Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
×
EBS ADFS SSO is a way of implementing Single Sign On functionalities into Oracle E-Business Suite by authenticating users against Microsoft Active Directory Federation Services using miniOrange.
"miniOrange SSO connector enables the Single Sign-On (SSO) between Oracle EBS and ADFS without the need to purchase and install Oracle Access Manager (OAM) and Oracle Internet Directory (OID) license."
Oracle EBS ADFS SSO integration is enabled with the help of miniOrange's Oracle EBS SSO Connector. This integration involves registering Microsoft Active Directory Federated Services – ADFS Services as a SAML Identity Provider (IdP) in the miniOrange connector. The authentication flow works like this: when a user tries to login into EBS, the authentication is delegated to miniOrange, which redirects the user to ADFS for Single Sign-On Login. Upon successful authentication, the user is granted access to Oracle EBS. Oracle EBS can also be protected with ADFS Multi-Factor Authentication. Oracle EBS URL can be added to ADFS Applications Dashboard by ADFS Admin, and users can launch it like any other ADFS Application. miniOrange SSO connector can enable ADFS SSO for the following supported Oracle EBS versions - R12 and R12.2 and it can also enable Oracle EBS integrations such as OBIEE, Hyperion/EPM Suite, ADF Applications, WebCenter and Agile. miniOrange SSO Connector can also enable Microsoft ADFS SSO for other Oracle Products as well such as Peoplesoft, Siebel and JD Edwards.
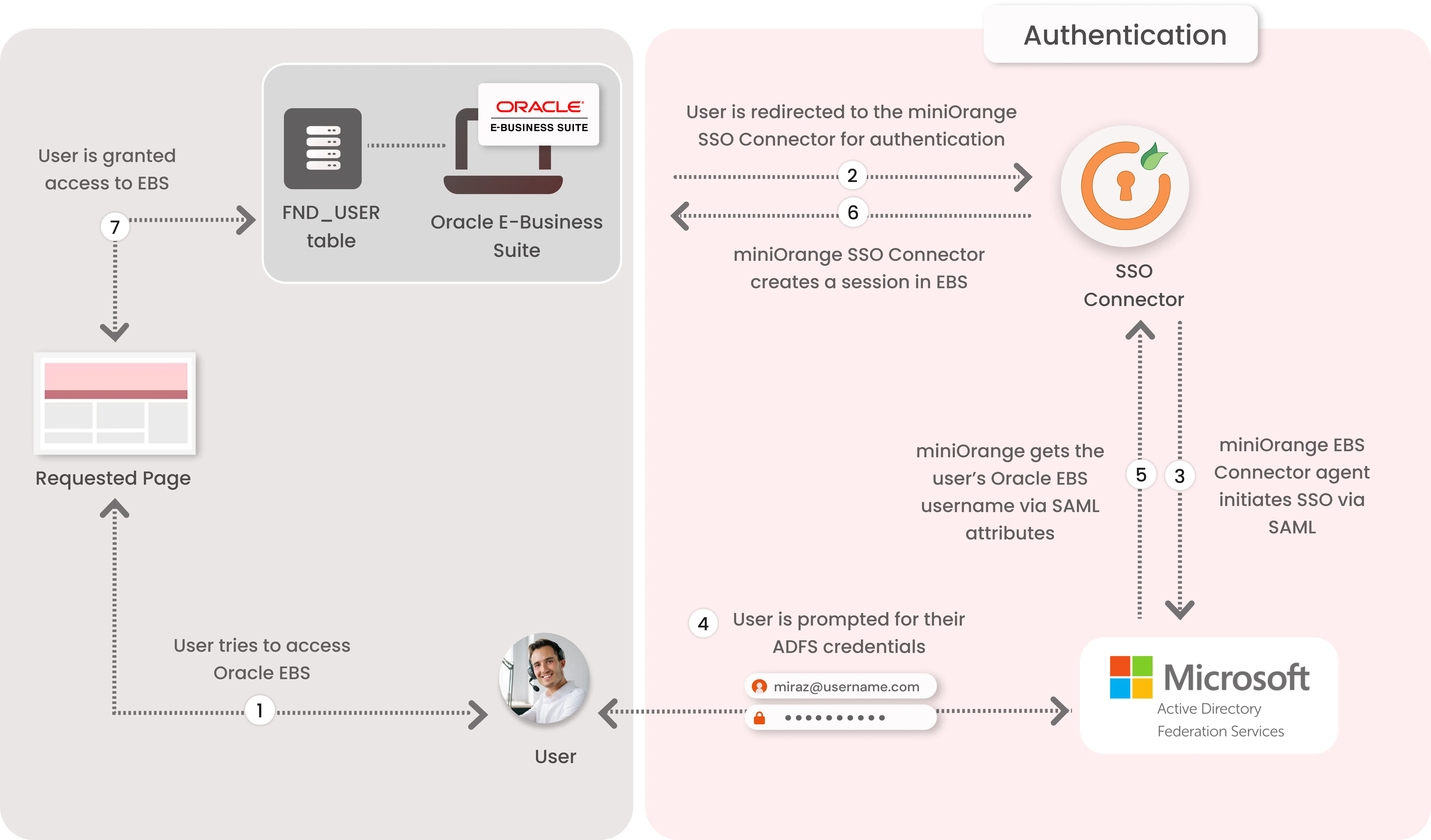
1. The User sends the request to access the Oracle E-Business Suite.
2. Oracle EBS redirects the request to the miniOrange SSO Connector for authentication.
3. The miniOrange SSO Connector redirects the user to ADFS for authentication.
4. The user is prompted for their ADFS credentials, and is authenticated upon a successful response.
5. The connector receives the user’s Oracle EBS registered username/email from ADFS via SAML attributes.
6. The connector checks the value of the username/email received from ADFS against the FND_USER table in the Oracle EBS Database & creates a session for them.
