Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
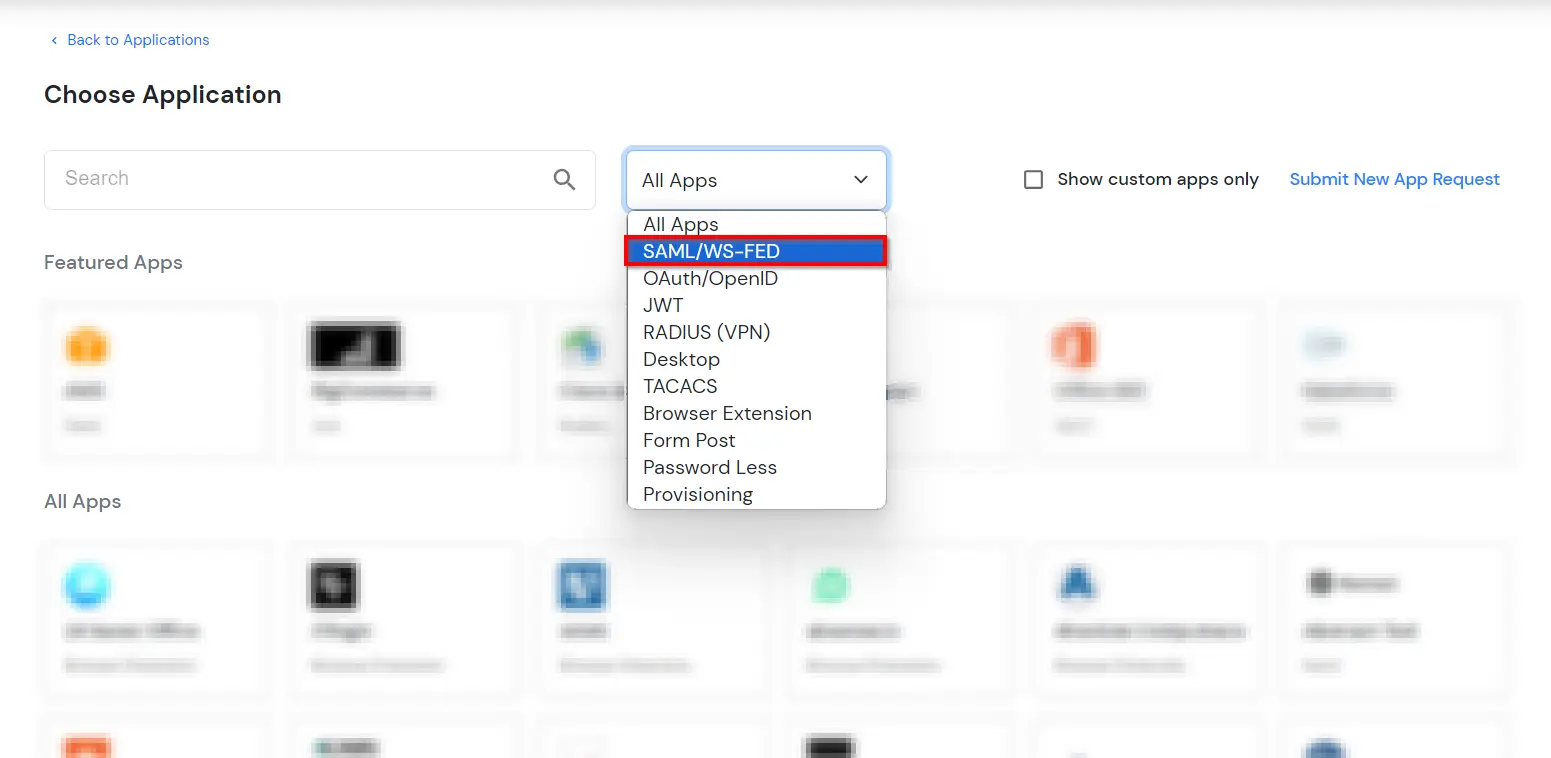
×Configure Google SSO in a few simple steps using this setup guide. miniOrange SAML Single Sign-On (SSO) allows secure Single Sign-On access to your Google Account & other specific On-Premise / Cloud apps using a single set of existing login credentials.
Google SSO solution also provides an option to integrate with multiple third-party Identity Providers which support SAML and OAuth sort of standard protocols. IDP here means (Okta, Auth0, Ping, Onelogin, etc) or Active Directory (AD) where your existing users are managed. Google SSO for Cloud Identity, eliminating passwords by redirecting users to an external identity provider (IdP) for authentication, enhancing user experience with existing credentials.
With miniOrange Google SSO, you can:
miniOrange offers free help through a consultation call with our System Engineers to Install or Setup Google SSO solution in your environment with 30-day free trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you in no time.
miniOrange Google SSO integration supports the following features:
IP based access control in cloud computing, allows you to enforce an IP restriction policy that enables the IT admin to restrict user access to business data in G Suite only through one or more specified IP addresses. This ensures that no business data is accessed in an unsecured, public, or unregistered IP address. Preventing data theft is a big concern, so IP restriction for G Suite helps you out with that concern.
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.

