Oracle Primavera Single Sign-On (SSO)
Configure Oracle Primavera SSO in a few simple steps using this setup guide. miniOrange Single Sign-On (SSO) helps you to log in to Oracle Primavera and other applications using a single set of credentials. Upon enabling SSO for Oracle Primavera, a person can securely access Oracle Primavera in one click without having to enter their username and password again.
With miniOrange Oracle Primavera SSO, you can:
- Enable your users to automatically login to Oracle Primavera
- Have centralized and easy access control of the users
- Connect easily with any external identity source like Azure AD, ADFS, Cognito, etc
Get Free Installation Help
miniOrange offers free help through a consultation call with our System Engineers to Install or Setup Oracle Primavera SSO solution in your environment with 30-day free trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you in no time.
Get Help
Supported SSO Features:
- SP Initiated SSO Login: Users can access their Redmine account via a URL or bookmark. They will automatically be redirected to the miniOrange portal for login. Once they've signed on, they'll be automatically redirected and logged into Redmine.
- IdP Initiated SSO Login: Users need to login to the miniOrange first, and then click on the Redmine icon on the applications dashboard to access Redmine.(If you have set up any more Identity Sources, you will log in to that platform).
- JIT Provisioning: Enables the automatic creation of user accounts in Redmine when a person logs in for the first time via Desktop SSO, IDP, or Active Directory (AD) authentication.
- Single Logout: With this feature, you will be automatically logged out of all the applications that are connected with Identity provider (IdP) when you log out from Redmine org or any other app.
- Mandate users to Login using SSO: Single Sign-on can make it mandatory for all users to log in using SSO. This will prevent any person from login using any other source and bypassing the login system. No person will be able to have direct login making it a streamline and secure process.
Connect with External Source of Users
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
Prerequisites:
Click here to see the Premavera installation and configuration steps.
Follow the step-by-step guide to setup Oracle Primavera Single Sign-On (SSO)
1. Configure Oracle Primavera in miniOrange
- Login into miniOrange Admin Console.
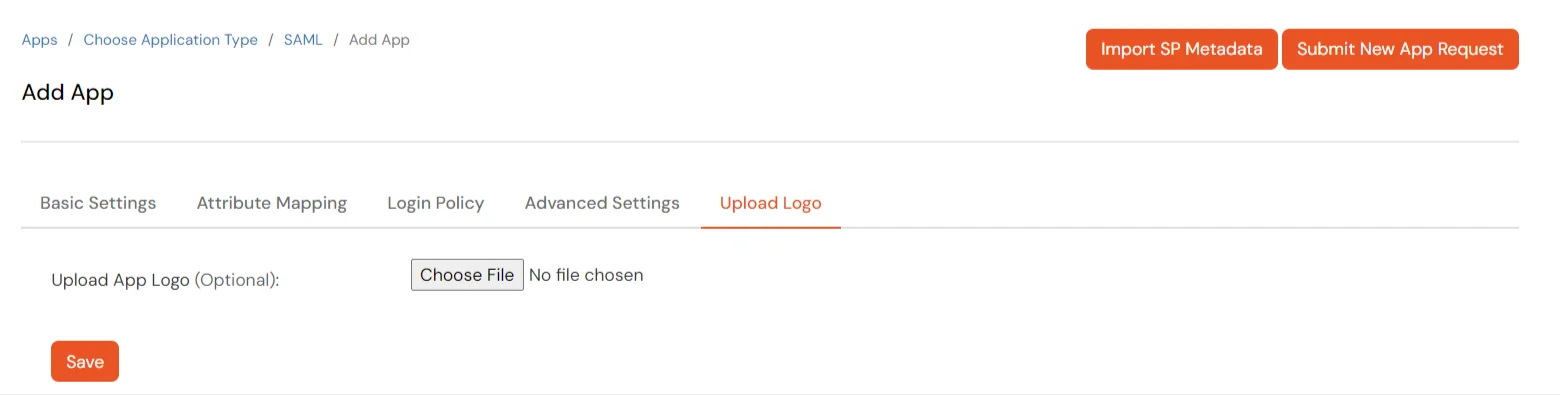
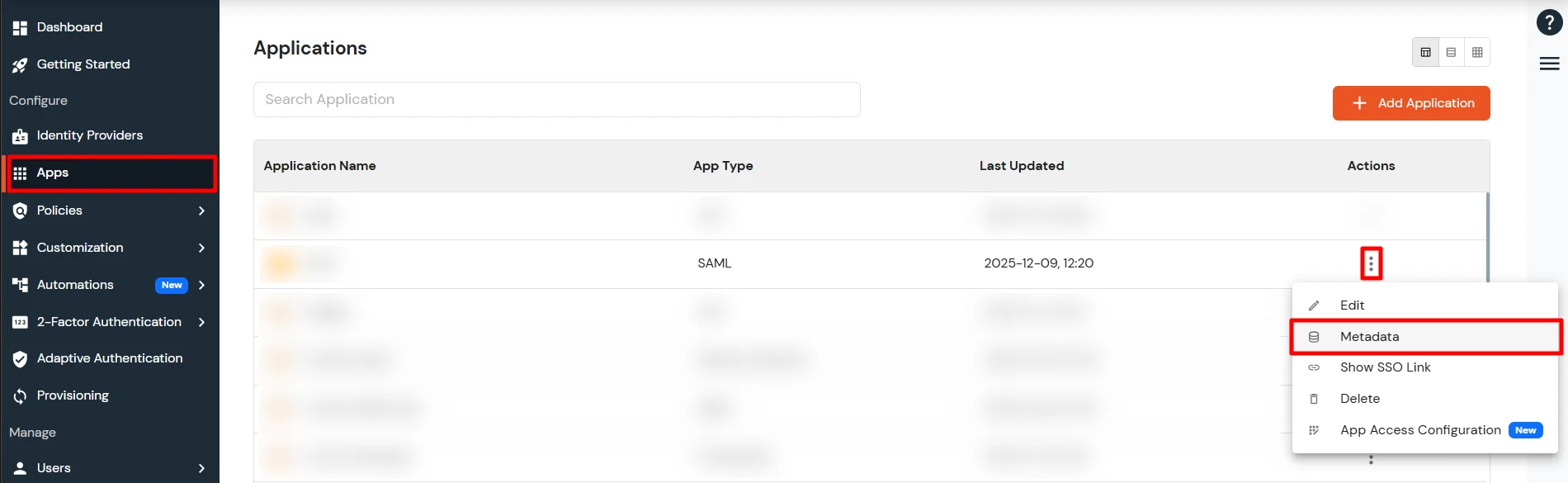
- Go to Apps and click on Add Application button.

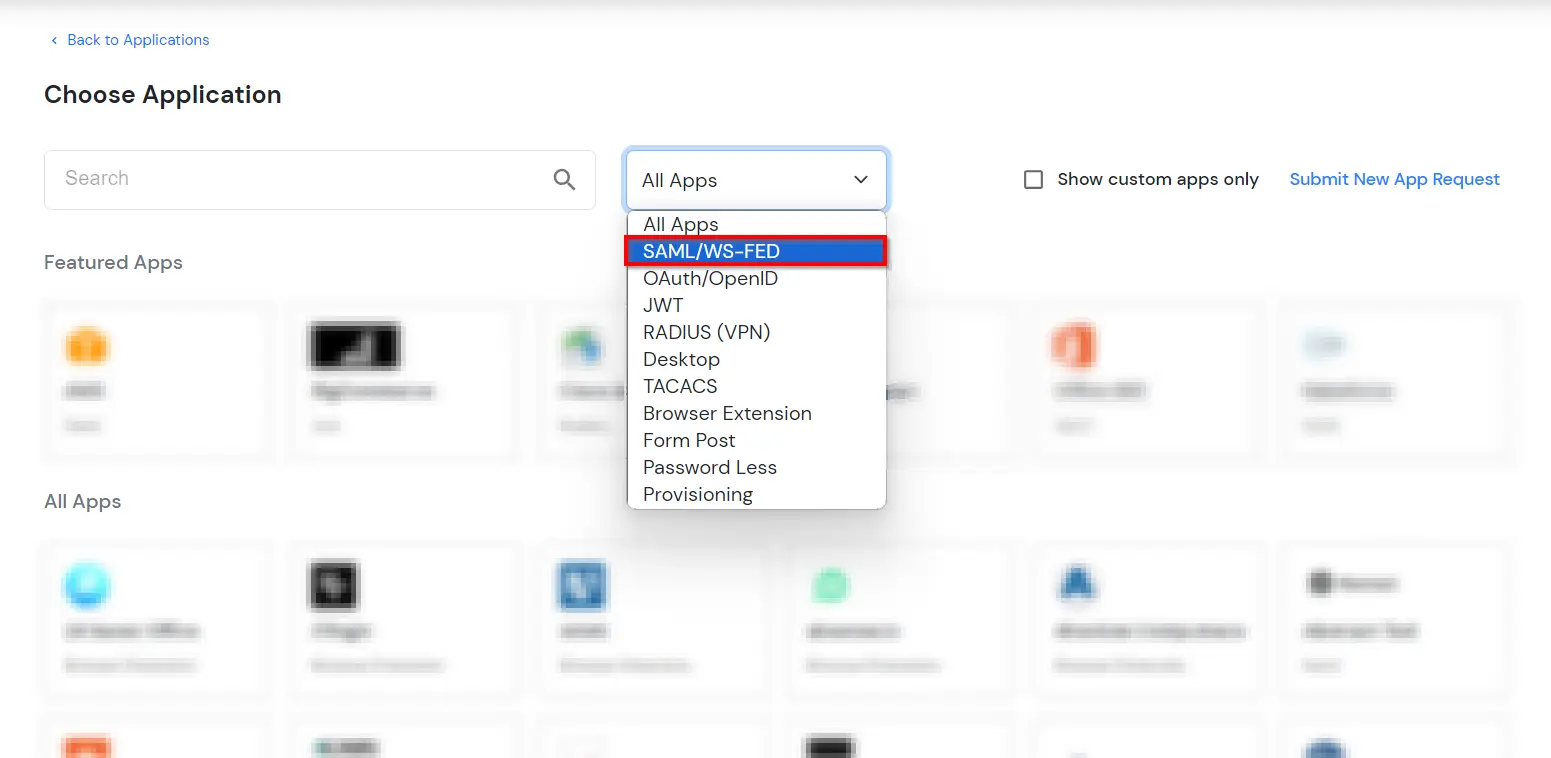
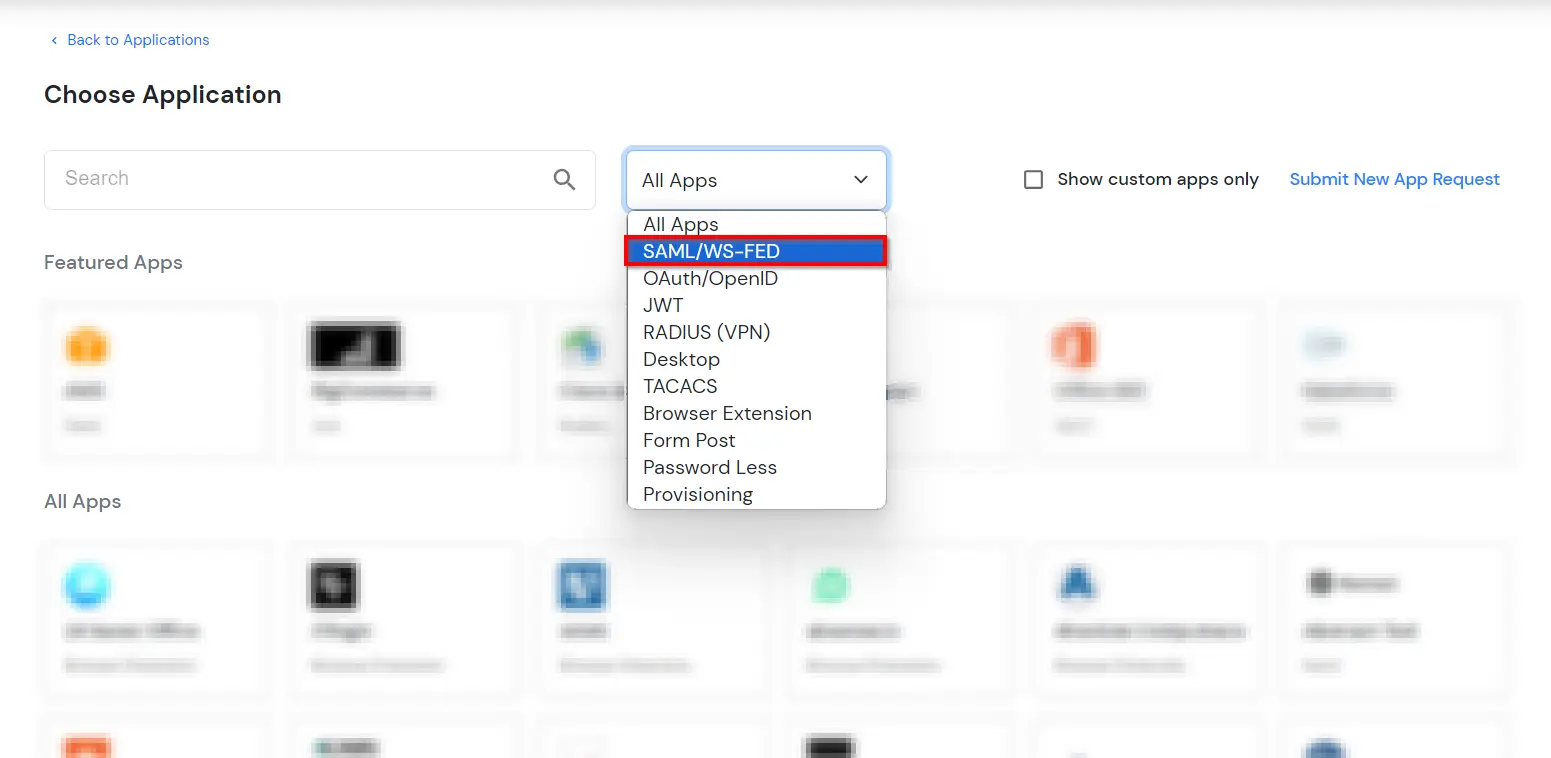
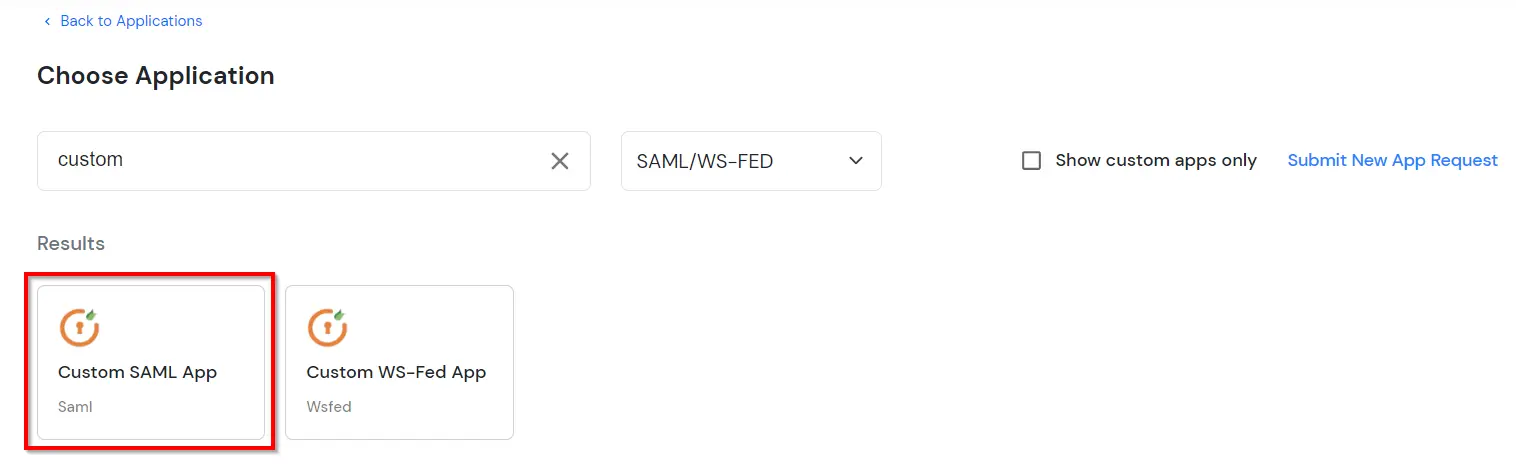
- In Choose Application Type, select SAML/WS-FED from the All Apps dropdown.
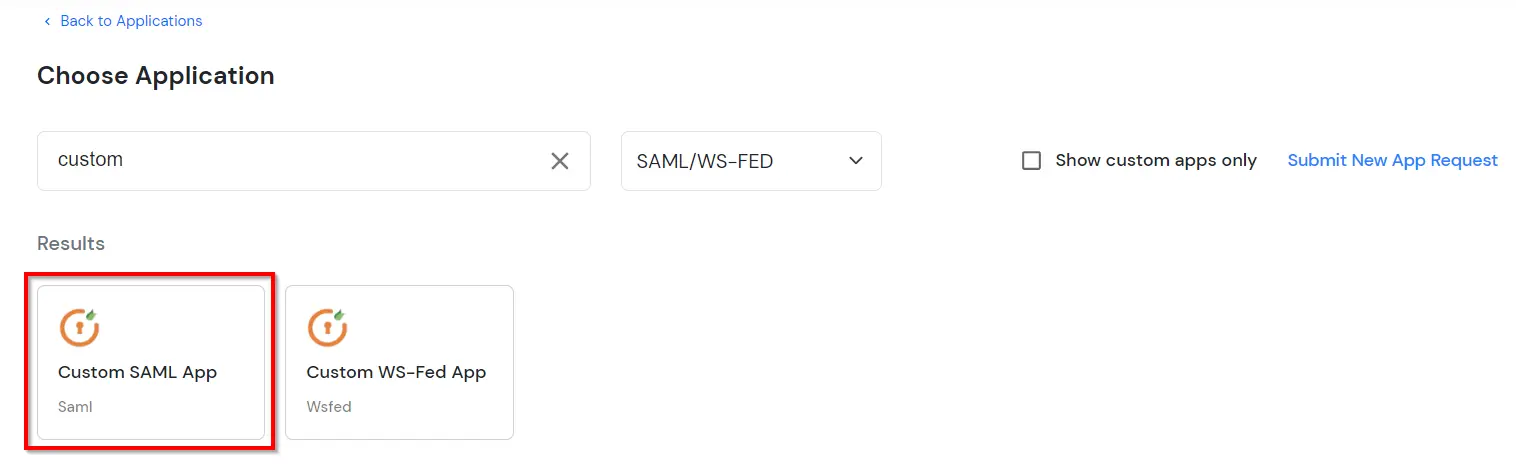
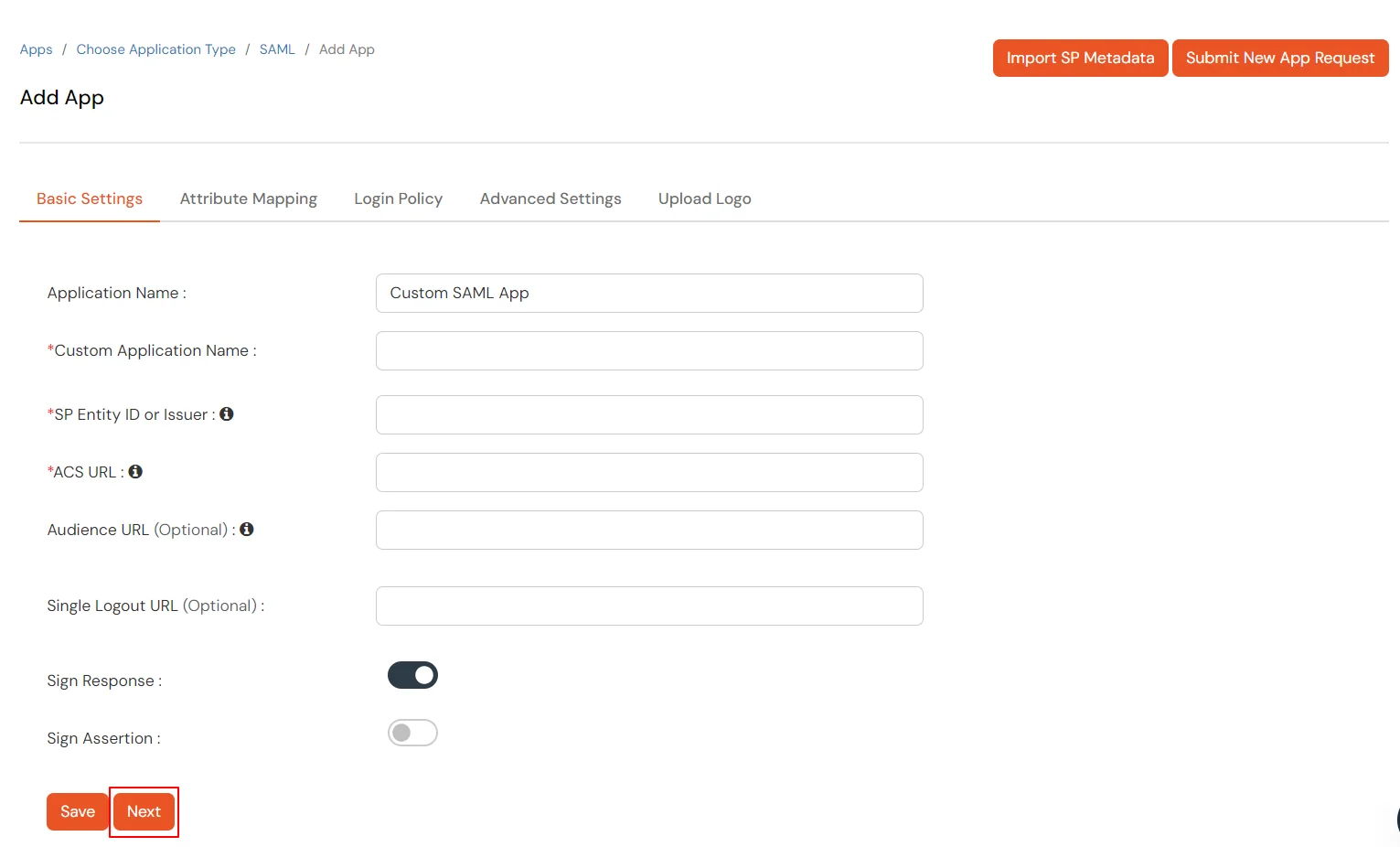
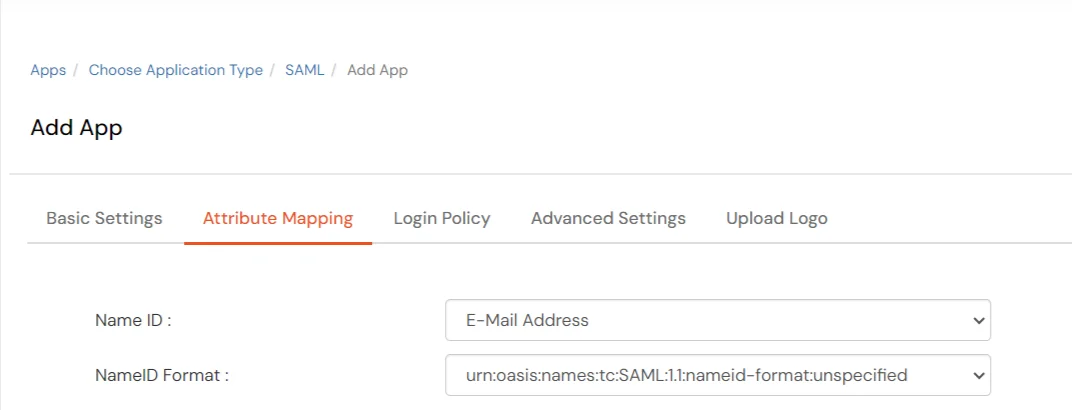
- Search for Oracle Primavera in the list, if you don't find Oracle Primavera in the list then, search for custom and you can set up your application in Custom SAML App.