7. Upon successfully creating a session, user is redirected to the Oracle E-Business Suite portal as logged-in user
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
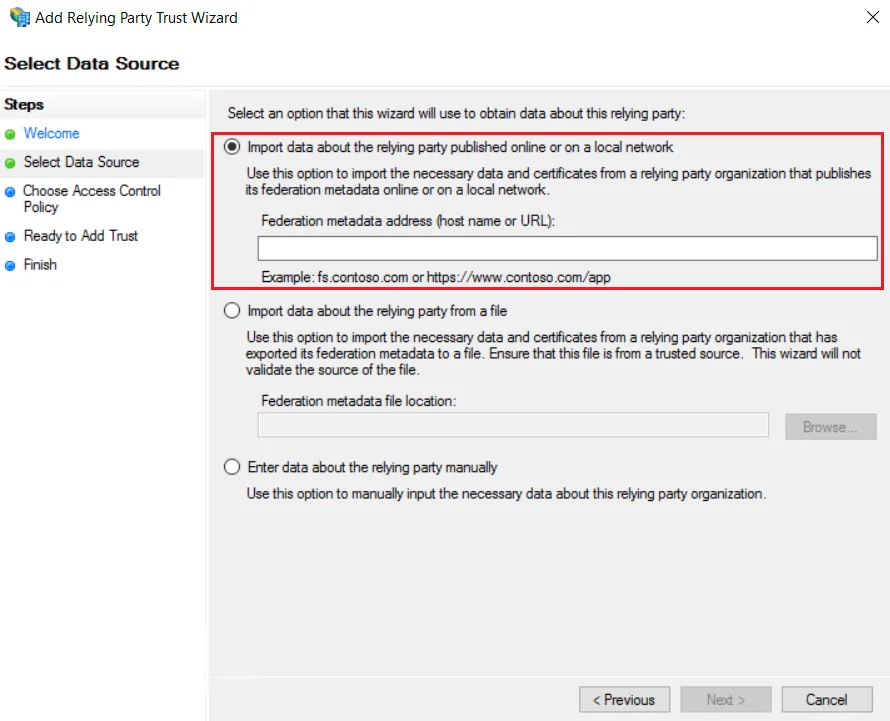