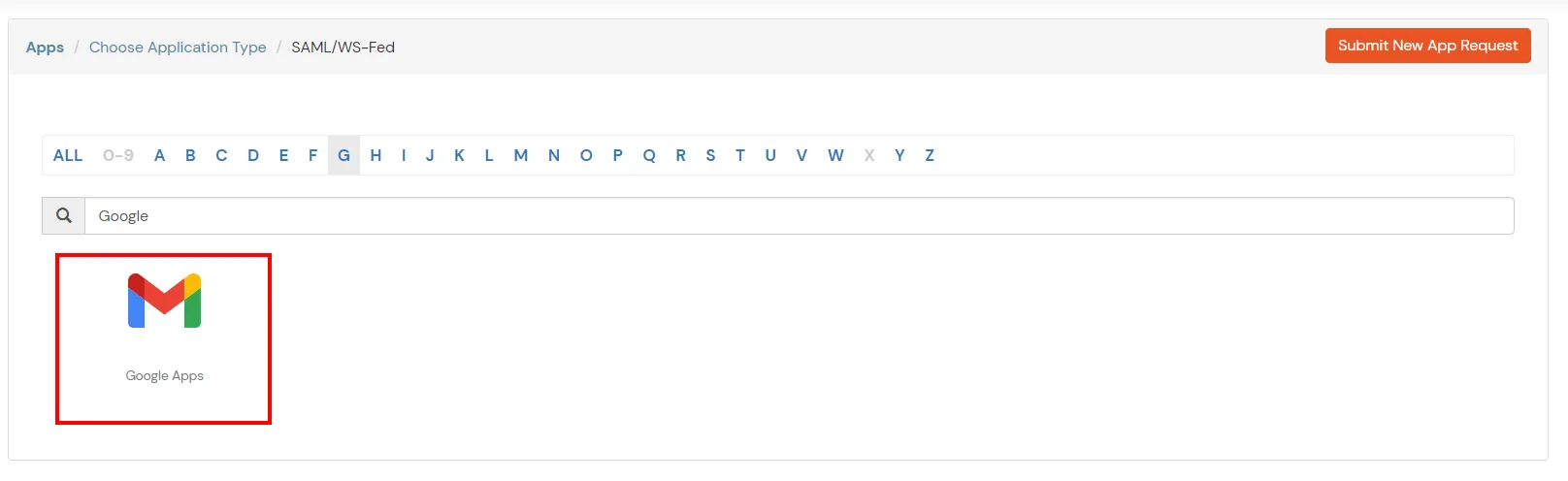
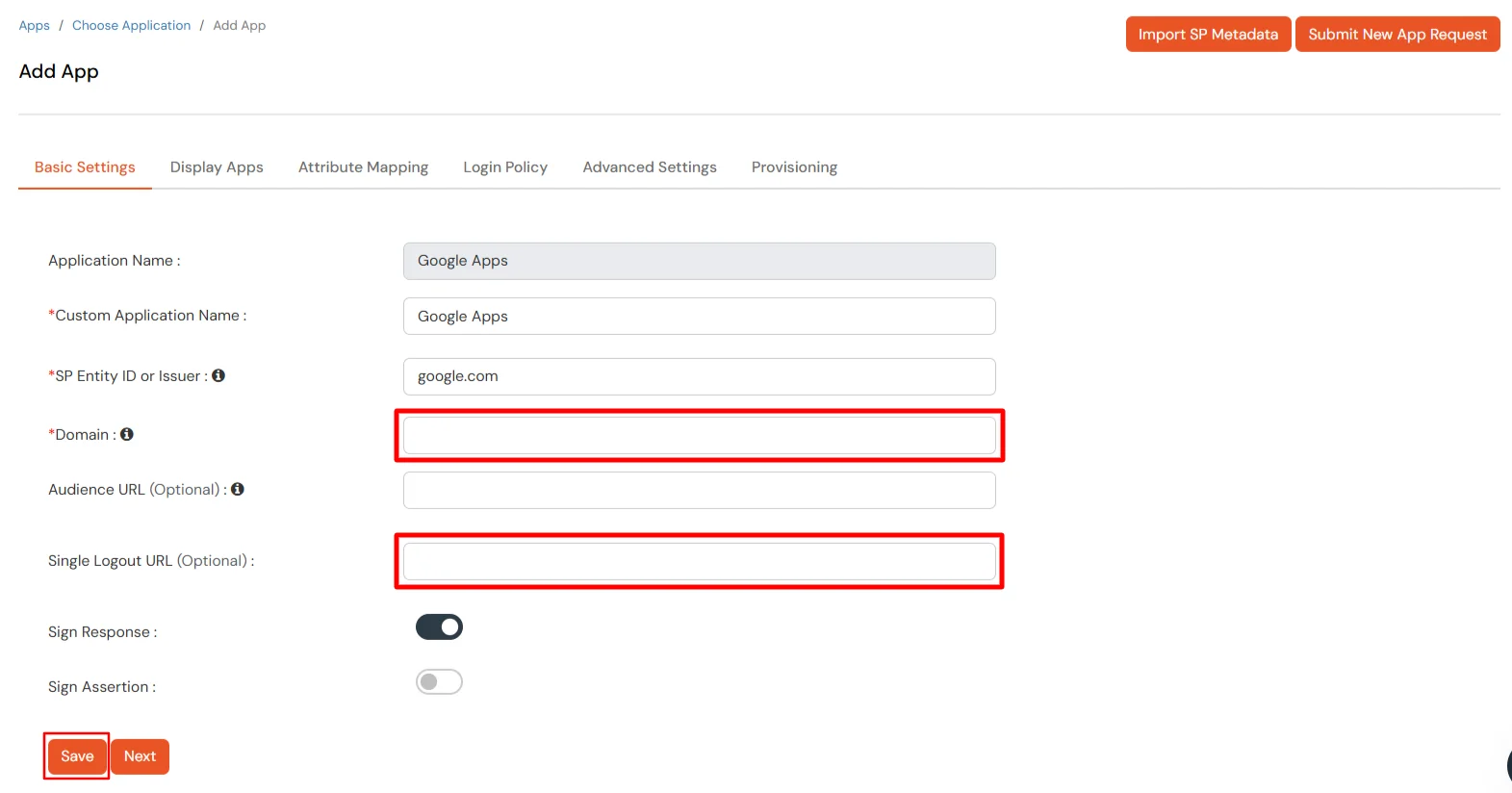
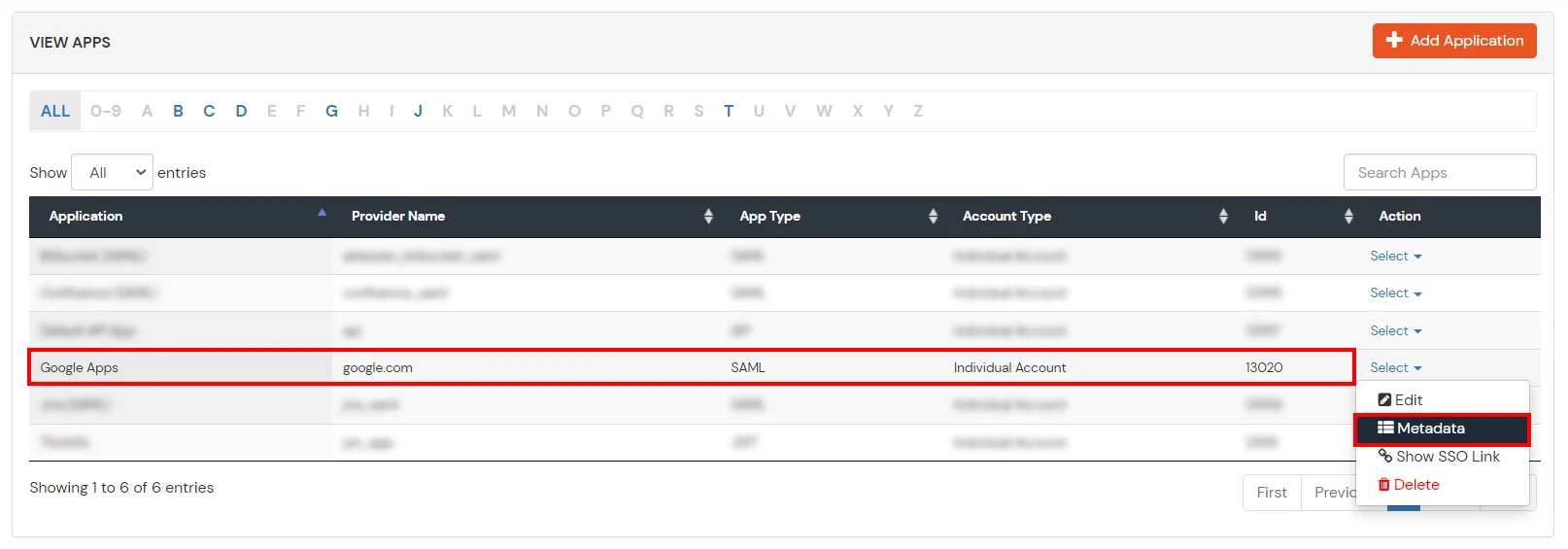
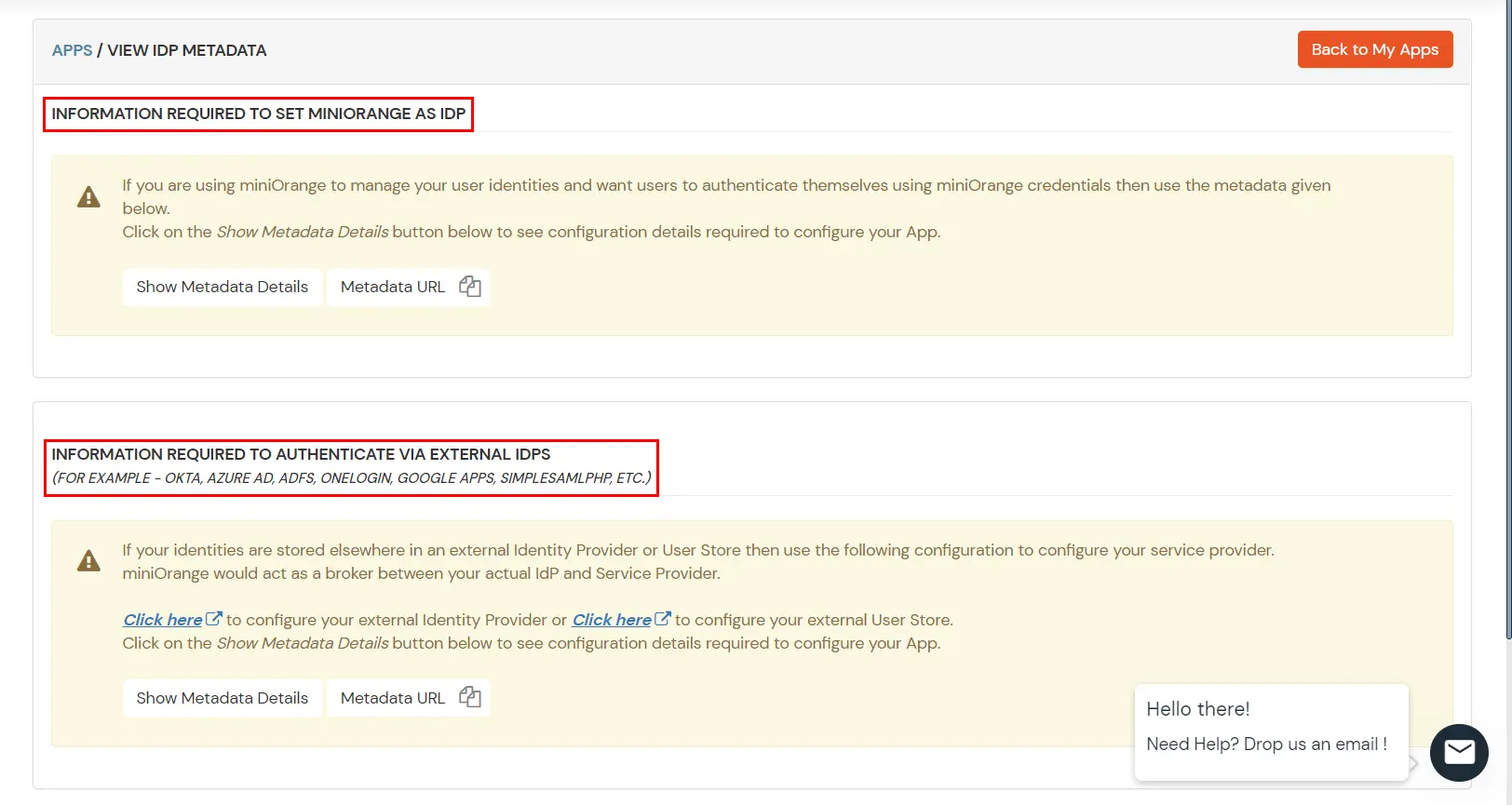
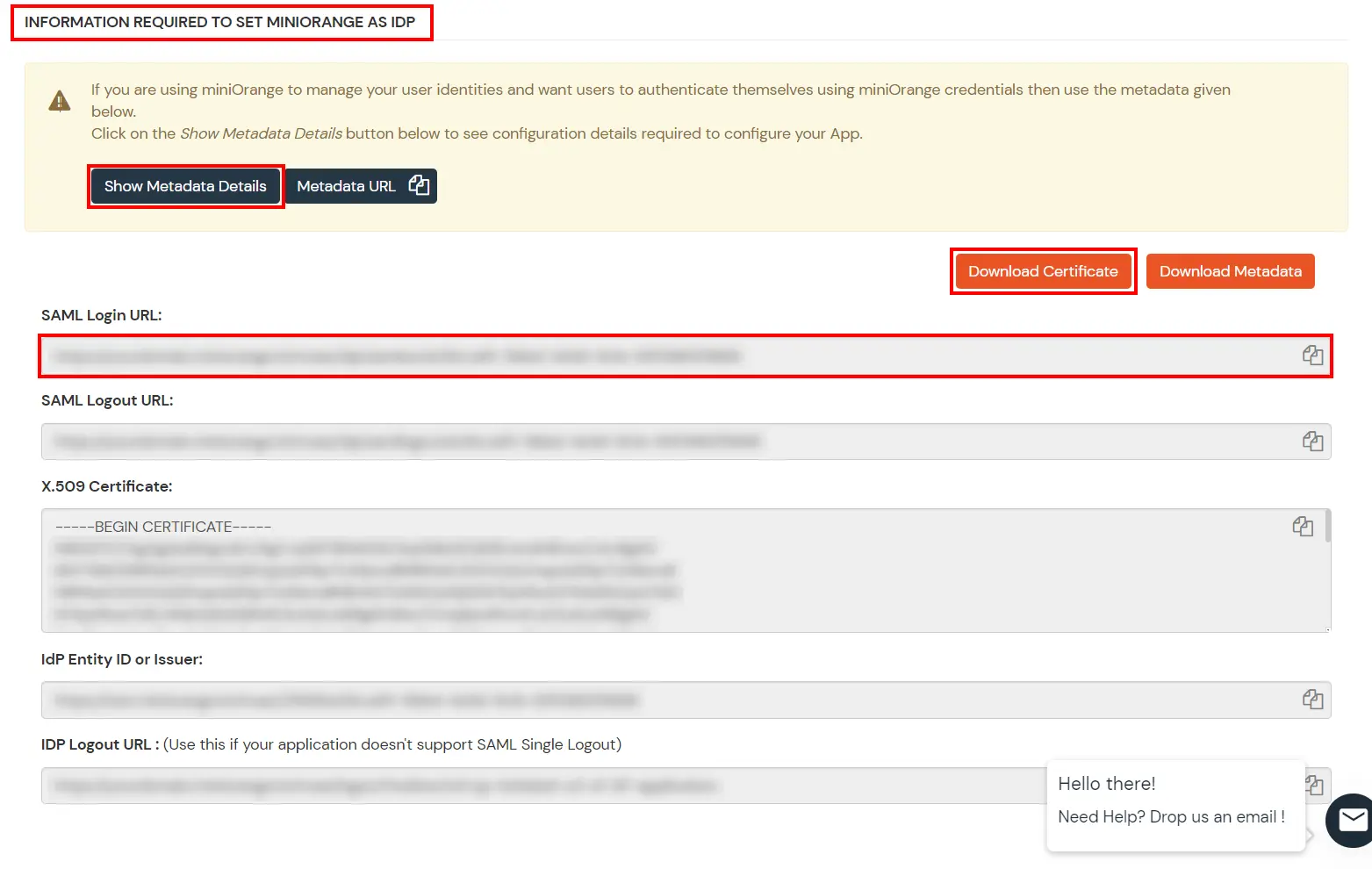
