Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
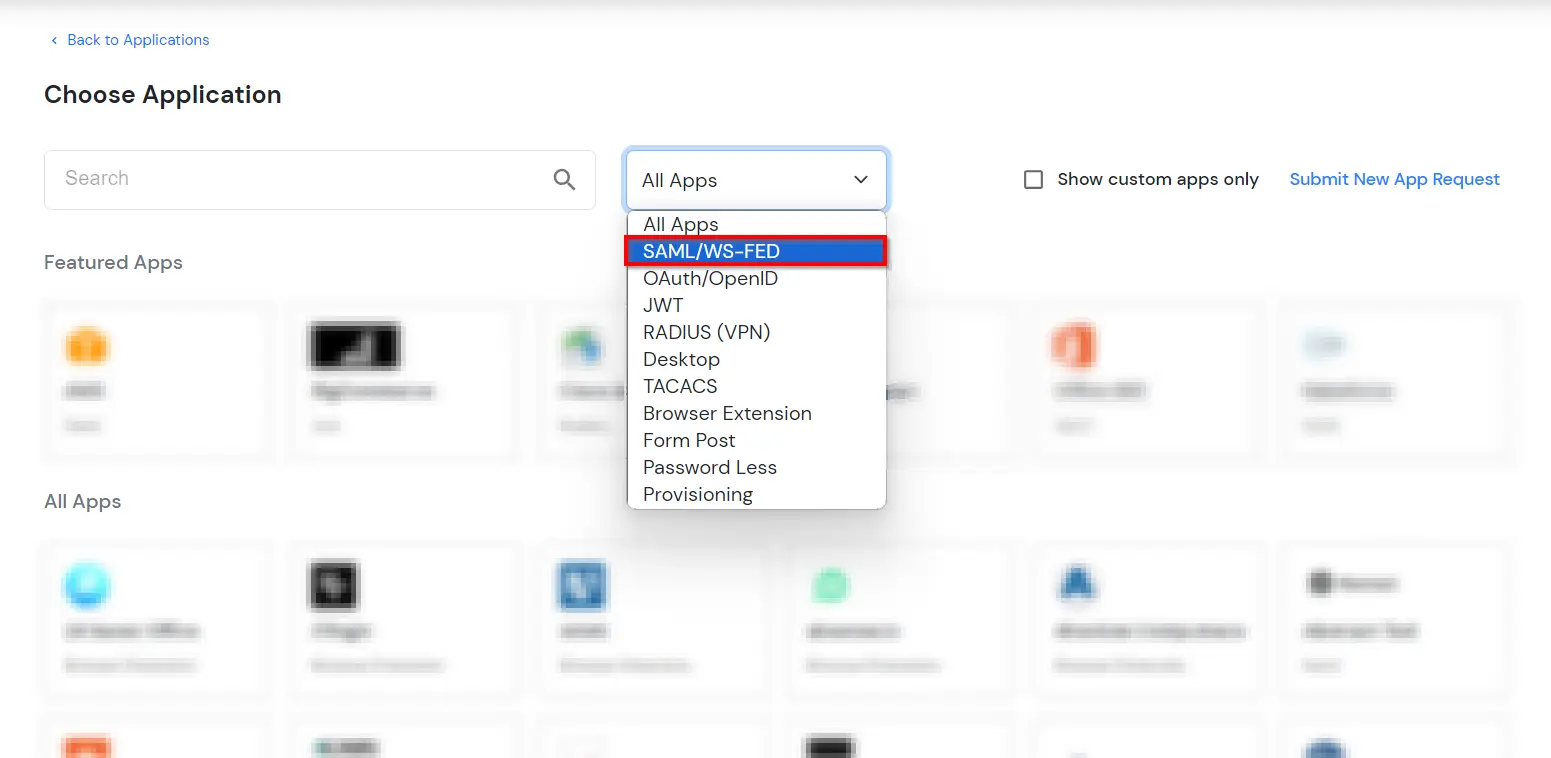
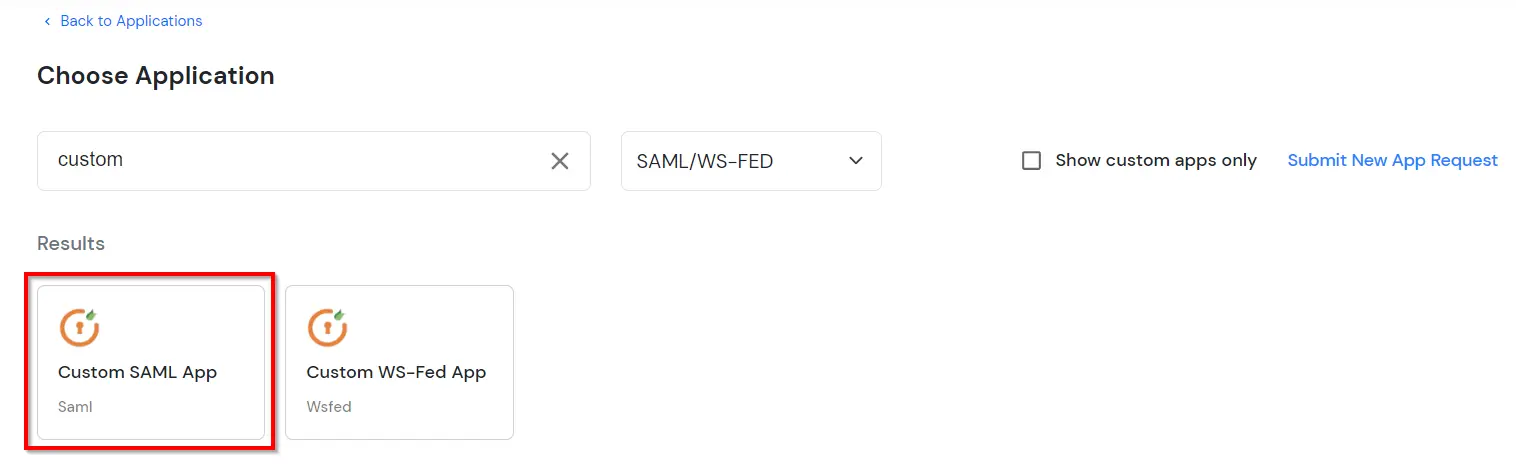
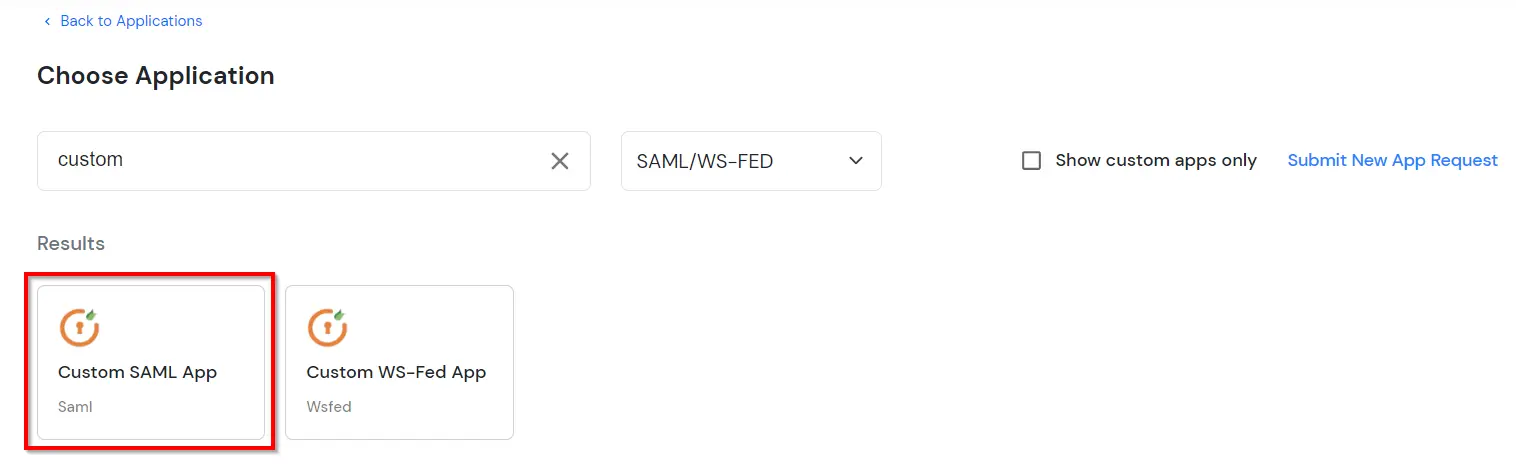
×FortiClient Single Sign-On (SSO) by miniOrange gives you secure single sign-on to on-premises and cloud applications with one set of credentials—including FortiClient VPN and related Fortinet services. With miniOrange as the SAML Identity Provider (IdP), users sign in through miniOrange (or through your linked directory) instead of managing separate Fortinet-only passwords. If your users already live in a third-party identity provider (Microsoft Entra ID, Okta, Auth0, and others), you can keep using those credentials for FortiClient and Fortinet access.
