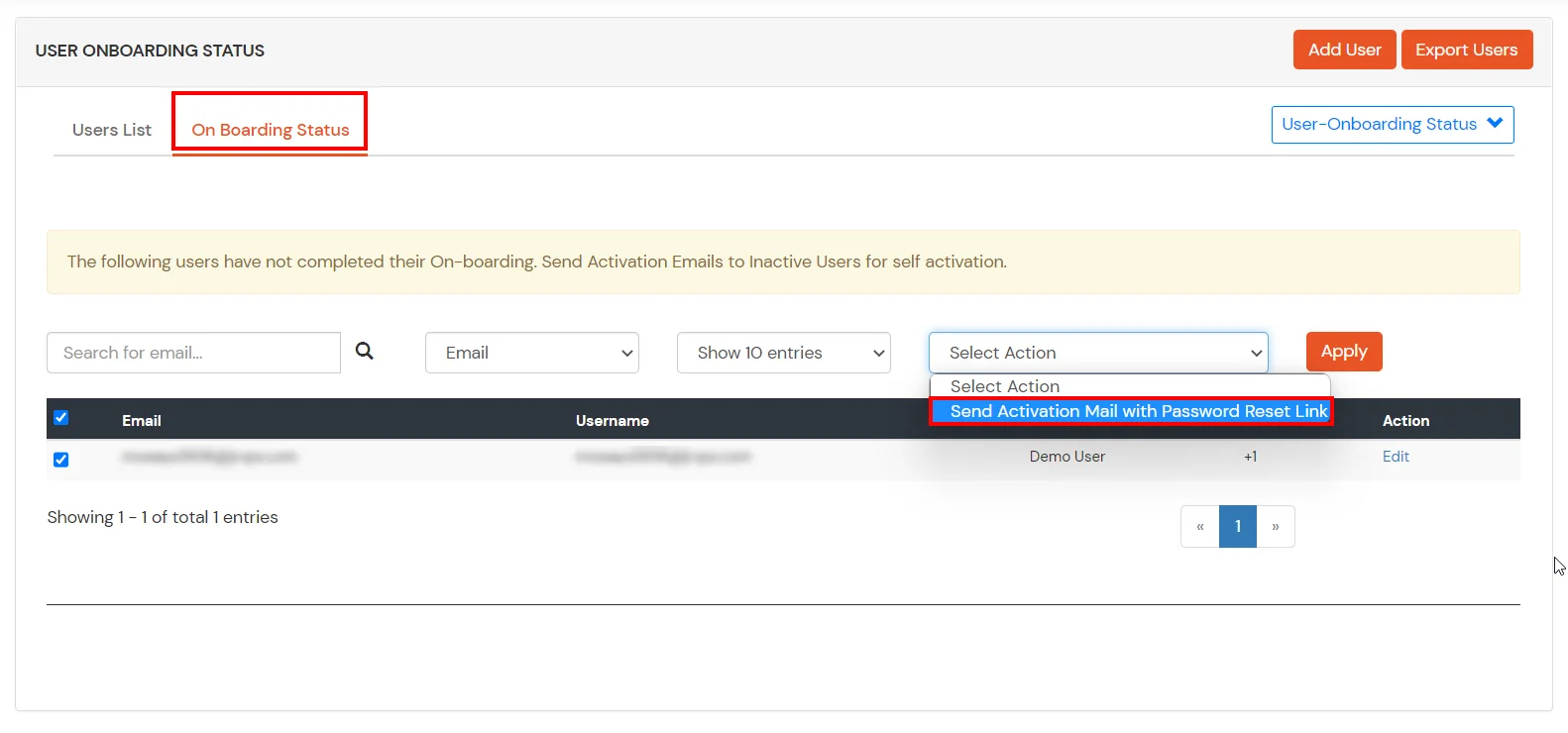
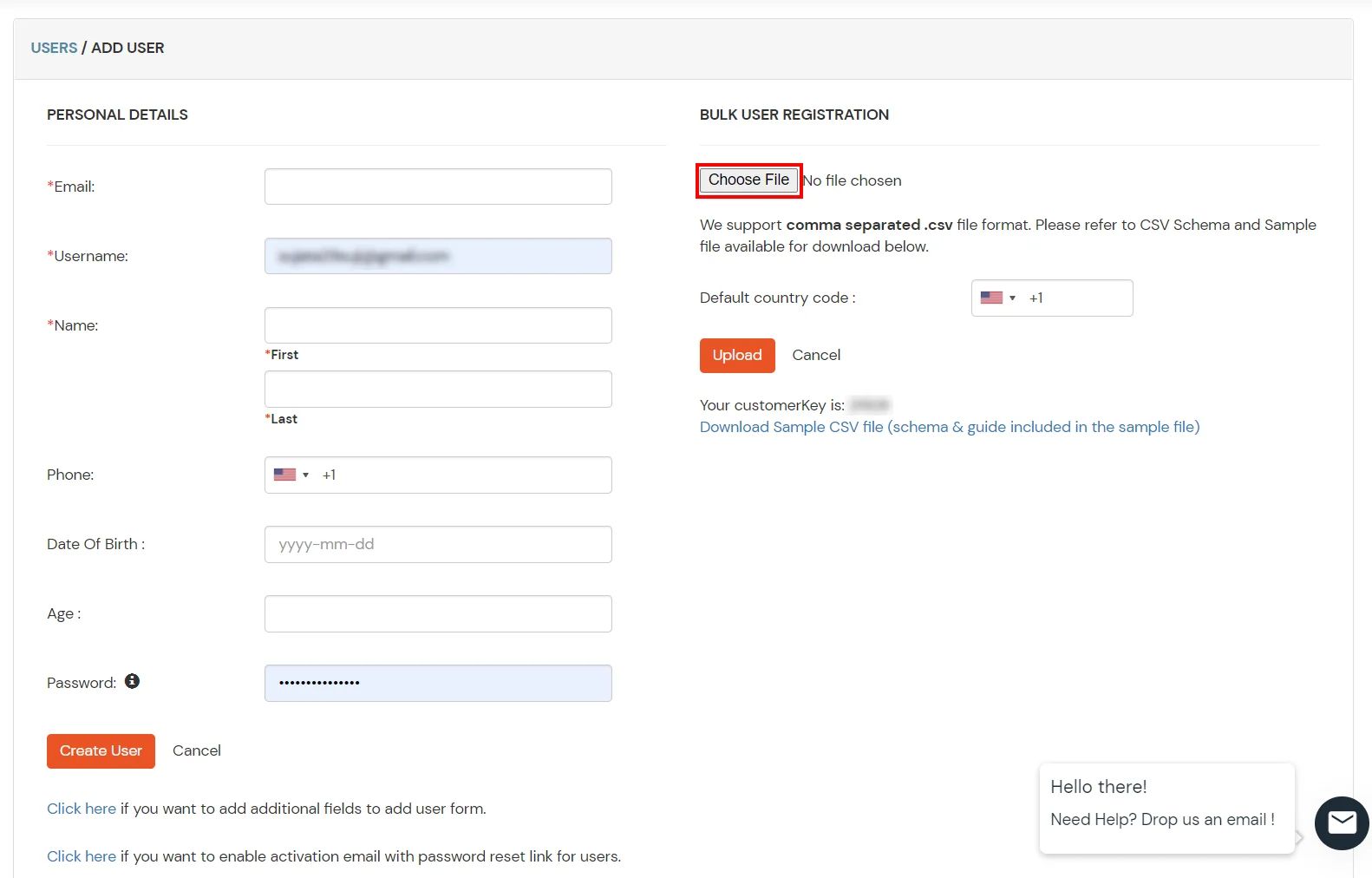
User Import and Provisioning from AD
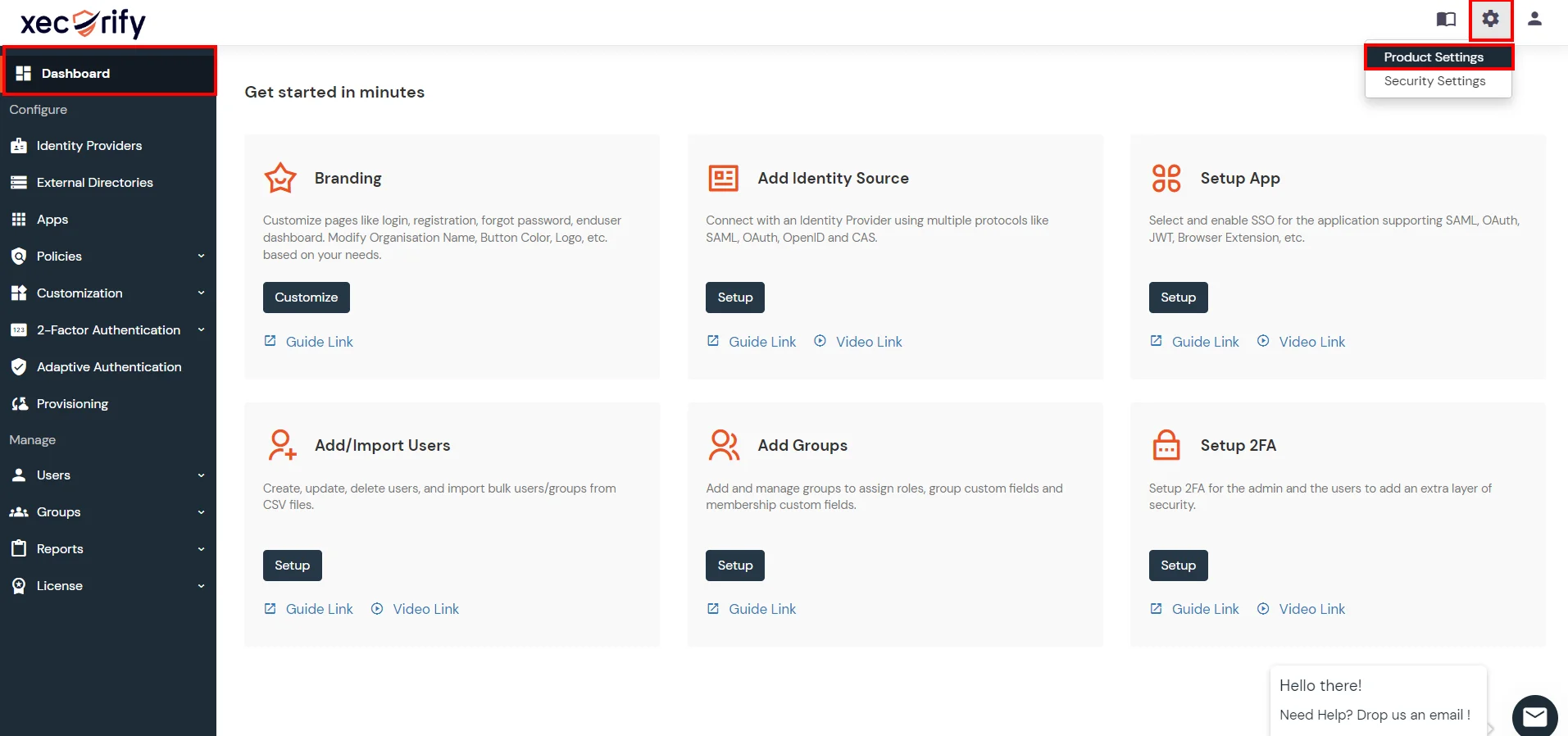
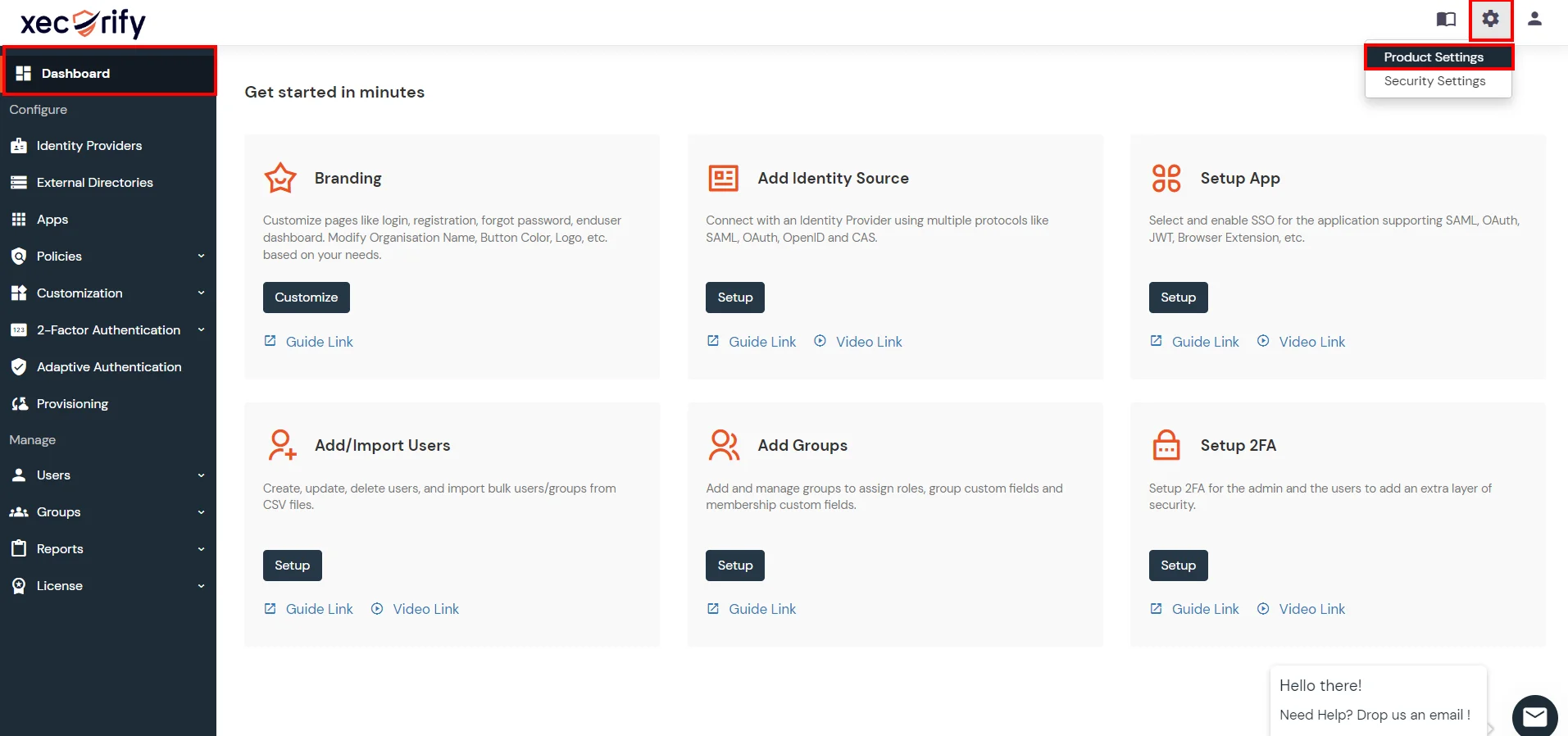