Get IdP Metadata Details to upload to Google Apps:
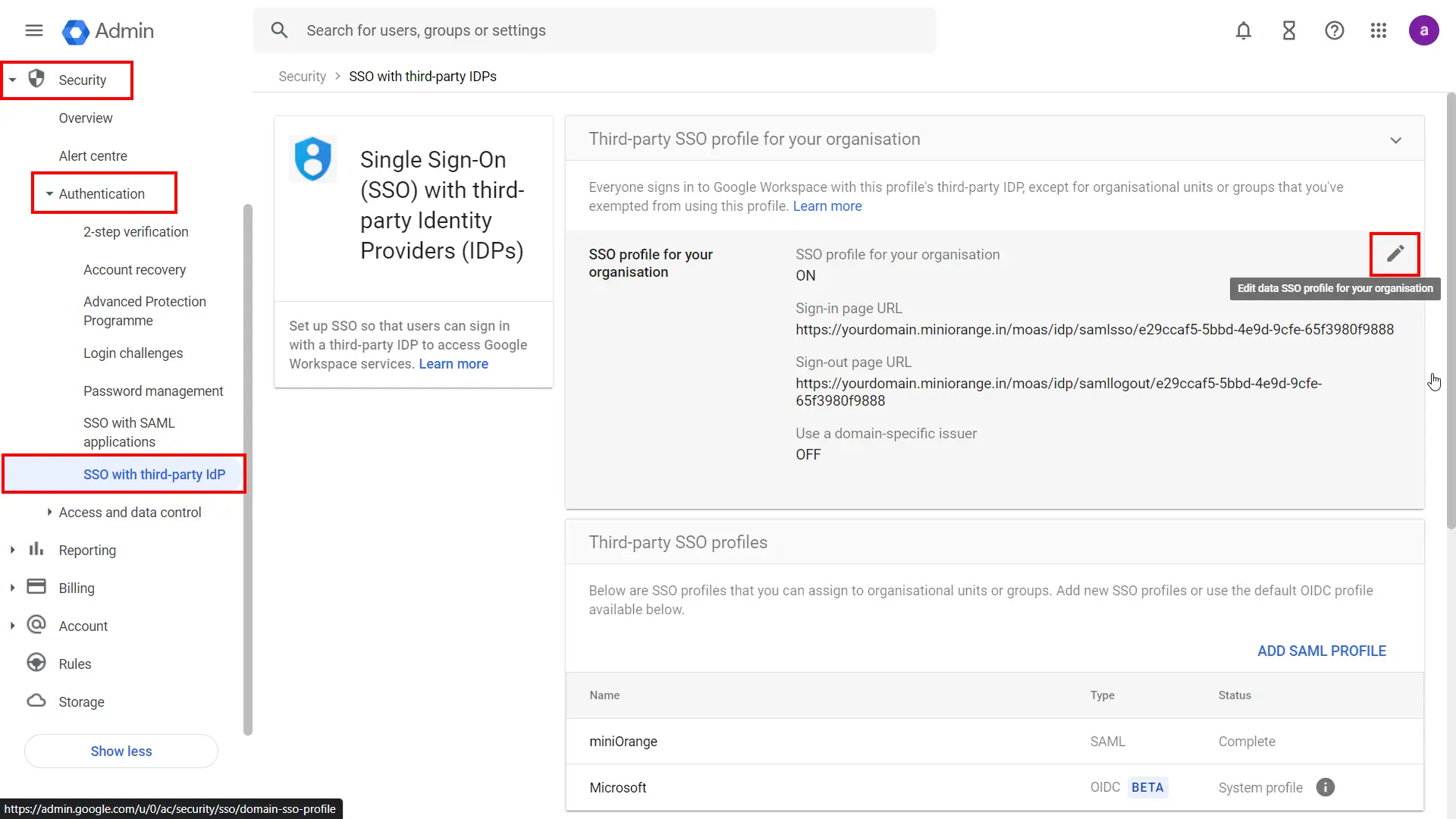
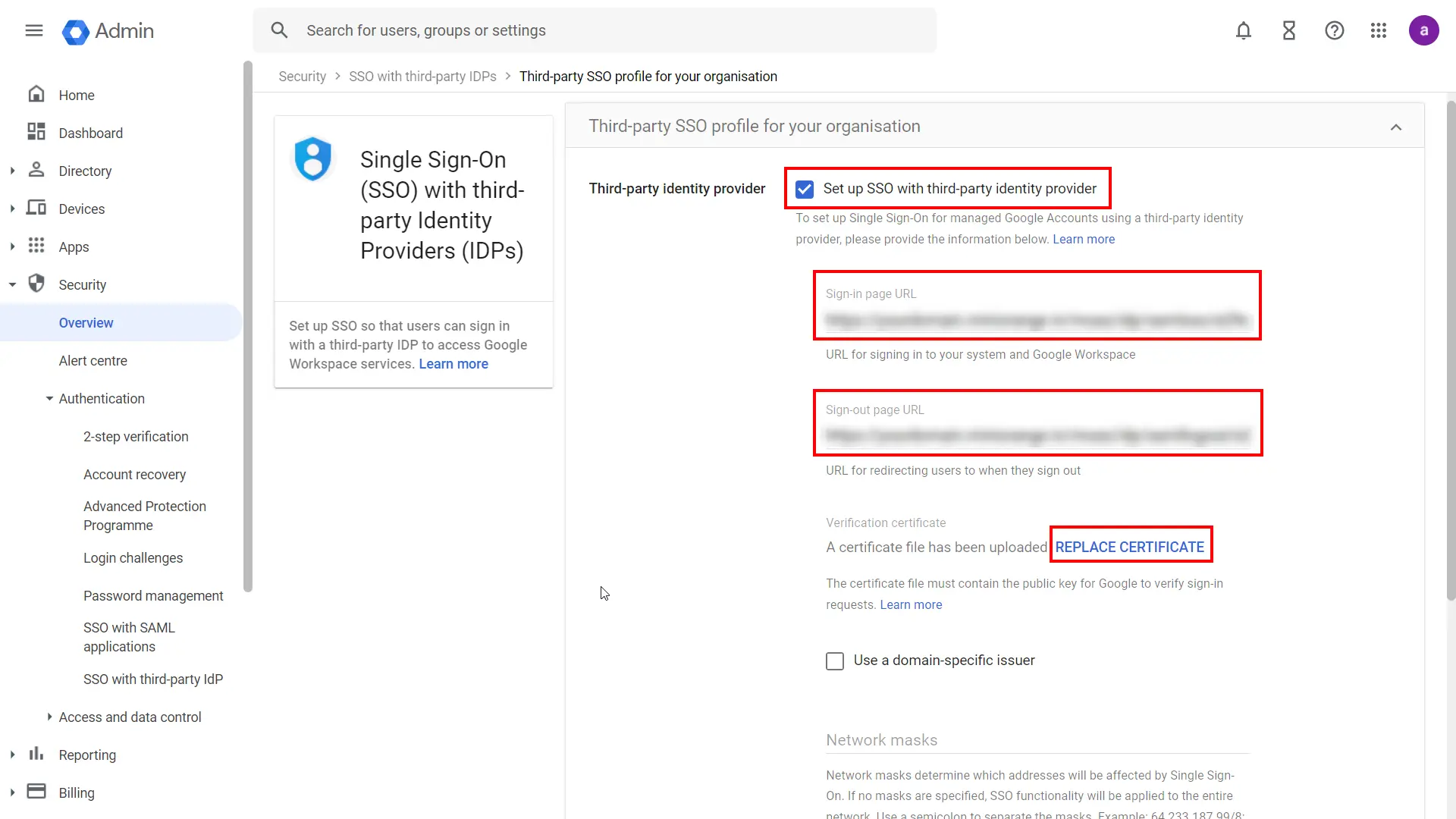
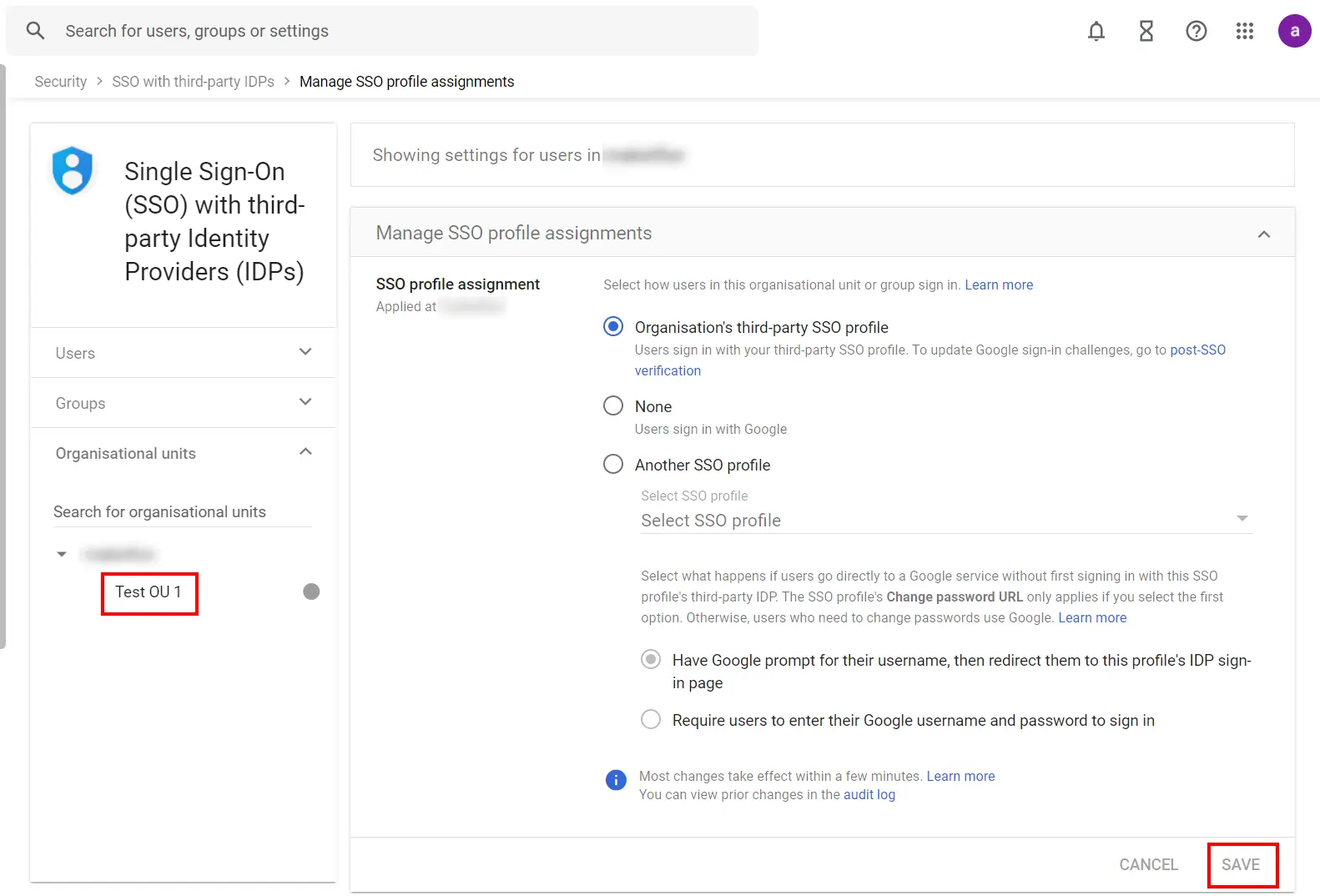
If you want some of your users to sign in to Google