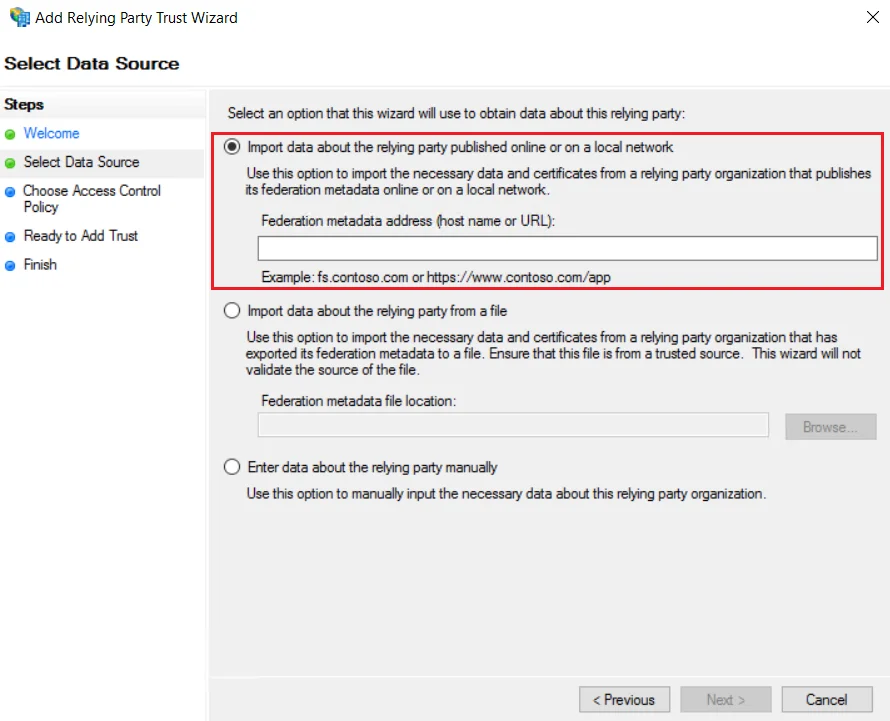
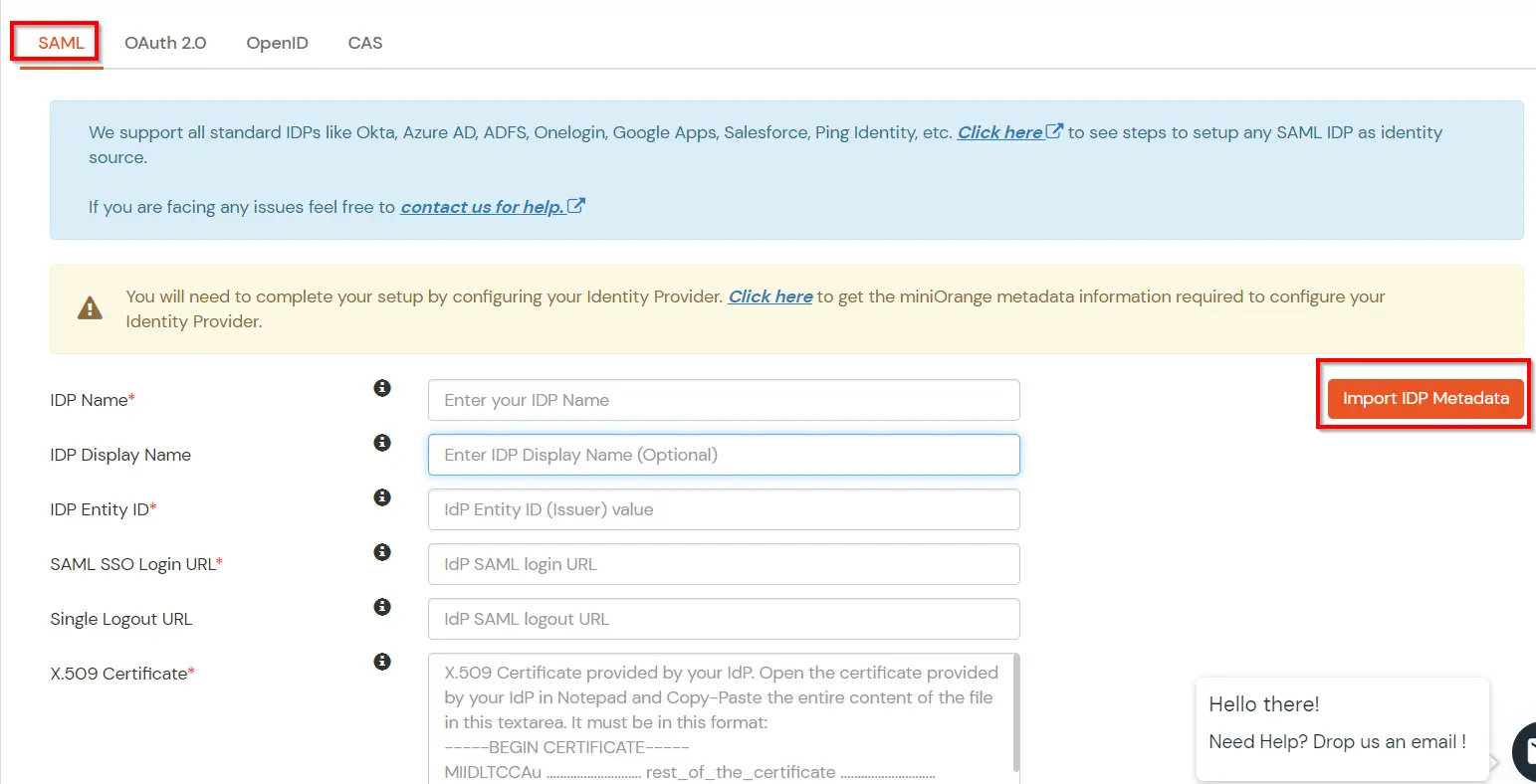
Using Metadata URL
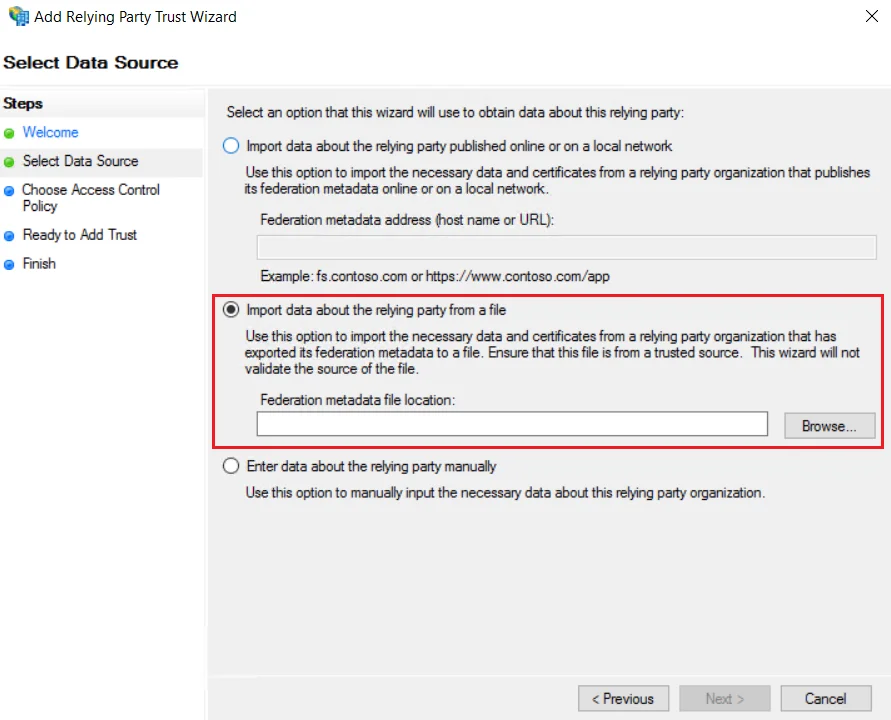
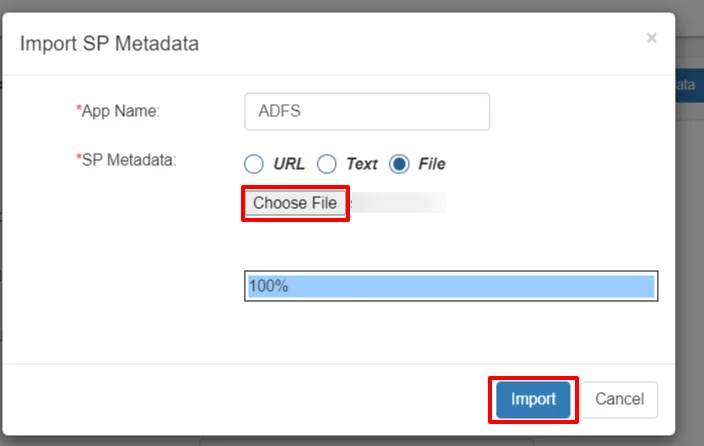
Using Metadata XML file
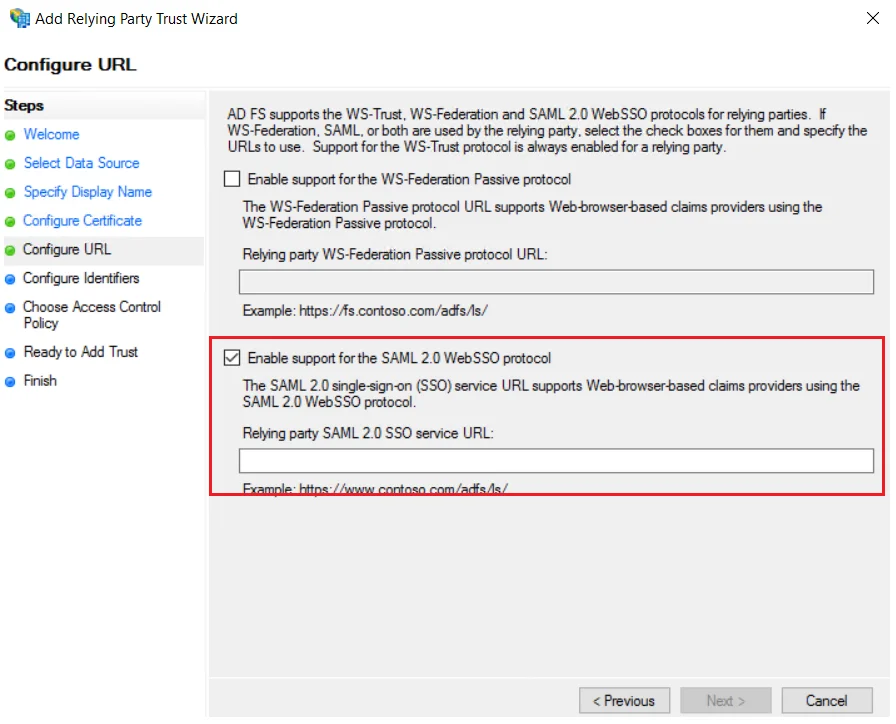