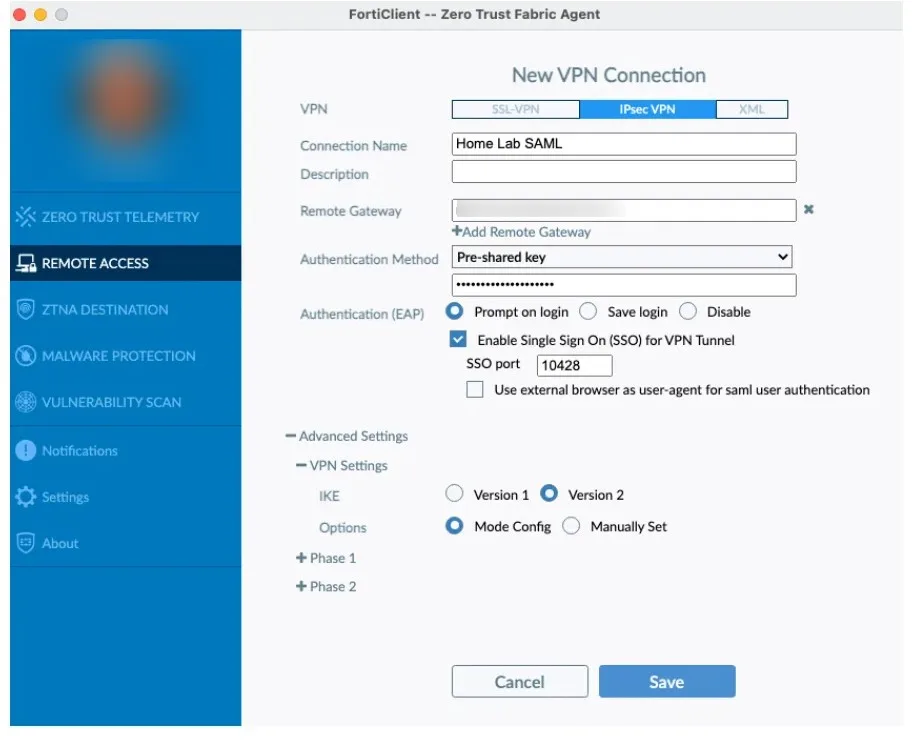
Scope: Steps 1–2 configure miniOrange as SAML IdP toward FortiAuthenticator (or equivalent SP metadata). For IPsec VPN with IKE-SAML (SAML during IKEv2 EAP), you also configure SAML on FortiGate, bind the IKE-SAML listener to your WAN, create user groups and an IKEv2 tunnel, and point FortiClient at that VPN—see Steps 3–7 below. If you only need Security Fabric or SSL VPN SAML without IPsec IKE-SAML, follow your FortiOS version guide and use the steps that apply to your deployment.
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.