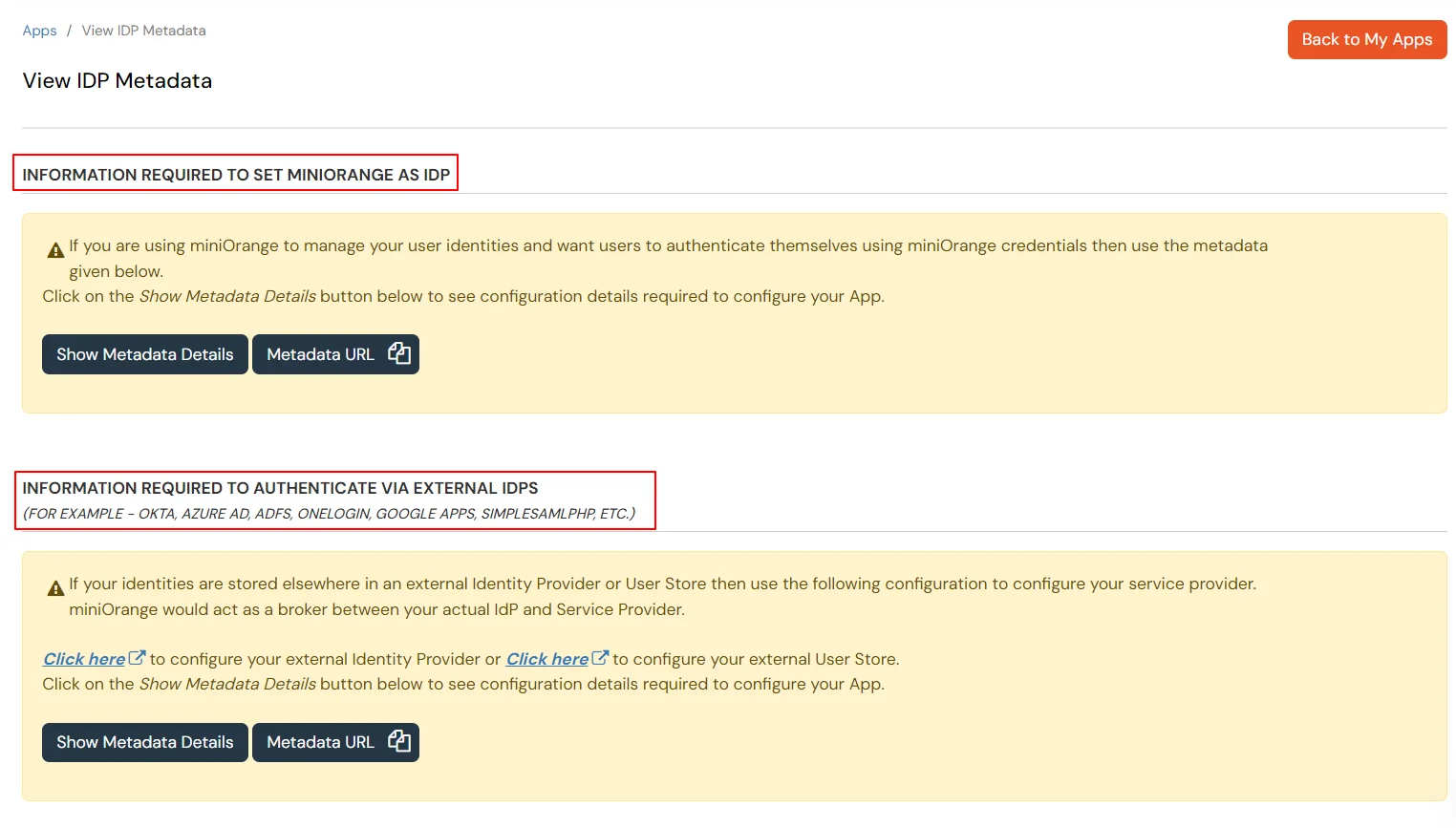
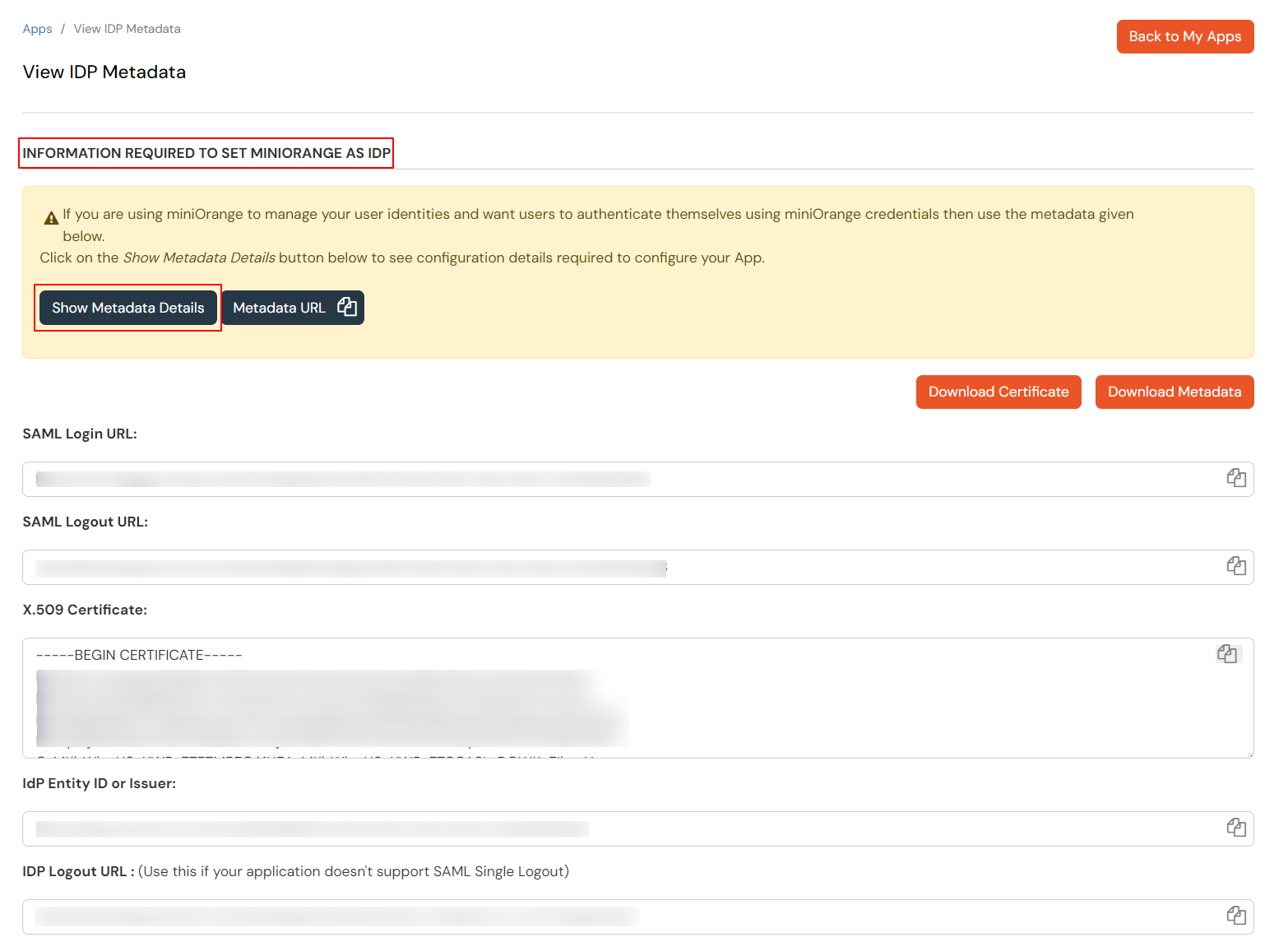
2. Configure SSO in Oracle Primavera P6 EPPM
- Open the Primavera P6 Administrator.
- In Authentication choose your configuration from the drop-down.
- Select Authentication.
- Under Login Mode dropdown menu, select WebSSO.
- To configure Web Single Sign-On settings:
Note: Need to change these settings require you to restart P6 server.
- Select Allow Alternate Login Attribute when using Oracle Single Sign-On, and you want to use an SSO login attribute other than the P6 user name. For example, you will enter your email address when authenticating Oracle Single Sign-On, but your P6 user name will map to the LDAP's UID field.
- In User Name Header Key field, enter the name of the HTTP Header you specified in the policy server.
The value you specify must match the property you created under the policy domain/realm, where the Web server for P6 resides.
For Oracle Single Sign-On, the value should be Proxy-Remote-User. The Proxy-Remote-User should match the LDAP server attribute that maps to the P6 EPPM database USER_NAME field. See Provisioning LDAP User Information for the First Time for details.
For Oracle Access Manager, the value should be OAM_REMOTE_USER, which is the default value.
