How to restrict user access to O365 IP
addresses
Enable IP restriction on MS Office 365 apps with miniOrange security solutions. Onboard users
and configure
custom Network IP restrictions to secure your data. Check the solution that fits your
business needs for
authenticating users by IP, restricting access to MS Office 365 in real-time, and managing
mobile and desktop
app access.

Login by Network IPs
Verify and authenticate user logins based on their Network IP before
granting access to
MS Office 365
apps using IAM. Learn More
Setup Now

MS 365 Cloud App IP Restriction
Allow access to MS Office 365 apps only when users are connected to a
whitelisted
network IP, and block
access in real-time when the network changes using CASB.
Learn More
Setup Now

Office 365 Mobile App IP Restriction
Restrict access to MS Office 365 apps on mobile devices unless connected
to a
whitelisted network IP. Learn More
Setup Now
Connect with External Source of Users
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
Prerequisites
1.
Sync On-Premise Active Directory with
Microsoft Entra ID
NOTE: If you want to use your On-Premise Active Directory as a user store for
Office 365 IP
Restriction then follow the below steps to sync your AD and Microsoft Entra ID.
- Download the Microsoft Entra ID Connect
- Run the Microsoft Entra ID installer on your domain machine and follow the setup.
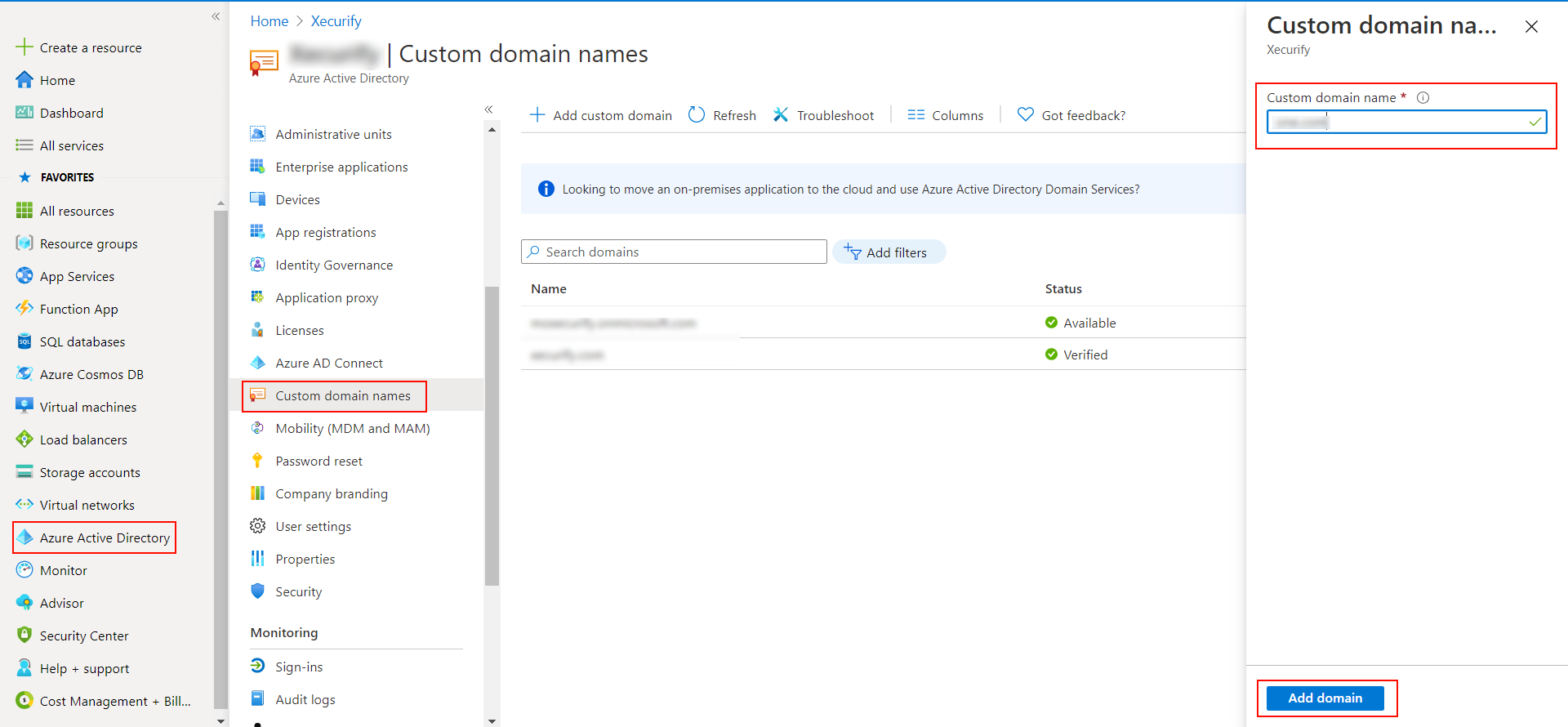
2. Verify your UPN Domain in Azure Portal
- In the Azure portal navigate to Microsoft Entra ID >> Custom domain names and
click on Add
custom domain.
- Enter the full domain name in the right pane that pops up and click on Add
domain.
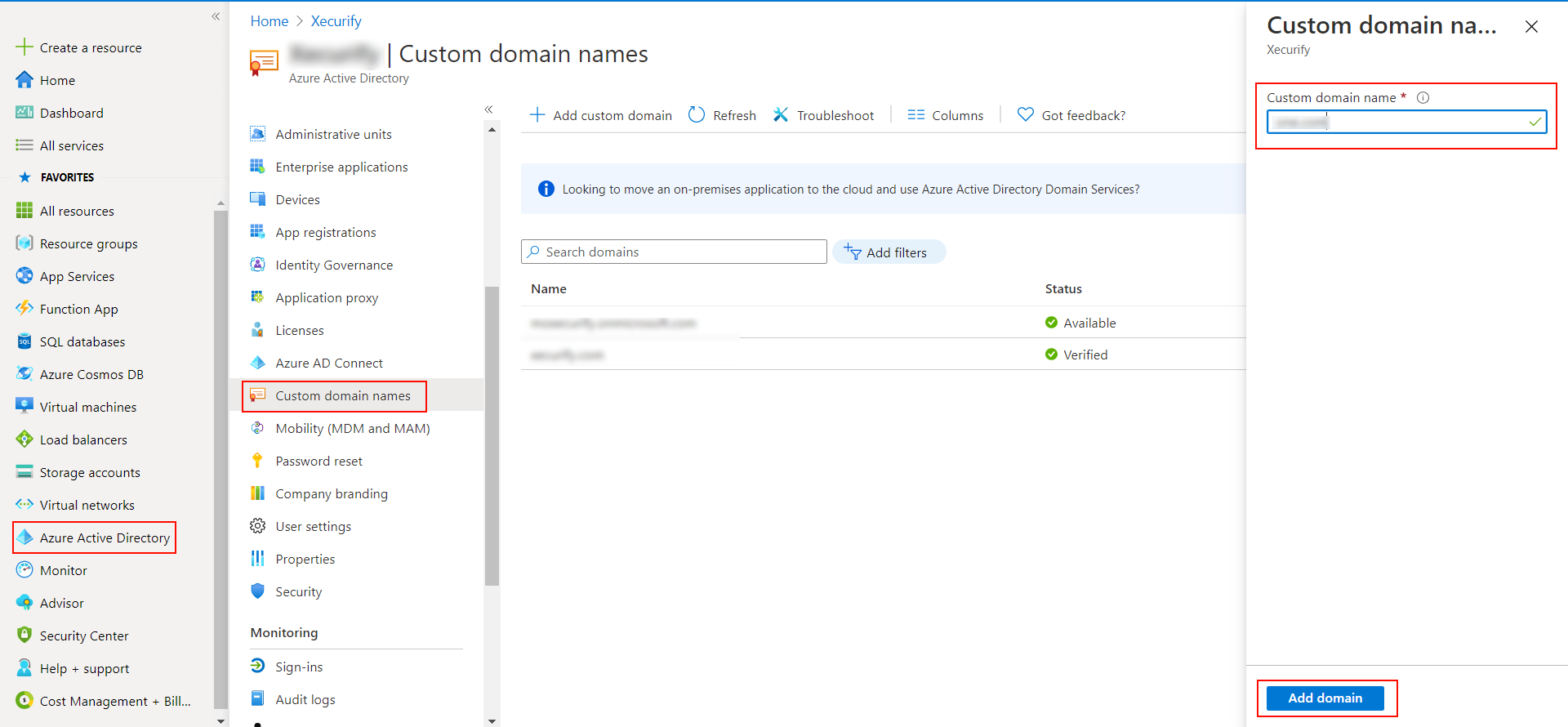
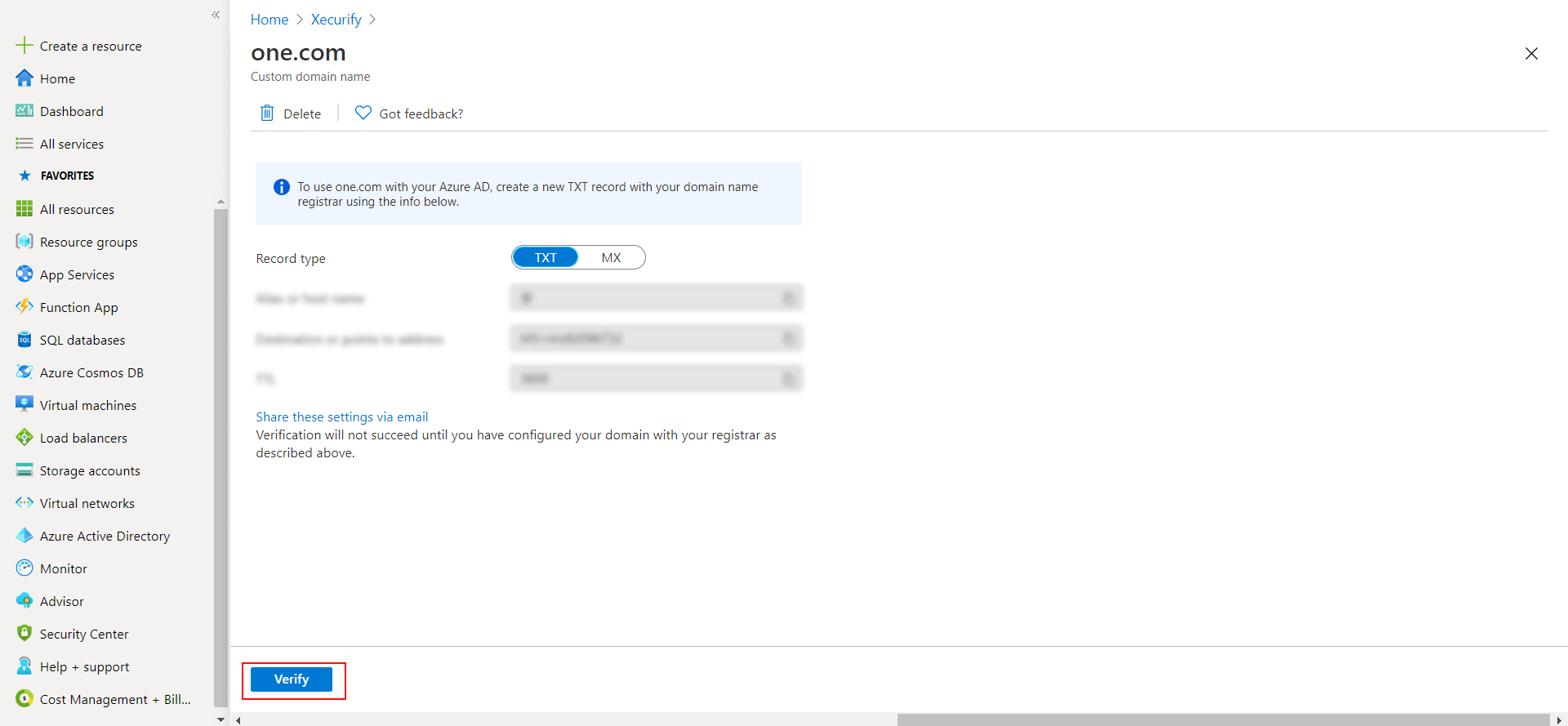
- A new window will open up with TXT/MX records for the domain. You will have to
add the resented
entry in your domain name registrar.
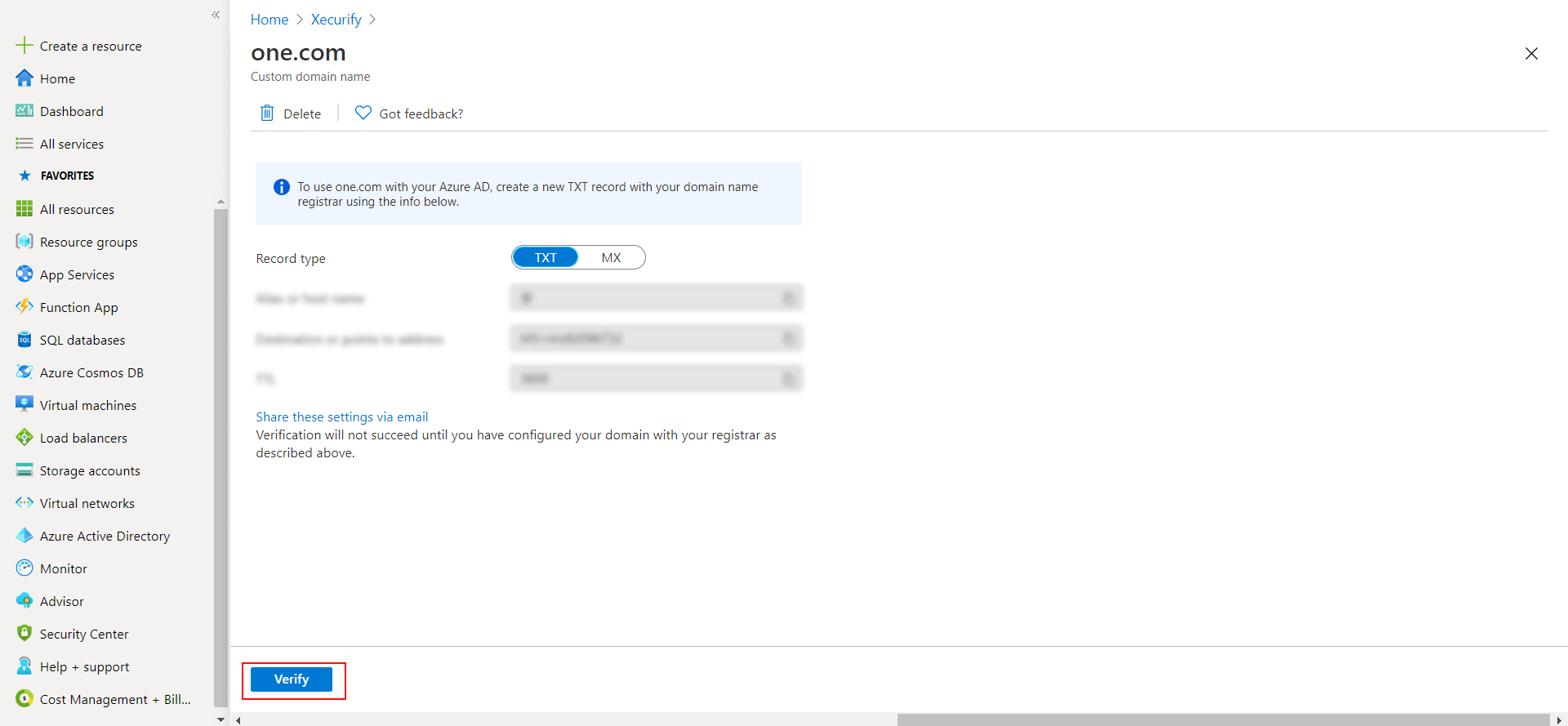
- Click on verify once you have added the entry
Prerequisites
-
To set up IP restriction for the Office 365 Mobile App, first configure SSO for your
application using this link.
Configure user access for Office 365 with IP restriction
Configure Real-time IP restriction for Office 365 apps
Configure IP Restriction for Office 365 apps over mobile
devices
1.
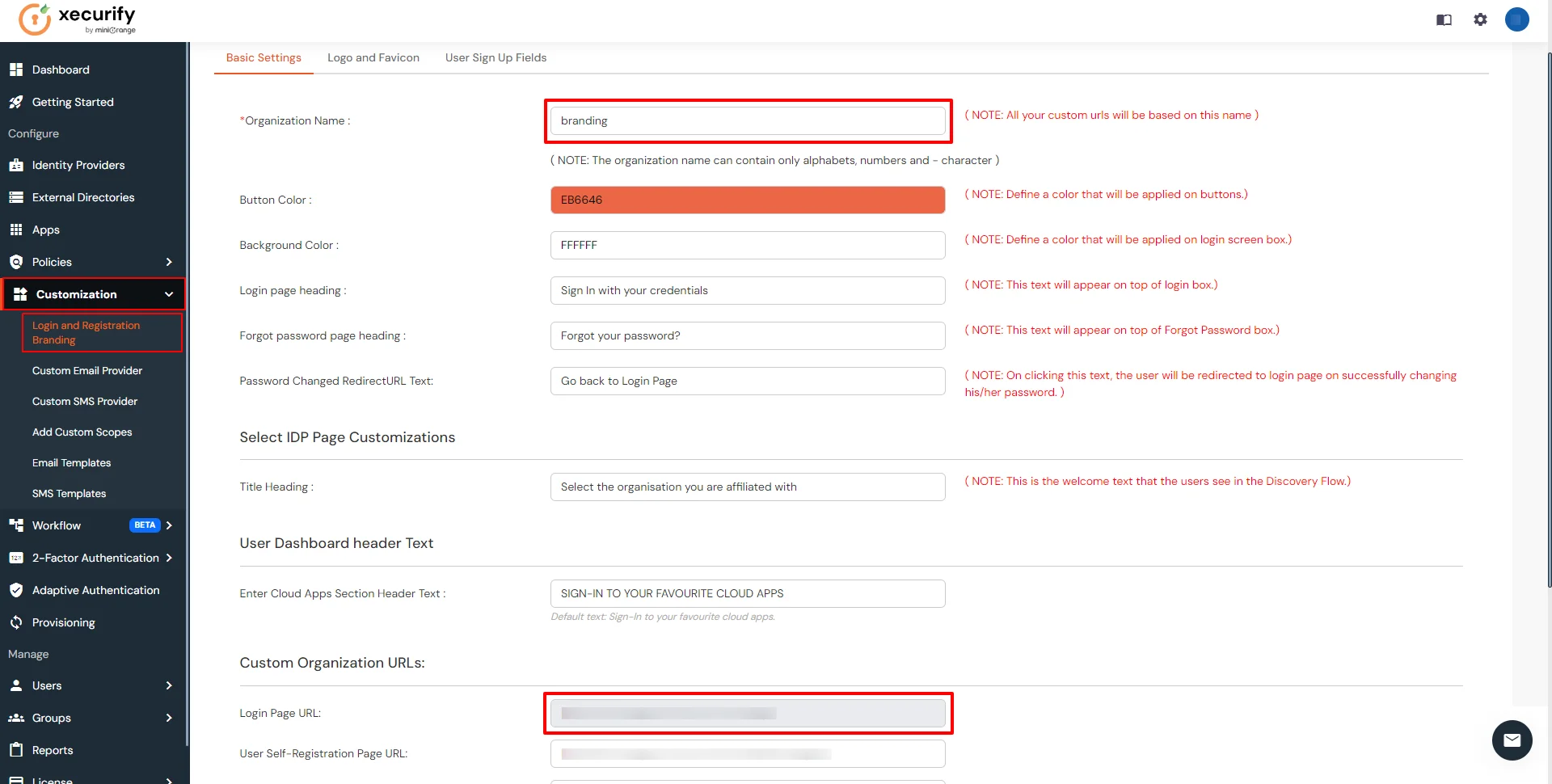
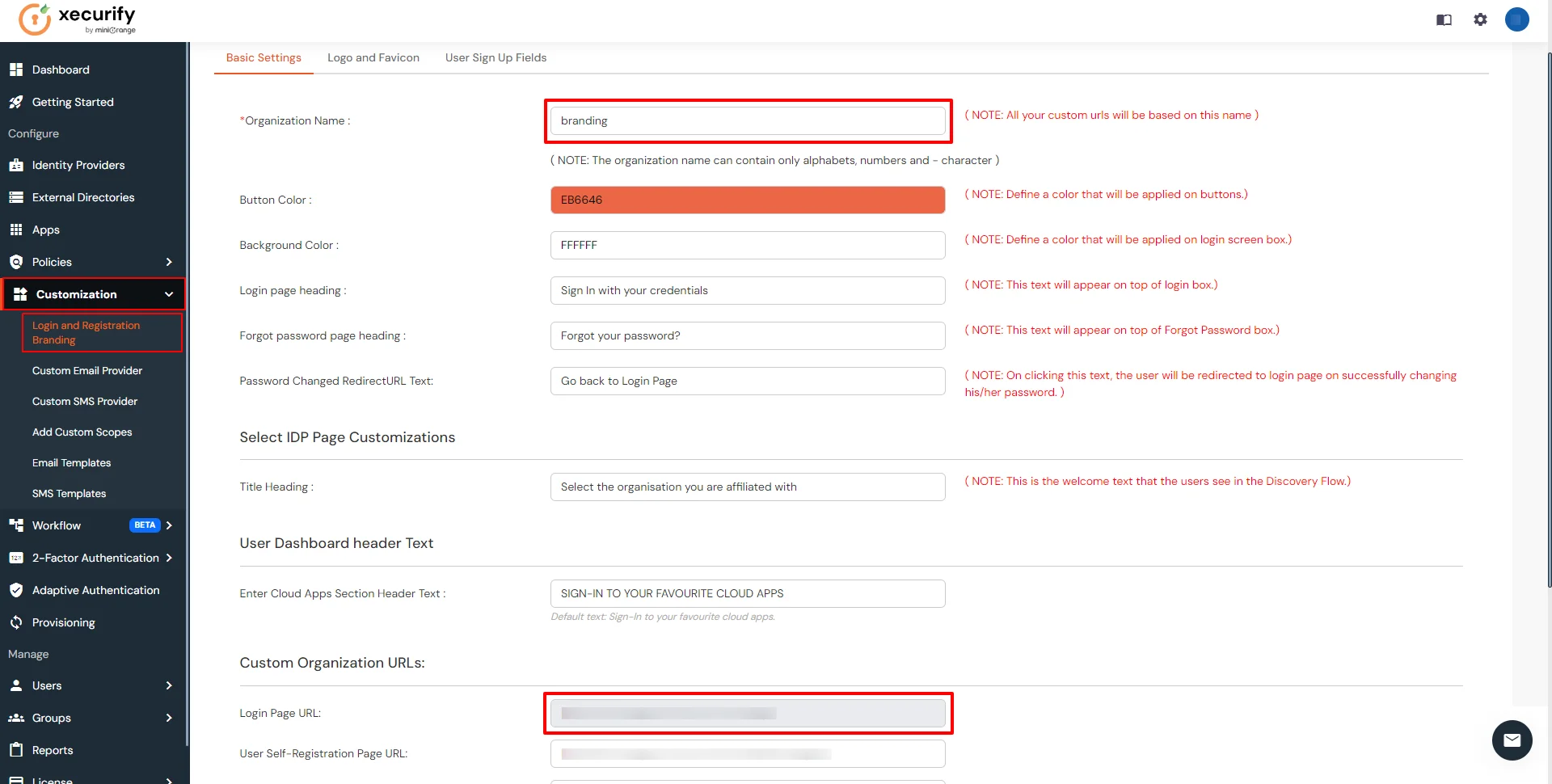
Setup a Custom Branded URL in miniOrange Admin Console
Office 365 IP Restriction requires a custom branded URL to be set. Access to miniOrange and
connected
resources will need to be through the custom branded URL in the format:
https://<custom_domain>.xecurify.com/moas
- Login to miniOrange Admin
Console.
- Click on Customization in the left menu of the dashboard.
- In Basic Settings, set the Organization Name as the custom_domain name.
- Click Save. Once that is set, the branded login URL would be of the format
https://<custom_domain>.xecurify.com/moas/login
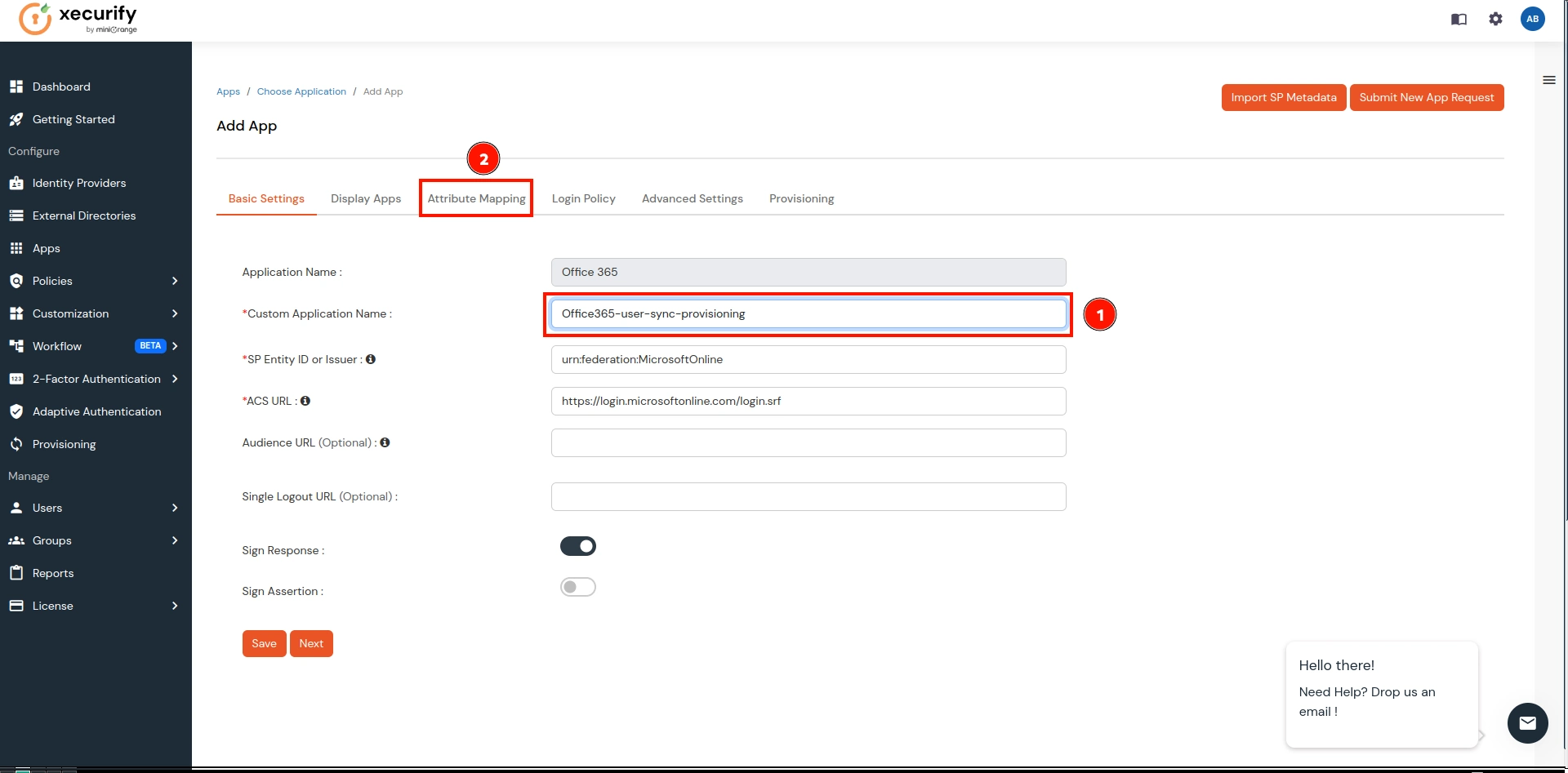
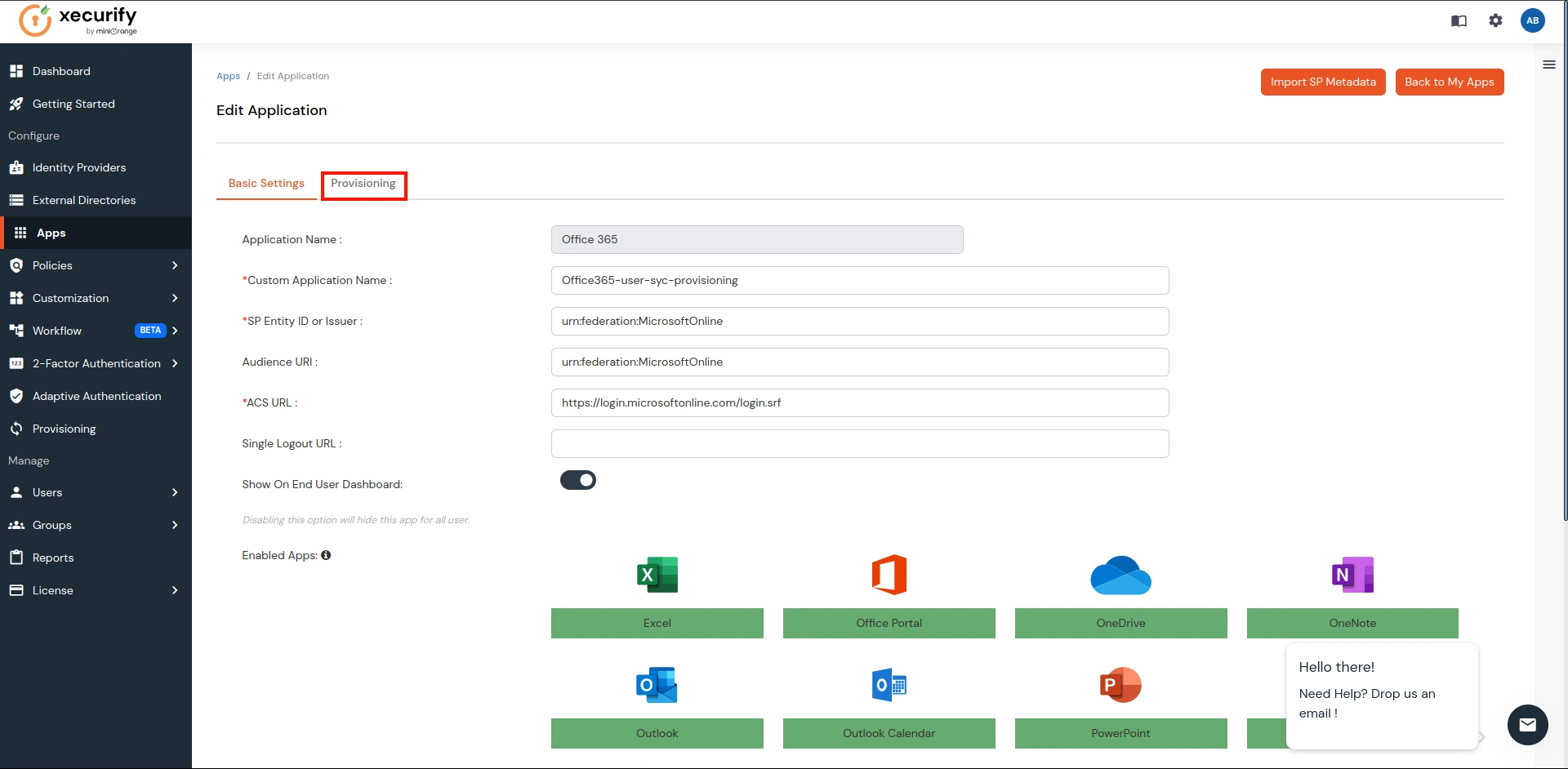
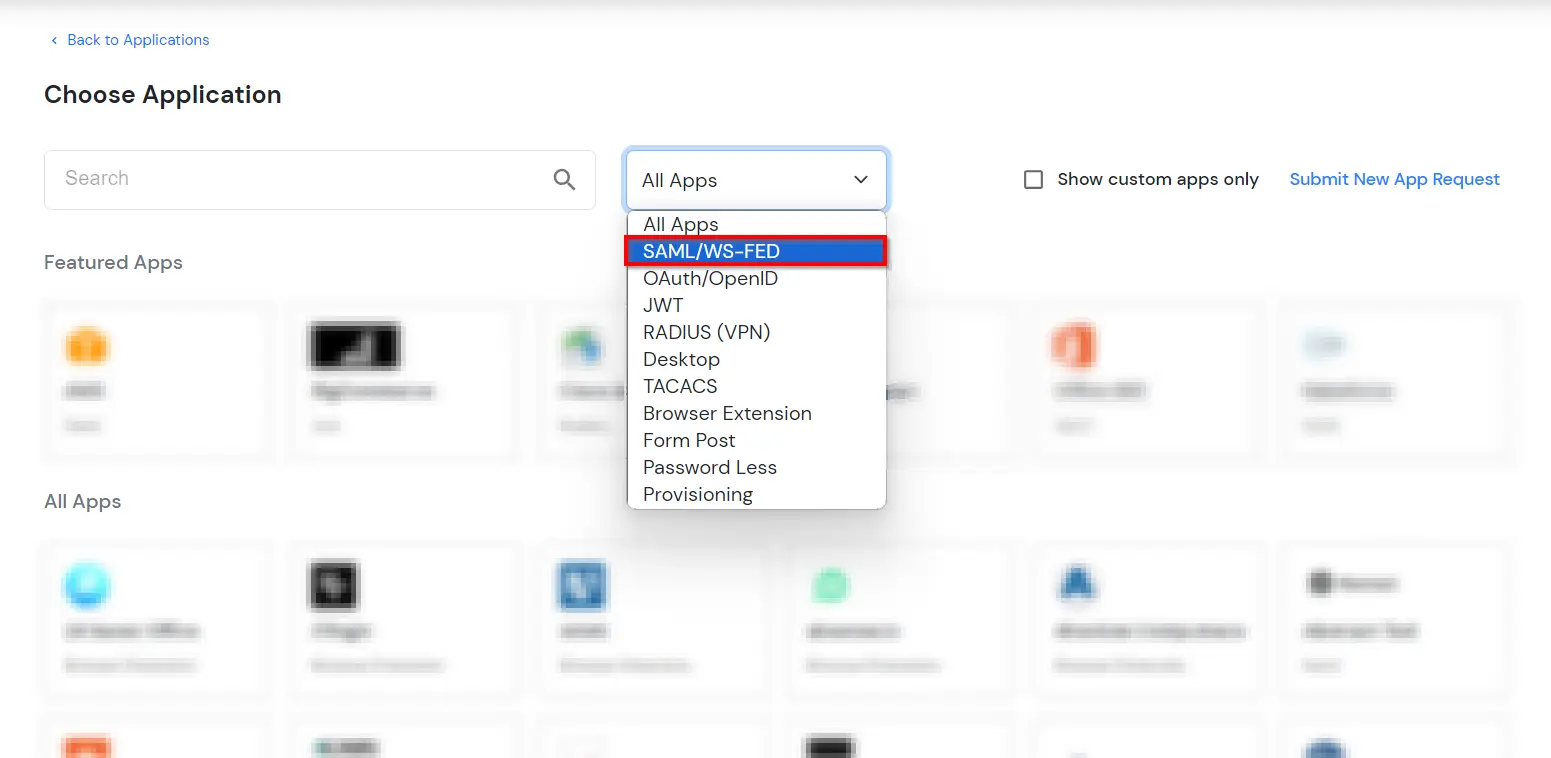
2. Configure Office 365 in miniOrange
- Login into miniOrange Admin
Console.
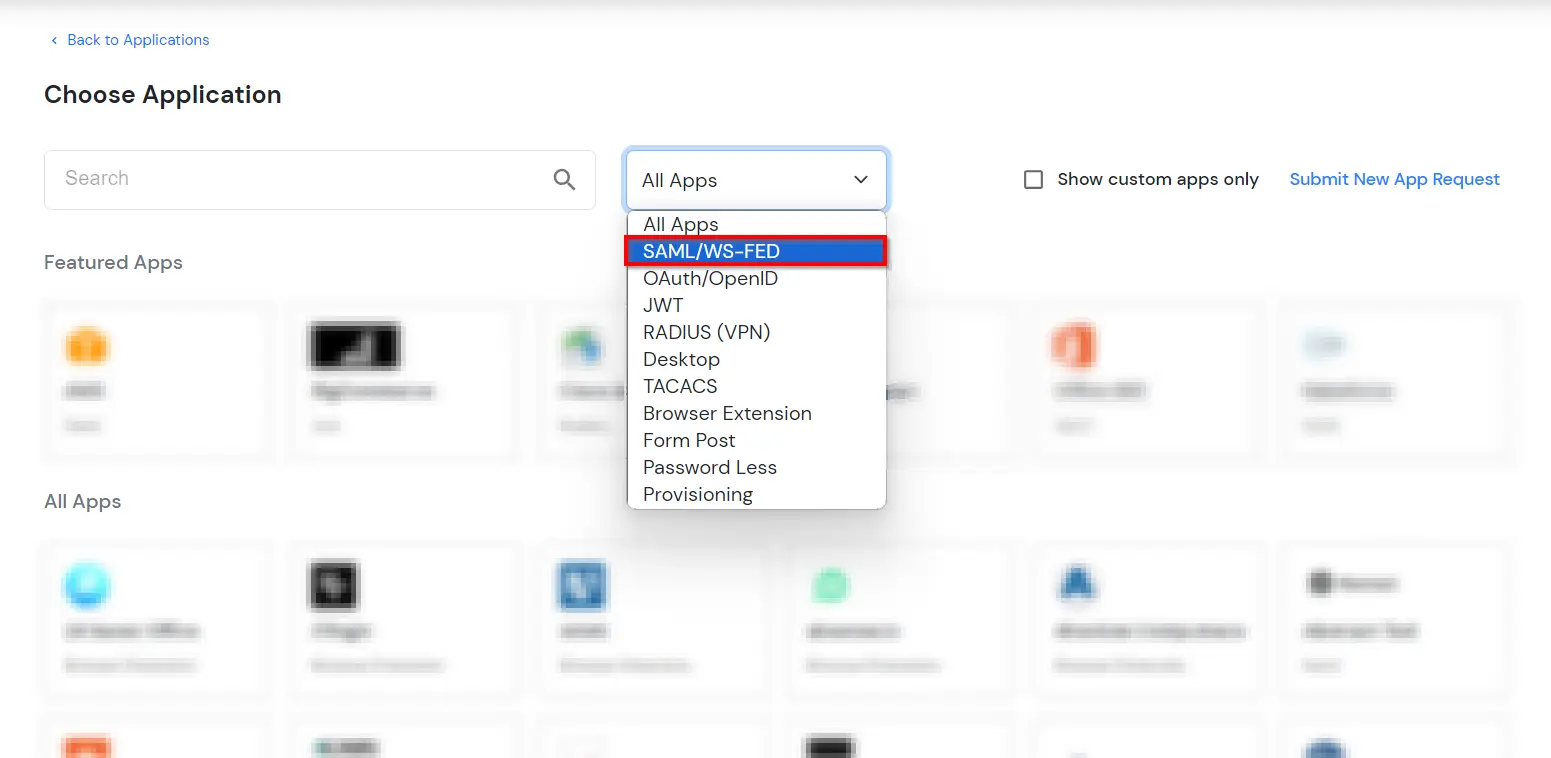
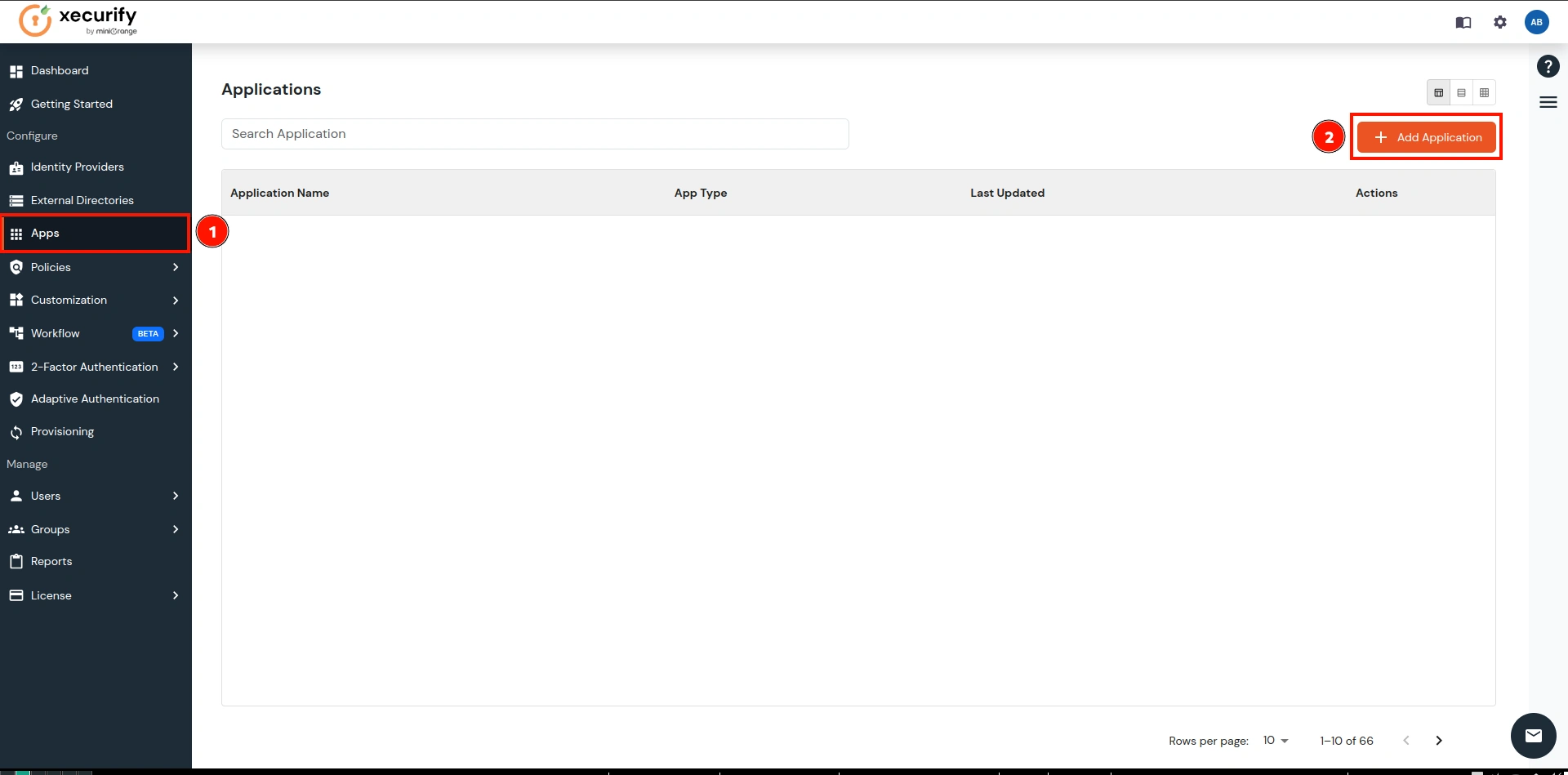
- Go to Apps and click on Add Application button.

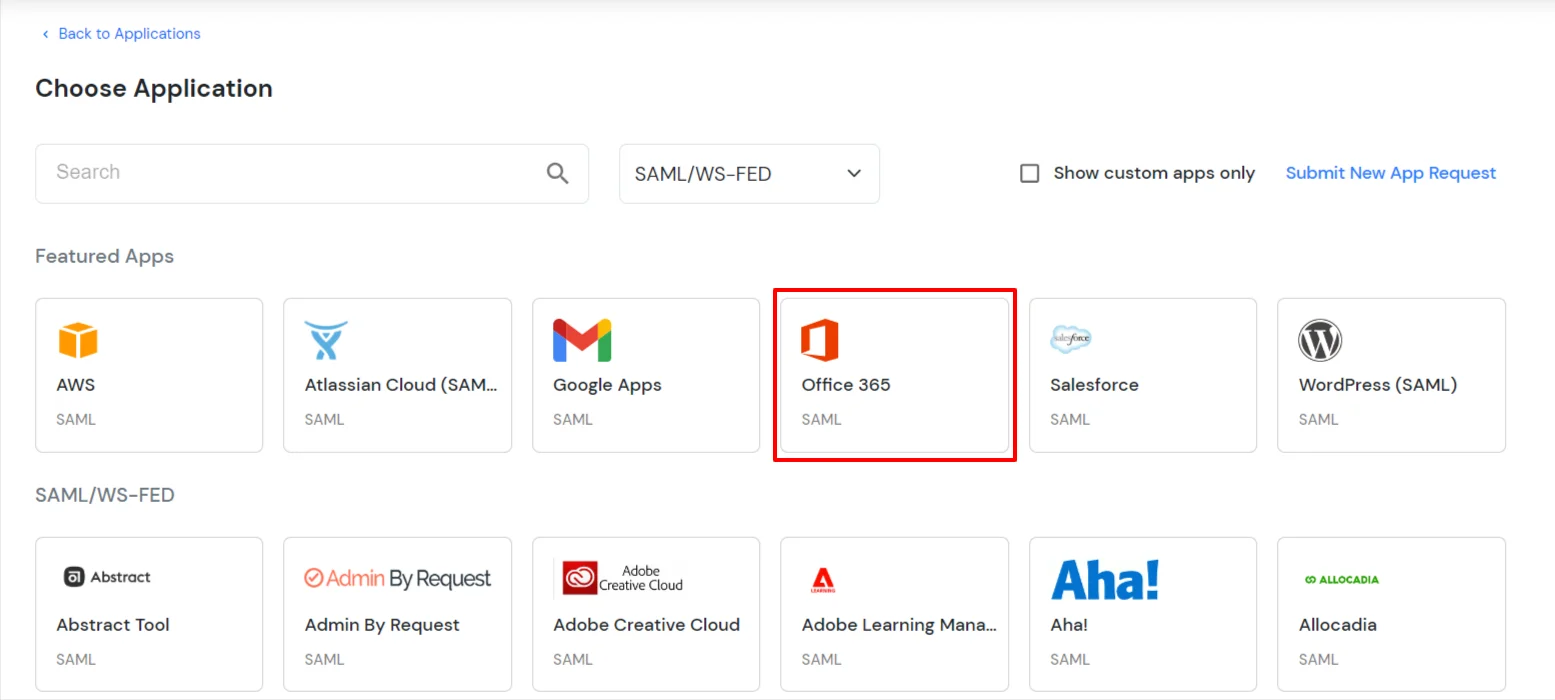
- In Choose Application Type click on Create App button in SAML/WS-FED
application type.
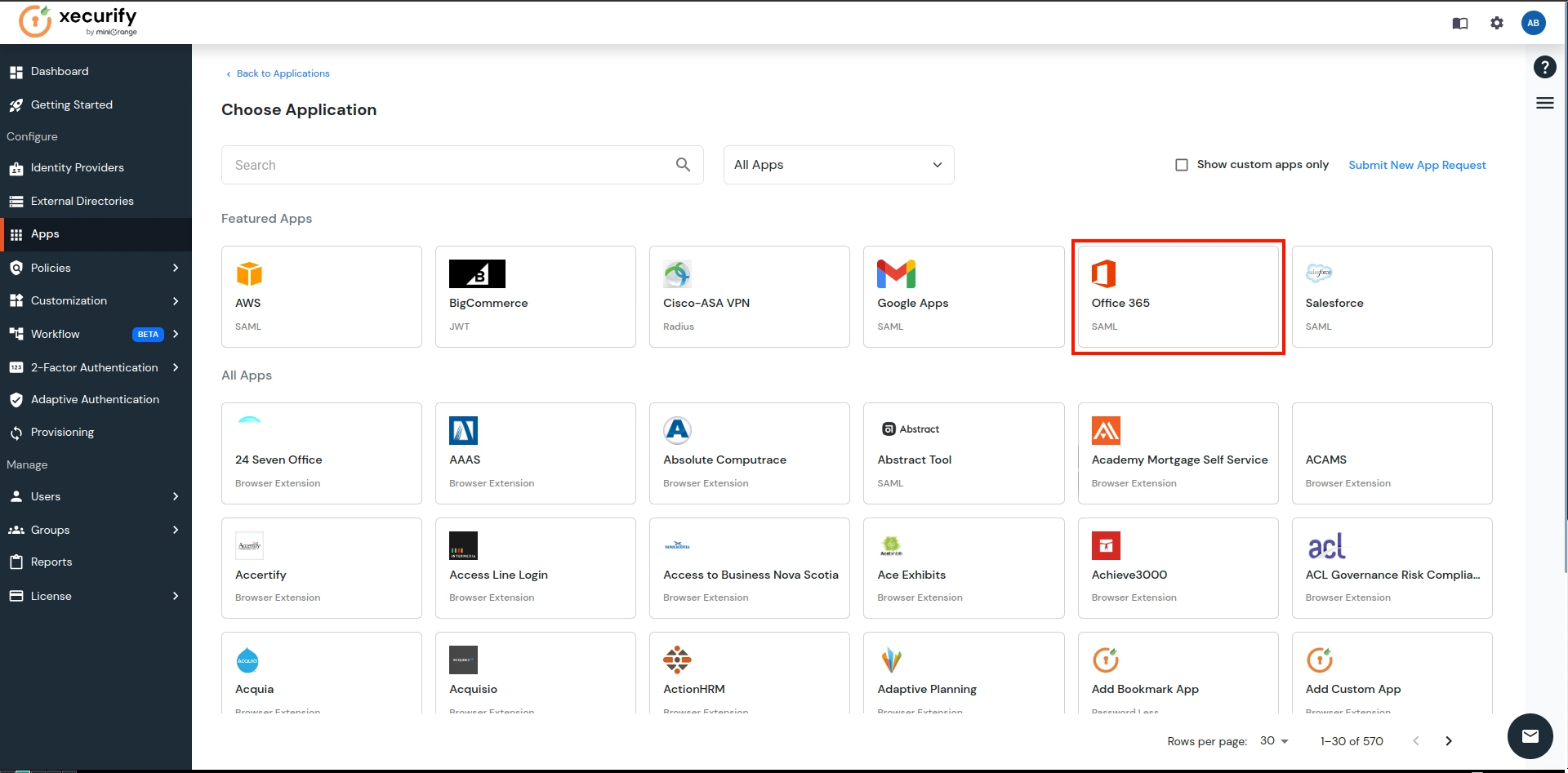
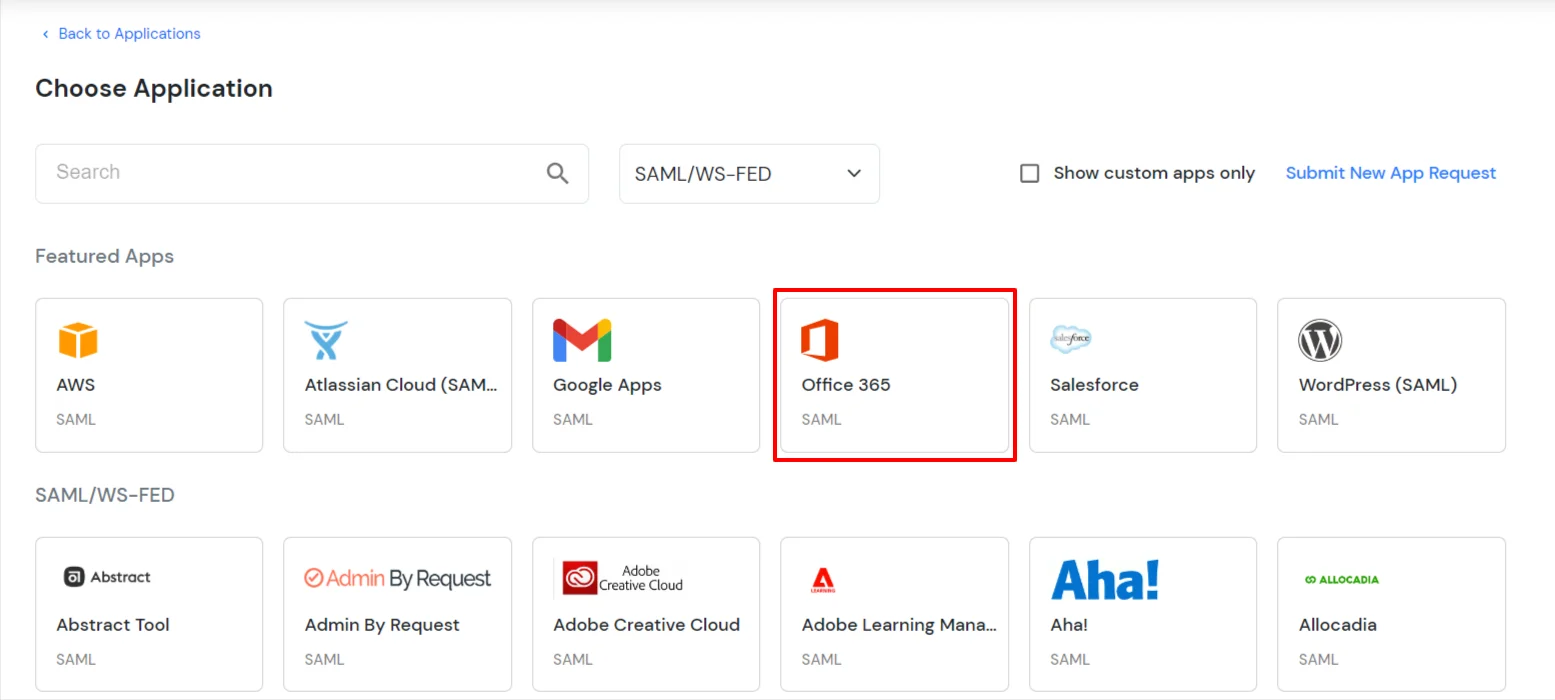
- In the next step, search for Office 365. Click on Office 365 app.
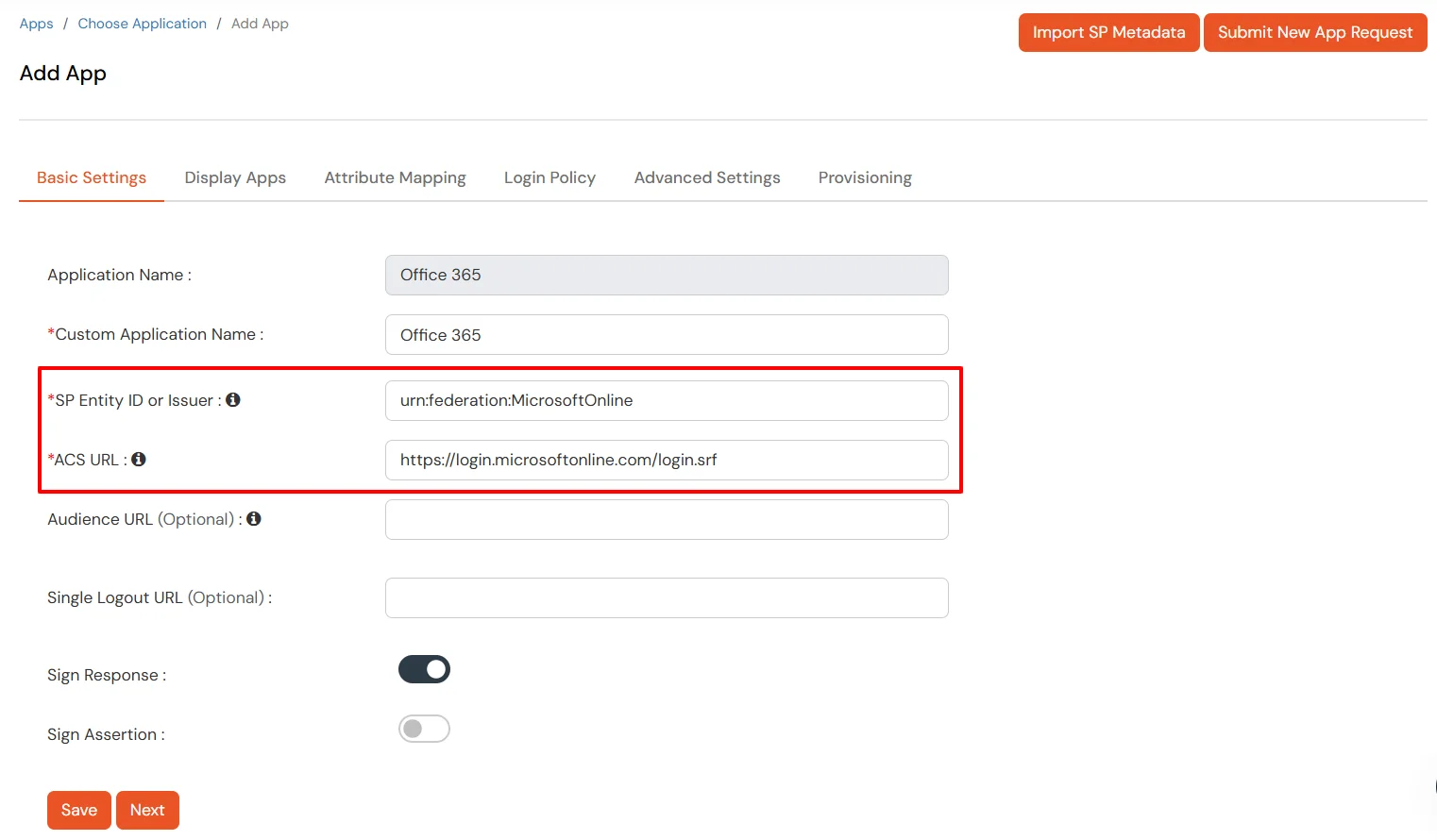
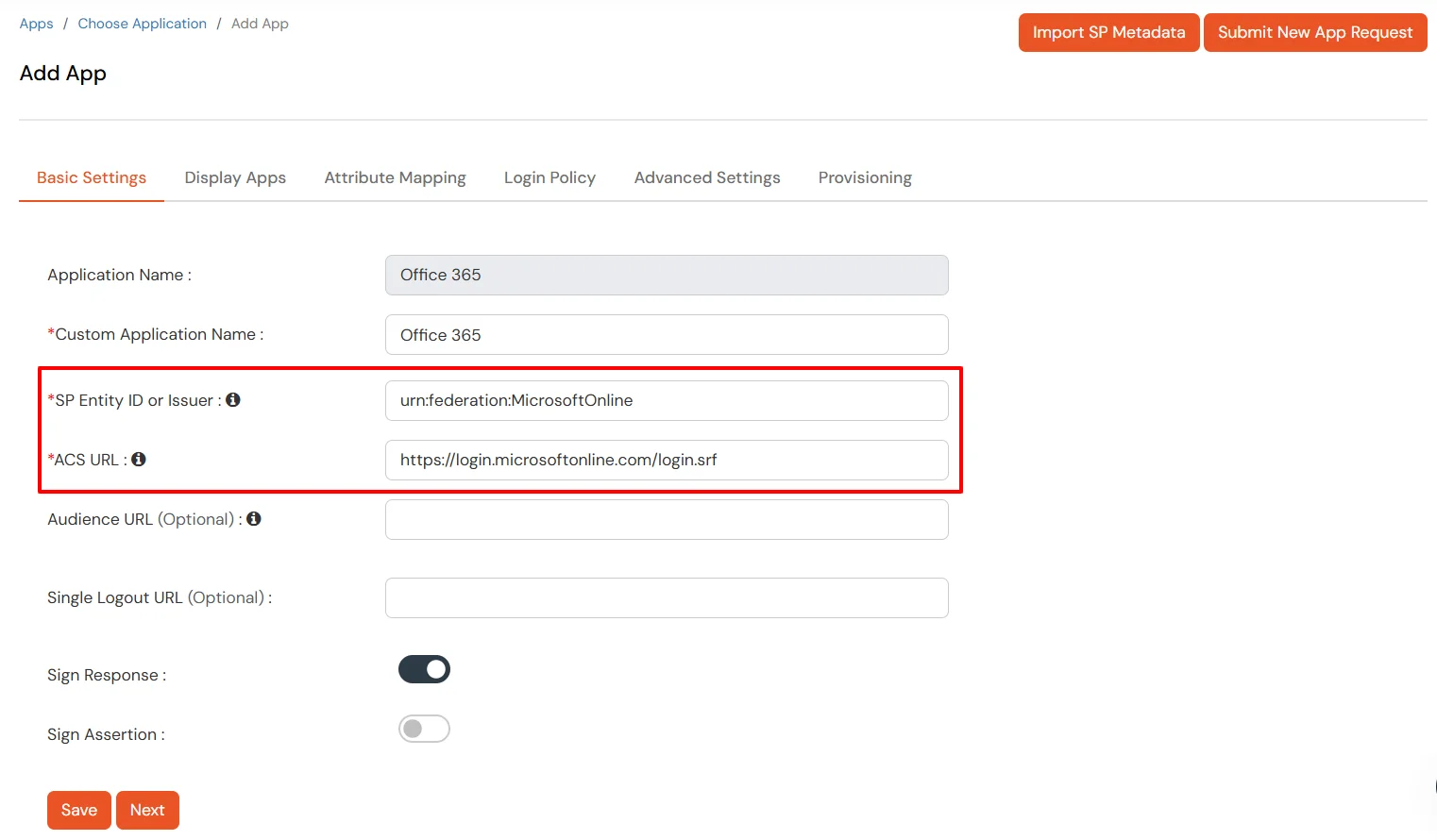
- Make sure the SP Entity ID or Issuer is: urn:federation:MicrosoftOnline
- Make sure the ACS URL is: https://login.microsoftonline.com/login.srf
- Click on Next.
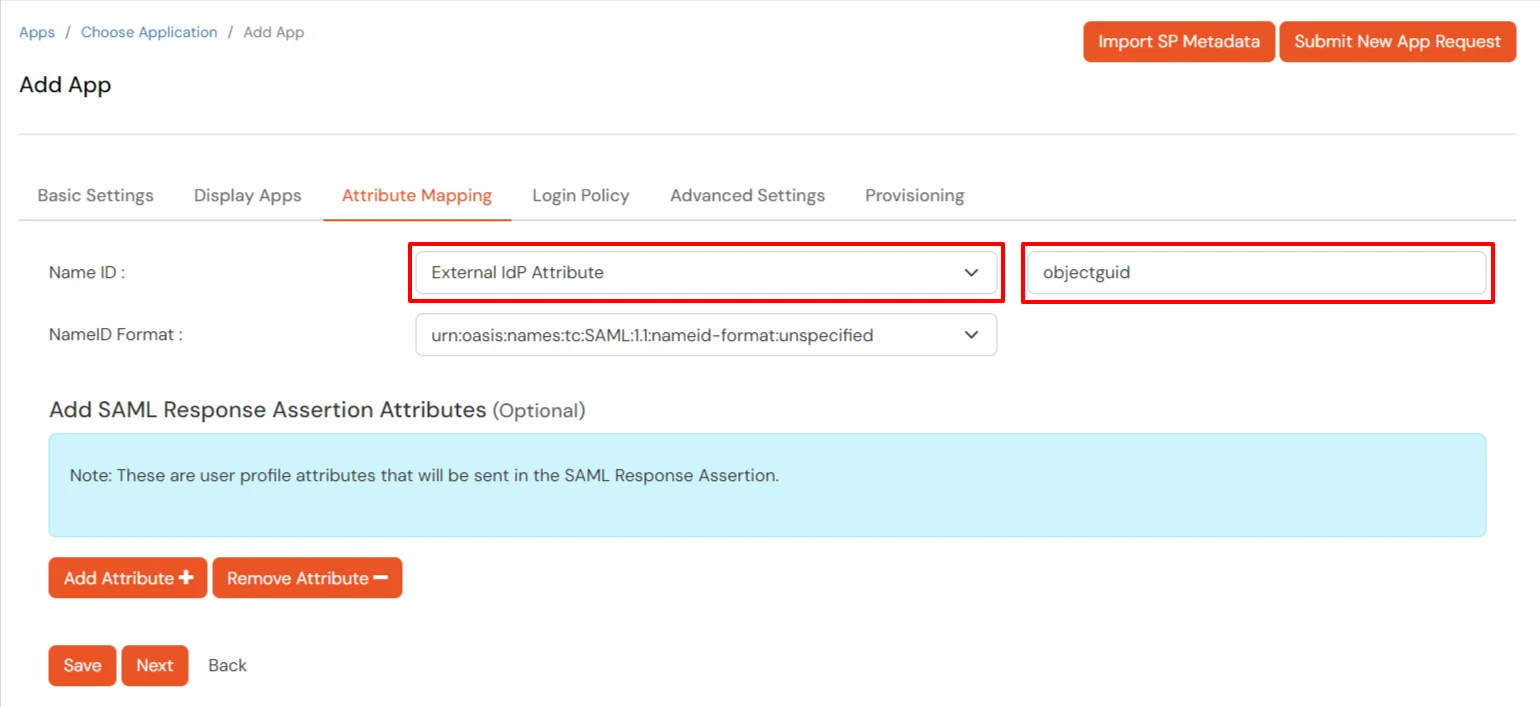
- Configure Name ID based on the User Store you are using:
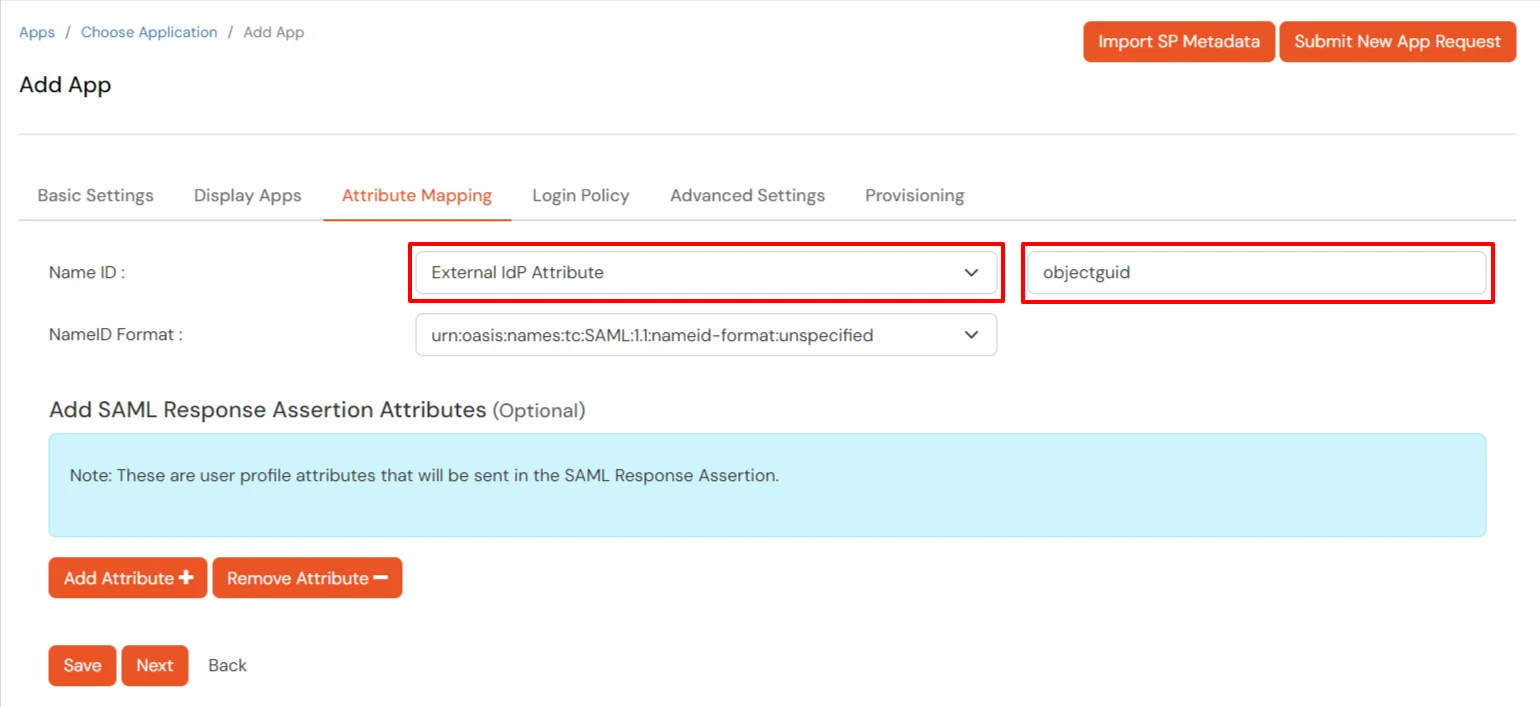
- Using Active Directory / miniOrange brokering service: Select External IDP
Attribute from the
dropdown and add objectguid in the text-box that appears.