- Go to Settings >> Product Settings in the Customer Admin Account.
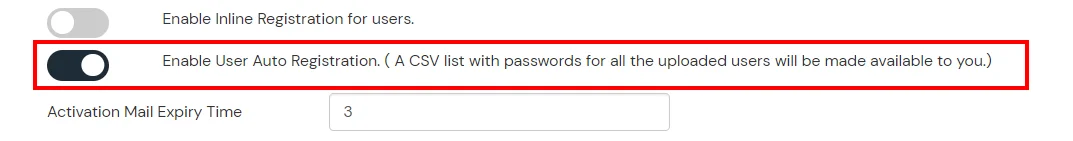
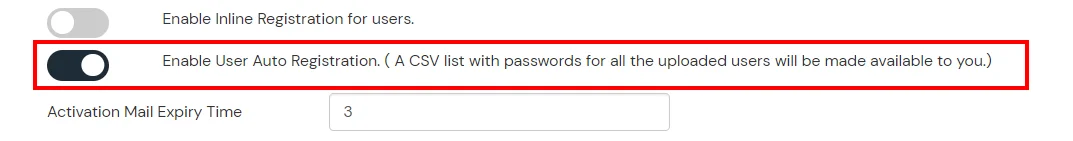
- Enable the "Enable User Auto Registration" option and click Save.
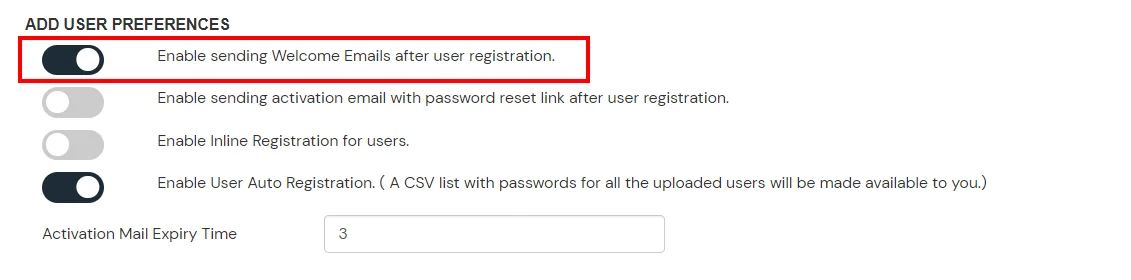
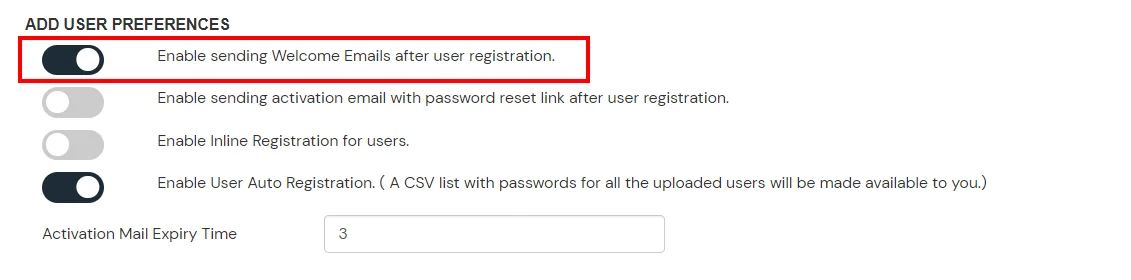
- (Optional) To send a welcome email to all the end users that will be imported, enable the "Enable sending Welcome Emails after user registration" option and click Save.