Using Manual Configuration
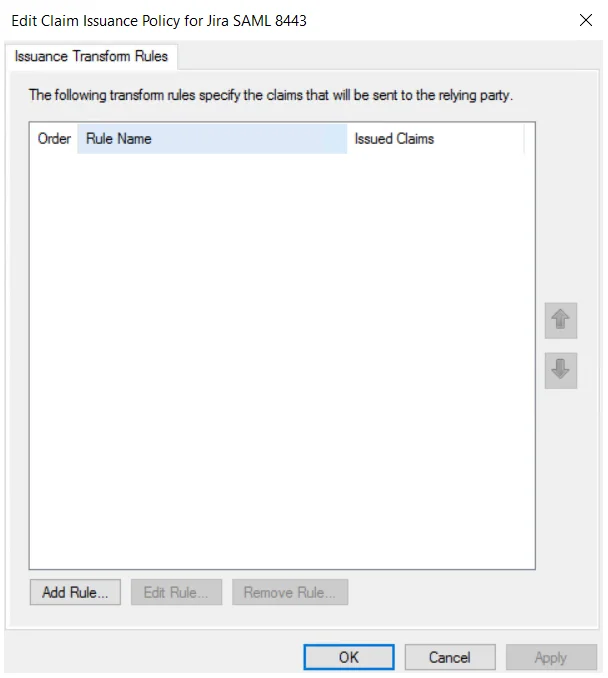
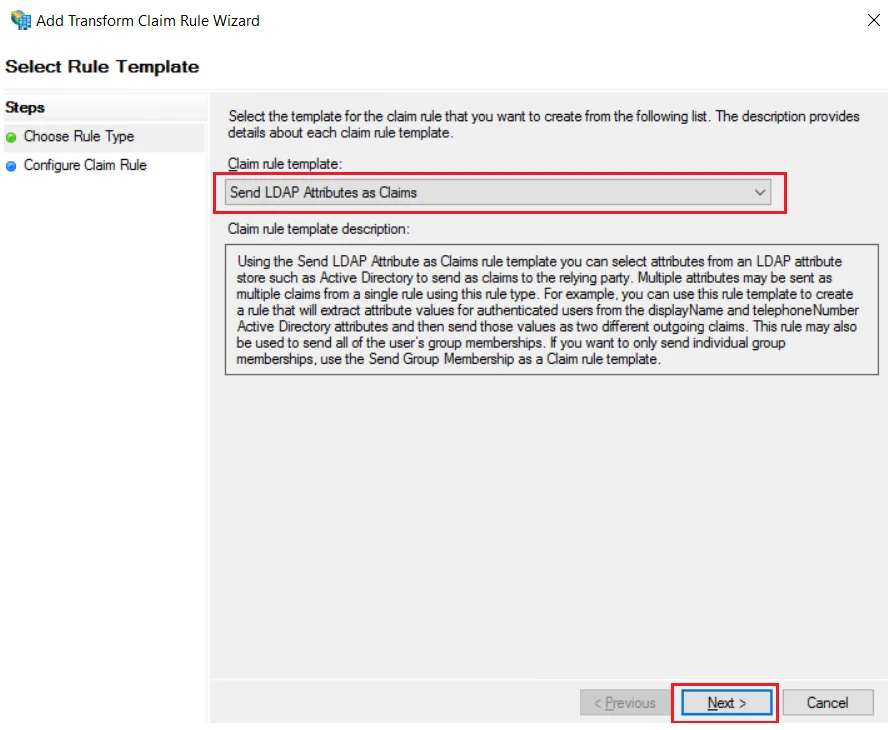
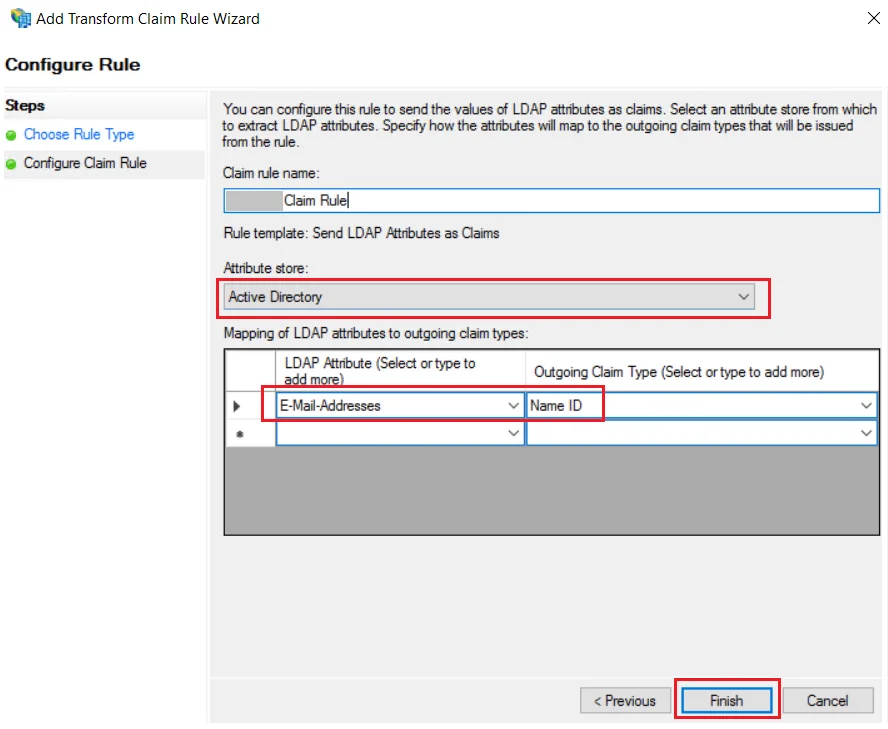
| Claim rule name: | Attributes |
| Attribute Store: | Active Directory |