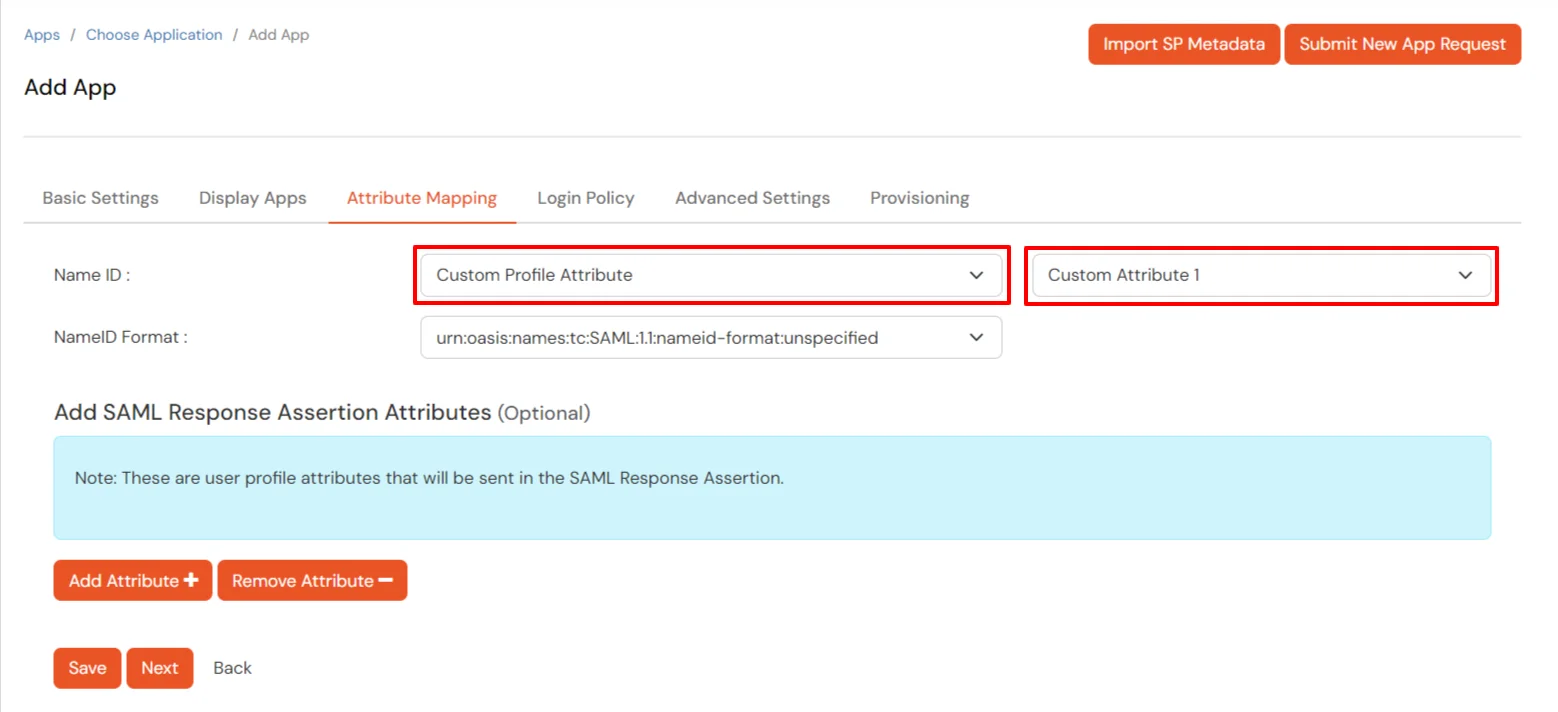
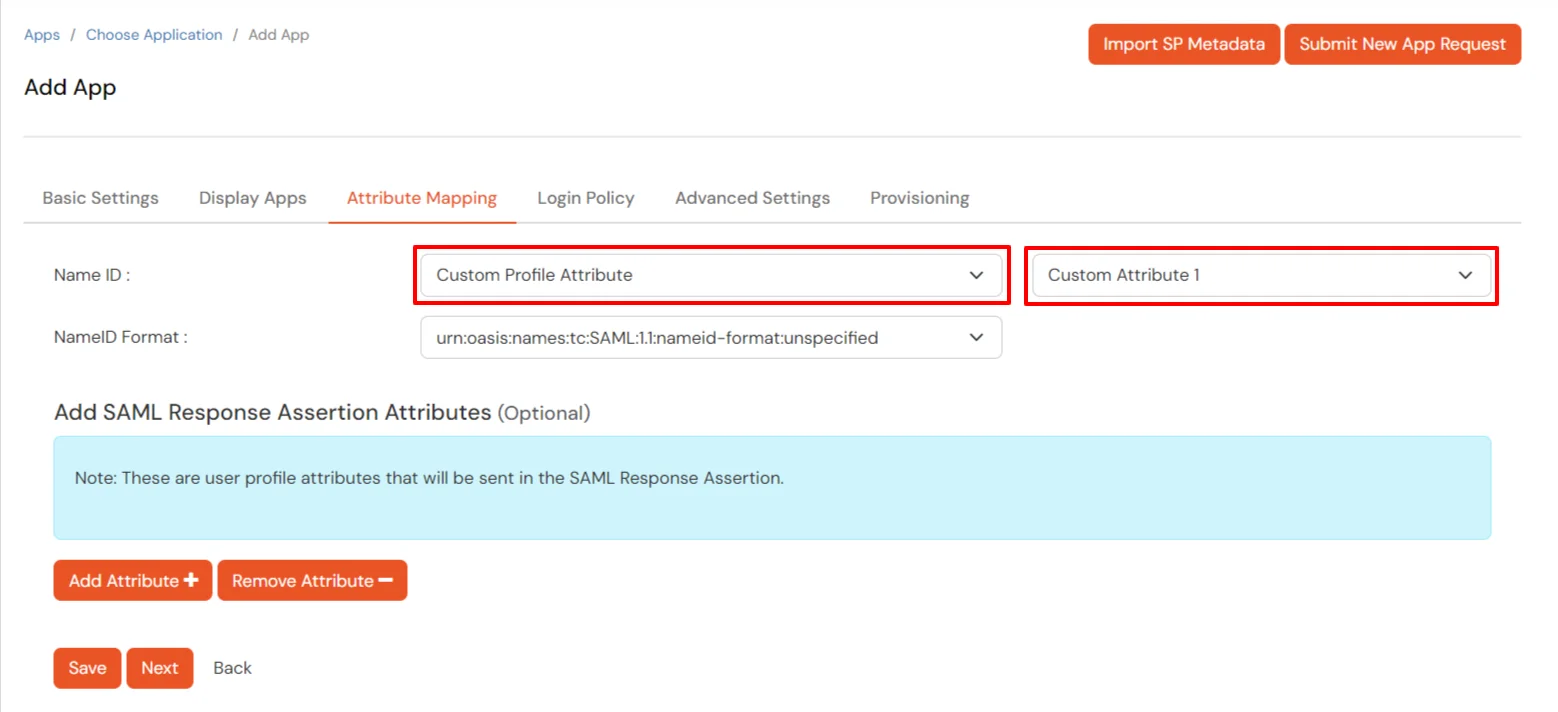
- Using miniOrange as a User Store: Select Custom Profile Attribute and select
a Custom
Attribute from the drop-down.
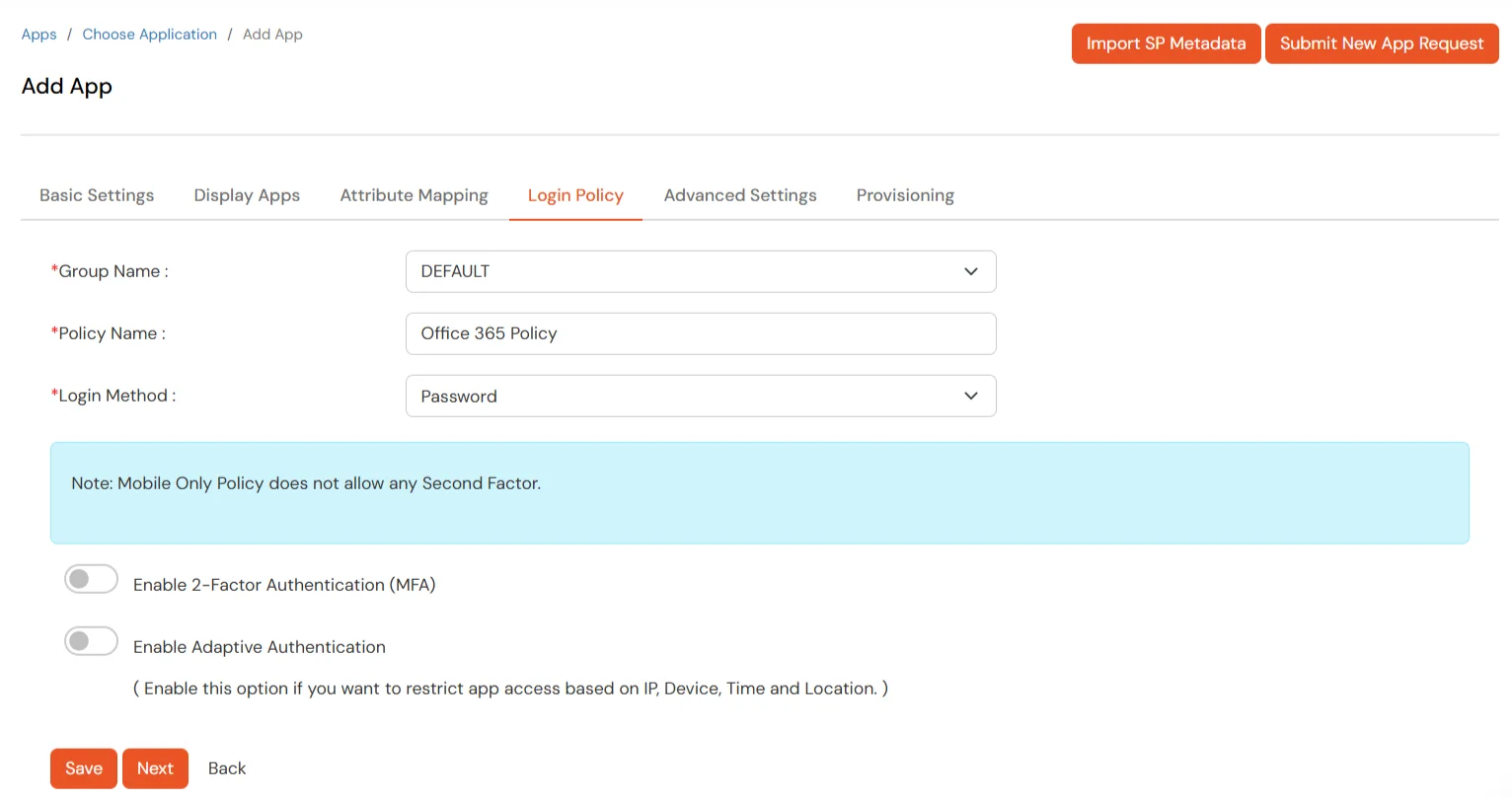
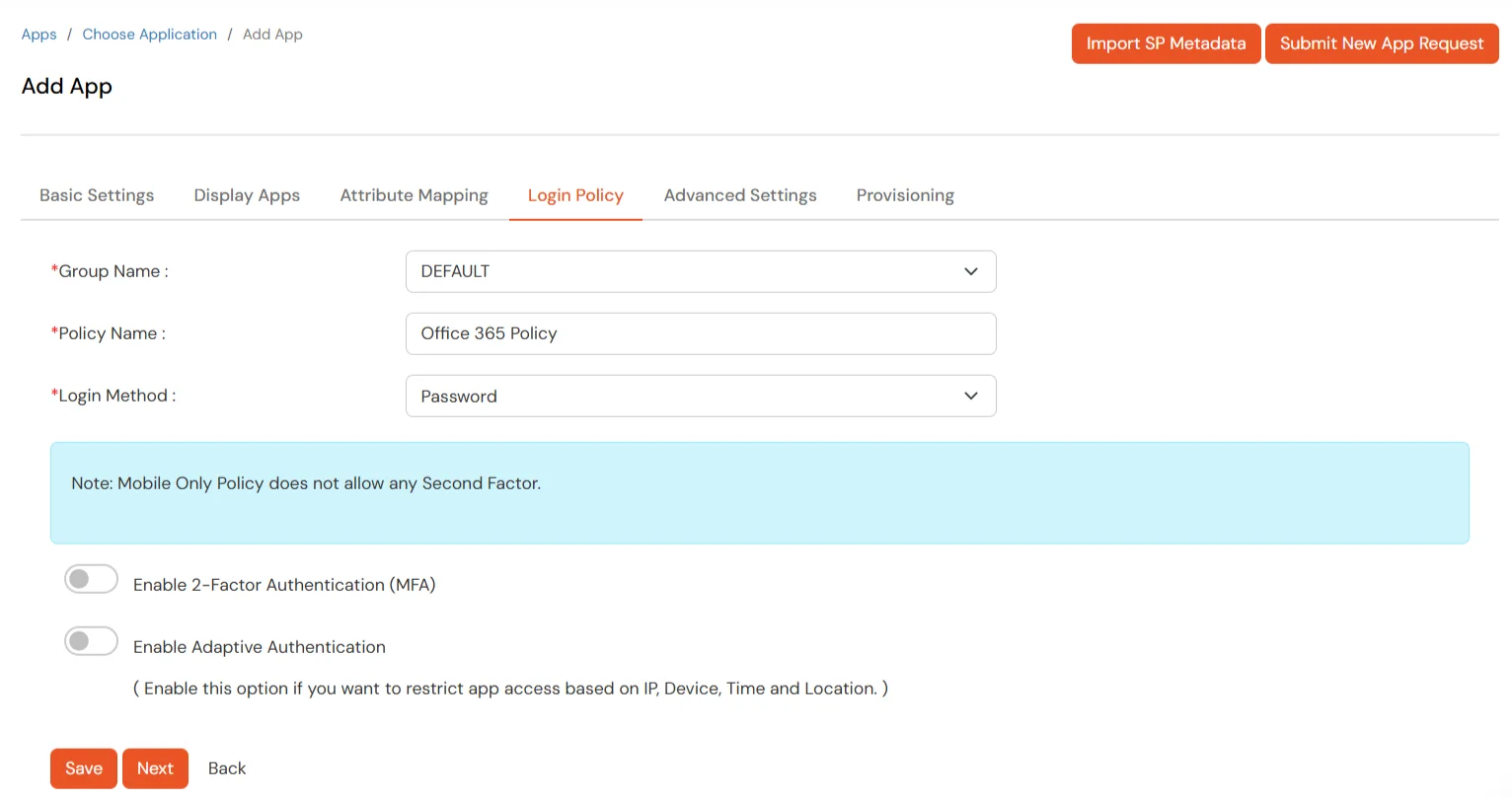
- Set the login policy. You can choose to enable 2FA for login or have users login
using a standard
username-password.
- Click on Save to configure Office 365.
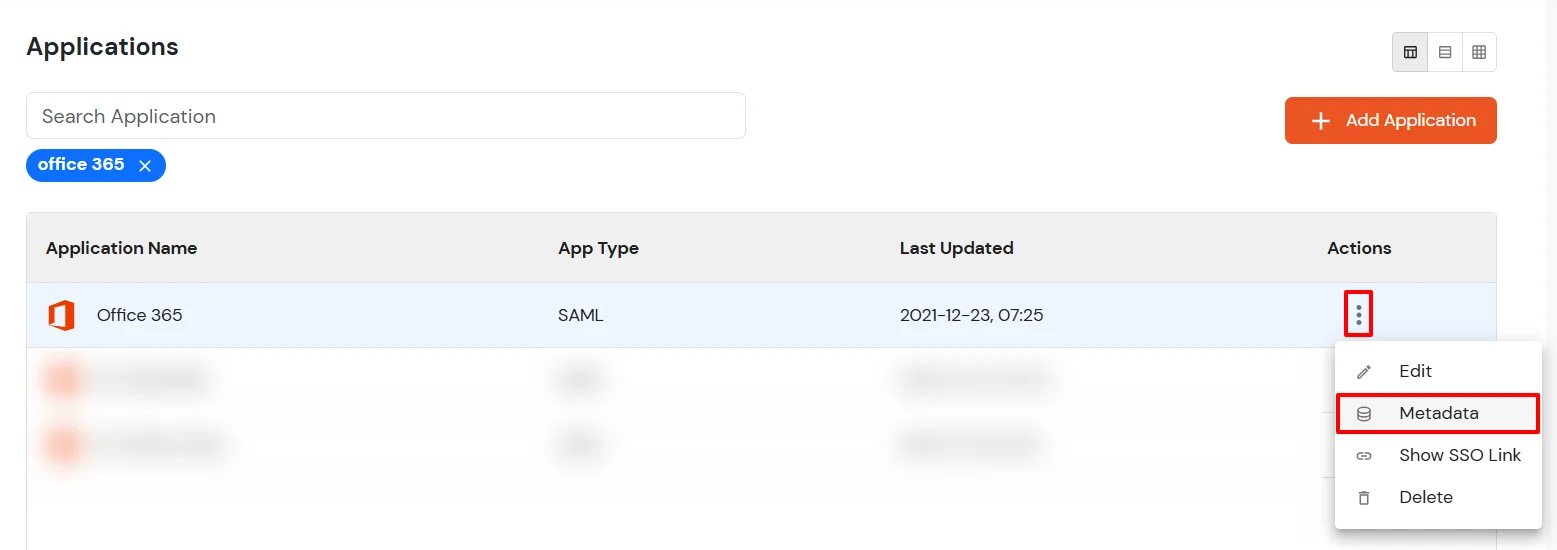
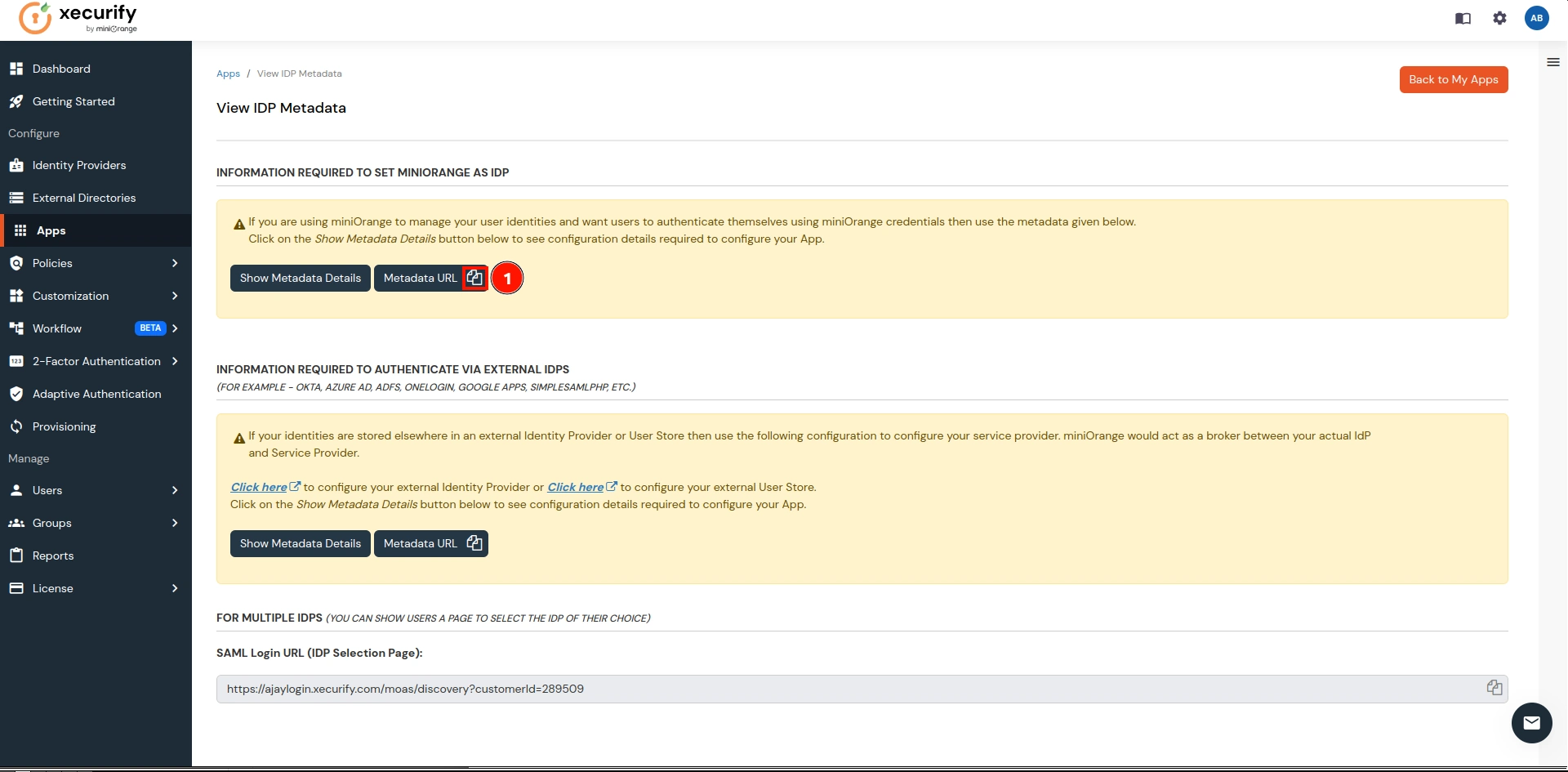
3. Configure Microsoft Online Services
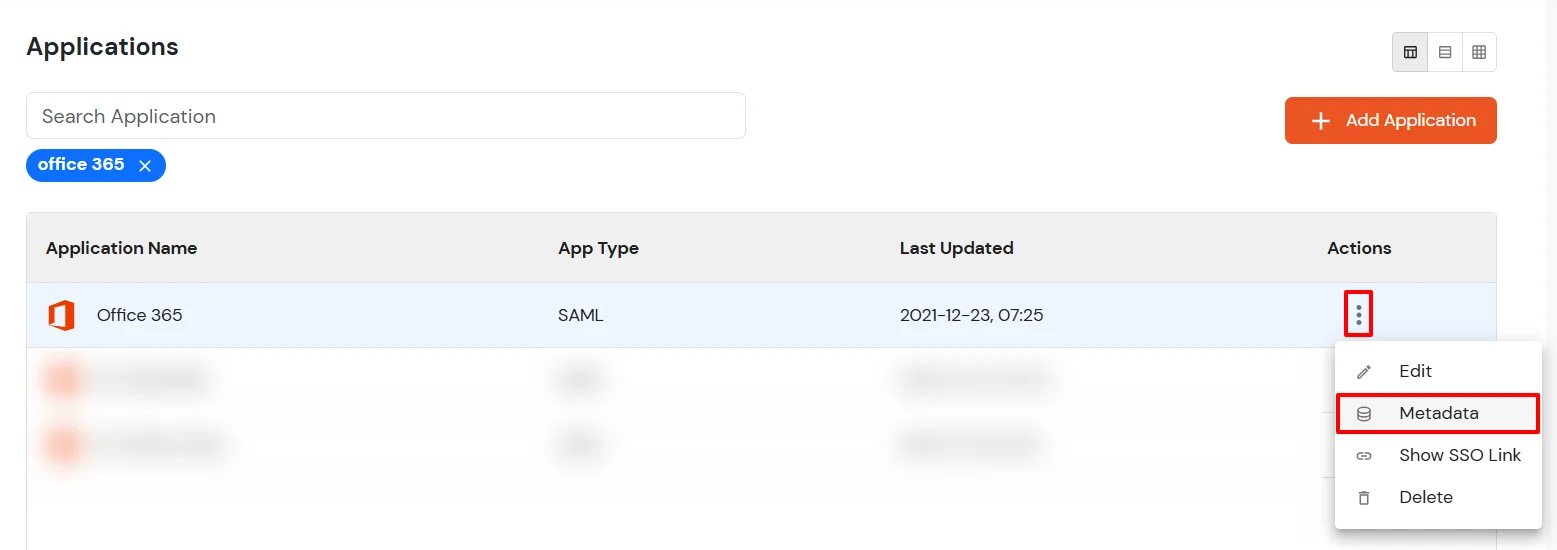
- Click on Select dropdown and choose Metadata.
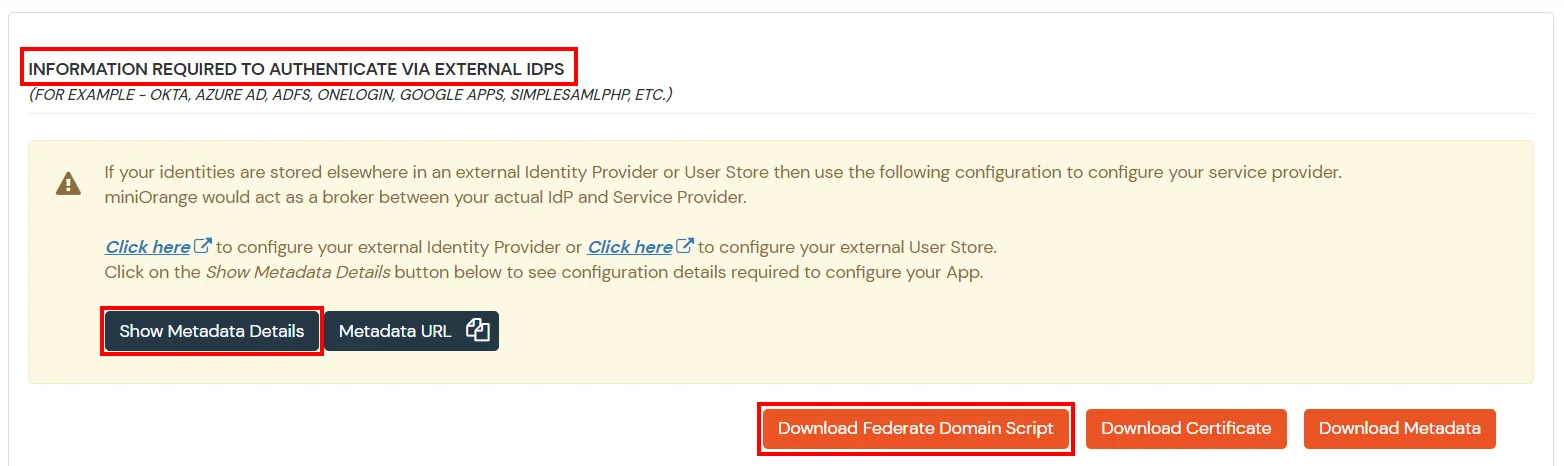
- Click on the Download Federate Domain Script button under "INFORMATION REQUIRED TO
AUTHENTICATE VIA EXTERNAL IDPS"
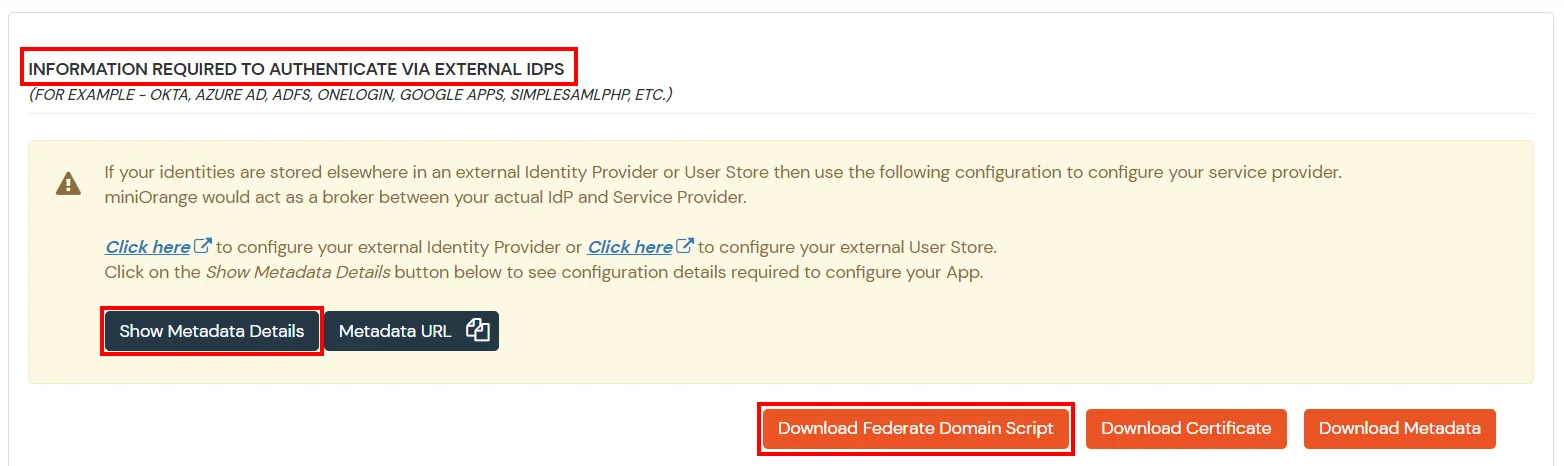
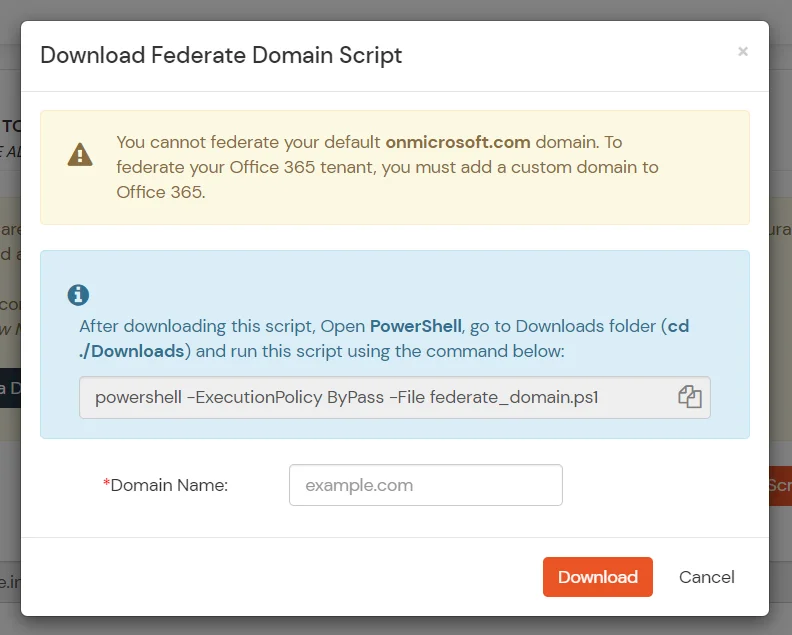
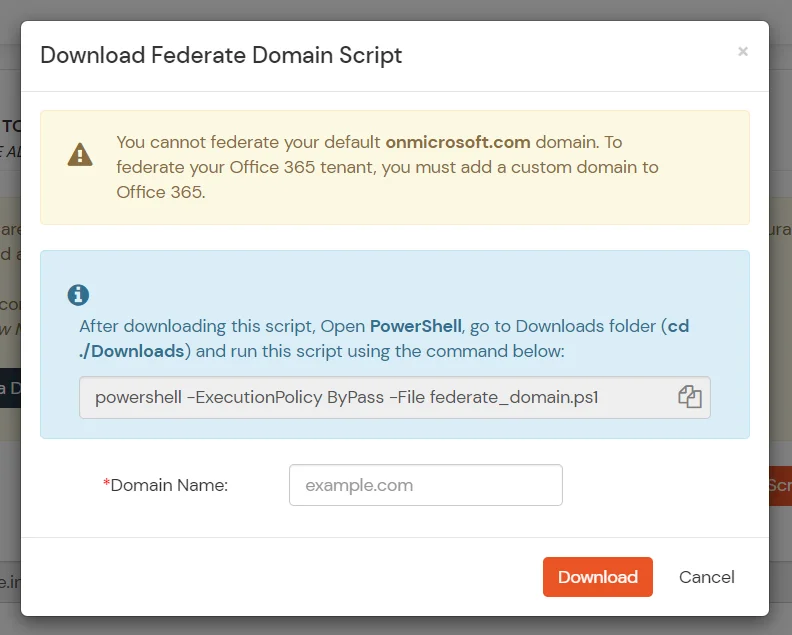
- Enter the domain name that you want to federate and click on Download.
Note: You cannot federate your default "onmicrosoft.com" domain. To federate
your Office
365 tenant, you must add a custom domain to Office 365.
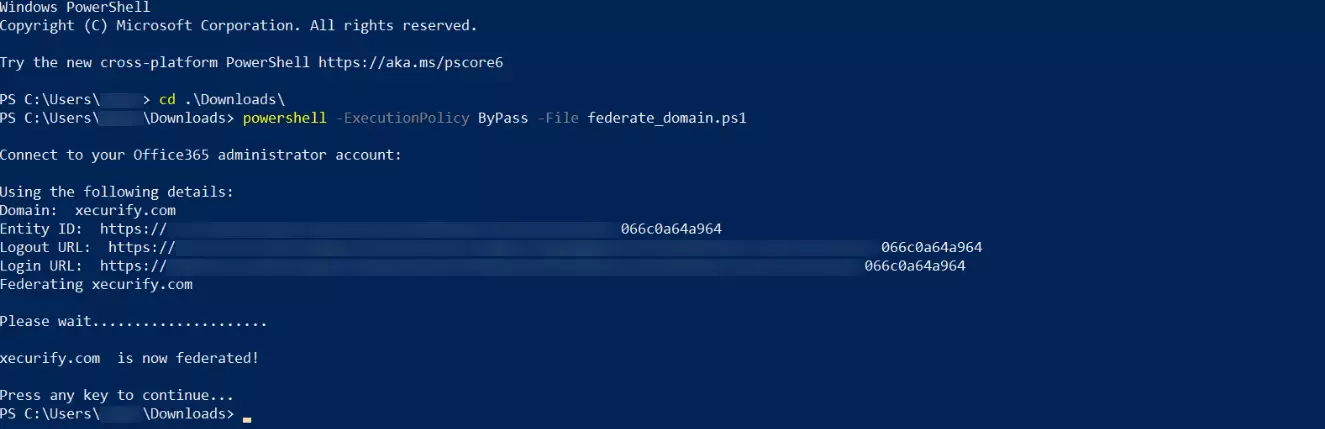
- After downloading the script, Open PowerShell run the federate_domain script using:
cd ./Downloads
powershell -ExecutionPolicy ByPass -File federate_domain.ps1
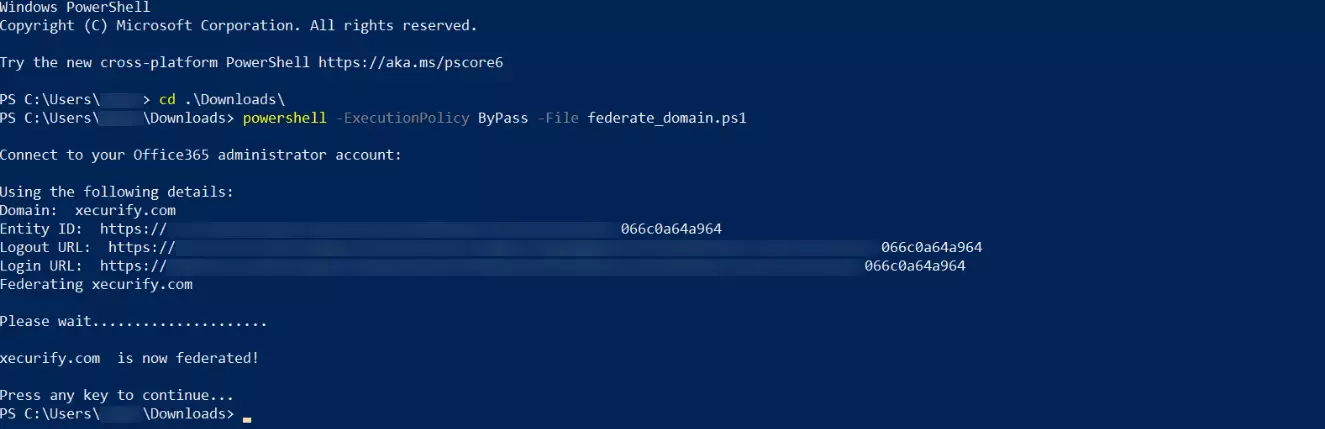
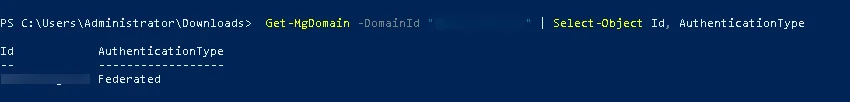
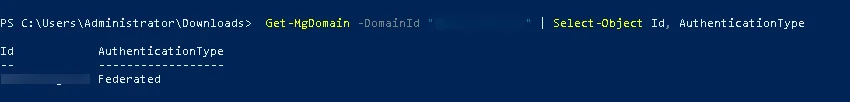
- Your domain is now federated. Use the commands below to check your federation settings:
Get-MgDomain -DomainId "<domain>" | Select-Object Id, AuthenticationType
4.
Configure IP Restriction: Restricting access with IP Blocking
You can allow an IP Address in a certain range for SSO or you can deny it based on your
requirements and
you can also challenge the user to verify their authenticity. Adaptive authentication manages
the user
authentication based on different factors such as Device ID, Location, Time of Access, IP
Address, and many
more, thus improving the security and functionality of Single Sign-On.
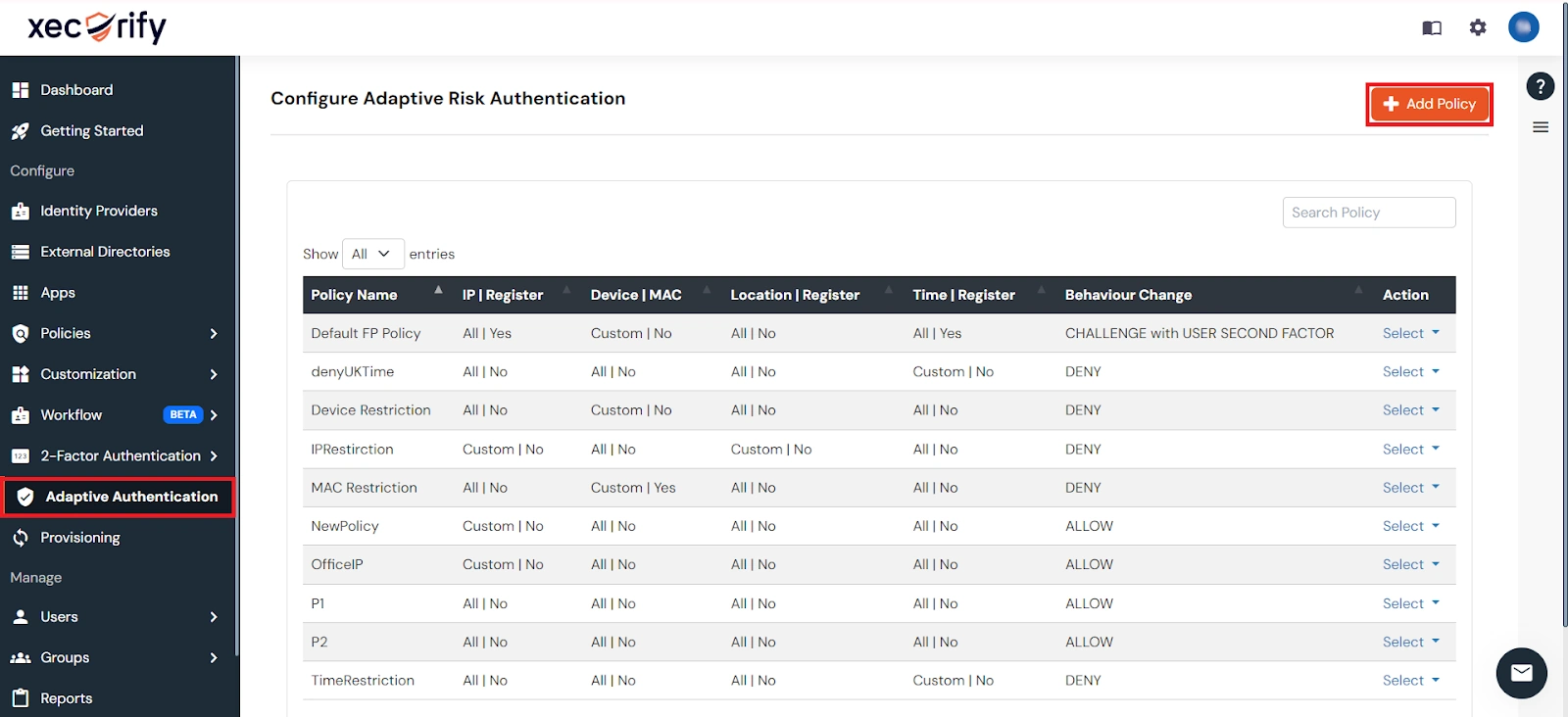
You can configure Adaptive Authentication with IP Blocking in the following way:
- Go to Adaptive Authentication from the left navigation bar.
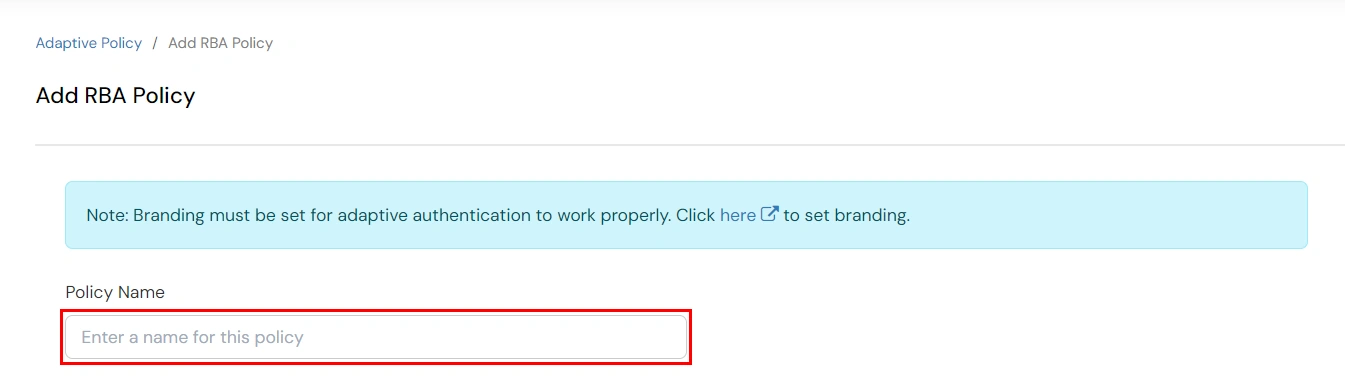
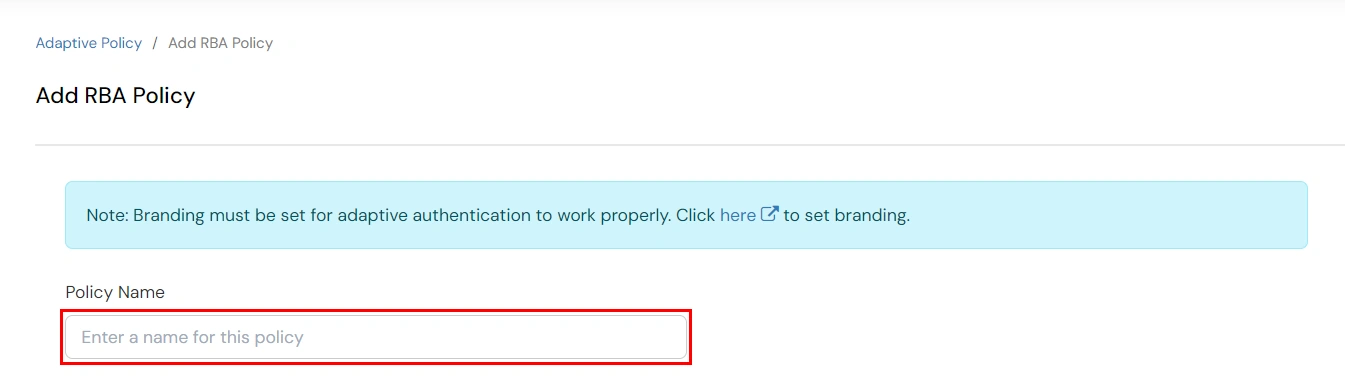
- Click on Add Policy tab.
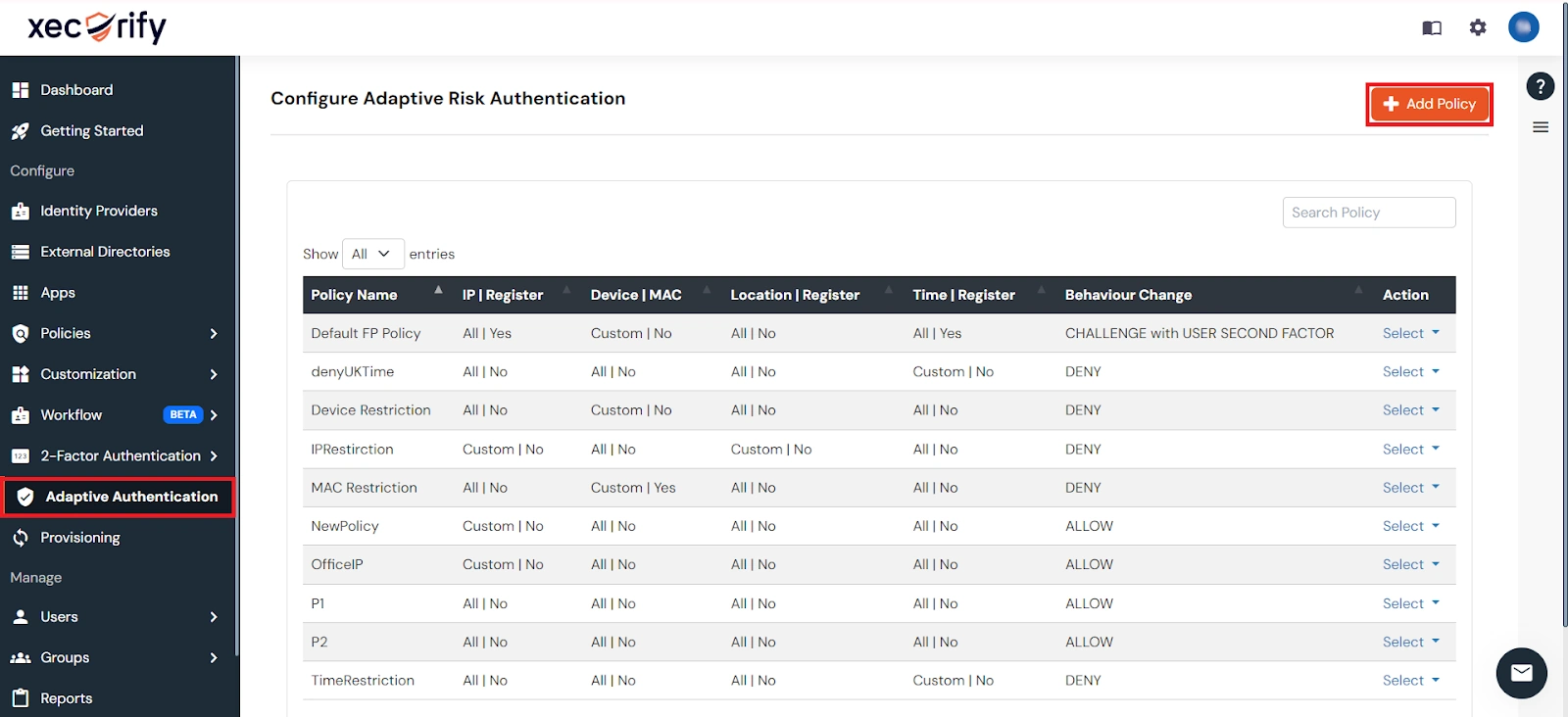
- Add a Policy Name for your Adaptive Authentication Policy.
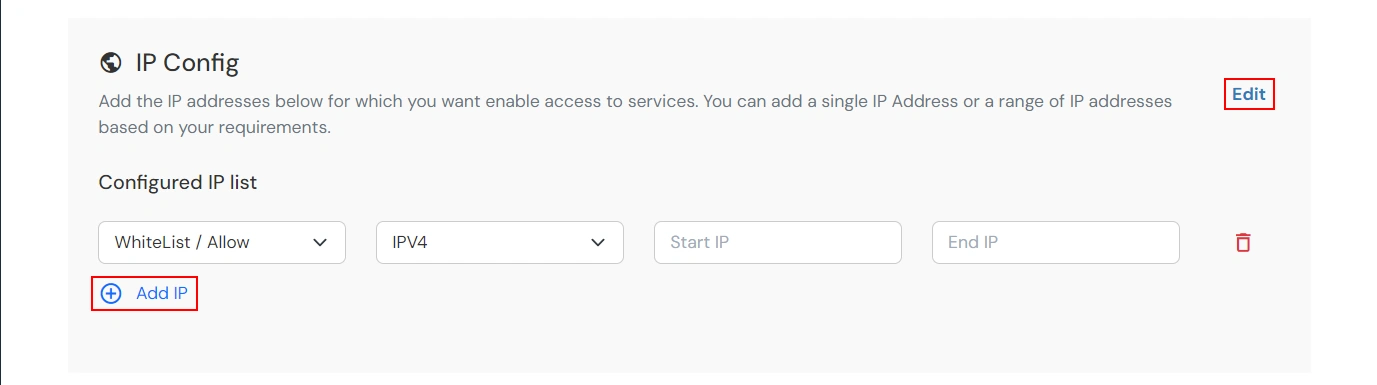
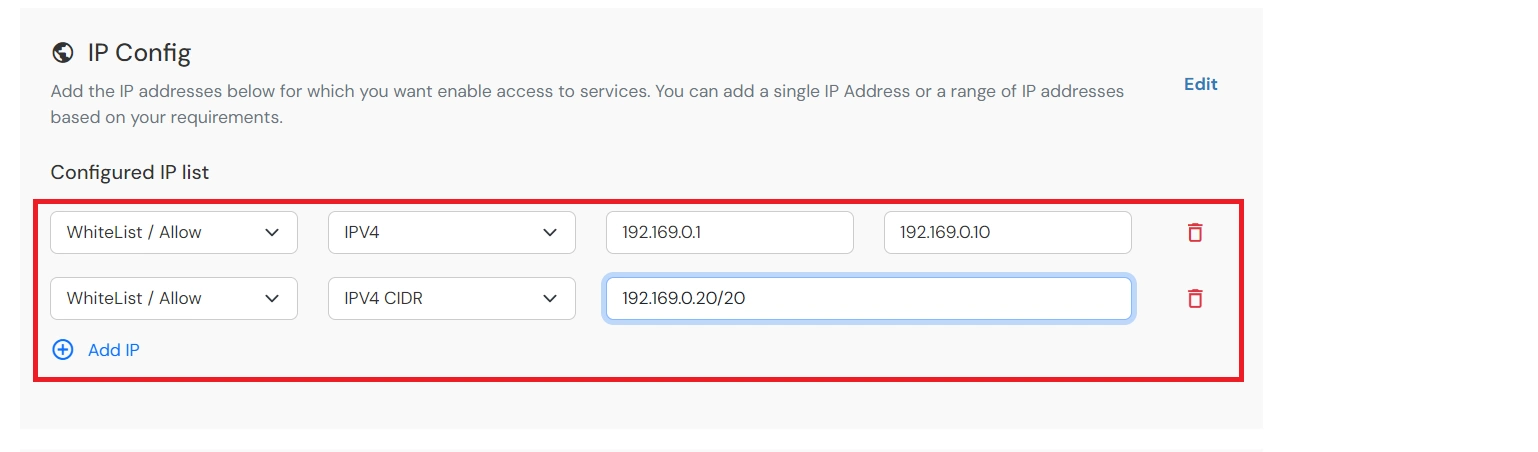
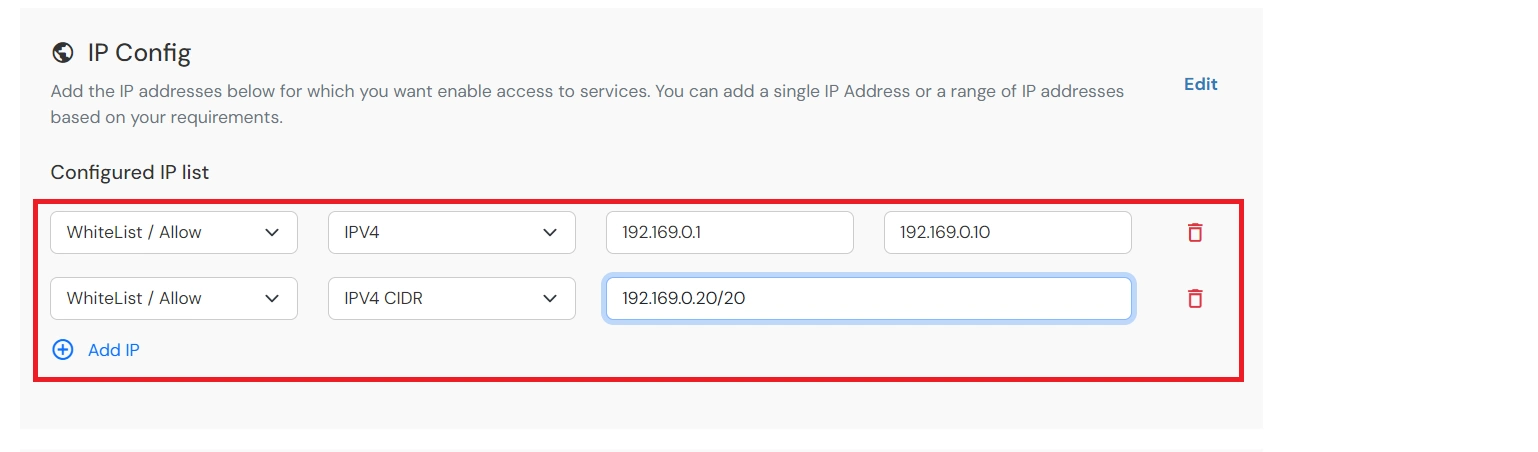
- Click on Edit in the IP Config section to configure the custom IP range. You
can add more
than one IP Address ranges by clicking on the Add IP button.
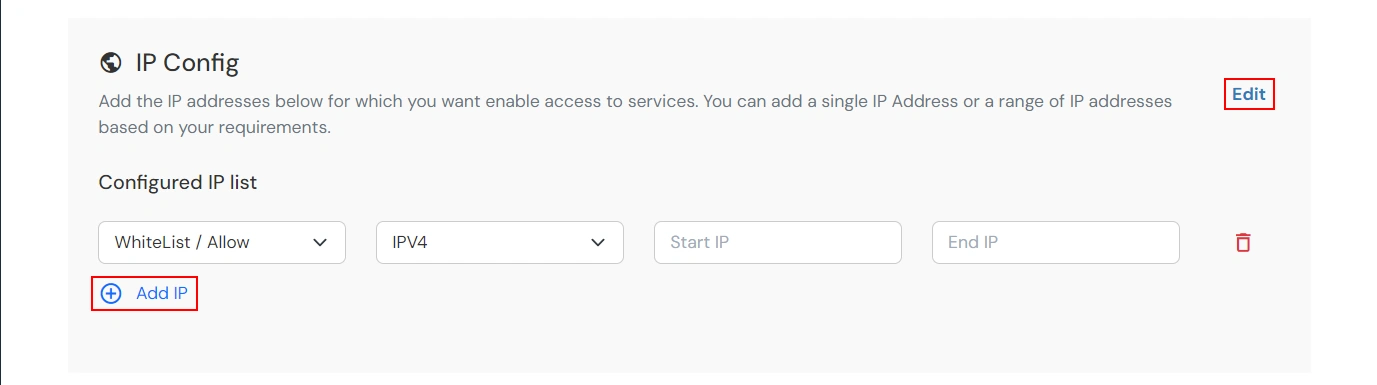
- We support IP addresses range in three formats i.e. IPv4, IPv4 CIDR and IPv6 CIDR.
You can choose
whichever is suitable for you from the dropdown menu.
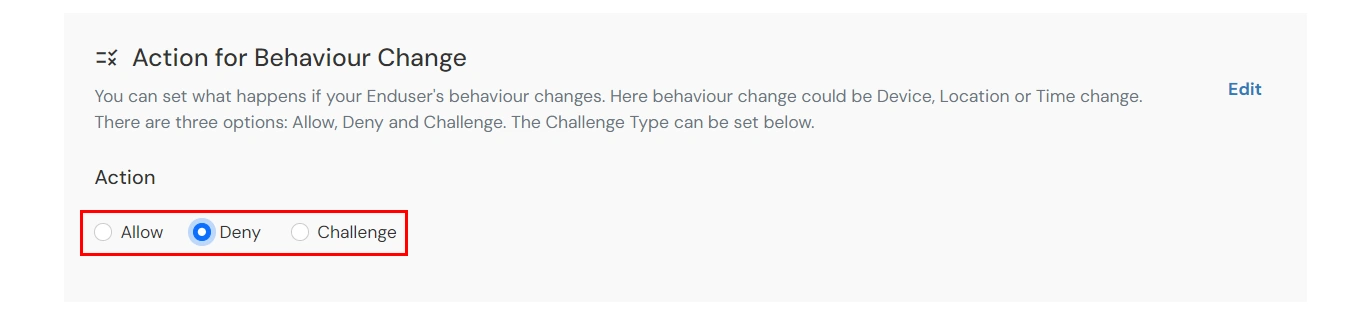
- Now, scroll down to the Action For Behaviour Change section and click on Edit.
Select the
action you want to perform if the IP address is out of the range. i.e. Allow, Challenge
or Deny.
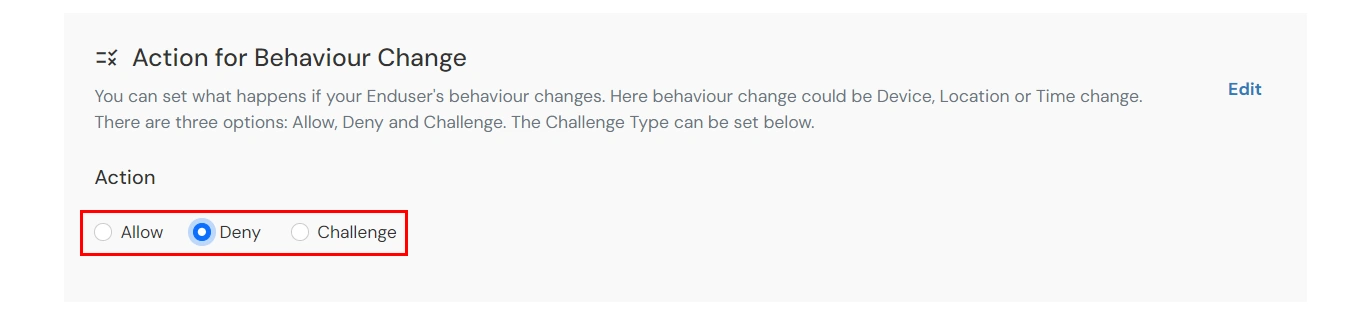
Action for behavior Change Options :
| Attribute |
Description |
| Allow |
Allow user to authenticate and use services if Adaptive authentication condition
is true. |
| Challenge |
Challenge users with one of the three methods mentioned below for verifying user
authenticity.
|
| Deny |
Deny user authentications and access to services if Adaptive authentication
condition is true.
|
Challenge Type Options :
| Attribute |
Description |
| User second Factor |
The User needs to authenticate using the second factor he has opted or assigned
for such as- OTP
over SMS
- PUSH Notification
- OTP over Email
- And 12 more methods.
|
| KBA (Knowledge-based authentication) |
The System will ask user for 2 of 3 questions he has configured in his Self
Service Console. Only
after right answer to both questions user is allowed to proceed further. |
| OTP over Alternate Email |
User will receive a OTP on the alternate email he has configured threw Self
Service Console. Once
user provides the correct OTP he is allowed to proceed further. |
- Scroll to the end and click on save.