directly, you can move those users into an organizational unit (OU) or group. Then, manage SSO settings for the OU or group so that those users are authenticated by Google rather than using your third-party IdP. Follow the following steps:
Note: Get started is only available if you’ve already enabled your third-party SSO profile.
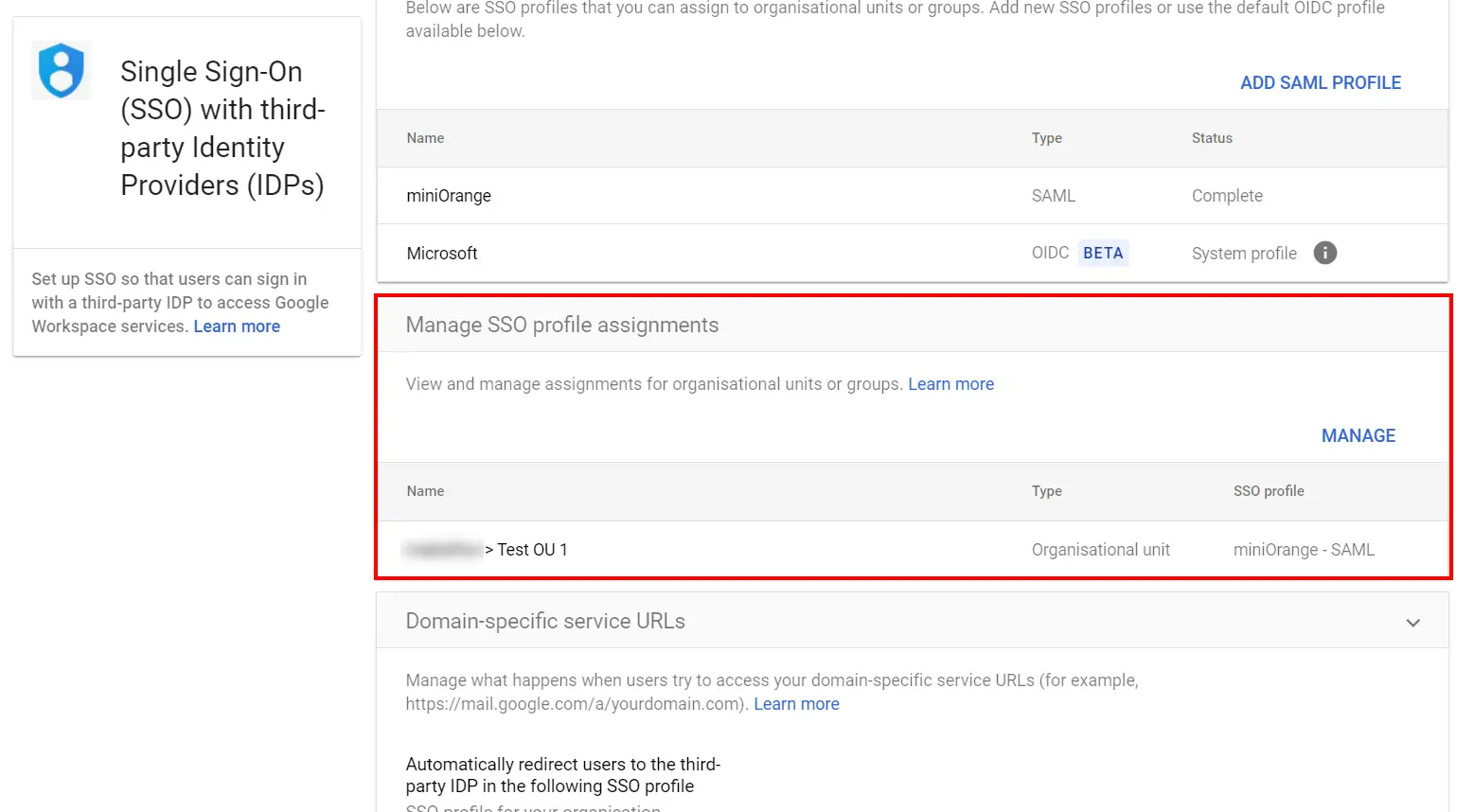
Note: If the SSO profile assignment for an OU or group differs from your domain-wide profile assignment,
an override warning appears when you select that OU or group. You can’t assign the SSO profile on a
per-user basis. The Users view let you check the setting for a specific user.