- In the Context Path Override field, enter the path used to pass web requests from the Single Sign-On Web server to the P6 server. The default listed is the value for P6 (/p6).
Note: If you enable the Allow Alternate Login Attribute setting, you must configure the Header Key and LDAP Search Attribute settings. You must also configure the LDAP settings for the appropriate database instance to establish a connection to the LDAP server. See Provisioning LDAP User Information for the First Time for details.
- In Header Key field, enter the HTTP Header Key which contains the global user ID. The default value is Osso-User-Guid.
- In LDAP Search Attribute field, enter the LDAP attribute searched by the Header Key to authenticate users. The default value is orclguid.
Note: You must configure the LDAP settings for the appropriate database instance to establish a connection to the LDAP server.
- Click on Save.
3. Test SSO Configuration
Test SSO login to your Oracle Primavera account with miniOrange IdP:
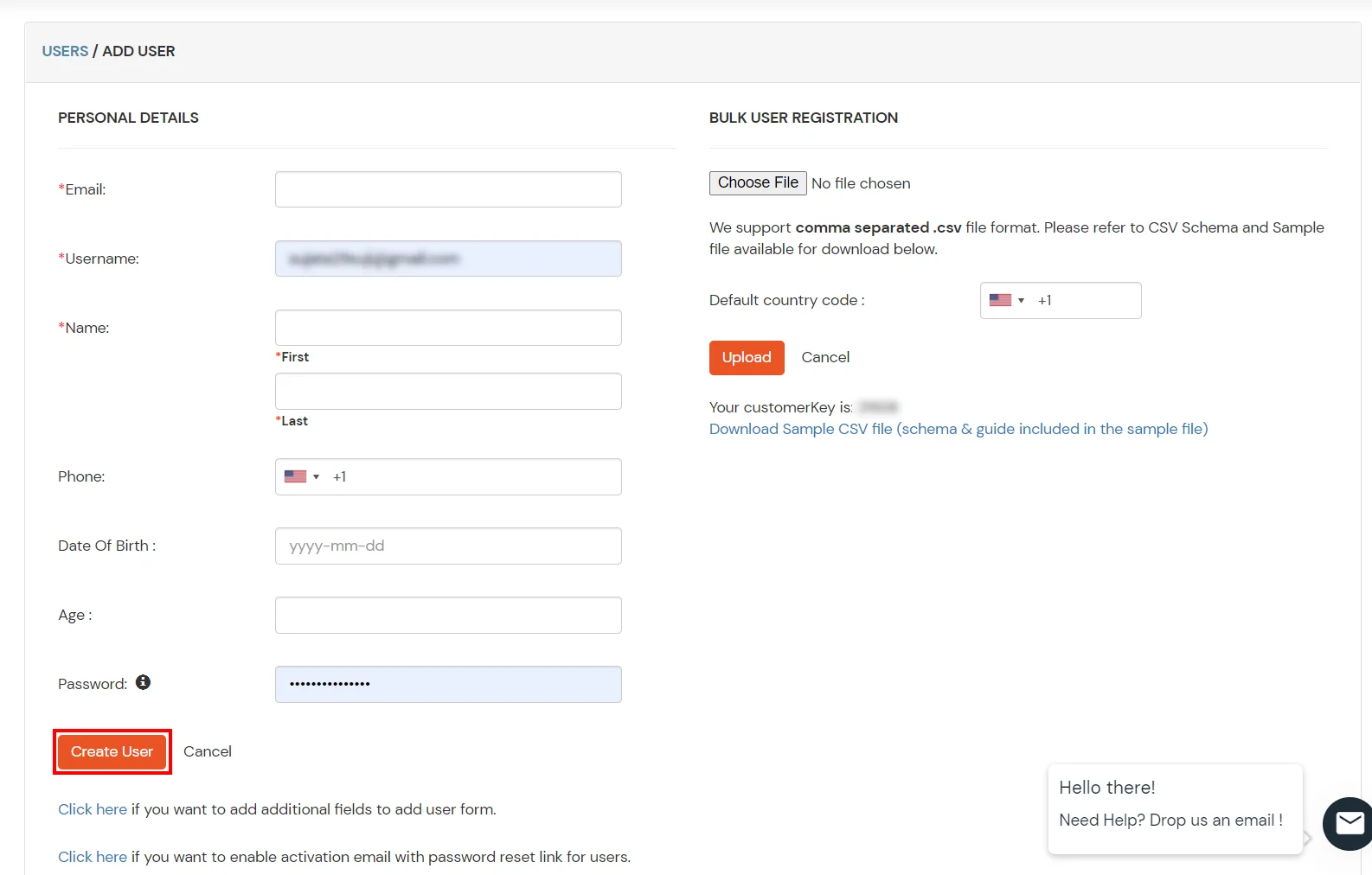
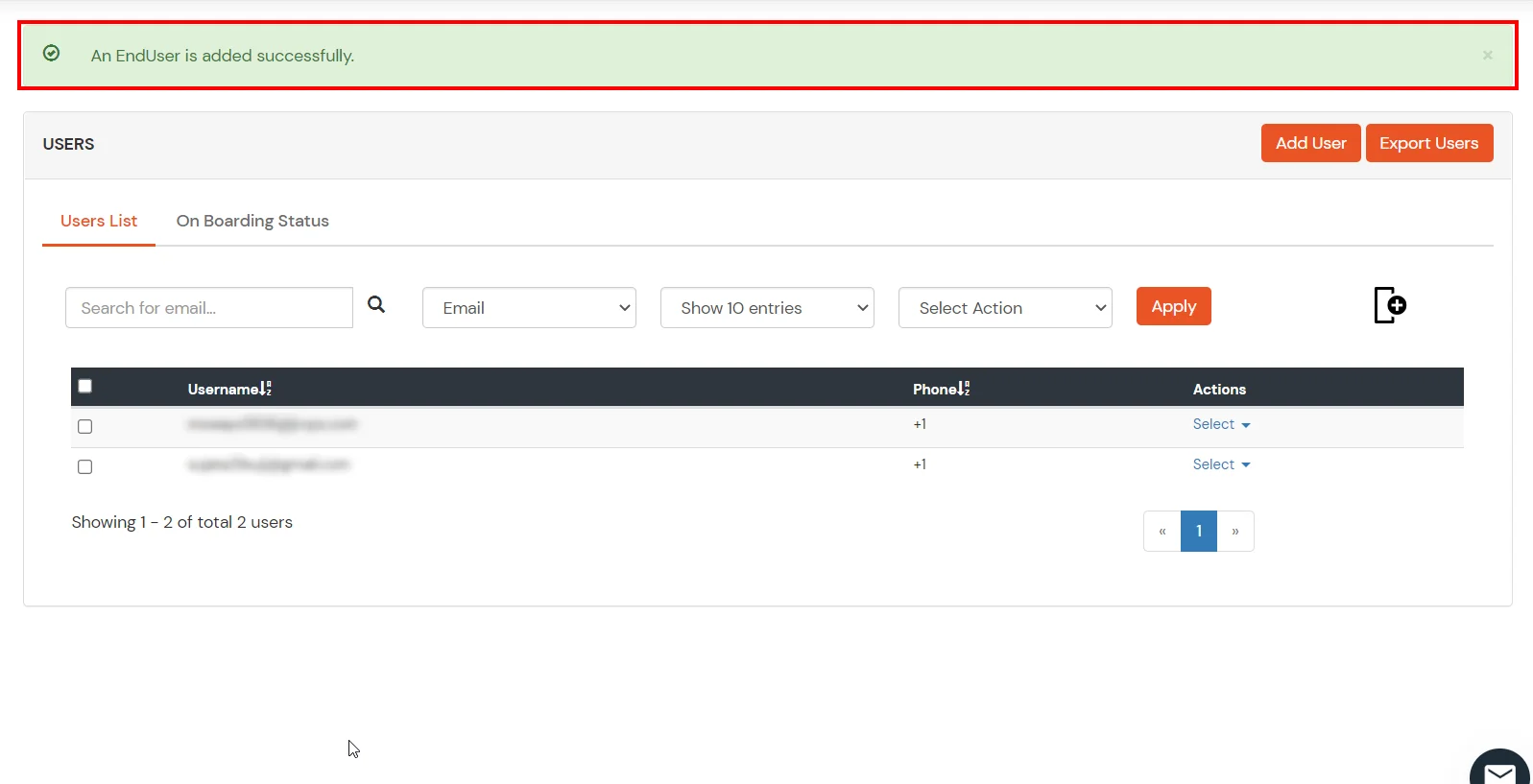
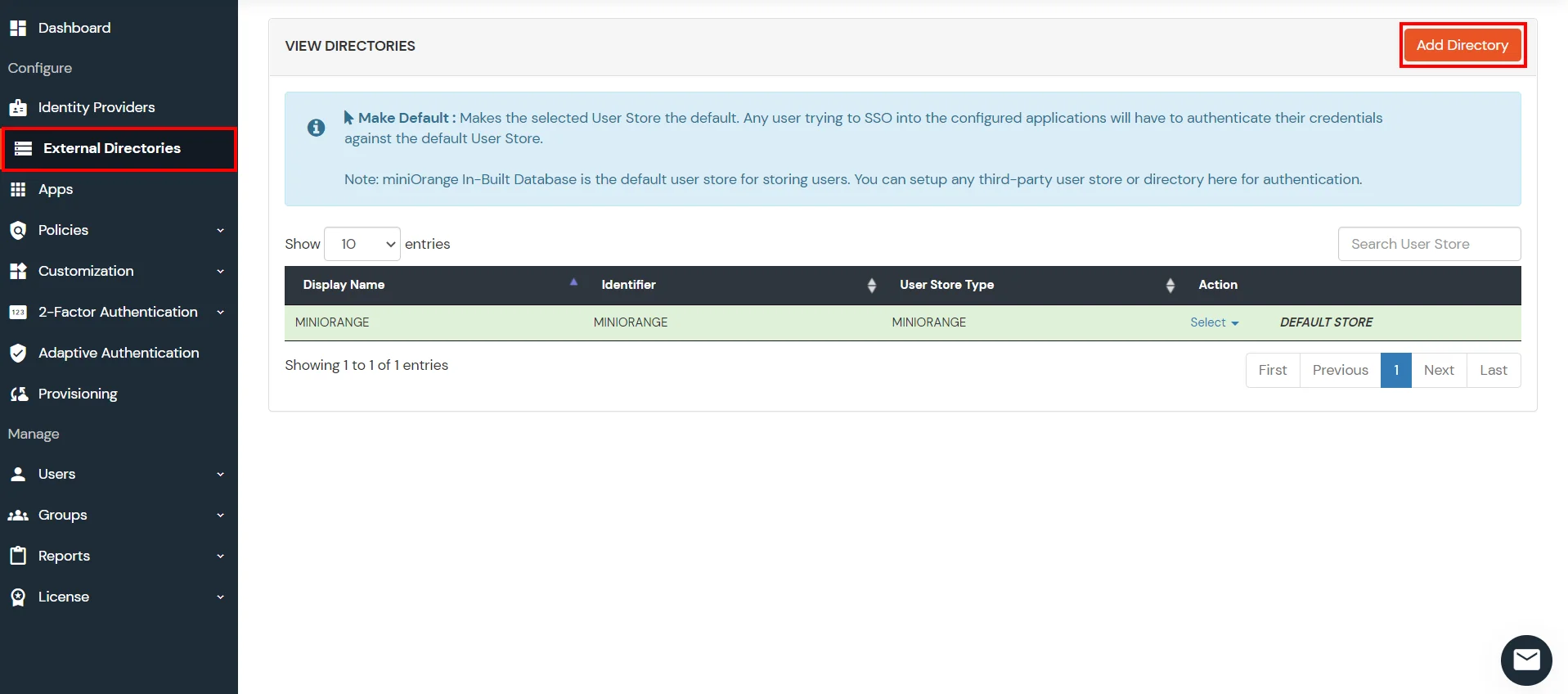
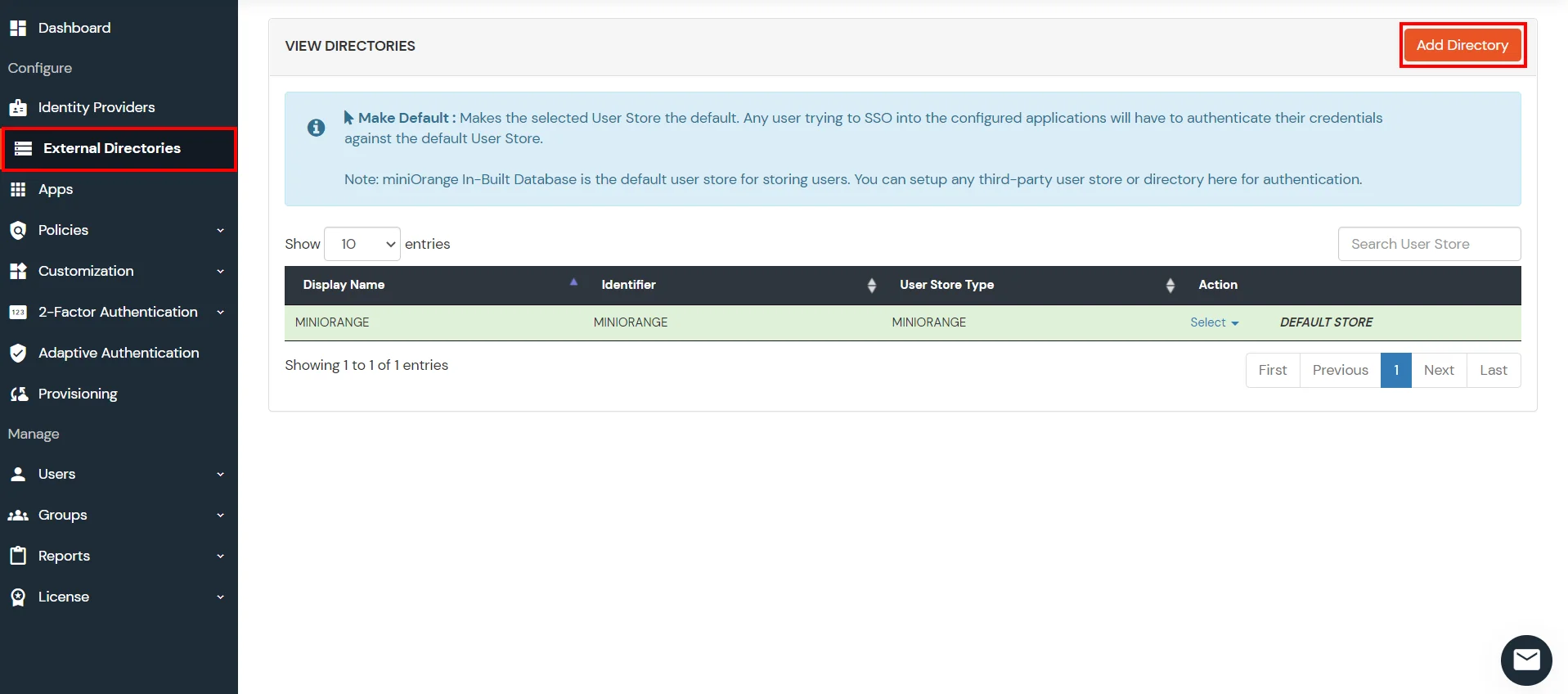
4. Configure Your User Directory (Optional)
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
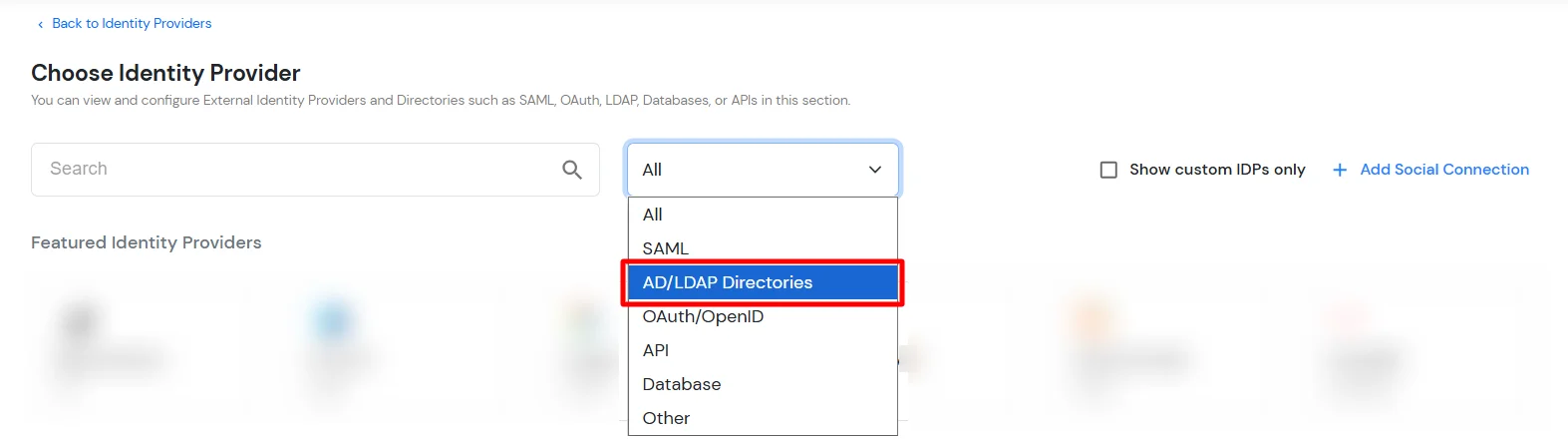
