Need Help? We are right here!
Search Results:
×






Saudi Arabia's NCA mandates strict cybersecurity standards for government entities, critical infrastructure operators, and cloud providers. Non-compliance means regulatory penalties, operational restrictions, and reputational damage that can threaten your license to operate in Saudi Arabia.
Meeting these requirements demands strong identity controls, continuous monitoring, and audit-ready documentation across every environment. miniOrange delivers the IAM and PAM capabilities organizations need to close compliance gaps and demonstrate readiness to NCA assessors with confidence.
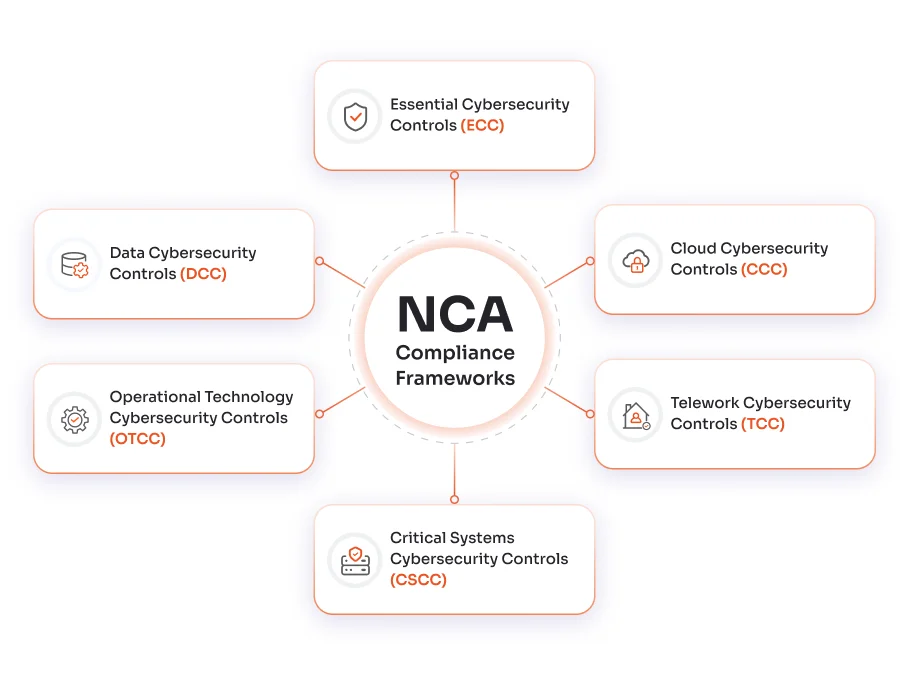
The ECC is the mandatory baseline for all NCA-regulated organizations, covering governance, identity management, network security, event logging, and incident response.
The CCC governs security for cloud service providers and tenants operating in Saudi Arabia, covering multiple domains across network security, backup, monitoring, and incident management.
The TCC secures remote and hybrid work environments by enforcing MFA, secure VPN access, endpoint monitoring, and incident response procedures for distributed workforces.
The CSCC protects high-value government and infrastructure systems, covering technical components, human operators, and supporting documentation, against advanced threats.
The OTCC addresses cybersecurity for industrial control systems and OT environments, focusing on OT/IT segmentation, device hardening, access control, and OT-specific incident response.
The DCC governs data protection across its full lifecycle, including classification, encryption, secure disposal, and access governance, for government and critical infrastructure organizations.
| NCA Control Area | miniOrange Solution | Applicable Framework |
|---|---|---|
| Multi-Factor Authentication (MFA) | Adaptive MFA supporting 15+ authentication methods, including TOTP, push, and hardware tokens | ECC, CCC, TCC, CSCC |
| Single Sign-On (SSO) | SAML/OIDC-based SSO with centralized access governance and full audit trails | ECC, CCC, TCC |
| Role-Based Access Control | RBAC/ABAC enforcing least-privilege access across applications and infrastructure | ECC, CSCC, DCC |
| Privileged Access Management (PAM) | Session recording, just-in-time access, and privileged account vaulting | ECC, CSCC, OTCC |
| Secure Remote Access | VPN-less zero-trust access with continuous identity verification for remote users | TCC, ECC |
| User Lifecycle Management | HR-integrated automated provisioning and deprovisioning tied to role changes | ECC, DCC, CSCC |
| Access Certification | Scheduled access review campaigns with one-click approval or revocation workflows | ECC, DCC |
| Third-Party Access Control | Secure external identity federation with scoped access controls for vendors and partners | ECC, CCC |
| Directory Integration | Unified identity sync across Azure AD, LDAP, Active Directory, and HR systems | ECC, CCC, TCC |
Ministries, authorities, and government-affiliated entities
Entities linked to public sector operations
Private organizations in sectors such as energy, water, healthcare, finance, and telecom
Organizations providing cloud services to the Saudi government or critical sector clients
Entities with employees accessing regulated or sensitive data remotely
Sectors with operational technology environments, such as utilities and manufacturing
Pre-built integrations with 6,000+ applications, Azure AD, LDAP, and OT environments enable fast, low-disruption deployment, reducing time-to-compliance.
Deploy miniOrange in your own environment or on the miniOrange cloud, fully supporting data residency requirements for Saudi government and critical sector organizations.
Trusted by leading government and enterprise organizations across Saudi Arabia, miniOrange has experience supporting complex IAM requirements in regulated environments
Built-in compliance dashboards and exportable access reports give your team the audit evidence needed for NCA assessments, without manual effort.
Our compliance specialists work alongside your team to map miniOrange controls to your specific NCA framework obligations and support you through every assessment cycle.
Identify which NCA frameworks apply to your organization based on sector, data type, technology environment, and operational model.
Assess current controls against NCA requirements. Prioritize gaps by risk exposure, with IAM, logging, and incident response as the highest-scrutiny areas.
Establish board-level cybersecurity oversight, assign CISO-level NCA compliance ownership, and align policies to NCA framework language.
Deploy IAM, PAM, access reviews, and SIEM coverage across cloud, remote, and OT environments. miniOrange addresses the IAM layer across all NCA frameworks.
Build your audit trail. Conduct an internal or third-party assessment to validate compliance before formal NCA submission.
Maintain controls through scheduled access reviews, quarterly vulnerability scans, annual policy updates, and regular incident response exercises.
miniOrange helps Saudi-based organizations implement the identity and access controls required across all NCA frameworks, with rapid deployment, on-premise options, and dedicated compliance support.
Years of Experience
Customers Worldwide
Customer Support
Cost Saved