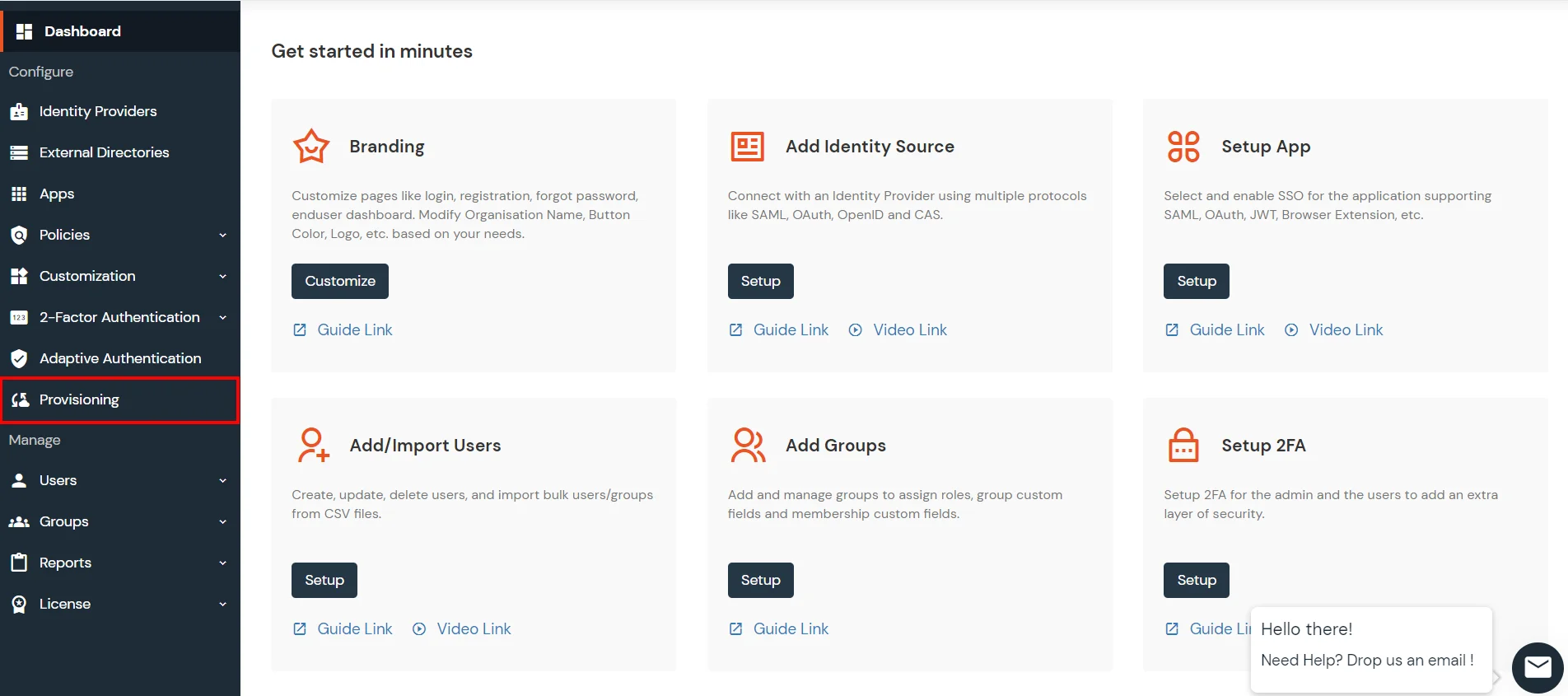
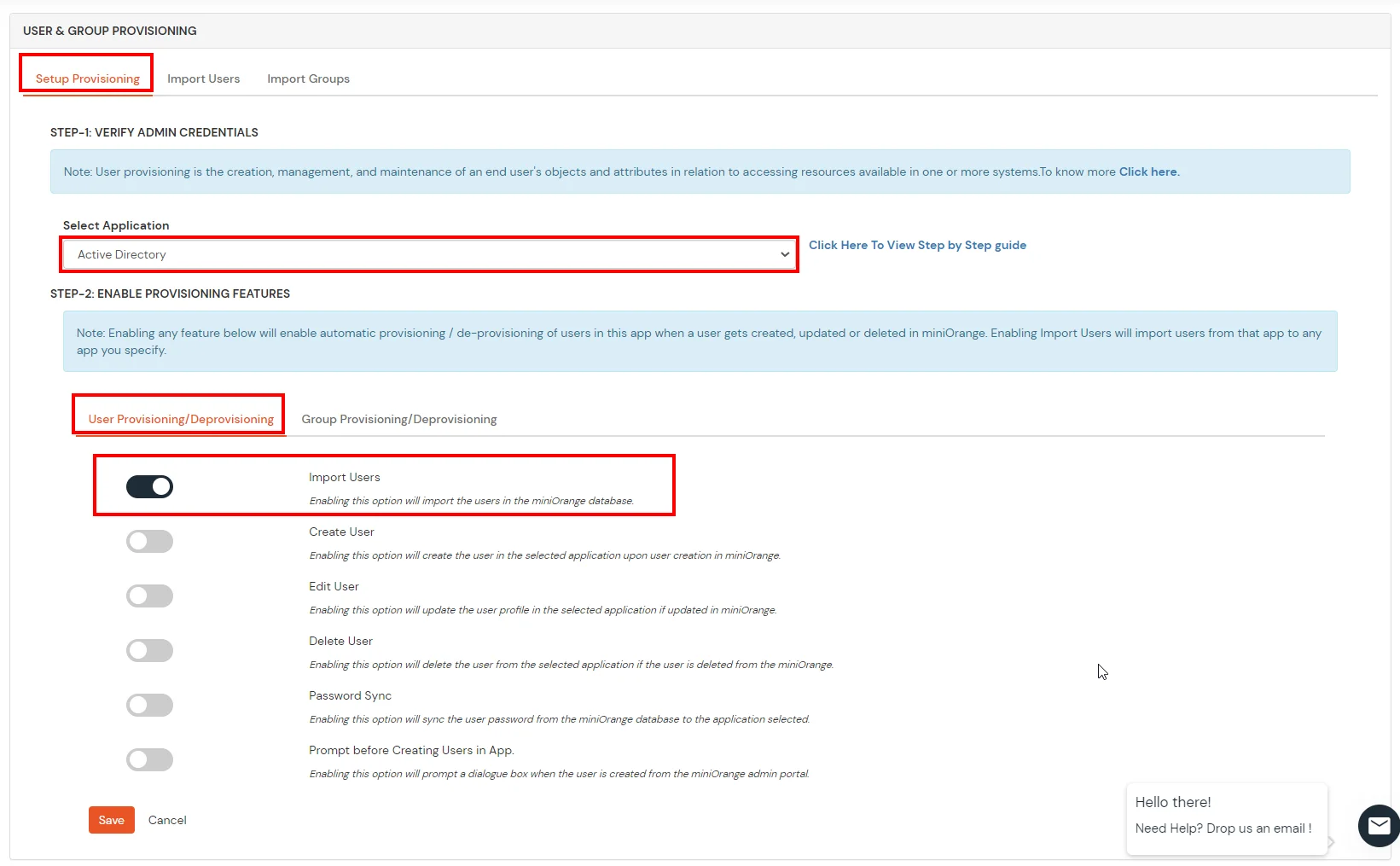
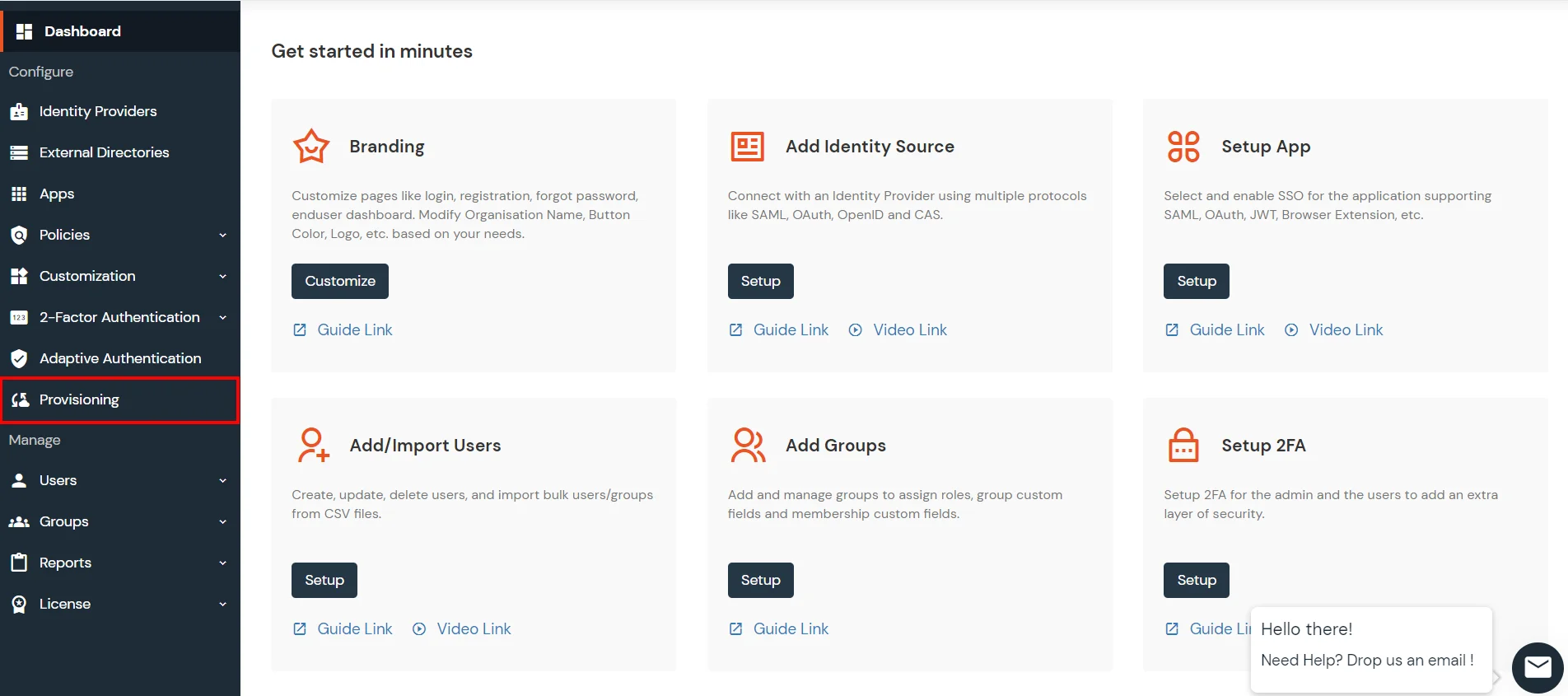