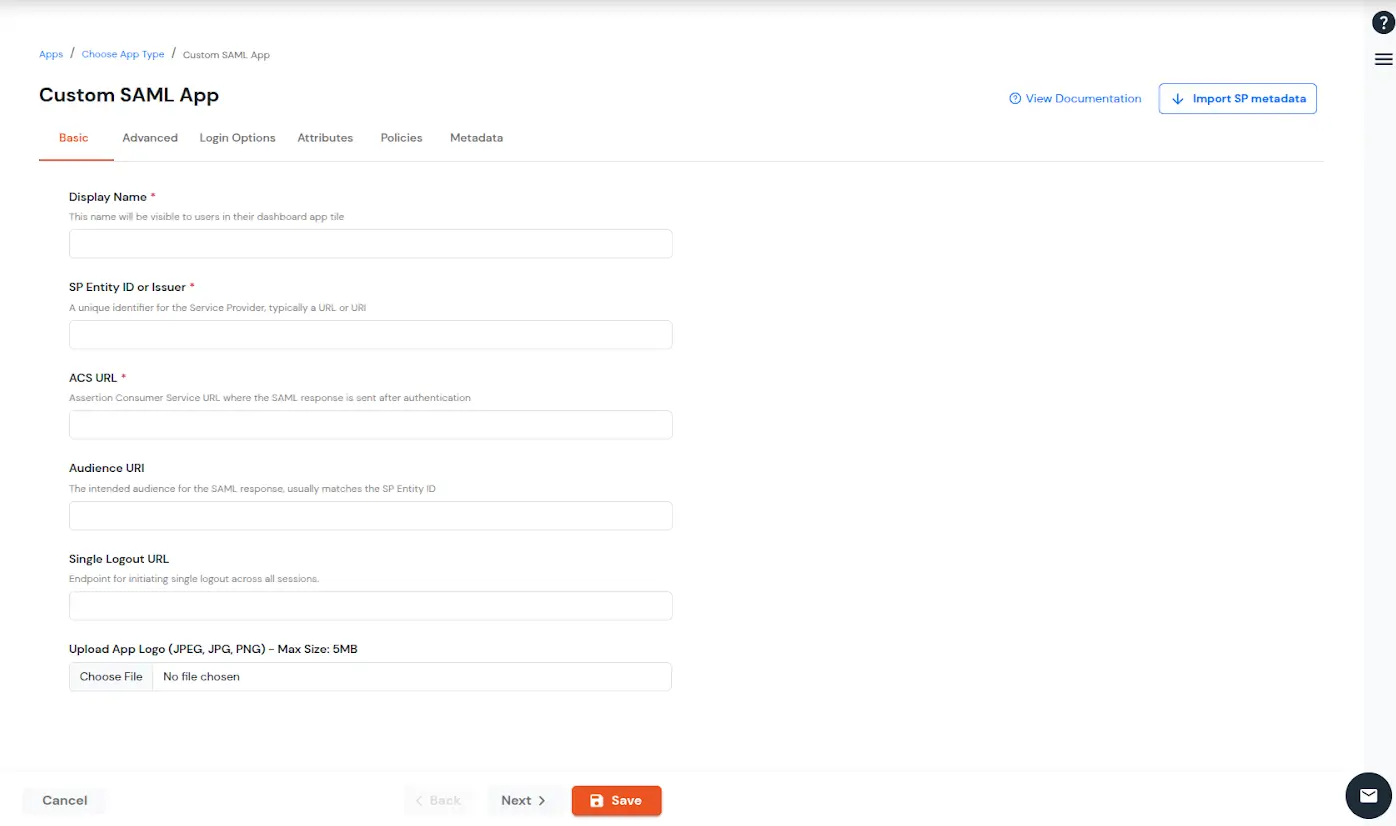
| SP Entity ID | SP Entity ID or Issuer from the Prerequisites. |
| Assertion Consumer Service | ACS URL from Prerequisites. |
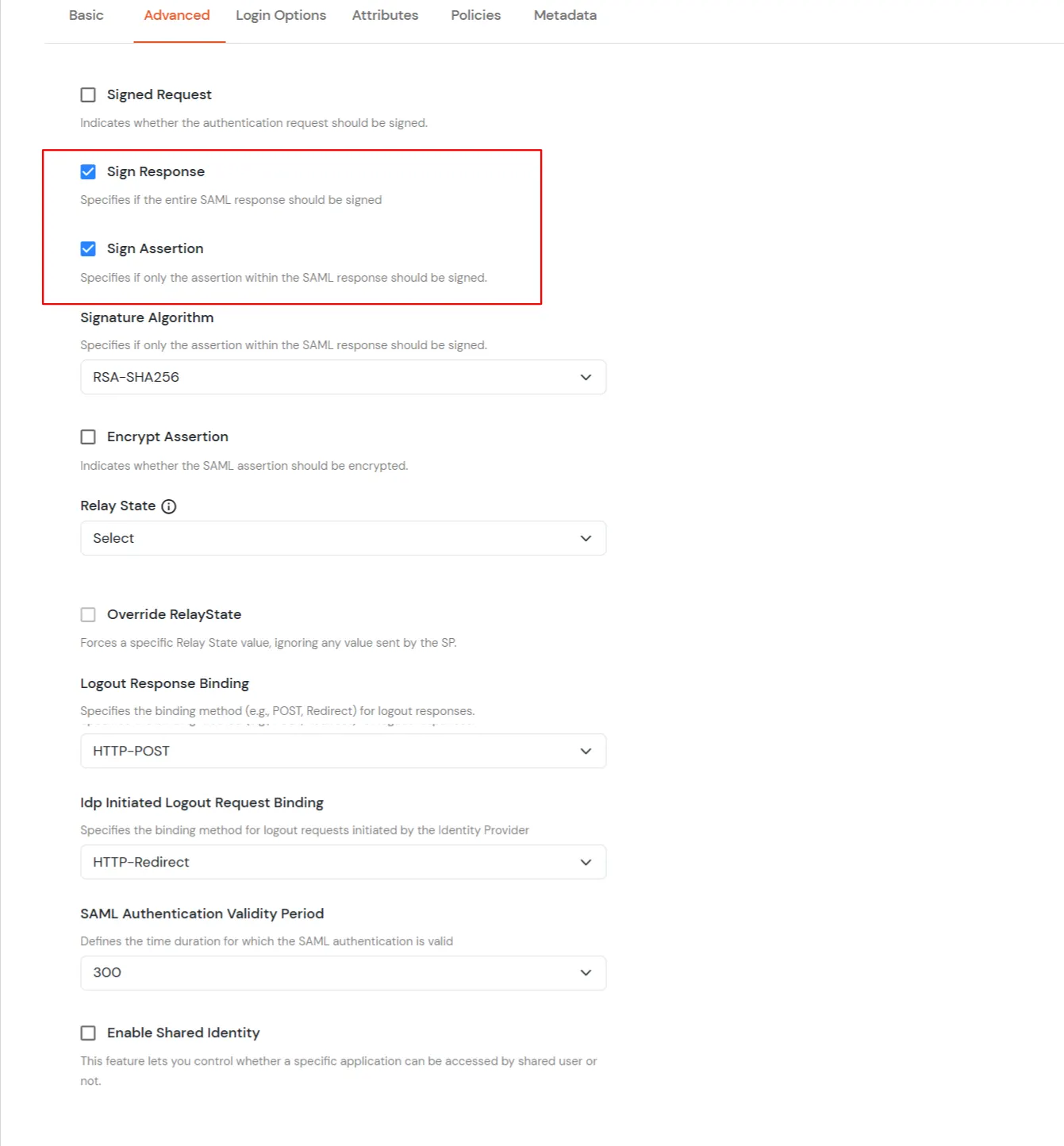
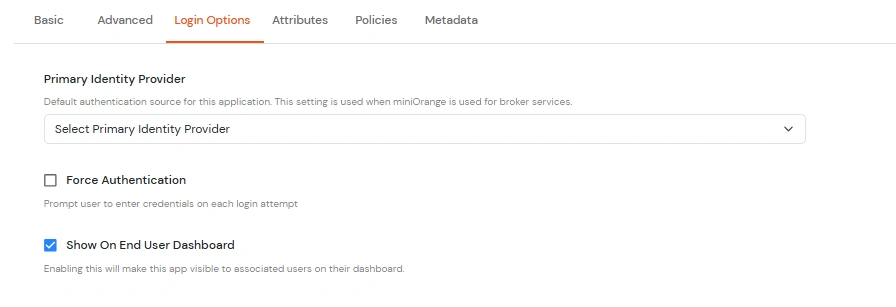
| Primary Identity Provider | Select the identity source from where you want the authentication to happen. You will see the list of all configured sources. |
| Force Authentication | Enable this to enforce authentication on each request to access the application. |
| Show On End User Dashboard | Disable this if you do not want the app to be visible for all users on end user dashboard. |
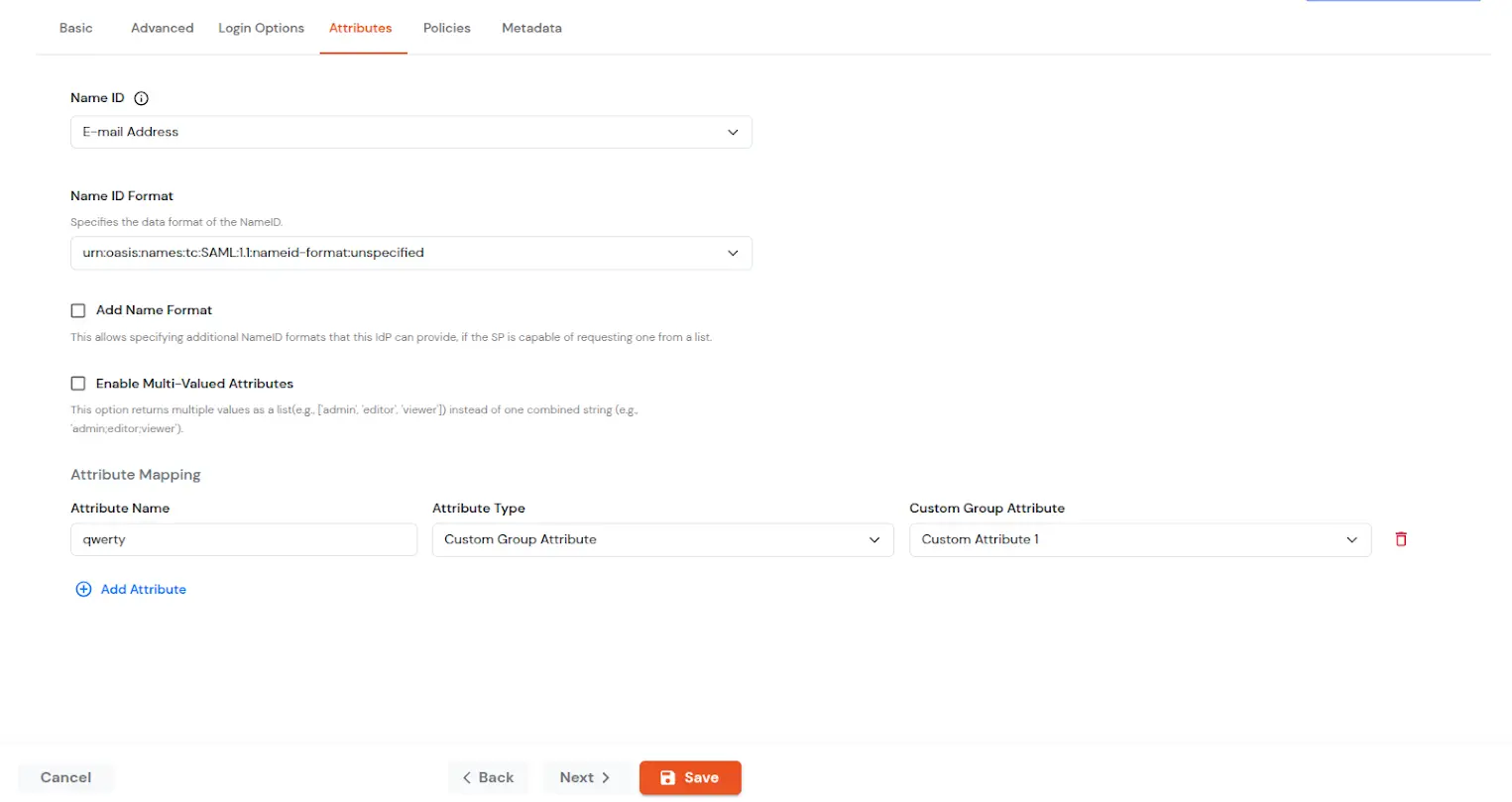