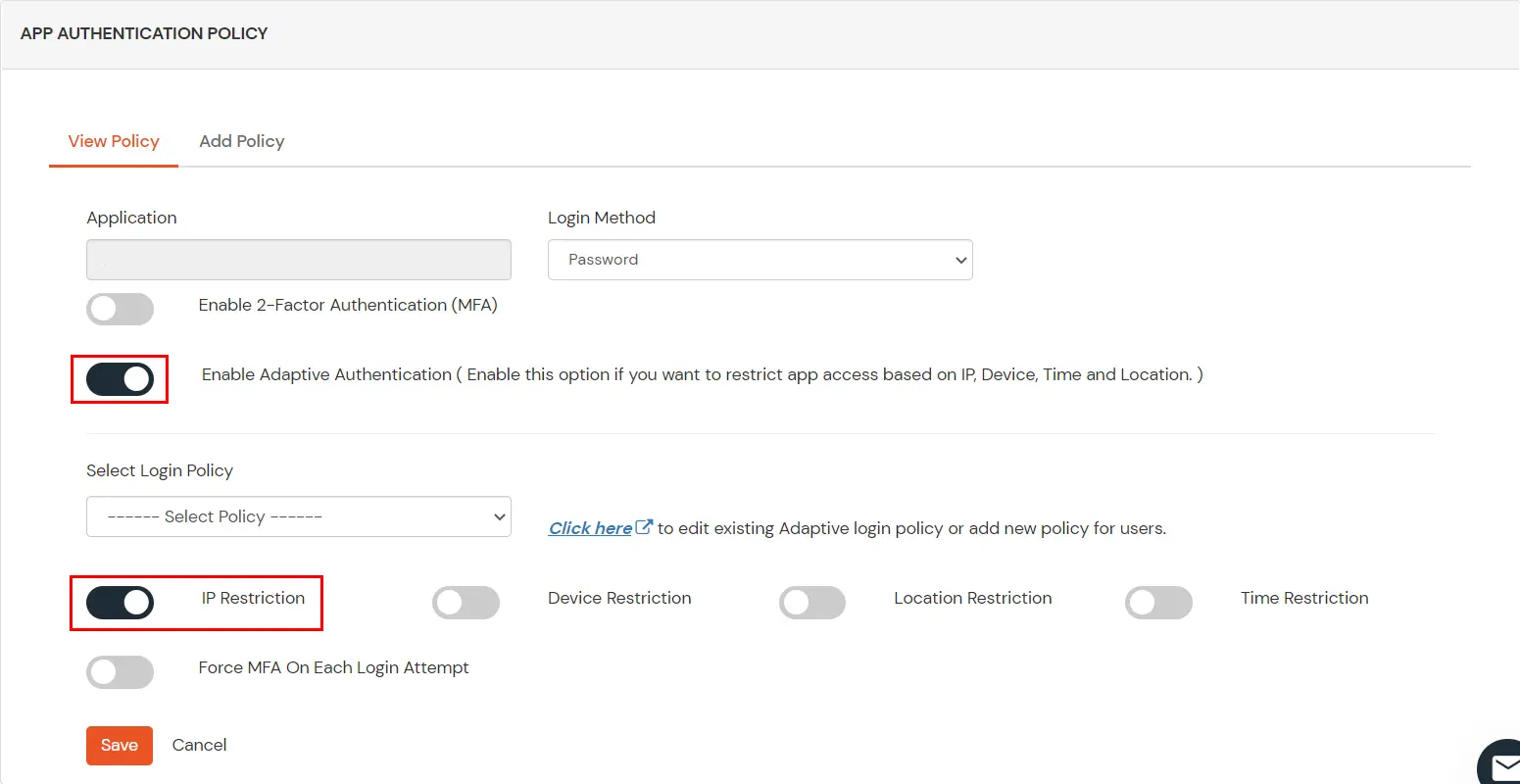
5. Enable
Restriction for Office 365
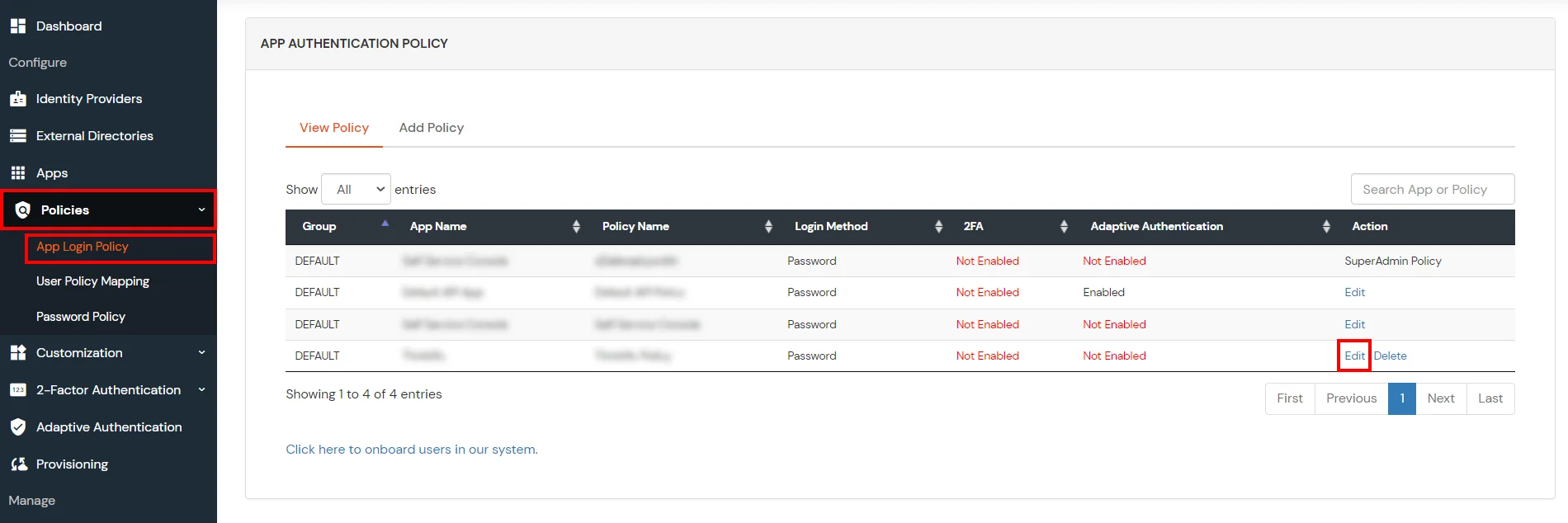
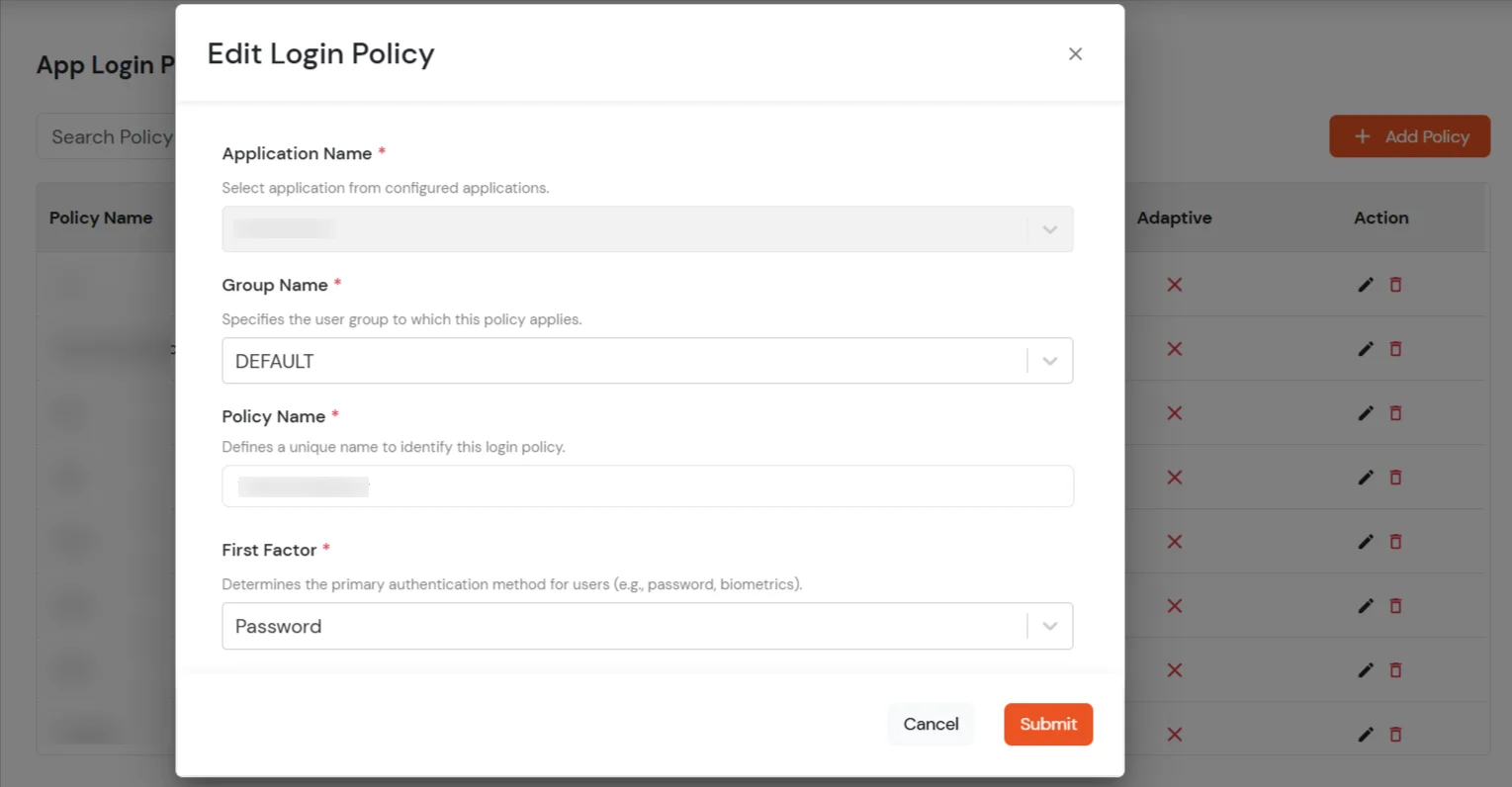
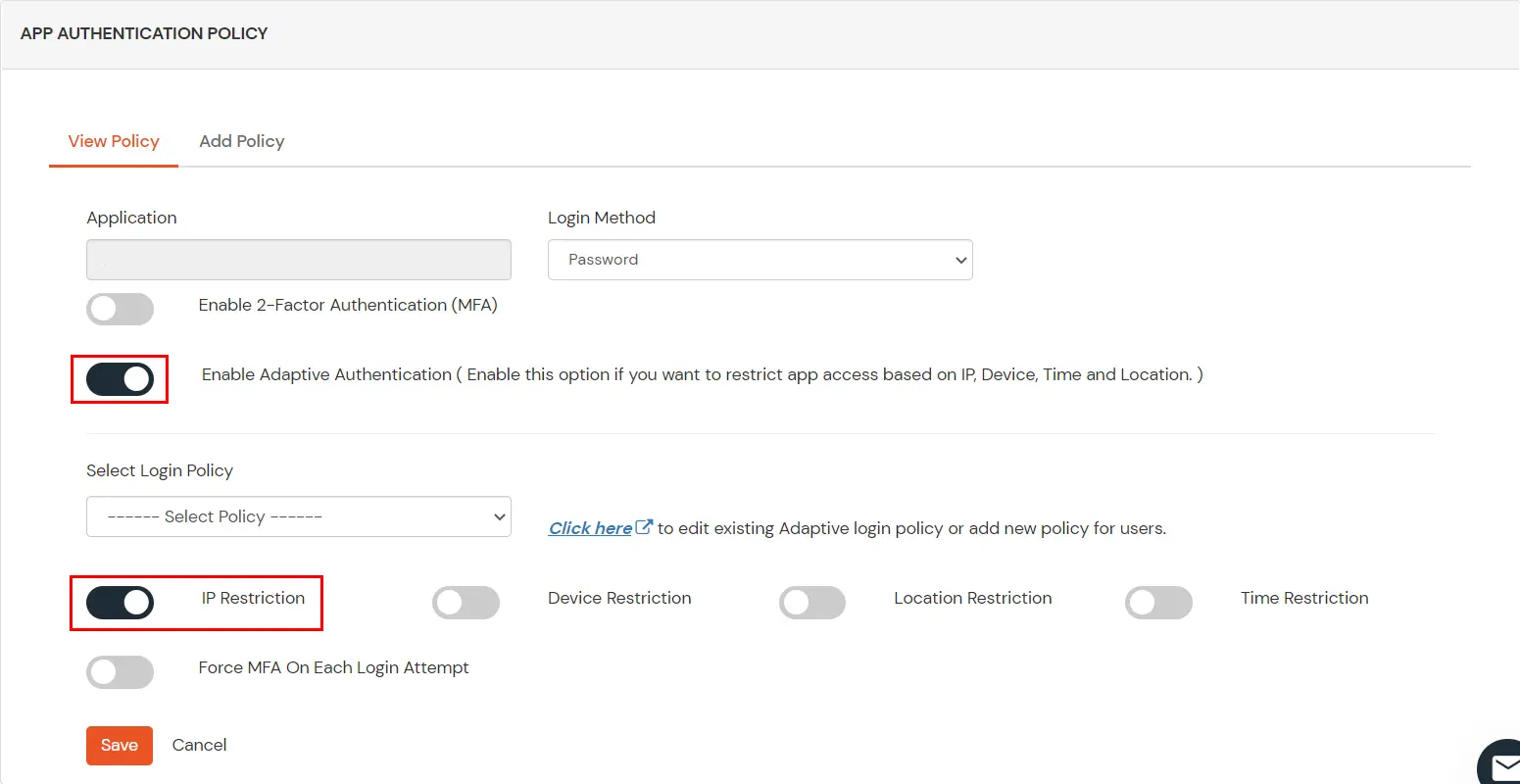
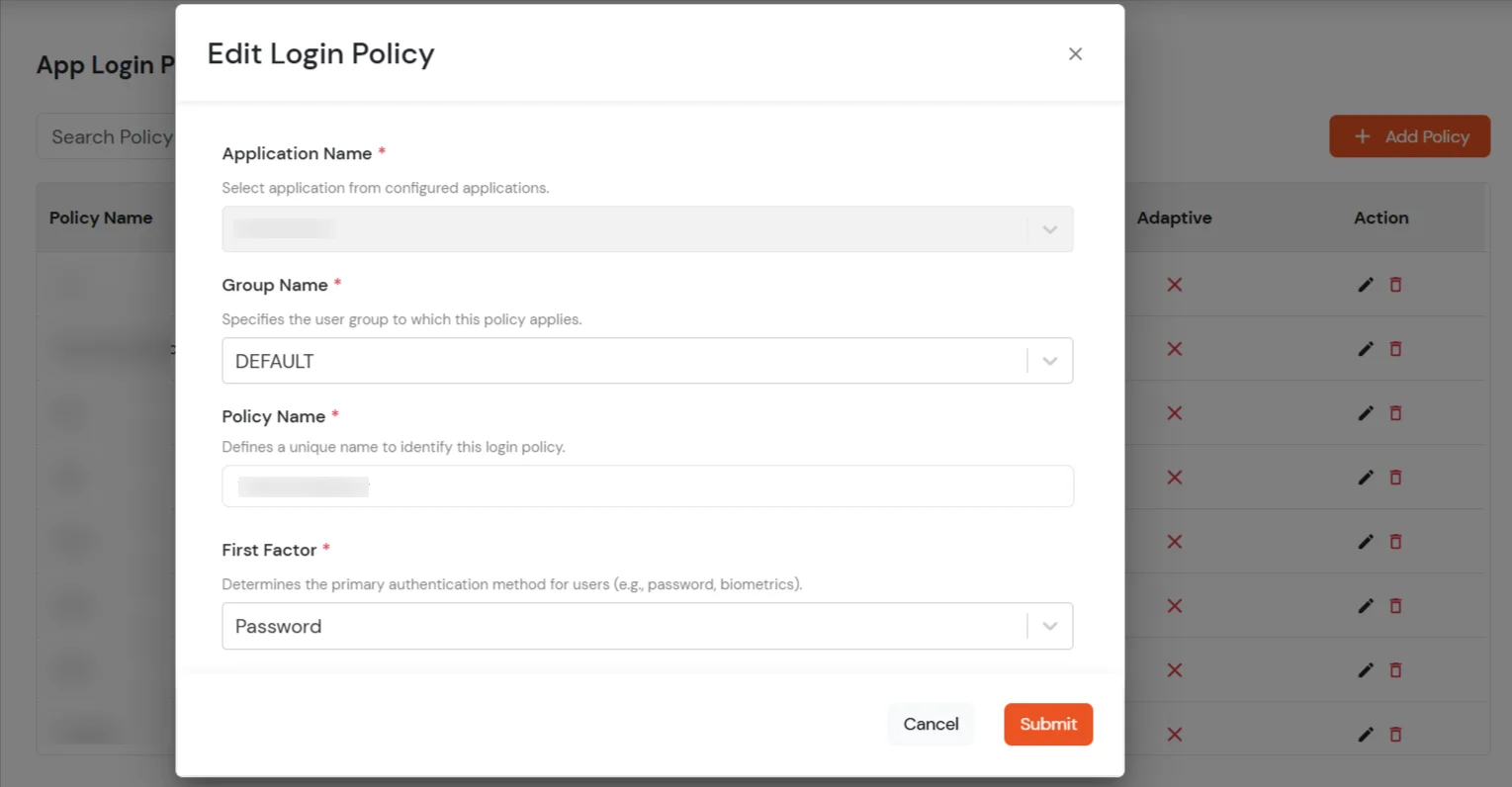
- Go to Policies >> App Login Policy from the left navigation bar.
- Click on edit Icon option against your selected app.
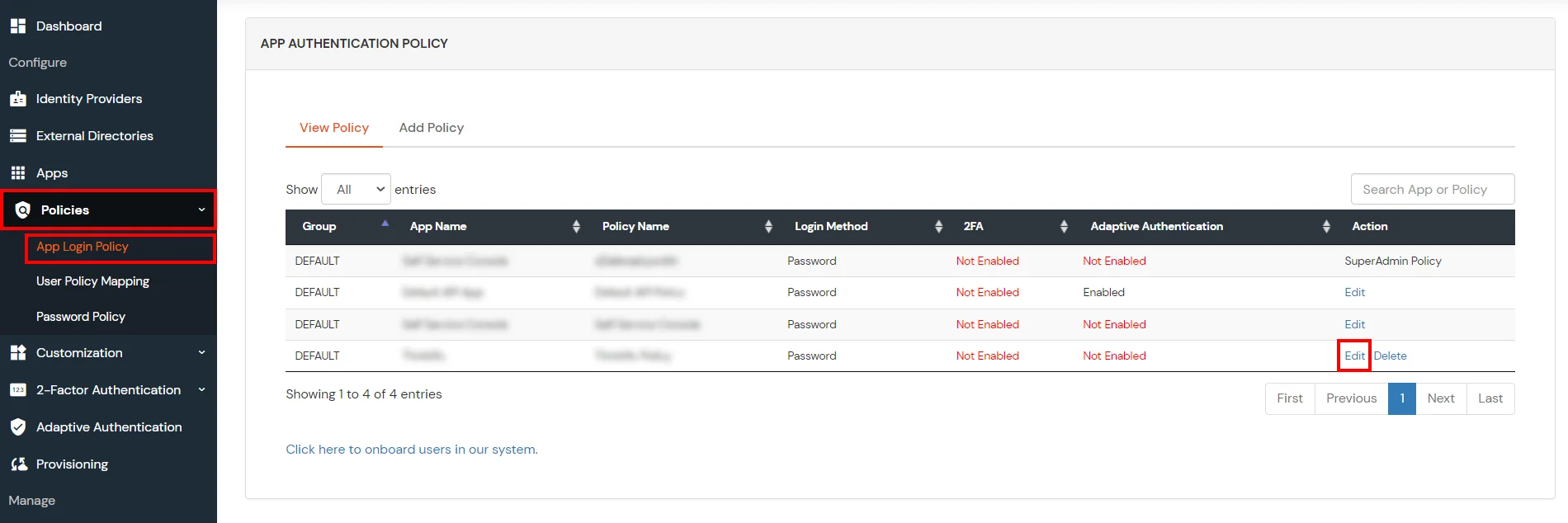
- Set your application name in the Application and select Password as First Factor.
- Scroll down to enable Adaptive Authentication.
- From the Select Login Policy dropdown, select the policy we created in the last step
and select
the required restriction method as an option.
- Click Submit.
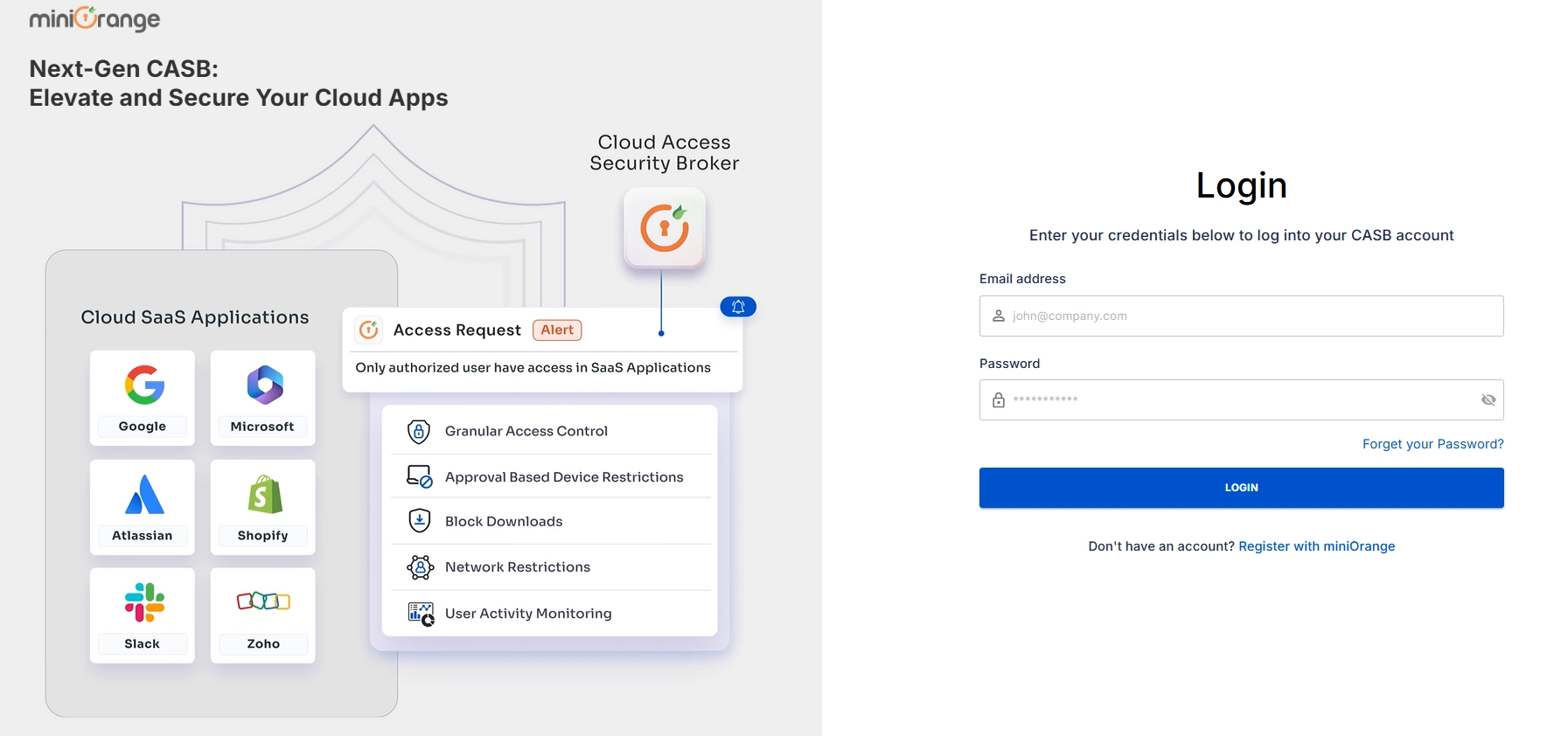
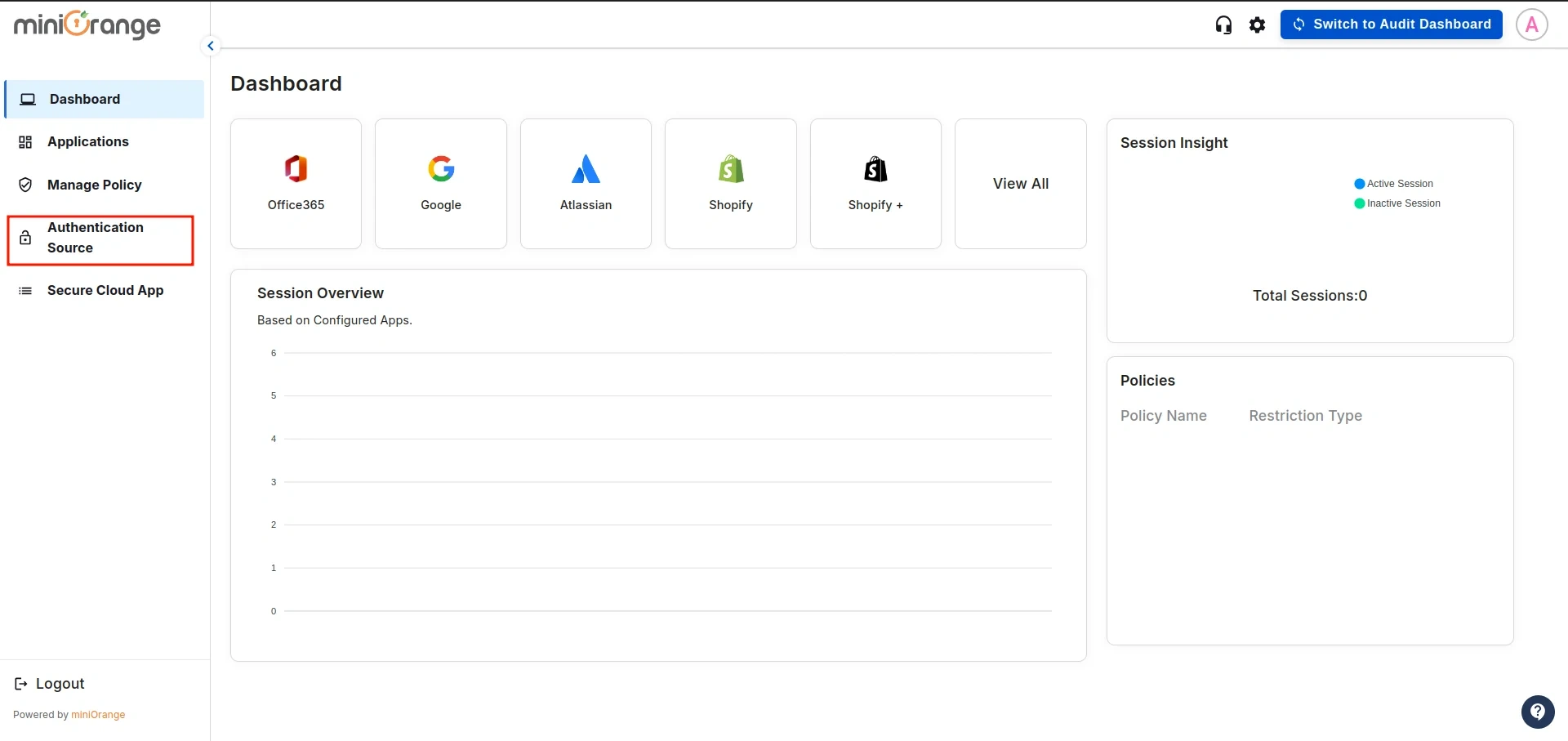
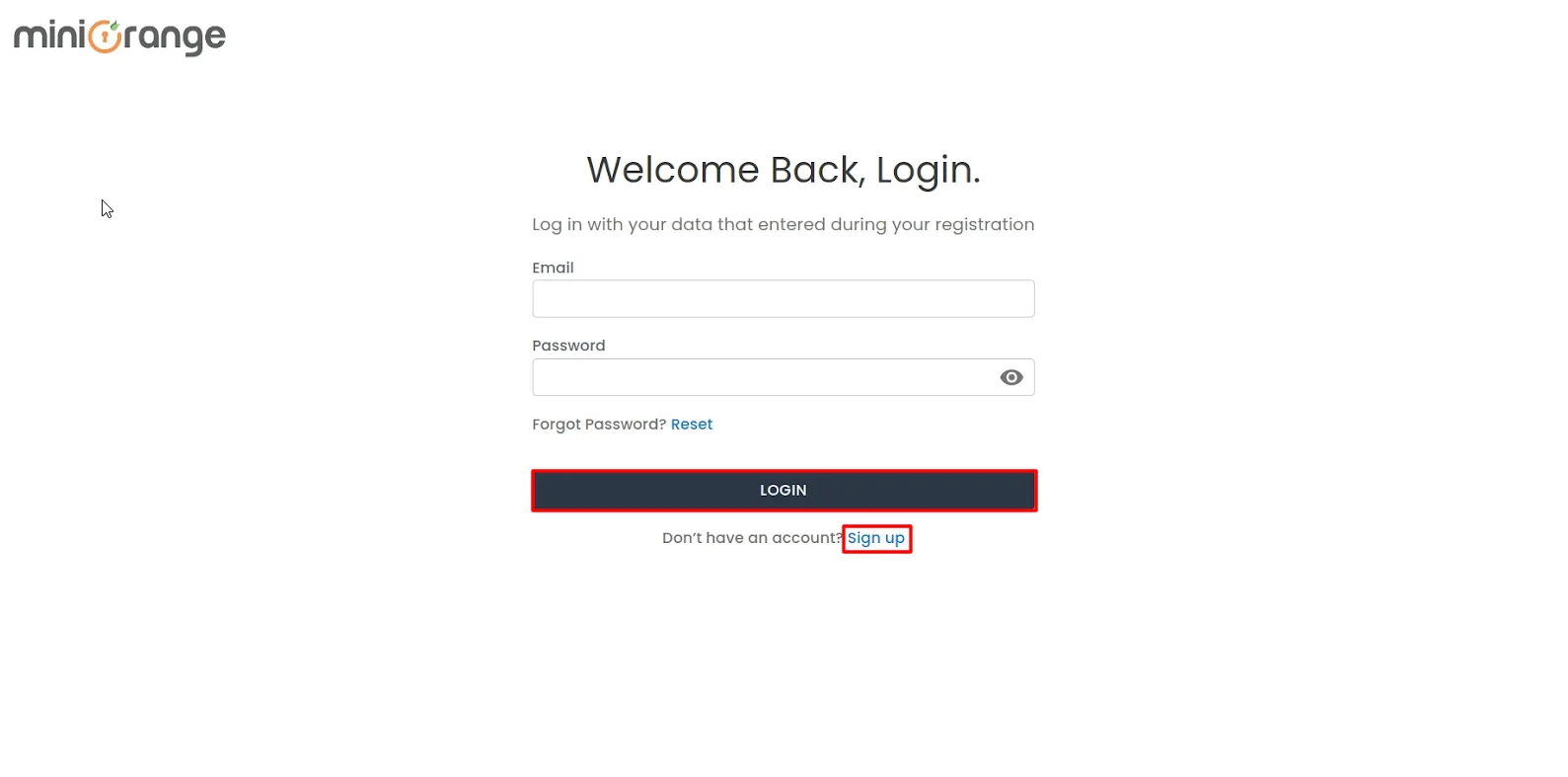
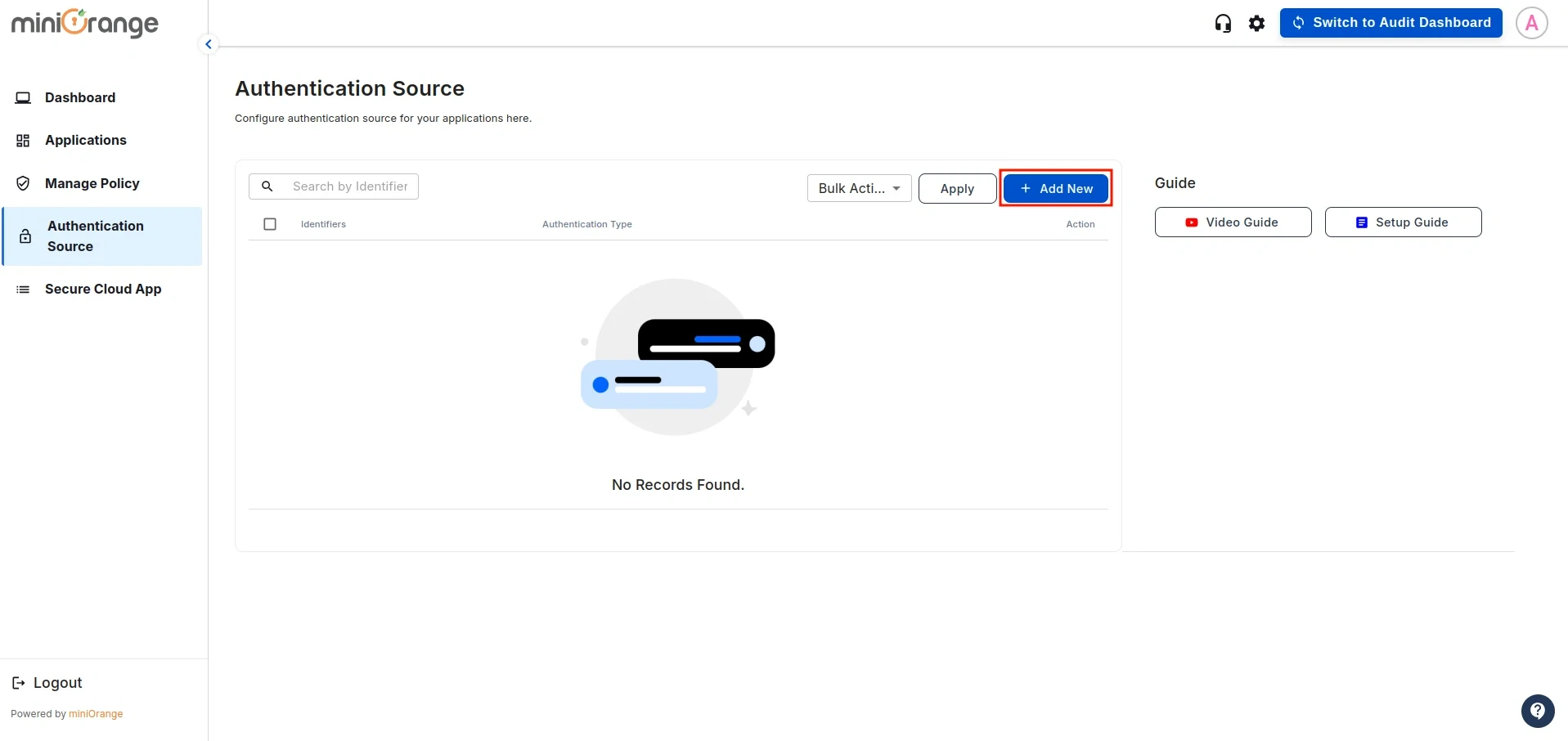
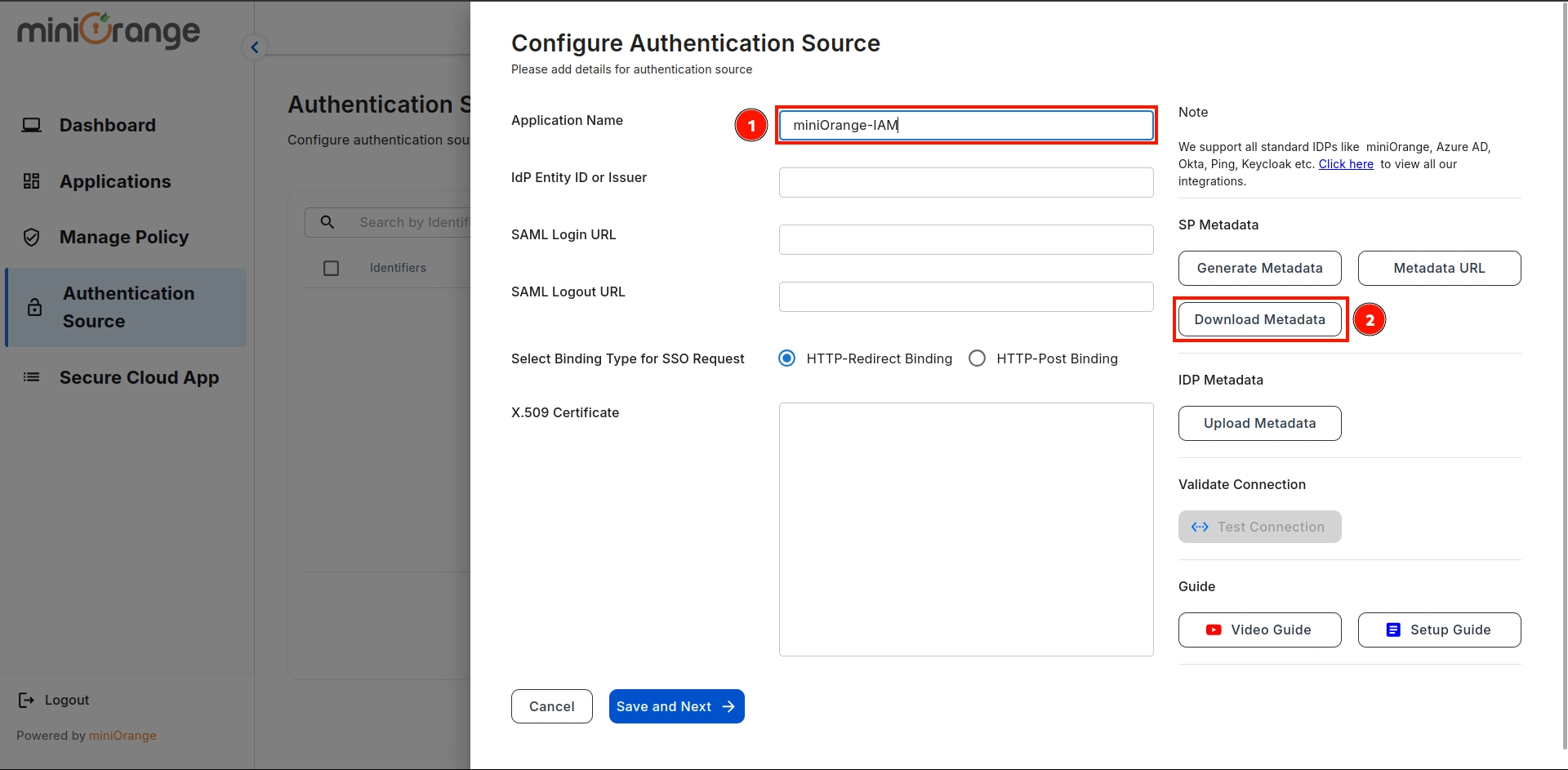
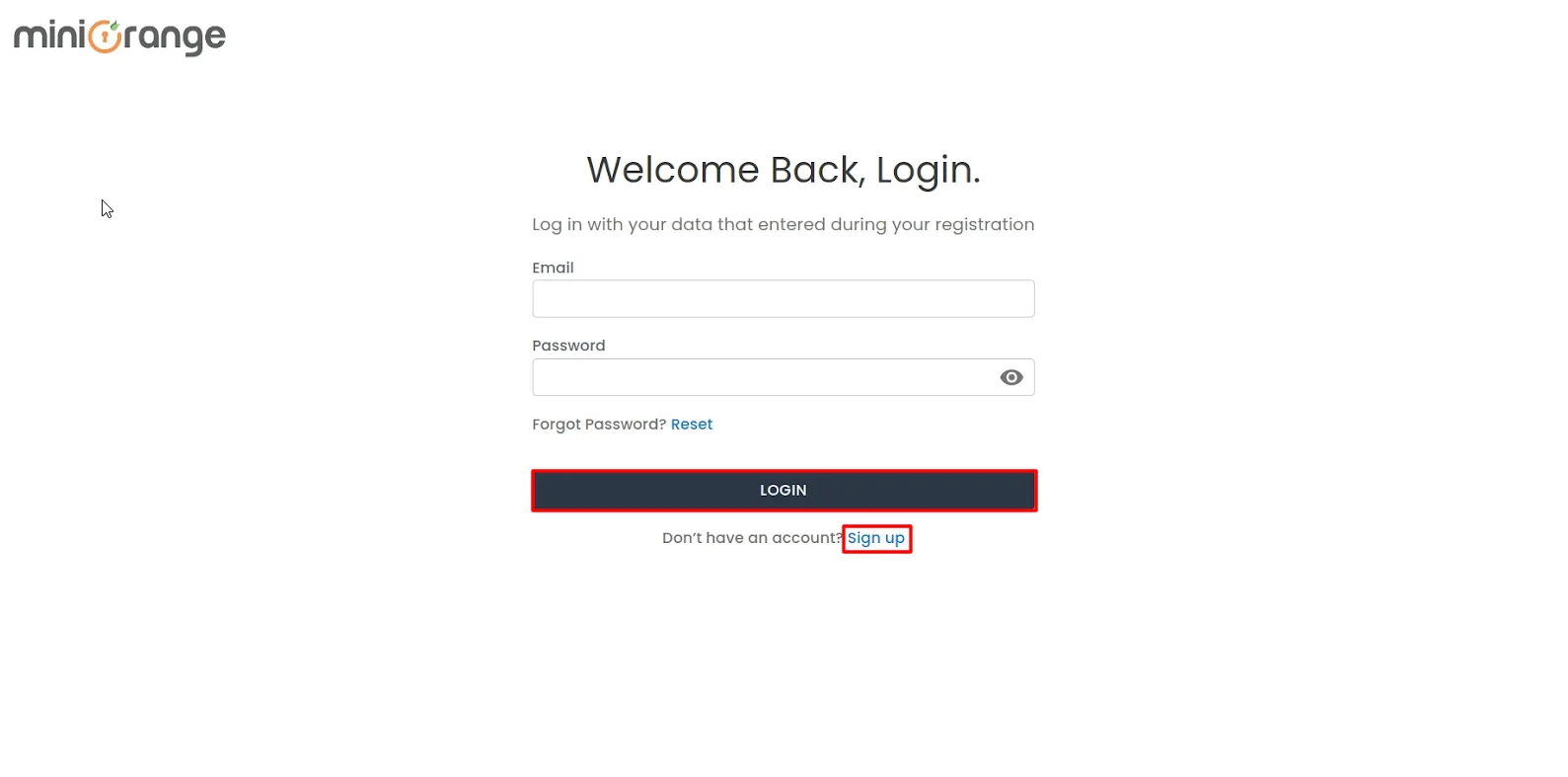
2. Configure authentication source in CASB
- Sign in to the Cloud Access Security Broker (CASB) with your email and
password. (Don't have an account? No worries, click here to create a new
account)
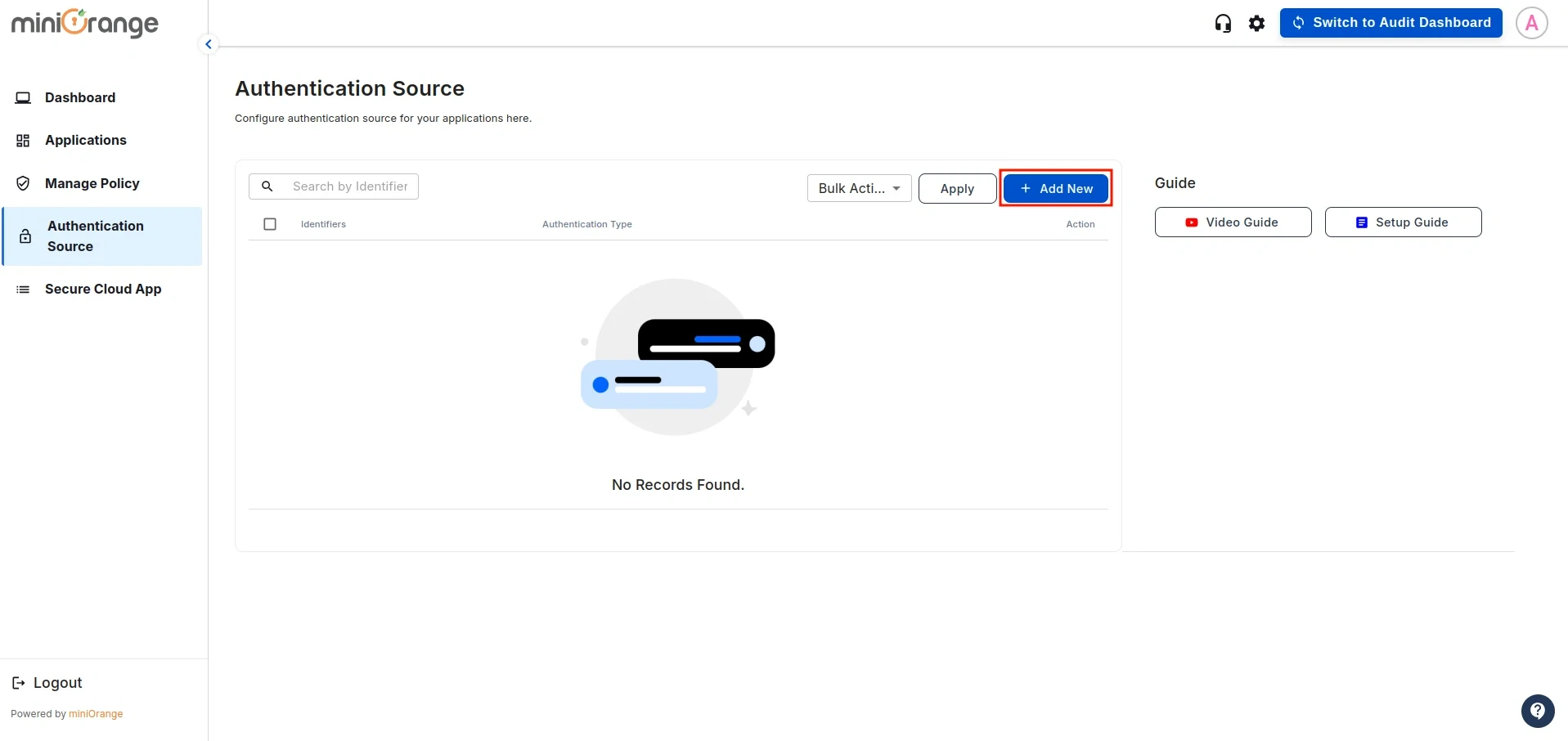
- After signing in, navigate to the Authentication Source in the left sidebar.
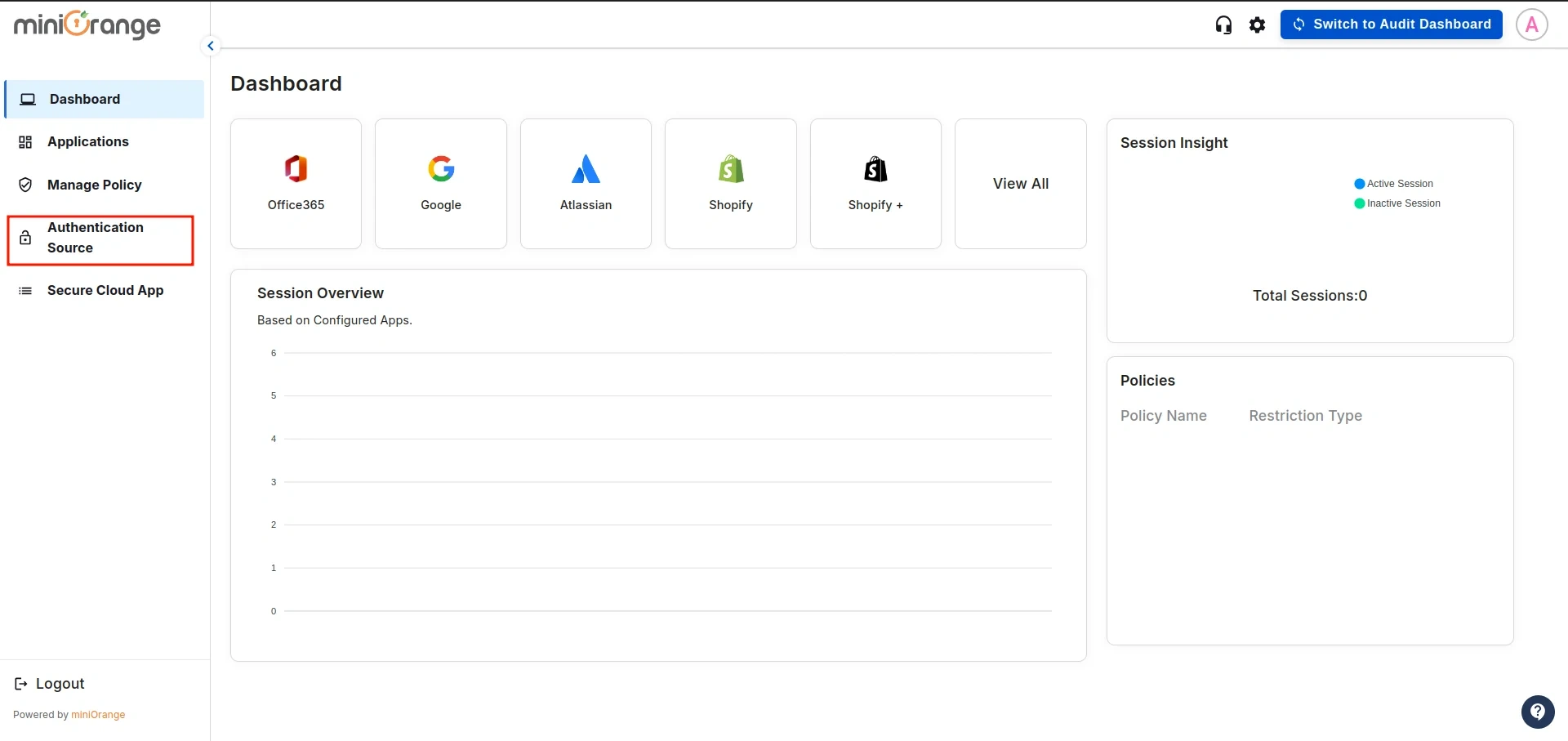
- You will see the list of all existing authentication sources configured in the CASB dashboard.
Click on Add New to create a new one.
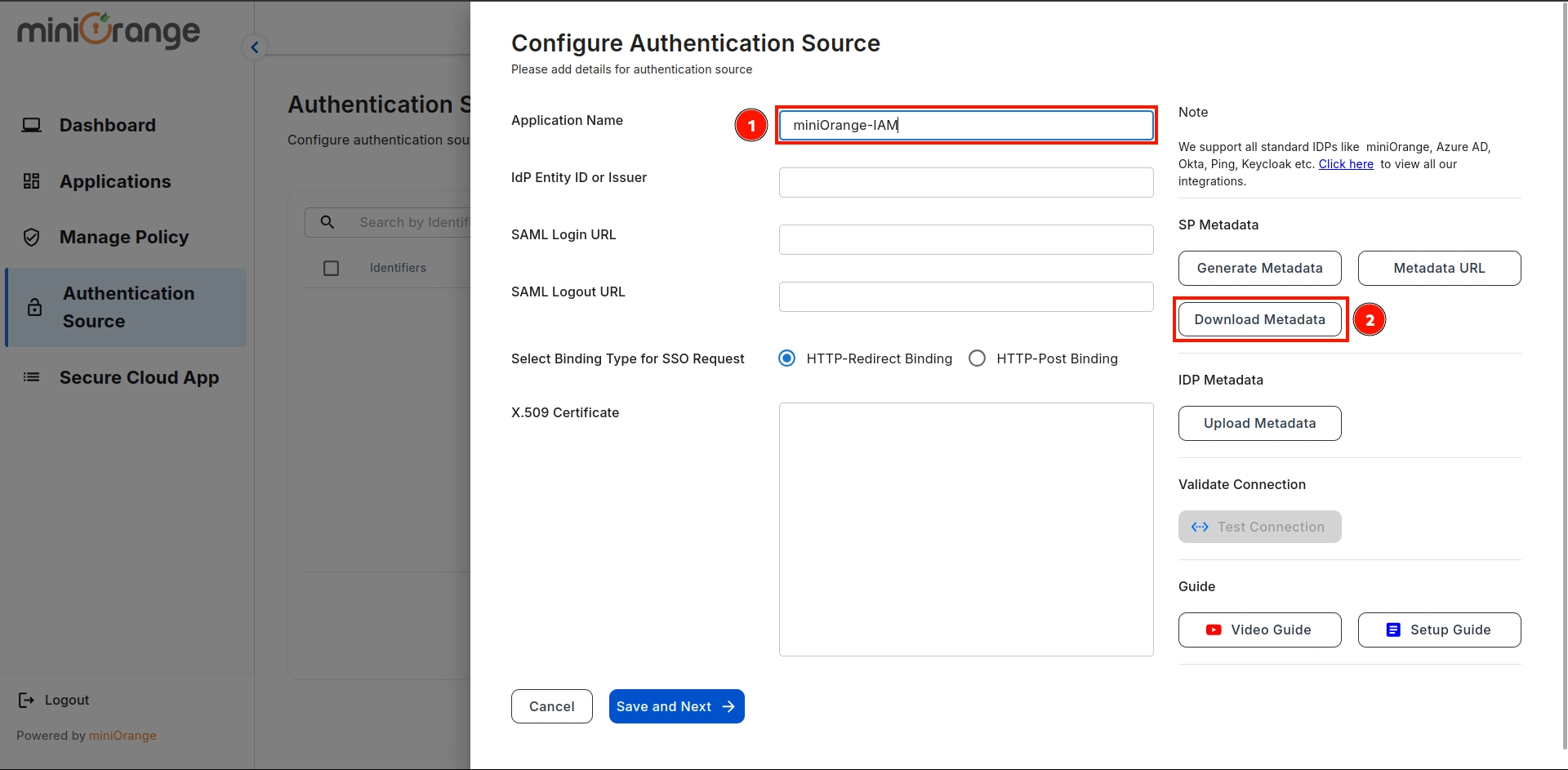
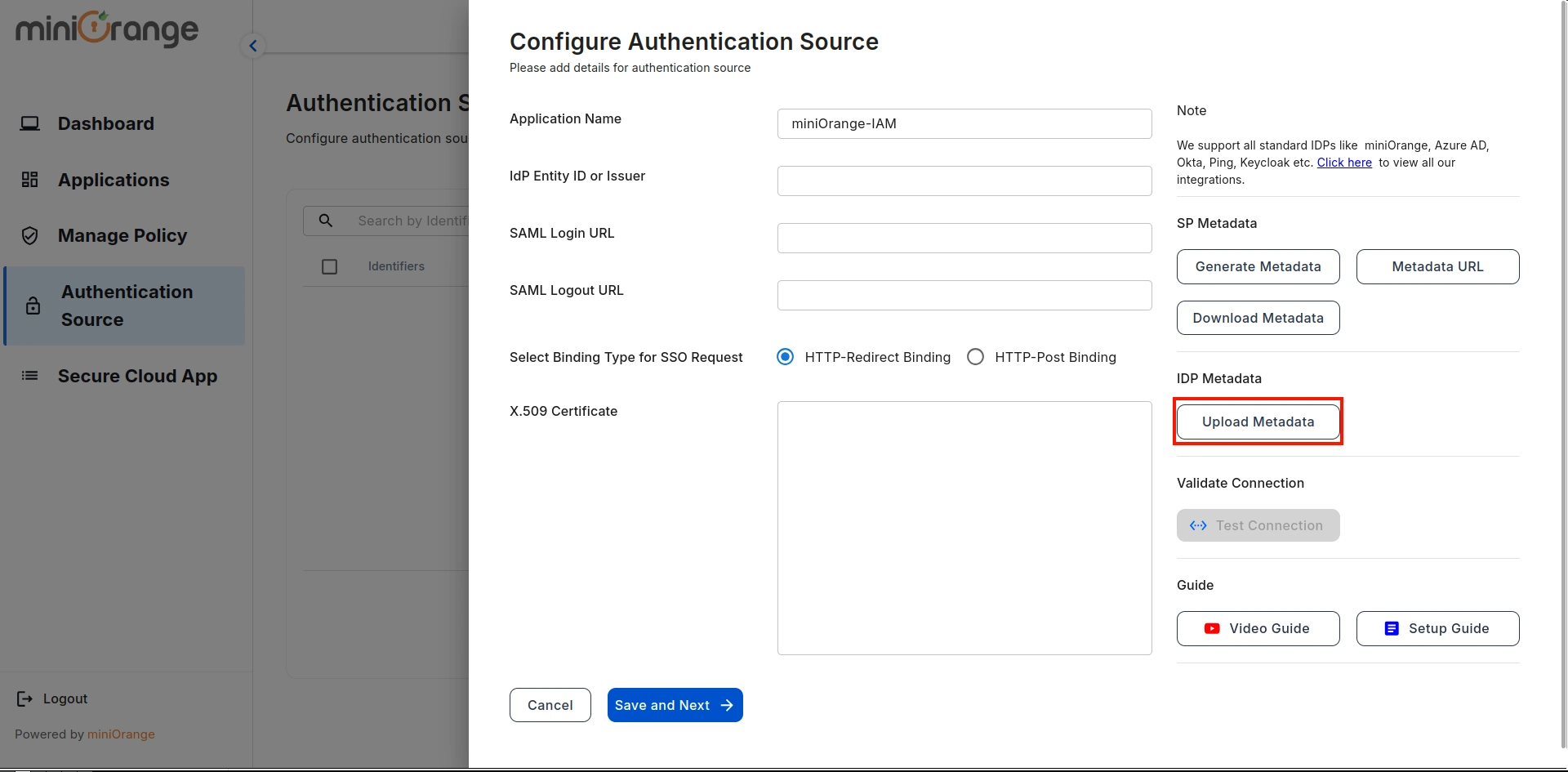
- This will open the configuration screen for the Authentication Source. Enter
the Authentication Source Name and click Download Metadata.
3. Configure Microsoft Office 365 as a Identity Provider
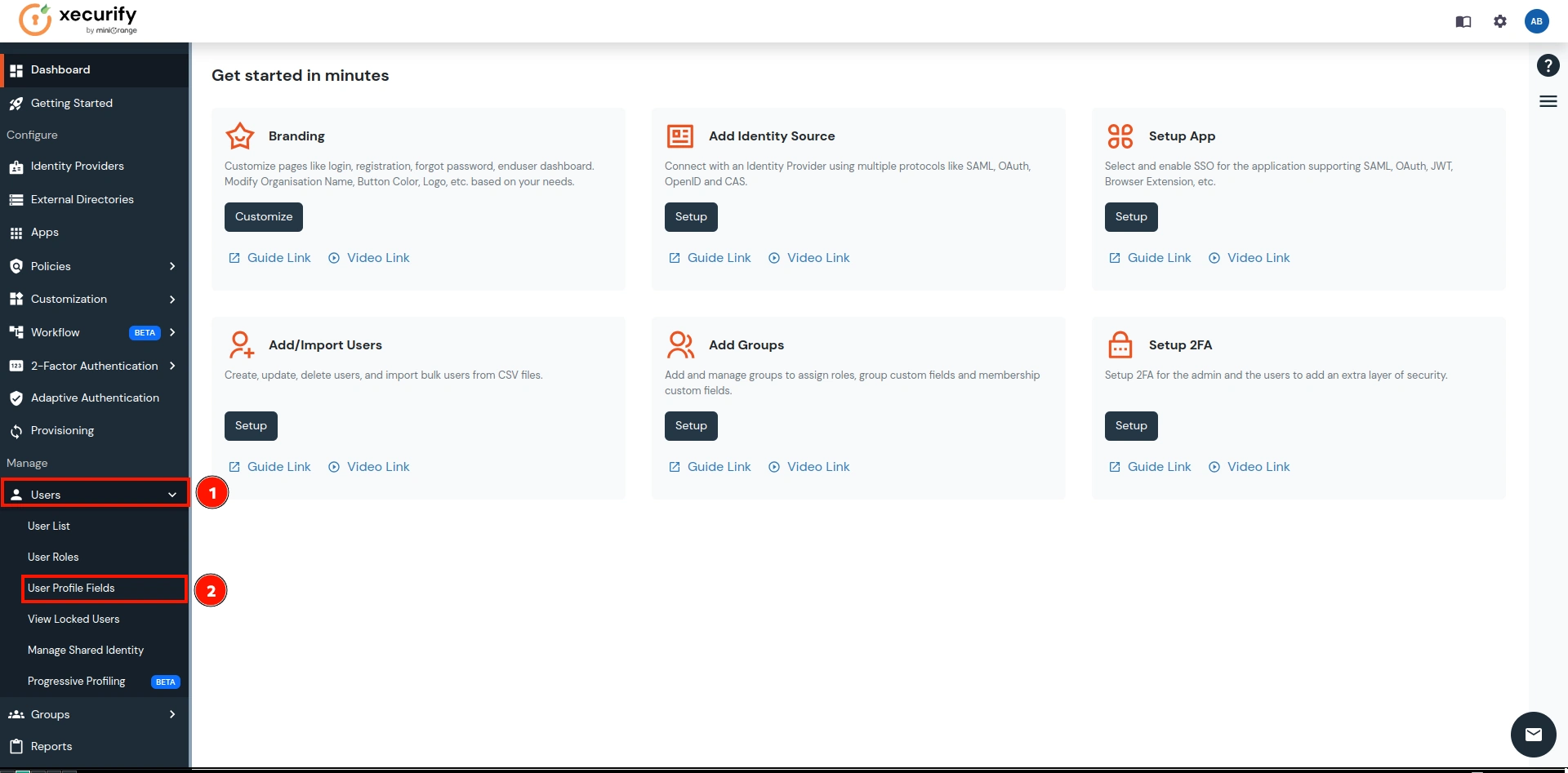
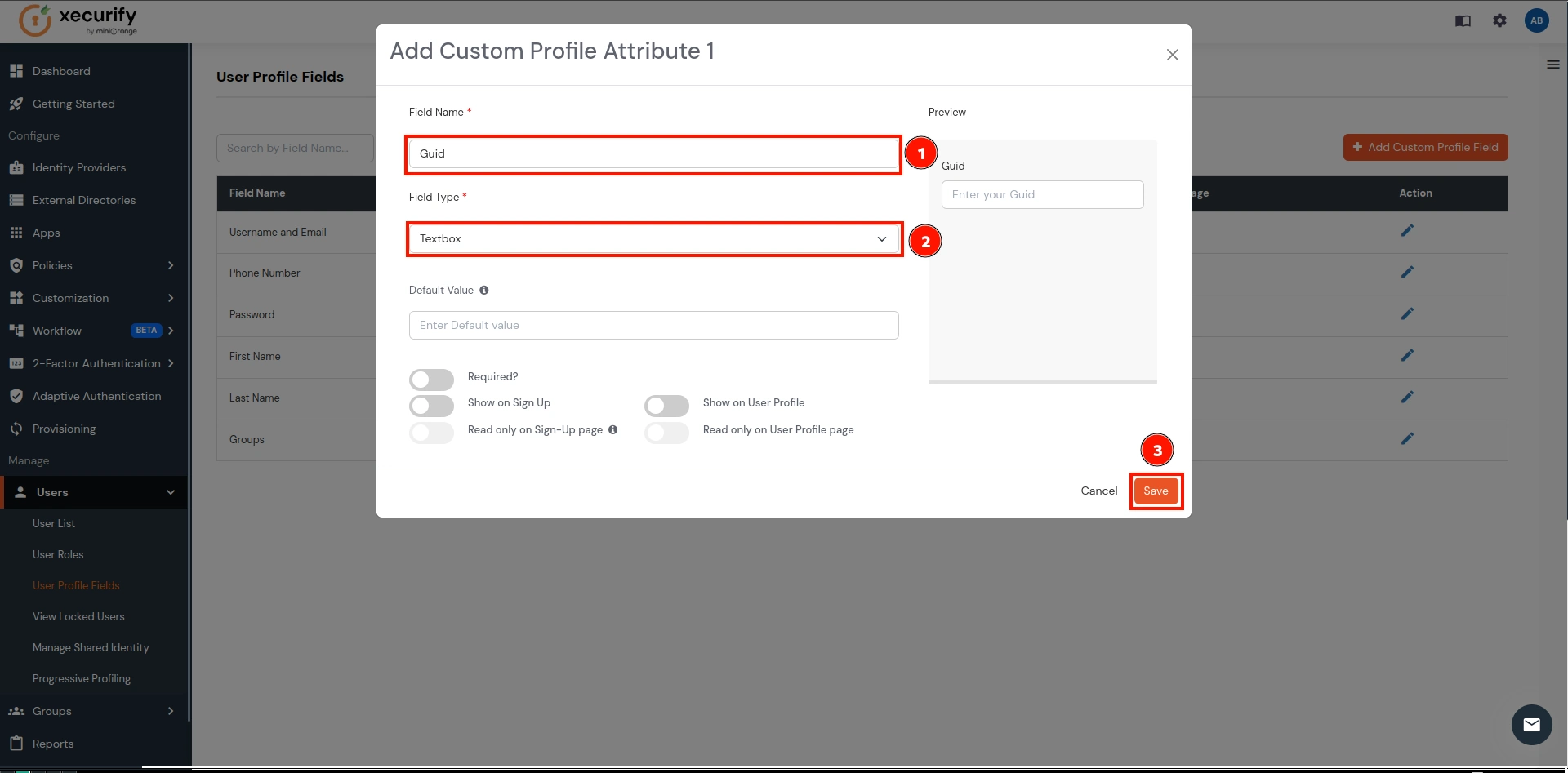
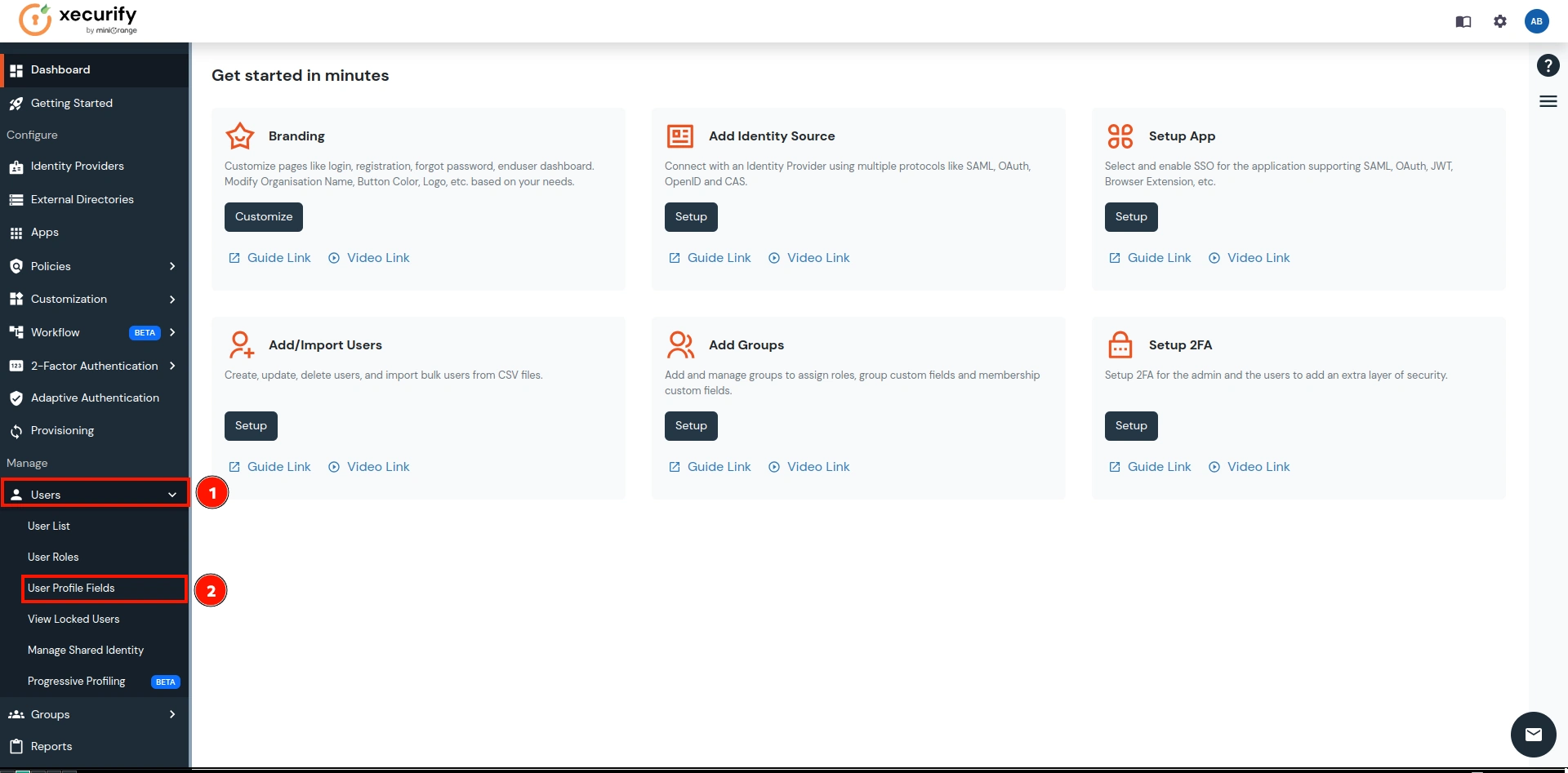
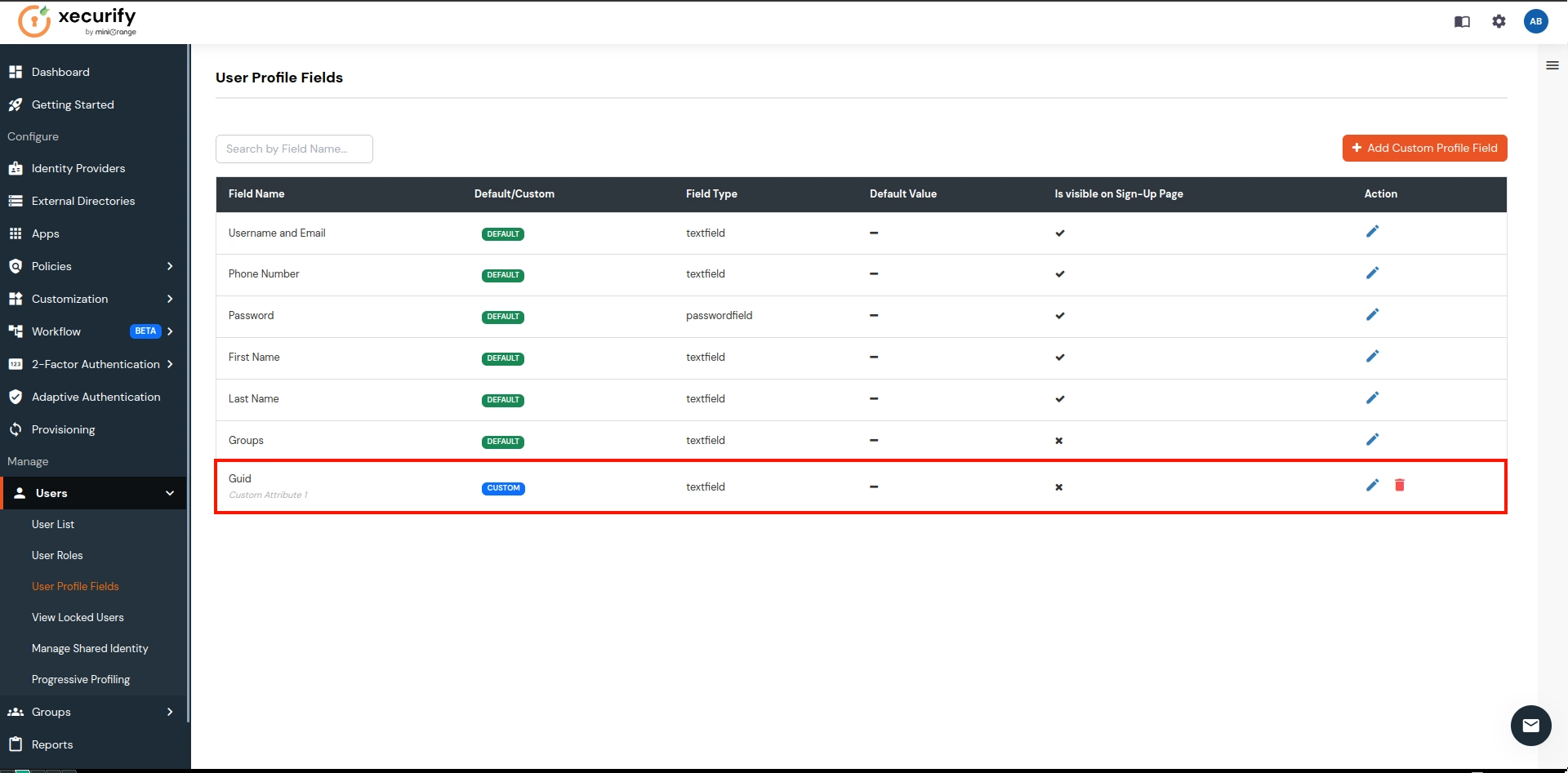
- Go to miniOrange IDP and click on the User Profile Fields as shown below in the image and click on it.