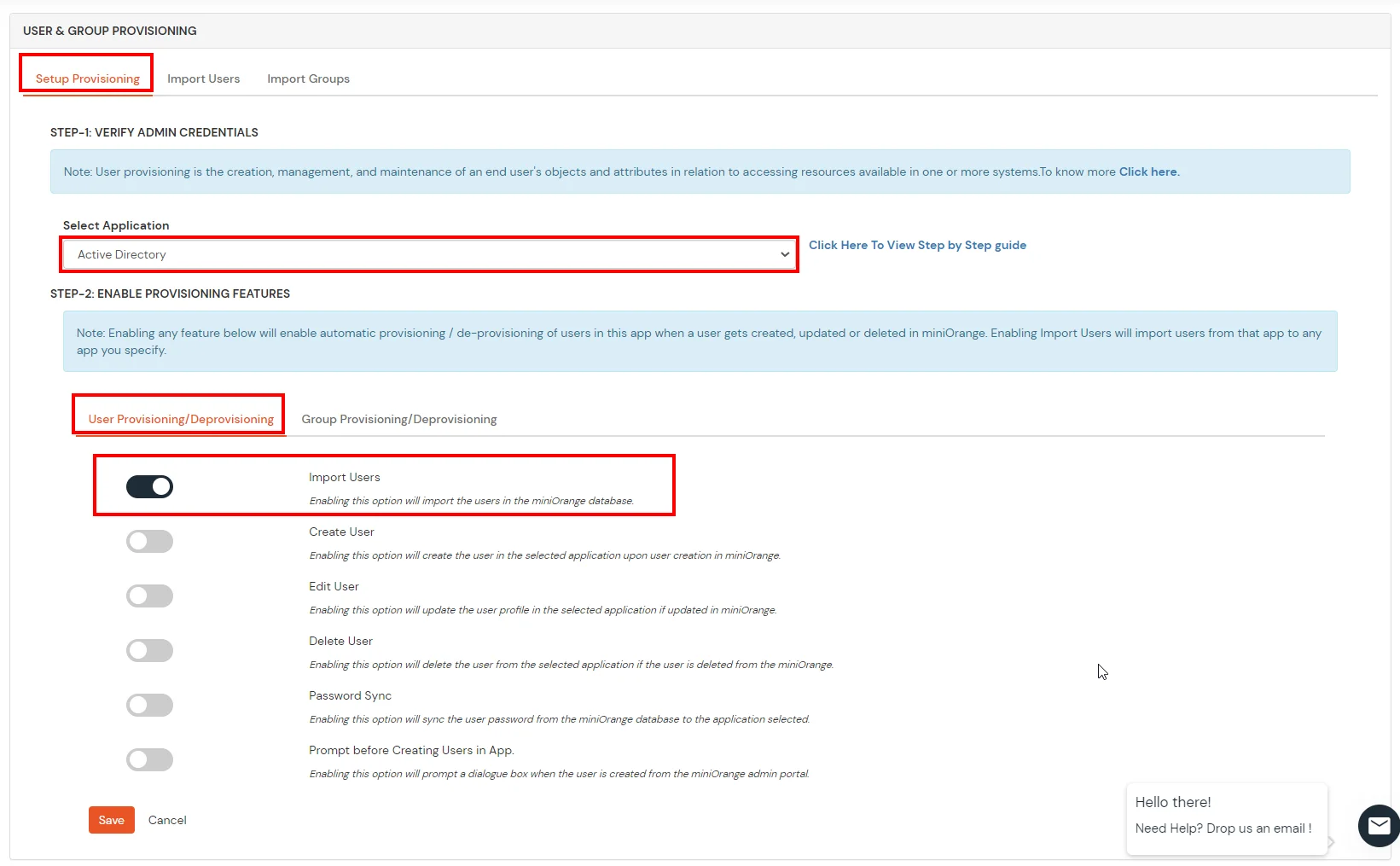
- From the Left-Side menu of the dashboard select Provisioning.