| NameID | NameID is the unique identifier for the authenticated user included in the SAML assertion. It allows the Service Provider to recognize and map the user to an account. Generally, NameID is a username or Email Address. |
| NameID format | Defines what type of identifier is used in the NameID (e.g., email, persistent, transient) so the SP can correctly map the user. If the SP does not request a specific format, the IdP can leave it unspecified and use a default. |
| Add Name Format | Name Format defines how attribute names are represented in a SAML assertion (e.g., as simple strings or URIs). It helps the SP correctly interpret attribute naming and ensures consistency between IdP and SP. |
| Enable Multi-Valued Attributes | Enabled: Commas (,) and semicolons (;) are treated as separators, so the attribute is split into a clean list. Example: roles = ['admin', 'editor', 'viewer']. Disabled: Commas and semicolons are not treated as separators, so the attribute stays as one combined string. Example: roles = "admin;editor;viewer". |
| Attribute Mapping | You can Add Attributes to be sent in SAML Assertion to SP. The attributes include user’s profile attributes such as first name, last name, full name, username, email, custom profile attributes, and user groups, etc. |
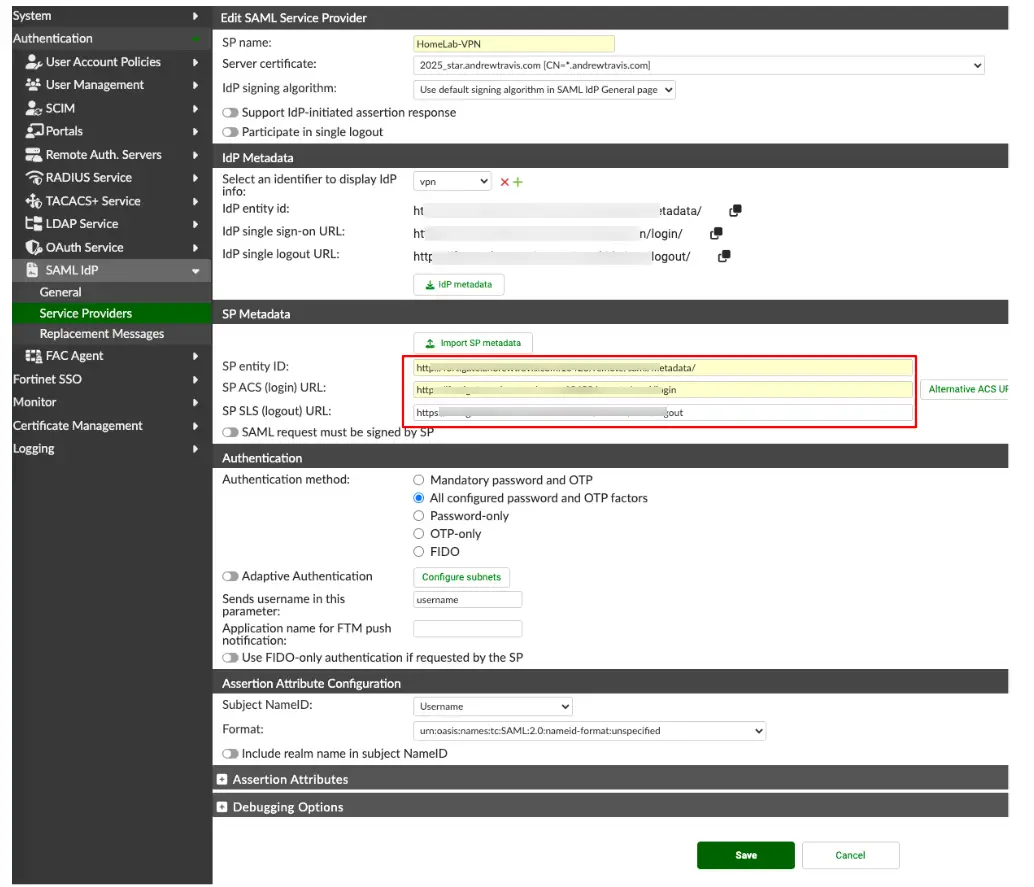
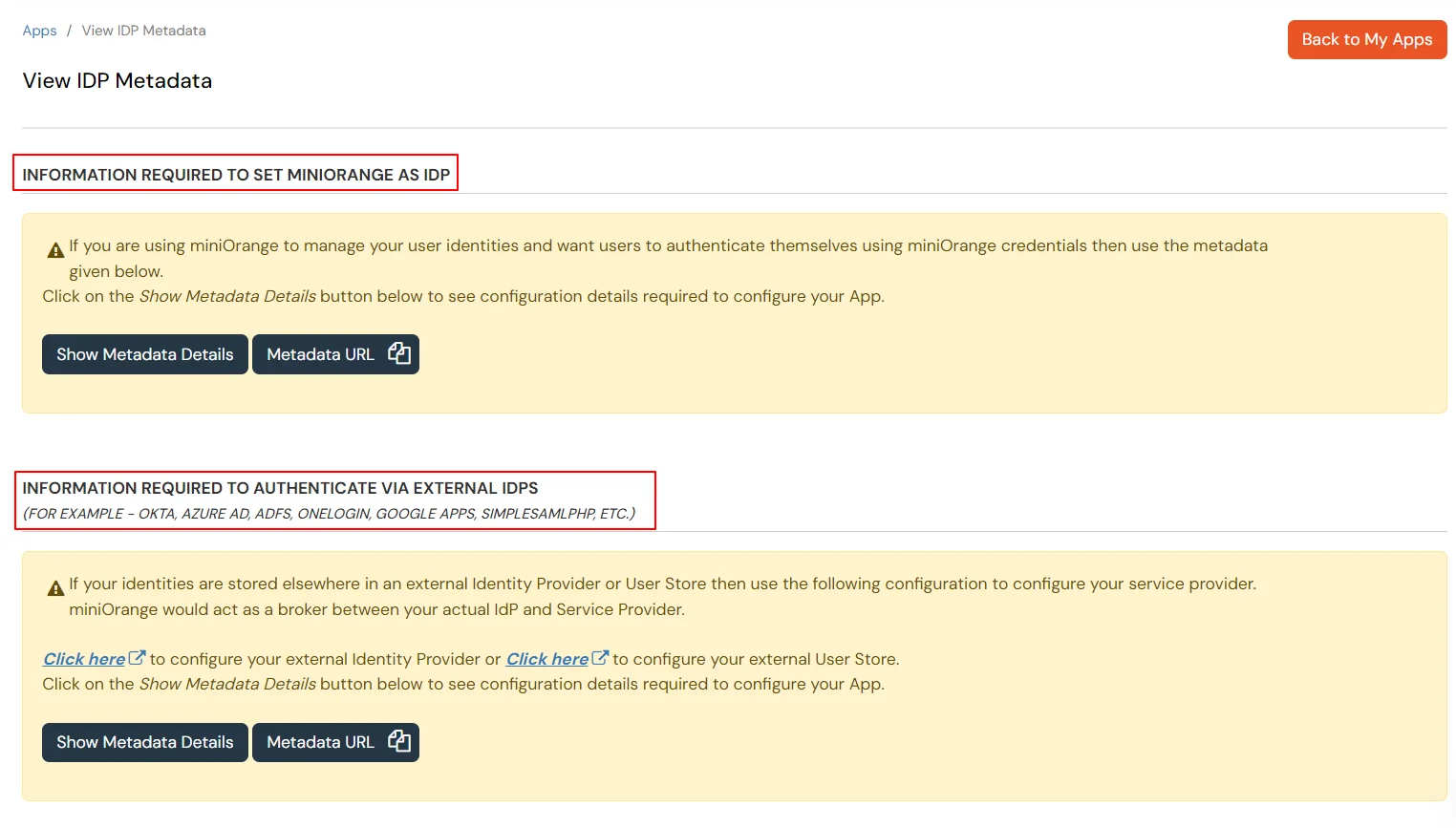
To get miniOrange metadata details in order to configure FortiClient :
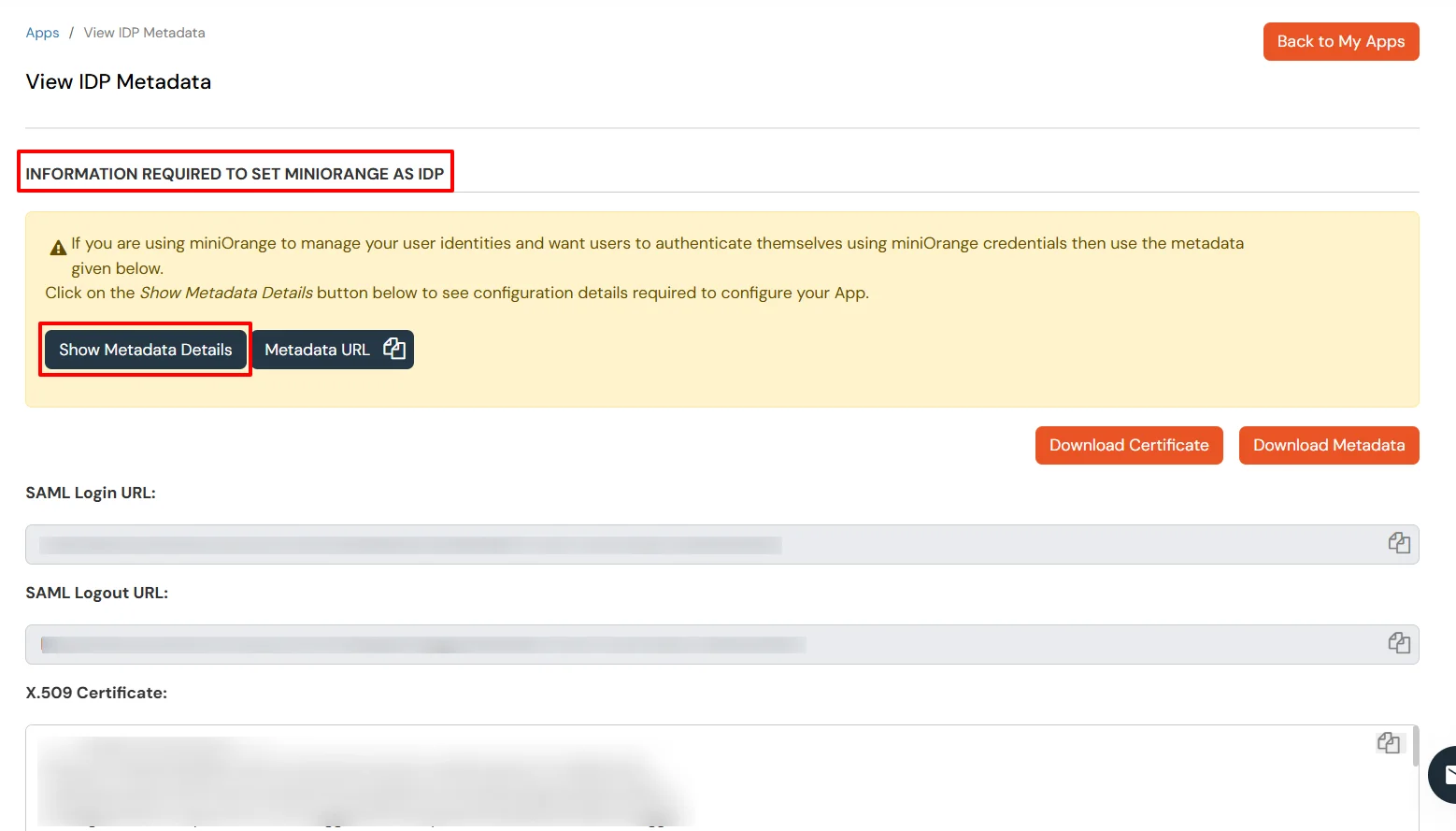