(In this guide, we are using miniOrange as the IDP, but you can contact us at
proxysupport@xecurify.com
to set up your preferred IDP.)
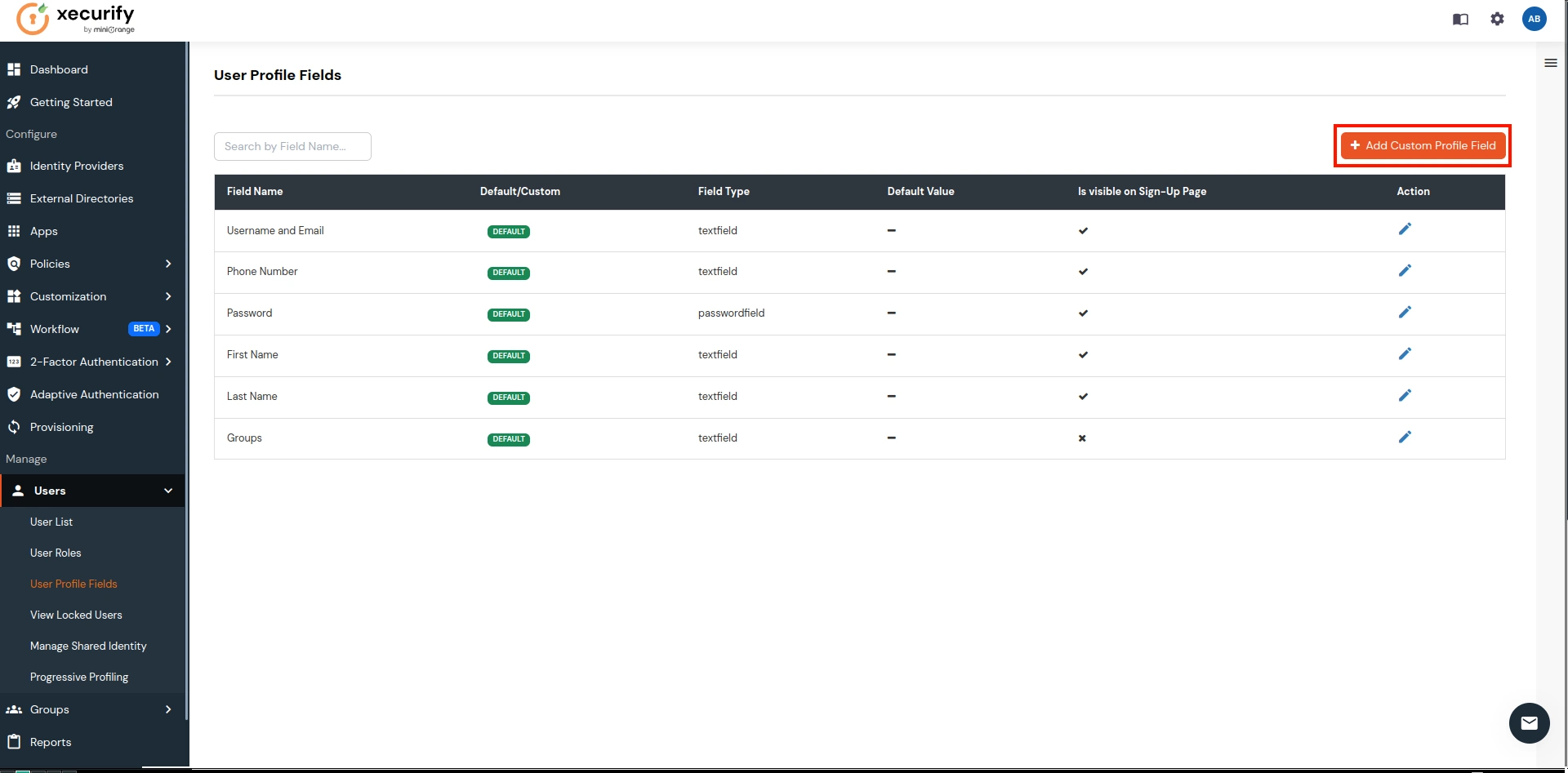
- Click on the Add Custom Profile Attribute button.
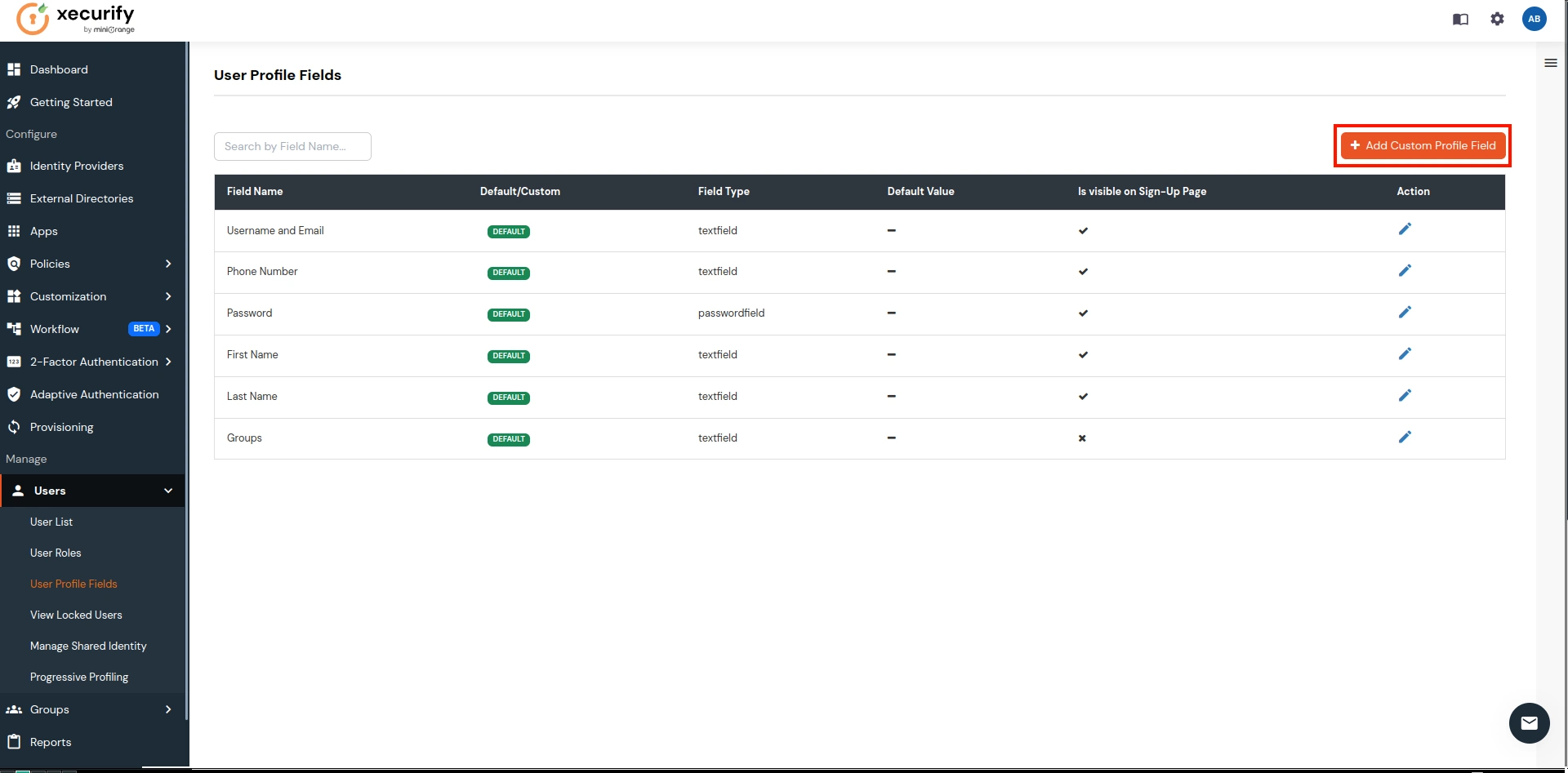
- Enter Field Name as Guid and Field Type as Textbox (select from dropdown). Click on save button.
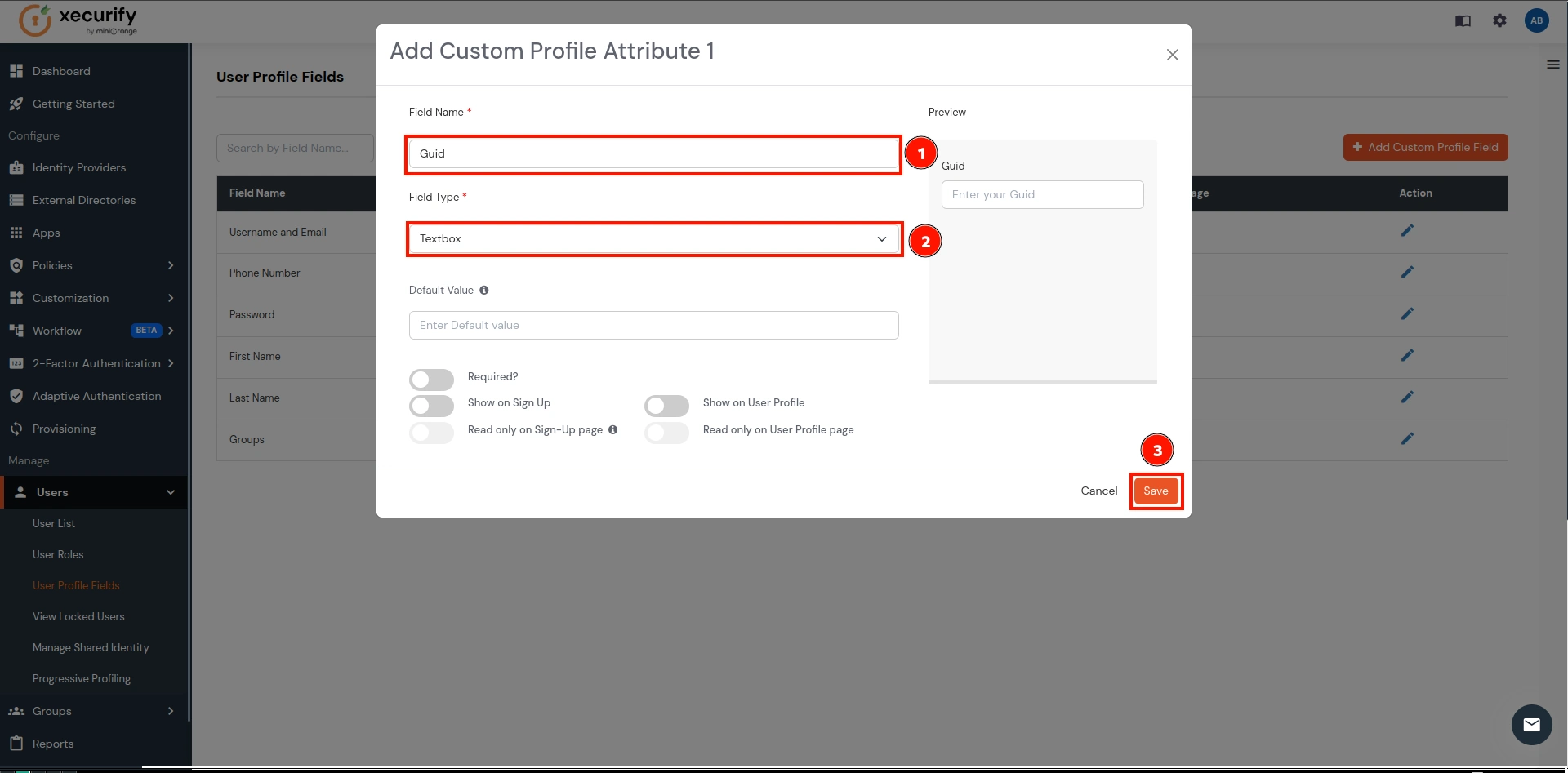
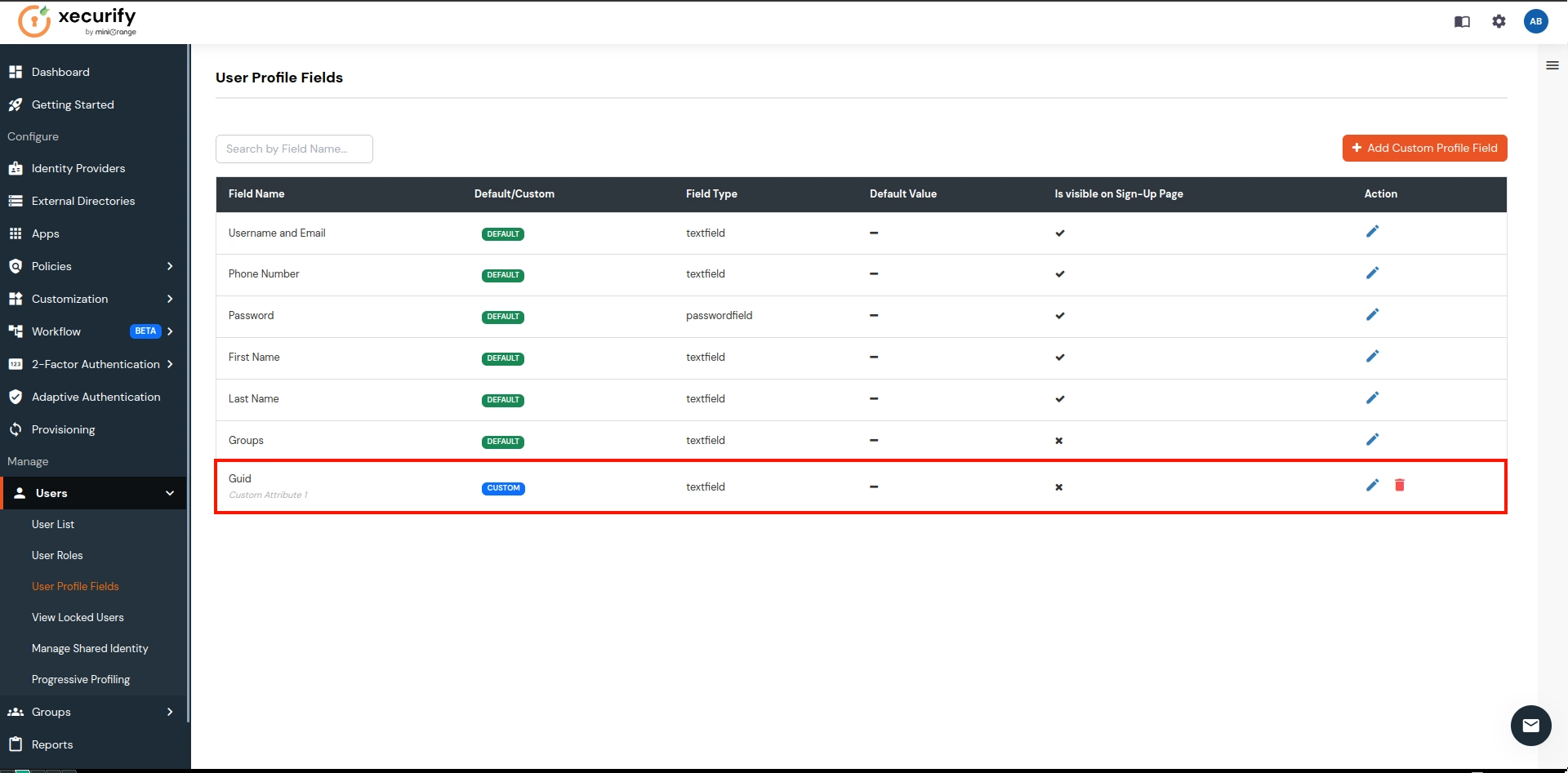
- This will create a custom attribute field as Guid as shown below in the image which will be used to sync the ImmutableID for the users.
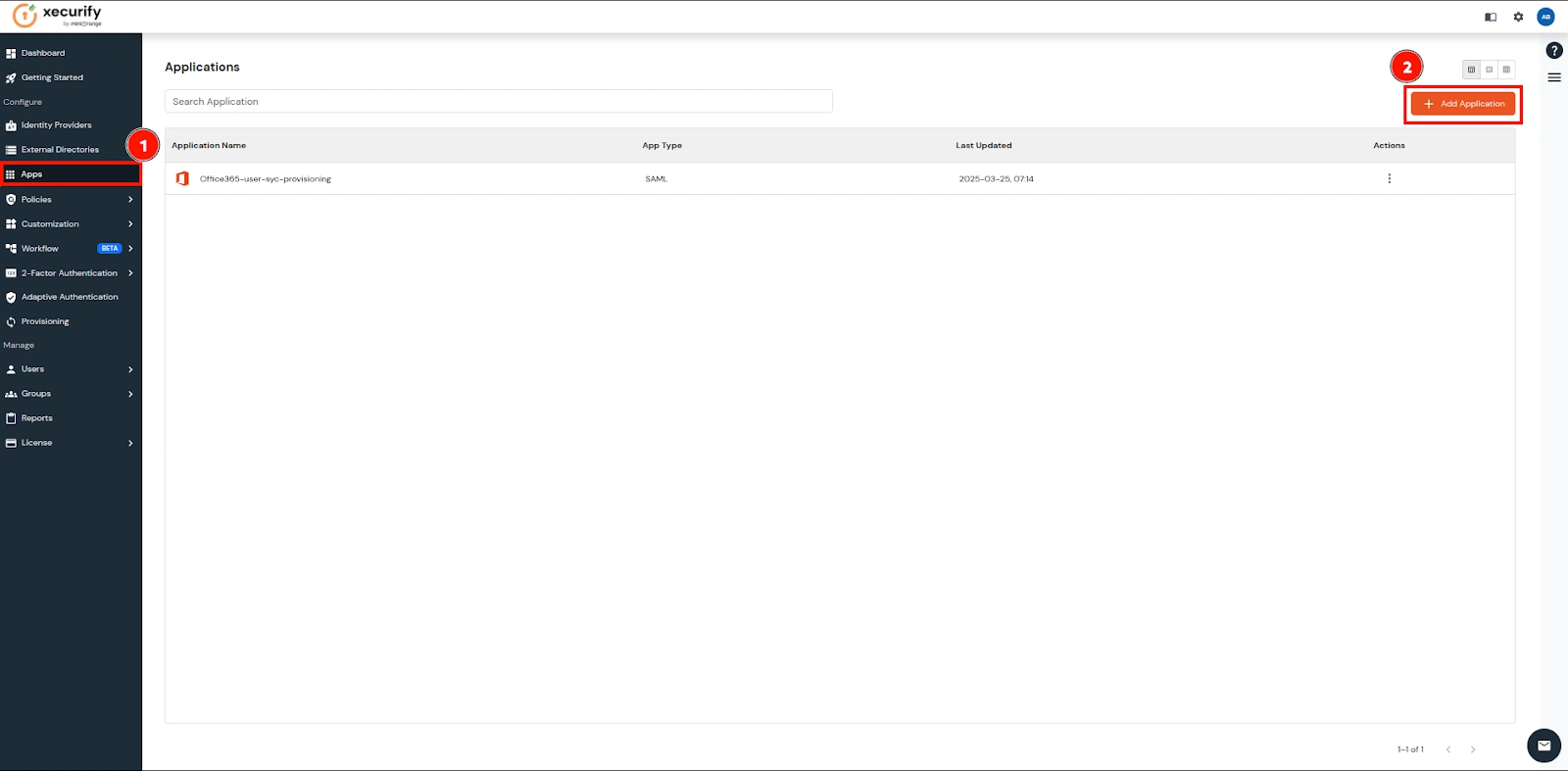
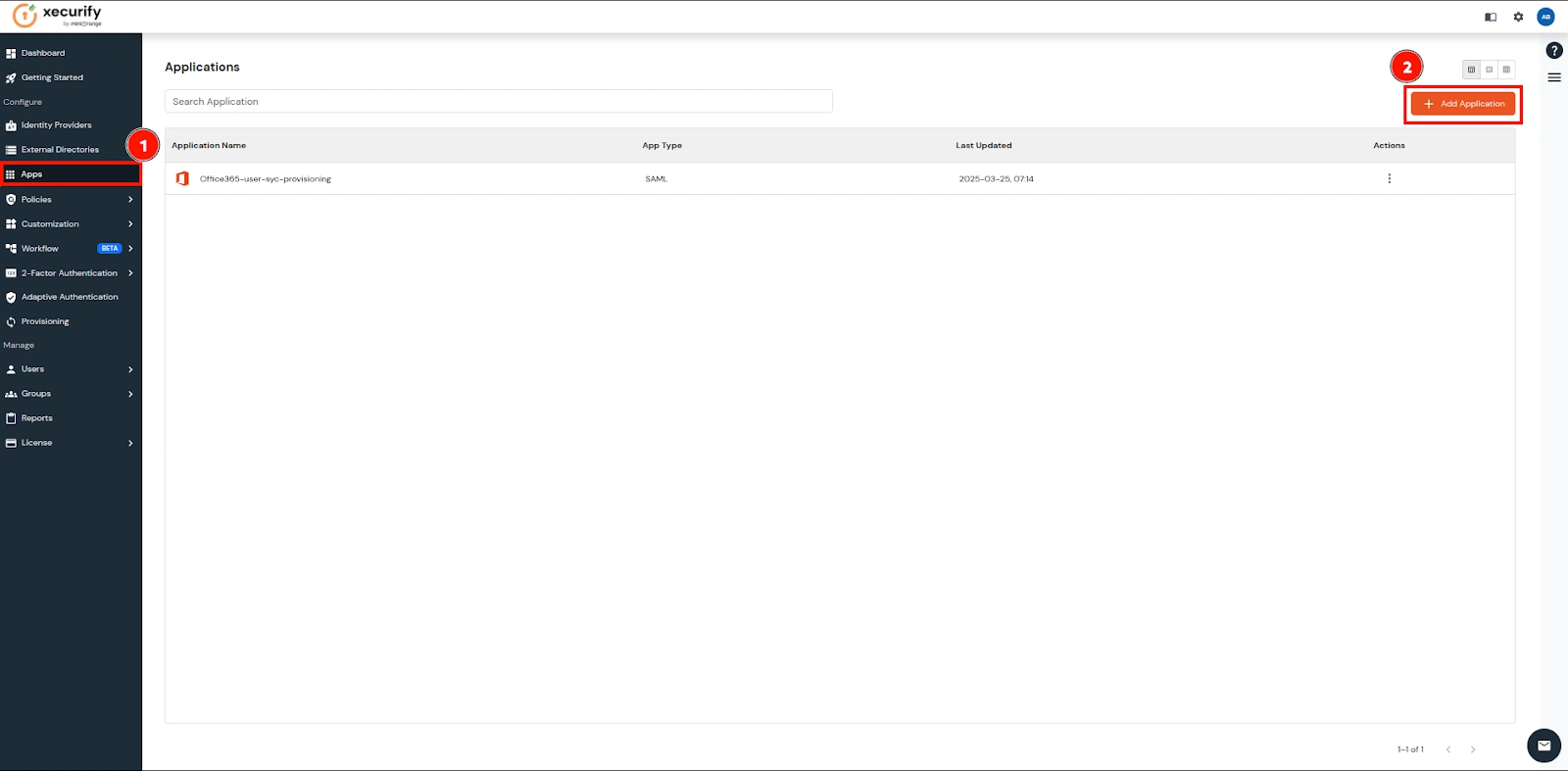
- Now navigate to the Apps and click on the Add Application button
.
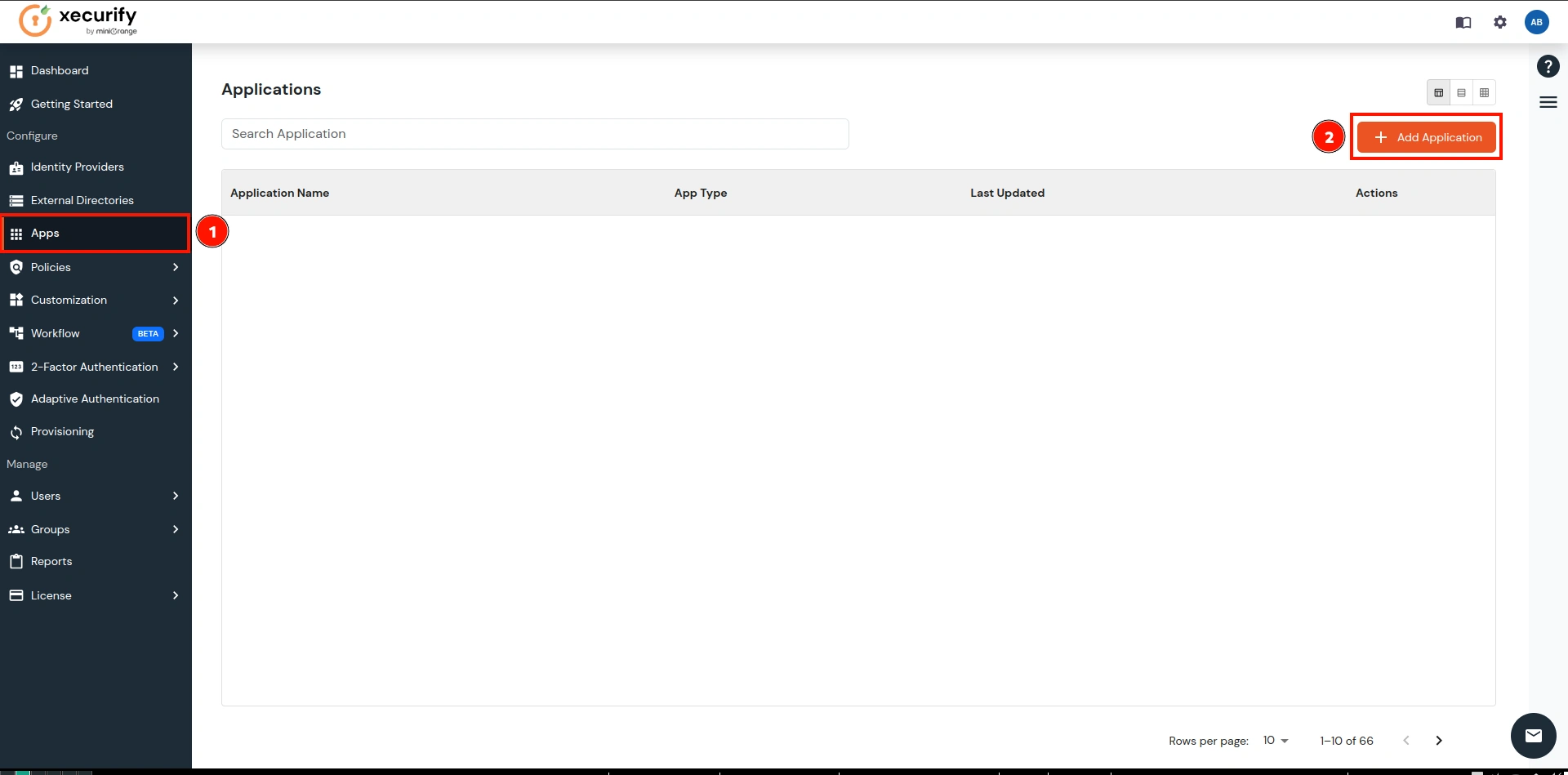
- Search for the Office 365 in the search box and click on it.
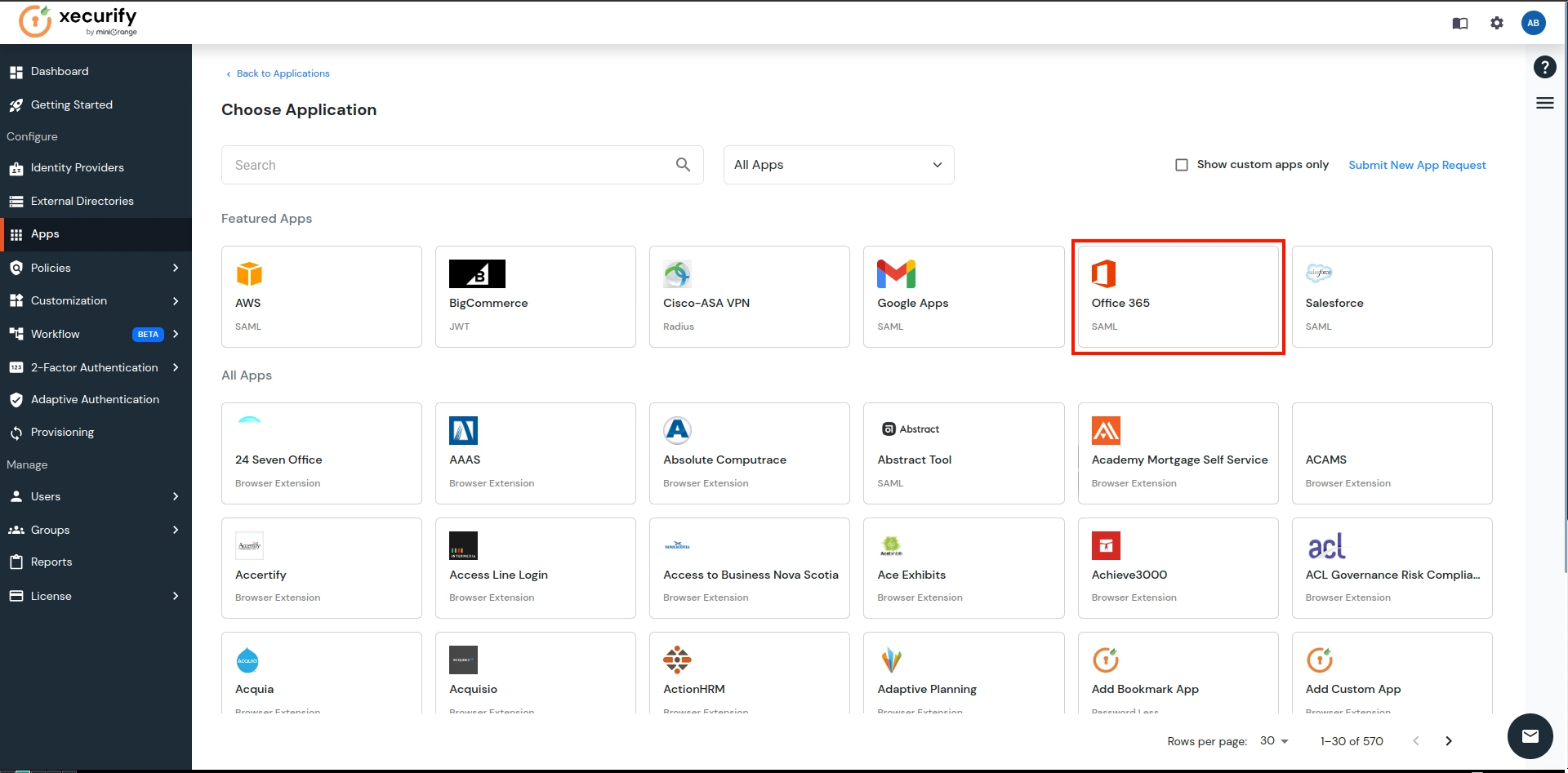
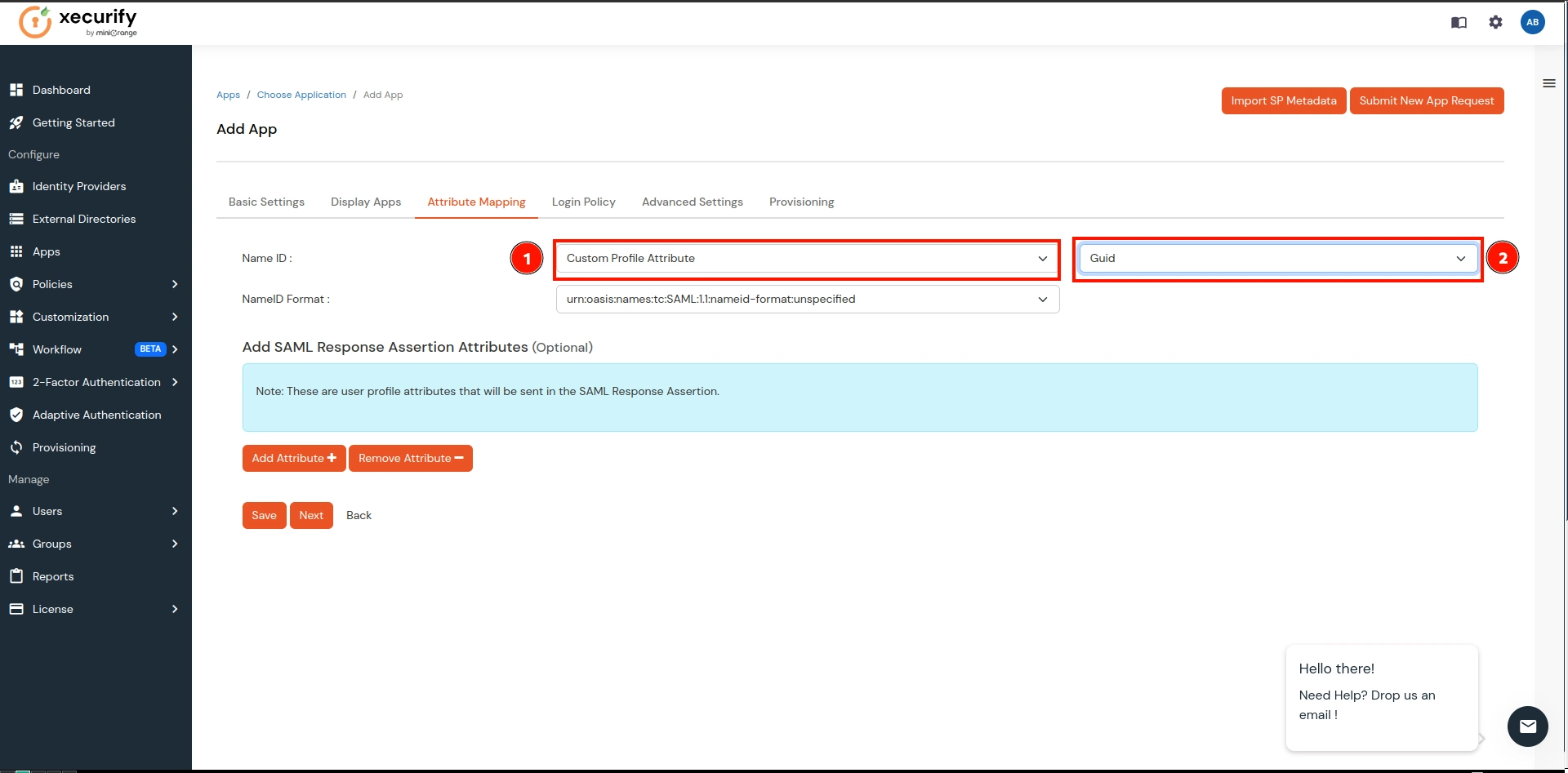
- Here, give the name of your application and go to Attribute Mapping. This application will be used to sync users from miniOrange IAM to Office 365.
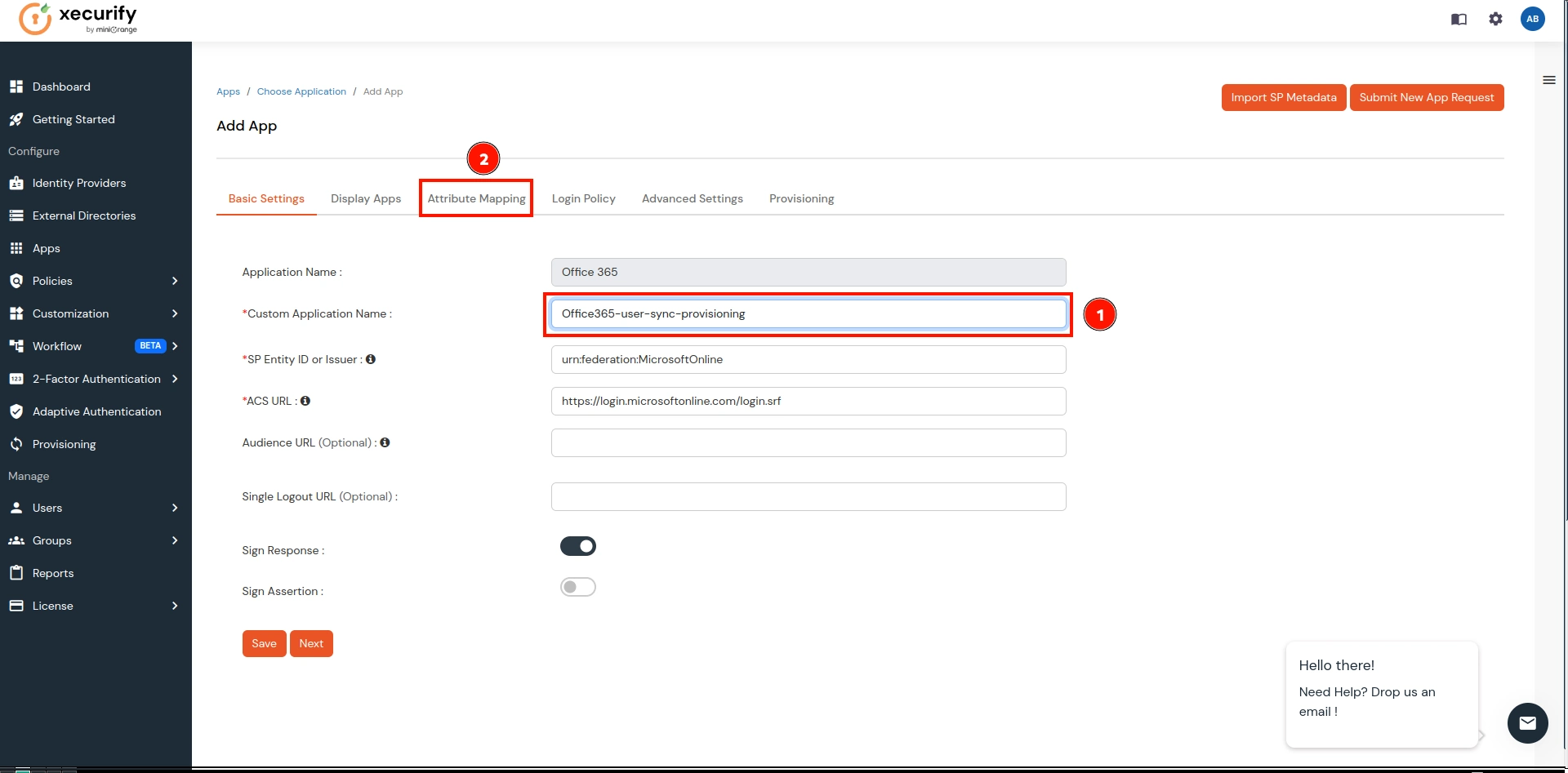
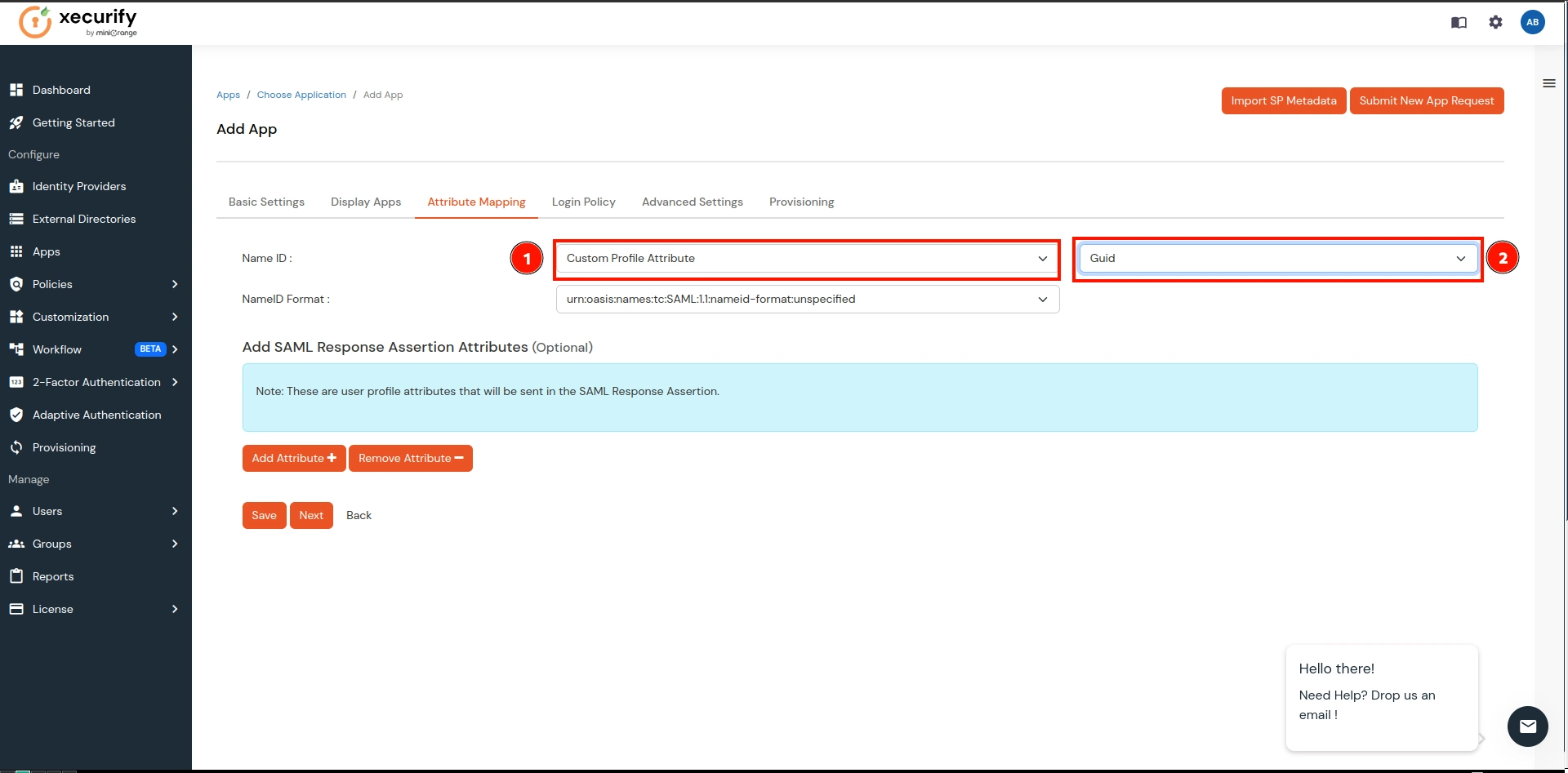
- On the Attribute Mappings:
- In NameID, select the Custom Attribute from the 1st dropdown.
- Now select Guid over the 2nd dropdown (which we created in the previous step).
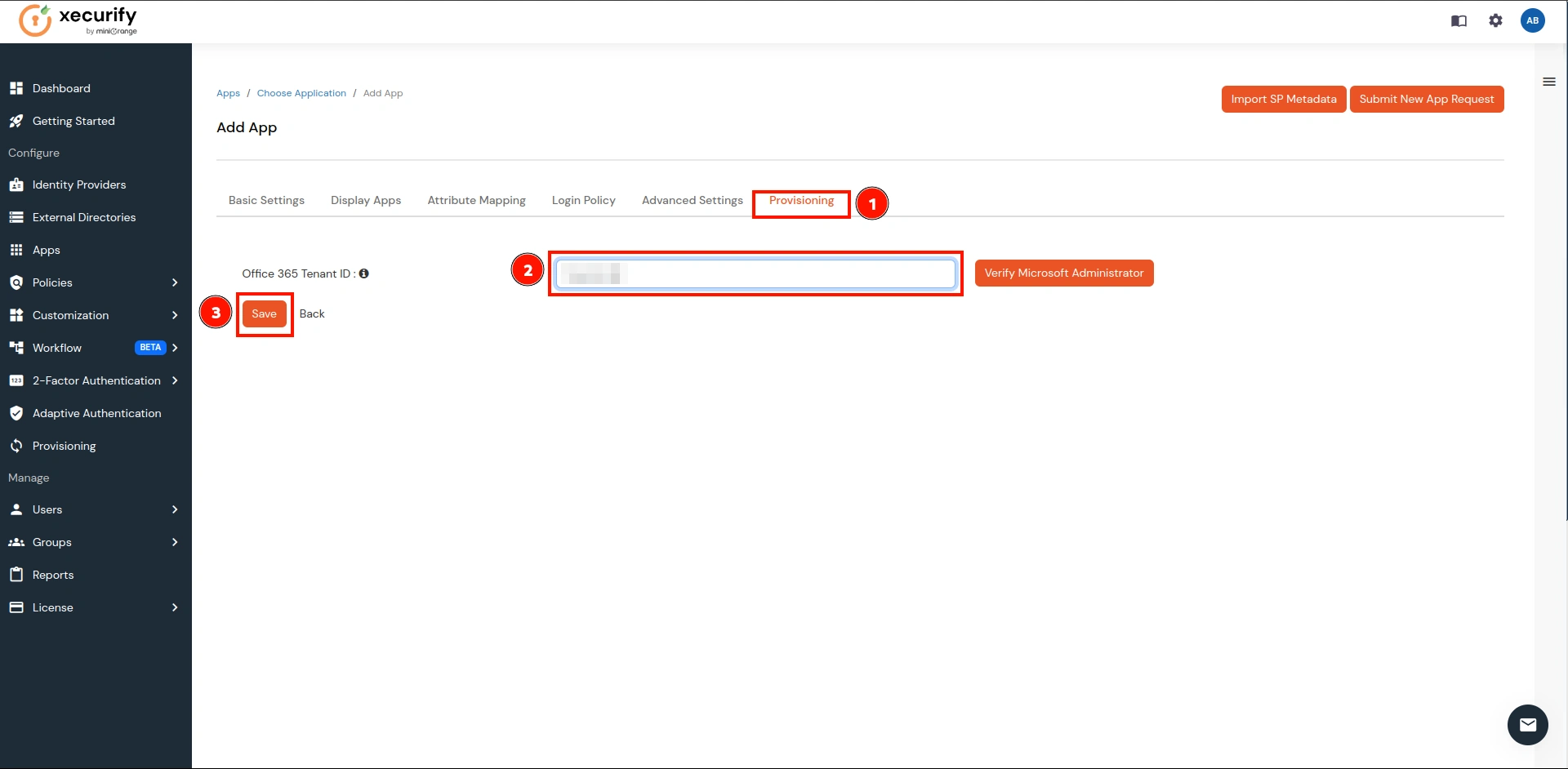
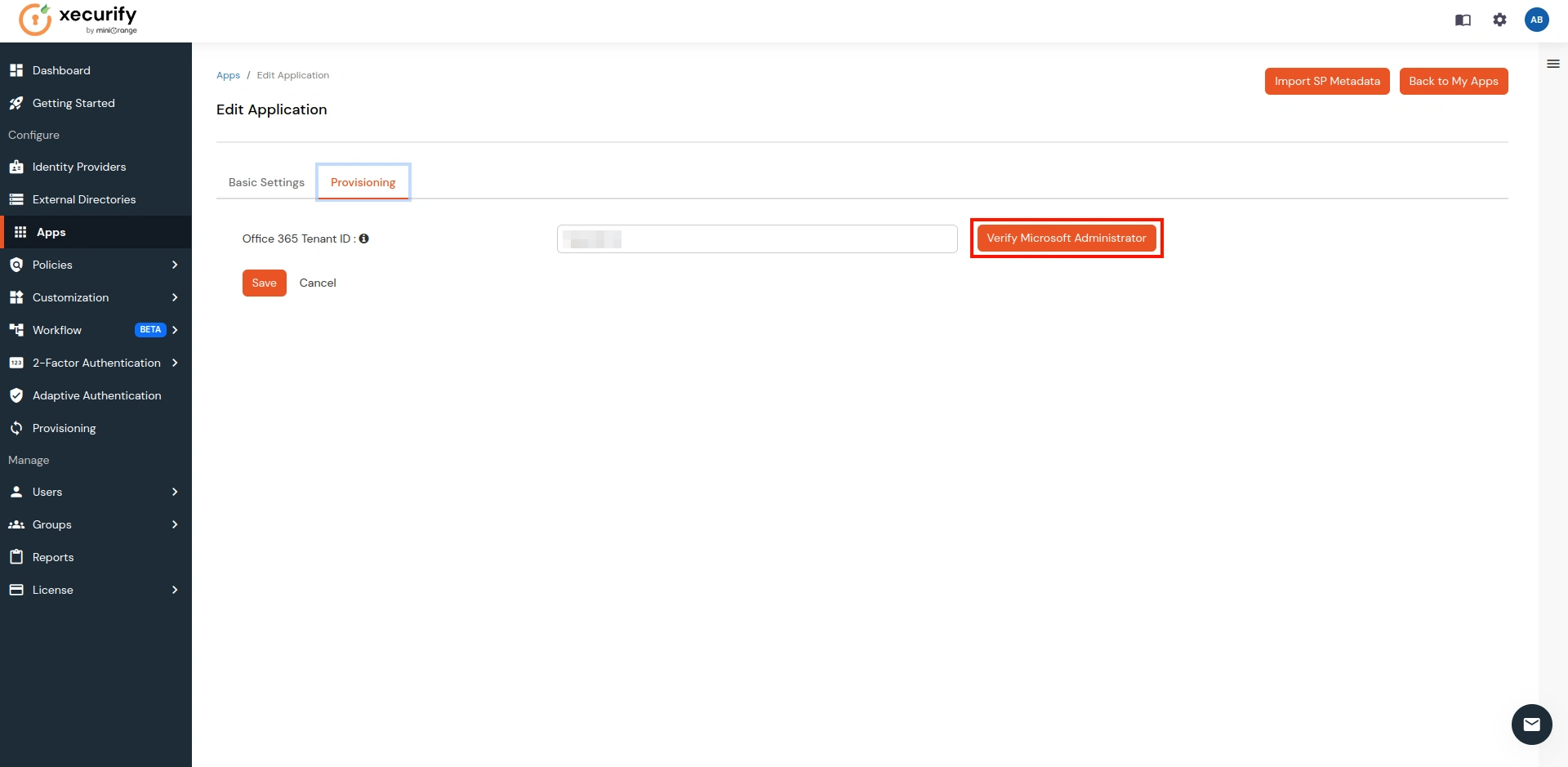
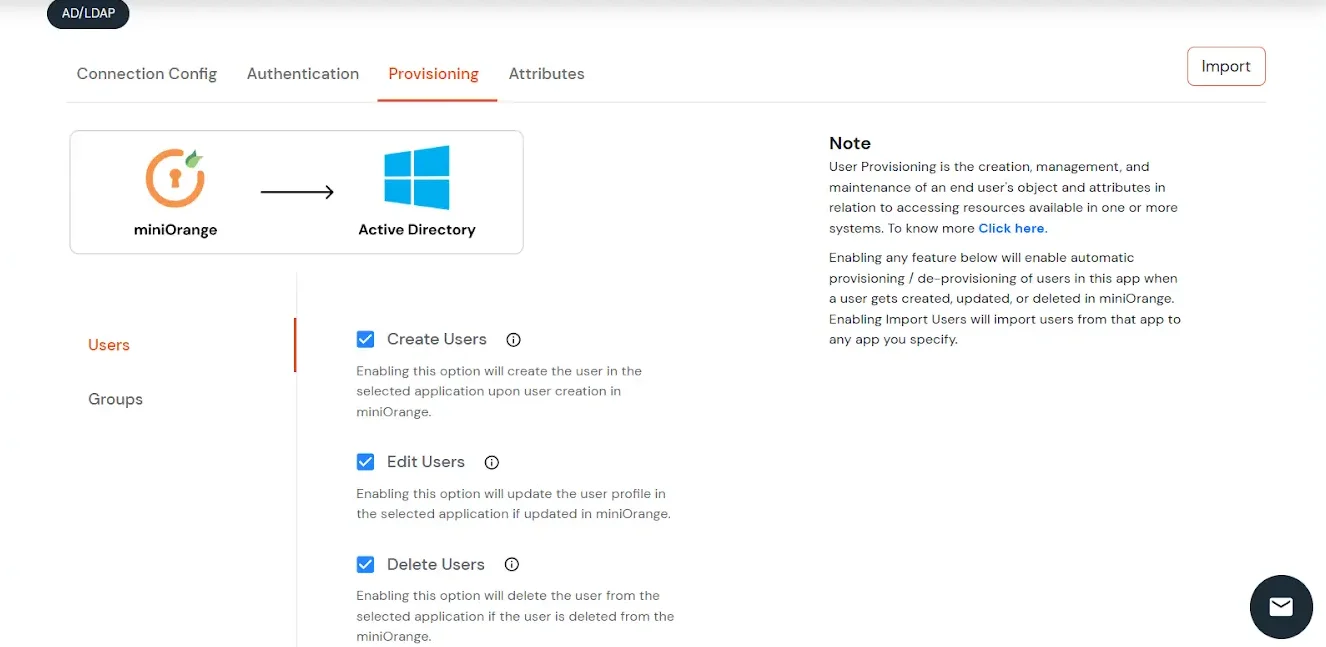
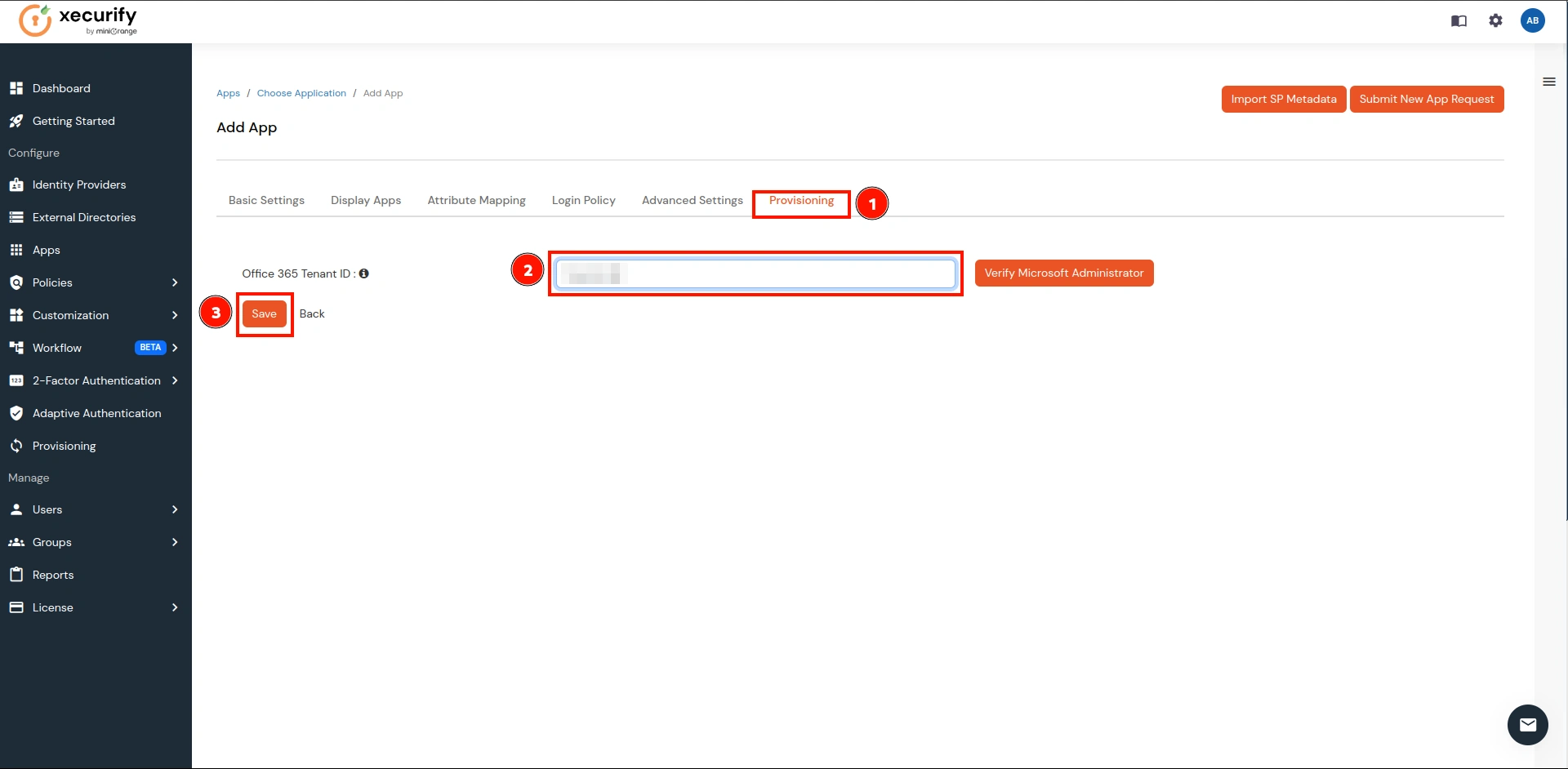
- Now navigate to the last tab Provisioning, enter your domain, and click on the Save button.
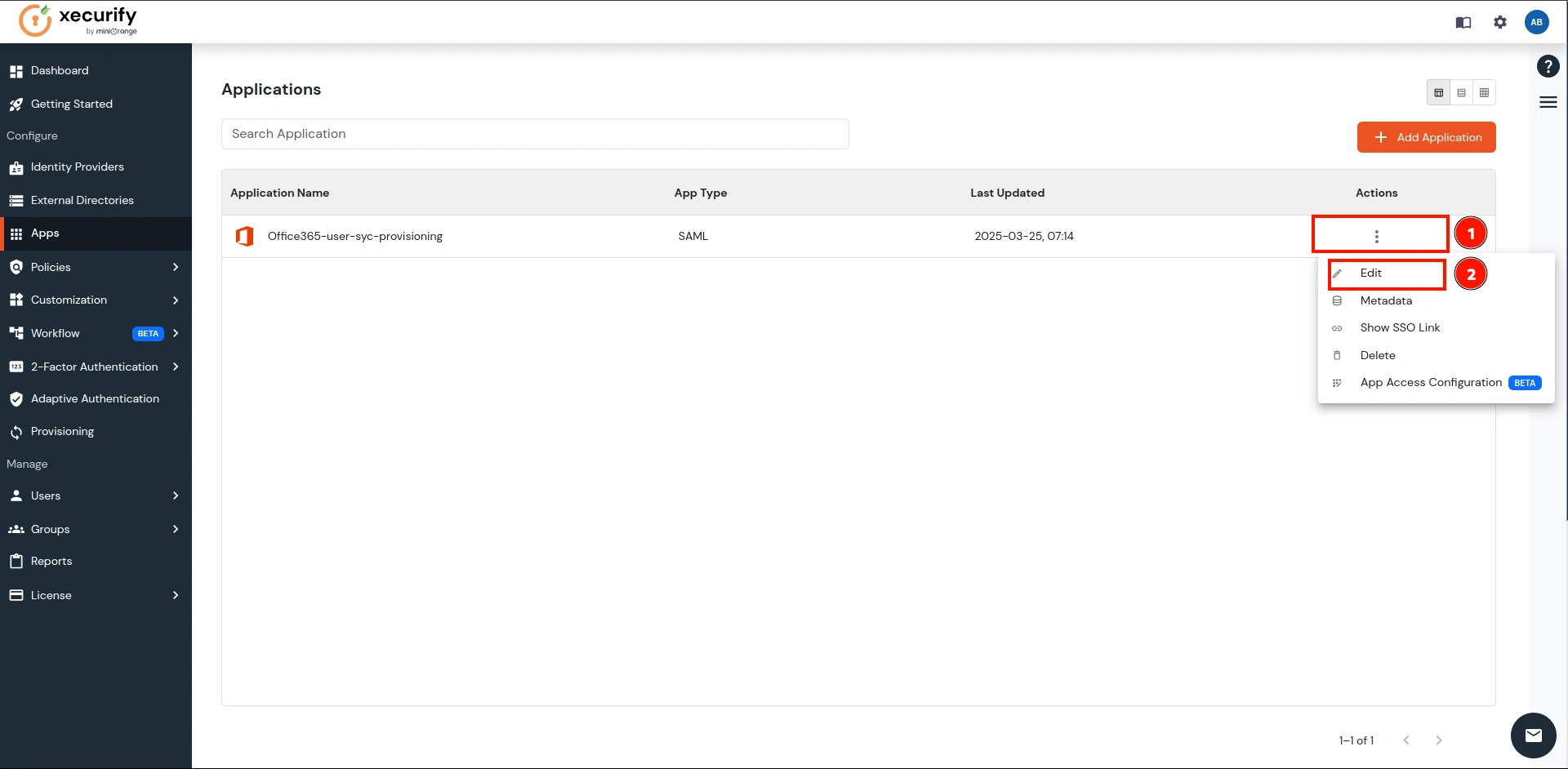
- Navigate to the newly created application and under the Actions column, click on the Edit button as shown below.