| LDAP Attribute: | E-Mail-Addresses |
| Outgoing Claim Type: | Name ID |
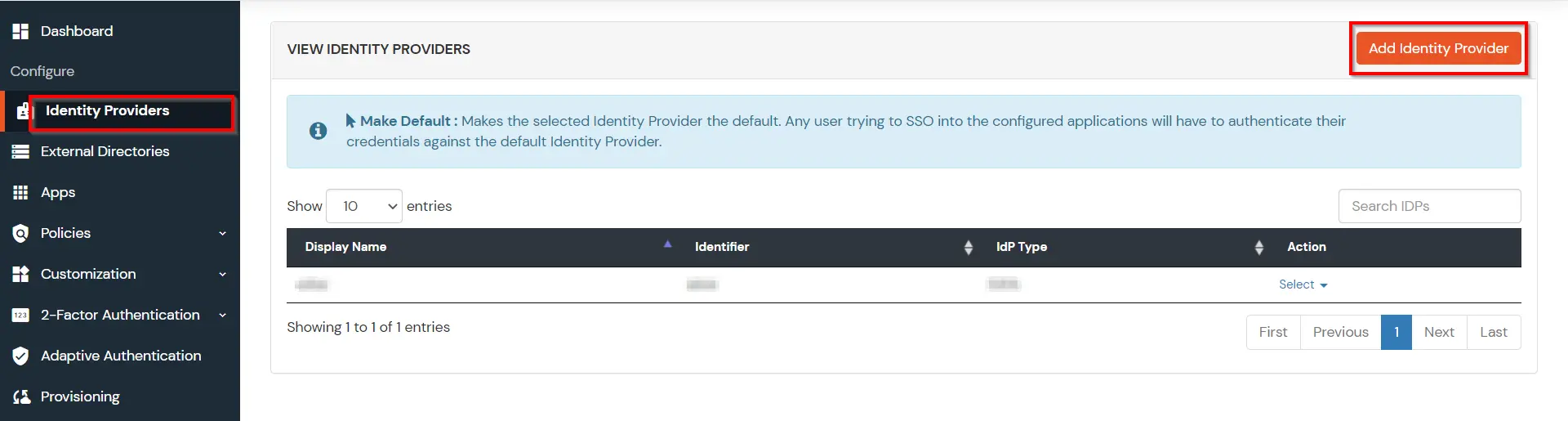
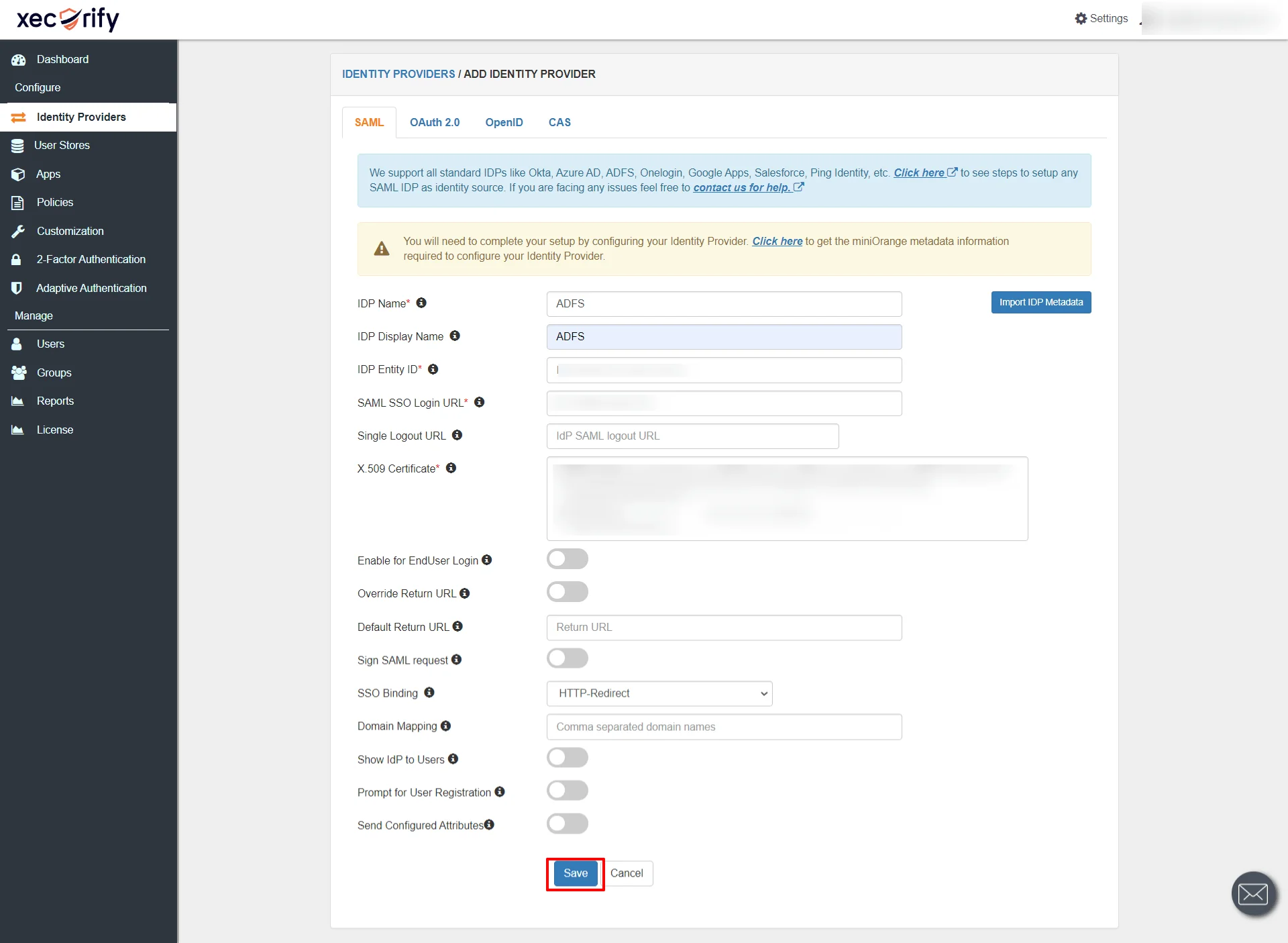
| Domain Mapping | Can be used to redirect specific domain user to specific IDP |