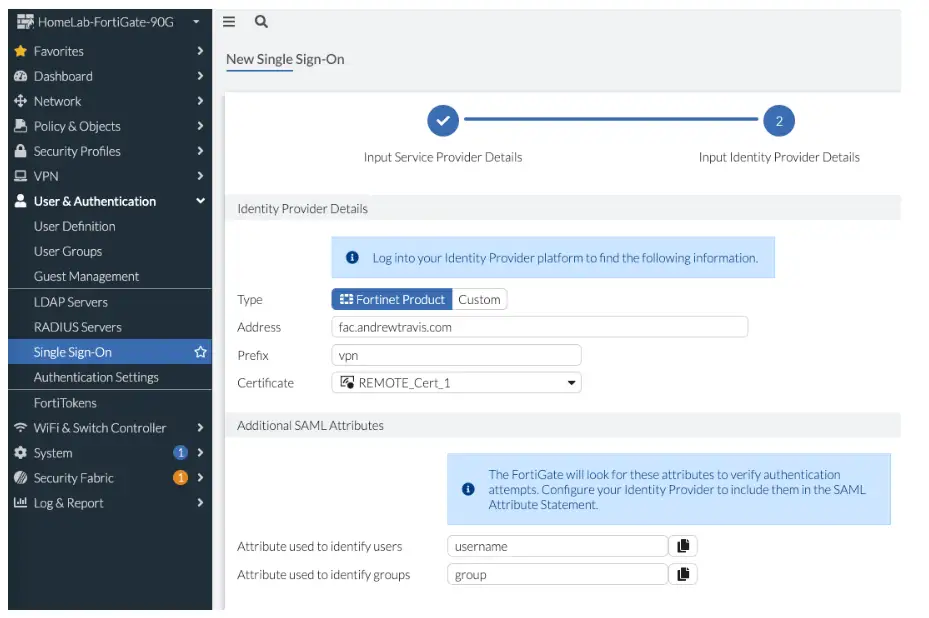
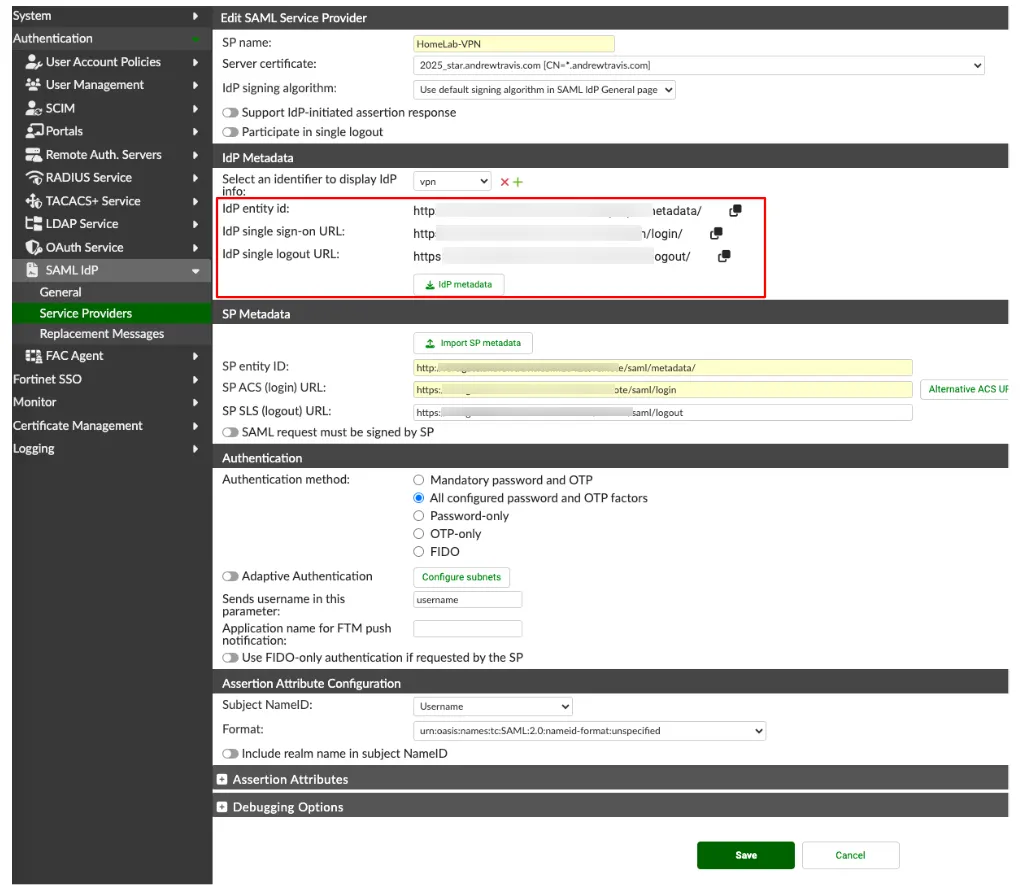
| IDP Entity ID | Entity ID or Issuer in miniOrange |
| IDP Single Sign-On URL | SAML Login URL in miniOrange metadata |
| IDP Single Logout URL | SAML Logout URL in miniOrange metadata |
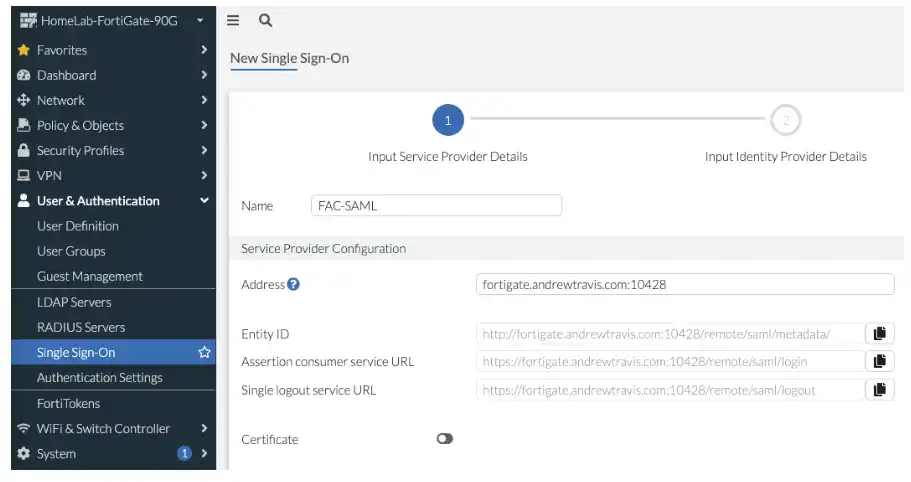
auth-ike-saml-port (valid range 1–65535; default is often 1001—use the same value you set in User & Authentication > Single Sign-On, for example 10428). If your FortiOS version requires it, set this in the CLI to match that port:
config system global
set auth-ike-saml-port 10428
end
config system interface
edit "wan1"
set ike-saml-server enable
next
end