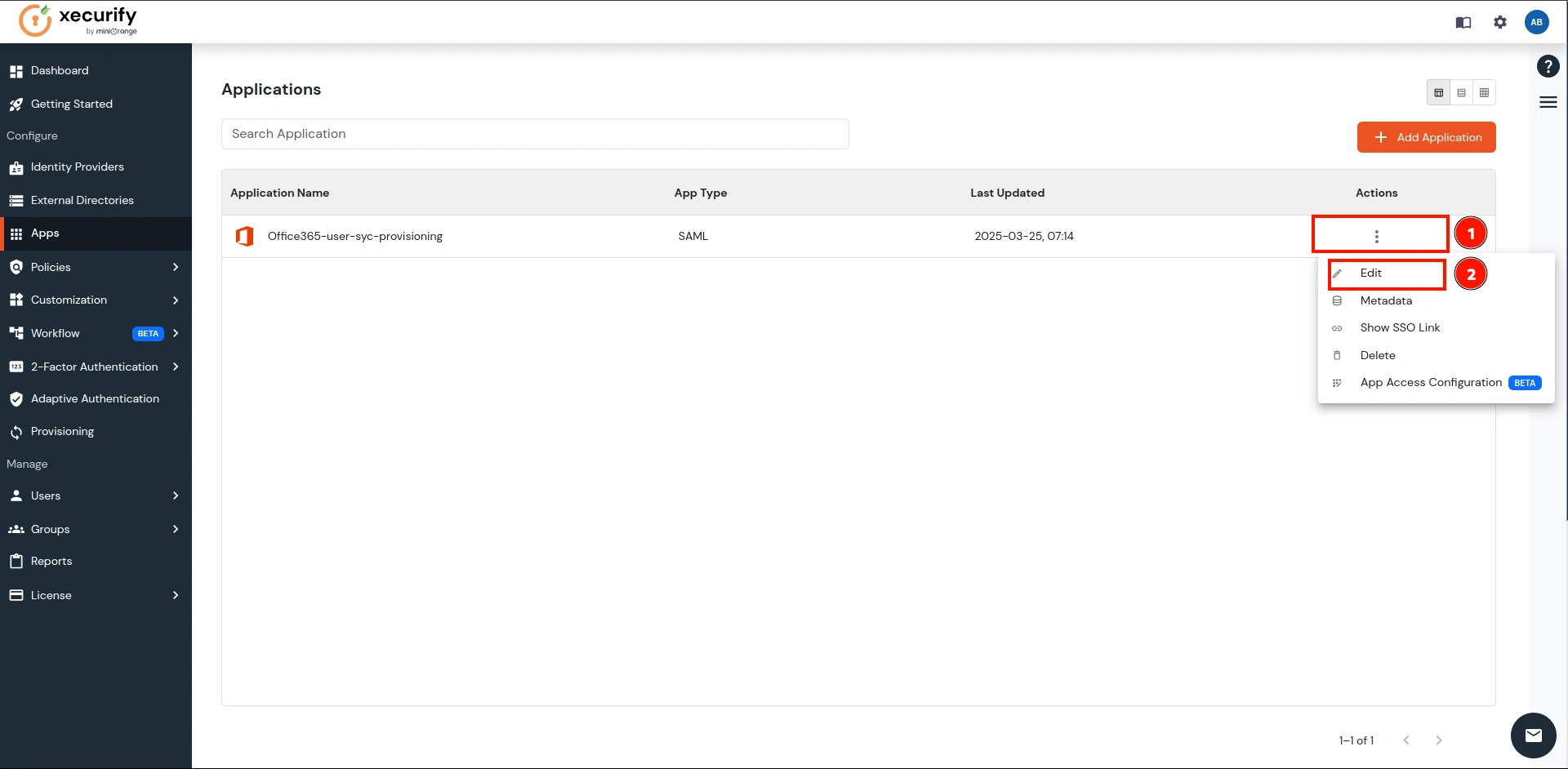
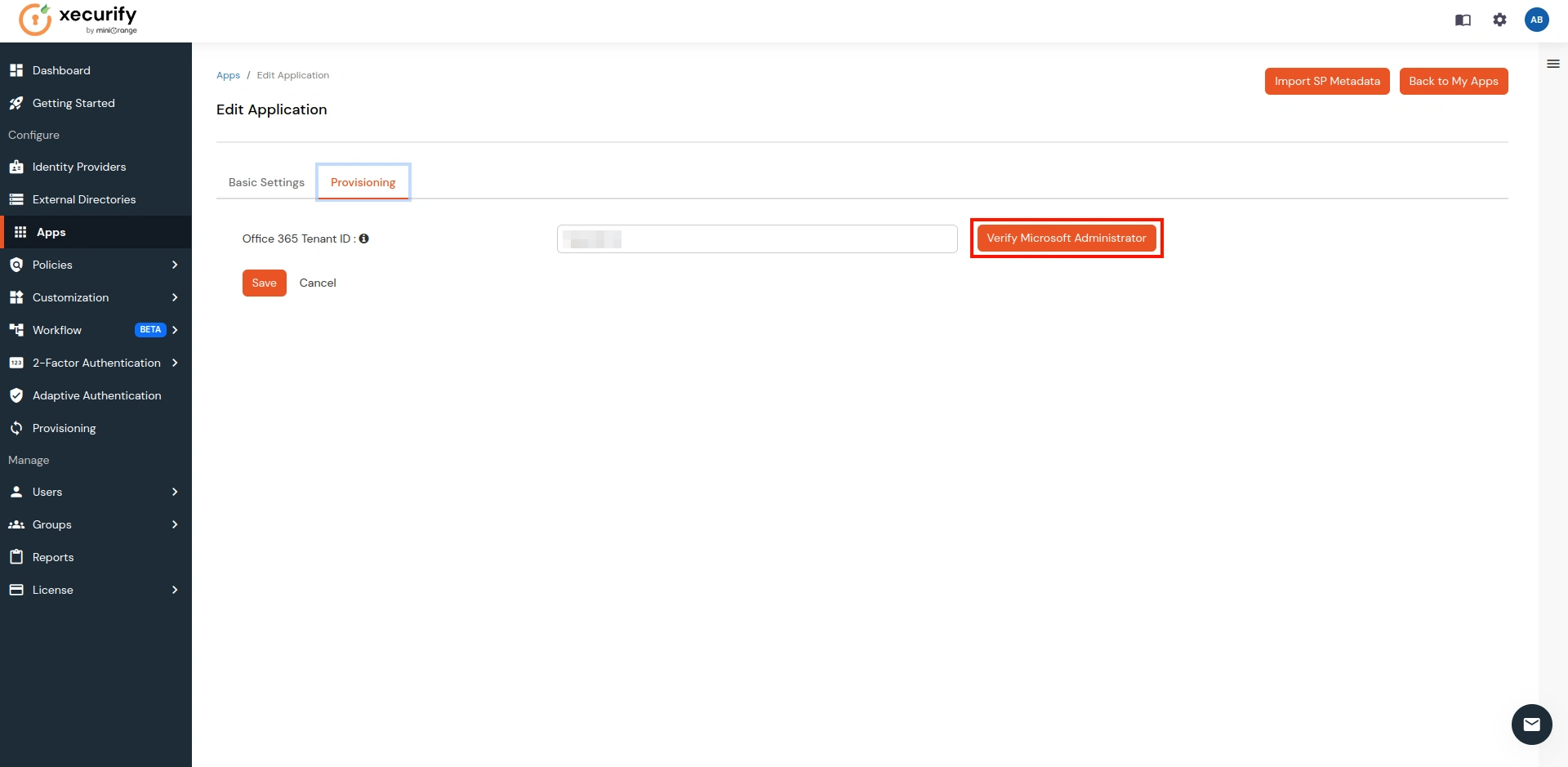
- It will open the Edit view of the application. Over there, go to Provisioning.
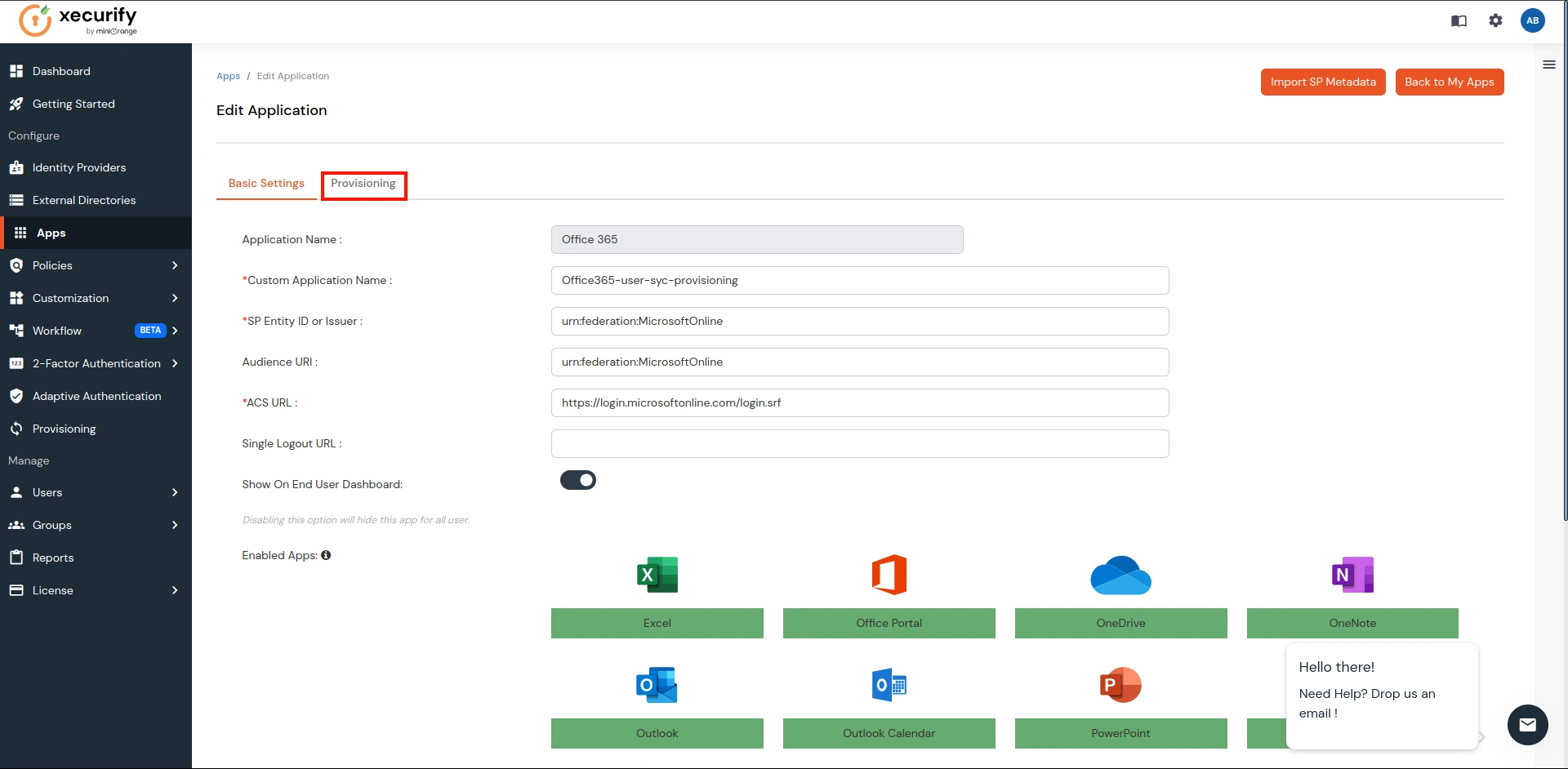
- Click on the Verify Microsoft Administrator button.
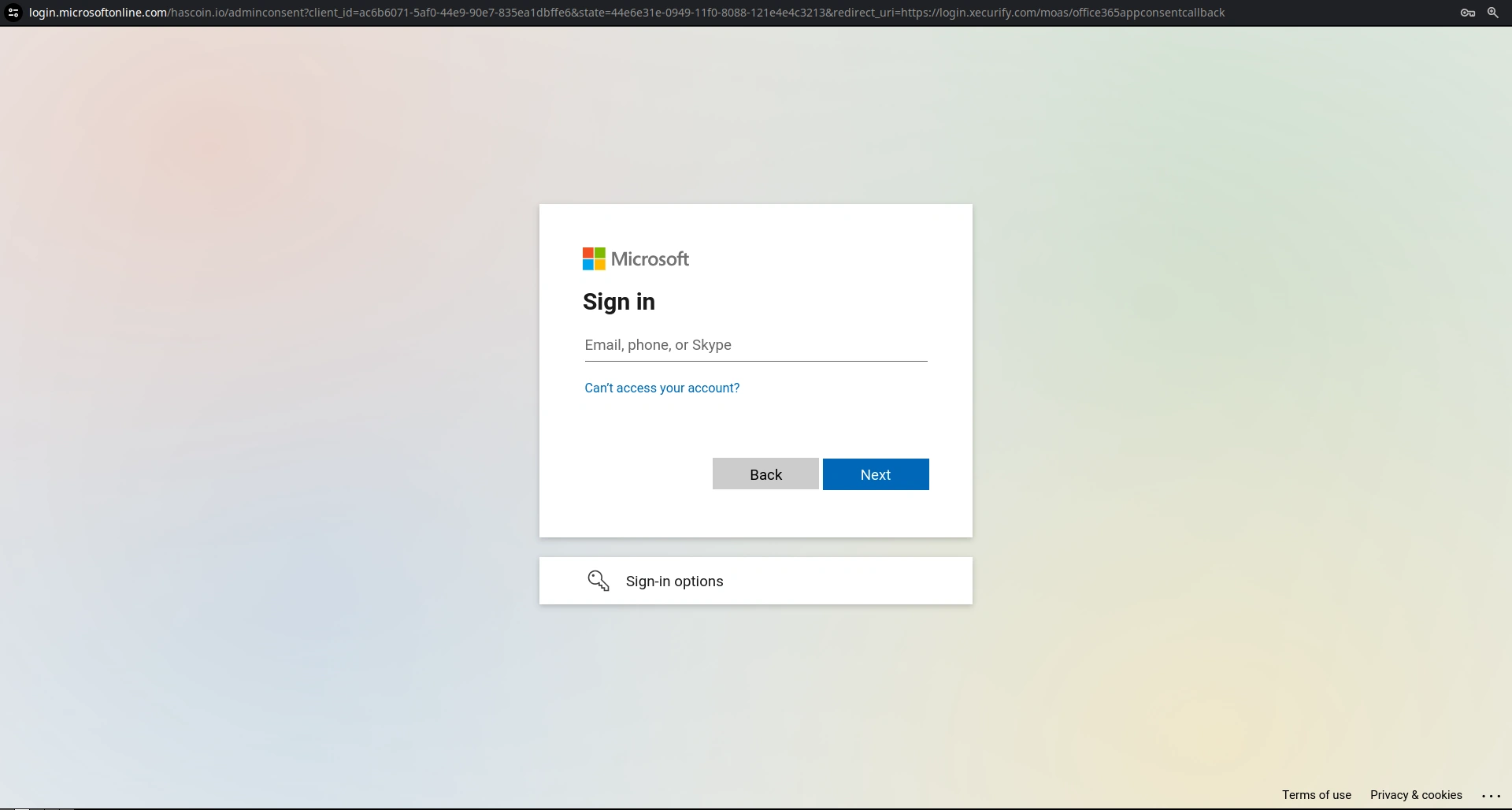
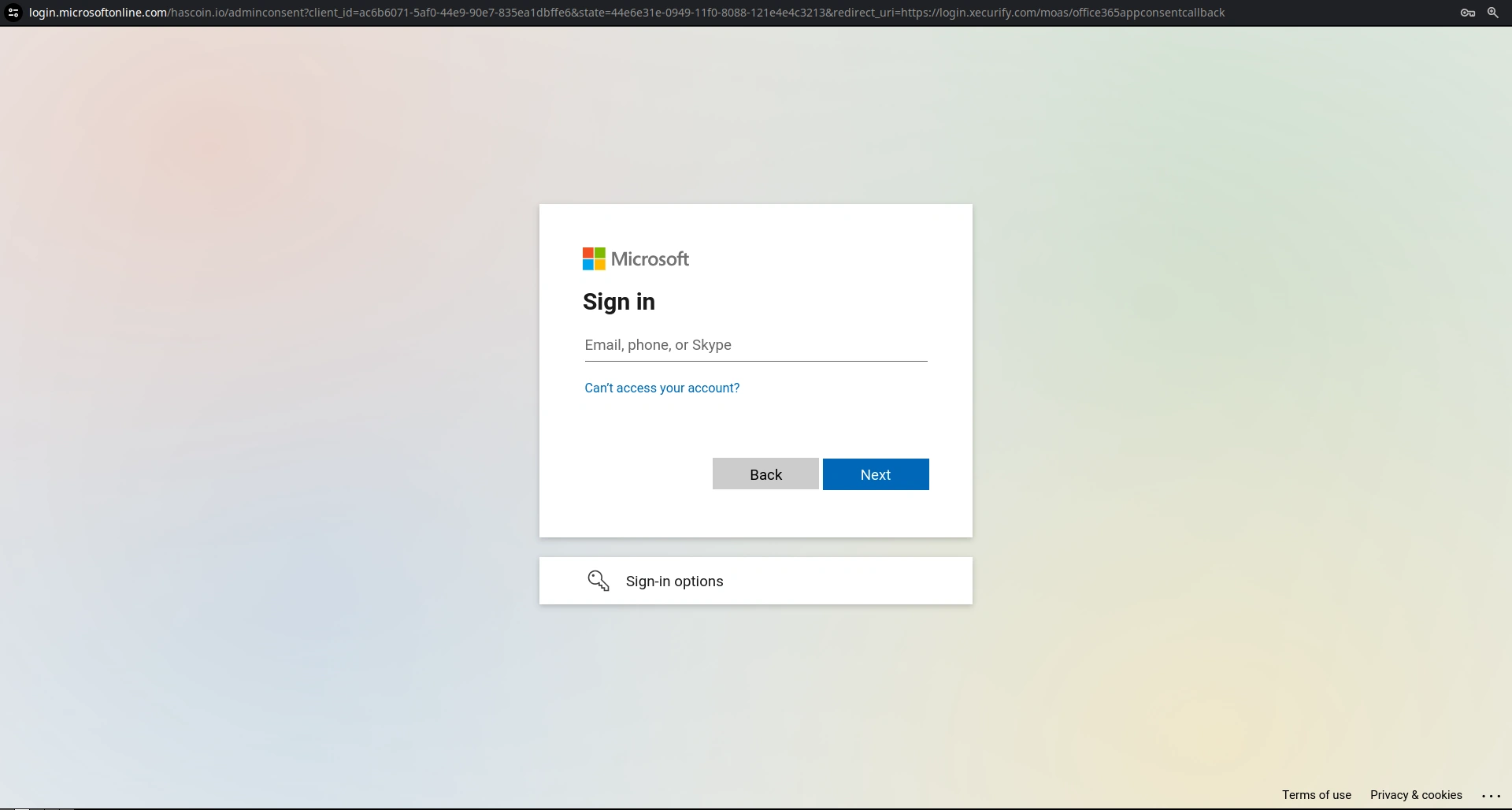
- It will take you to the Microsoft login page. Log in with your Admin Credentials for your Microsoft account.
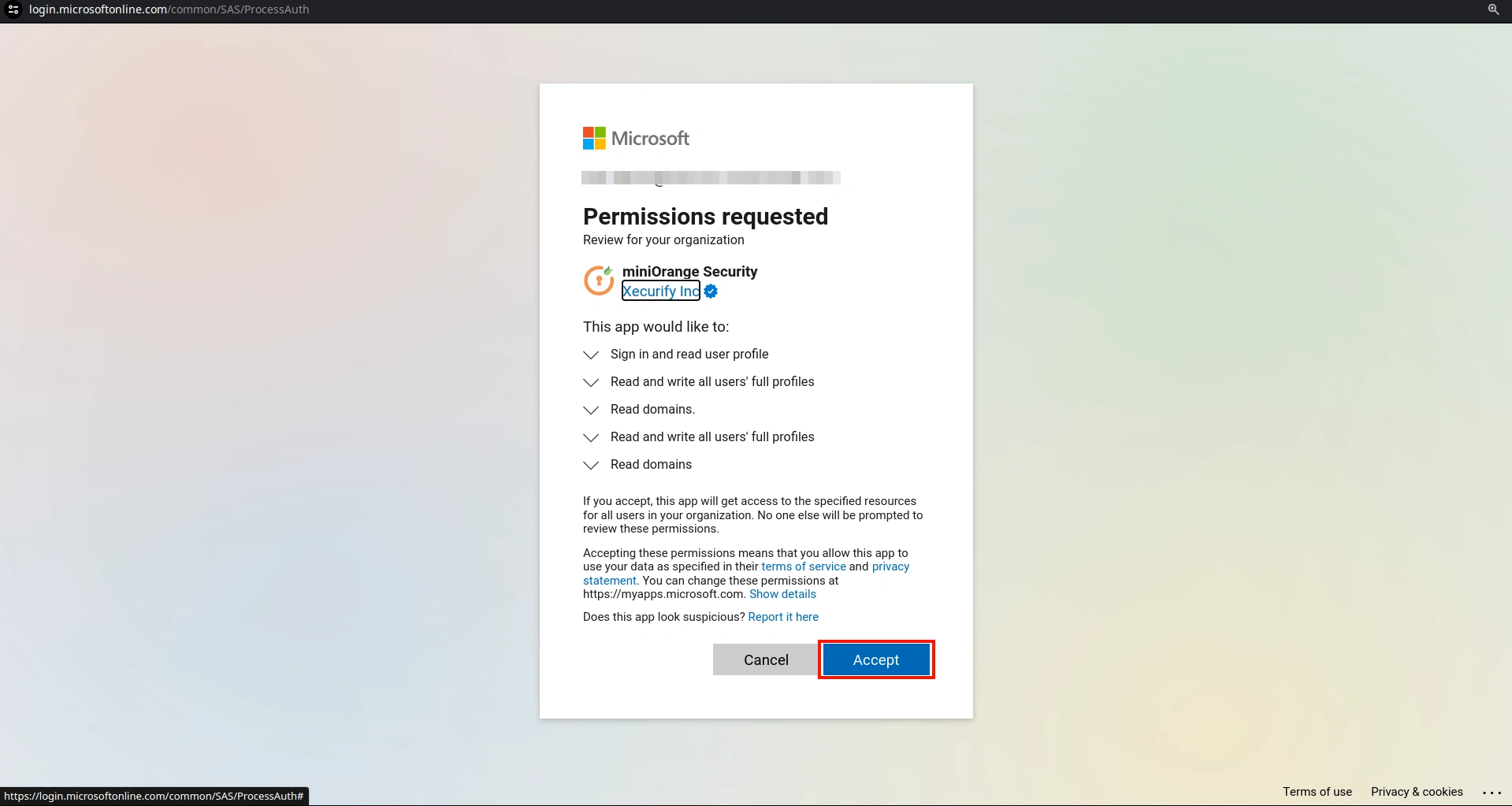
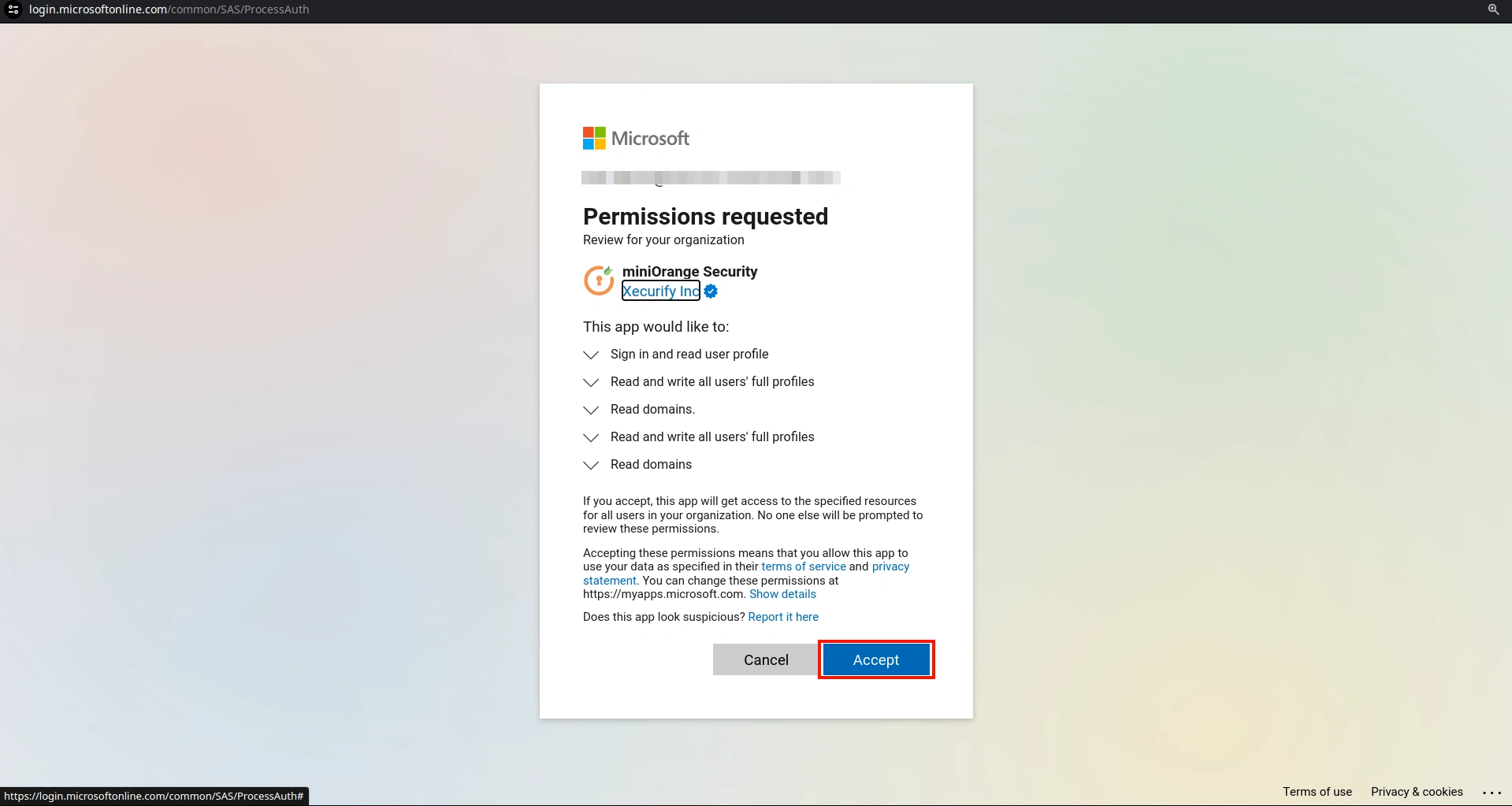
- Once you are logged in with the admin user, it will show you the page below. Click on the Accept button.
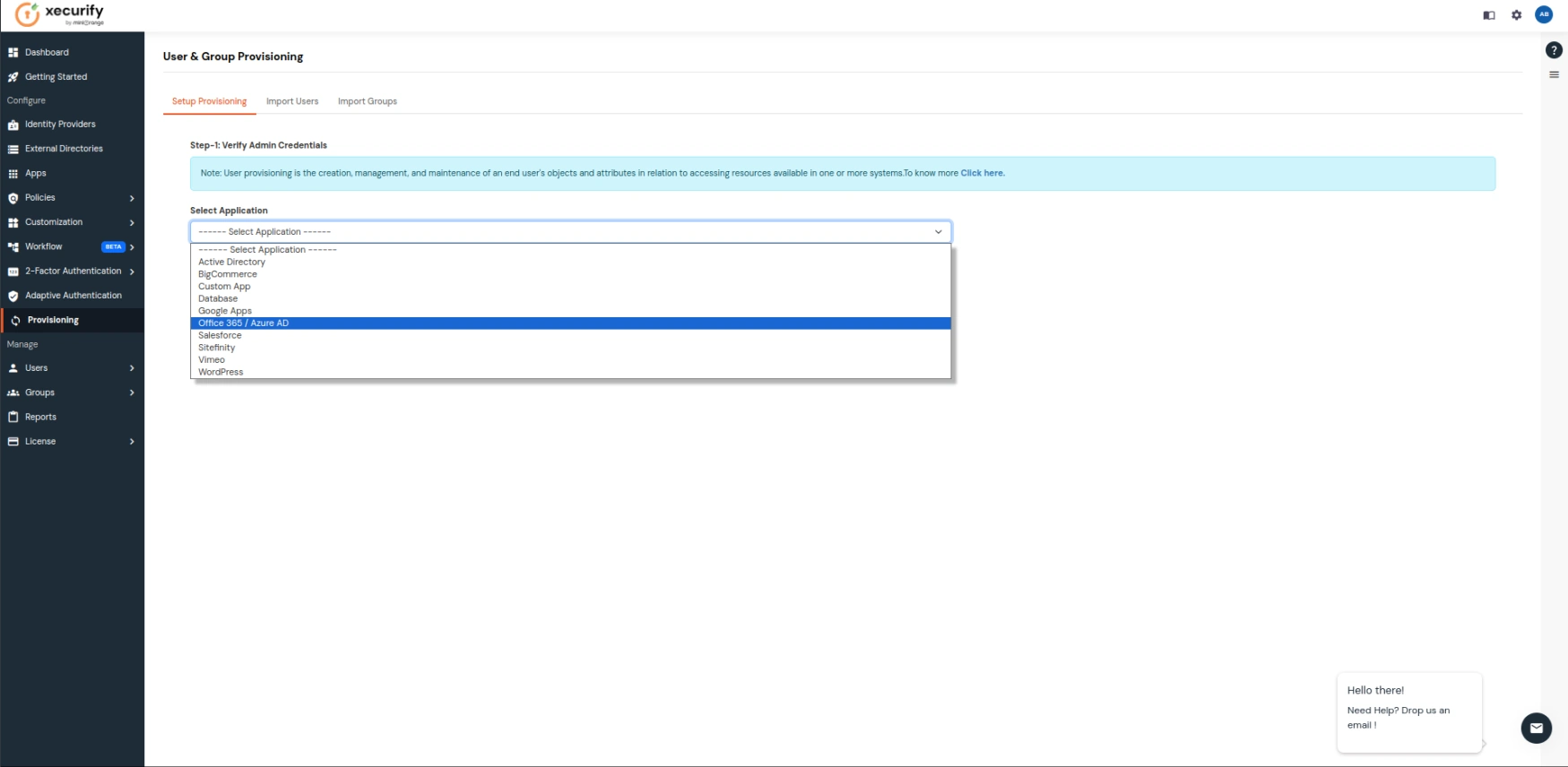
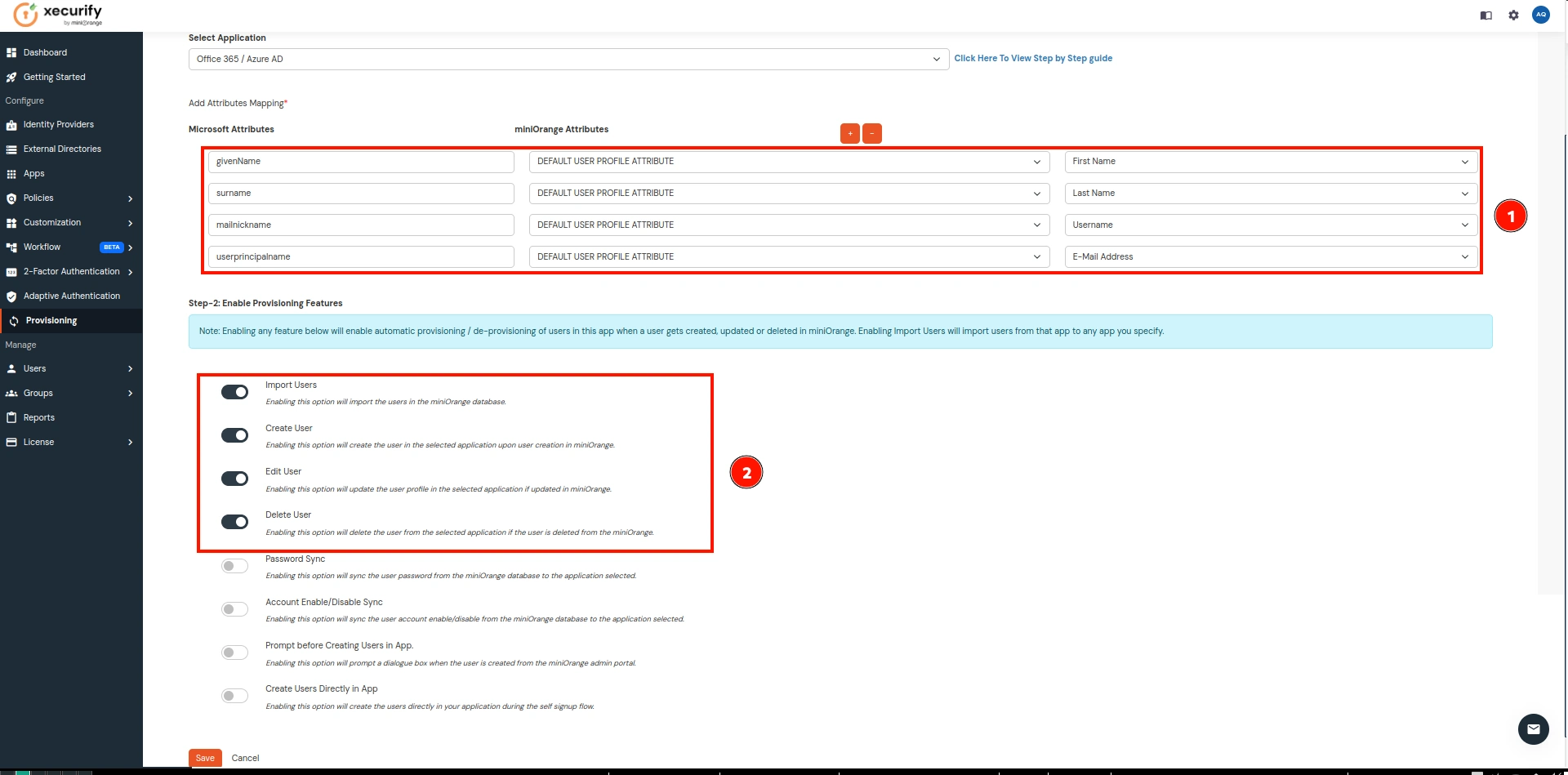
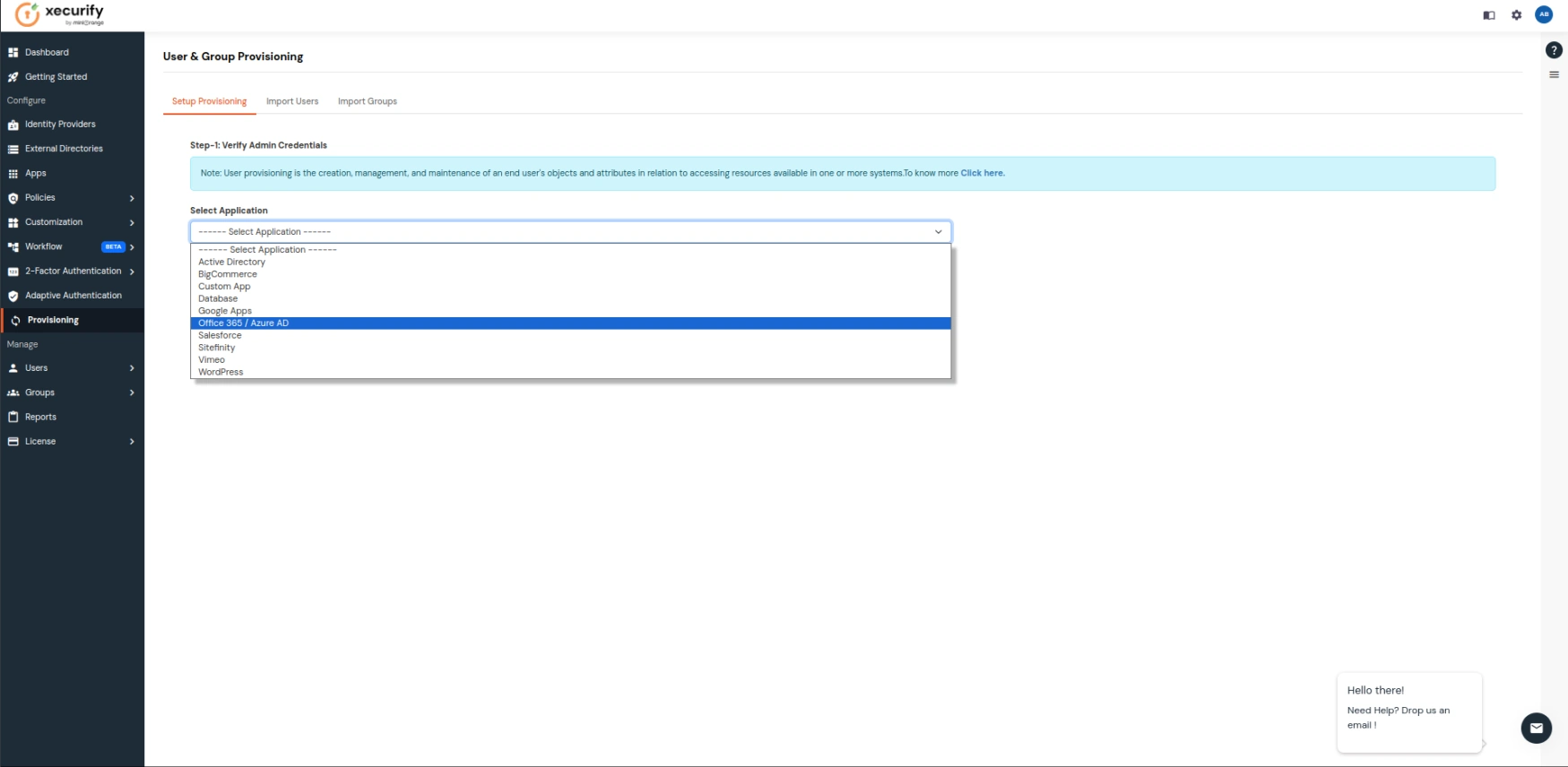
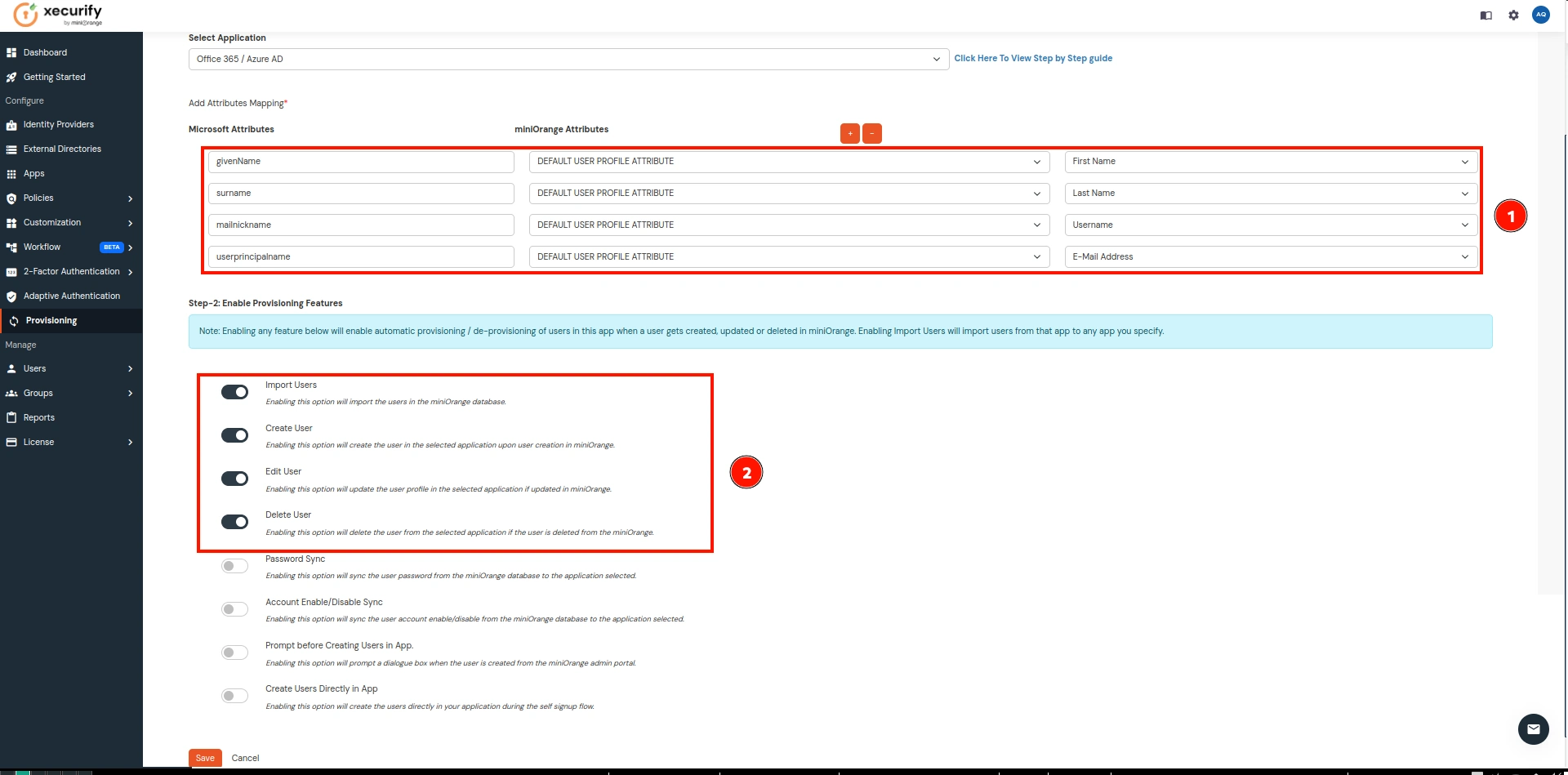
- Now go to Provisioning on the sidebar and in the Select Application dropdown, choose Office 365 / Azure AD.
- Keep the Attribute section with the values shown in the image below, enable the required Provisioning Features, and click on Save once you are done.
| Microsft Attributes |
miniOrange Attributes |
|---|
| givenName |
First Name |
| surname |
Last Name
|
| mailnickname |
Username
|
| userprincipalname |
Email Address
|
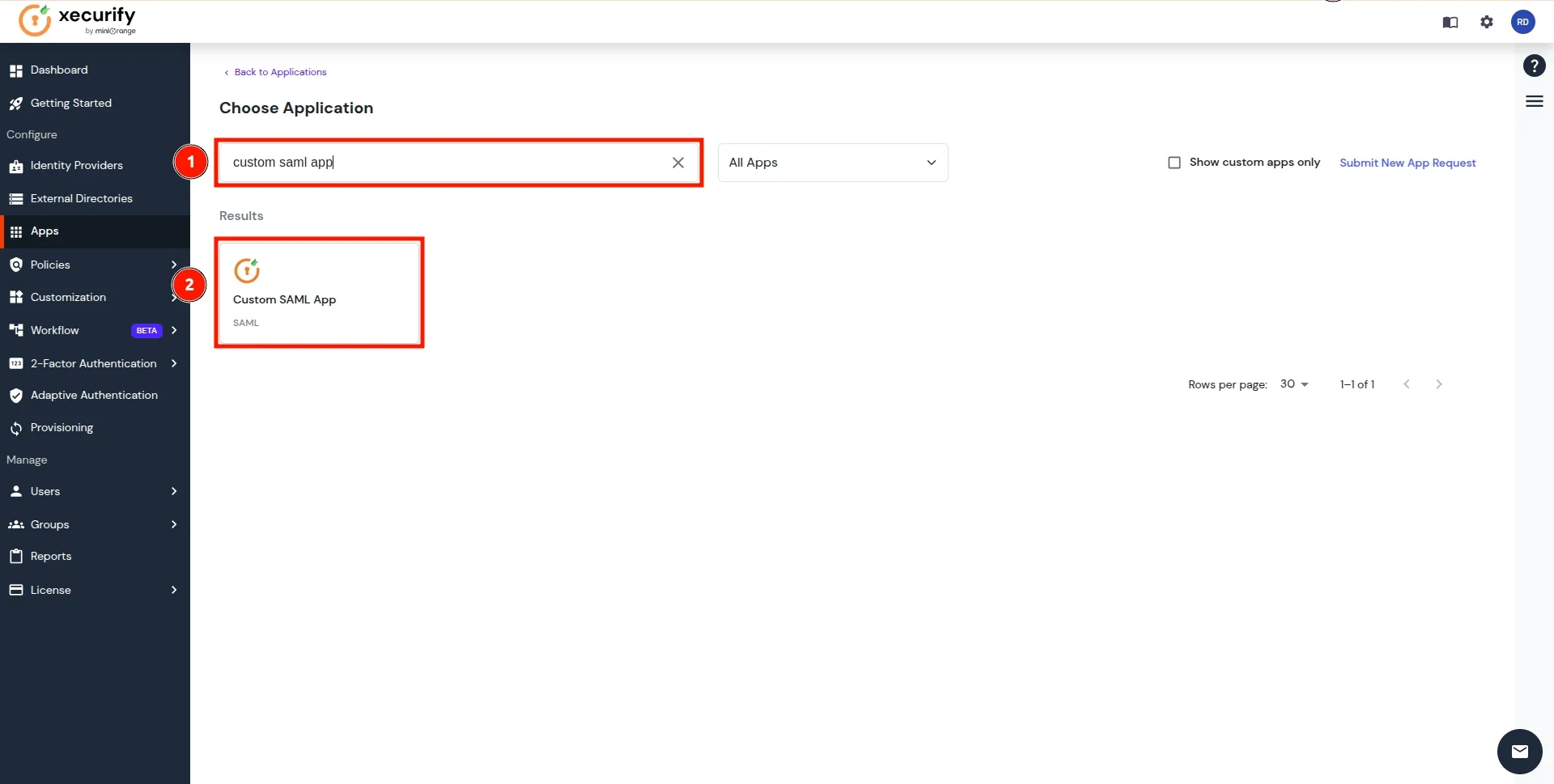
- Now go to the Apps on the sidebar and click on Add Application.
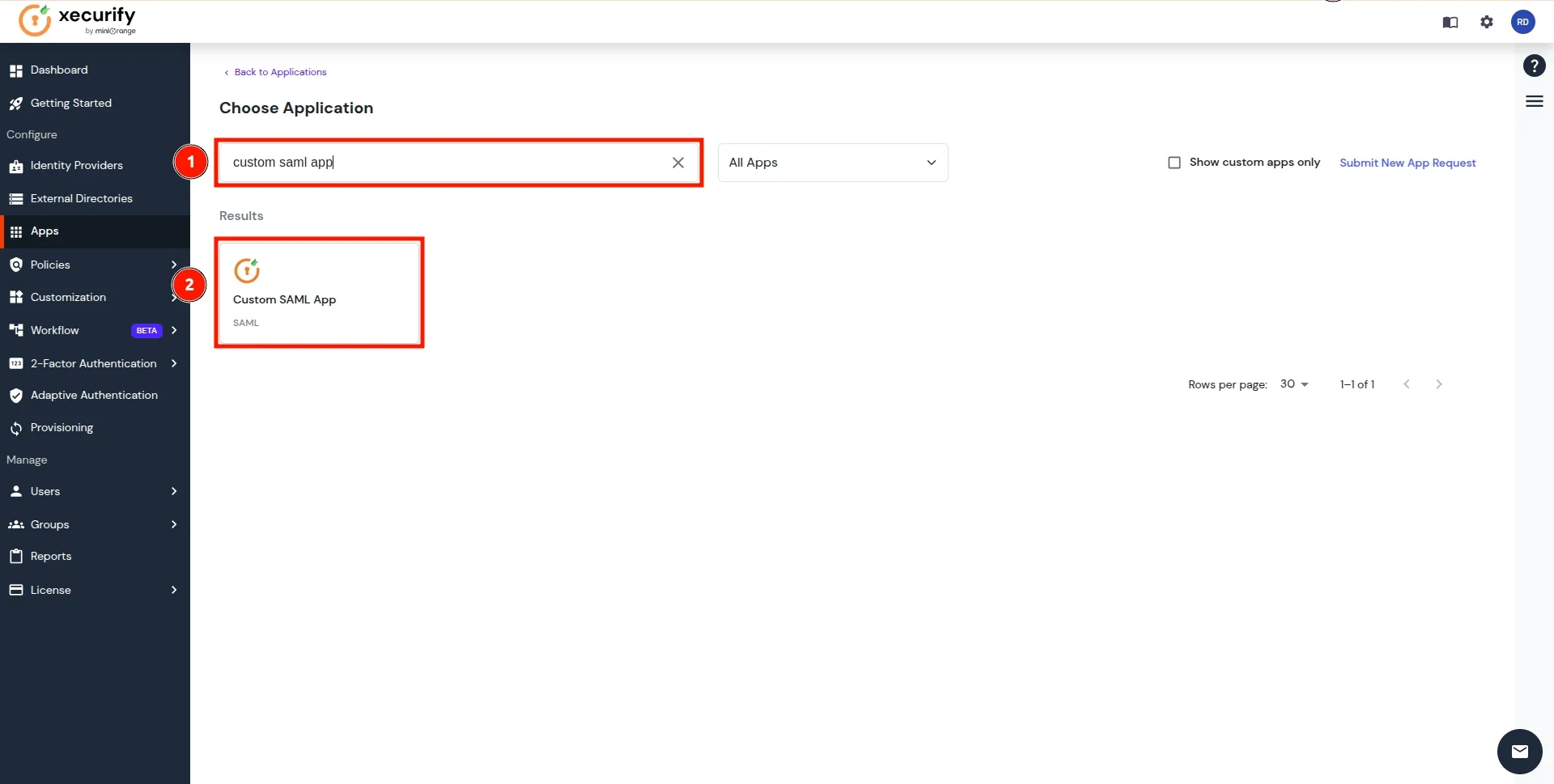
- Search for Custom SAML App and click on it.
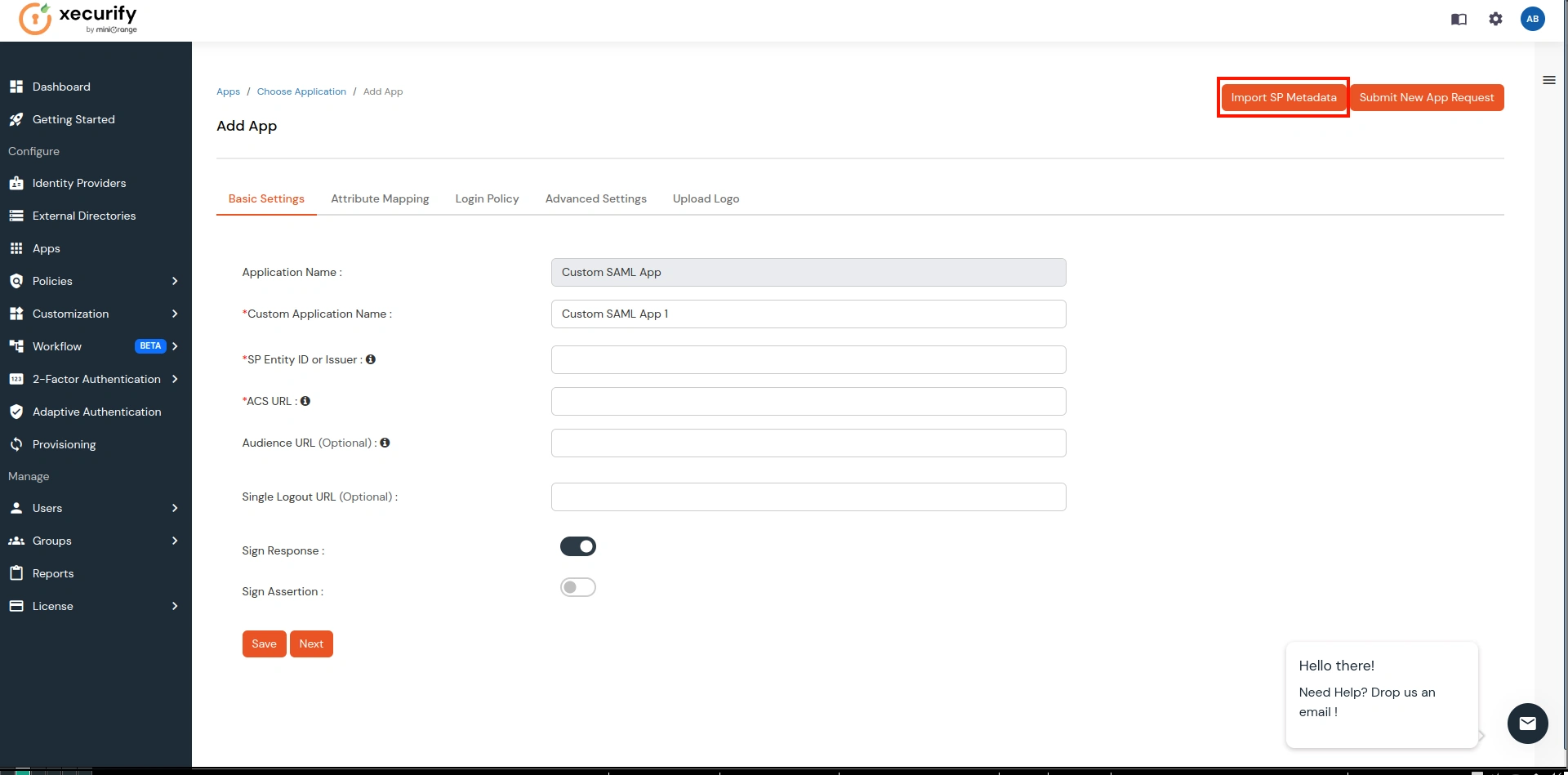
- Click on the Import SP Metadata button as shown below.
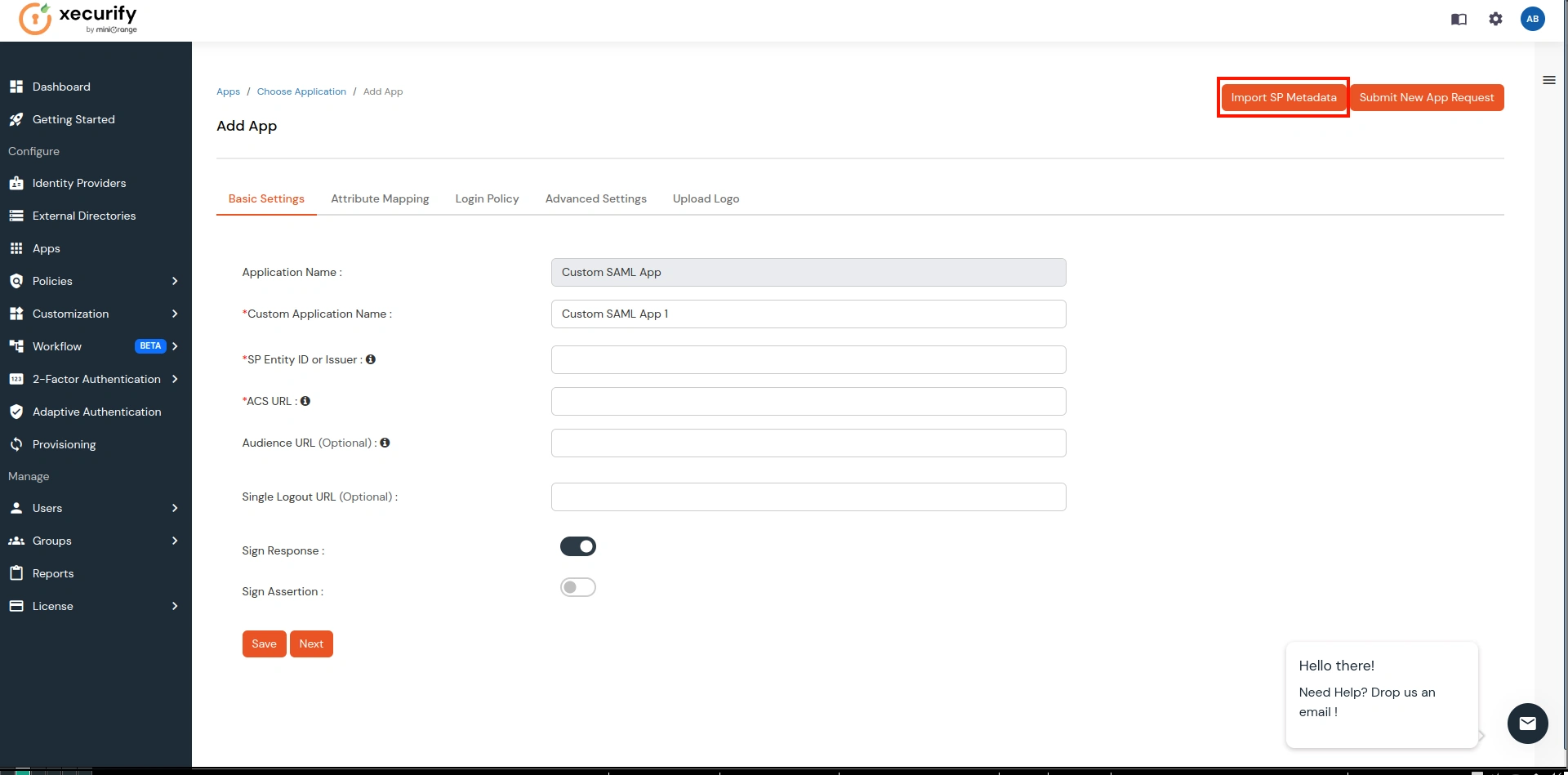
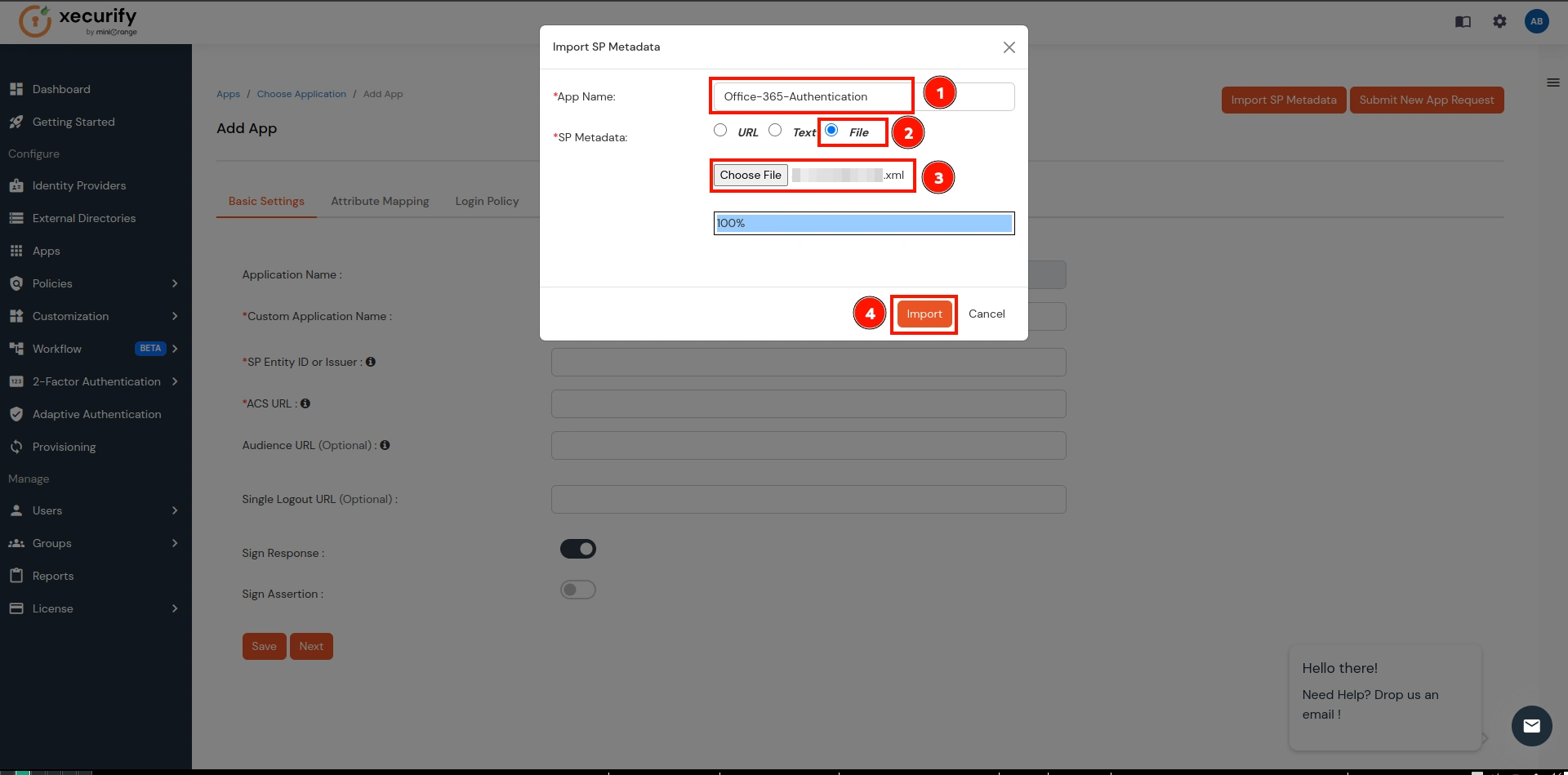
- Provide a name for your Office-365 Authentication application, choose the File option, upload the file downloaded in step 1, and click on Import.