- In Setup Provisioning tab select Active Directory in the Select Application drop-down.
- Toggle the Import Users tab, click on Save button.
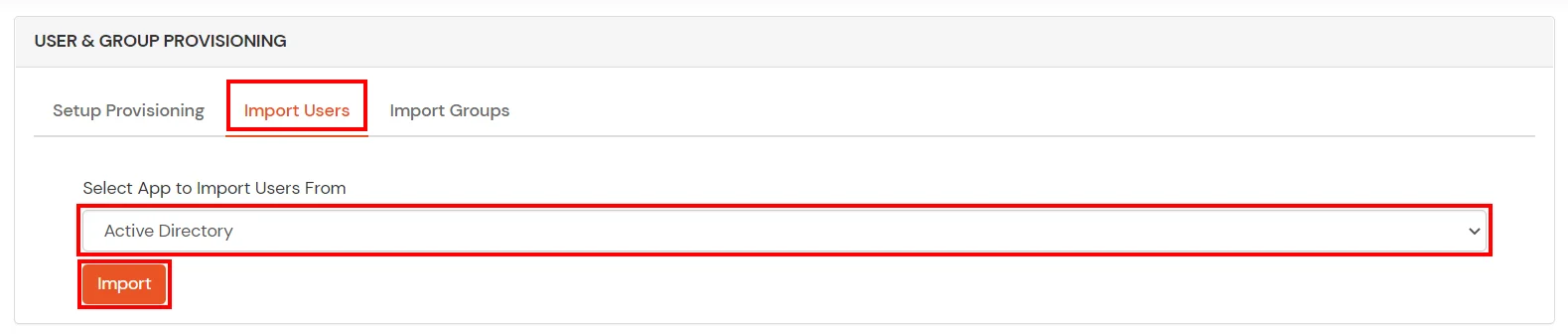
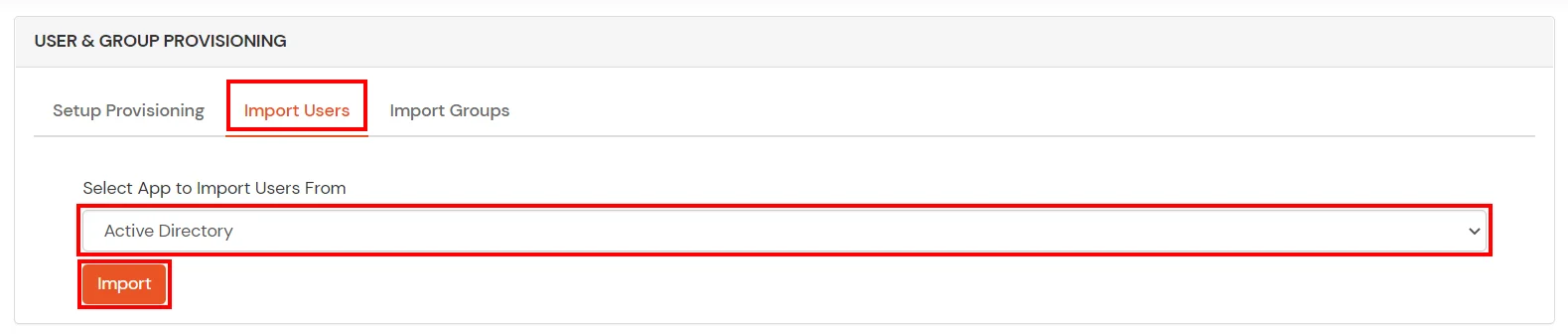
- On the same section, switch to Import Users section.
- Select Active Directory from the dropdown and click on the Import Users tab, to import all the users from Active Directory to miniOrange.