- Click on Identity Providers >> Add Identity Provider in the left menu of the dashboard
- In Choose Identity Provider, select AD/LDAP Directories from the dropdown.
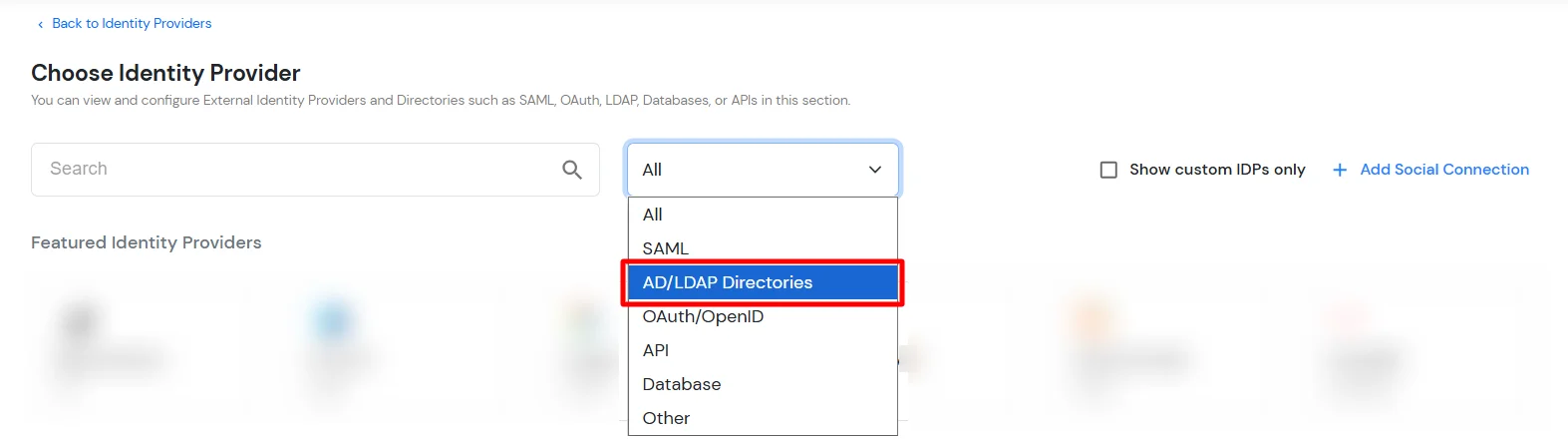
- Then search for AD/LDAP and click it.
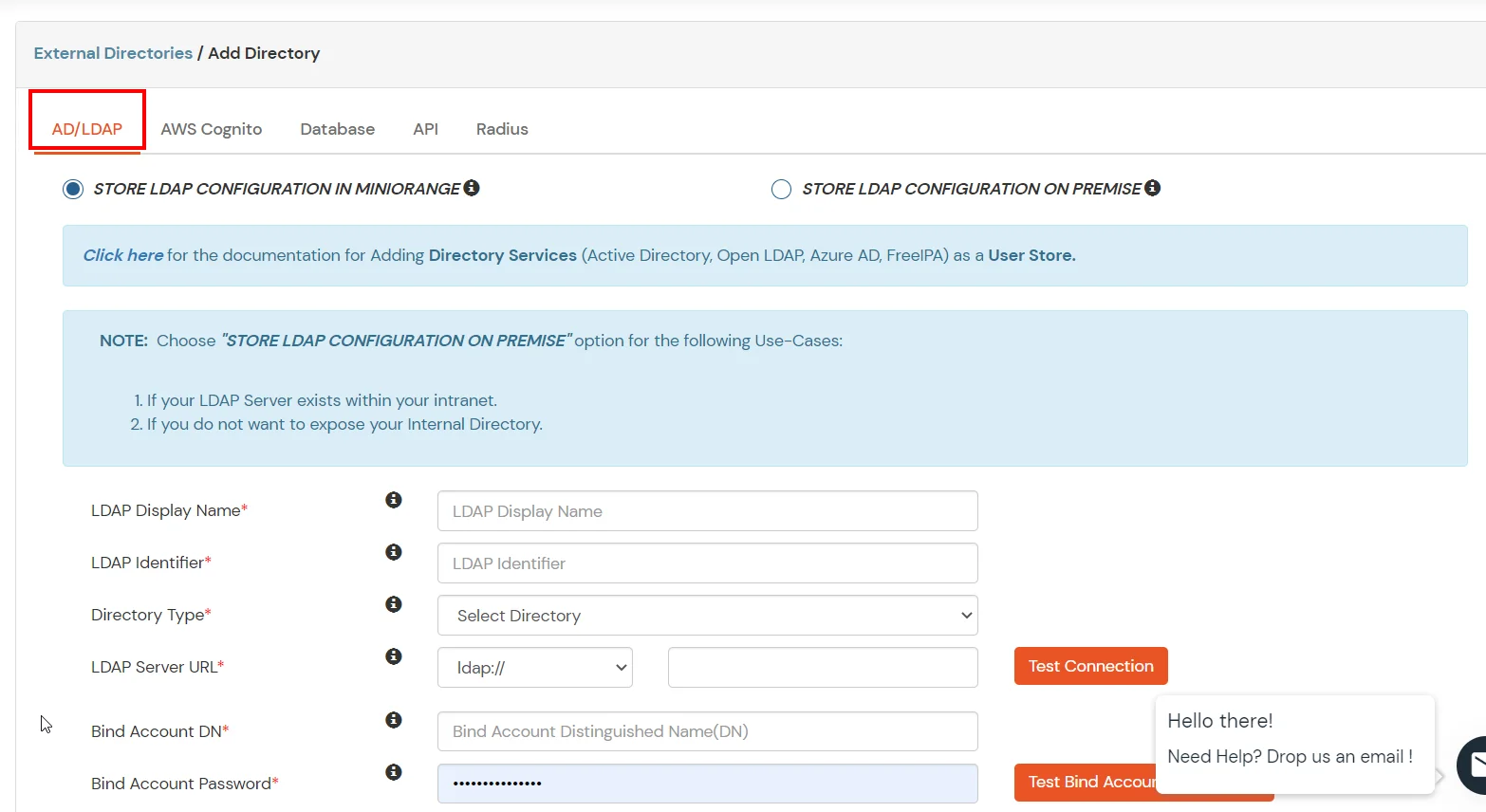
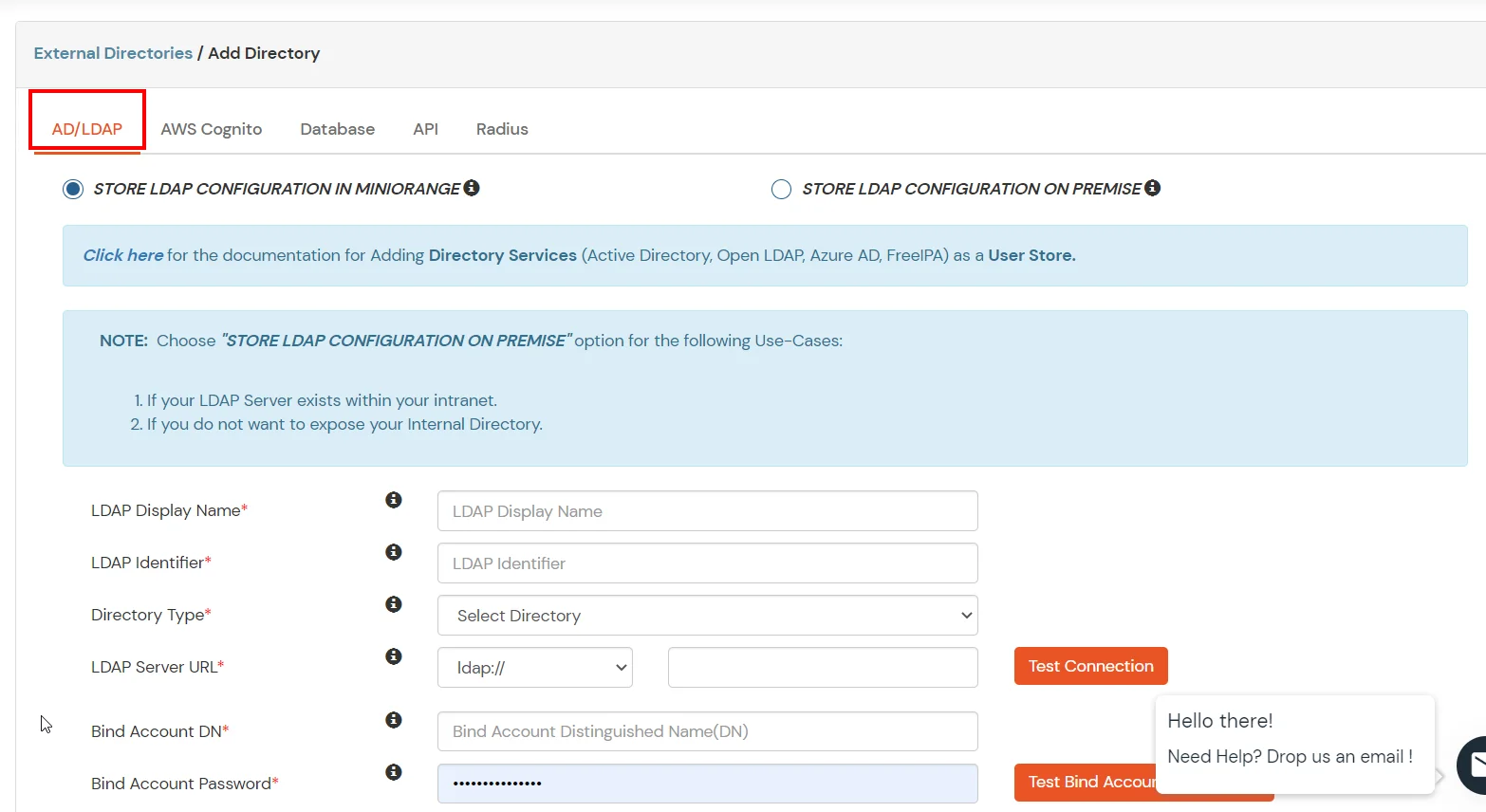
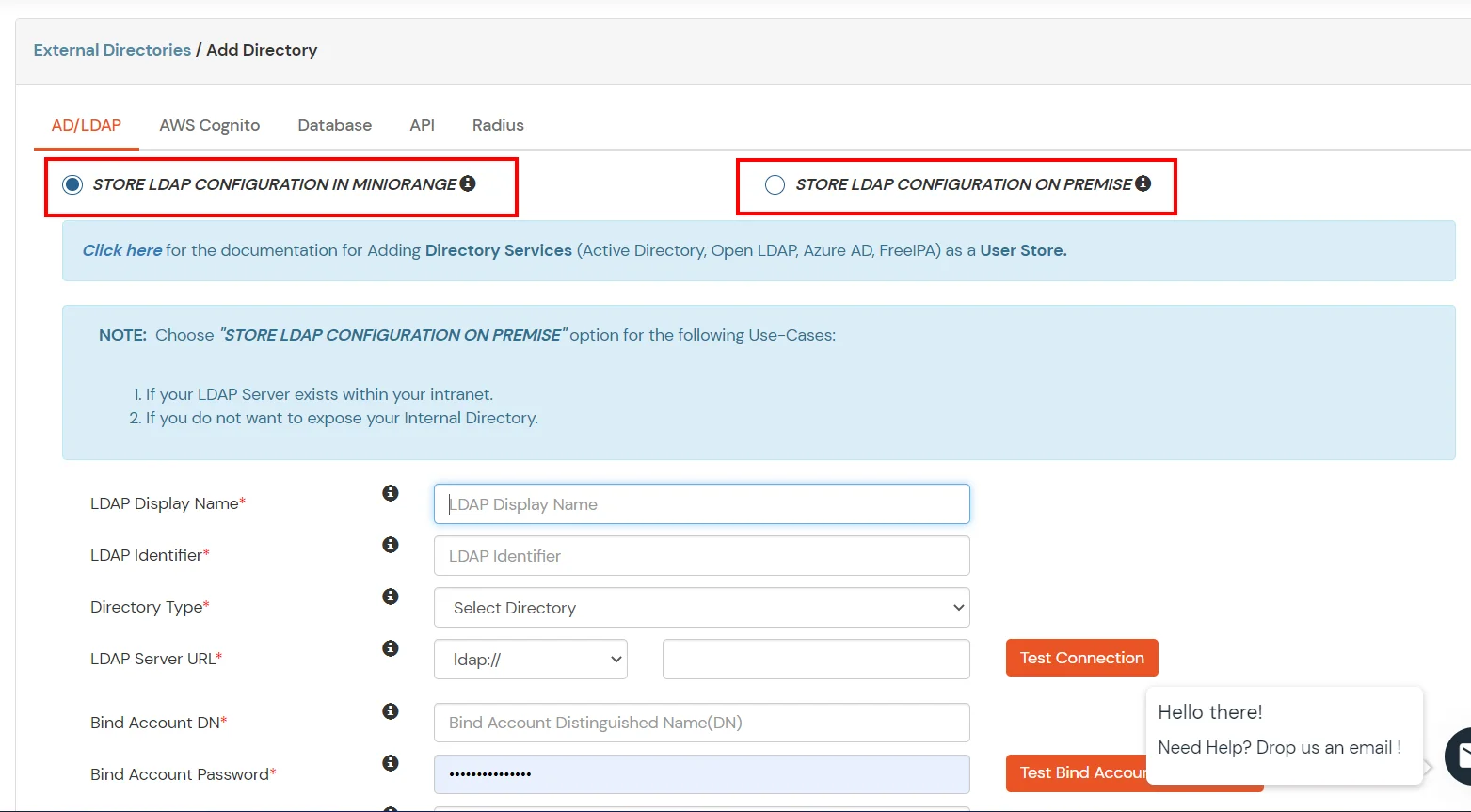
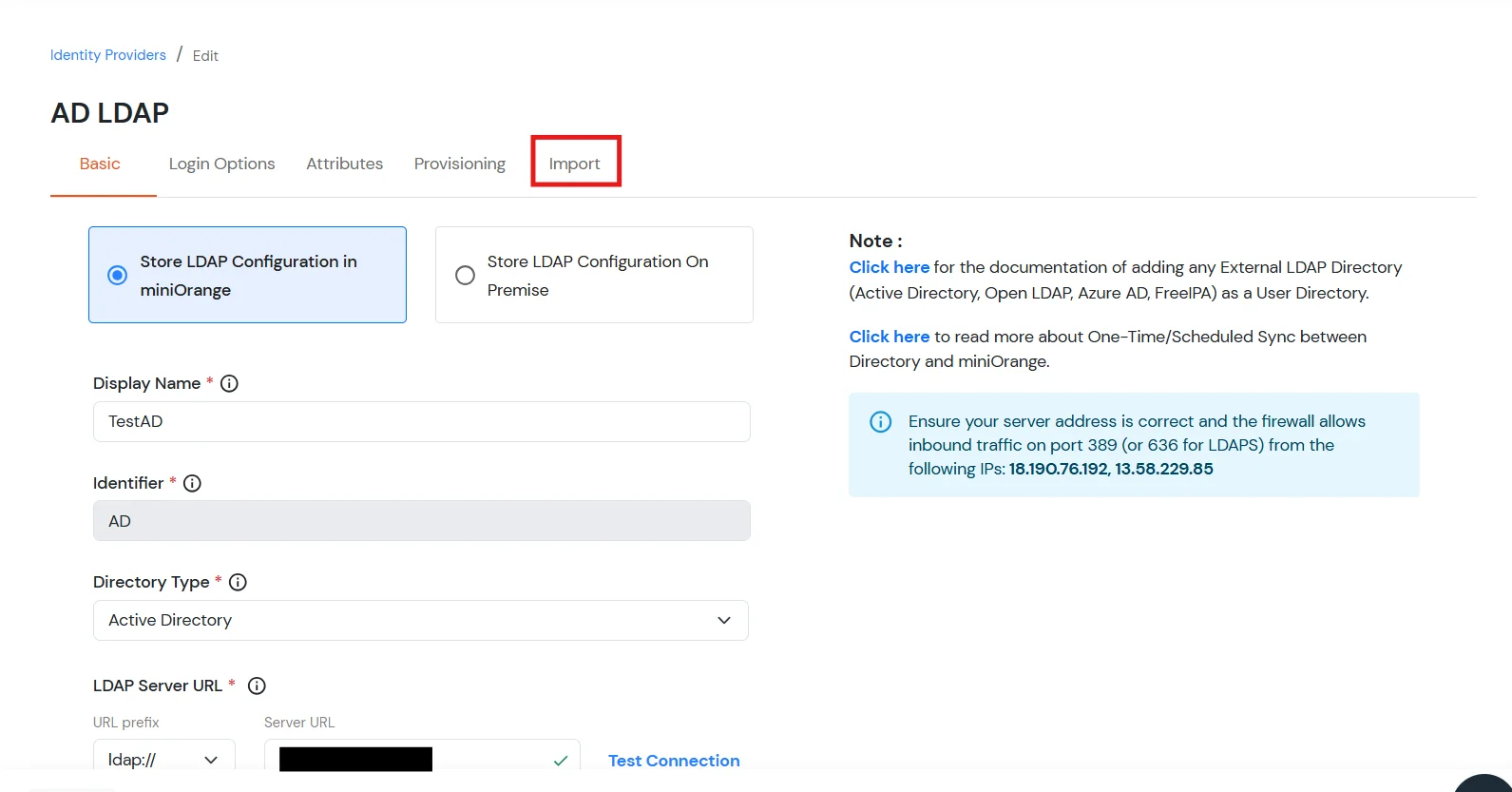
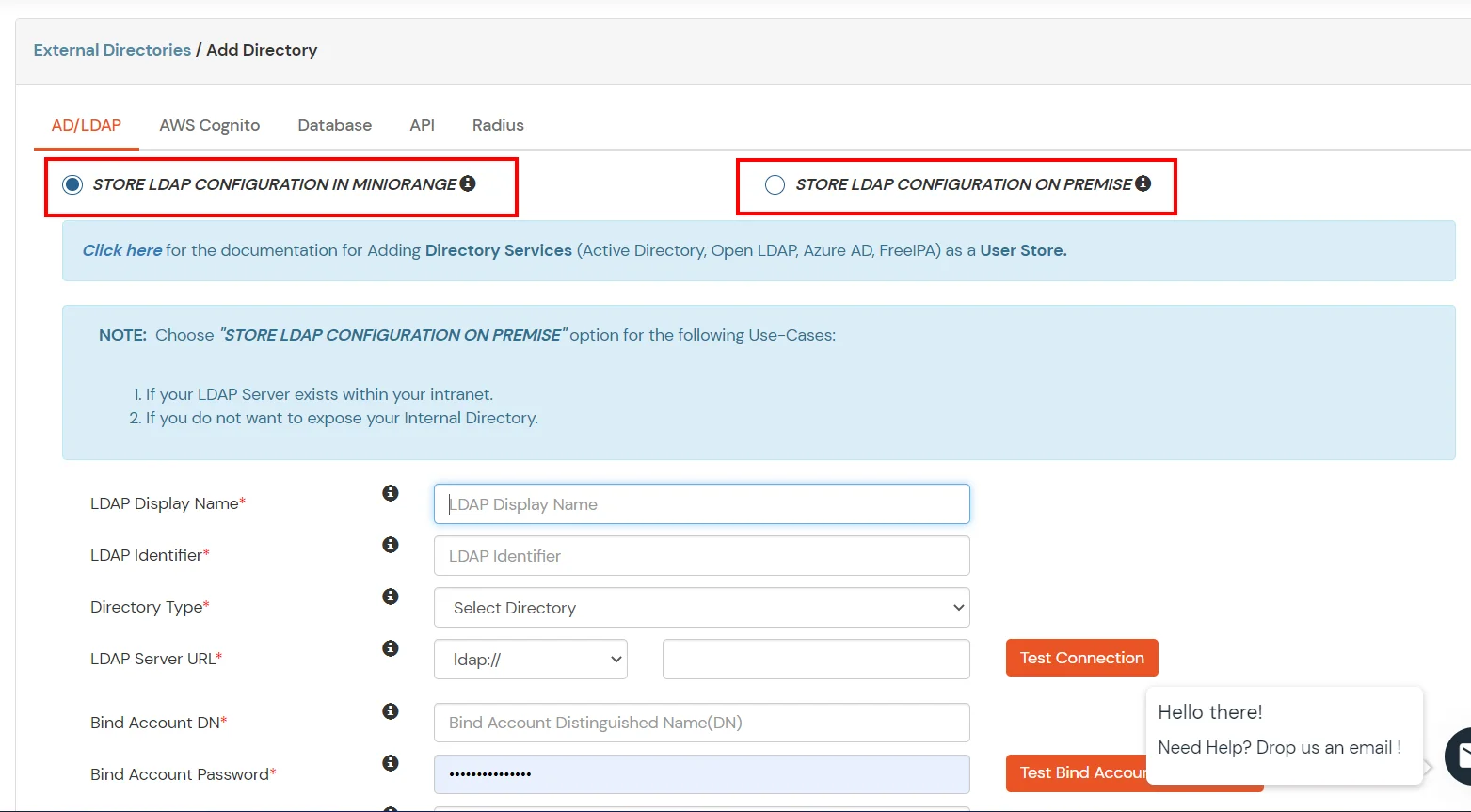
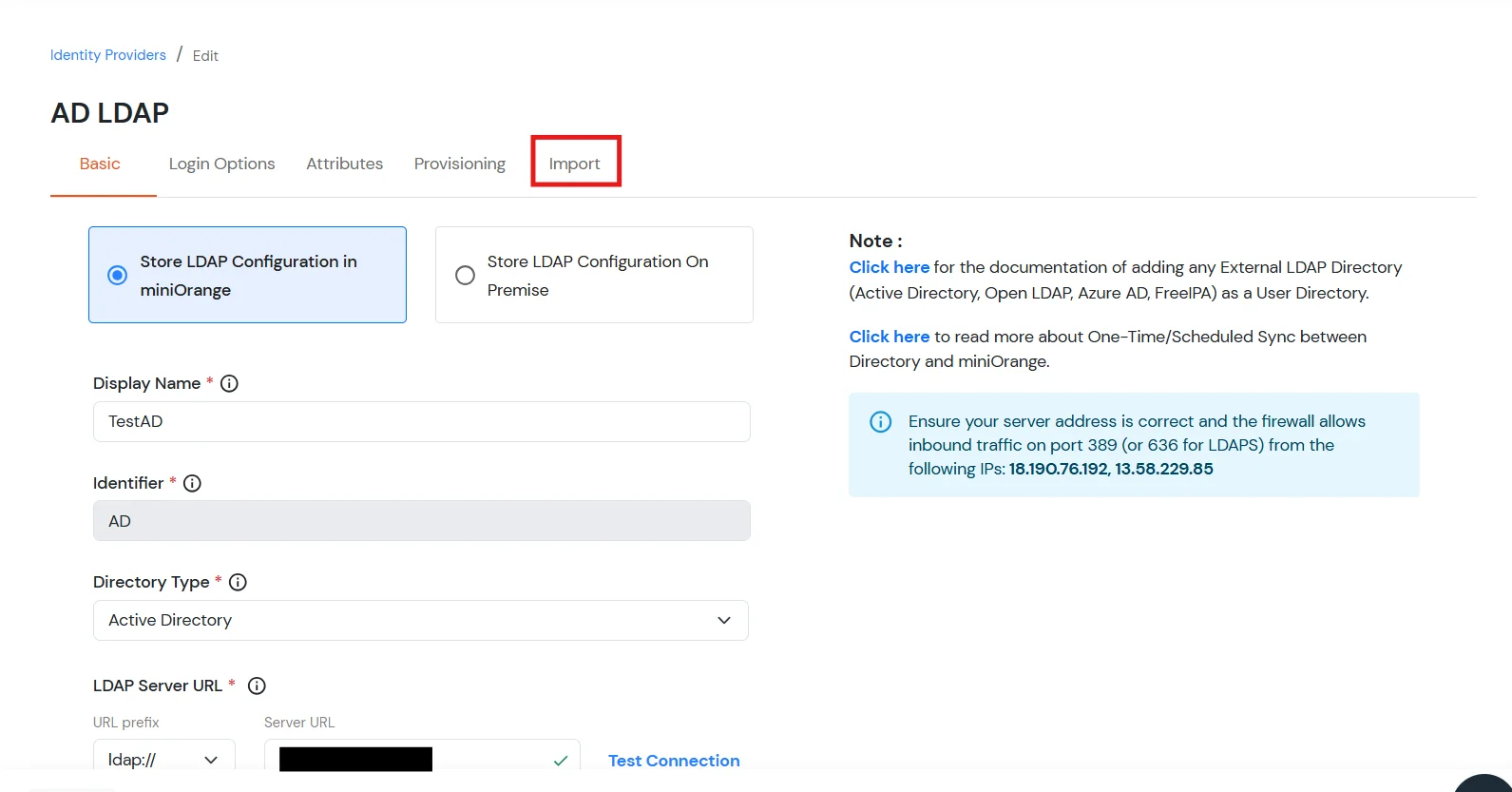
- STORE LDAP CONFIGURATION IN MINIORANGE: Choose this option if you want to keep your configuration in miniOrange. If the active directory is behind a firewall, you will need to open the firewall to allow incoming requests to your AD.
- STORE LDAP CONFIGURATION ON PREMISE: Choose this option if you want to keep your configuration in your premise and only allow access to AD inside premises. You will have to download and install miniOrange gateway on your premise.
- Enter AD/LDAP Display Name and Identifier name.
- Select Directory Type as Active Directory.
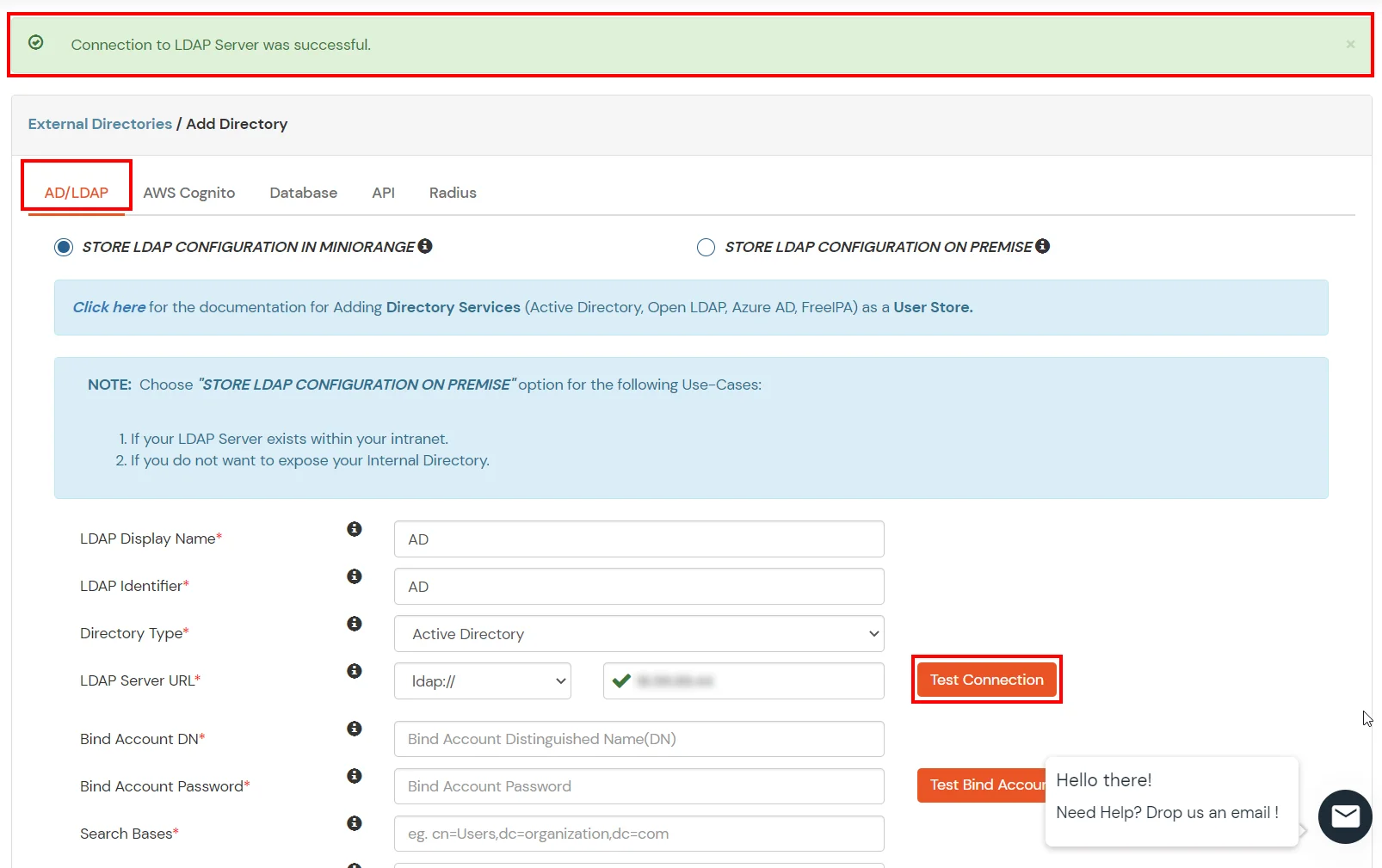
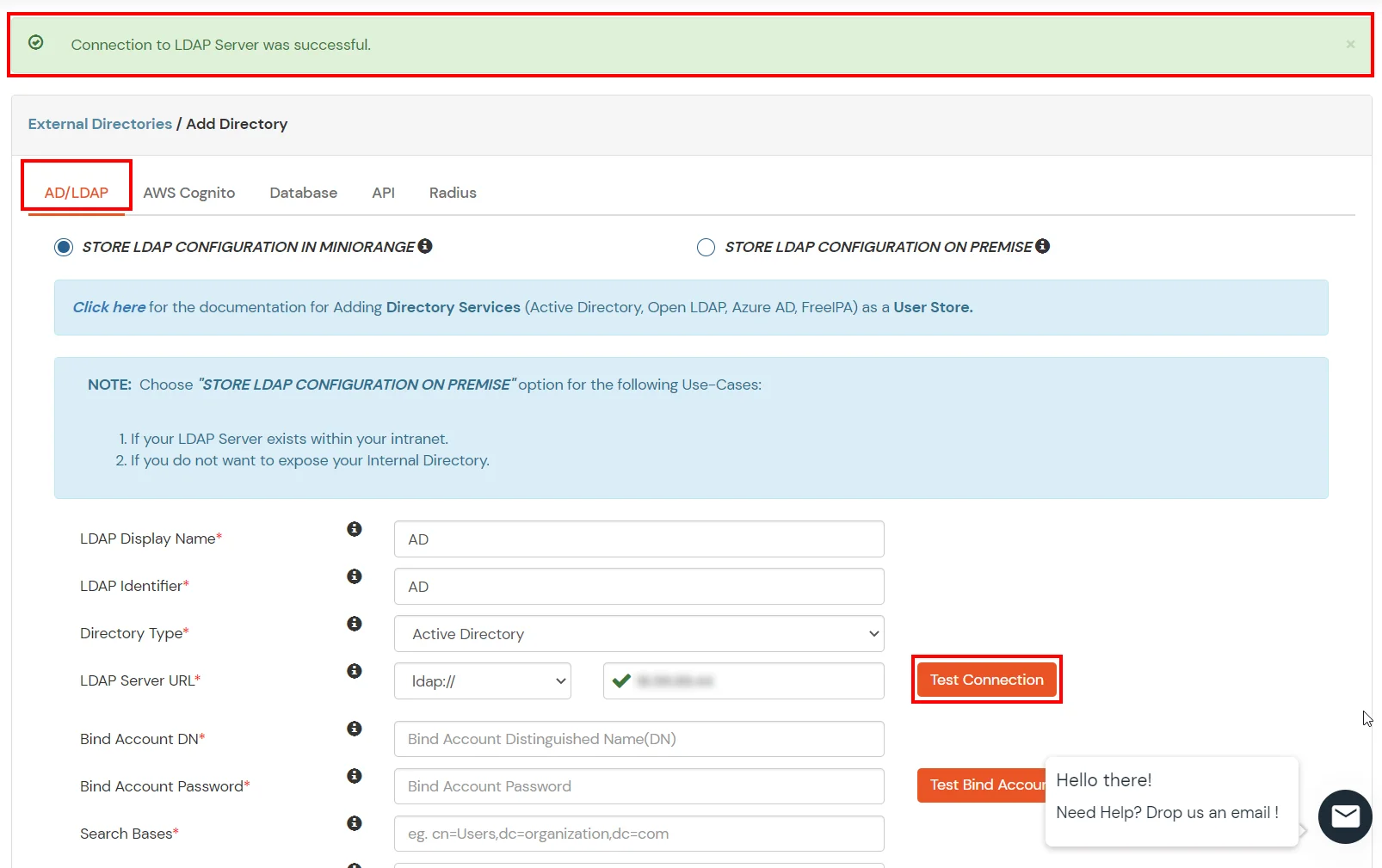
- Enter the LDAP Server URL or IP Address against the LDAP Server URL field.
- Click on the Test Connection button to verify if you have made a successful connection with your LDAP server.