If you want to turn off the third-party authentication for all your users without changing the SSO profile assignment for OUs or groups, you can disable the third-party SSO profile:
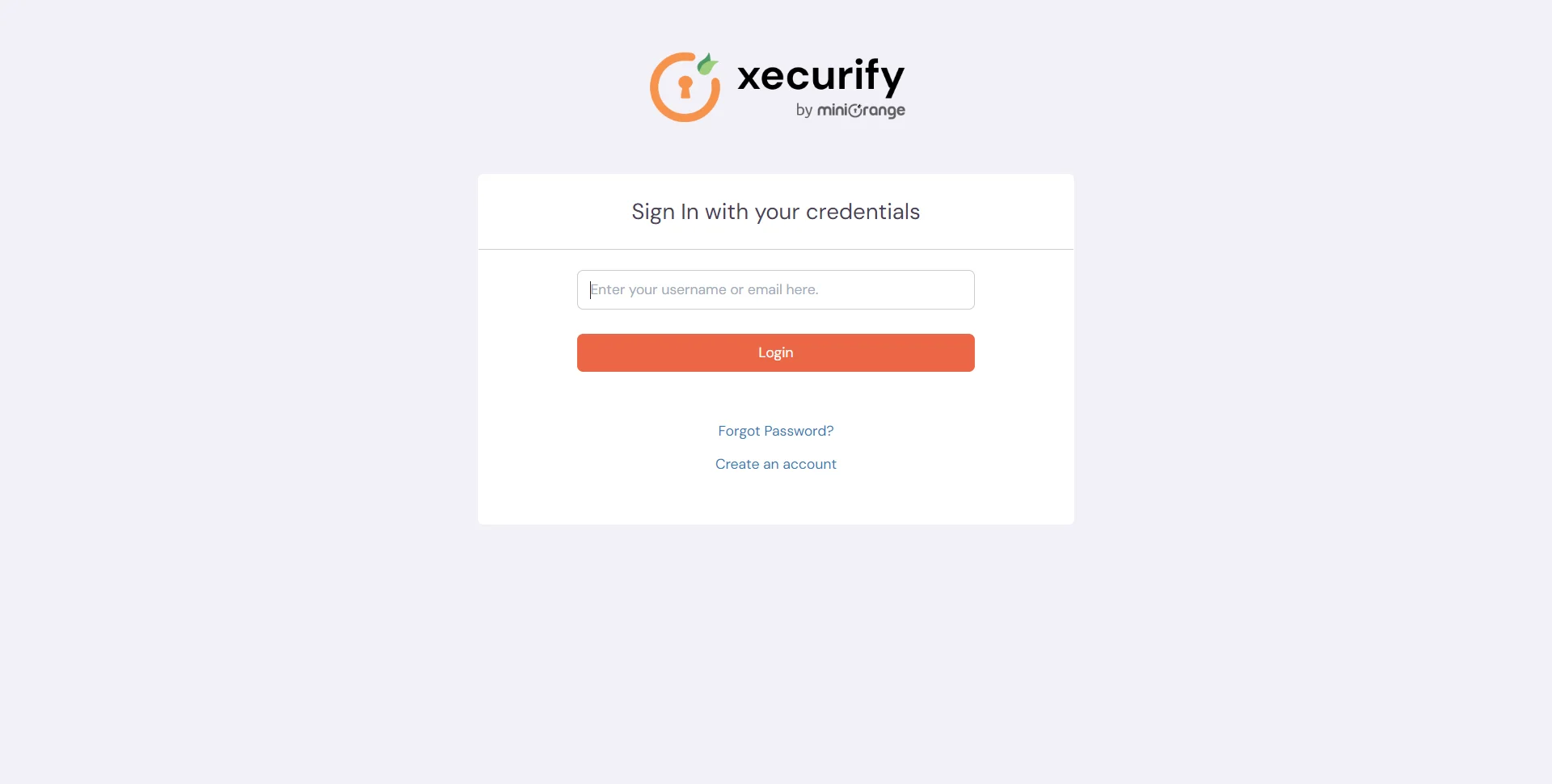
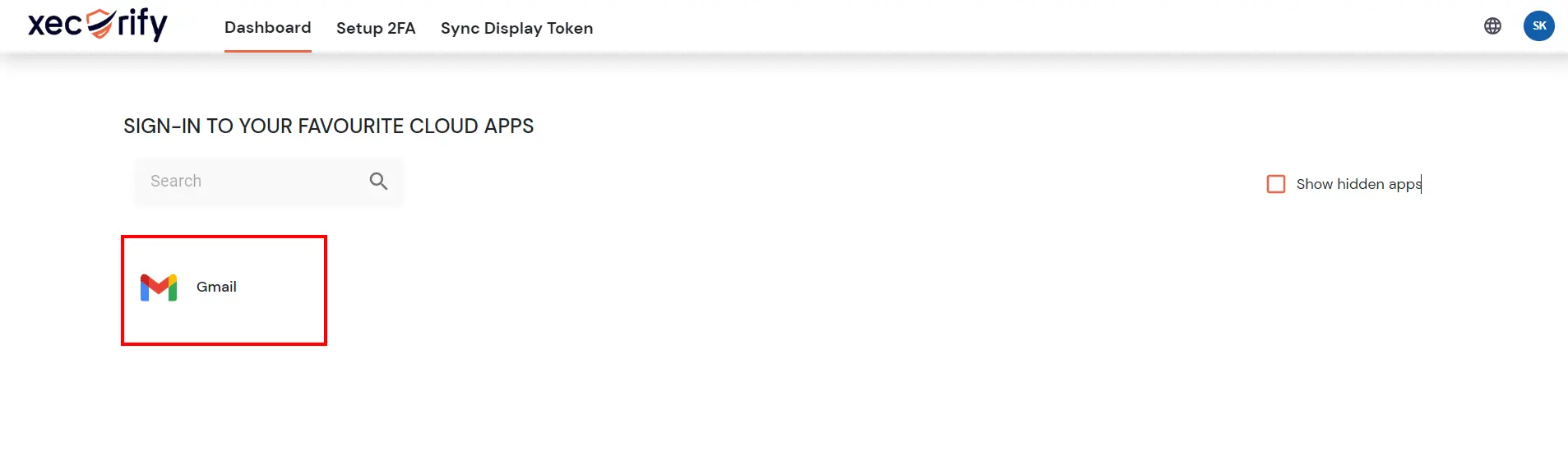
Test SSO login to your Google Apps account with miniOrange IdP:
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.