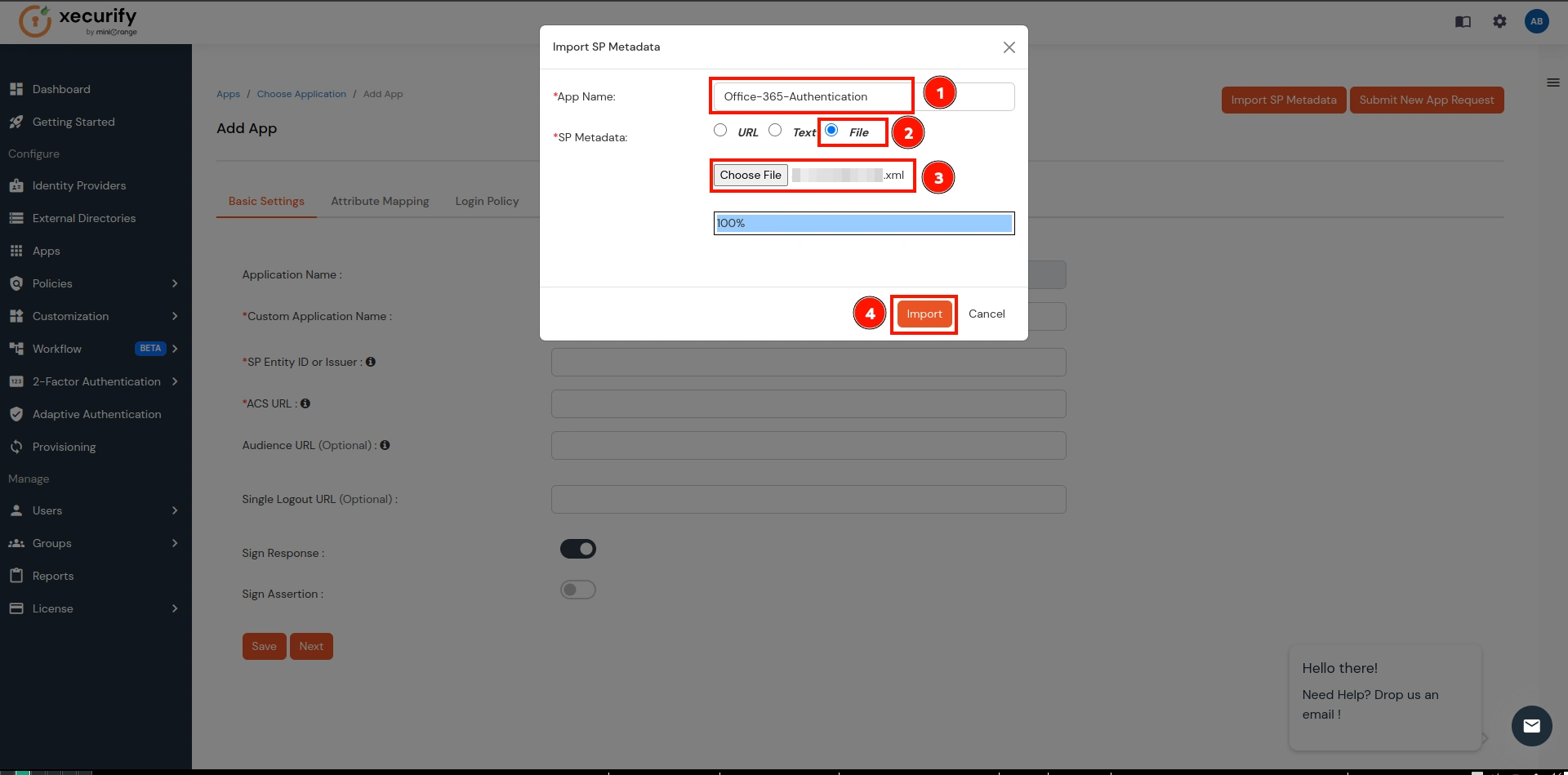
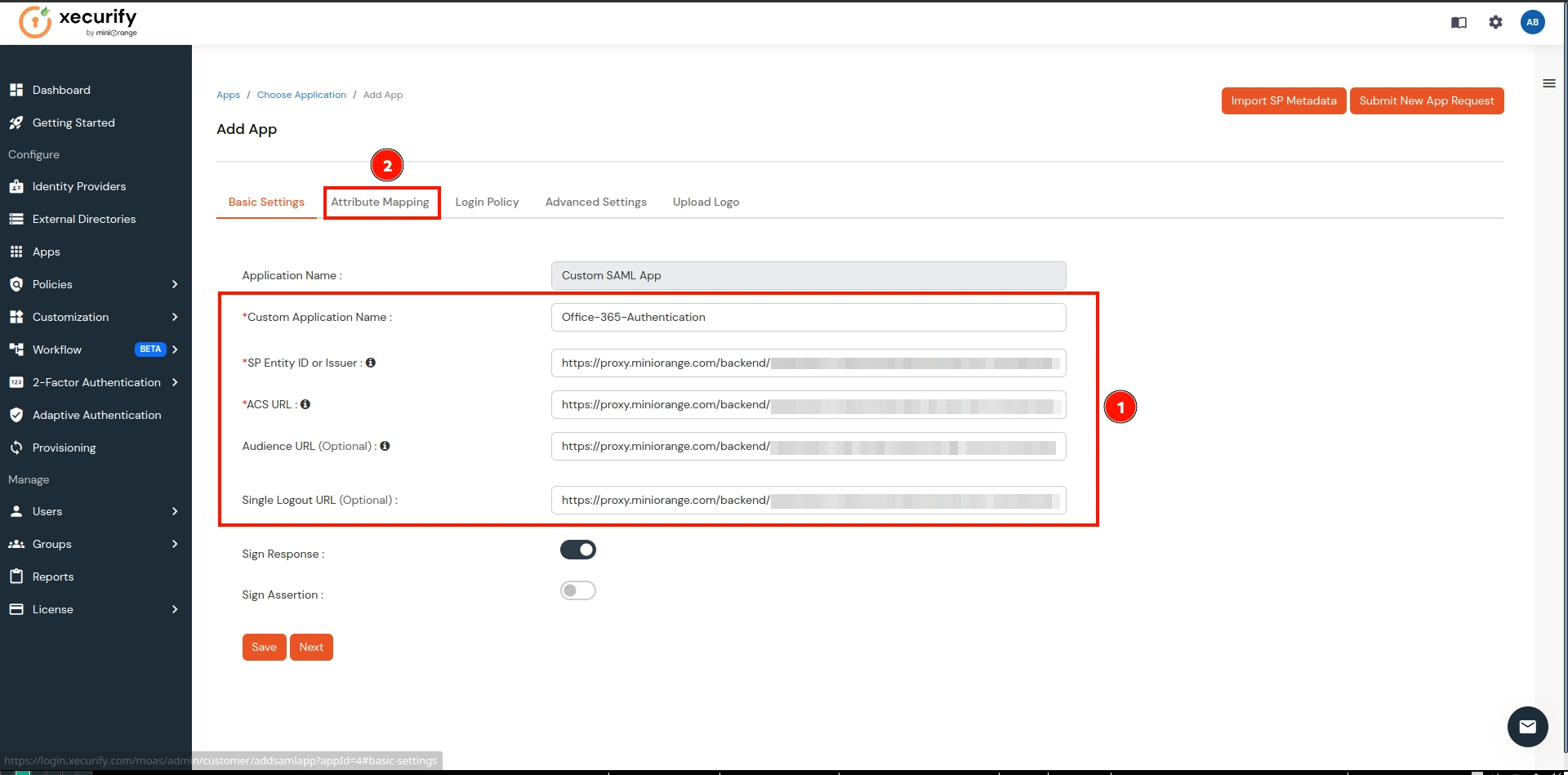
- This step will import the metadata for SAML Authentication. Now go to the Attribute Mapping section.
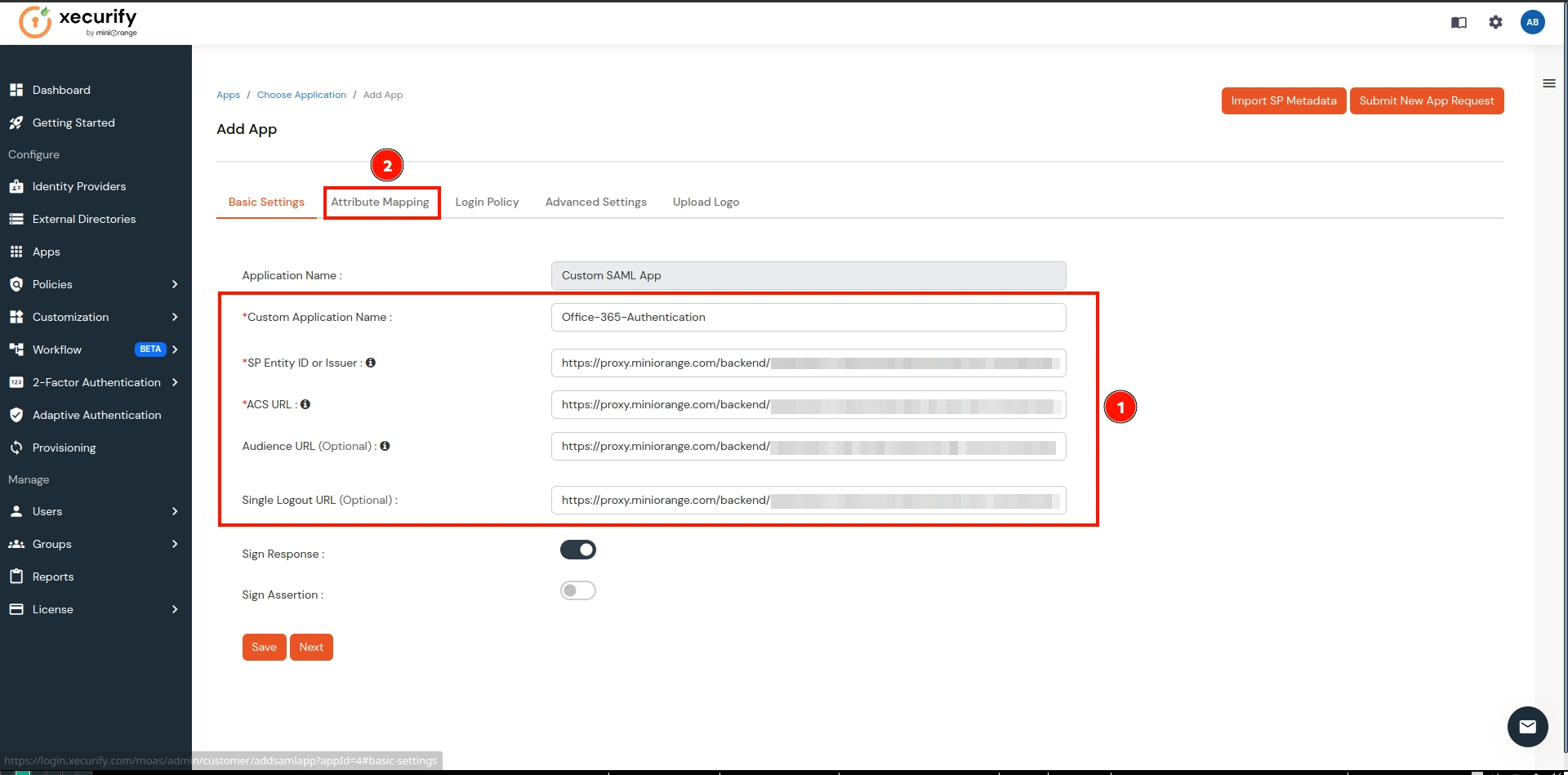
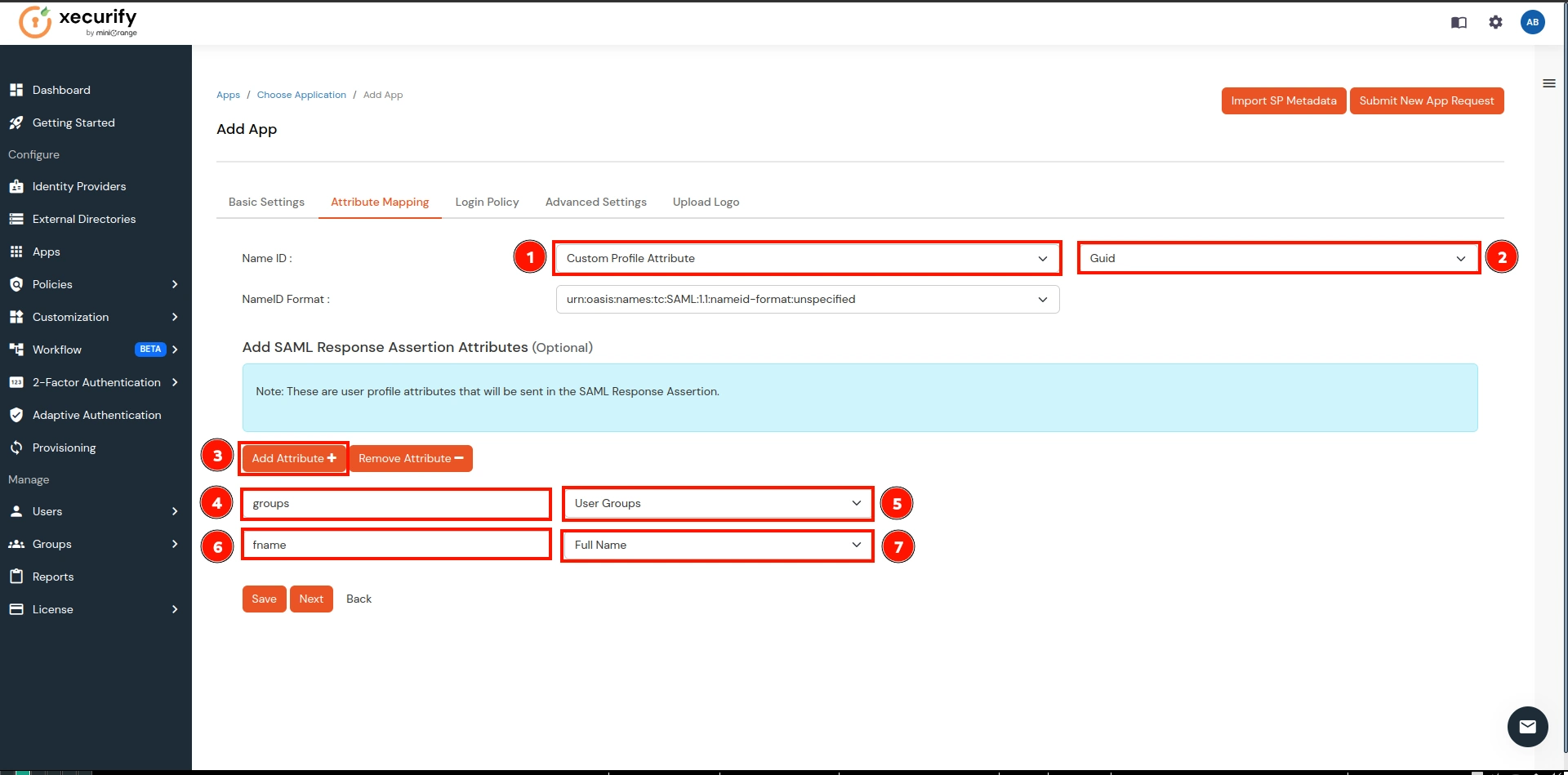
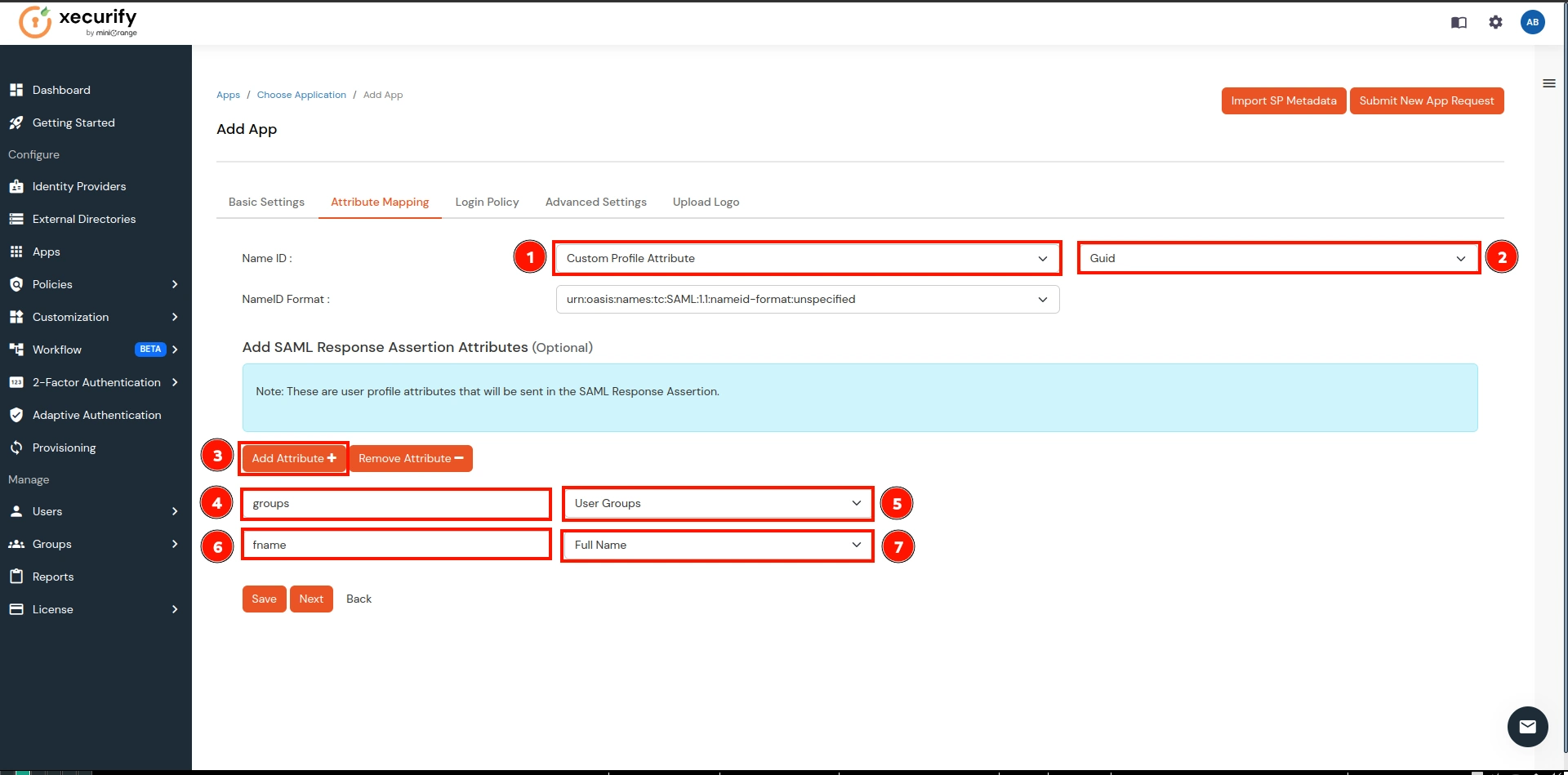
- In the Attribute Mapping, make the following configurations and click on the Save button:
- NameID → Select the Custom Profile Attribute from the 1st dropdown and select Guid from the 2nd dropdown.
- Click on Add Attribute button as shown below in the 3rd.
- Group Attribute Mapping:
- Attribute Name → groups
- Attribute Value → User Groups (select from dropdown)
- Name Attribute Mapping:
- Attribute Name → fname
- Attribute Value → Full Name (select from dropdown)
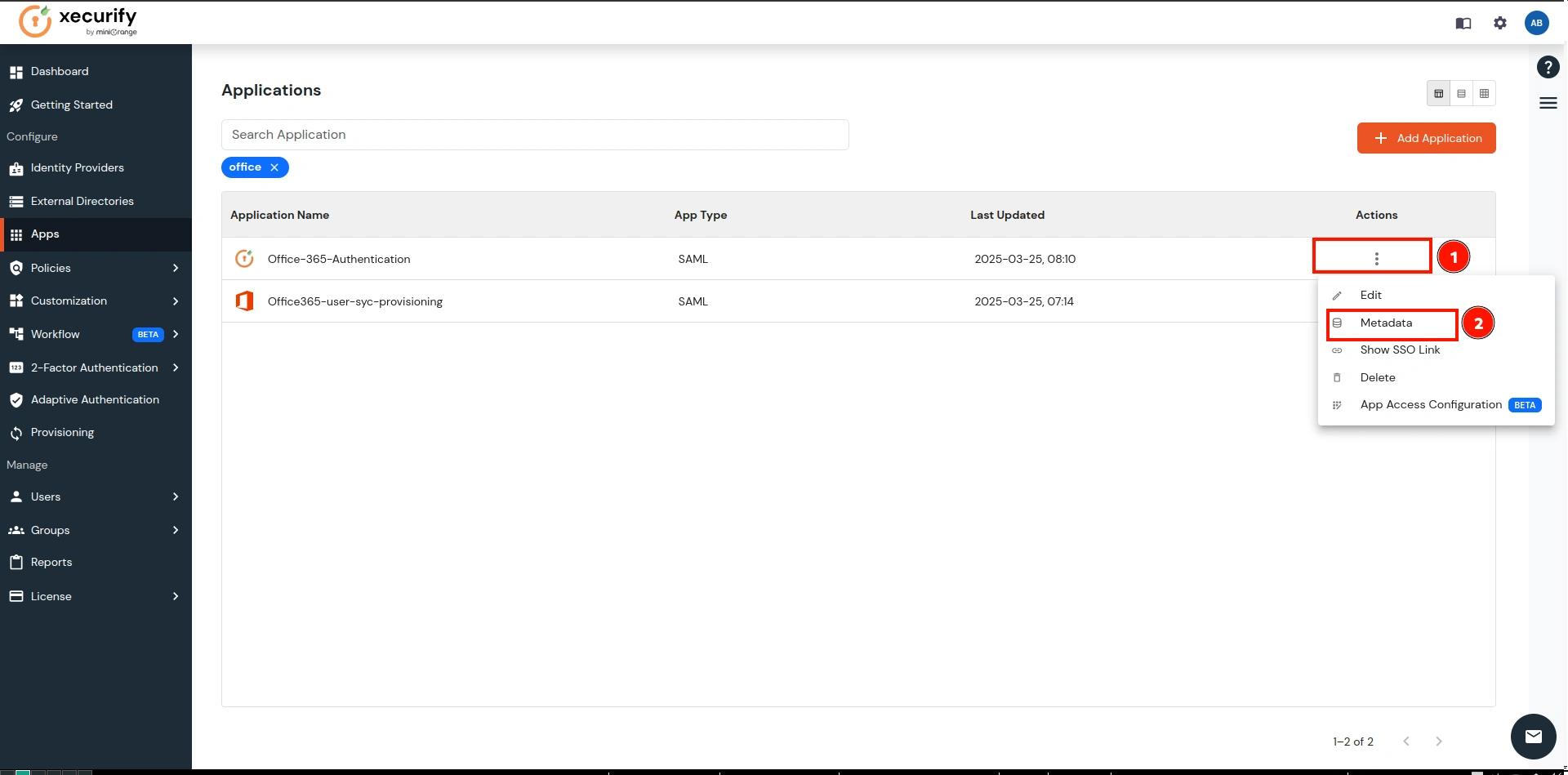
- Navigate to the newly created application, click on the three dots under the Action column, and select the Metadata option.
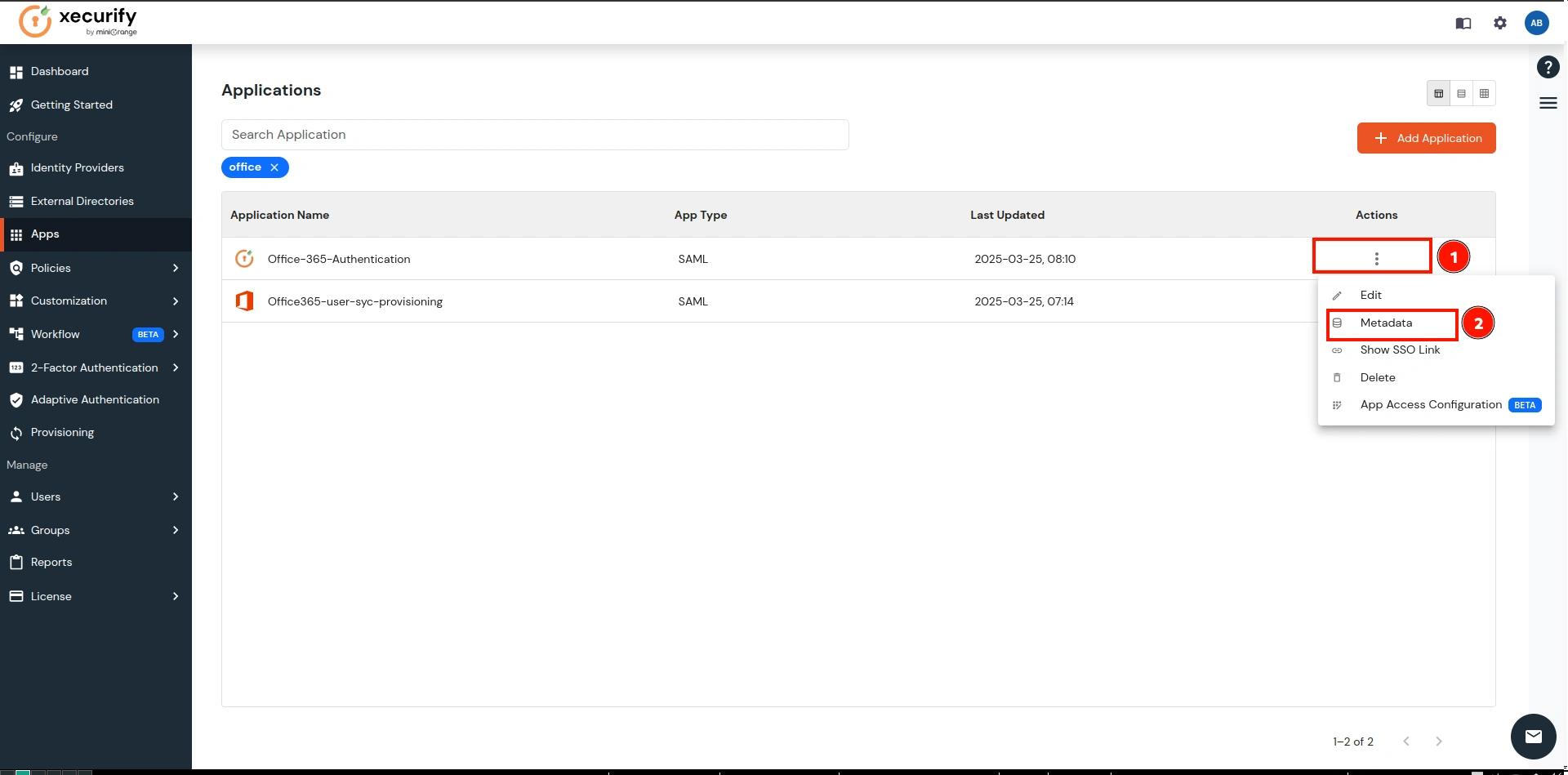
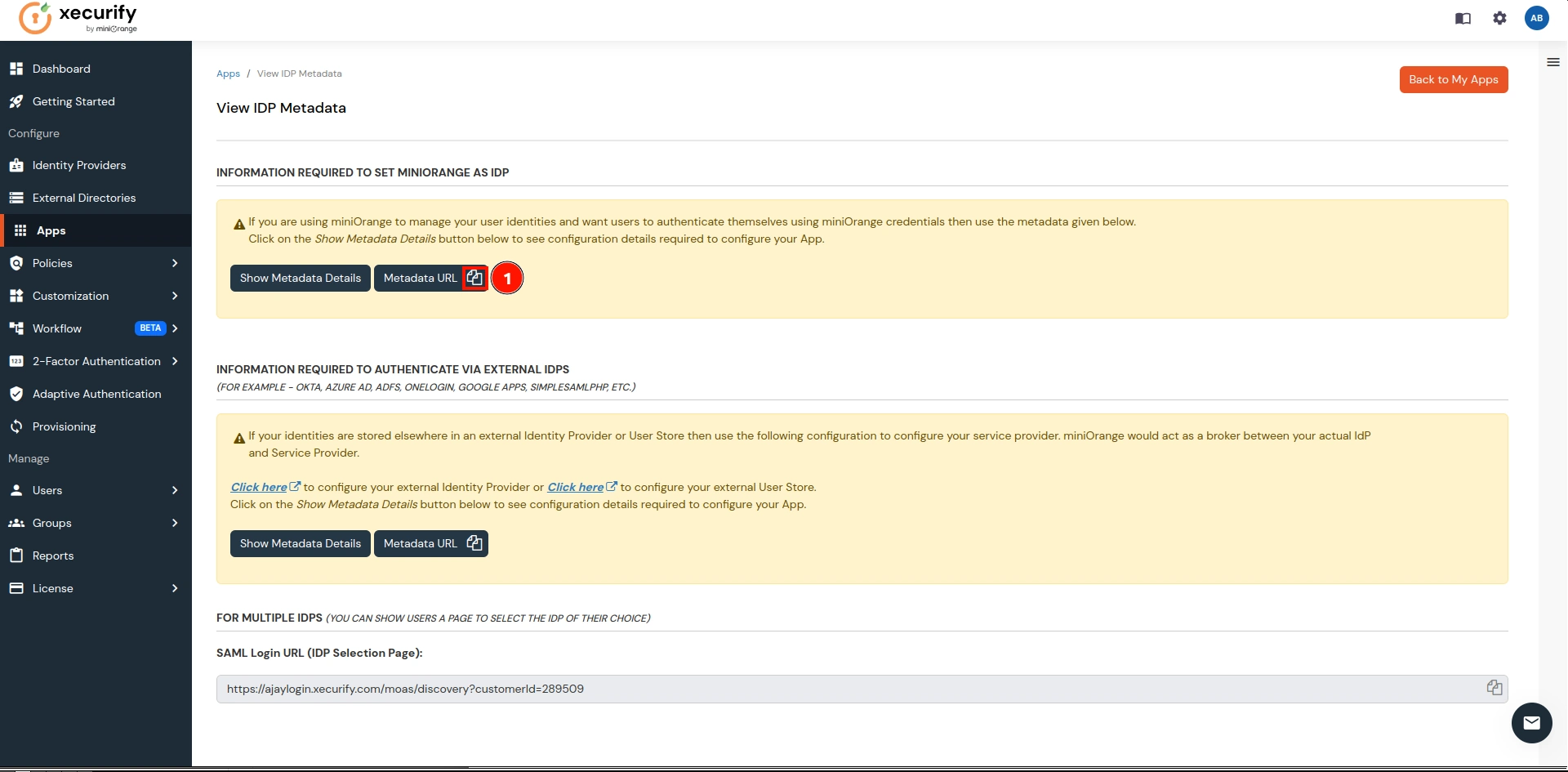
- Copy the Metadata URL and return to the CASB Dashboard.
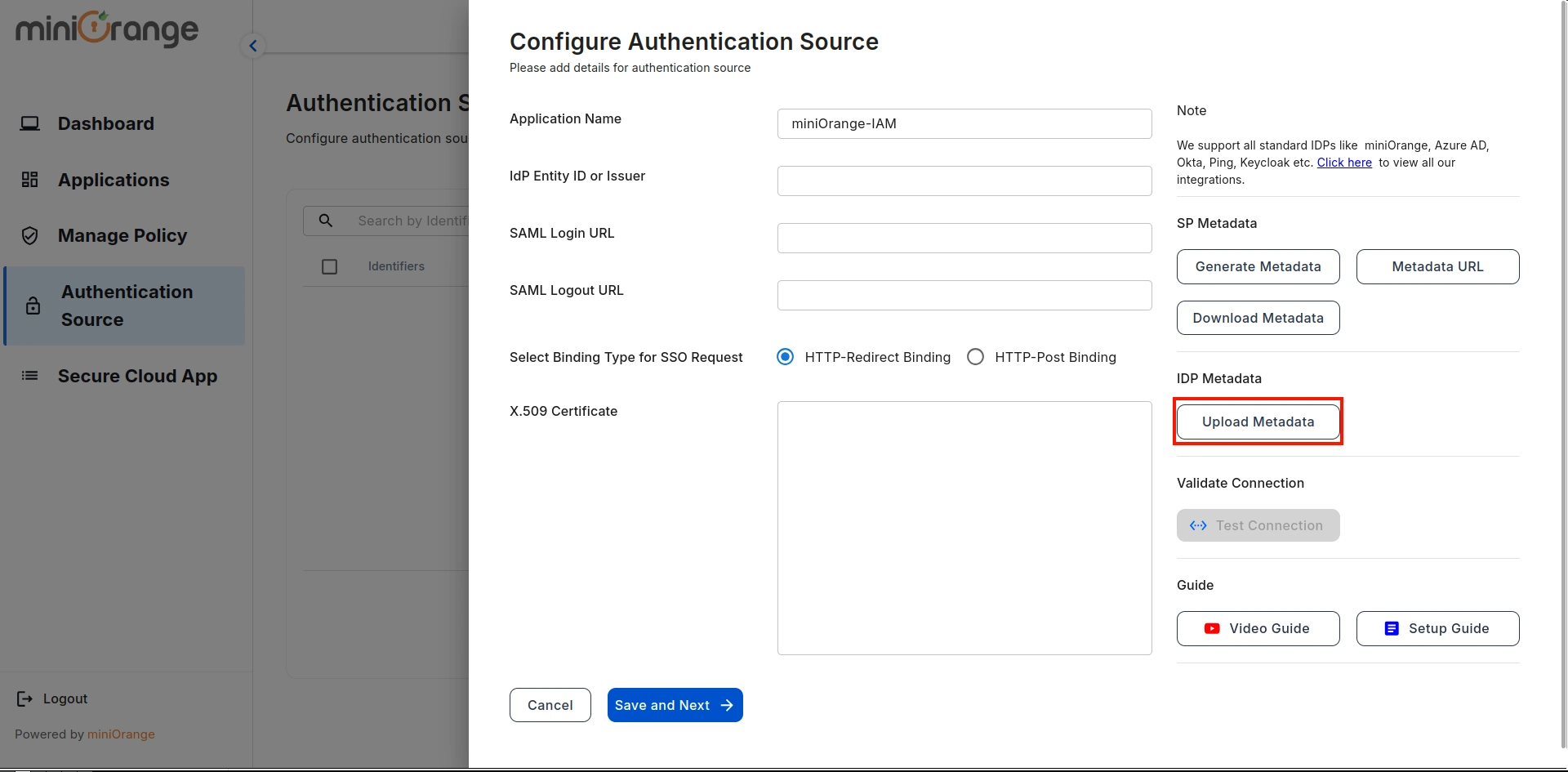
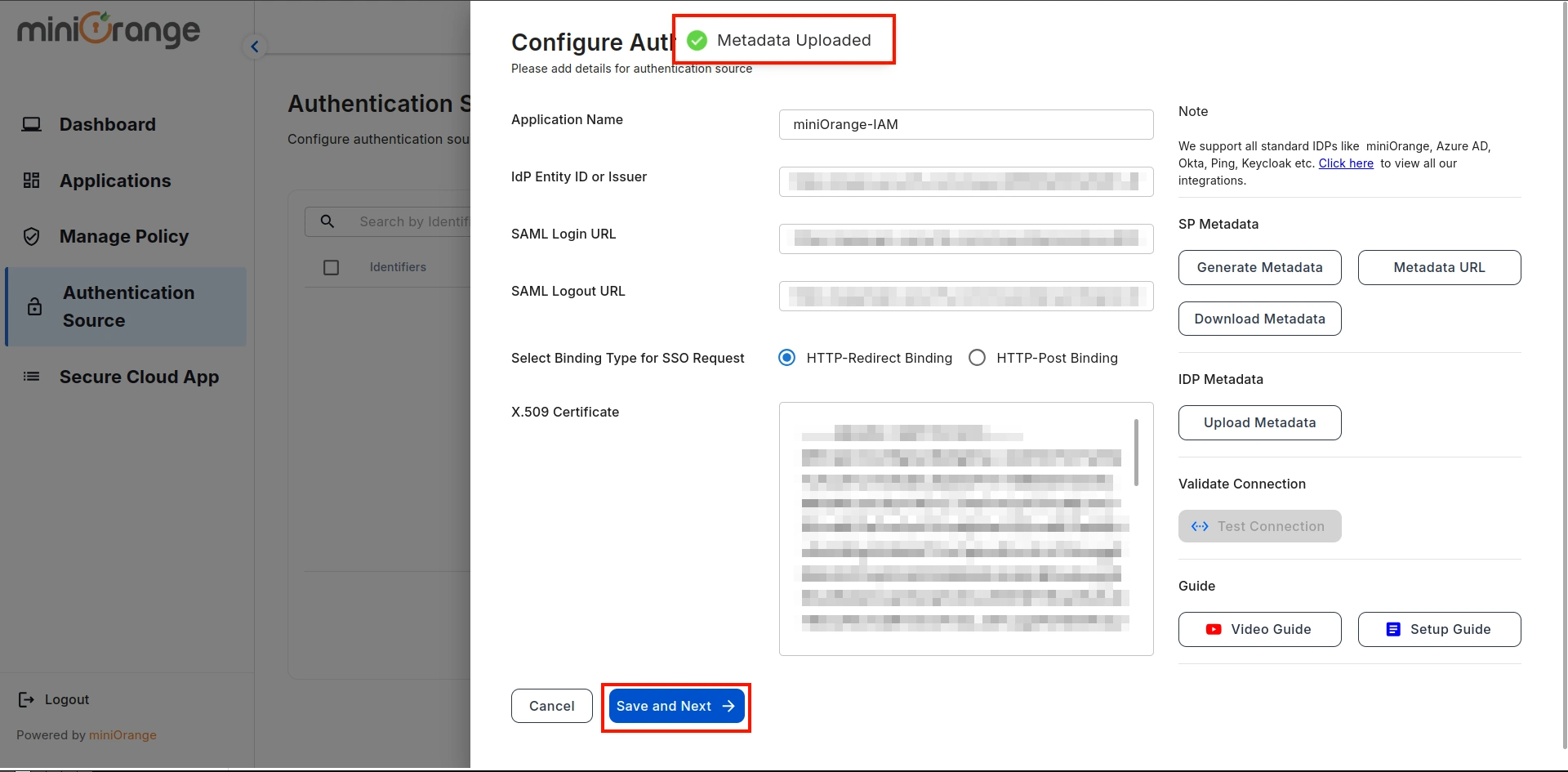
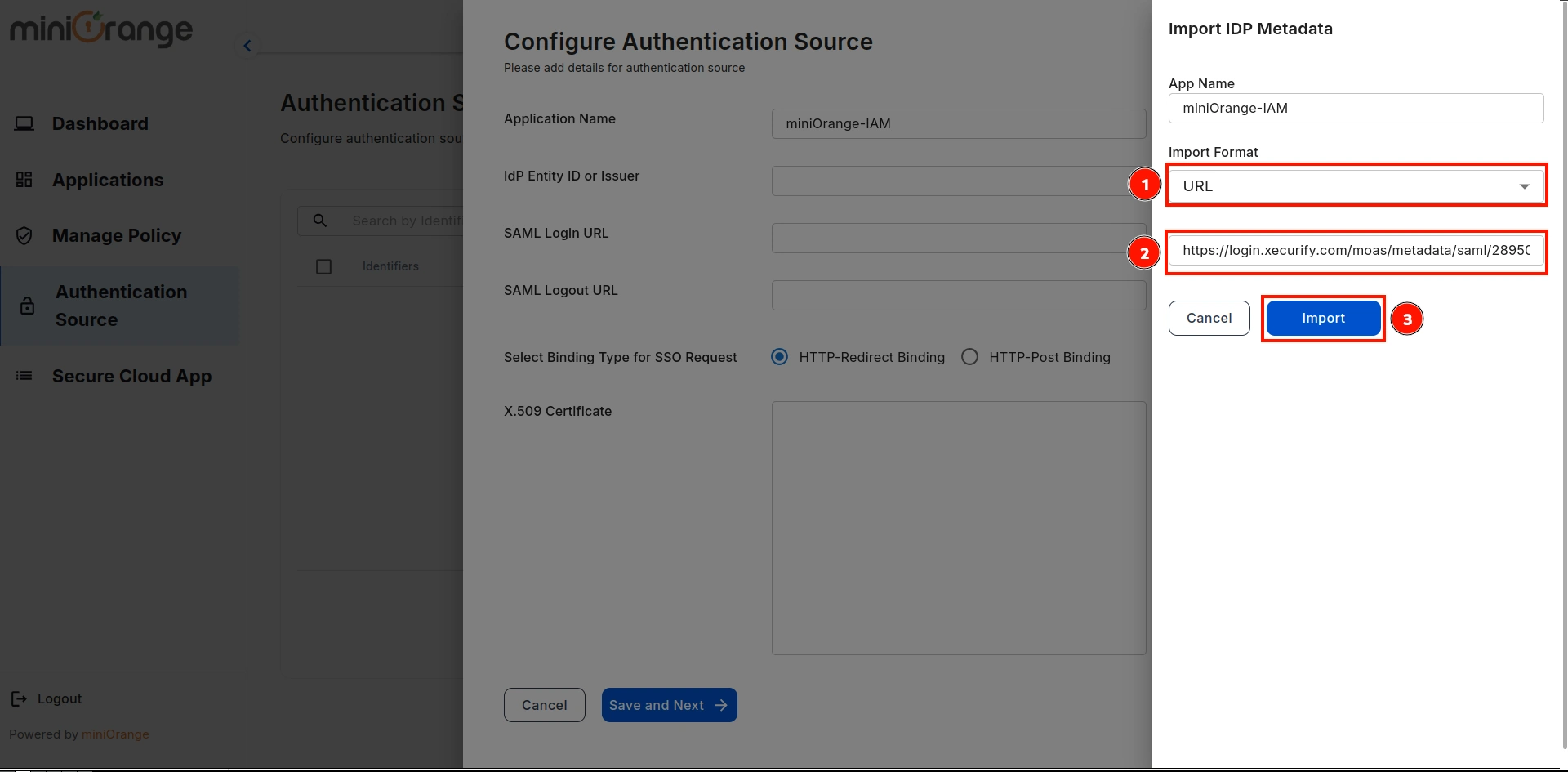
- On the CASB Dashboard, go to Authentications Source and click on the Upload Metadata option.
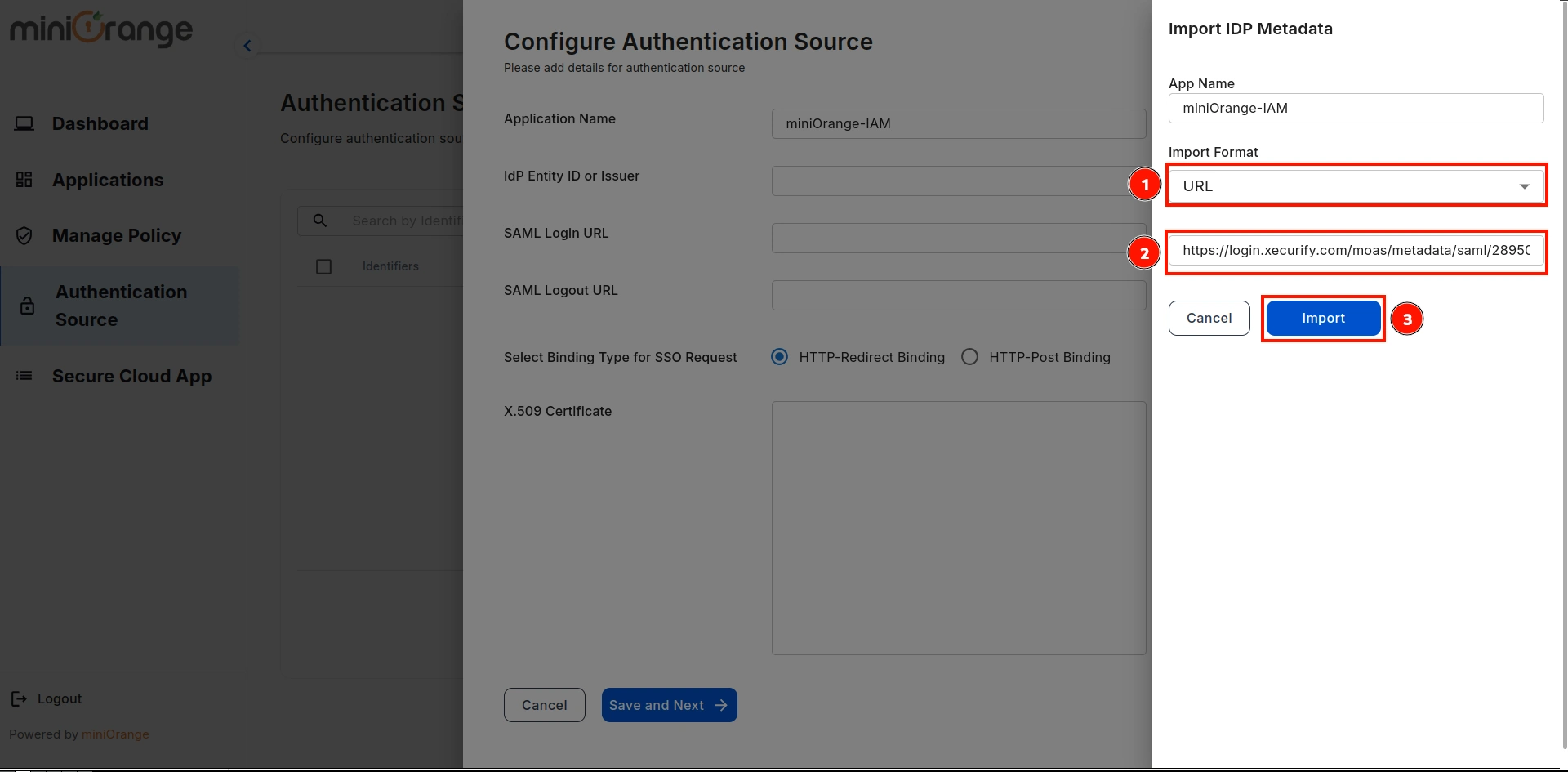
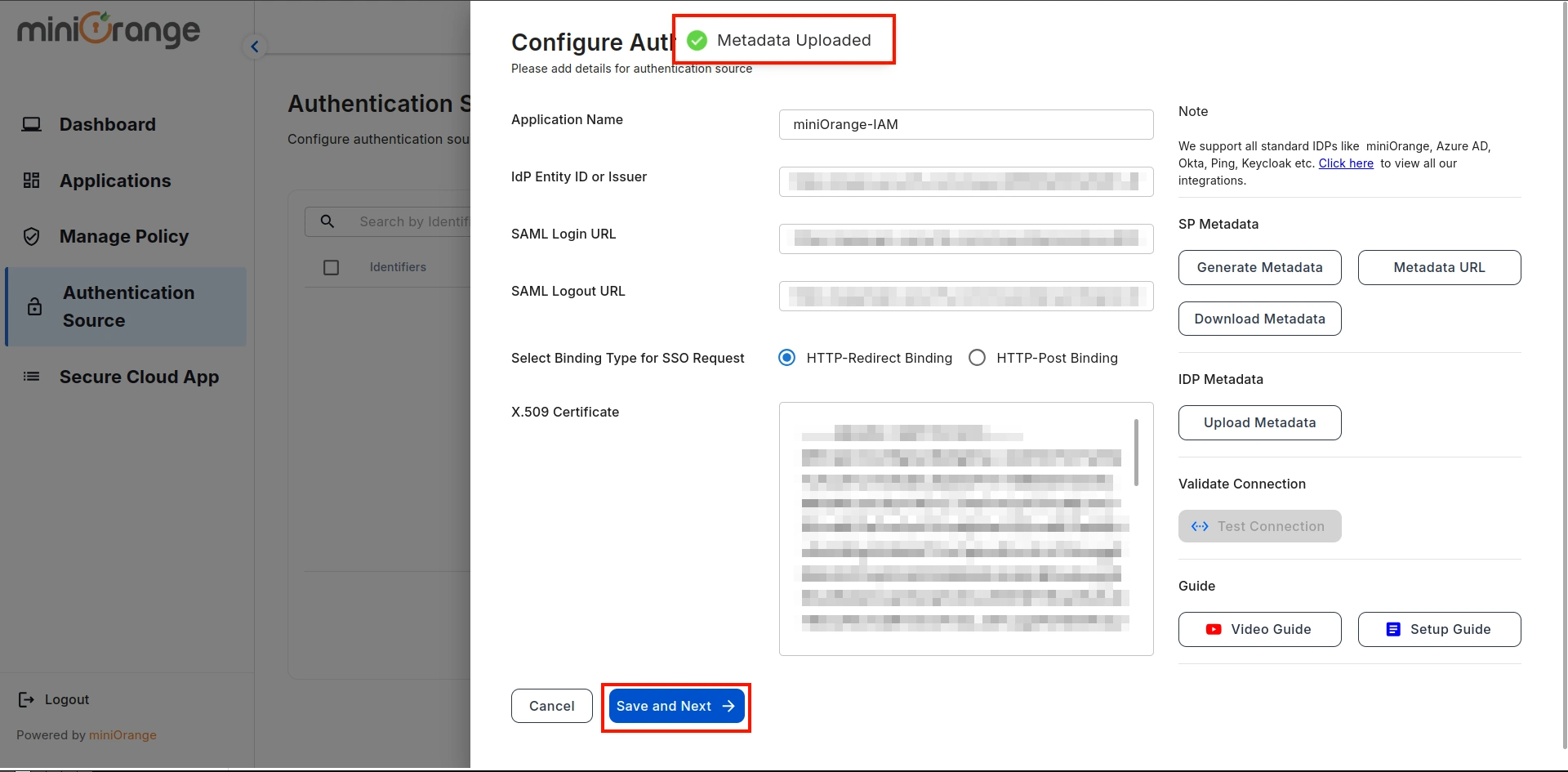
- Select Input Format as URL, paste the copied URL, and click on Import.
- A prompt will confirm that the metadata has been uploaded successfully. Click on the Save button to save the Authentication Source.
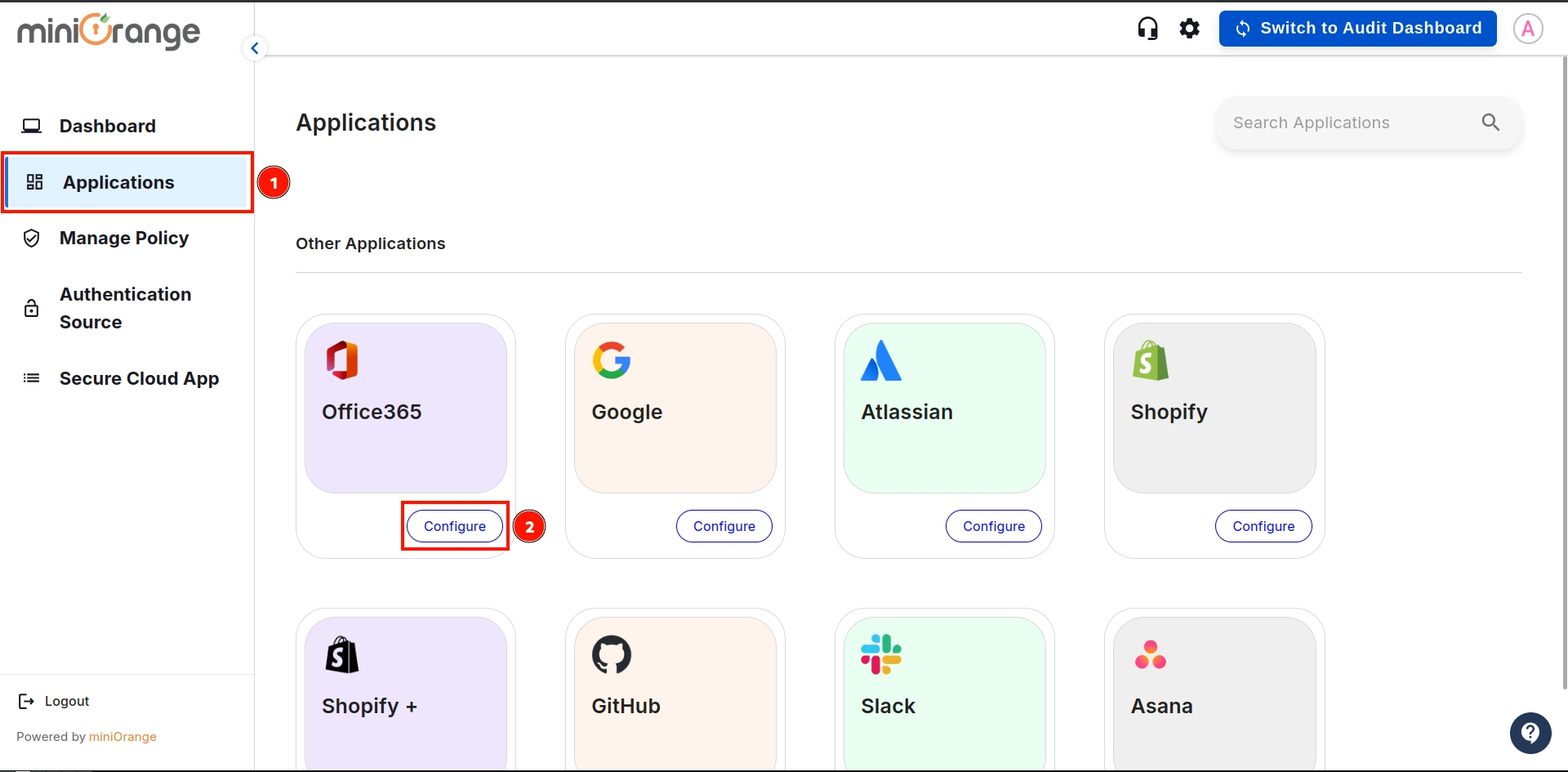
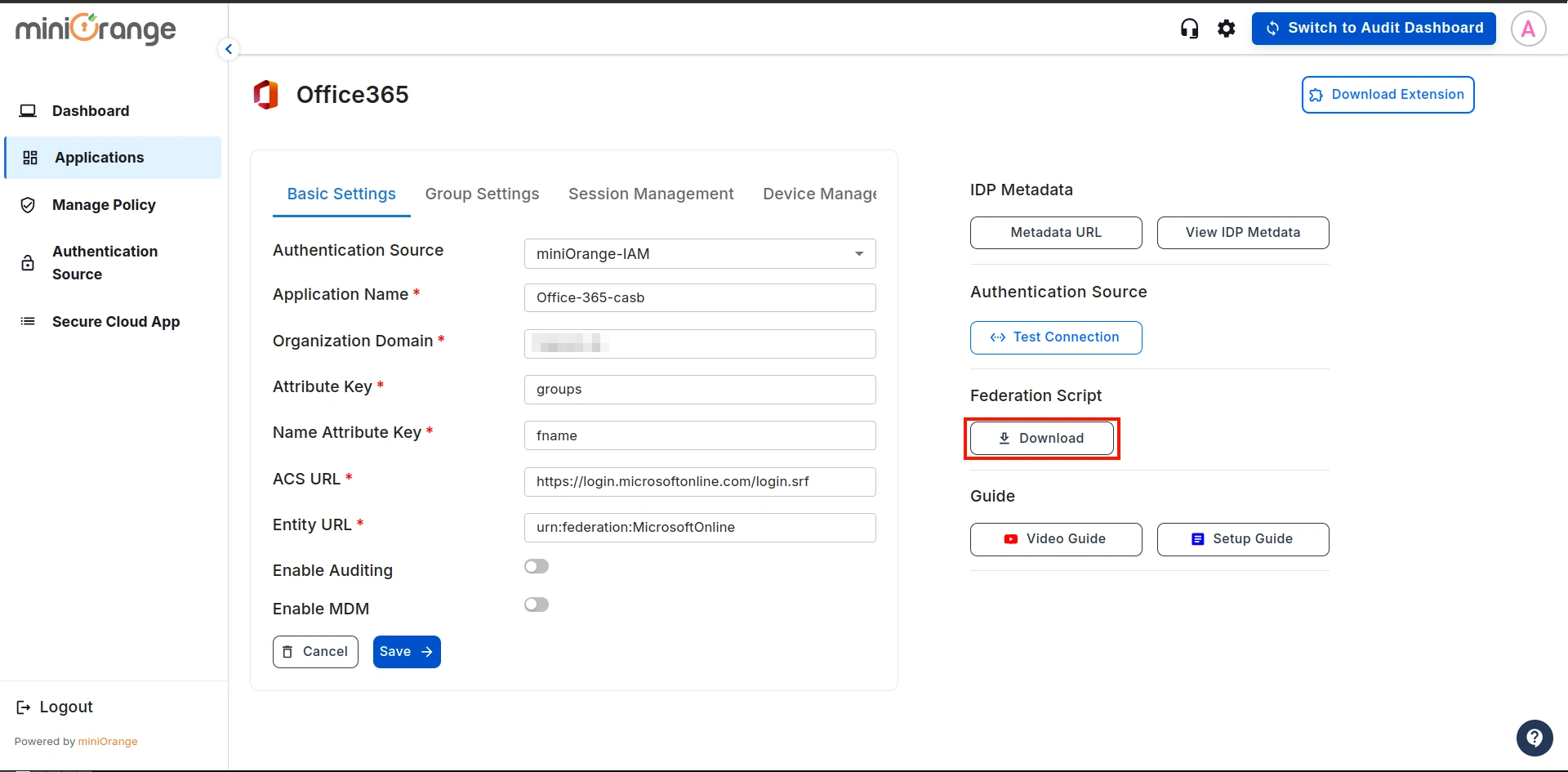
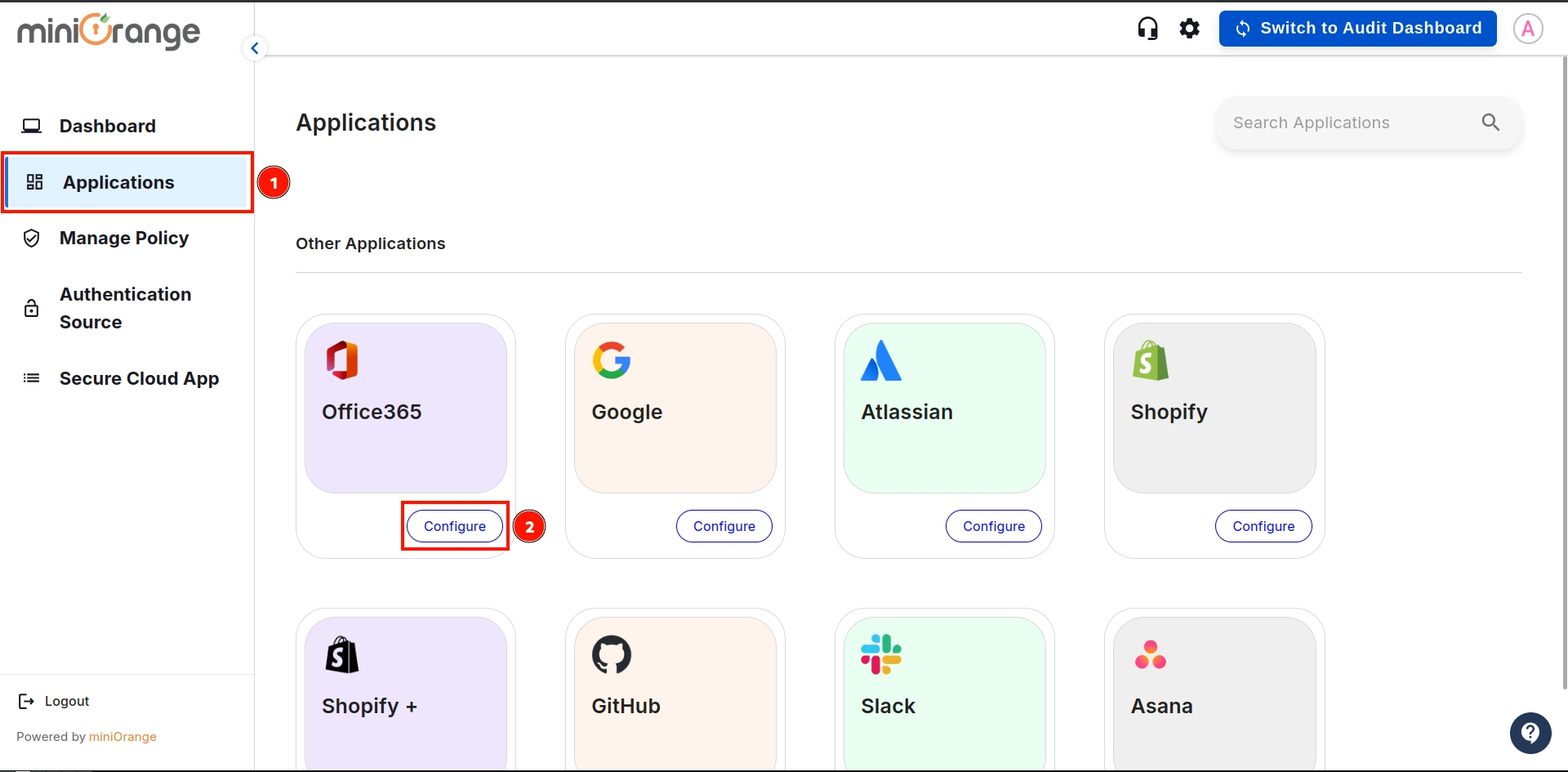
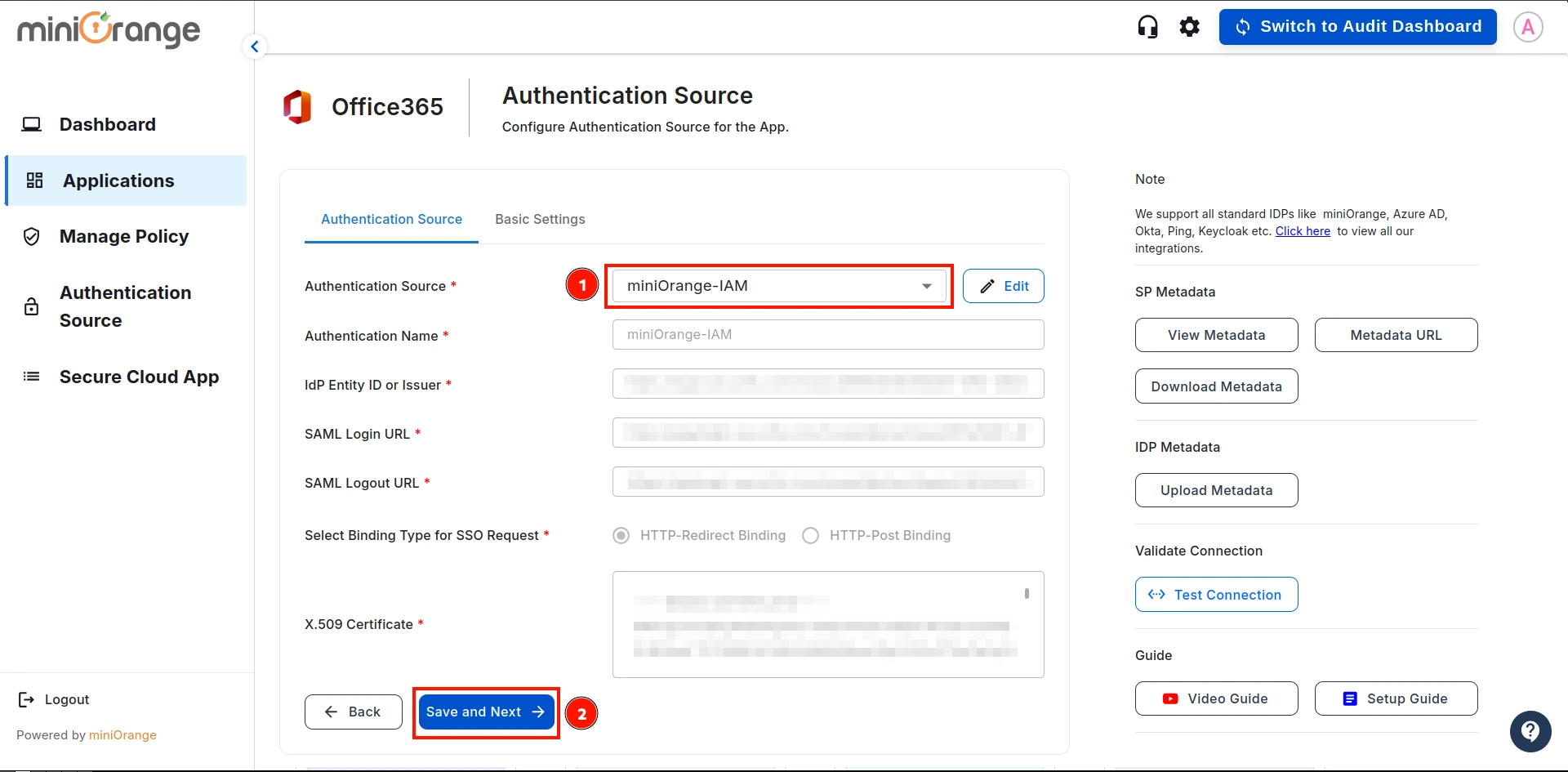
4. Configure Microsoft Office 365 in CASB
- Navigate to Applications on the sidebar, go to Office 365, and click on the Configure button.
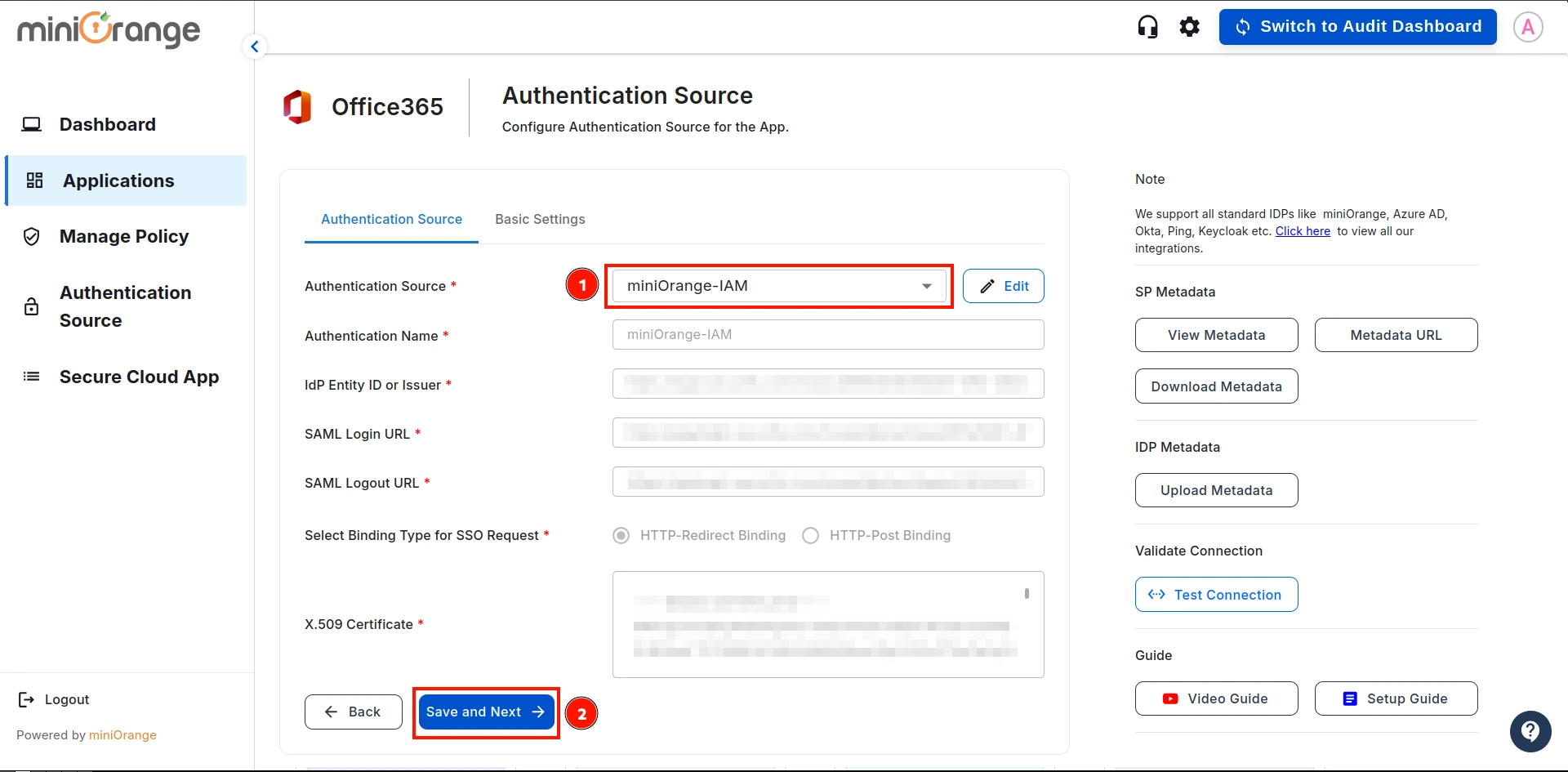
- Select the Authentication Source from the dropdown that we created in the previous step, then click on Save and Next.