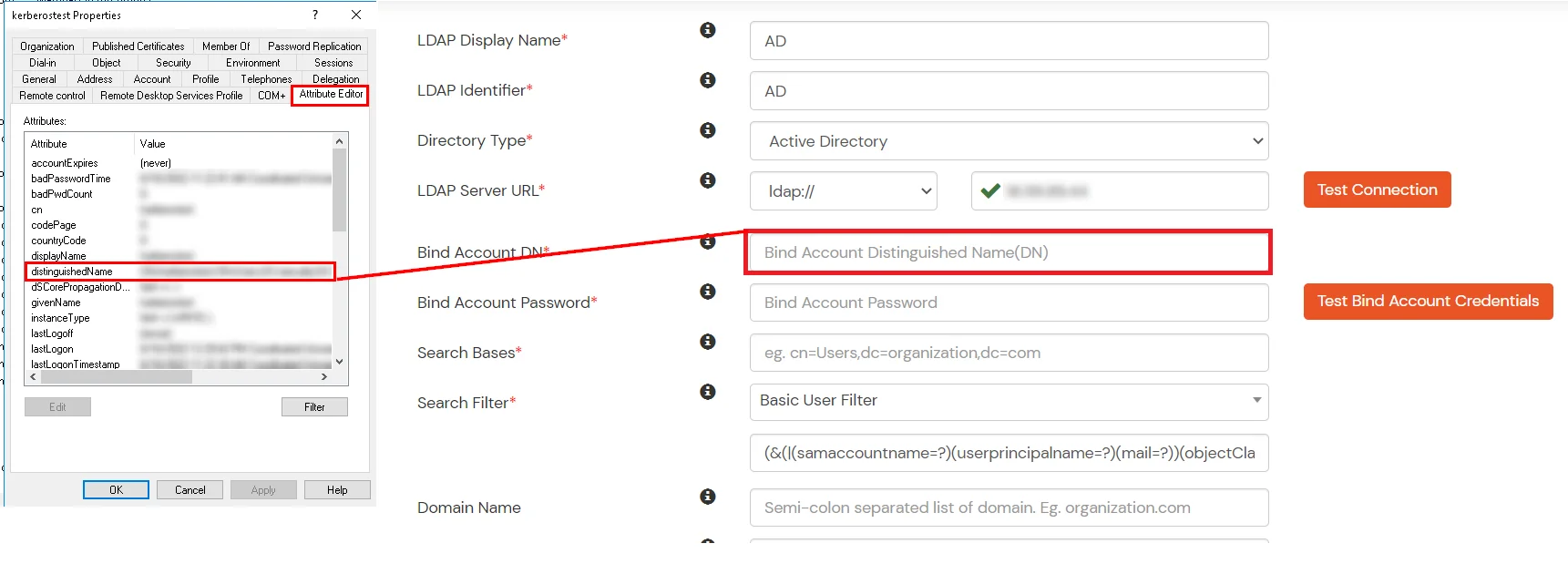
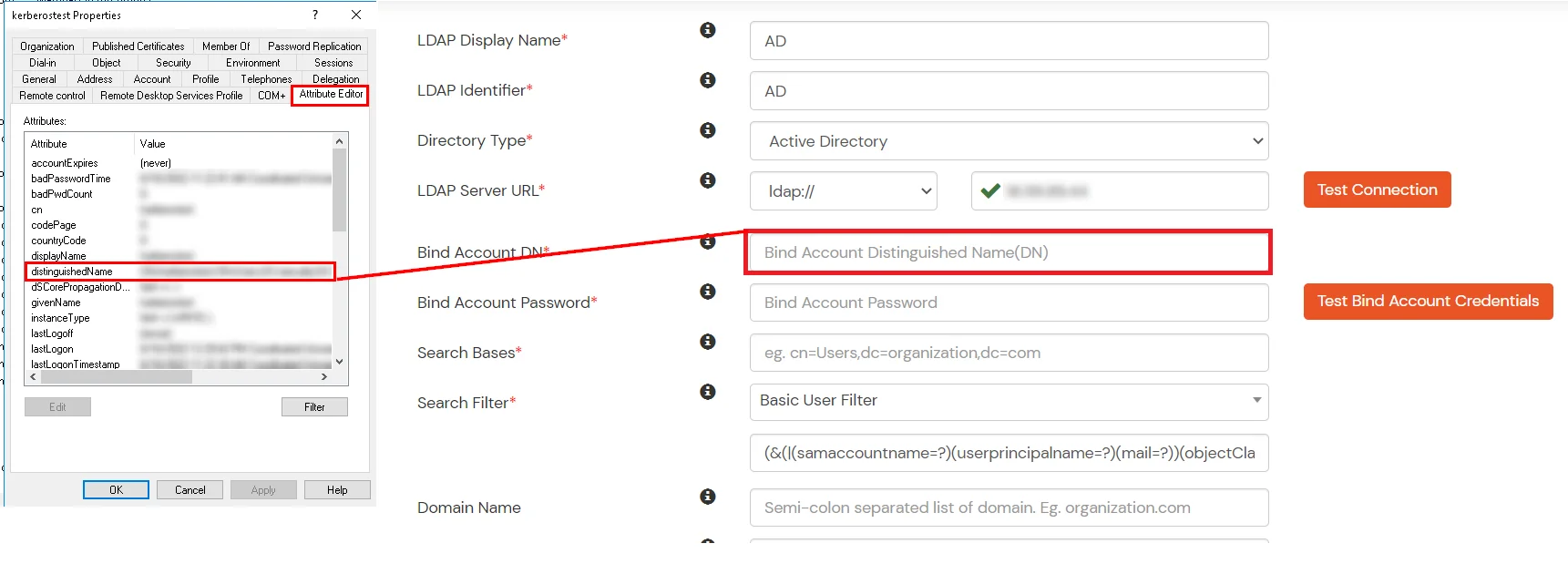
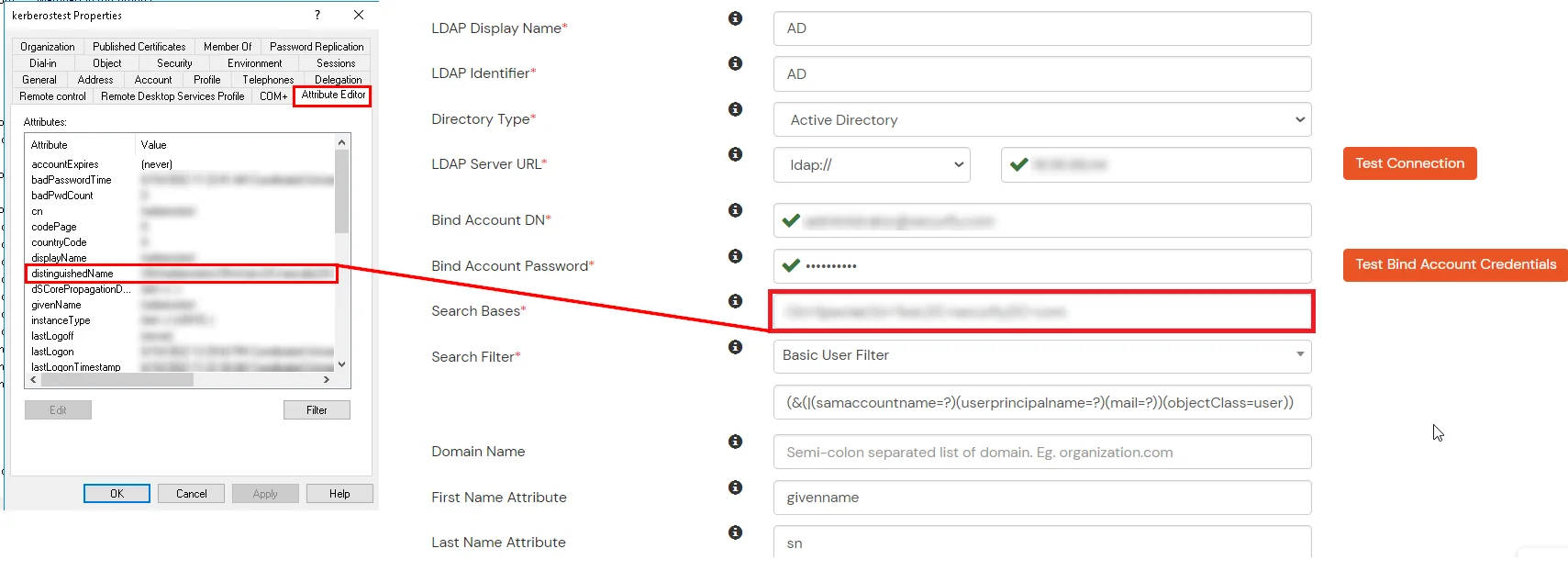
- In Active Directory, go to the properties of user containers/OU's and search for the Distinguished Name attribute. The bind account should have minimum required read privileges in Active Directory to allow directory lookups. If the use case involves provisioning (such as creating, updating, or deleting users or groups), the account must also be granted appropriate write permissions.
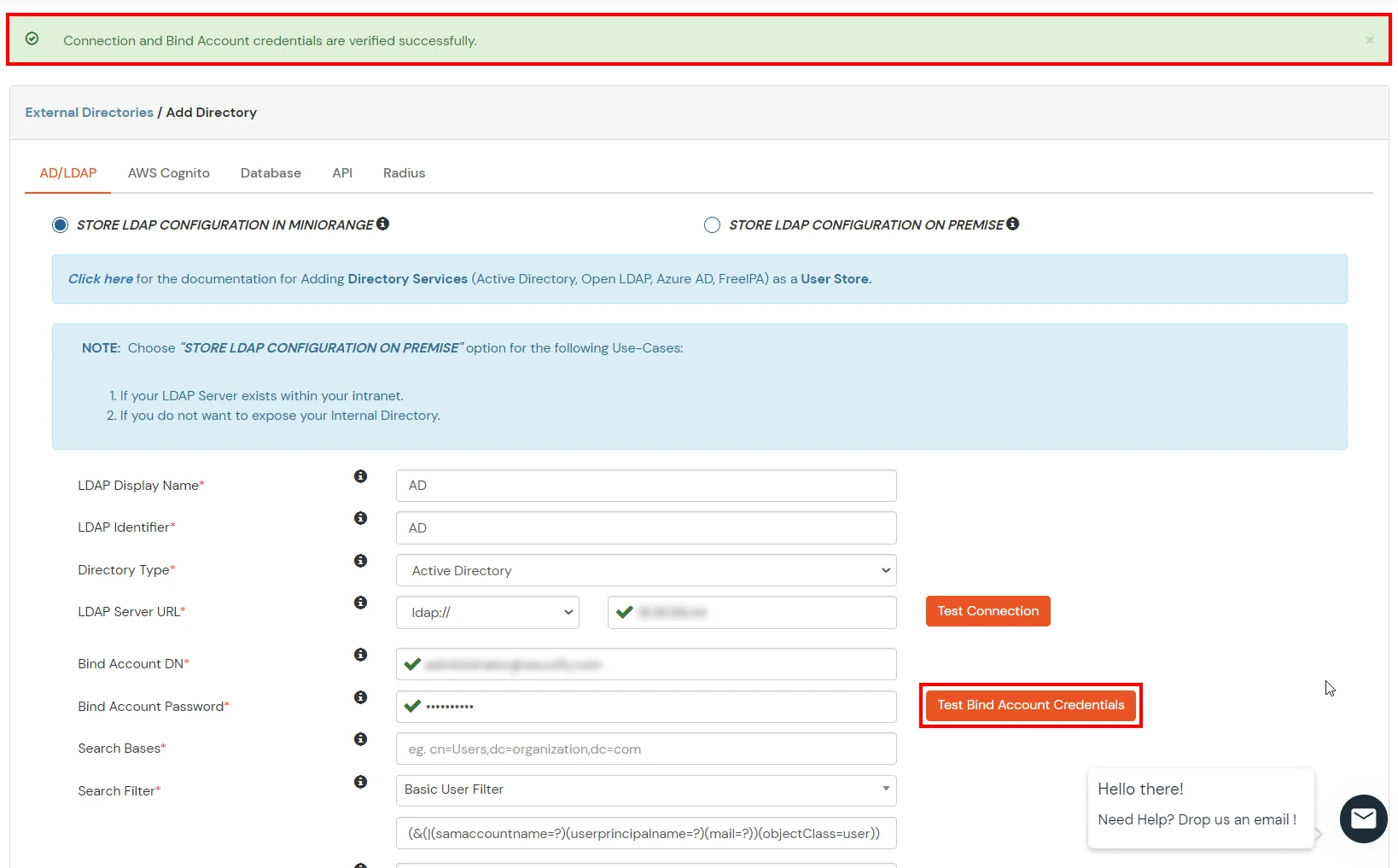
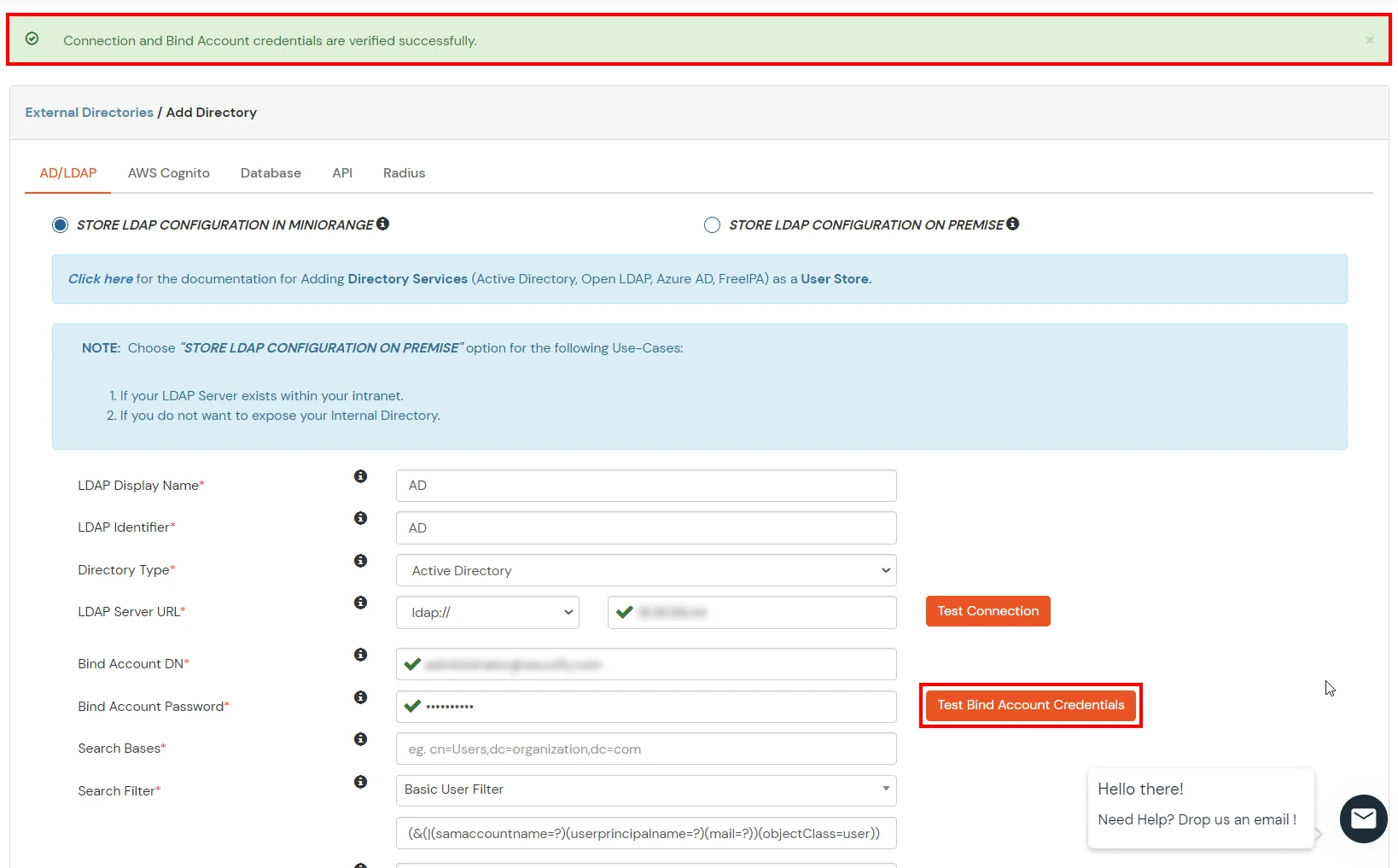
- Enter the valid Bind account Password.
- Click on the Test Bind Account Credentials button to verify your LDAP Bind credentials for LDAP connection.
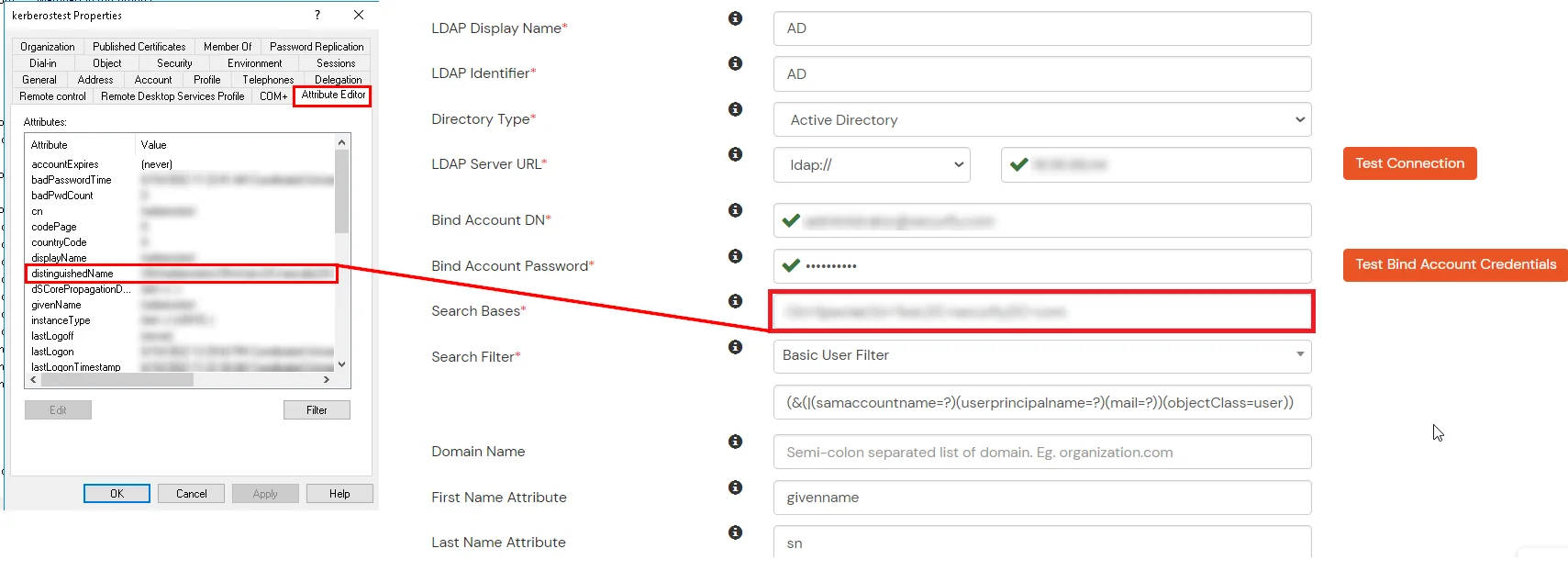
- Search Base is the location in the directory where the search for a user begins. You will get this from the same place you got your Distinguished name.
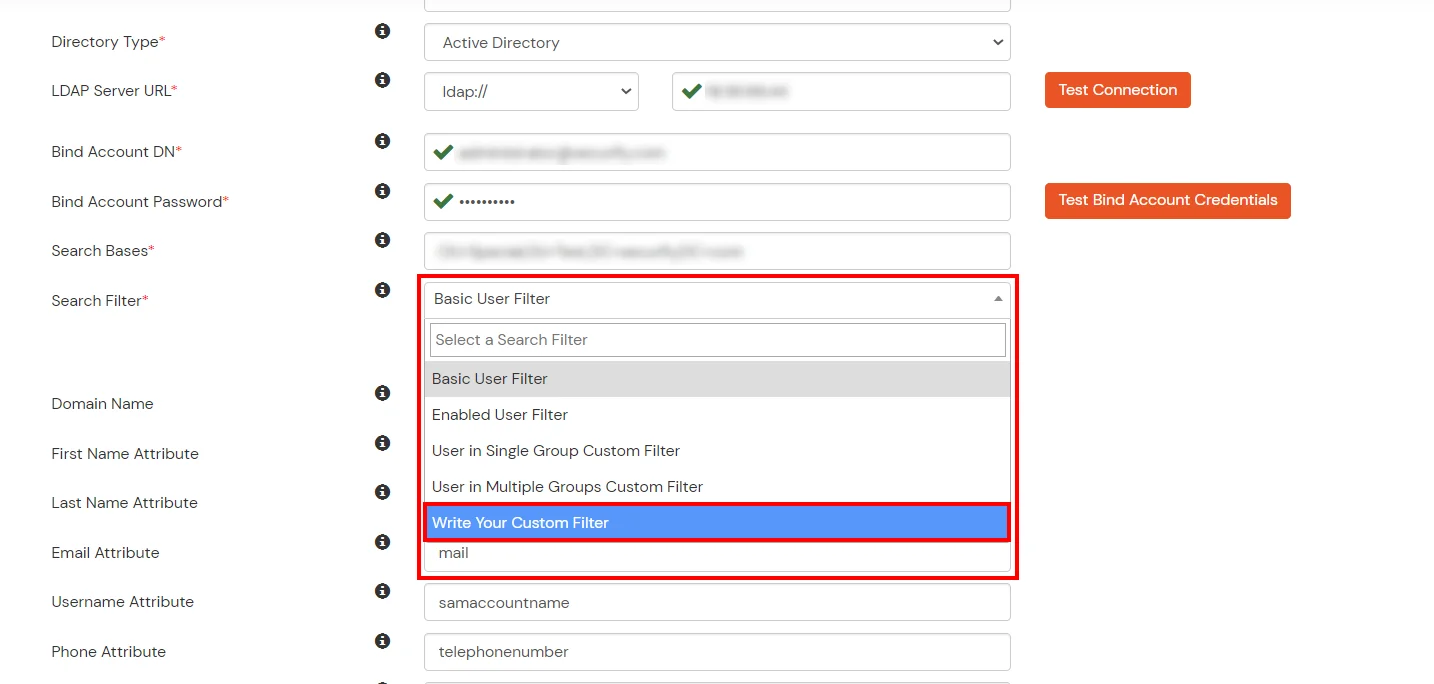
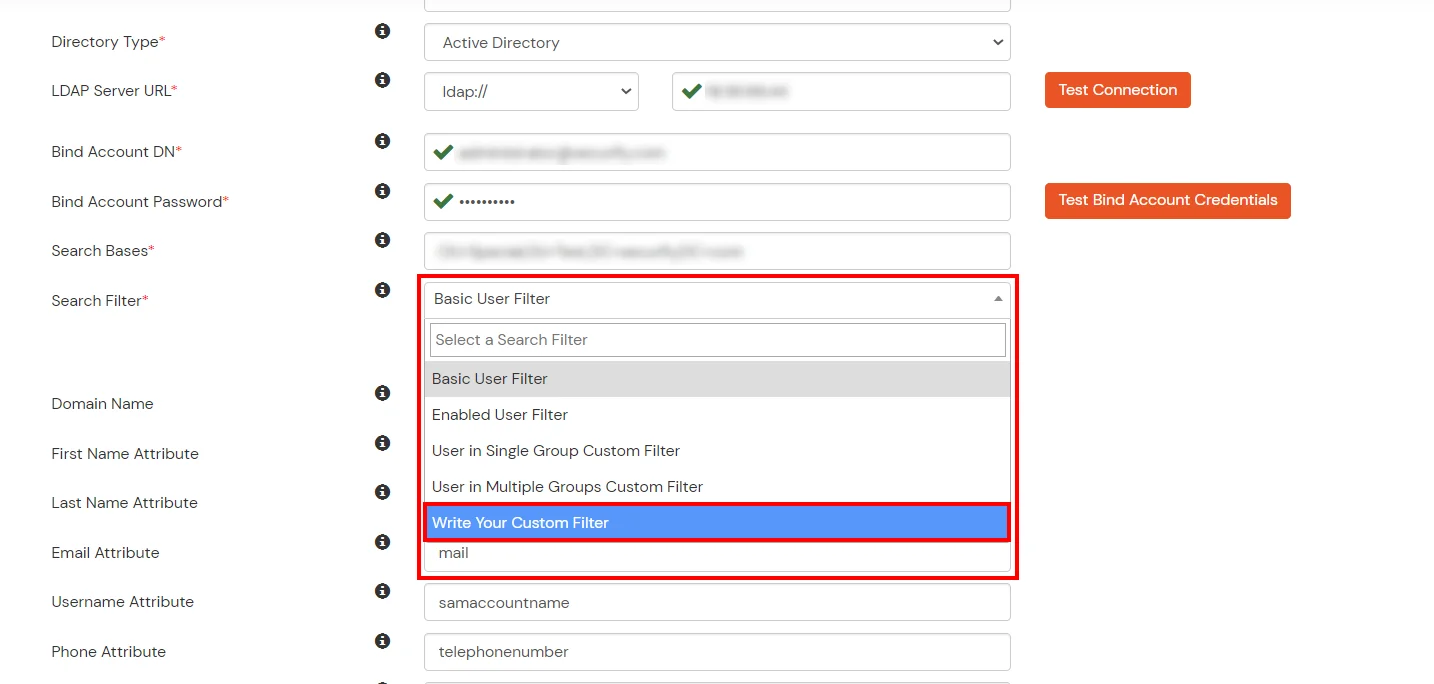
- Select a suitable Search filter from the drop-down menu. If you use User in Single Group Filter or User in Multiple Group Filter, replace the <group-dn> in the search filter with the distinguished name of the group in which your users are present. To use custom Search Filter select "Write your Custom Filter" option and customize it accordingly.