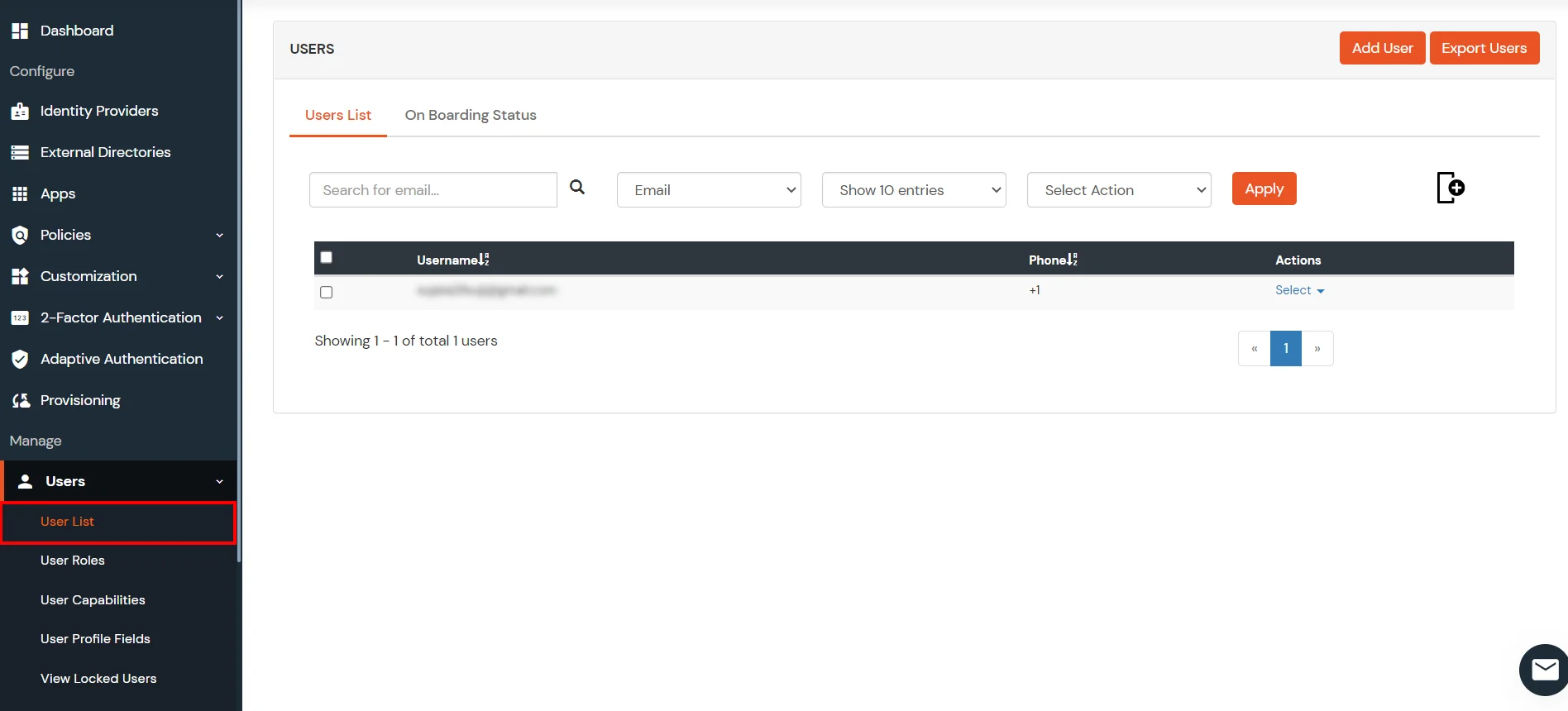
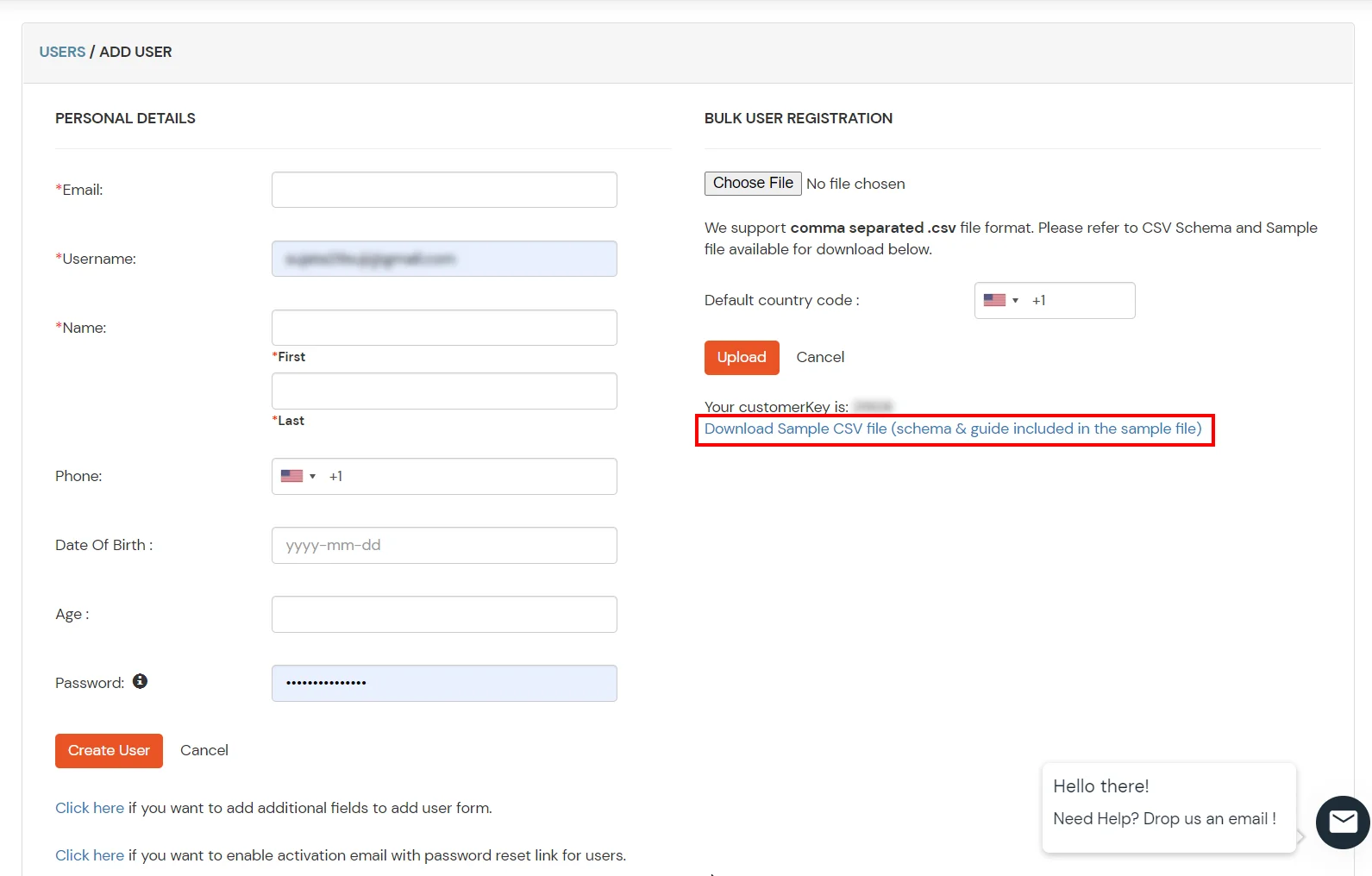
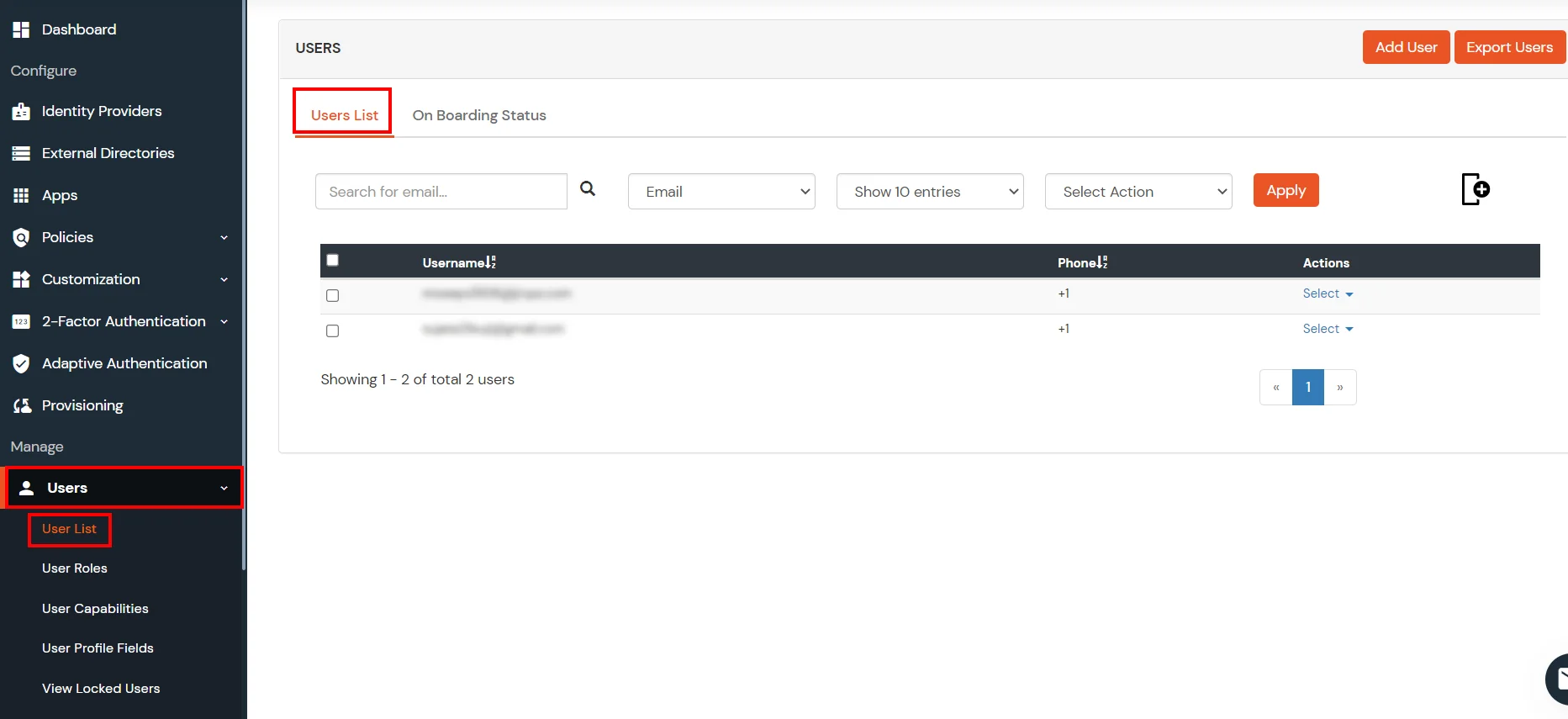
- You can view all the Users you have imports by selecting Users >> User List from Left Panel.