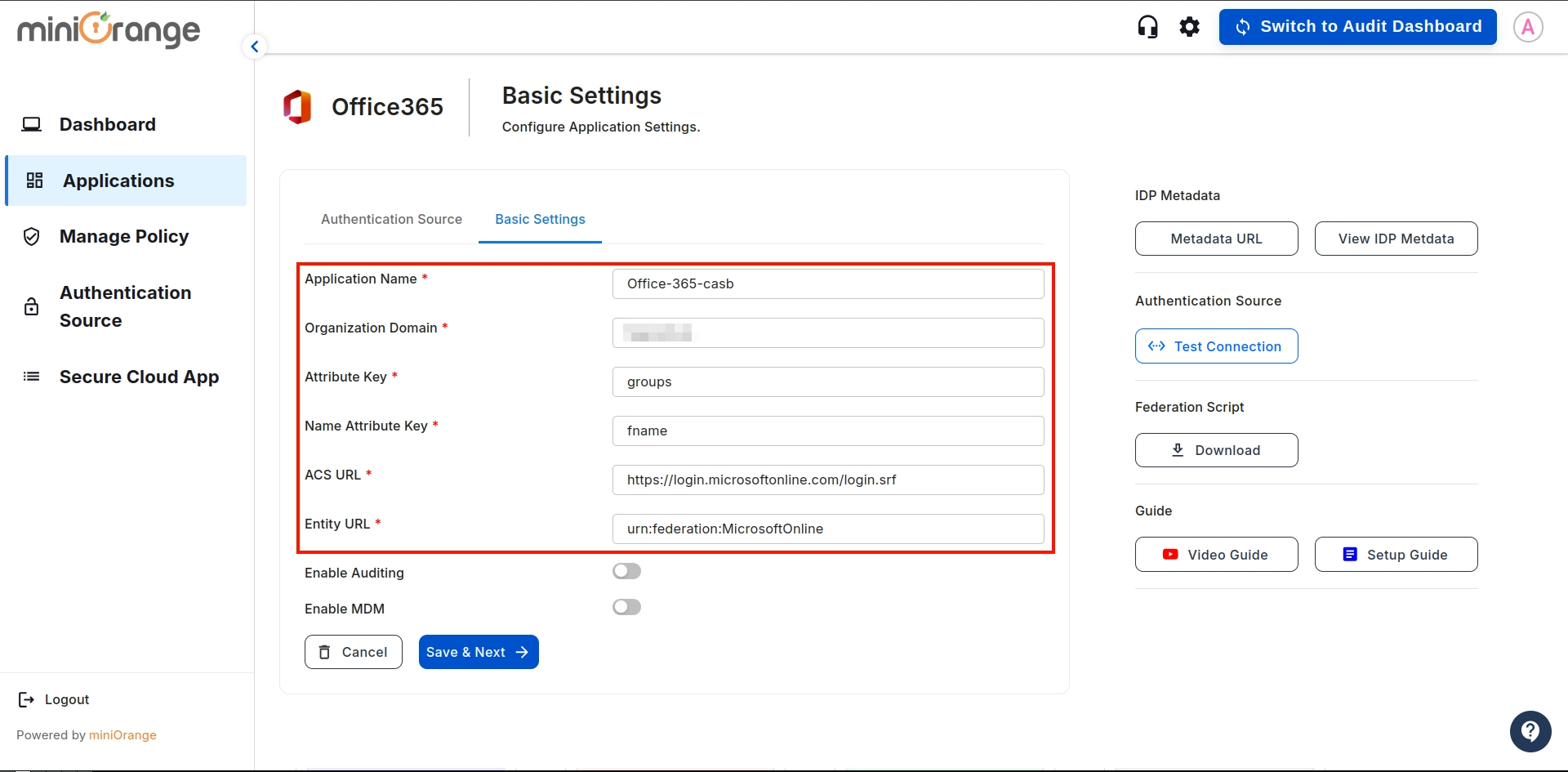
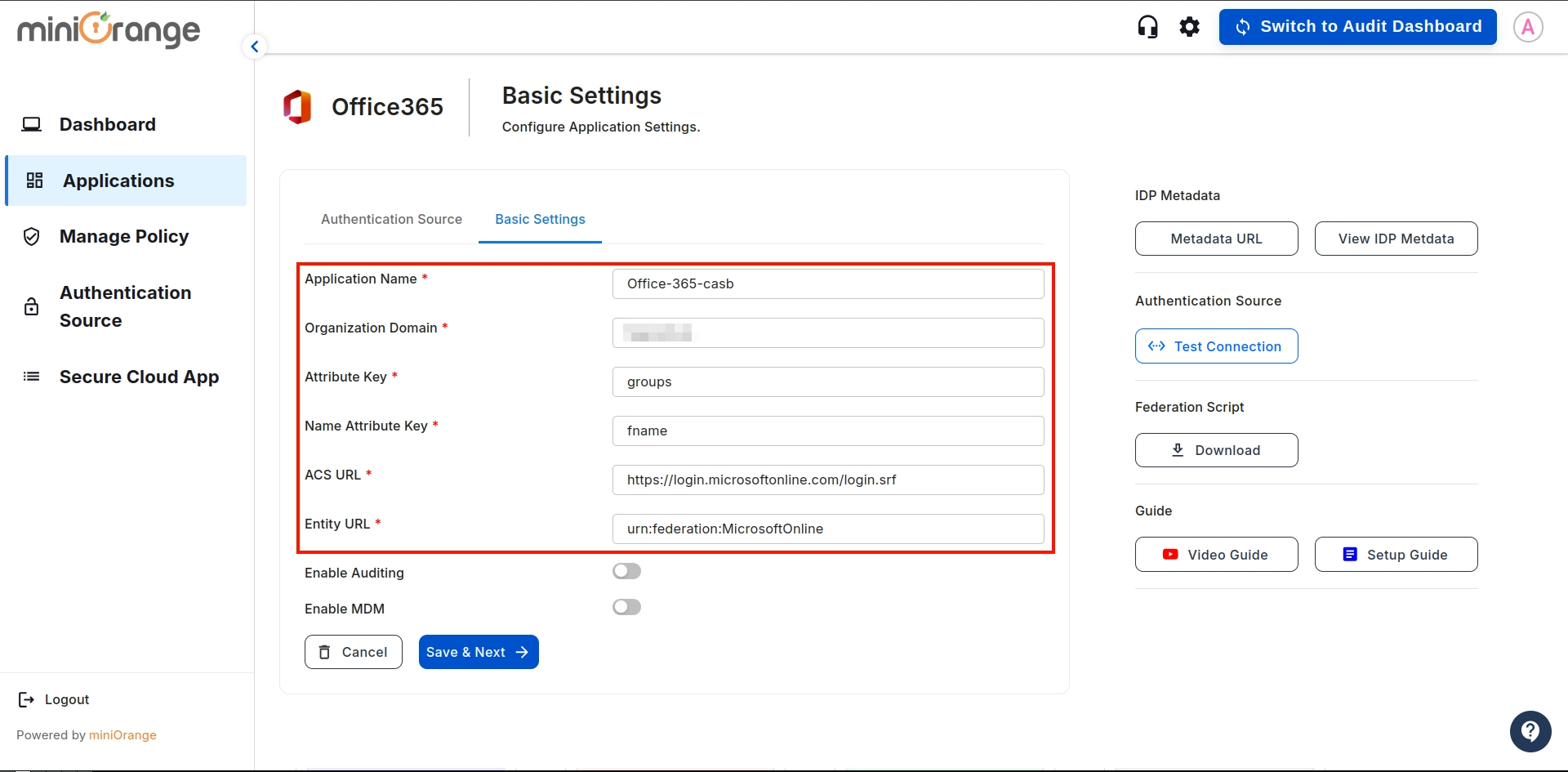
- Configure the following details and click on the Save button:
| Application Name: |
Enter the name of your application |
| Organization Domain: |
Enter the domain of your organization. (Ex: example.com)
|
| Attribute Key: |
Enter the Group Attribute Key for the SSO app, which you have configured in the IDP under
the SAML attributes section.
|
| Name Attribute Key: |
Enter the attribute name like fname,Lname etc.
|
| Enter ACS URL: |
Enter the office365 ACS URL as : https://login.microsoftonline.com/login.srf |
| Enter Entity URL: |
Enter the office365 Entity URL as : urn:federation:MicrosoftOnline |
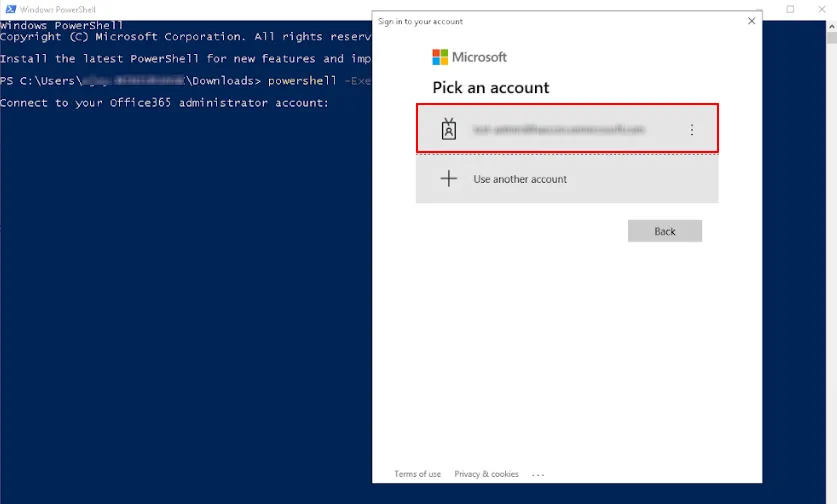
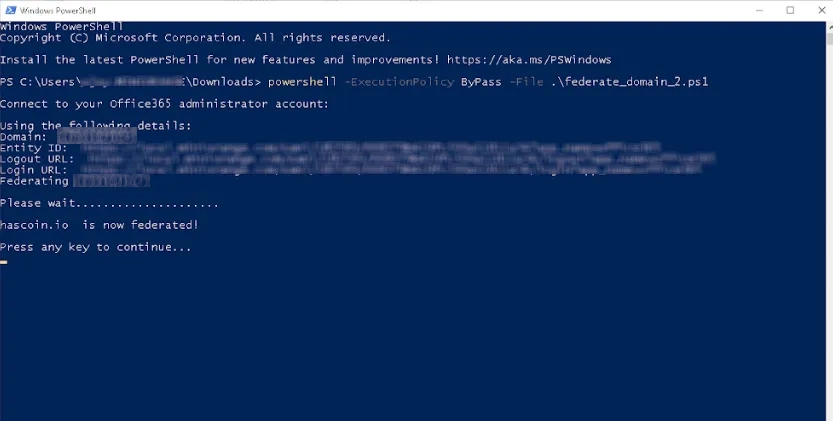
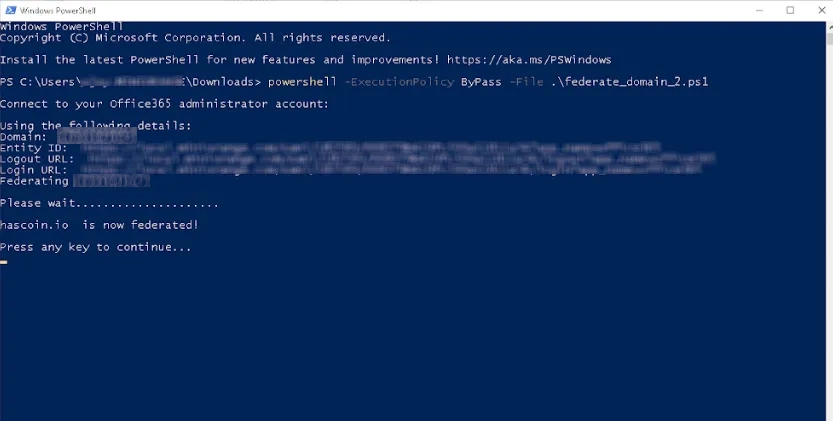
- Once everything is configured, download the federation script.
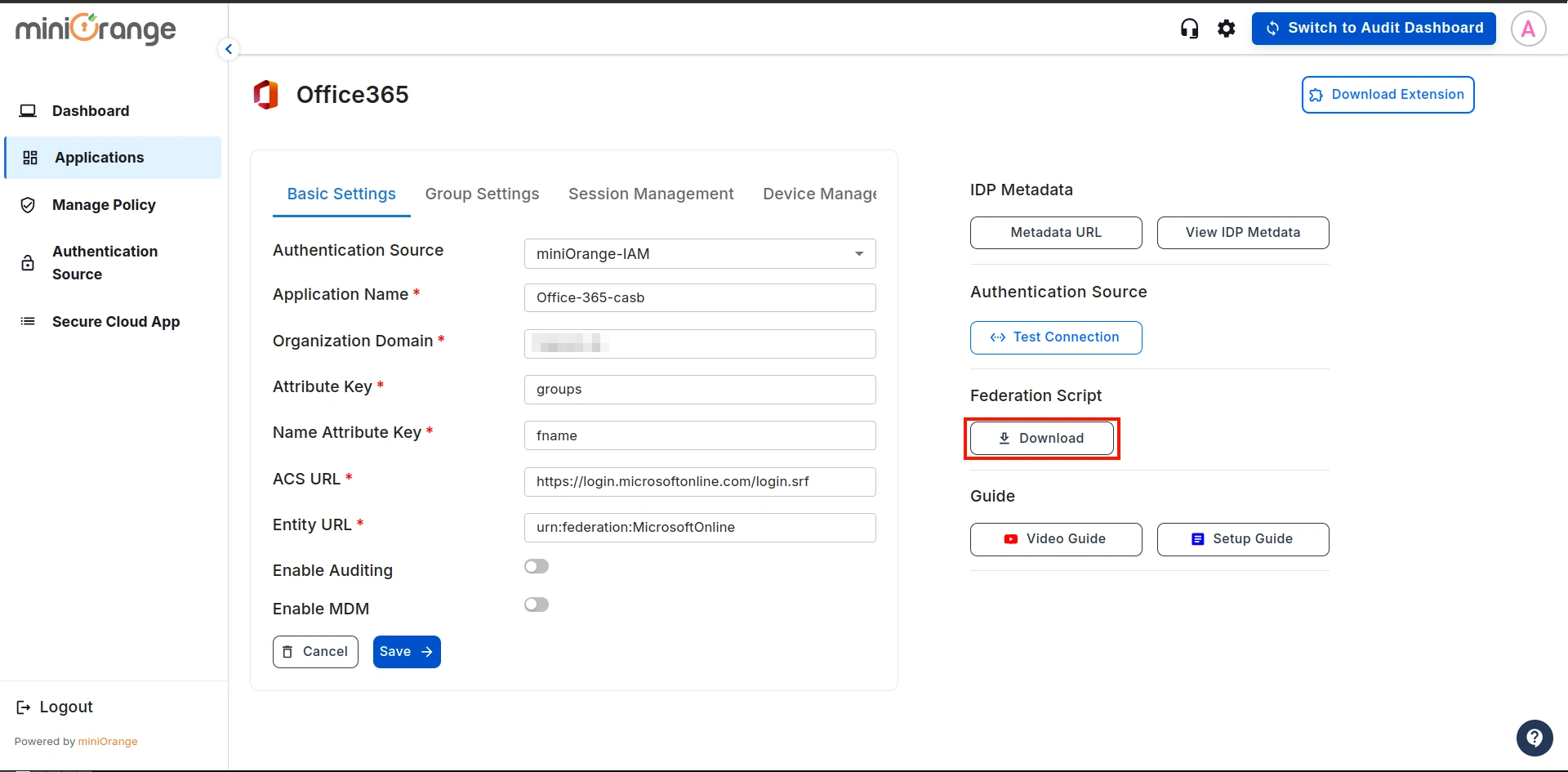
- Note: Run the downloaded federation script using the following command:
powershell -ExecutionPolicy ByPass -File [Your File Name].ps1
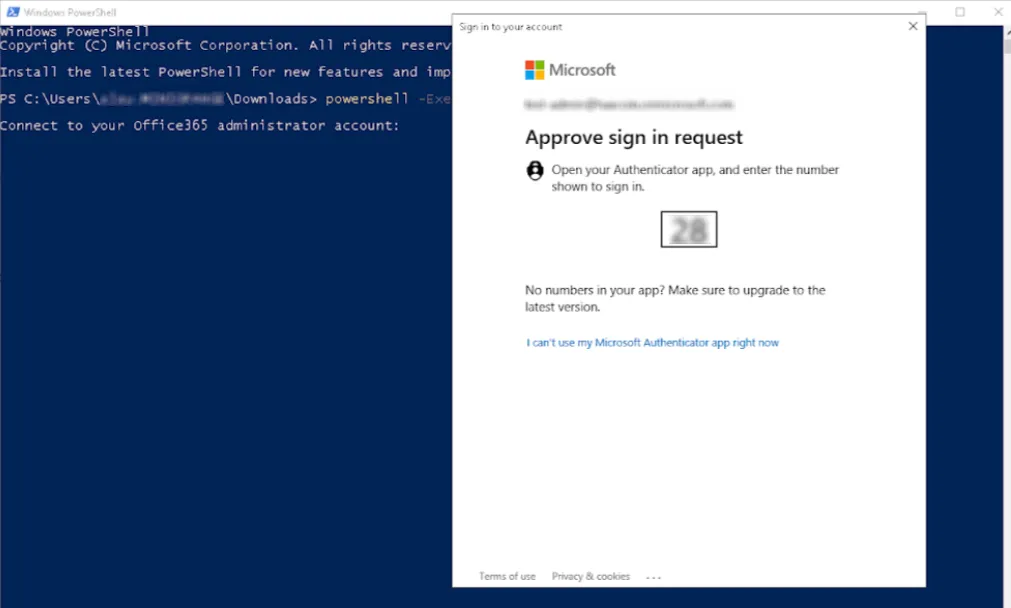
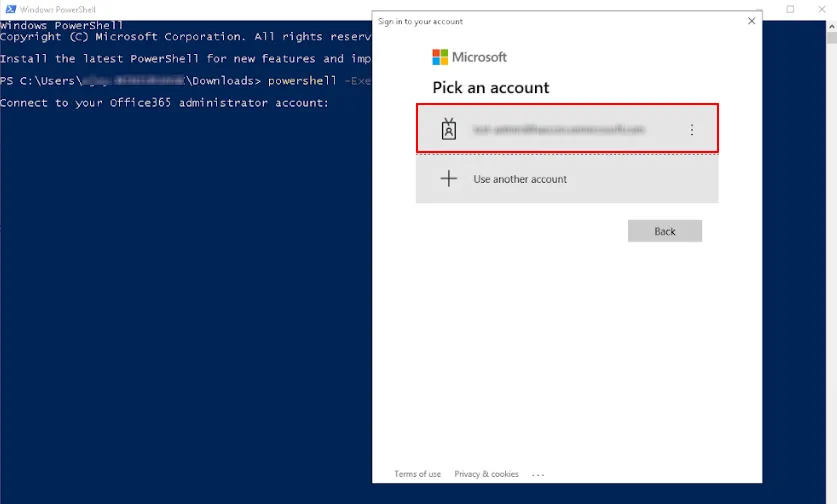
After running the command in Windows PowerShell, a pop-up will appear and Enter your Office365 Admin
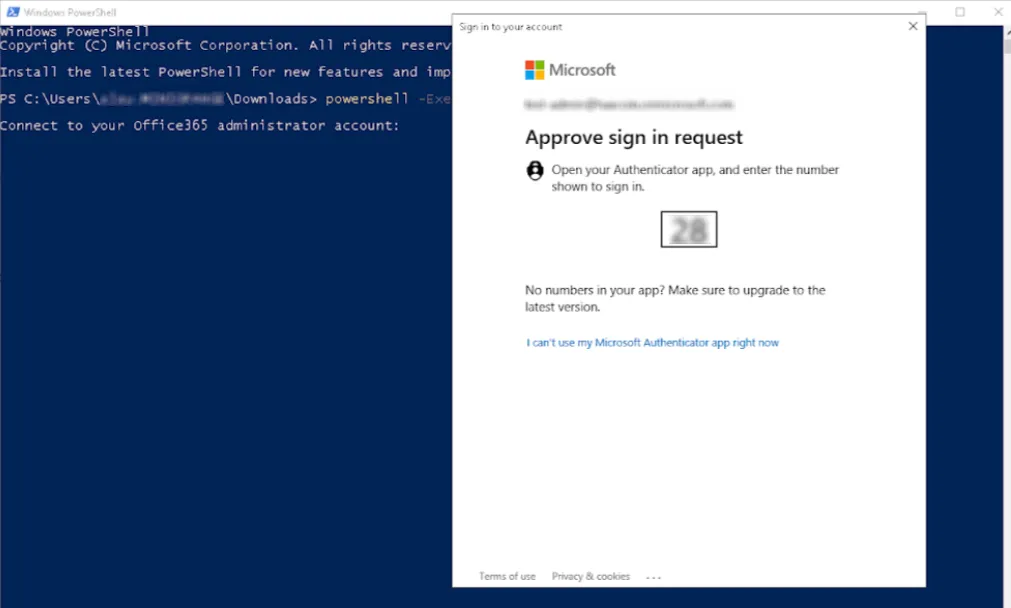
account credentials.
Open your authenticator app and enter the displayed number to approve the sign-in request.
The federation script successfully completed, as shown in the image below.
5. Configuring Policies and Groups
Let's see how to configure policies and groups for Office365 CASB.
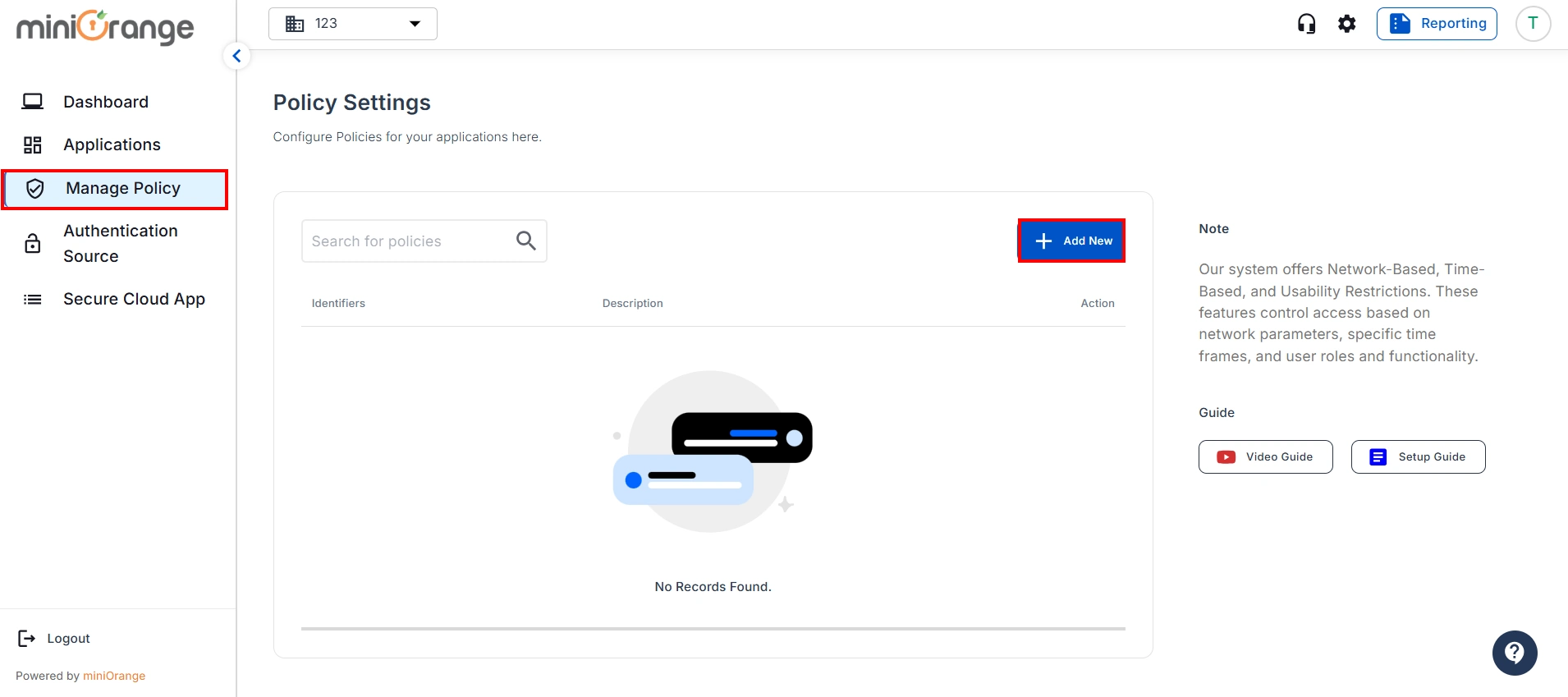
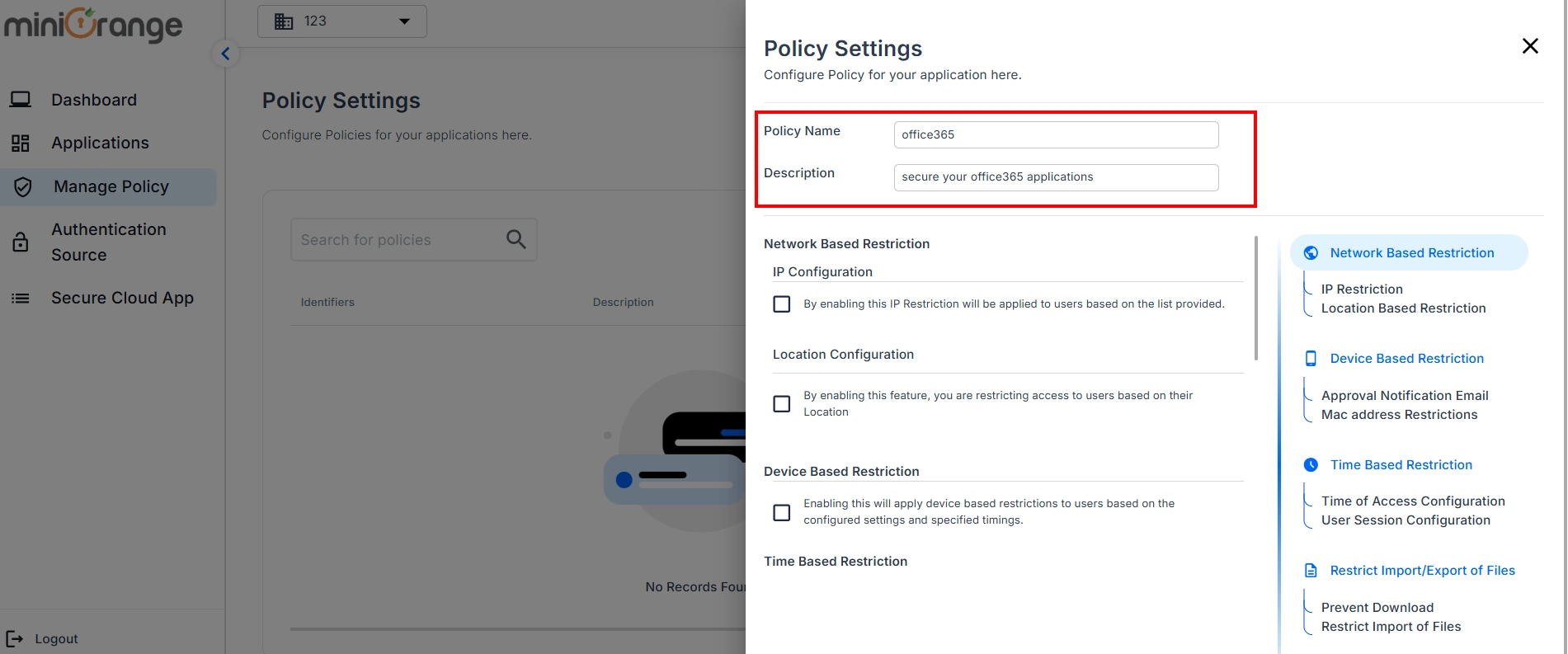
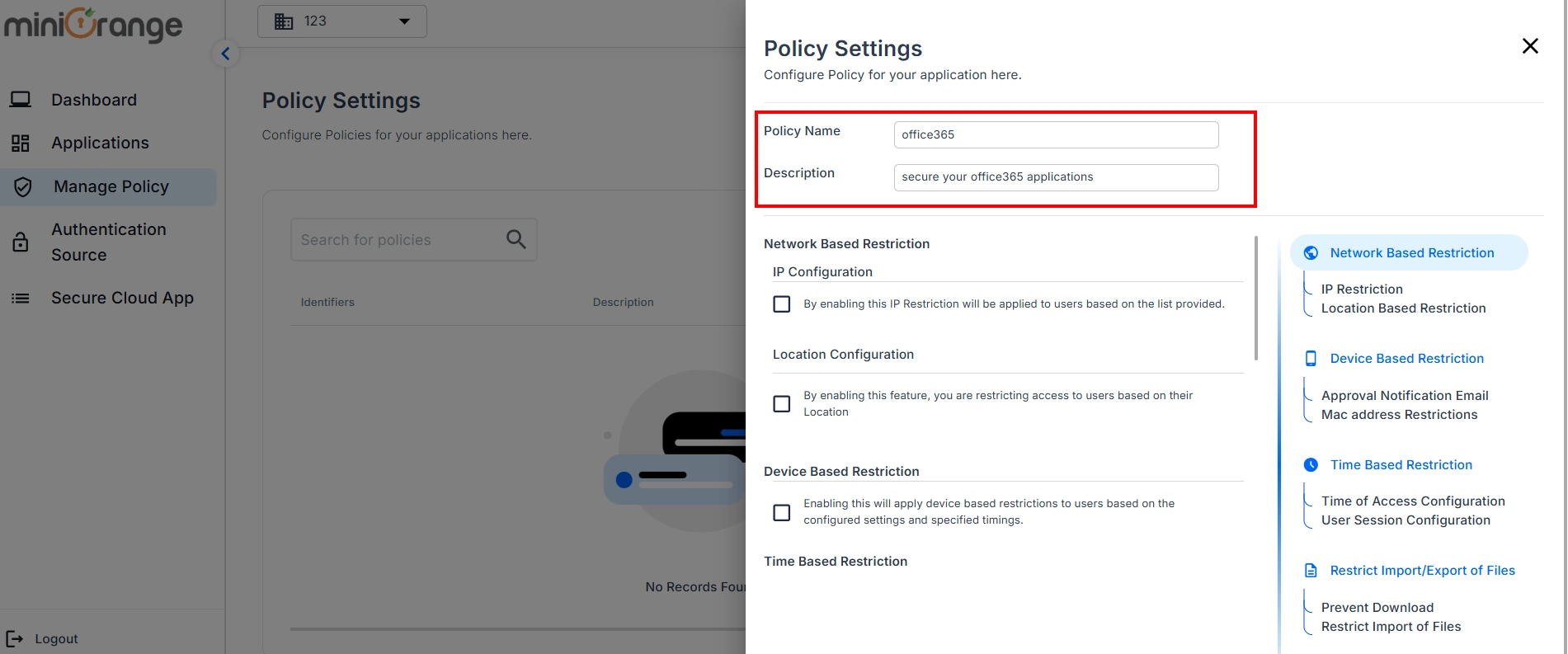
- Go to Manage Policy screen and click on Add New button.
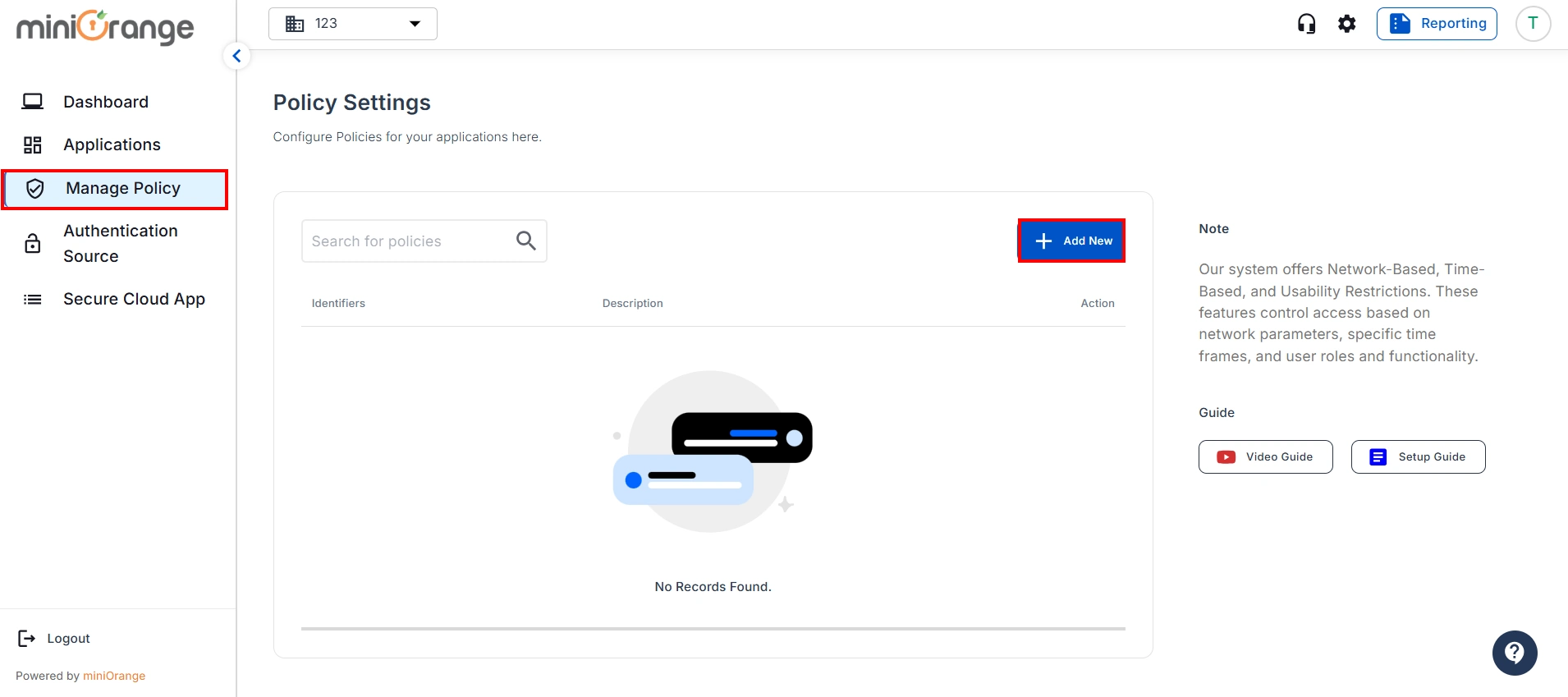
- Enter your policy details, like Policy Name and Policy Description.
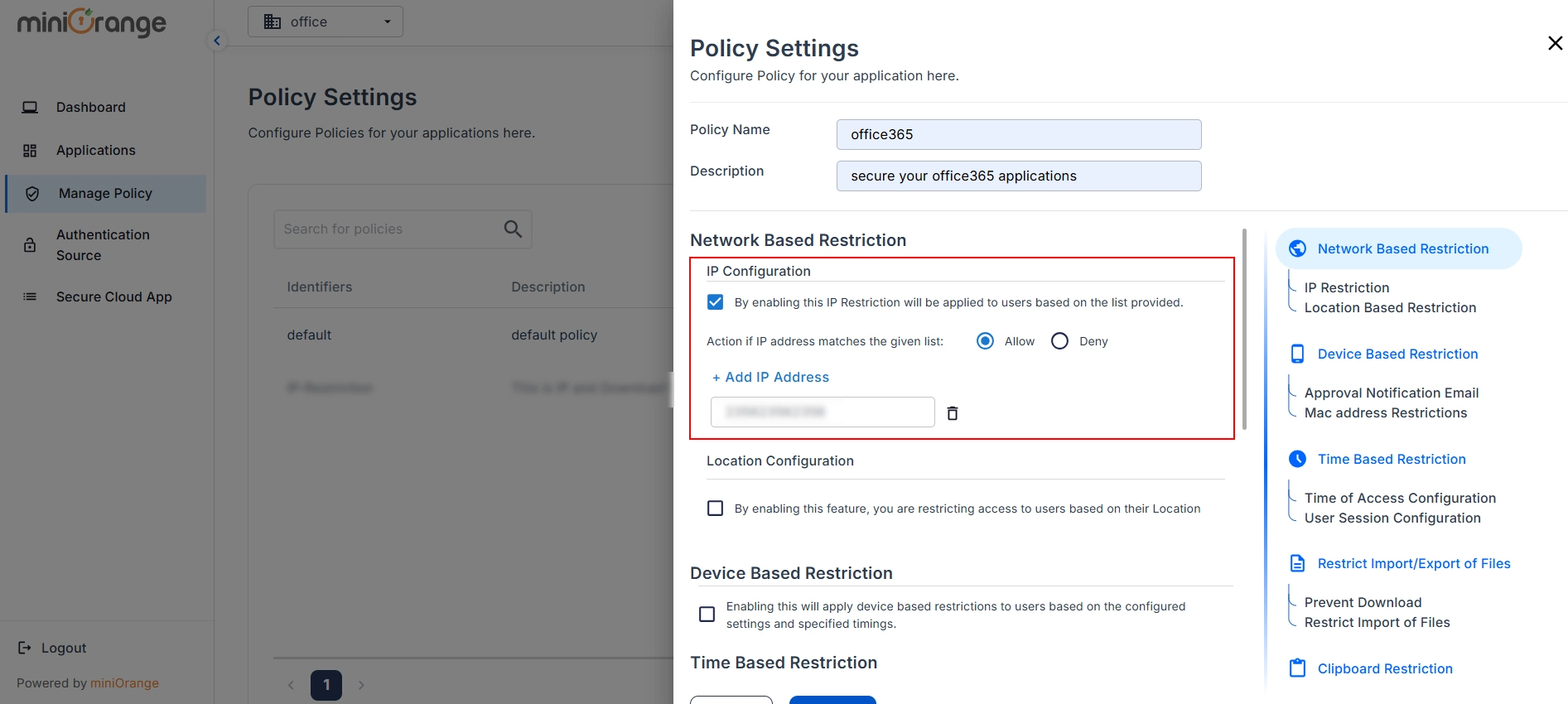
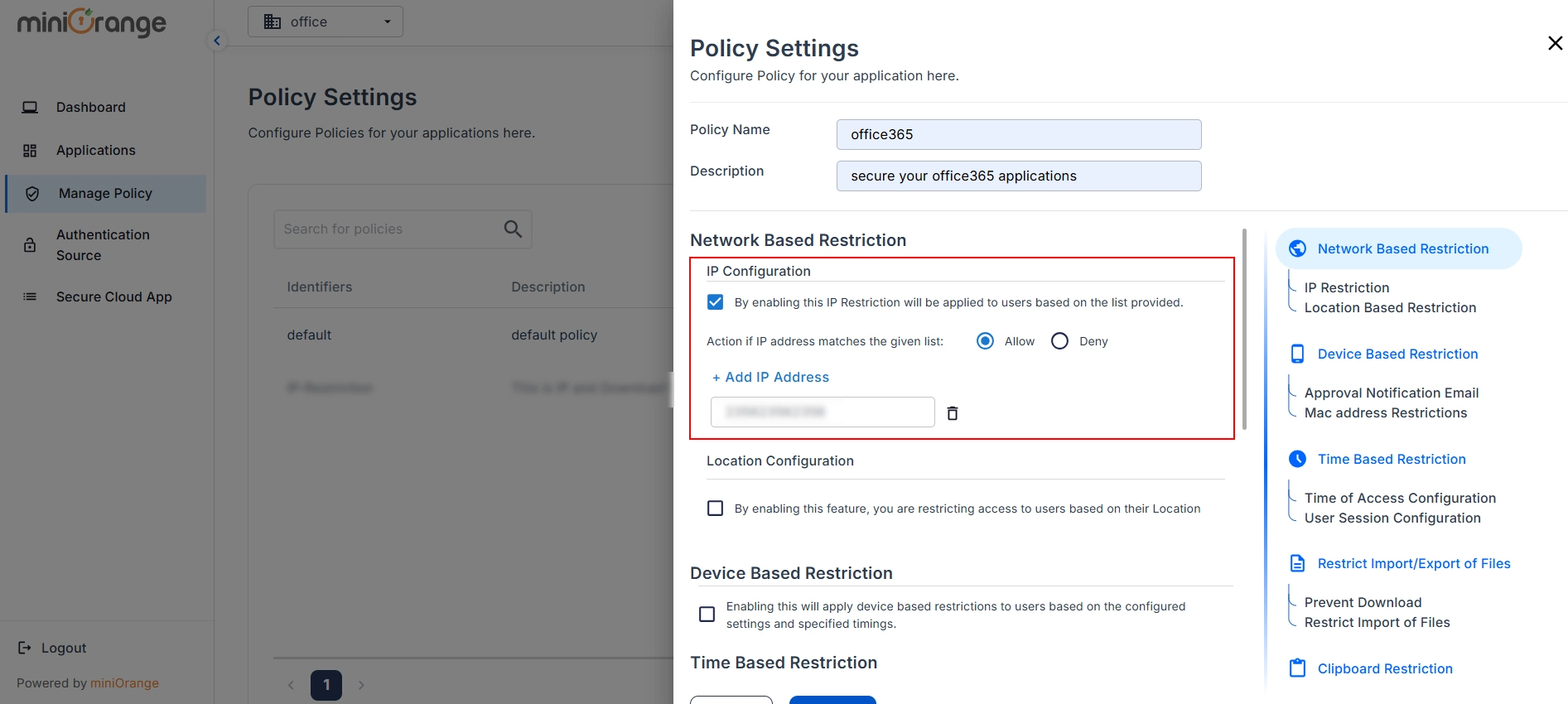
- Click on Checkbox to enable the IP Restriction as shown in the image below.
- By enabling this IP Restriction feature, you are restricting access to users based on their IP addresses:
1) Select the Allow or Deny option to either permit or restrict certain IP
addresses.
2) Click on the Add IP Address icon to create a new field where you can add the IP
addresses you want to regulate.
- Once done, click on Save button.
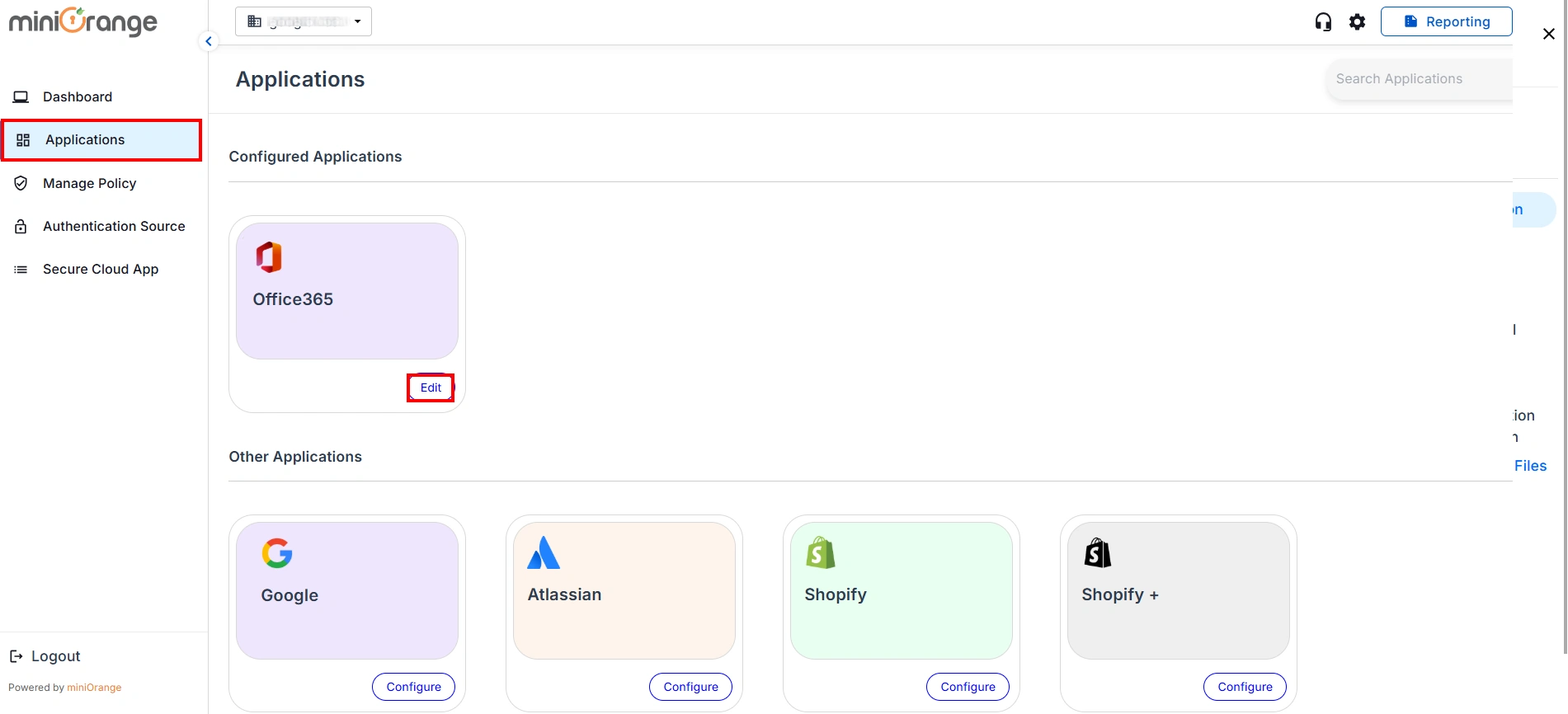
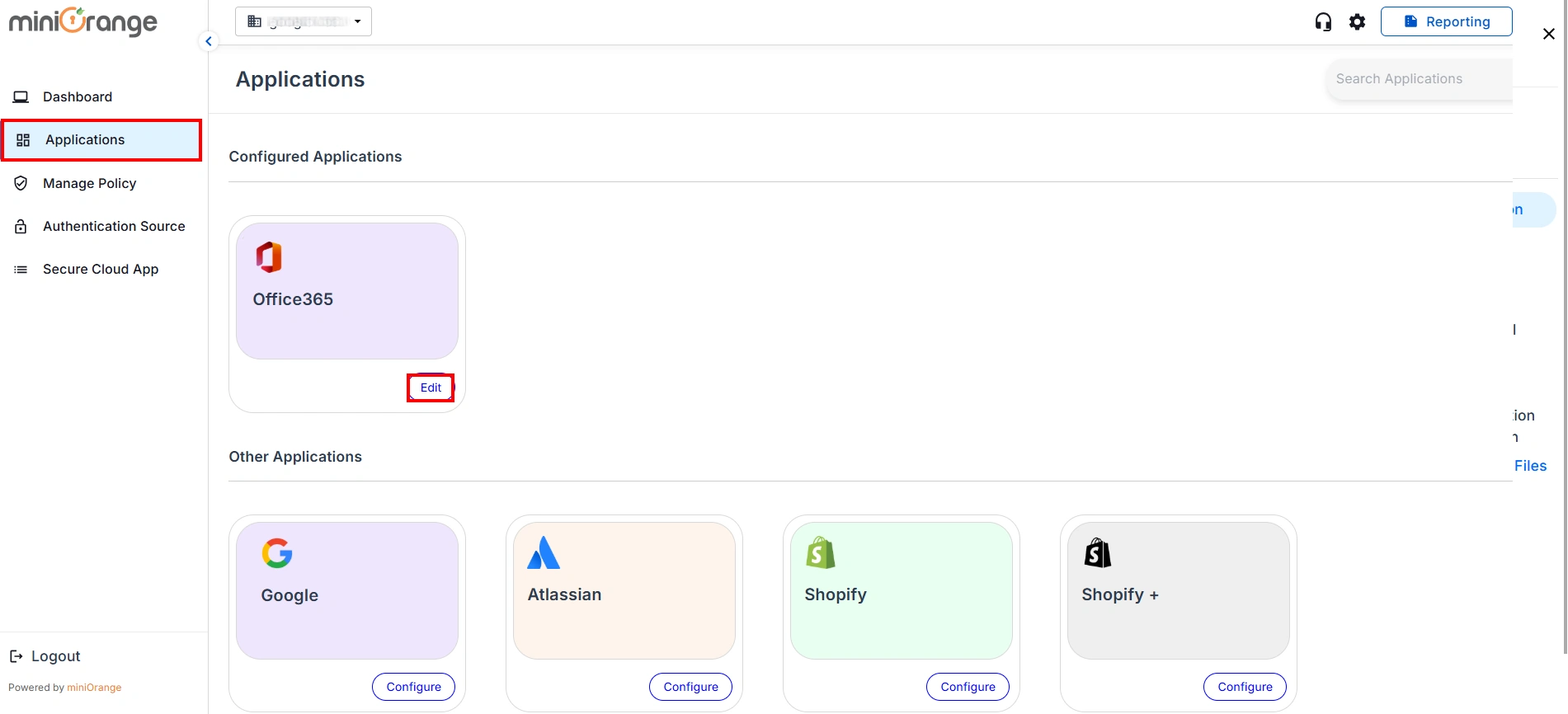
- Now, go to the Applications tab and click the Edit option for your application.
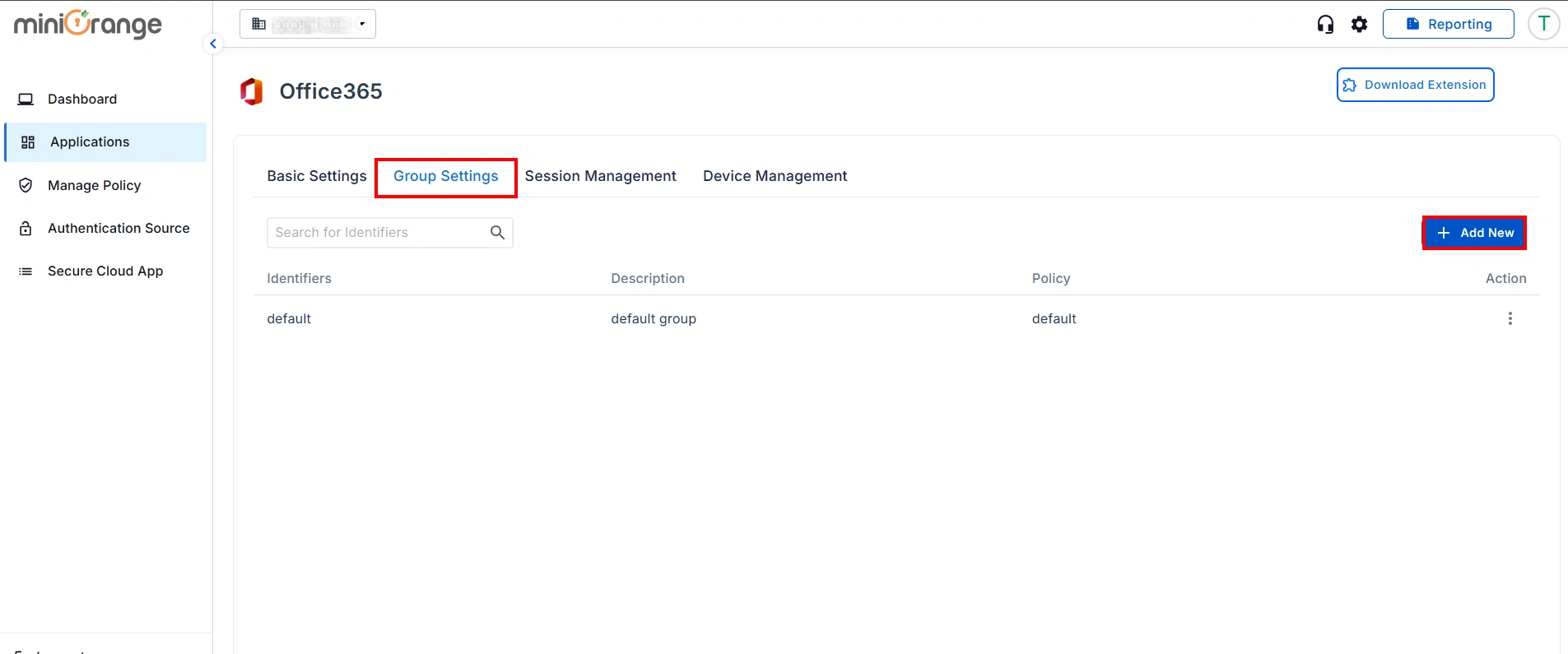
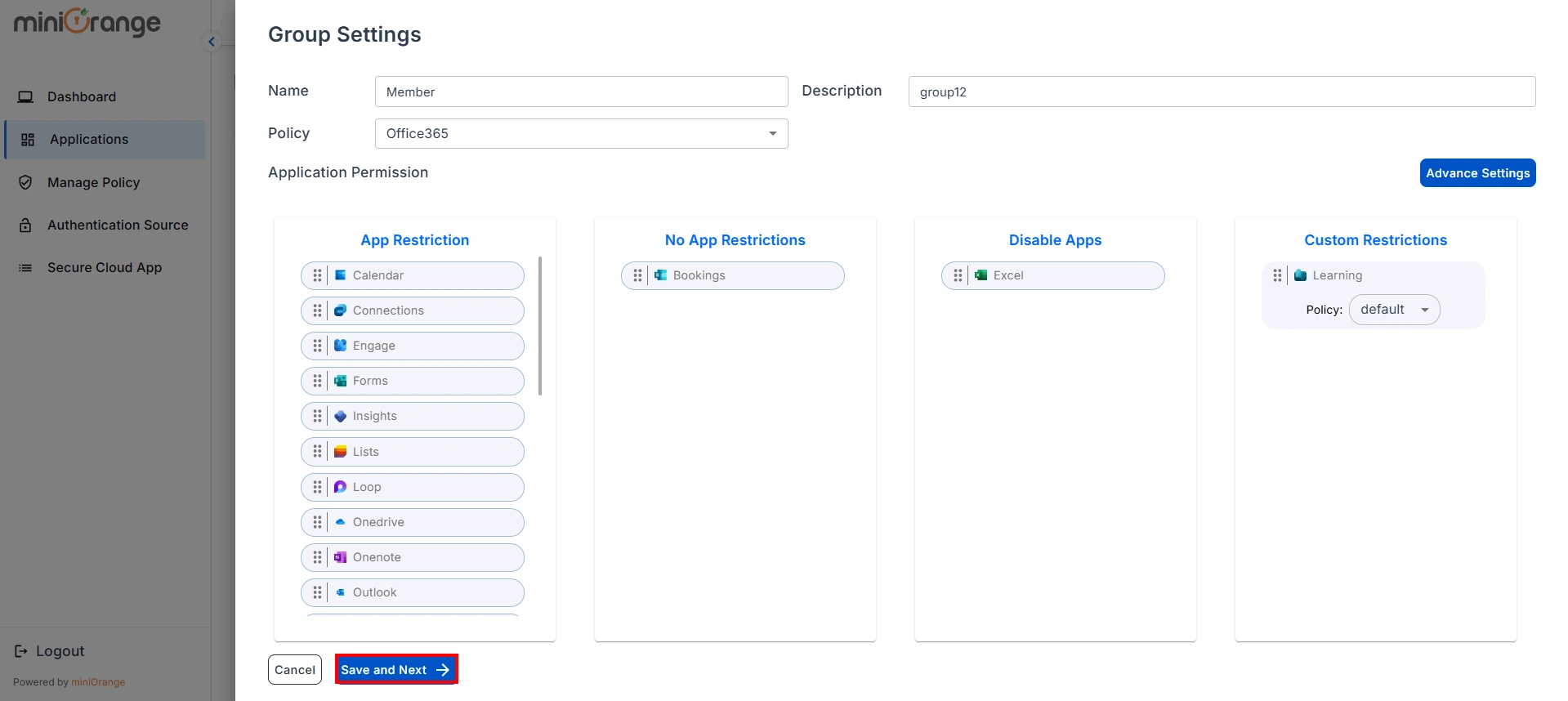
- Click on Group Settings and then click Add New button.
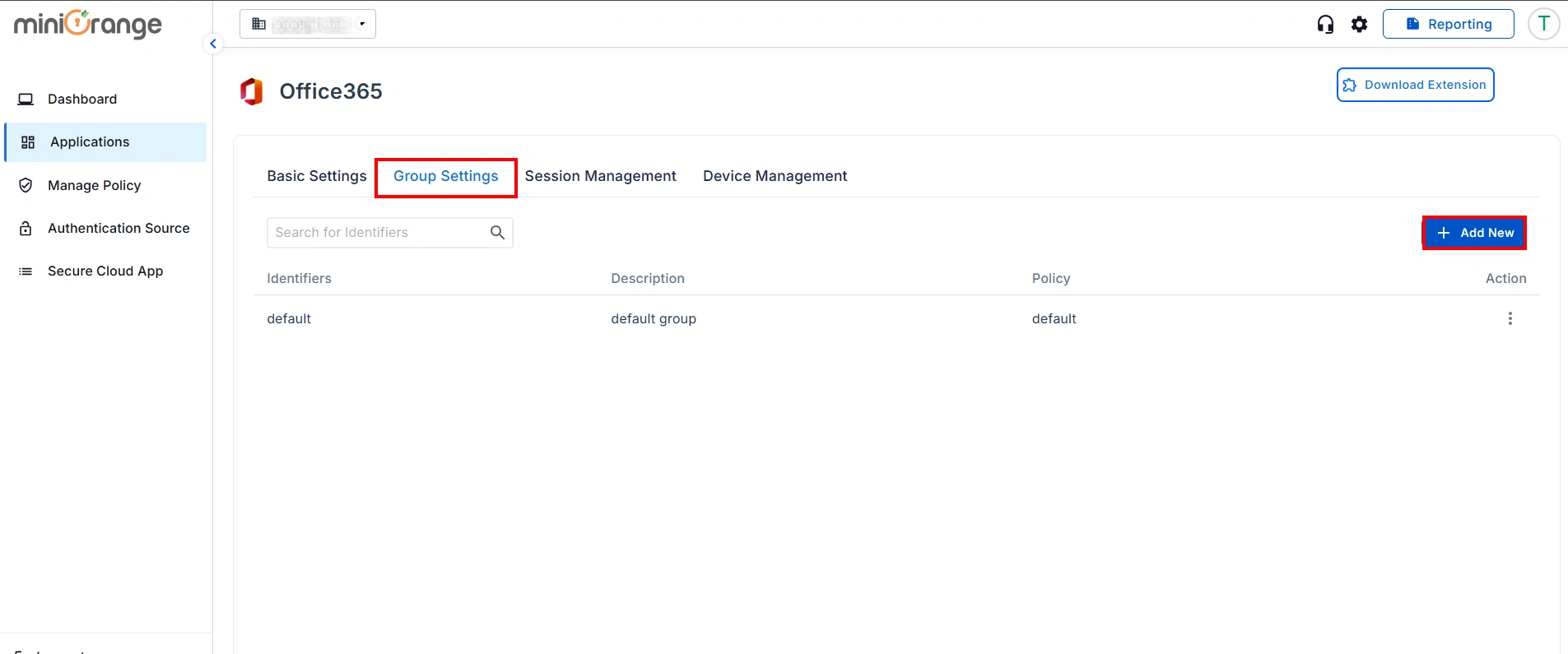
- Enter the Group Name and Group Description. Select the Office365 Policy from the drop-down menu.
- Choose the application to which you want to apply below permissions.
1) App Restriction: In this, the restrictions will be applied over the application based on the policy that you have configured for the group.
2) No App Restriction: In this, there will be no restrictions on the application for the group.
3) Disable App: By choosing this option, the application becomes inaccessible from anywhere for the entire group.
4) Custom App Restriction: By using this, you can apply an application-specific custom application restriction policy to an application that overpowers the group's restriction policy.
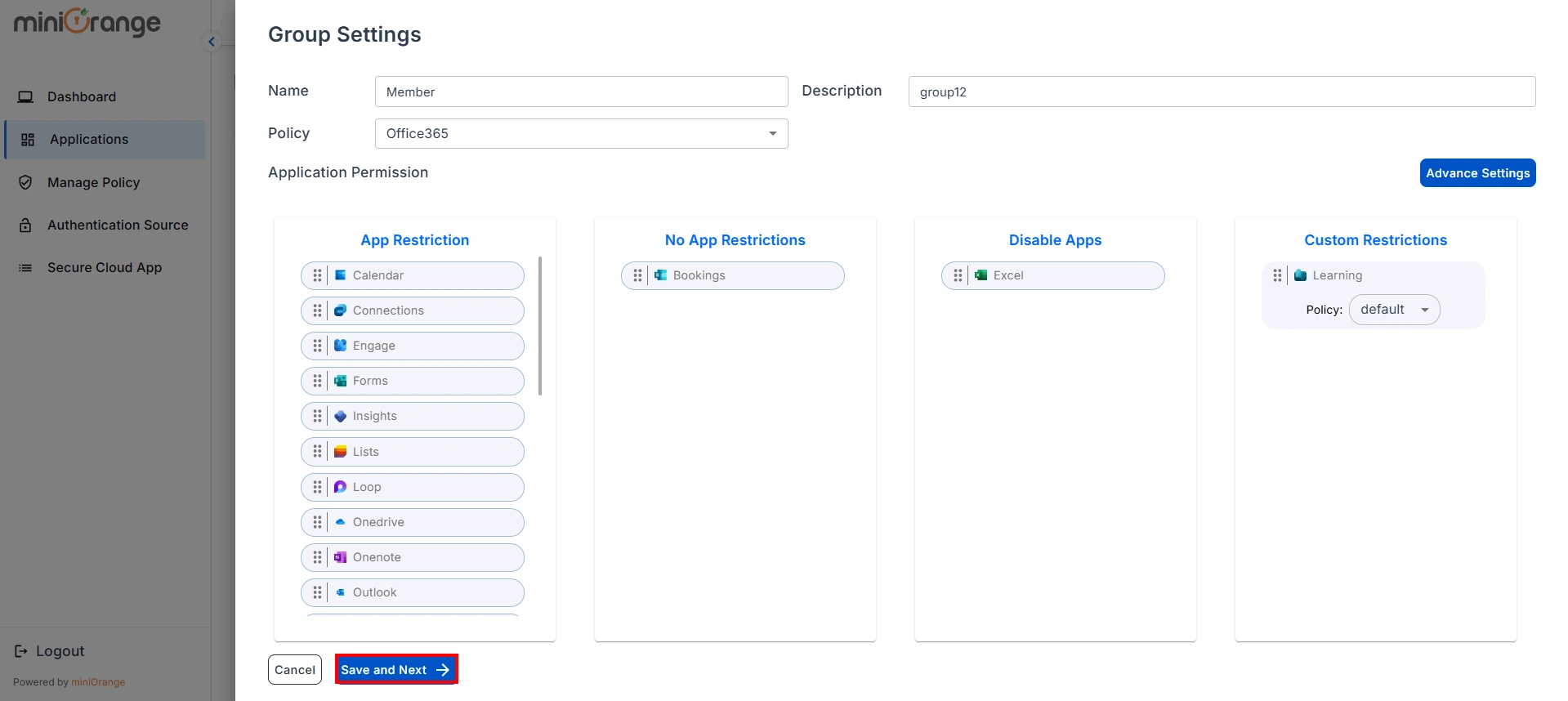
- Now, click on Save & Next button.
Note:
To access your applications, you need to set up the miniOrange CASB extension. Click here to follow the steps.