- Click on the Next button, or go to the Login Options tab.
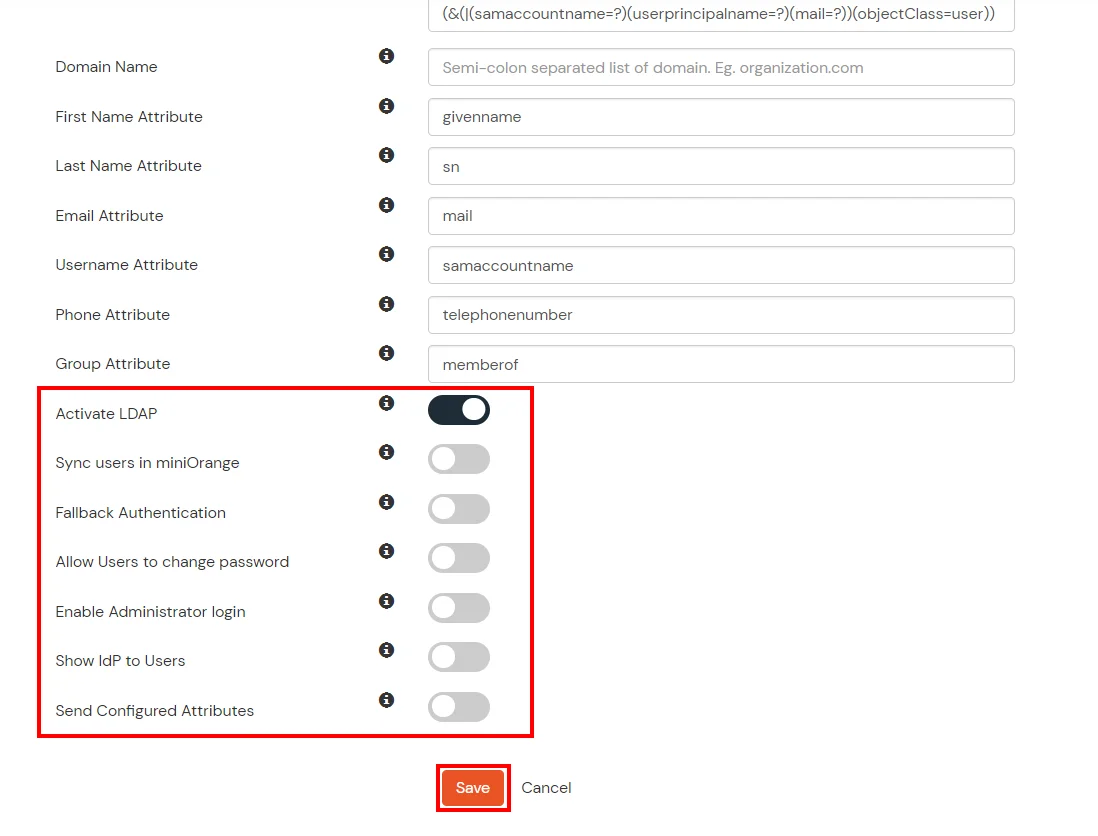
- You can also configure following options while setting up AD. Enable Activate LDAP in order to authenticate users from AD/LDAP. Click on the Next button to add user store.
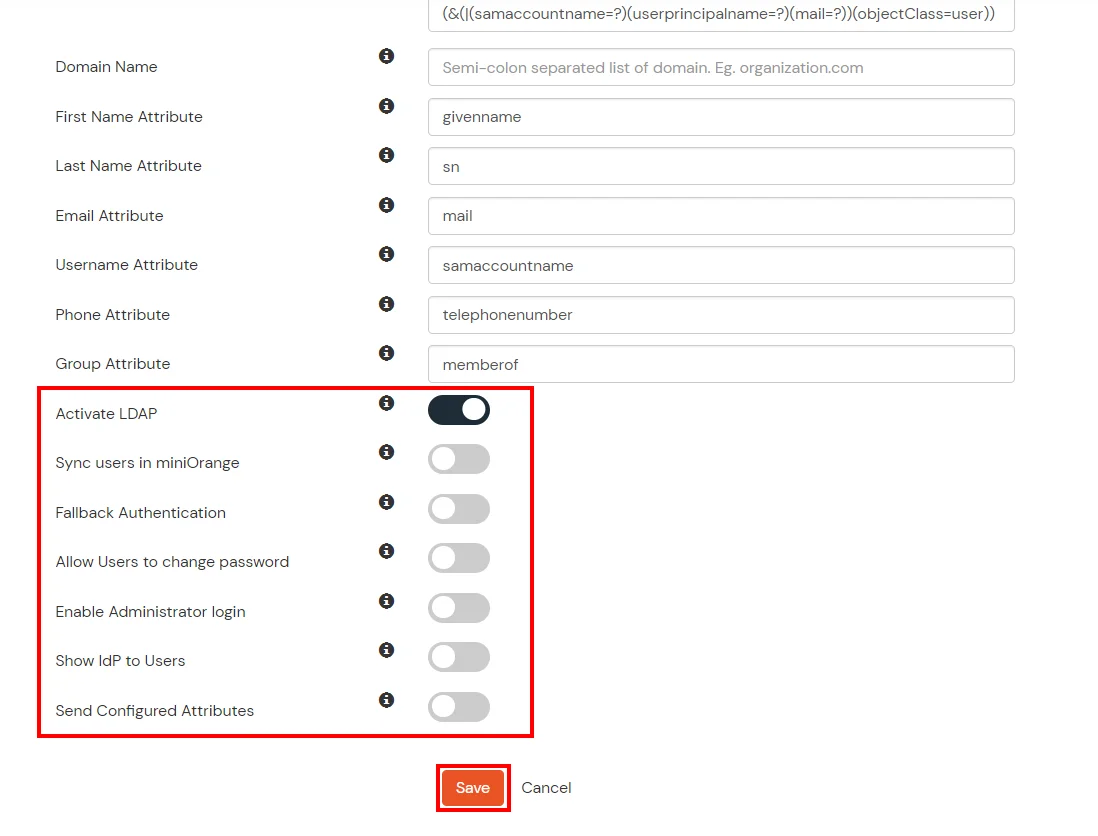
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute |
Description |
| Activate LDAP |
All user authentications will be done with LDAP credentials if you Activate it |
| Fallback Authentication |
If LDAP credentials fail then user will be authenticated through miniOrange |
| Enable administrator login |
On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users |
If you enable this option, this IdP will be visible to users |
| Sync users in miniOrange |
Users will be created in miniOrange after authentication with LDAP |
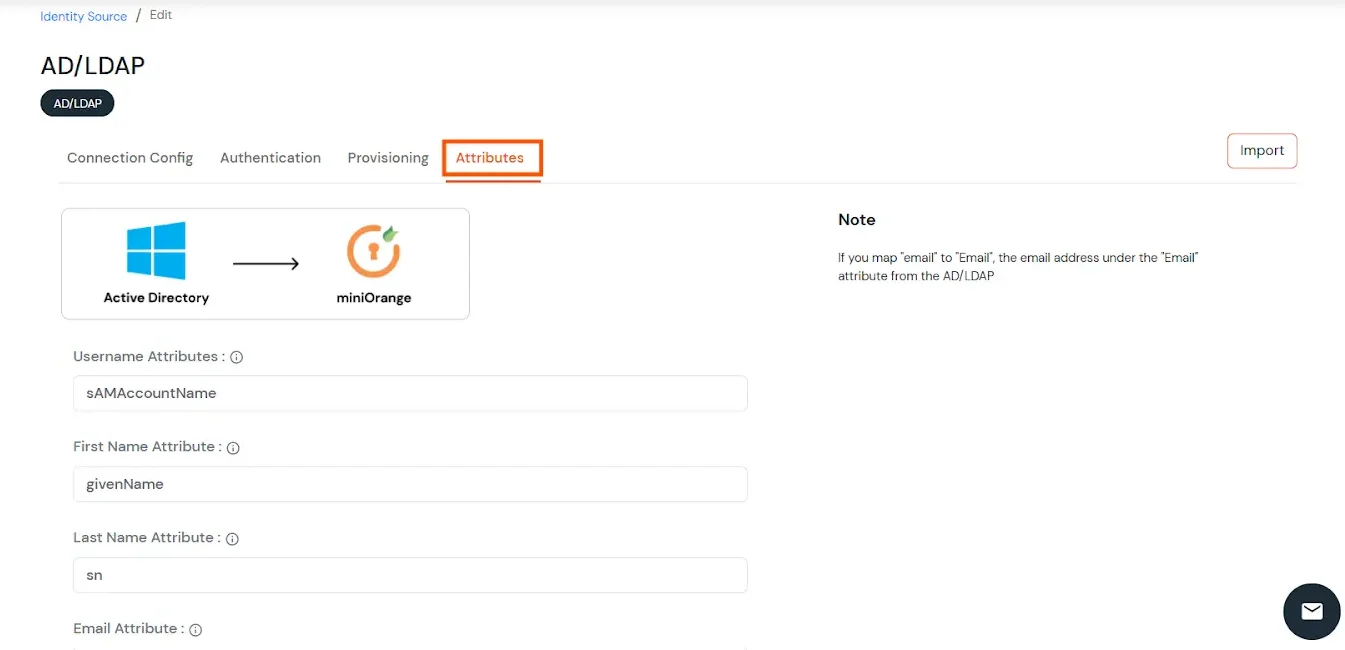
- Click on the Next button, or go to the Attributes tab.
Attributes Mapping from AD
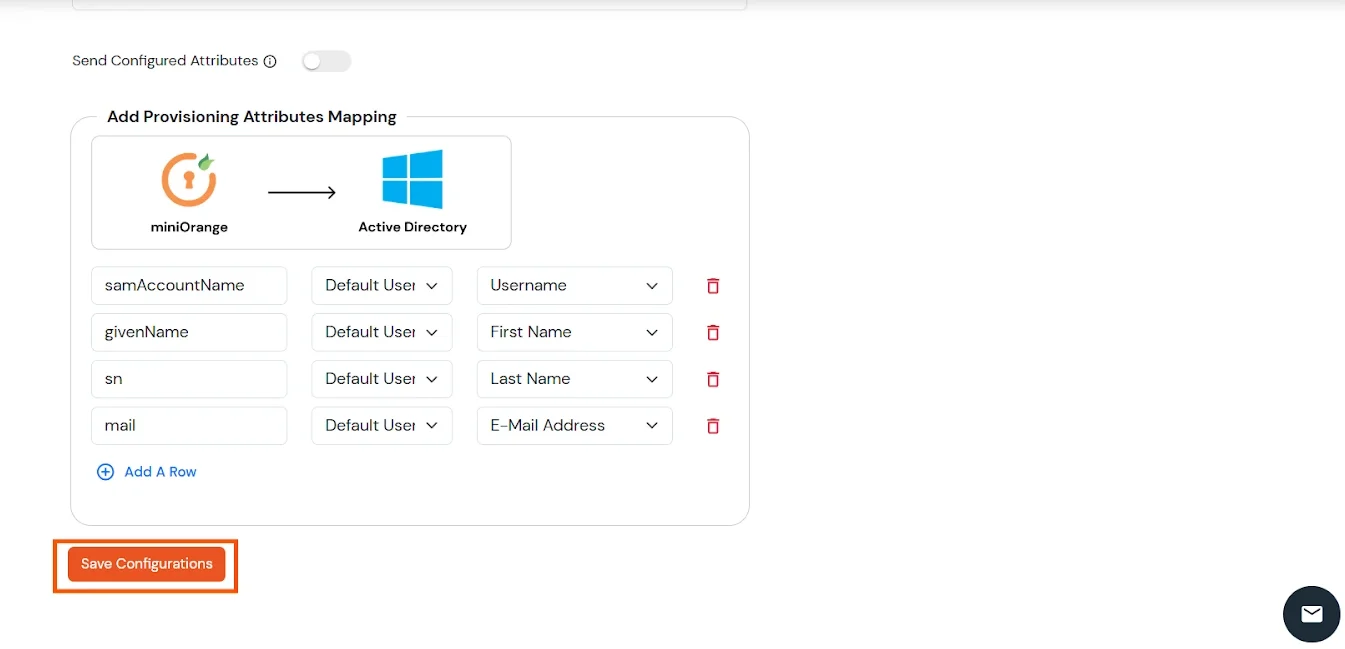
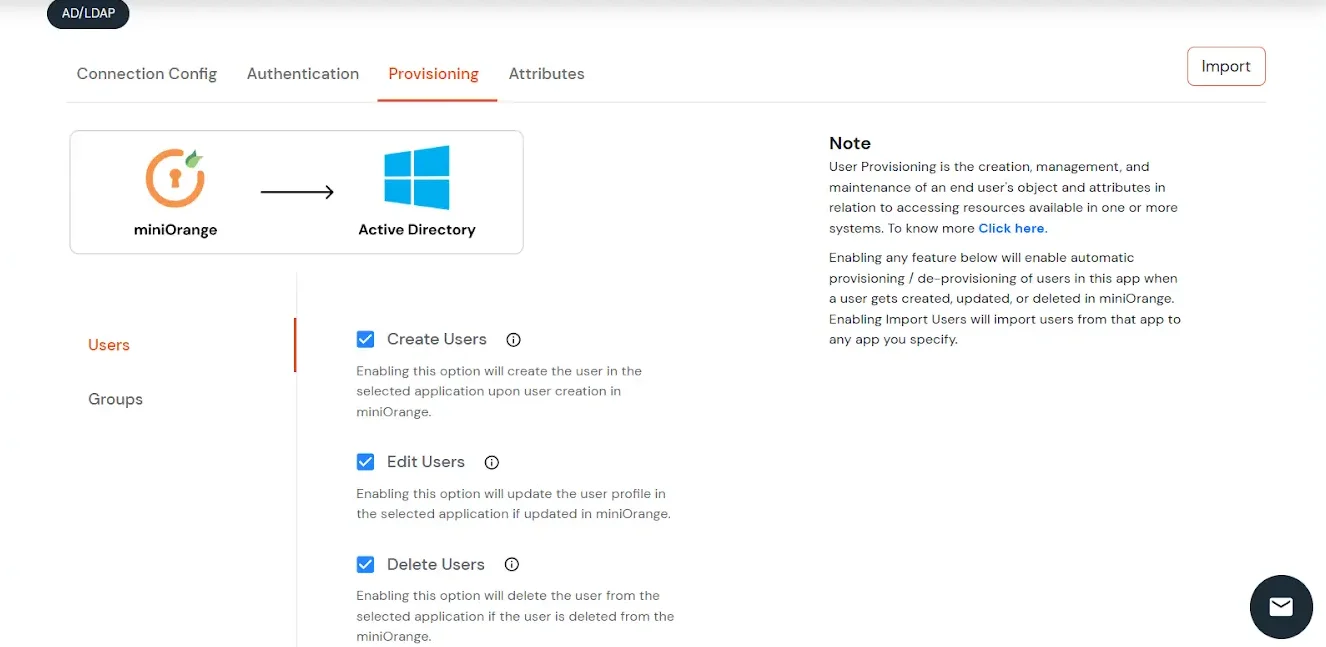
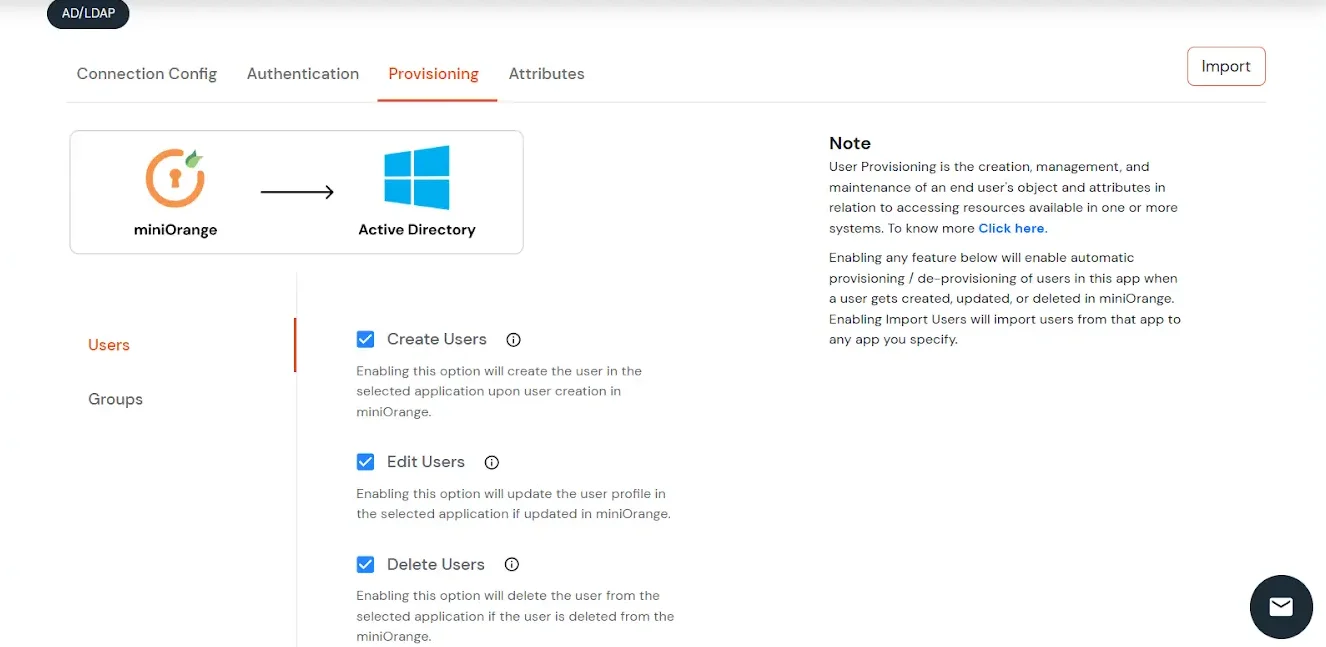
User Import and Provisioning from AD
- If you want to set up provisioning, click here for detailed information. We will skip this step for now.
Import Password Policy from AD
- If you want to import your Active Directory password policy into miniOrange, click here for detailed information. We will skip this step for now.