| Show IdP to Users | Enable this if you want to show this IDP to all users during Login |
| Send Configured Attributes | Enabling this would allow you to add attributes to be sent from IDP |
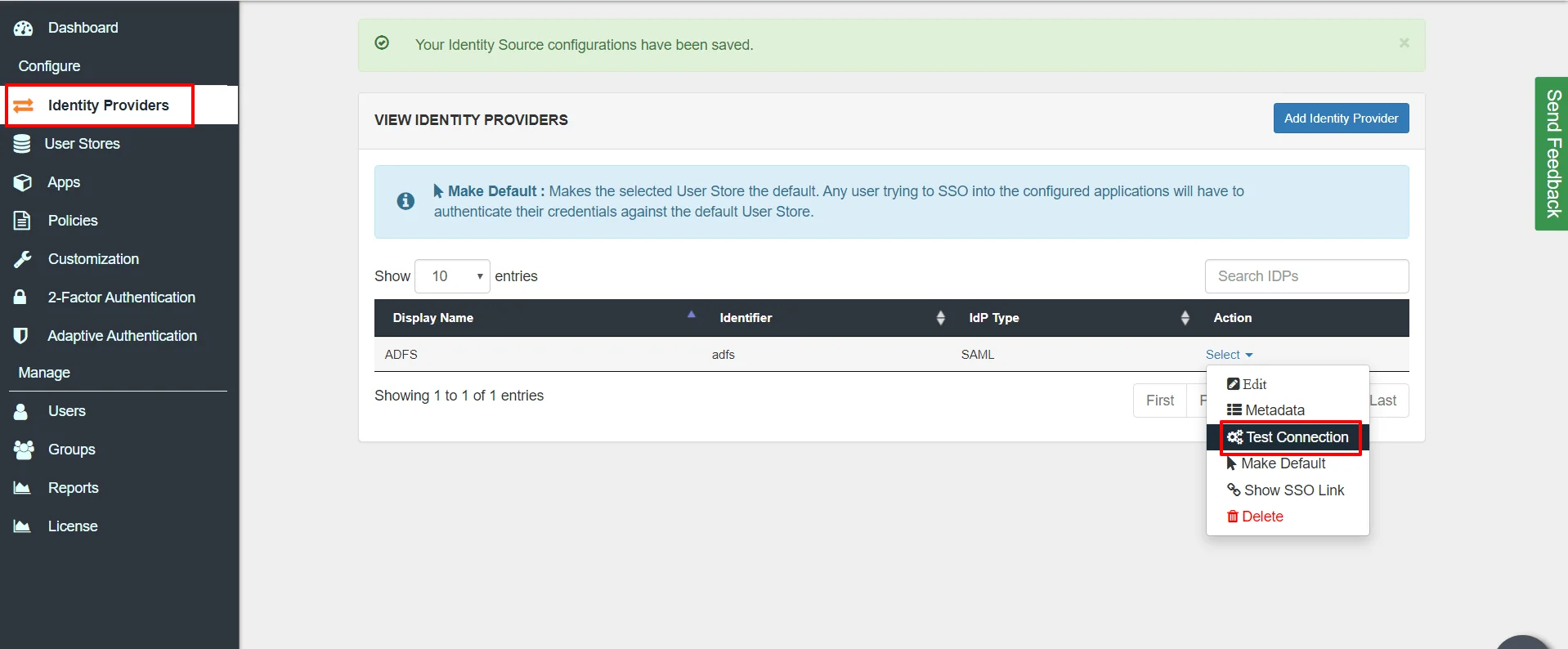

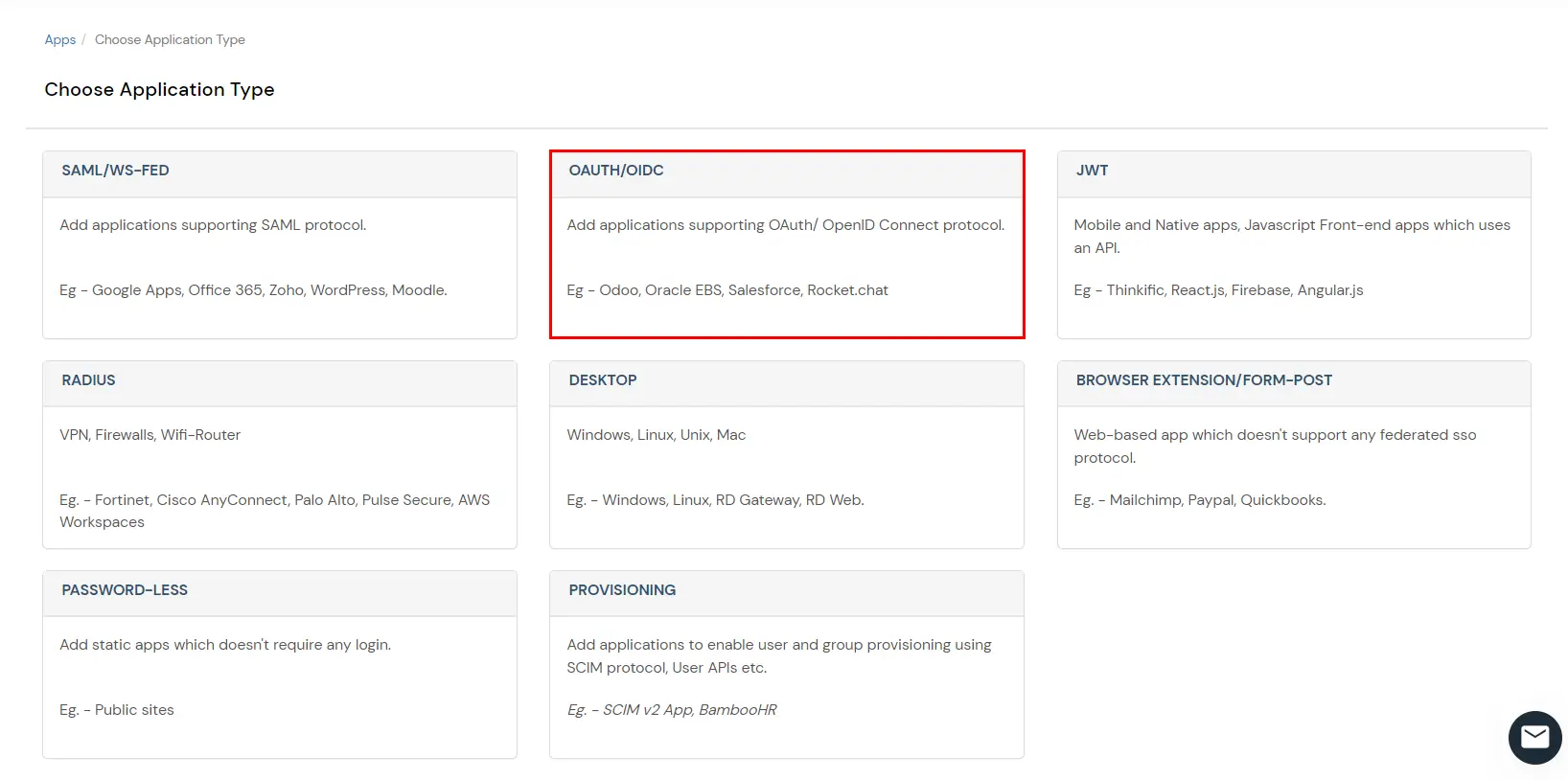
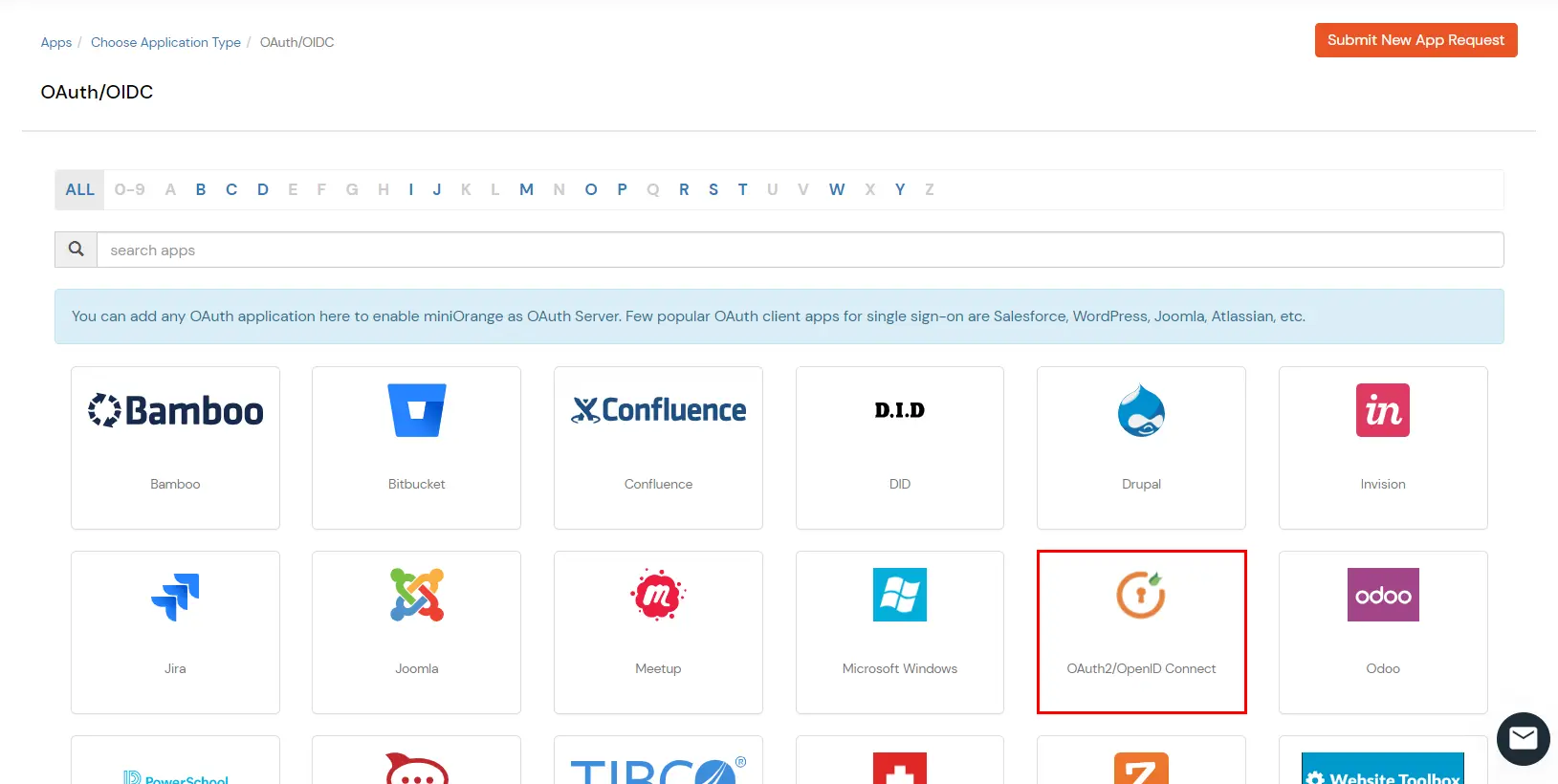
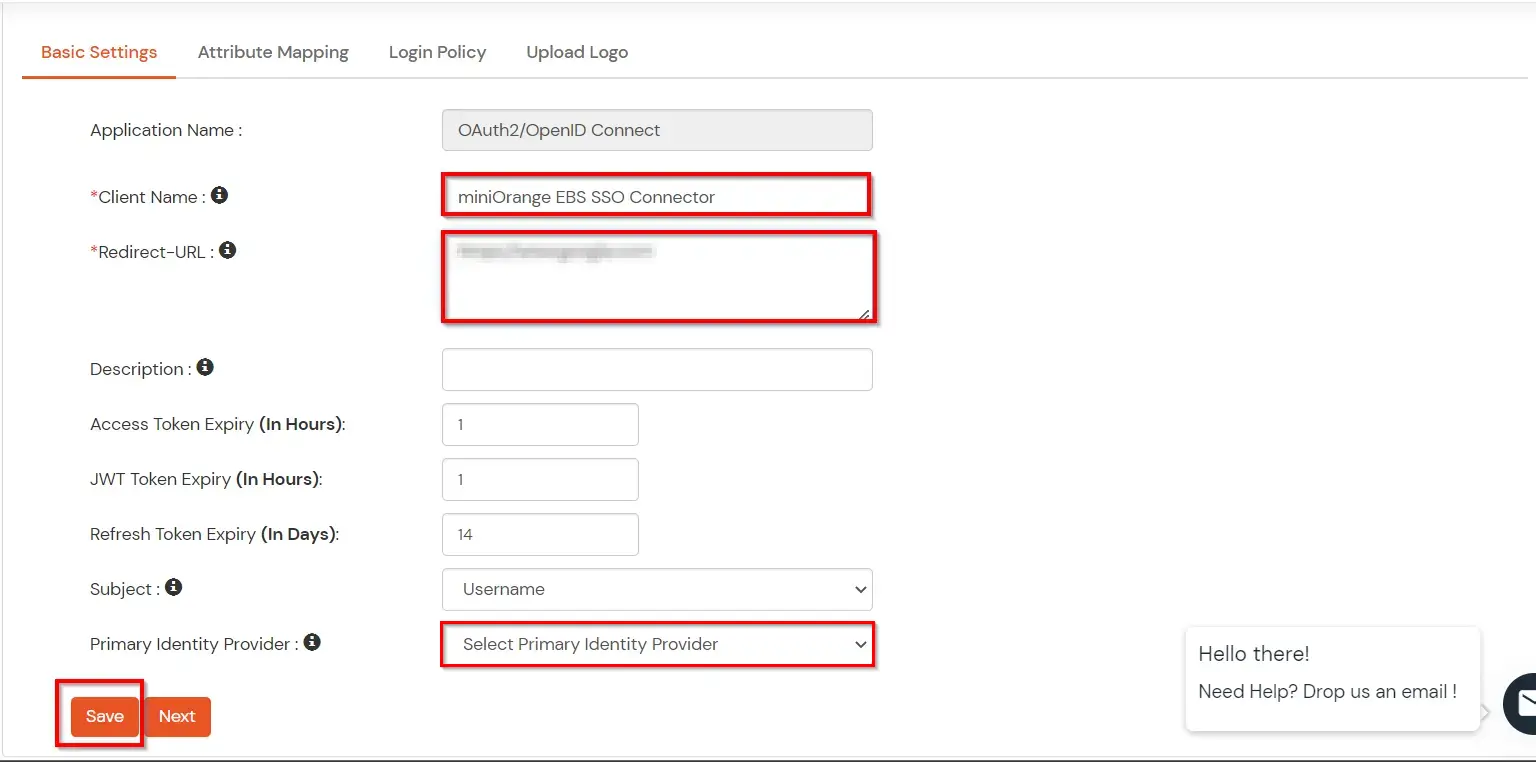
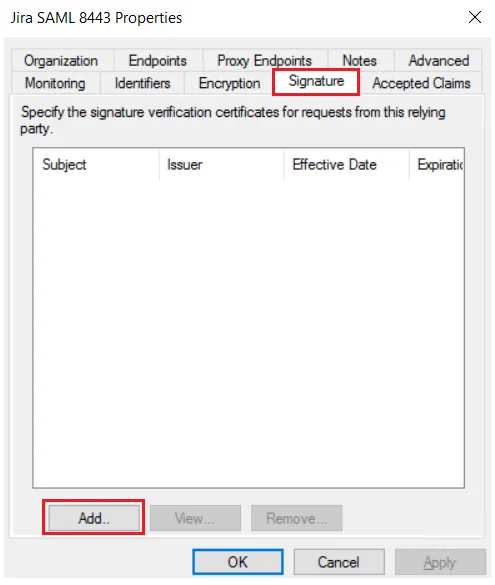
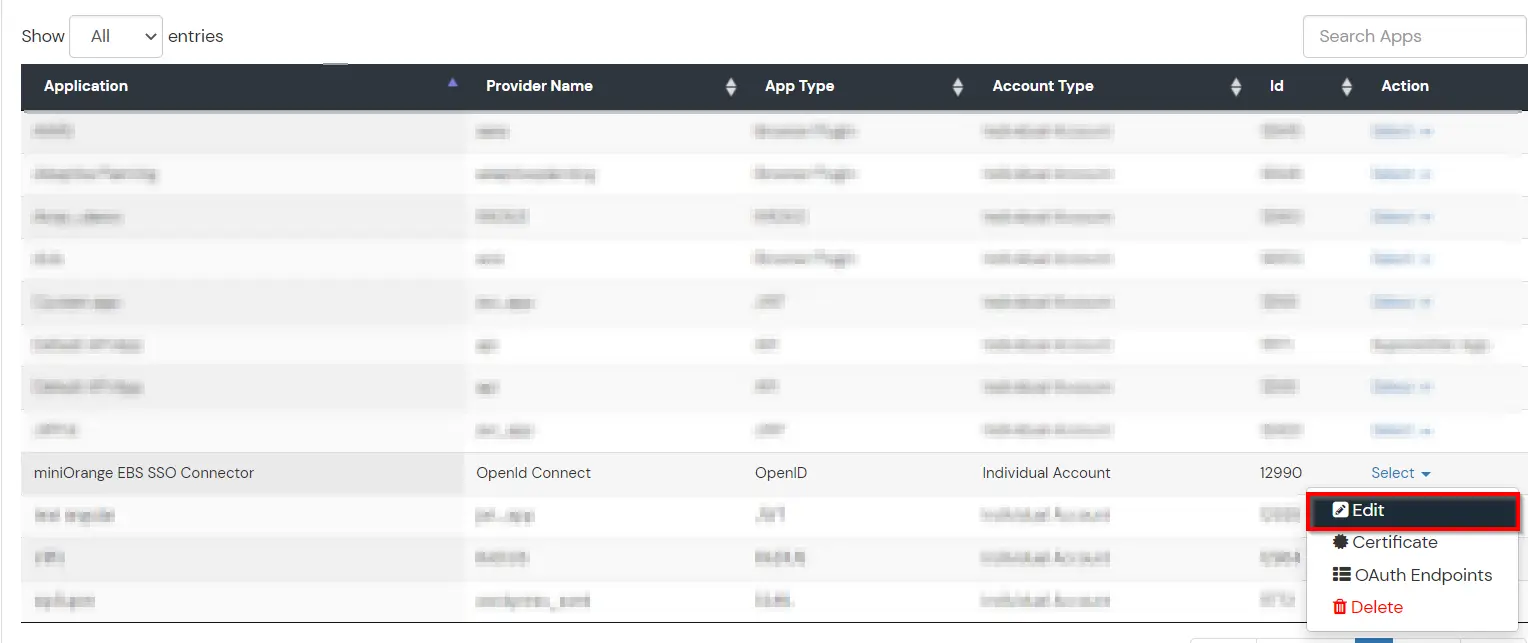