Note: To avoid invalid certificate warnings in FortiClient, the certificate’s subject or SAN should match the IPsec remote gateway hostname or FQDN users enter. If the server cert chains to a private CA, import that CA into the endpoint’s trusted root store (or deploy it via your device-management policy).
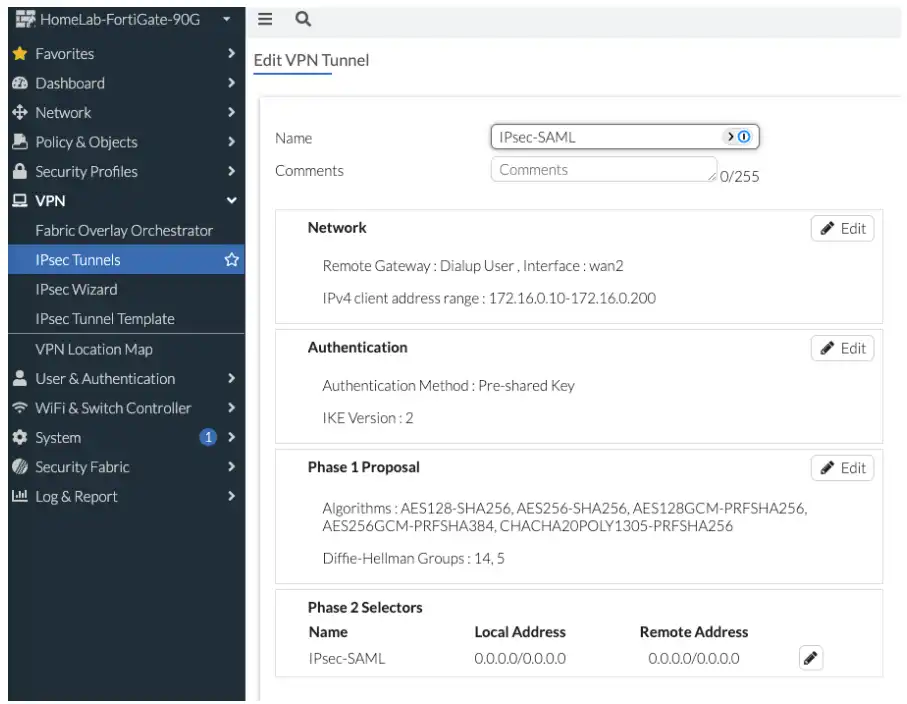
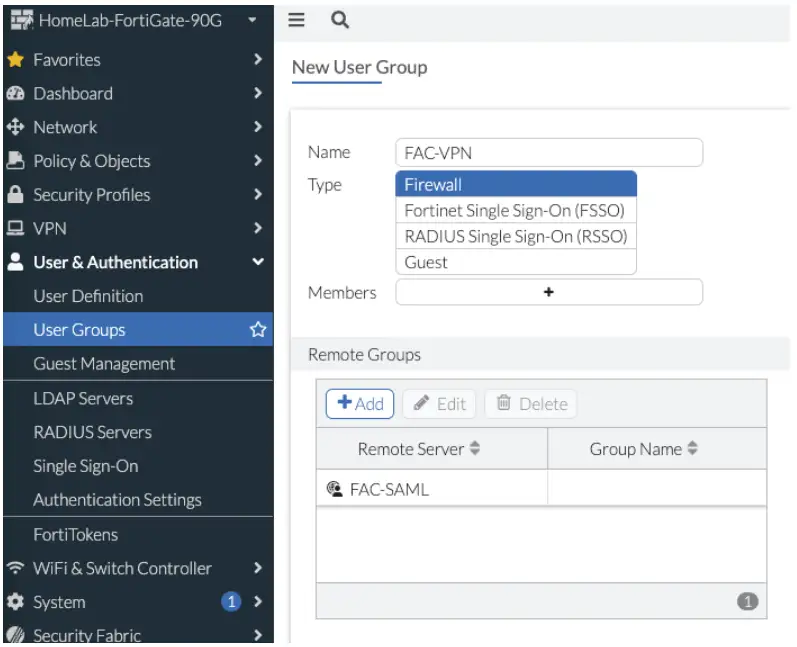
FAC-VPN) on the phase 1 interface. Example (adjust the tunnel name to match yours):
config vpn ipsec phase1-interface
edit "IPsec-SAML"
set eap enable
set eap-identity send-request
set authusrgrp "FAC-VPN"
next
end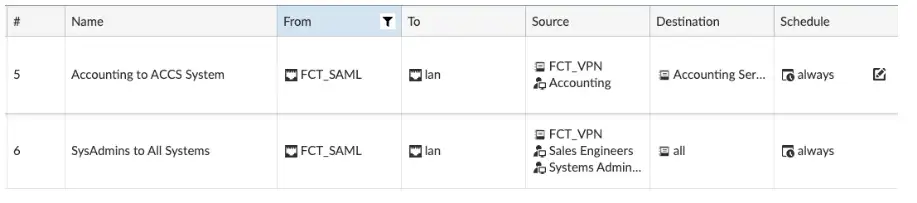
FAC-VPN group to a test subnet:
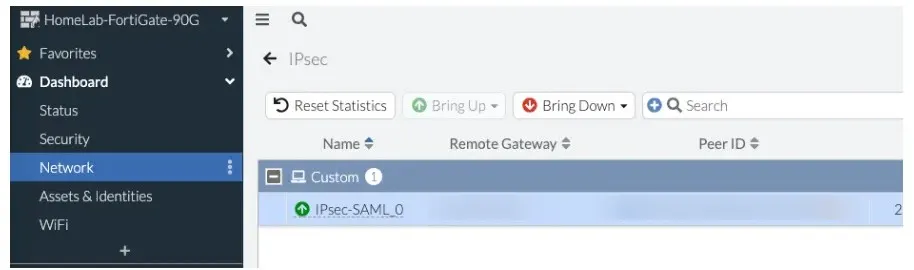
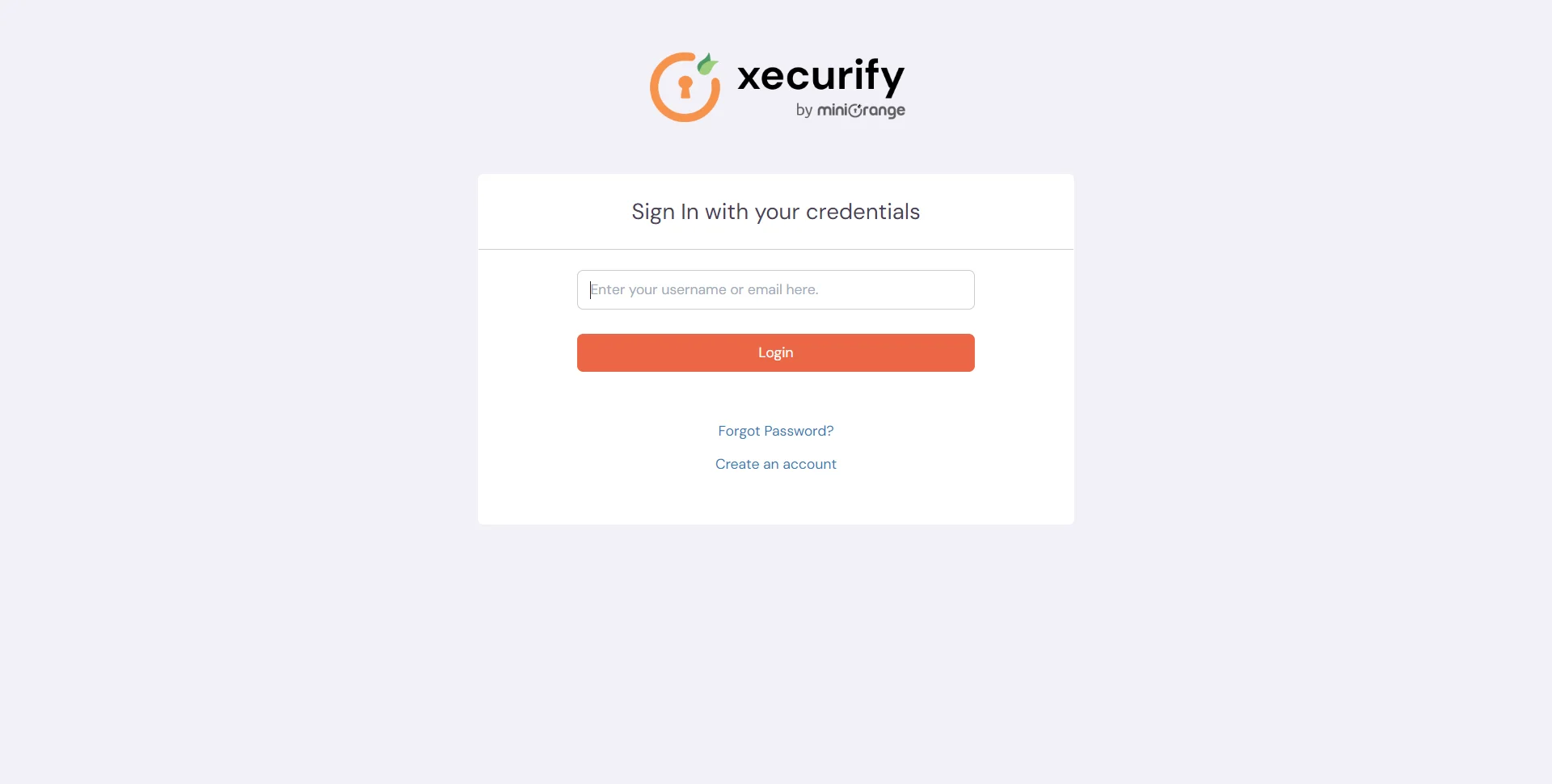
Test SSO login to your FortiClient account with miniOrange IdP:
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.
diag debug reset
diag debug application ike -1
diag debug application samld -1
diag debug application fnbamd -1
diag debug application eap_proxy -1
diag debug console timestamp enable
diag debug enable
Fortinet Single Sign-On (FSSO) is an authentication protocol that enables Fortinet security products like FortiGate to transparently identify and authenticate users by monitoring login events within Active Directory or other supported identity stores. When SAML is configured on FortiGate or FortiAuthenticator as a Service Provider, FortiClient can use the same SSO flow for VPN and related access per your FortiOS and SSL VPN settings.