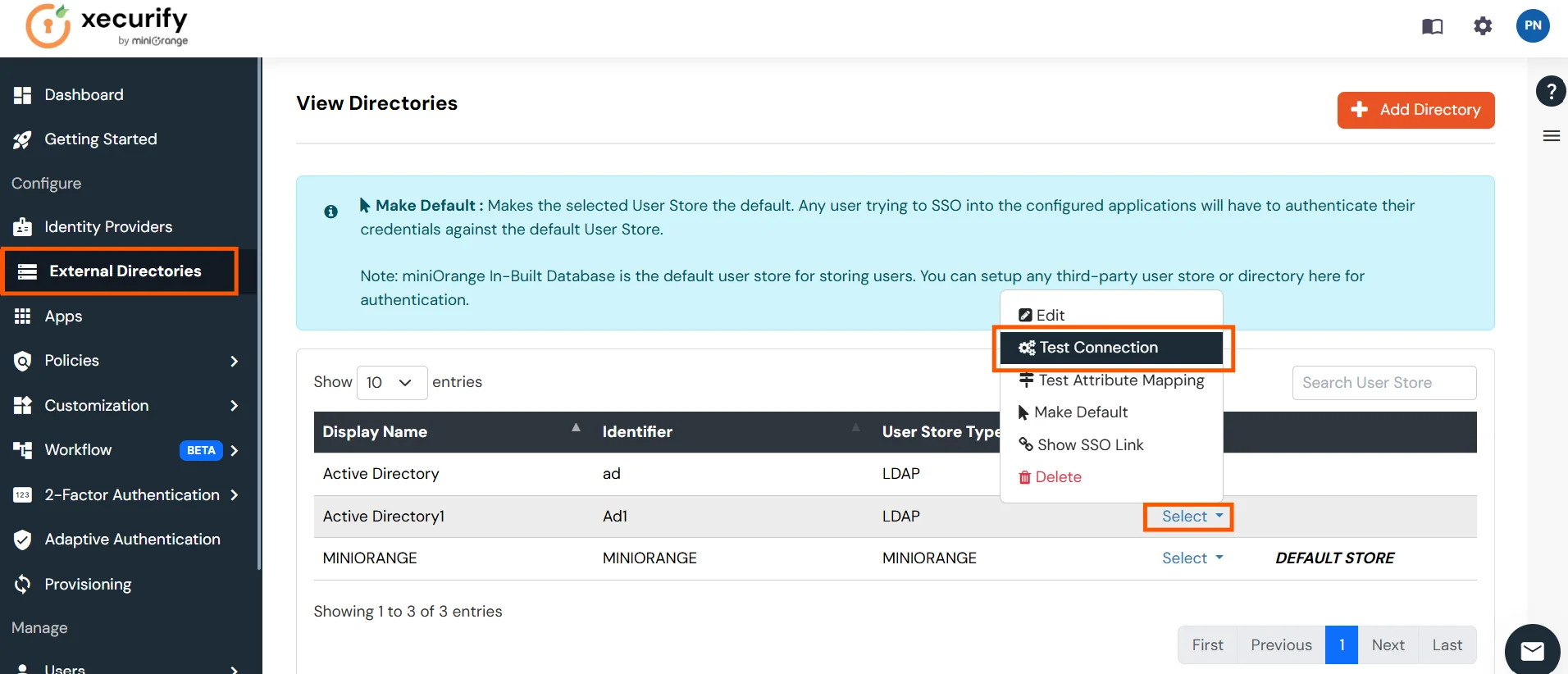
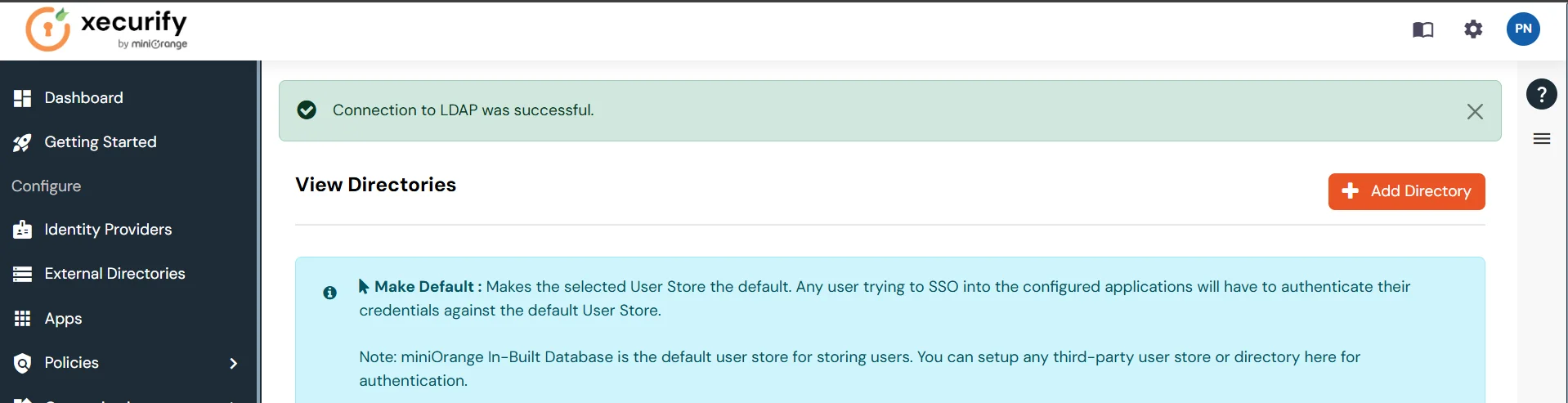
Test Connections
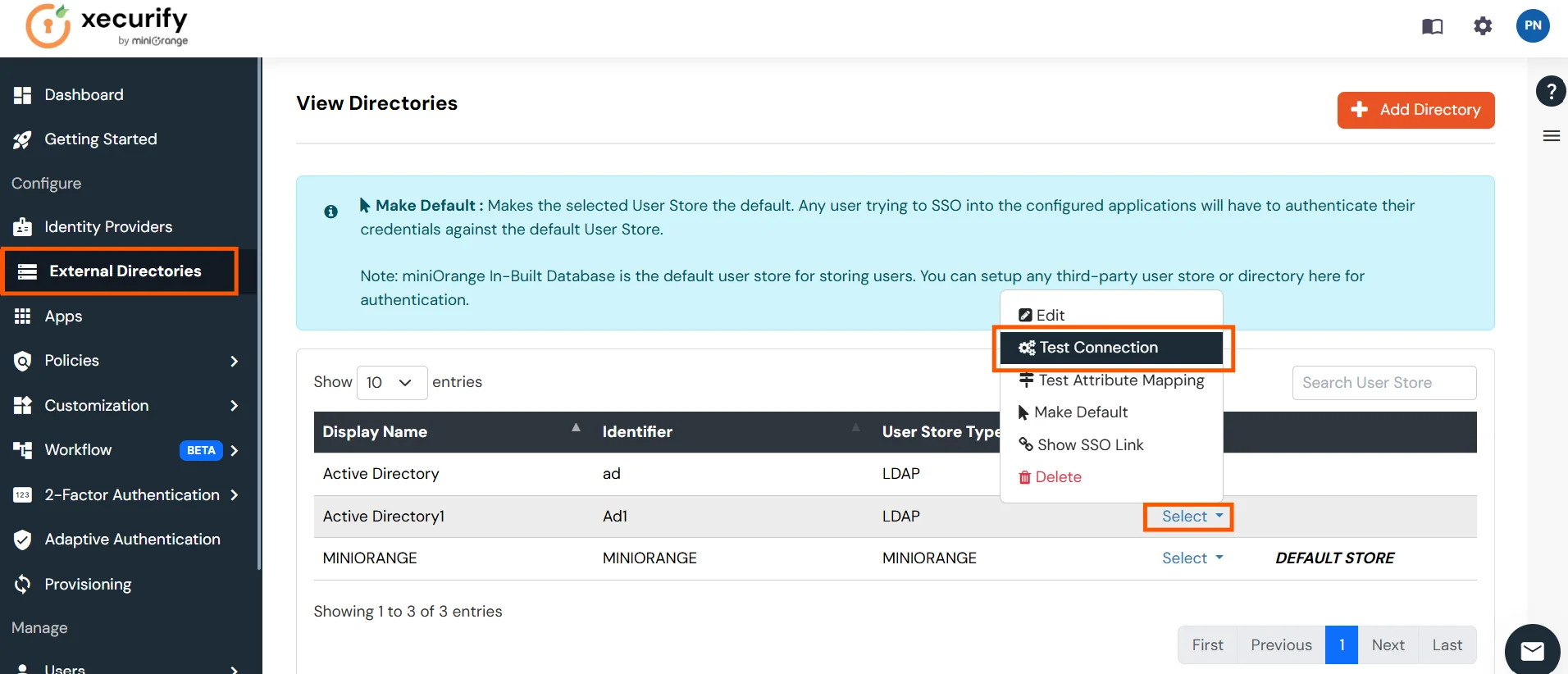
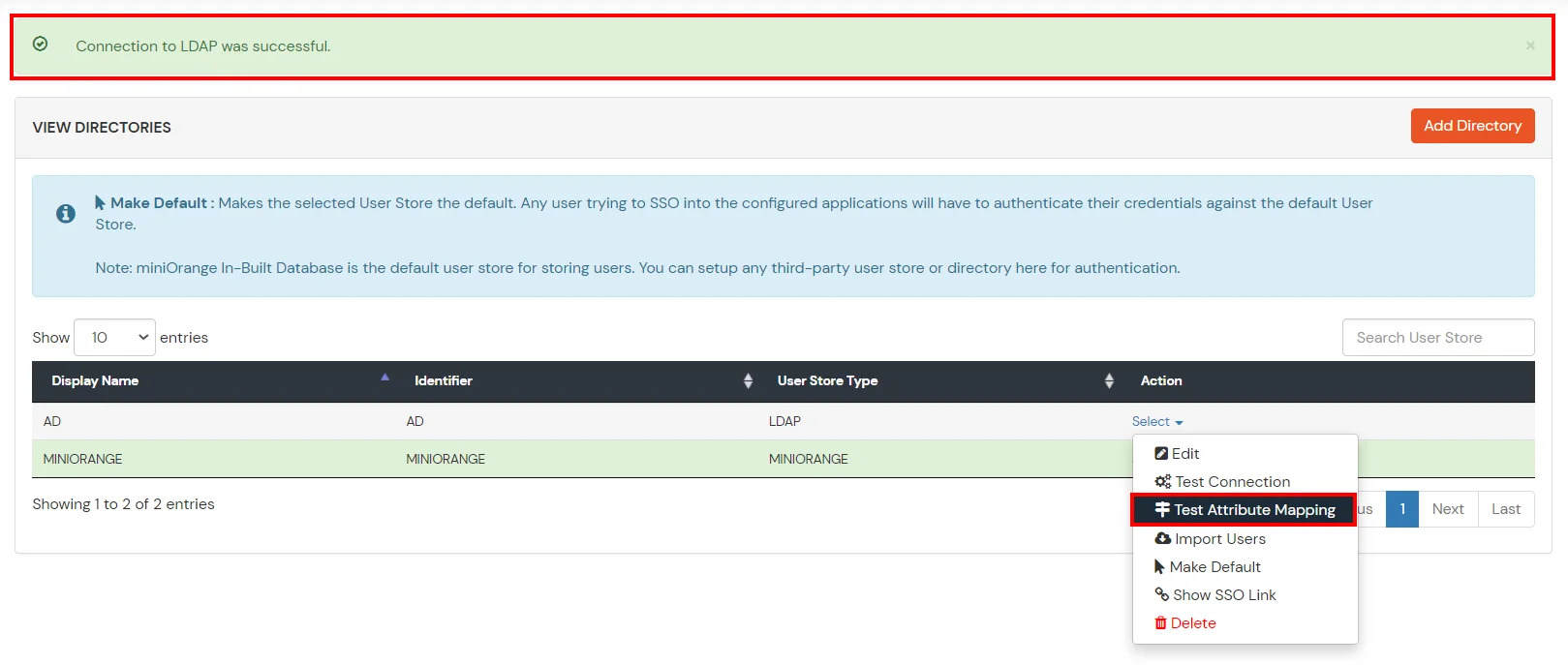
- You will see a list of directories under Identity Providers. From the dropdown, select AD/LDAP Directories, search for your configured directory, click the three dots next to it, and select Test Connection.
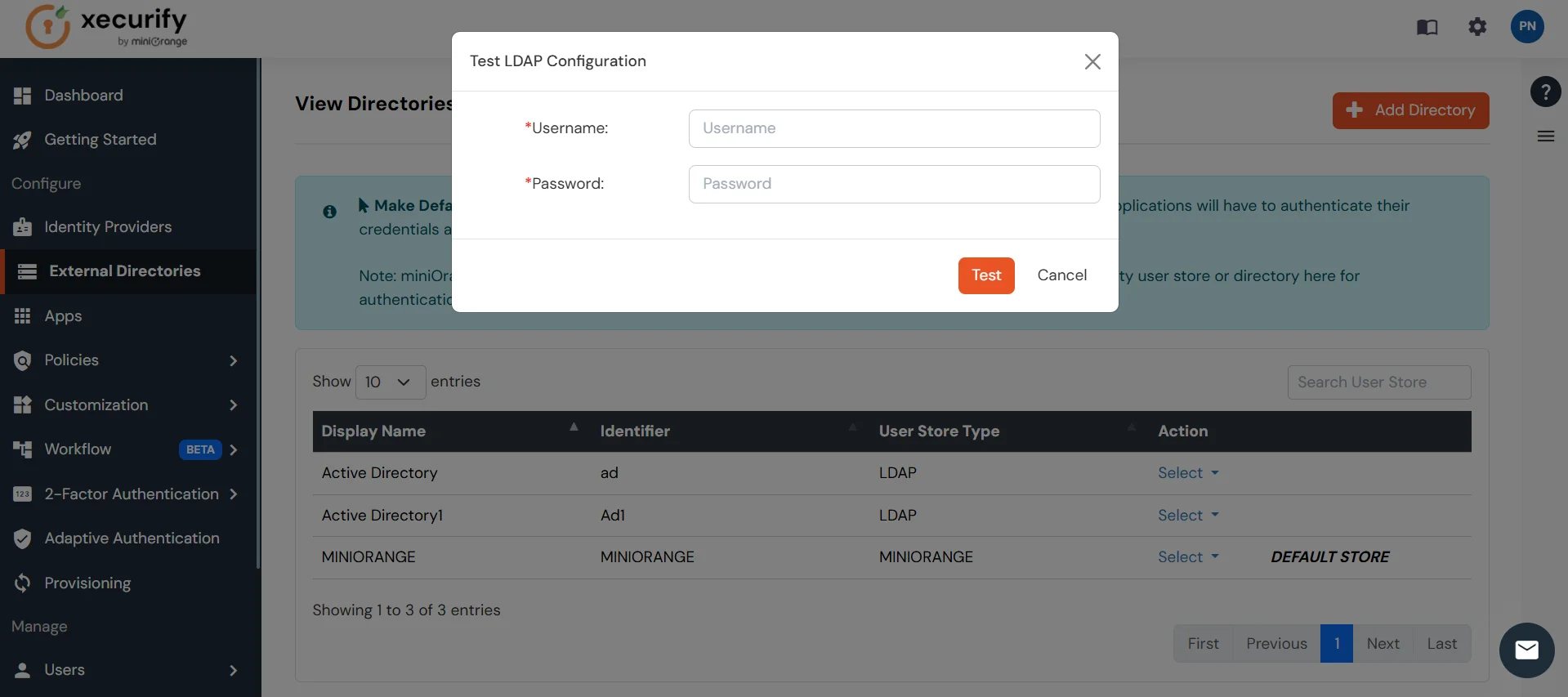
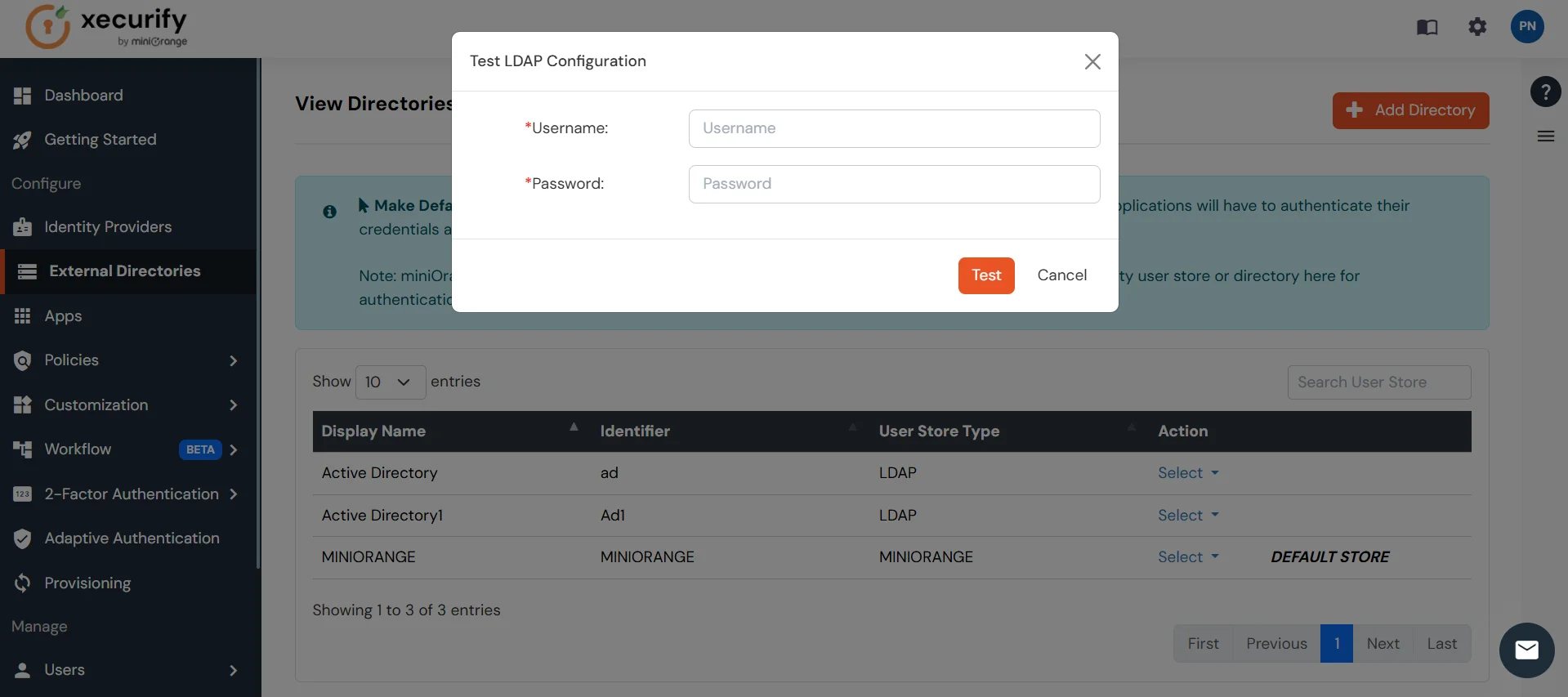
- A pop-up appears prompting you to enter a username and password to verify your LDAP configuration.
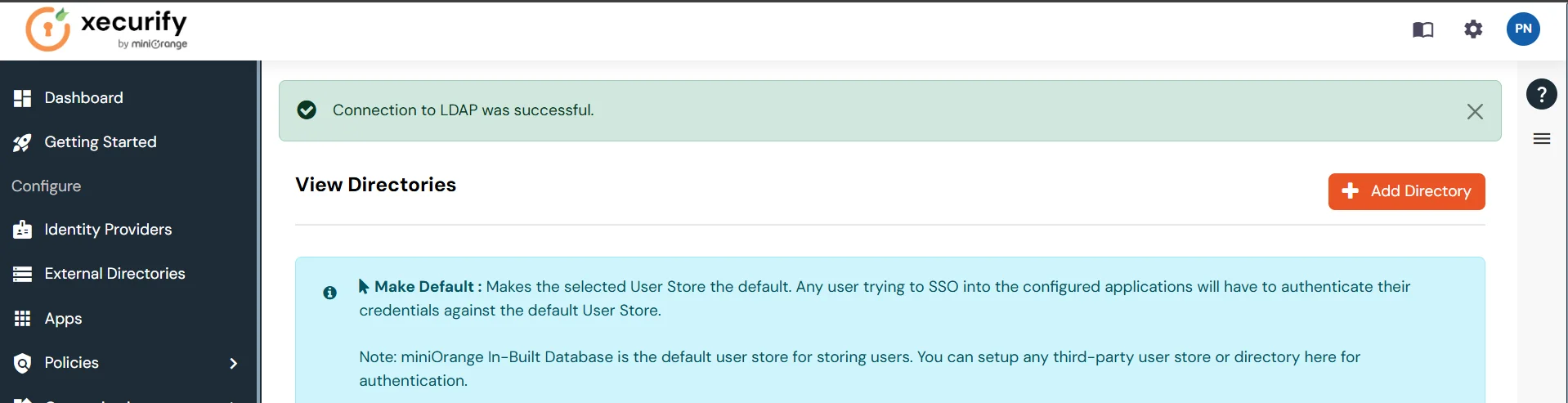
- On Successful connection with LDAP Server, a success message is shown.