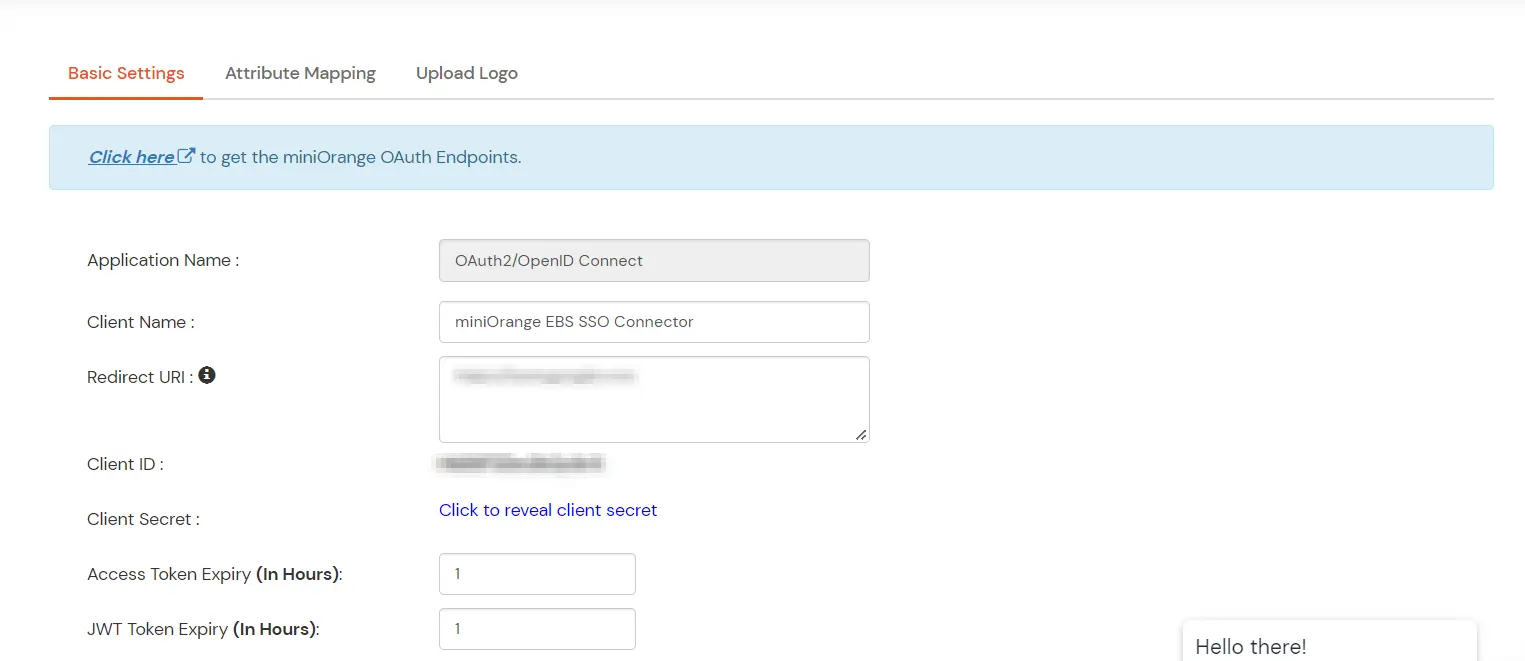
You can edit Application by using the following steps:
Note: Oracle and Java are registered trademarks of Oracle and/or its affiliates. miniOrange is a separate entity.