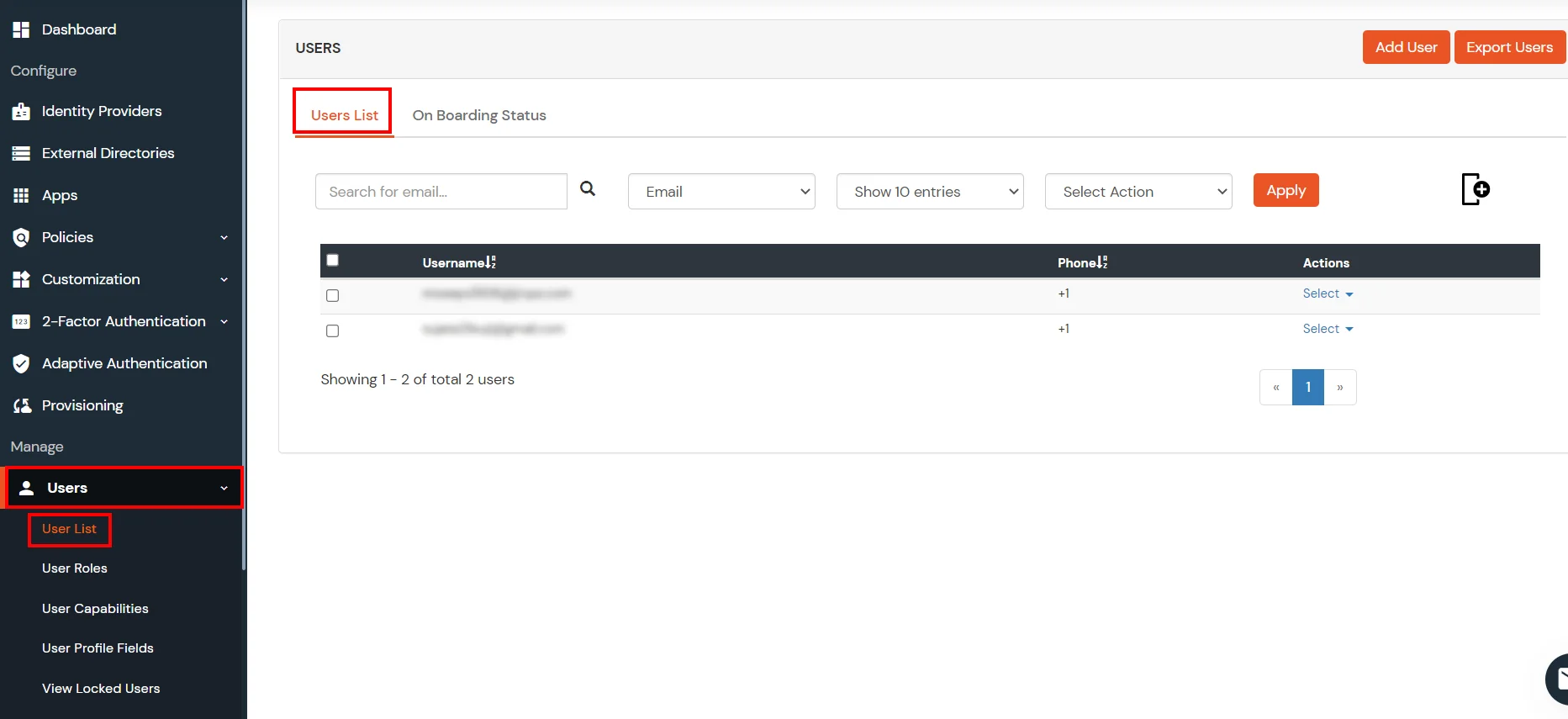
- All the imported users will be auto registered.
- These groups will be helpful in adding multiple 2FA policies on the applications.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
External References