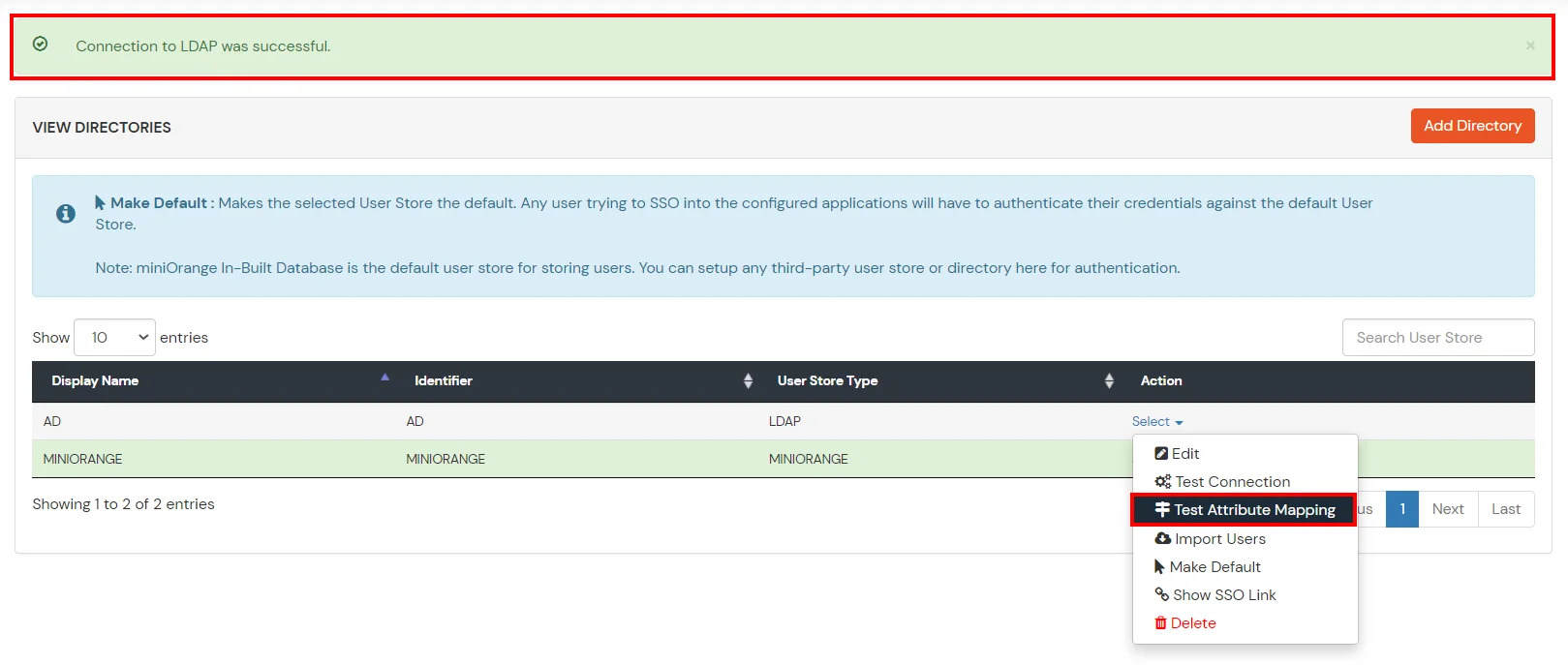
Test Attribute Mapping
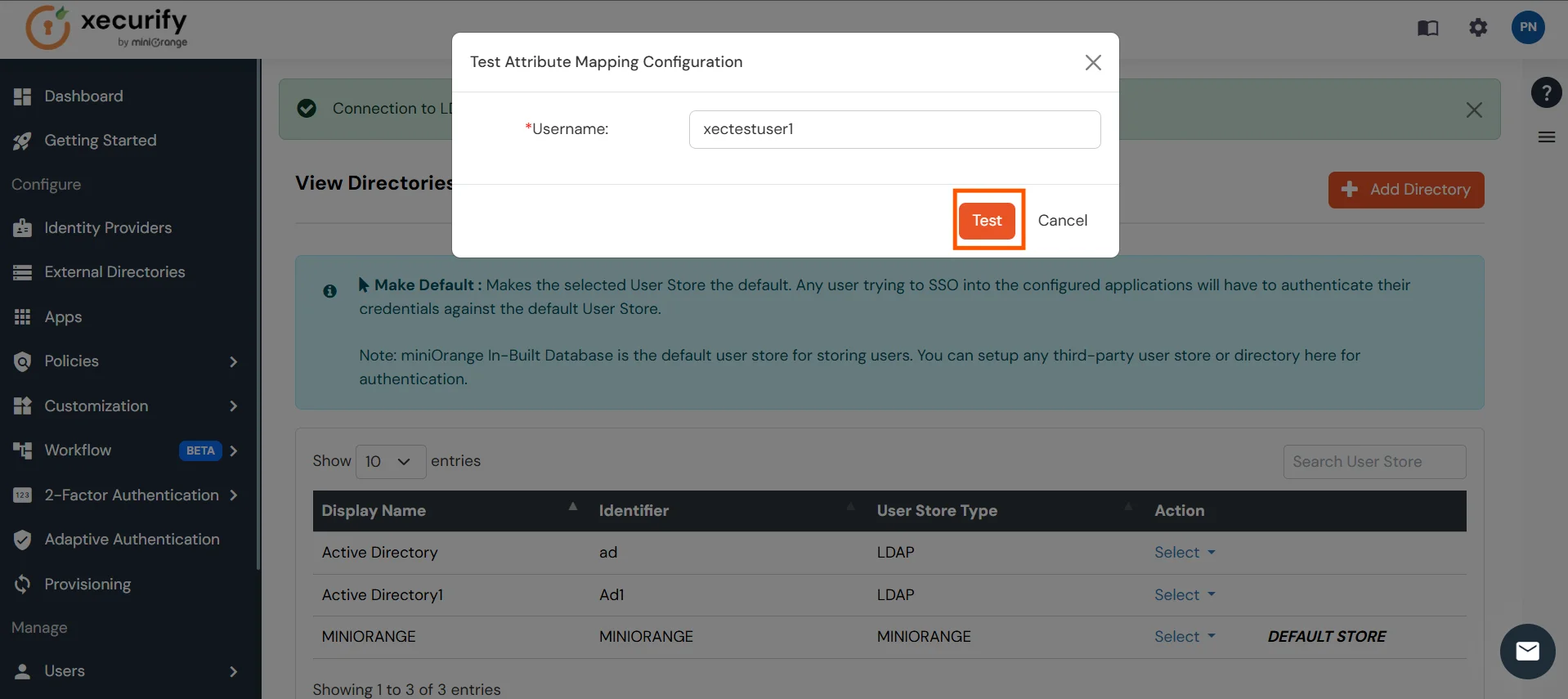
- You will see a list of directories under Identity Providers. From the dropdown, select AD/LDAP Directories, search for your configured directory, click the three dots next to it, and select Test Attribute Mapping.
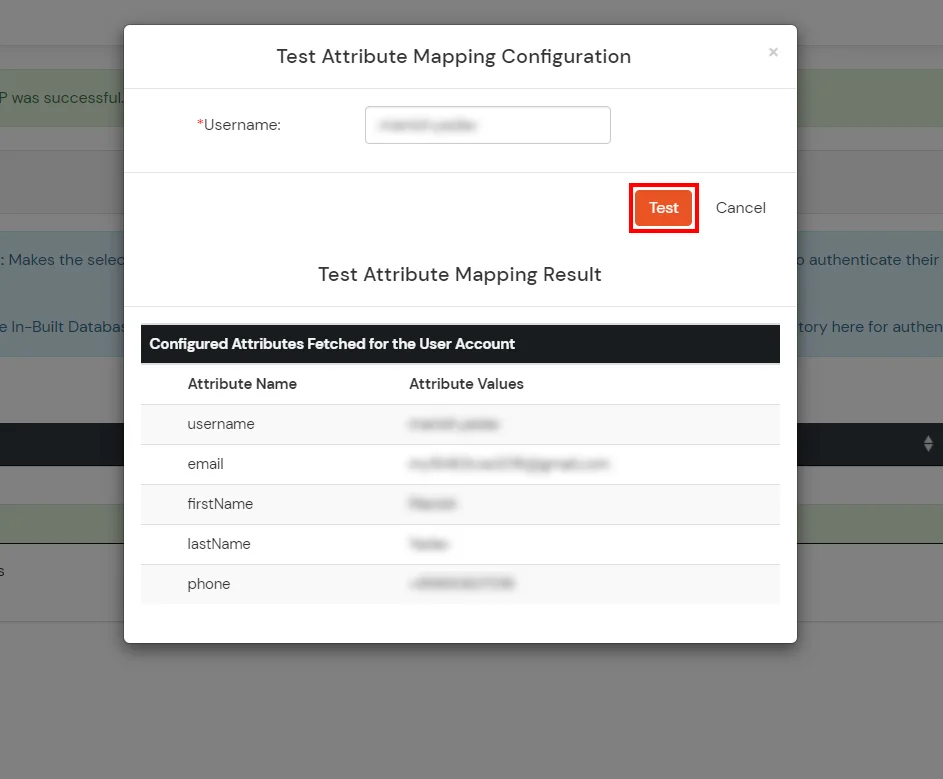
- A pop‑up appears to enter a username and click Test.
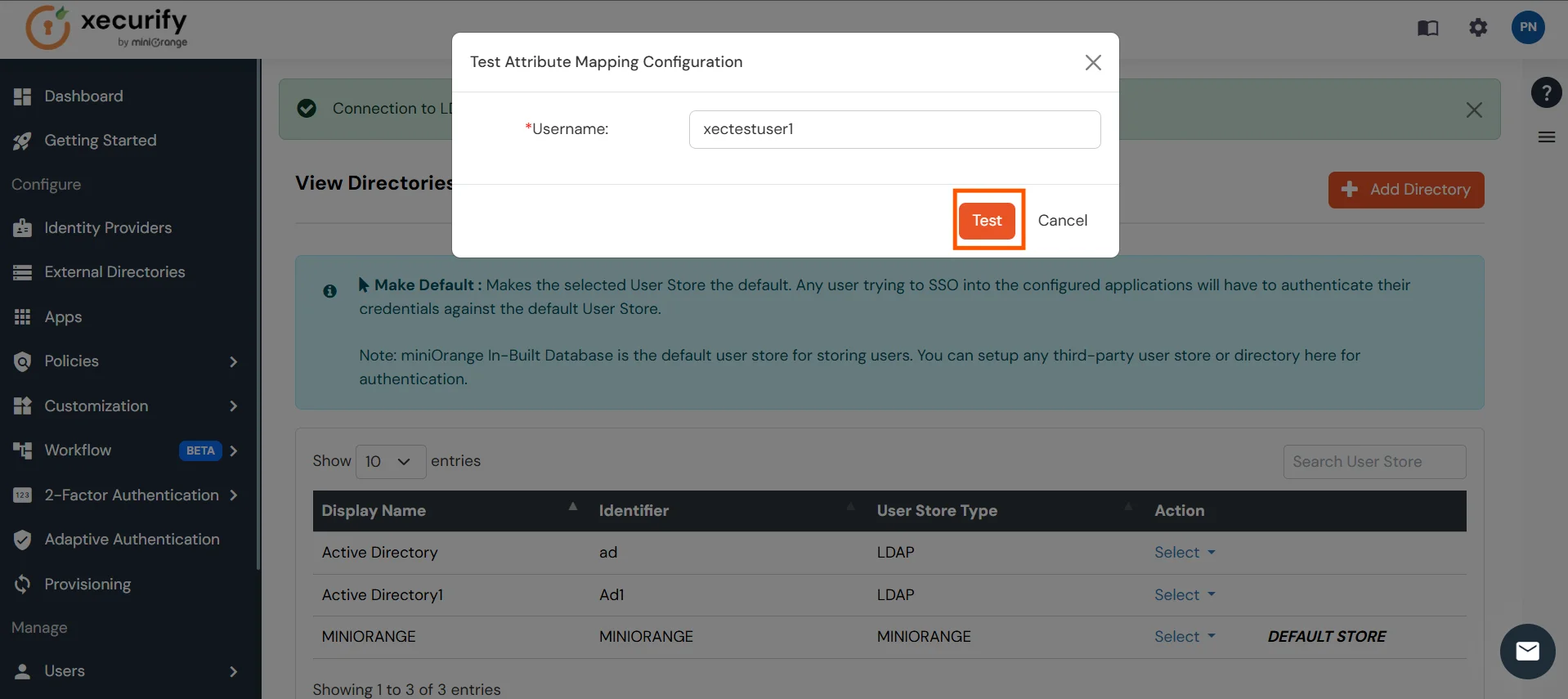
- The Test Attribute Mapping Result will be displayed.
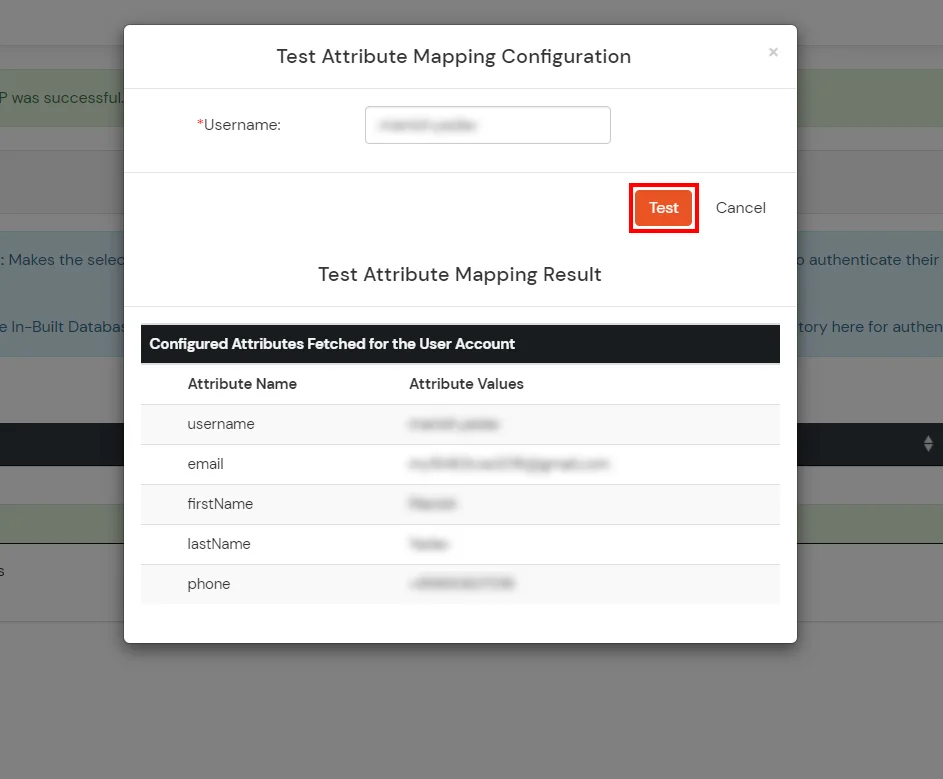
Set up AD as External Directory configuration is complete.
Note: Refer our guide to setup LDAP on windows server.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
Troubleshooting
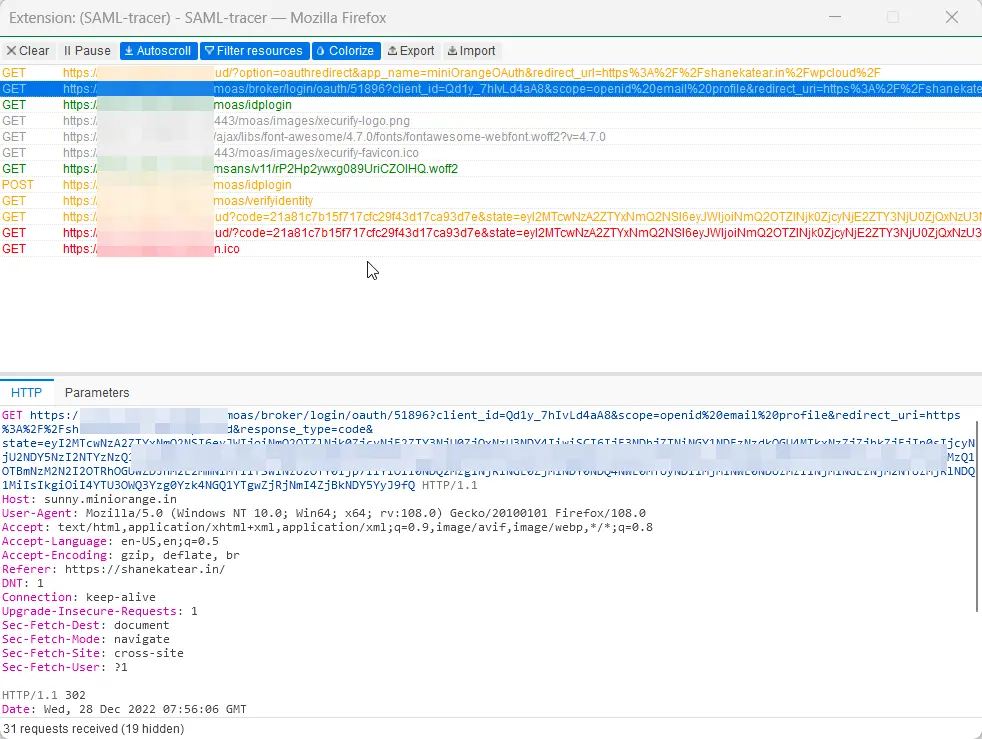
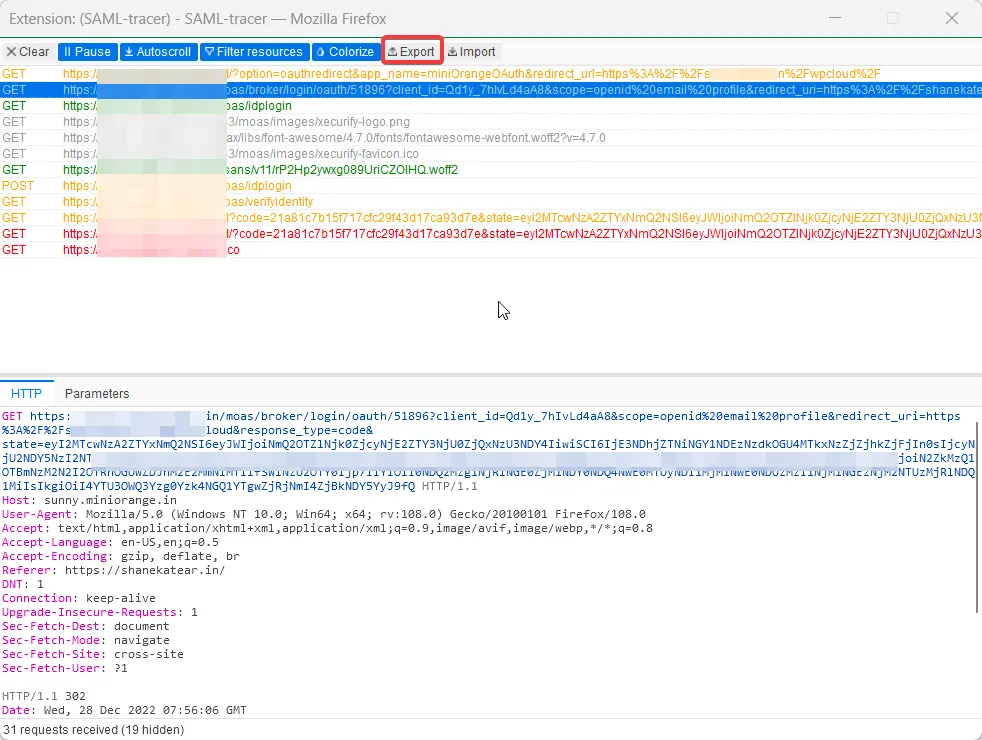
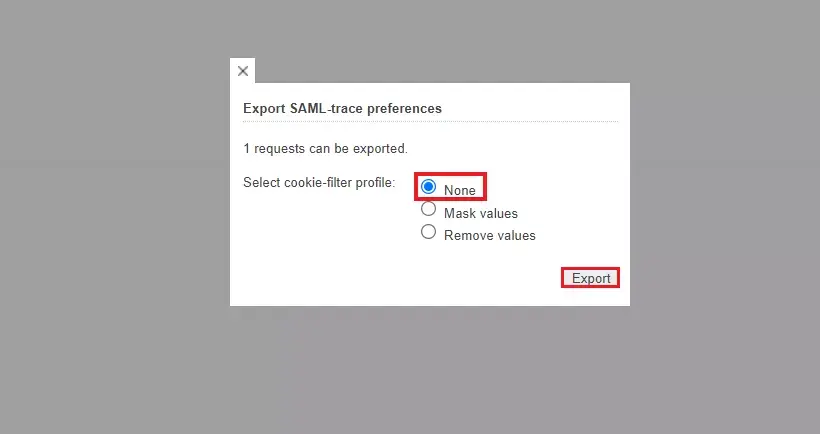
How can I trace and export the SAML tracer logs?
Frequently Asked Questions (FAQs)
What is SAML SSO?
SAML Single Sign-On (SSO) is an authentication process in which a user is provided access to multiple applications and/or websites by using only a single set of login credentials (such as username and password). This prevents the need for the user to login separately into the different applications.
What is pricing of miniOrange SSO solution?
Click here to check the pricing of miniOrange SSO solution.
External References