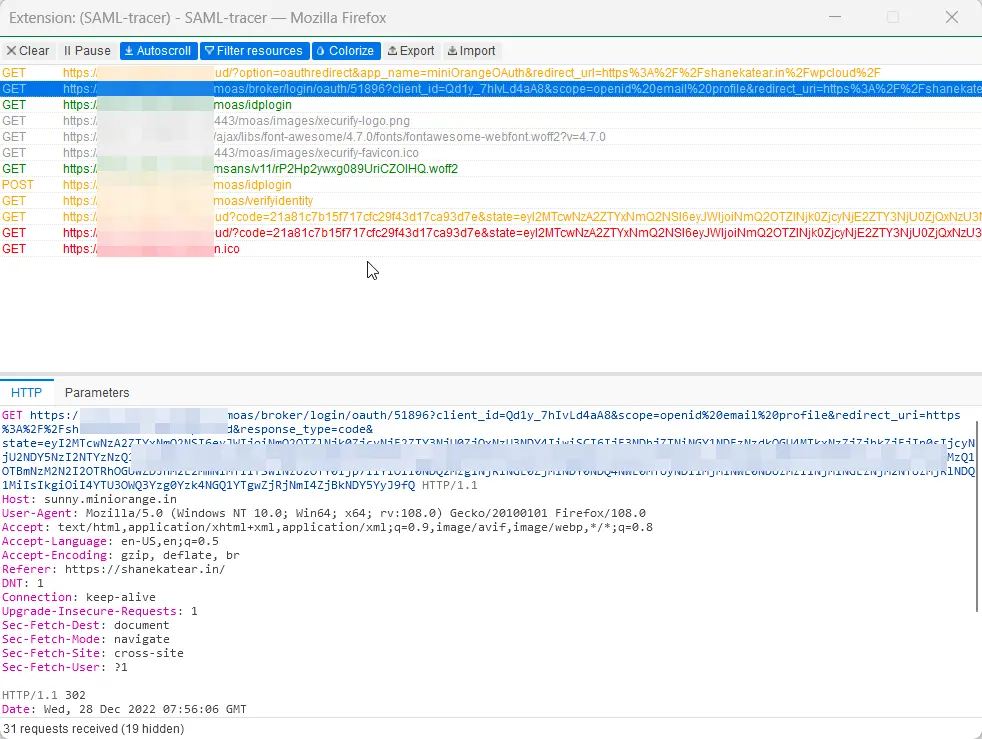
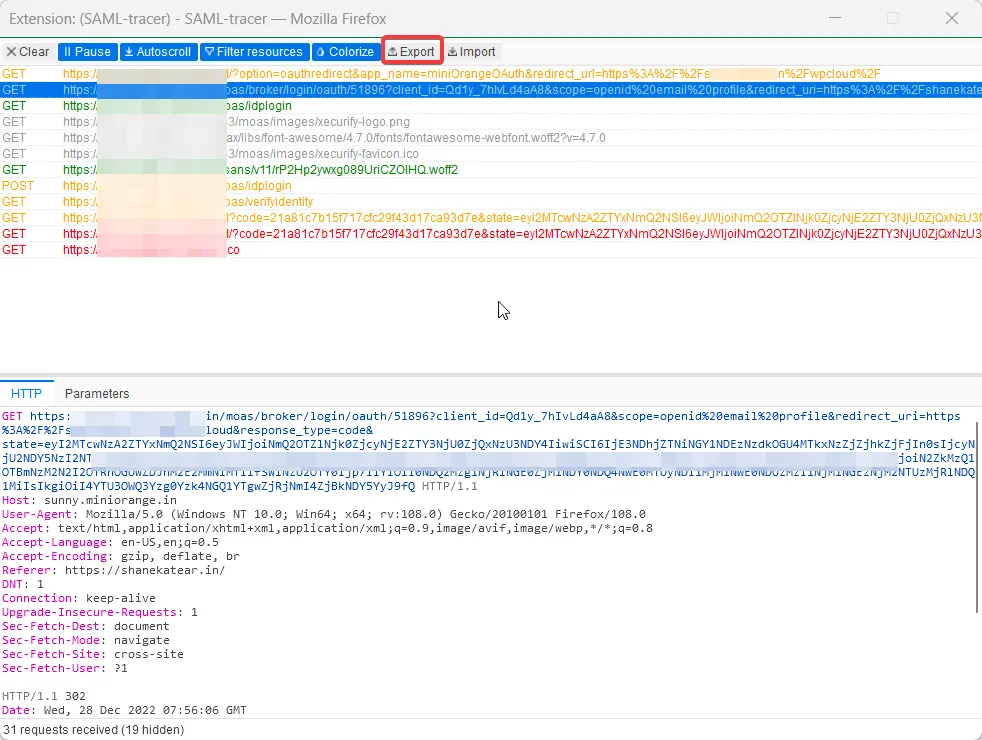
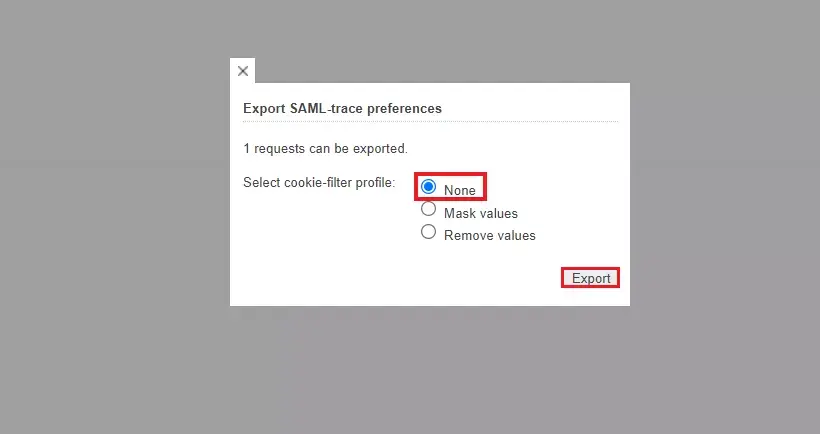
For Firefox: Add SAML tracer Add-On from the Firefox marketplace.
For Chrome / Edge or Chromium-based browsers: Install the SAML tracer extension from Chrome Webstore.