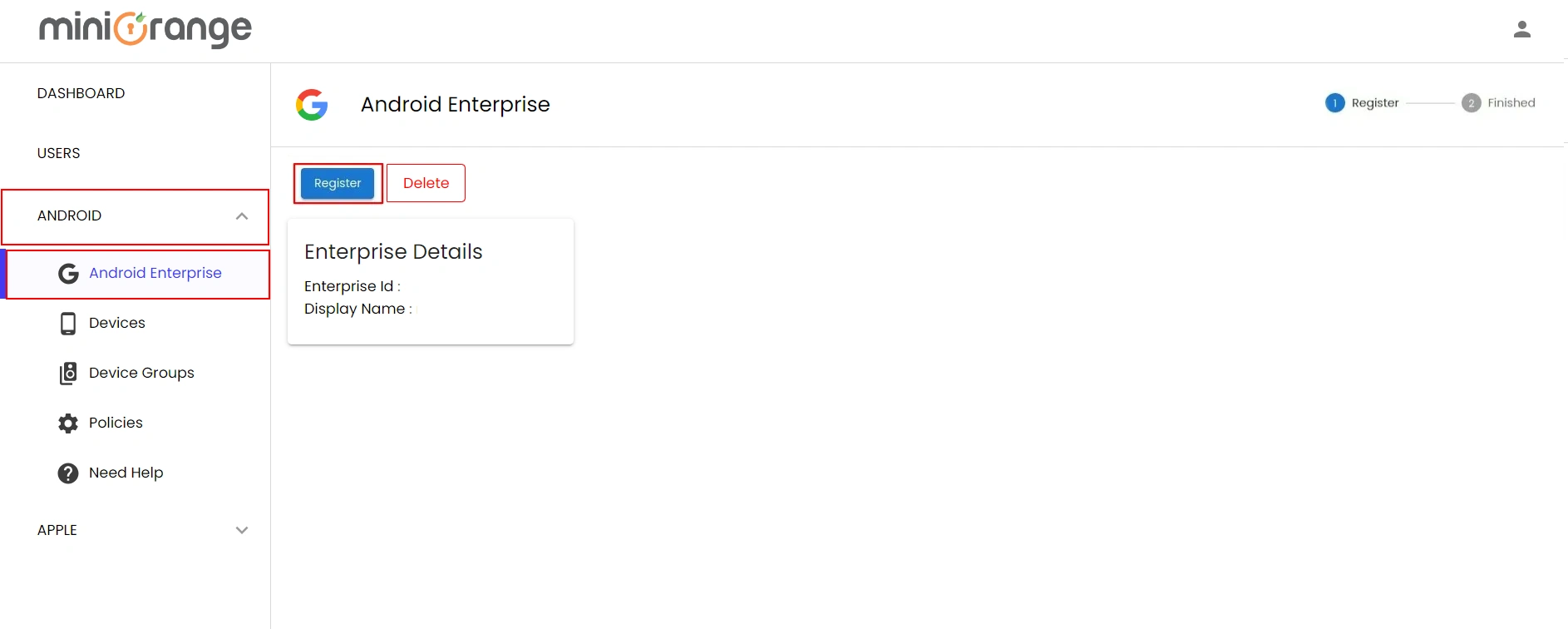
1. Register your organization with Android Enterprise.
- Login into miniOrange MDM dashboard by clicking here.
- Once logged in, Navigate to ANDROID -> Android Enterprise and click on
Register button.
You will need to Register your organization with Android Enterprise initially and this will
be a one-time
process.
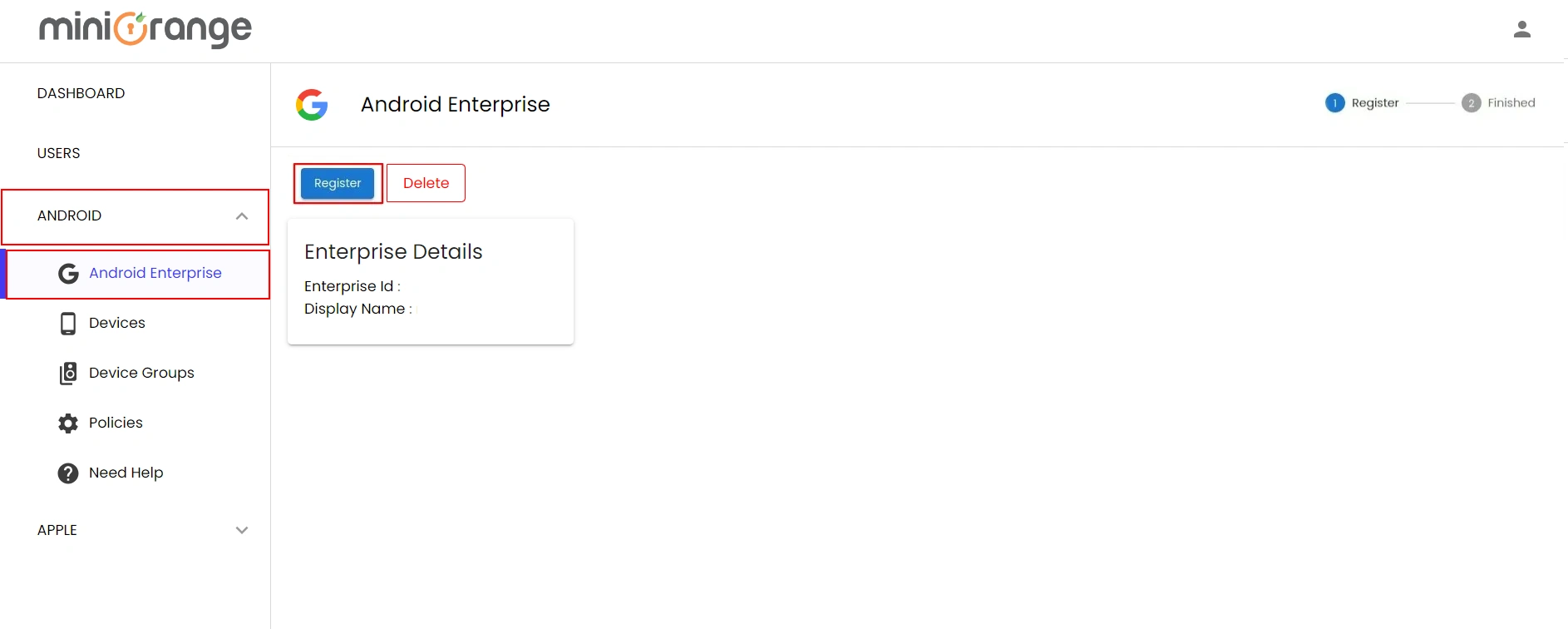
- Click here for detailed instructions on registering your
organization with Android
Enterprise.
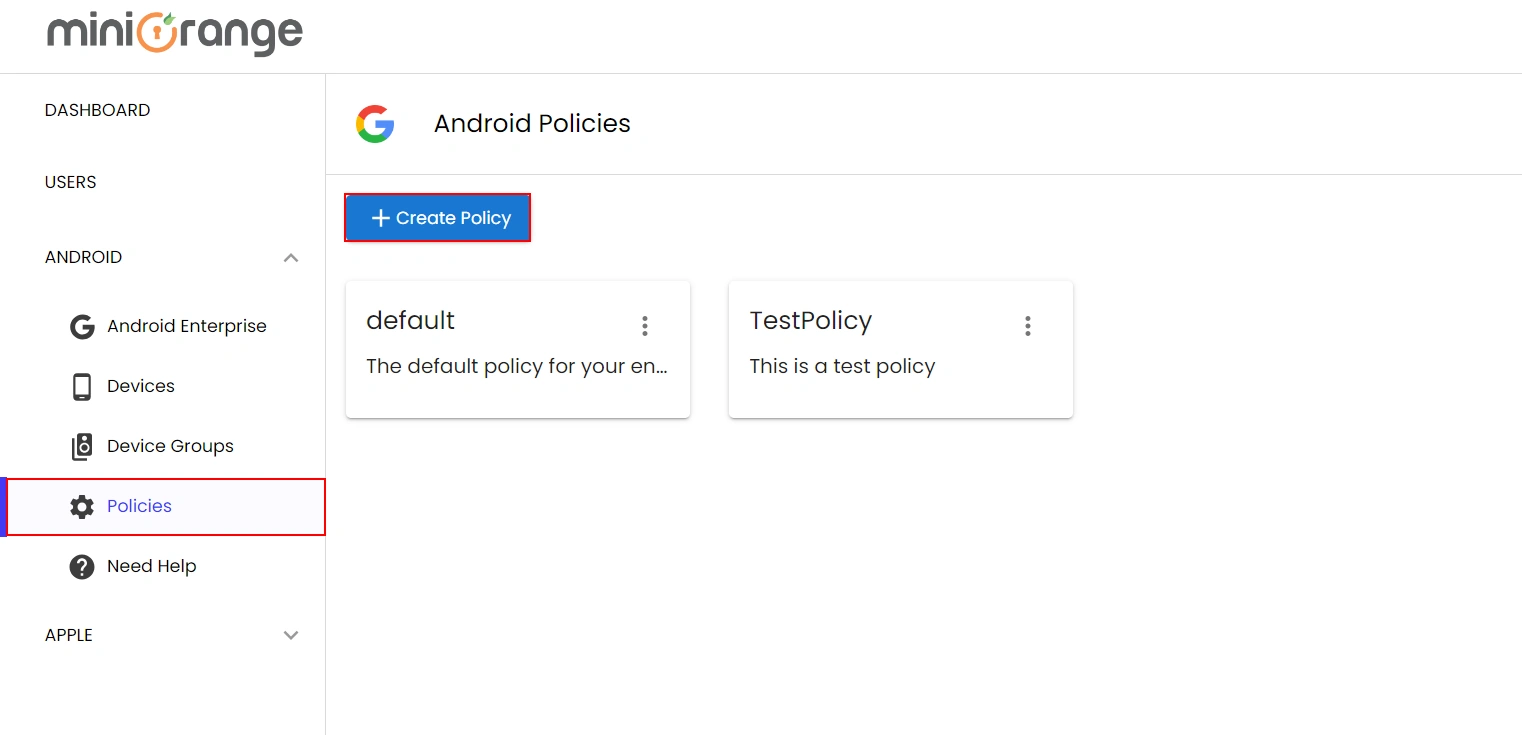
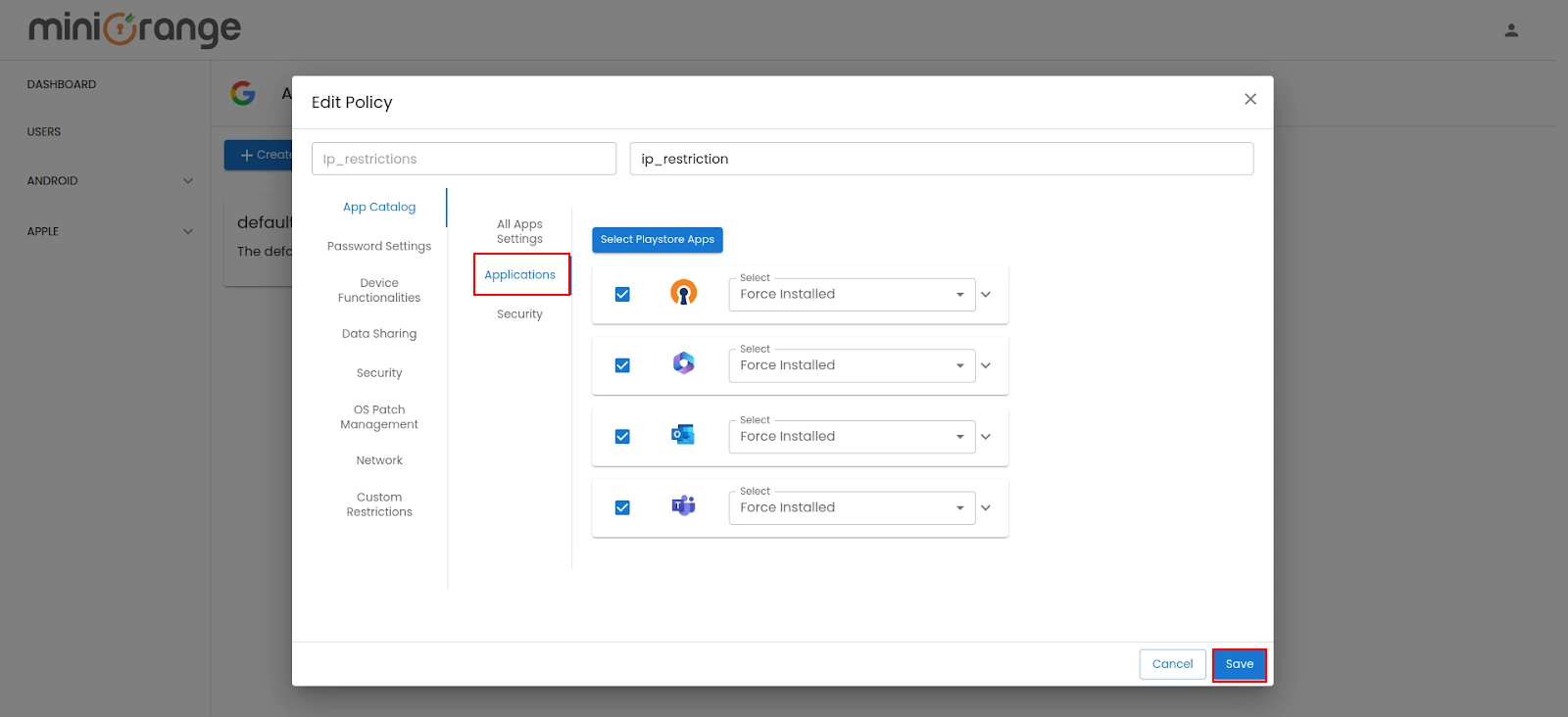
2. Create a new policy
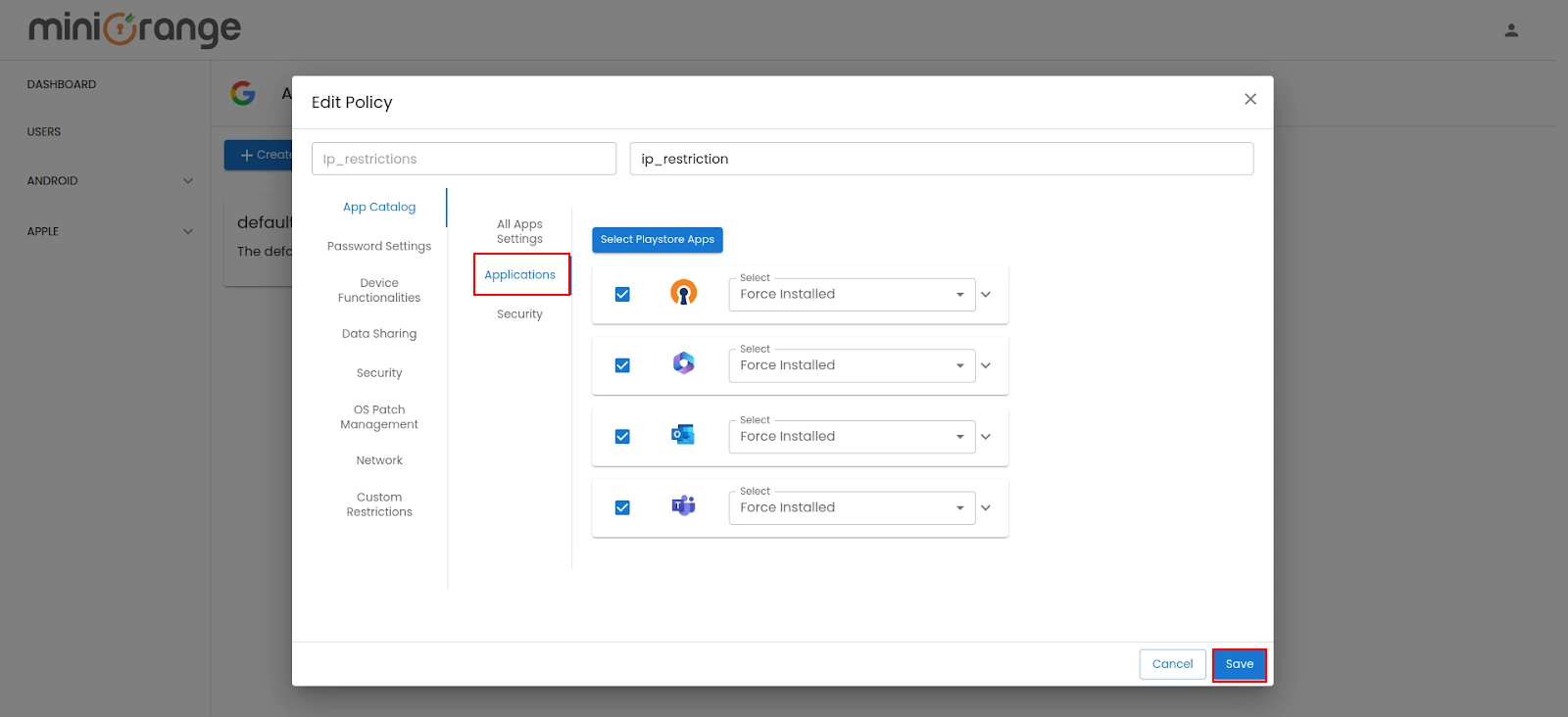
- Go to ANDROID -> Policies. Click on Create Policy to create the new policy.
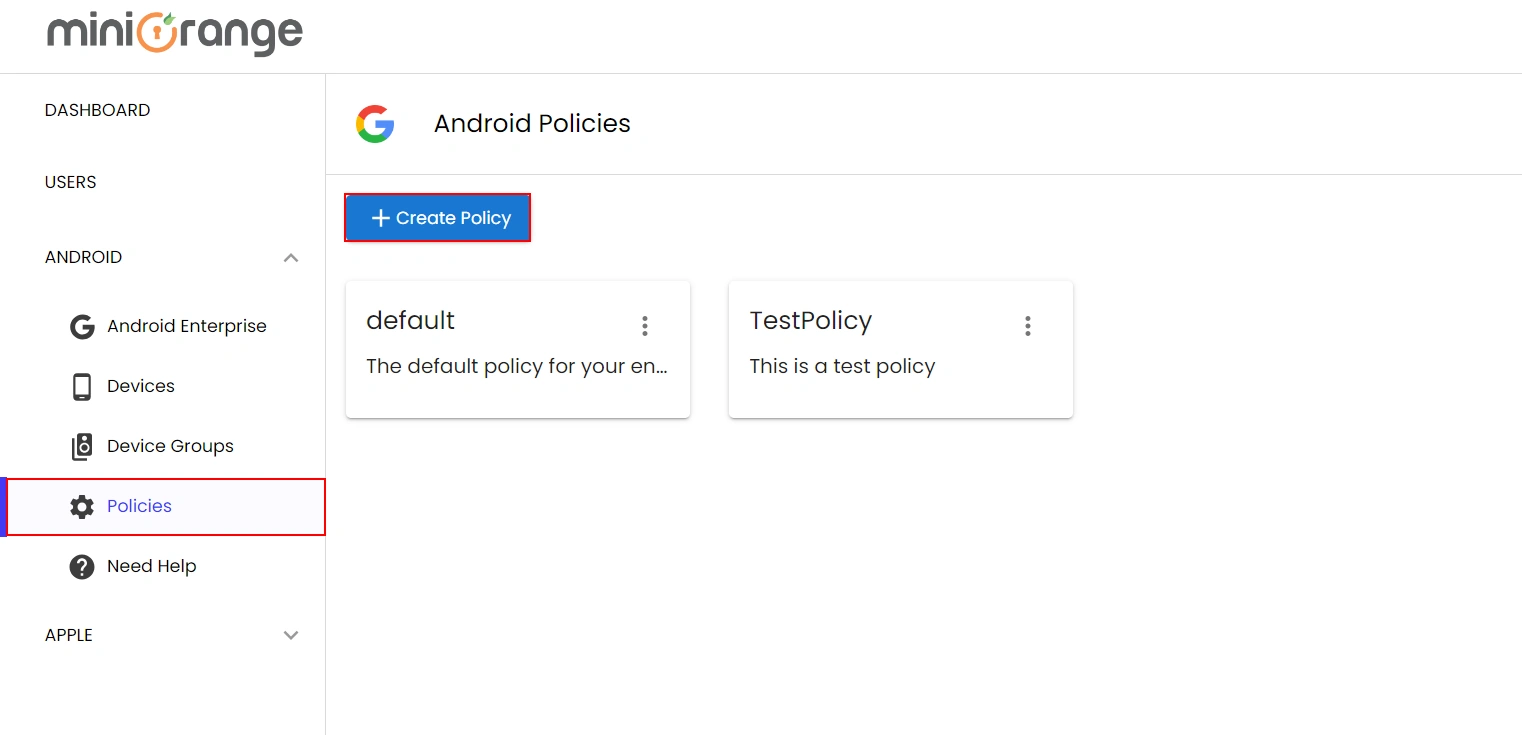
- Now, go to the Application section and choose the specific Microsoft 365
applications for
which you want to enforce IP restrictions.
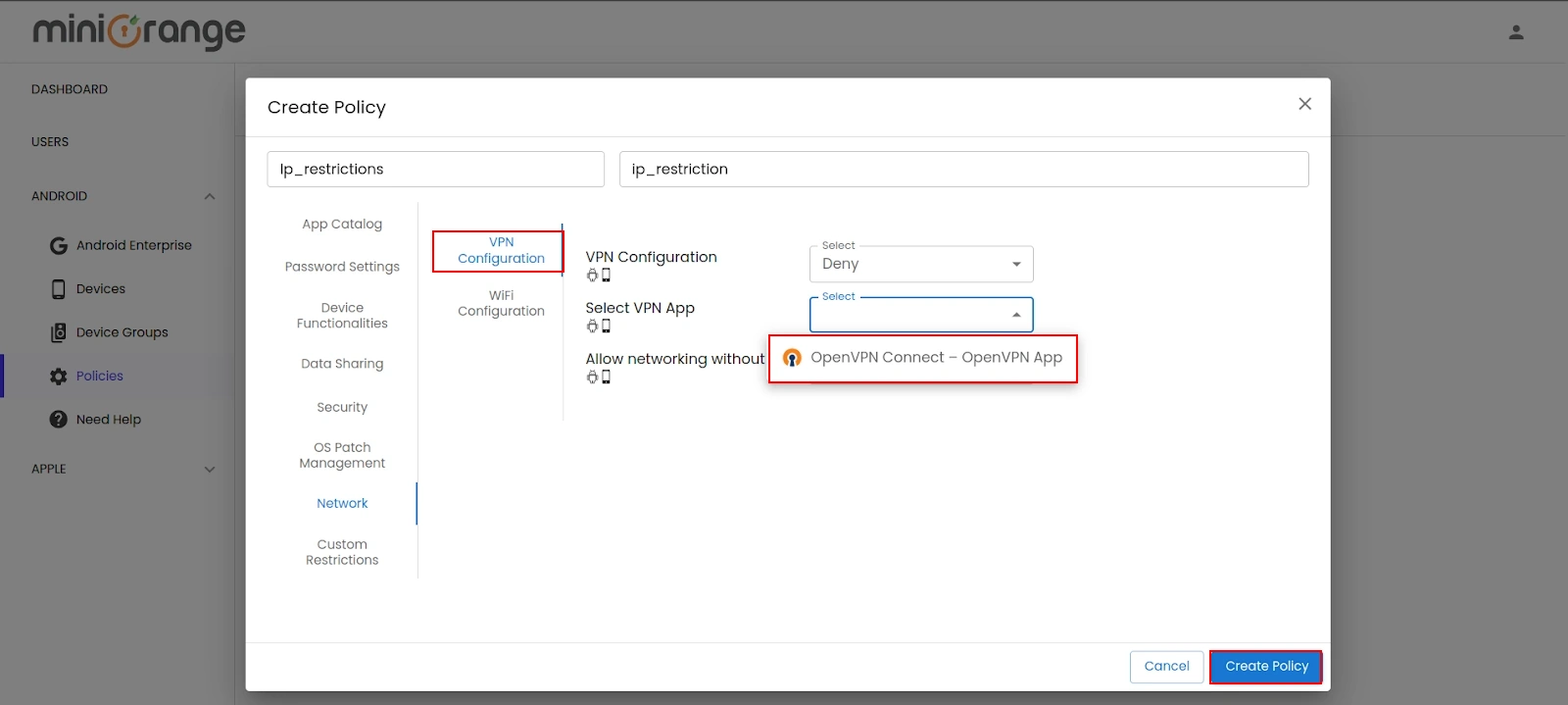
3. Configure VPN for IP Restriction
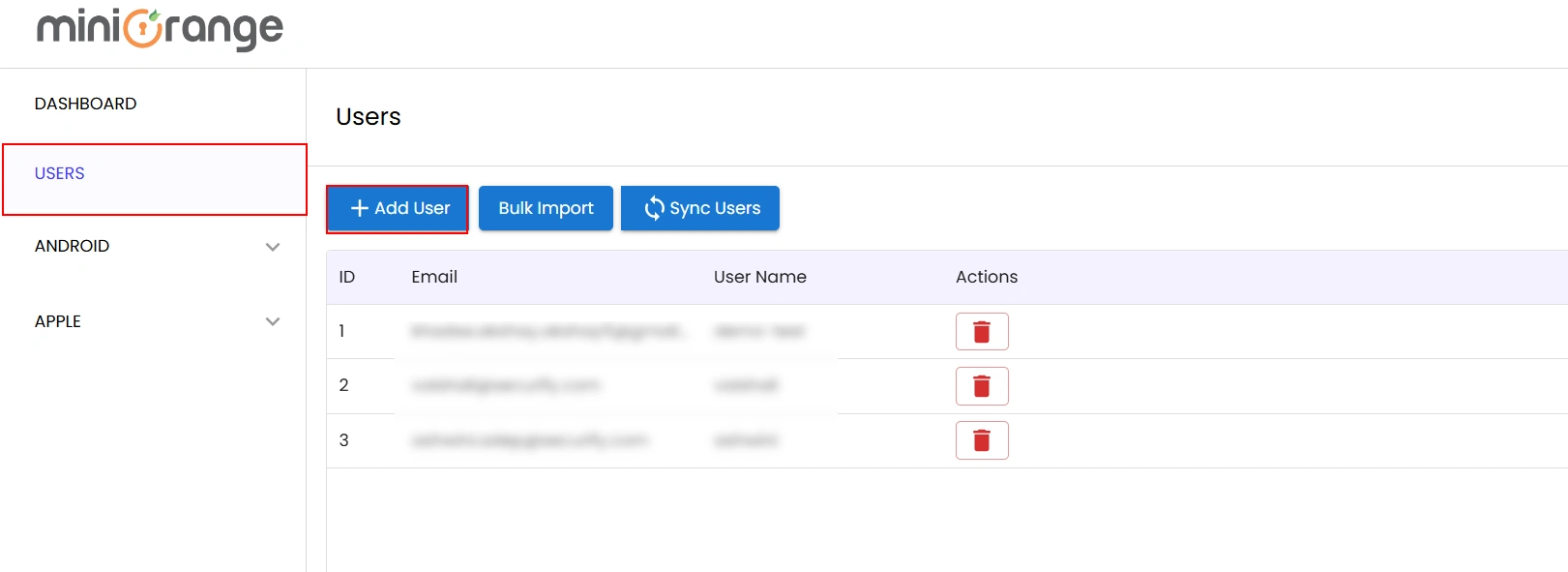
4. Create Users & Attach Policy
to Device
Group
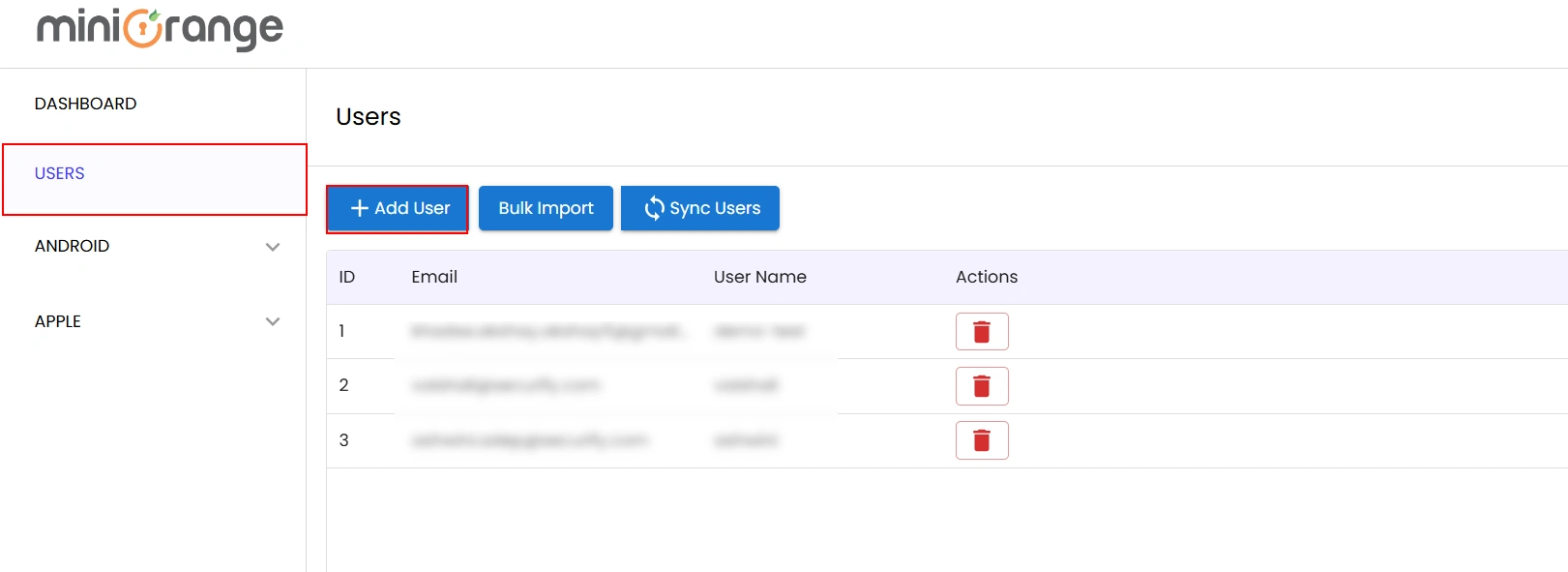
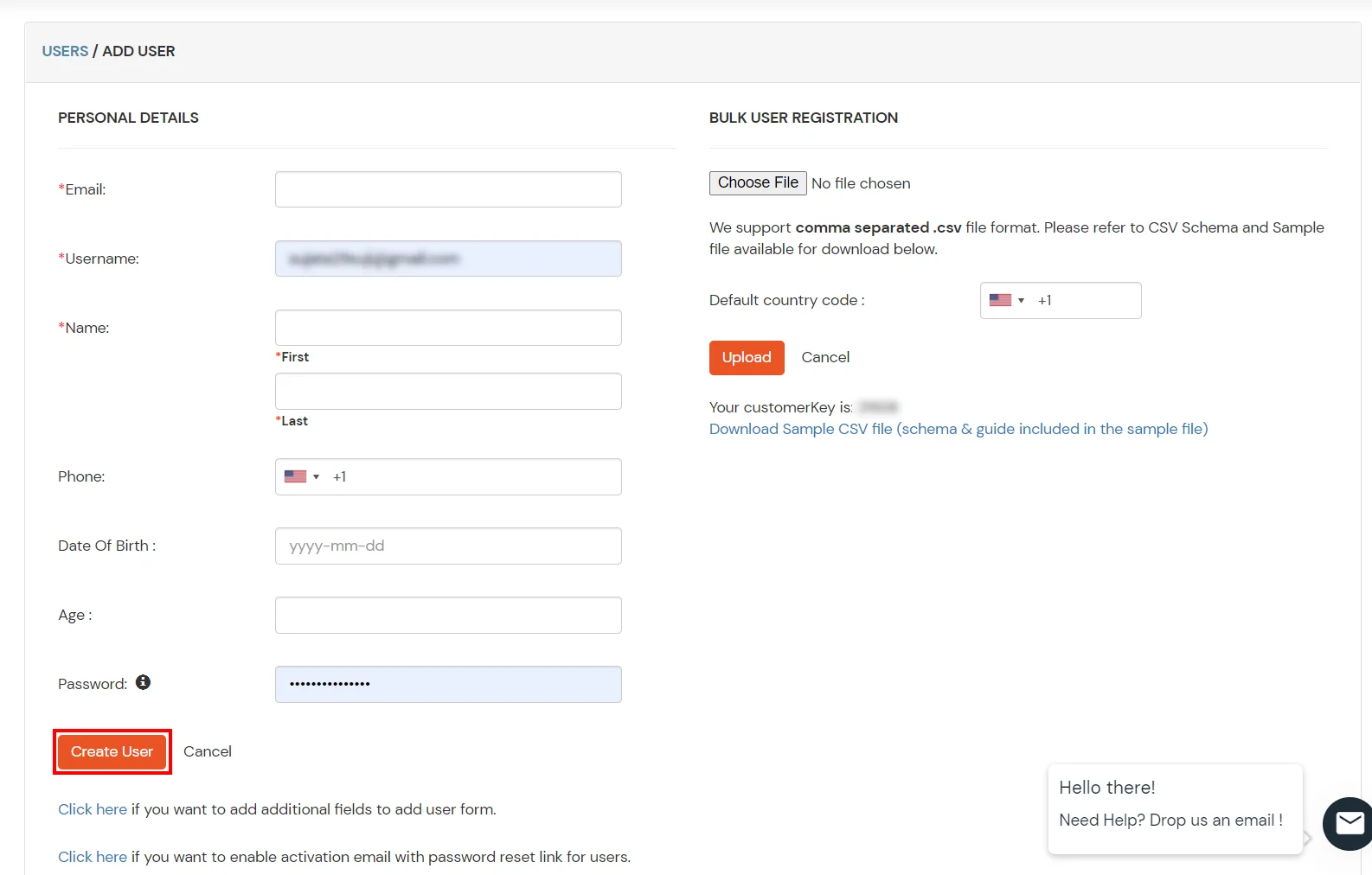
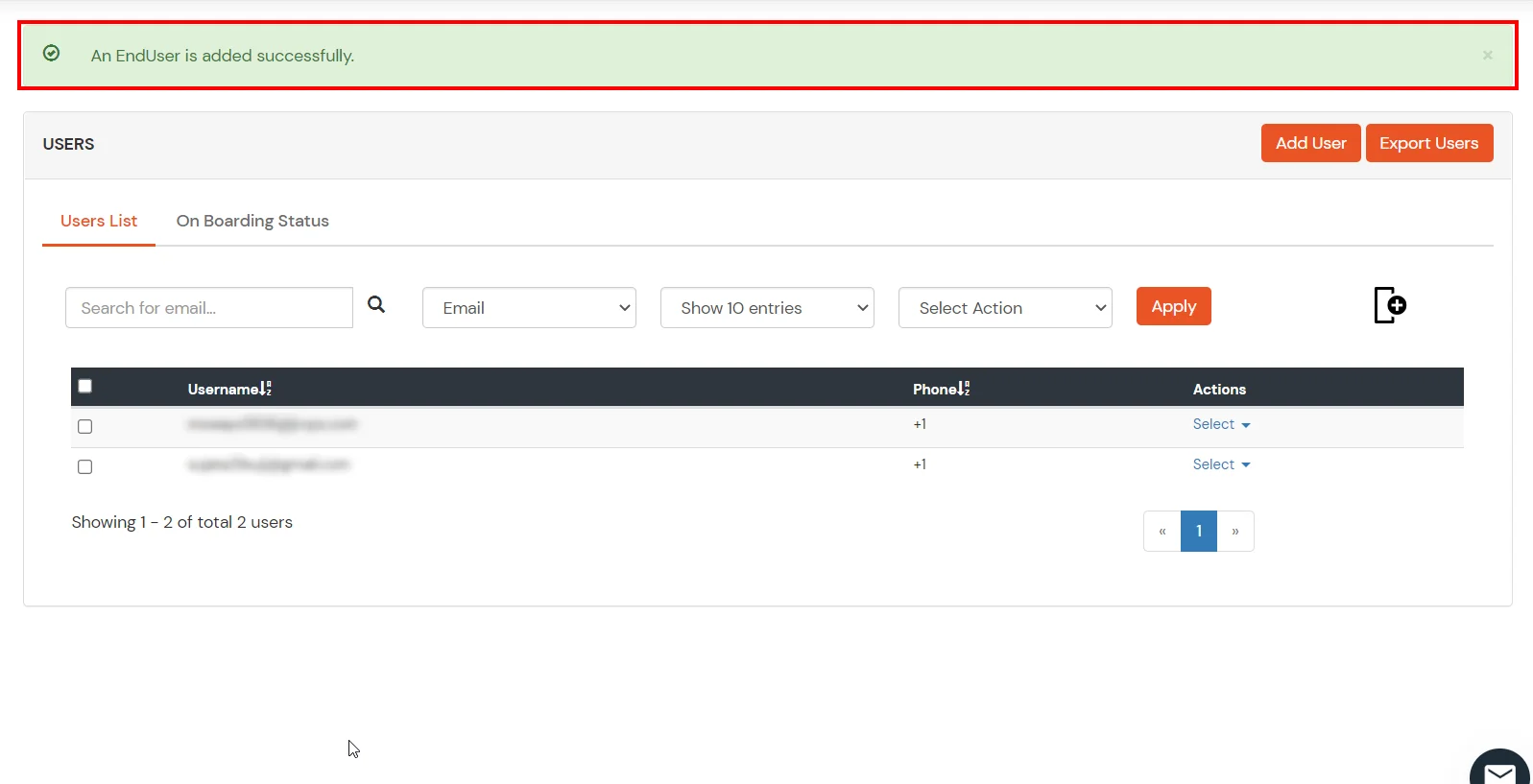
- Now, Go to the USERS tab and click on Add User to create a new user and enter
Email and
User Name and click on Add User button.
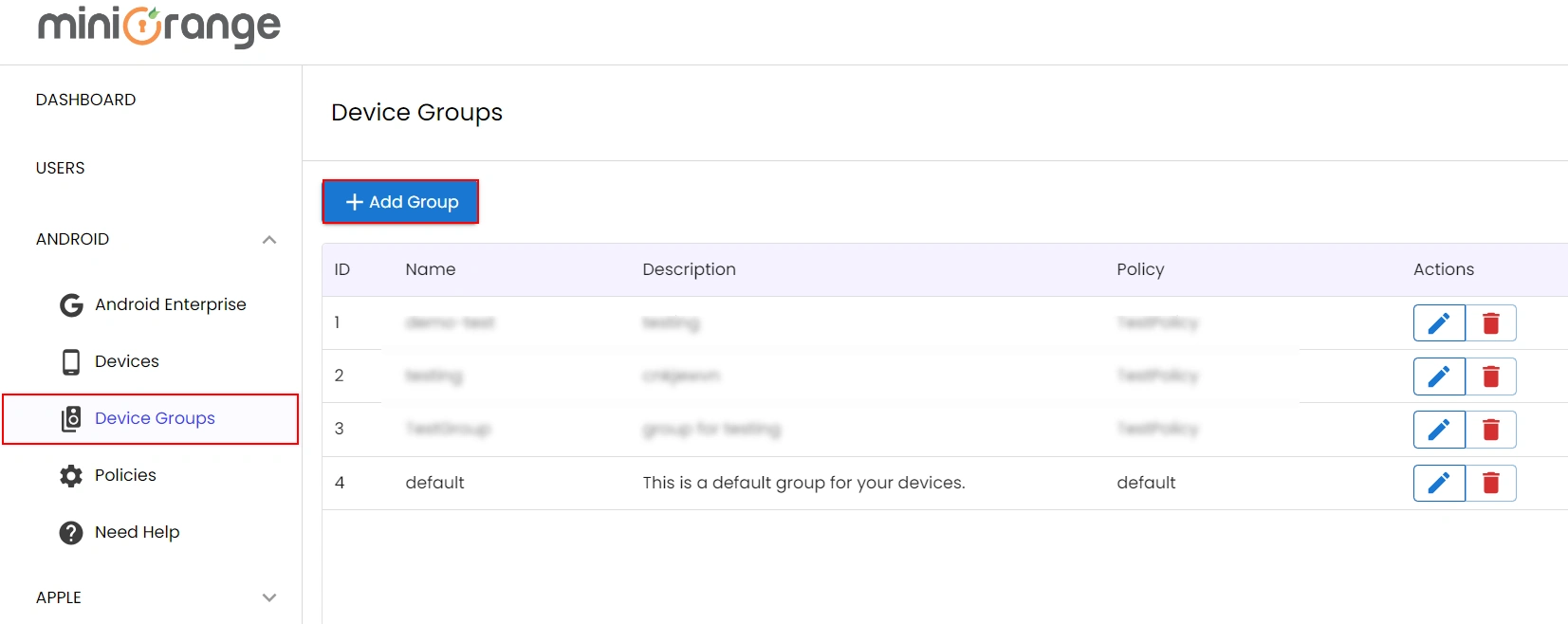
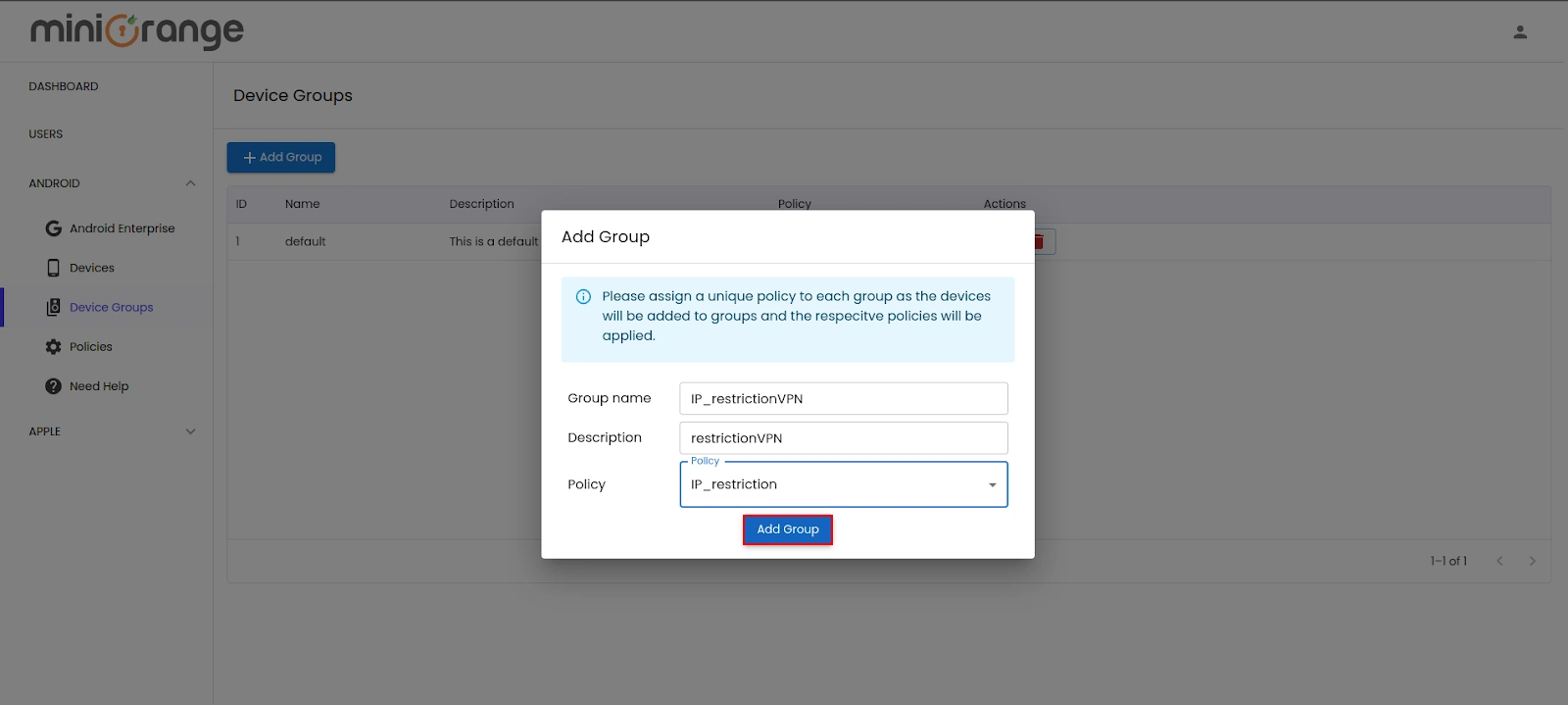
- Go to ANDROID -> Device Groups, here the default group will already created with the
default
policy assigned. You can create other groups as per your requirements. Click on Add
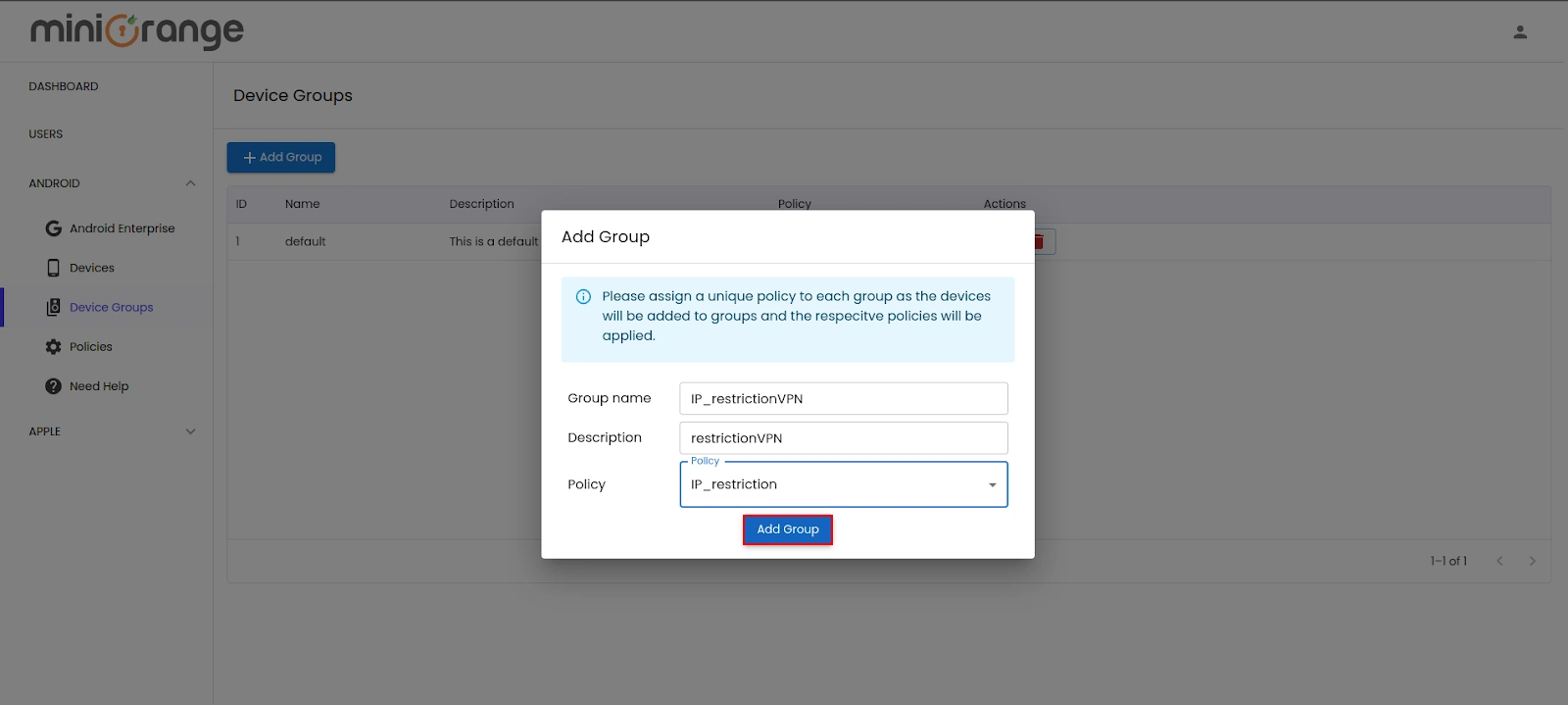
Group button.
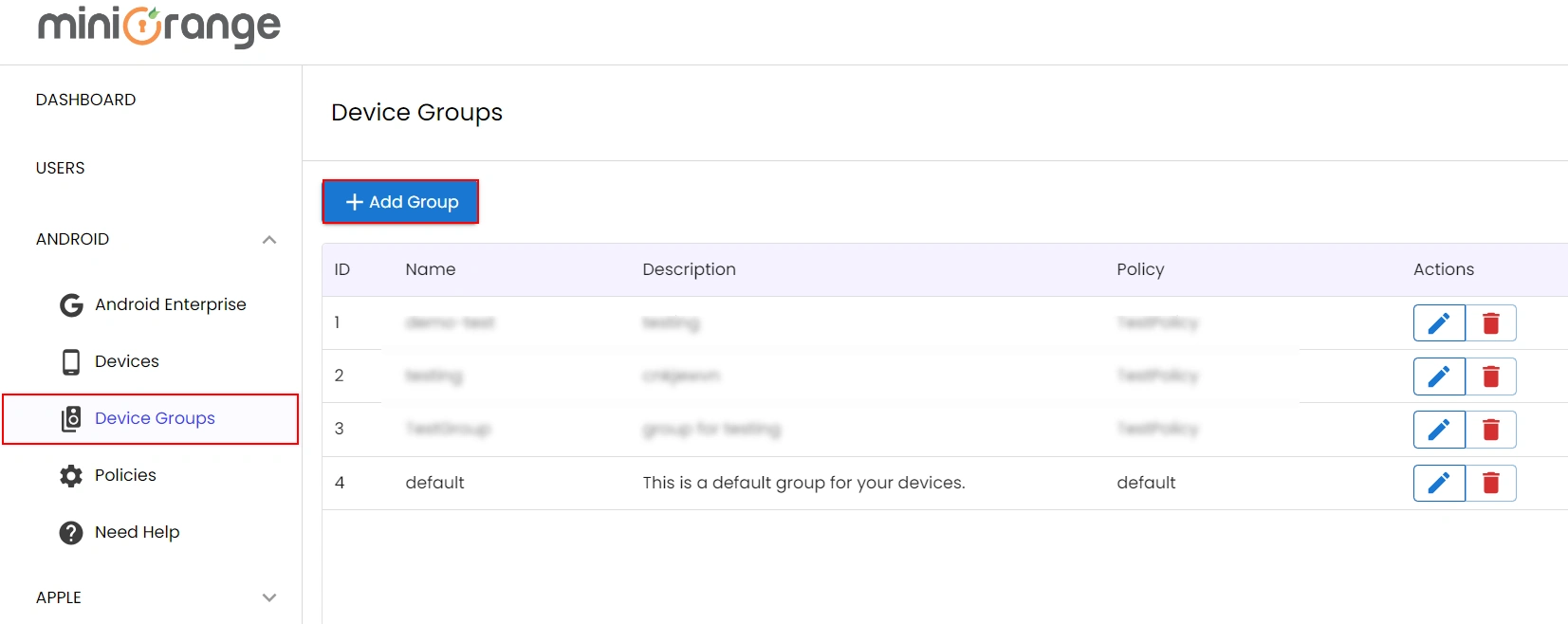
- Choose the appropriate device group to which you want to apply the policy.
- Attach the newly created policy to the selected device group. This will ensure that the
policy is
enforced for all devices within that group. Click on Add Group.
- Click here to enroll your new device and complete the setup
process.
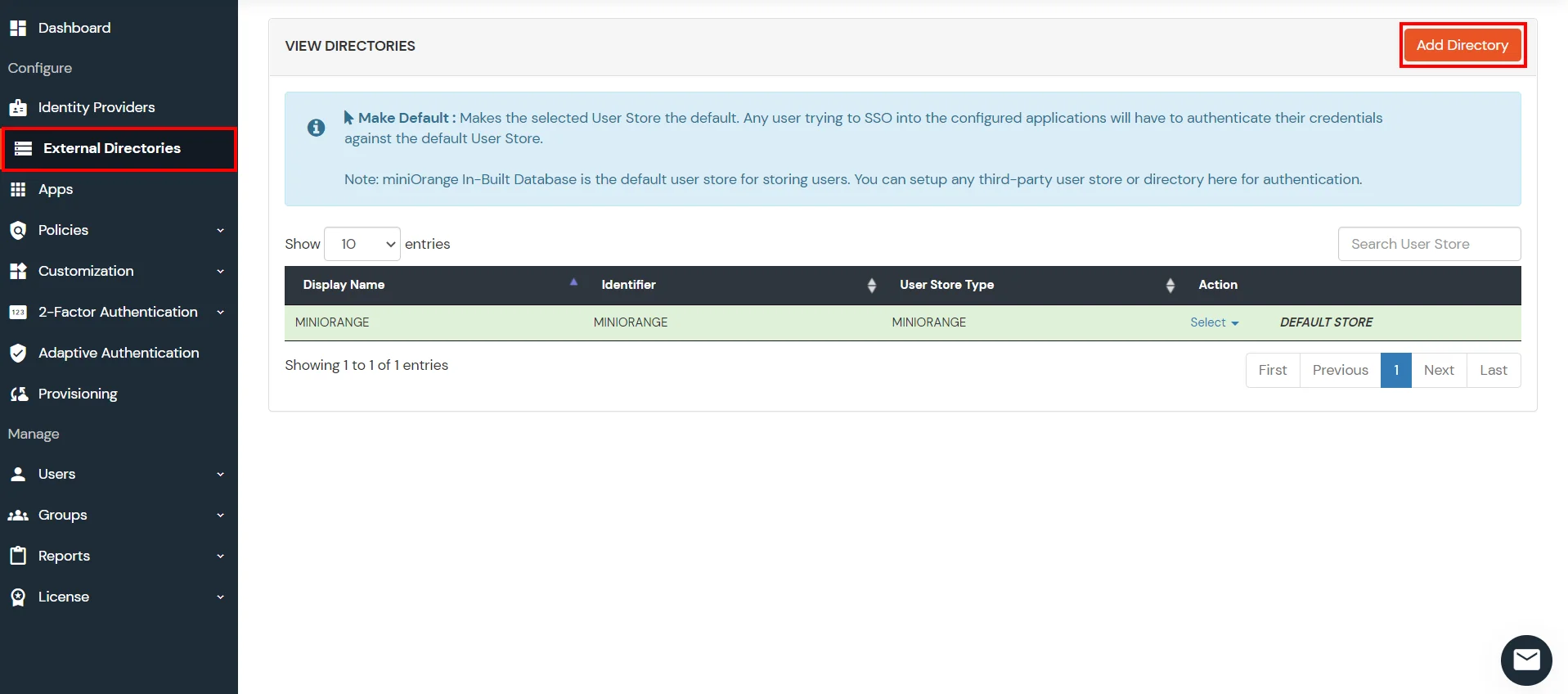
6. Configure Your User Directory (Optional)
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
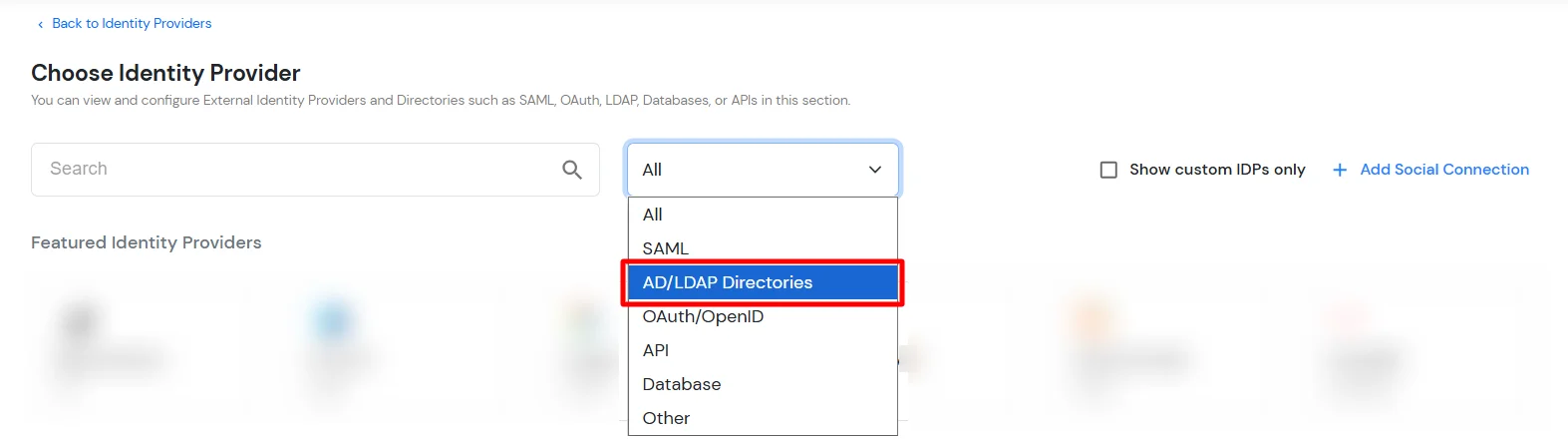
- Click on Identity Providers >> Add Identity Provider in the left menu of the dashboard
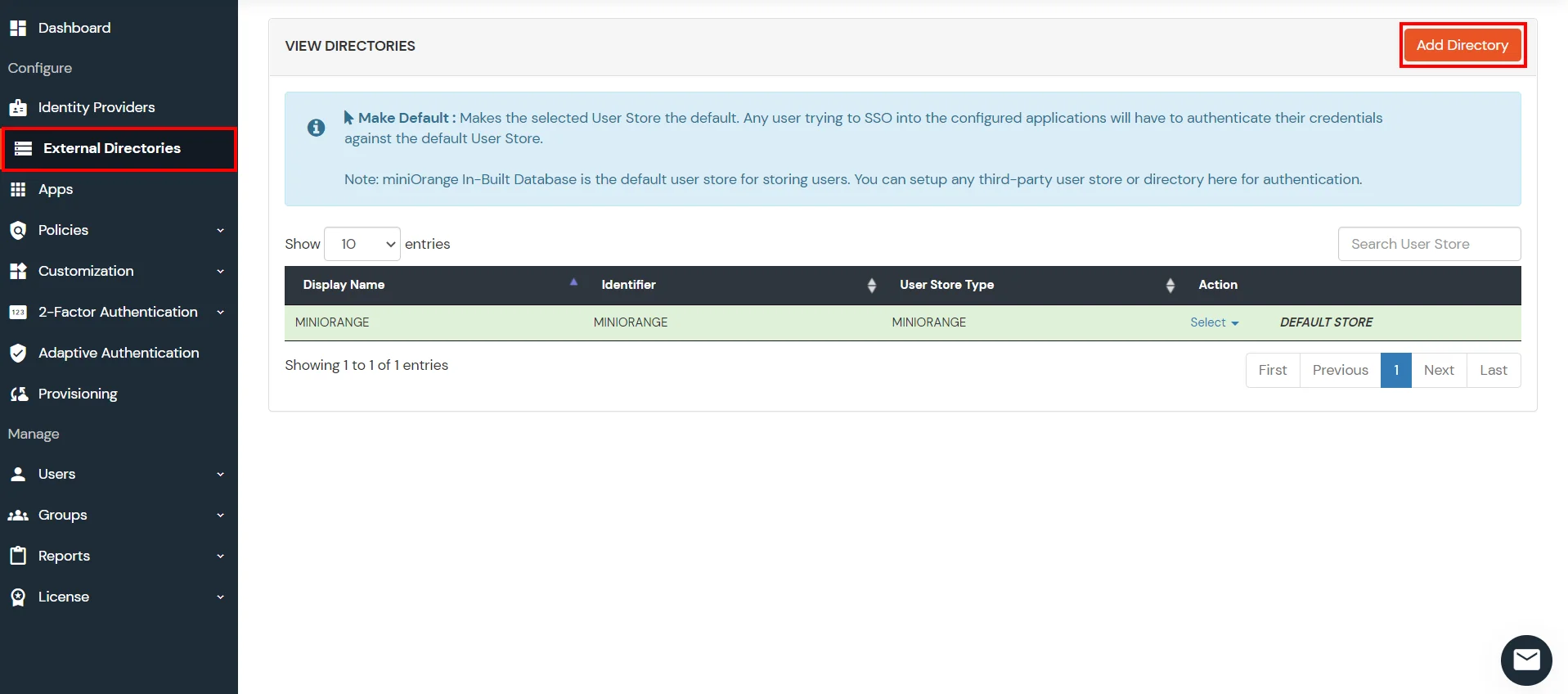
- In Choose Identity Provider, select AD/LDAP Directories from the dropdown.
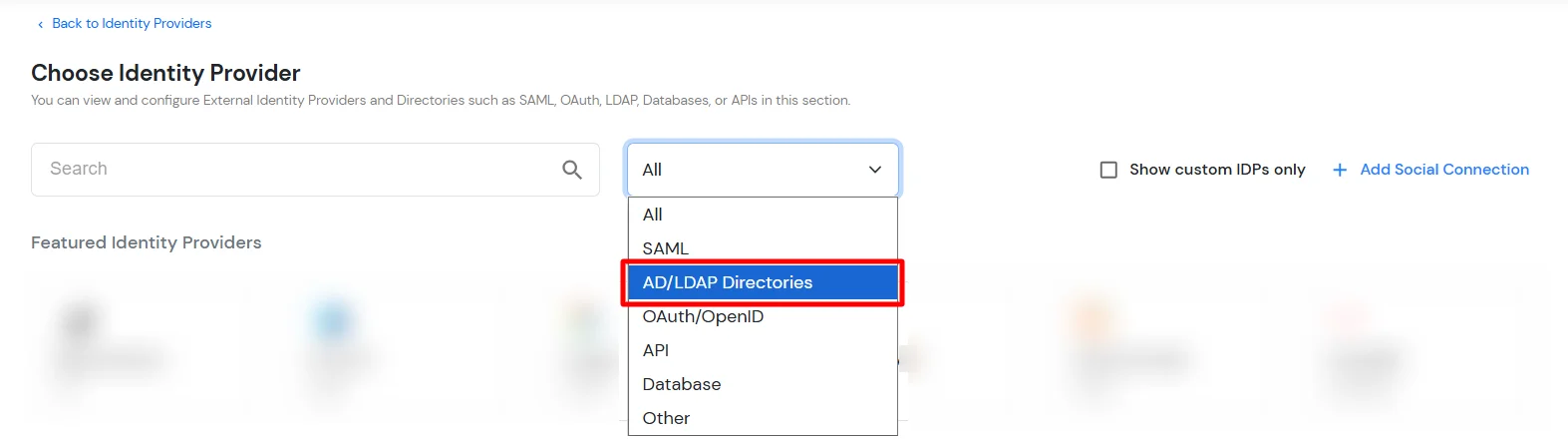
- Then search for AD/LDAP and click it.
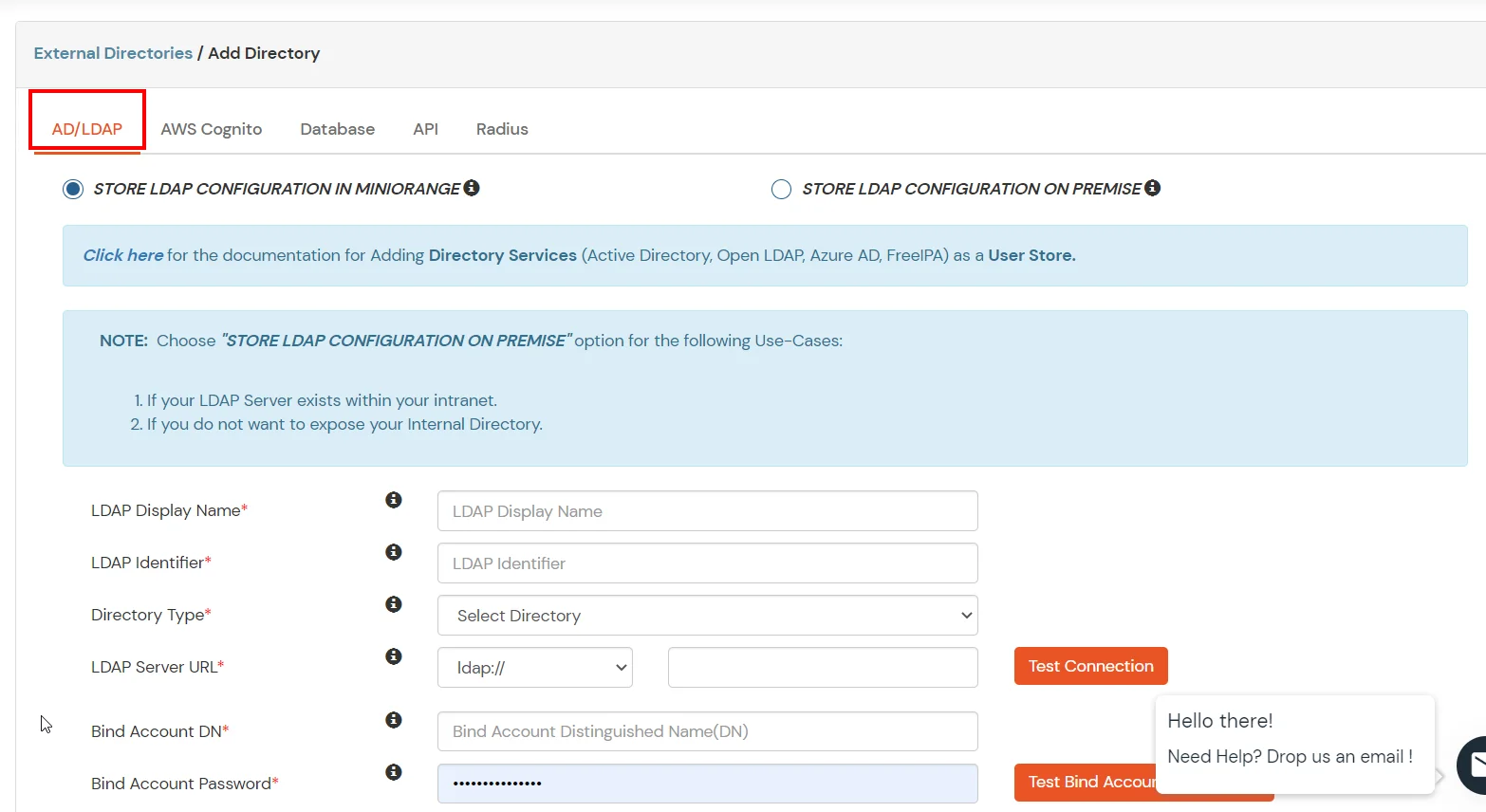
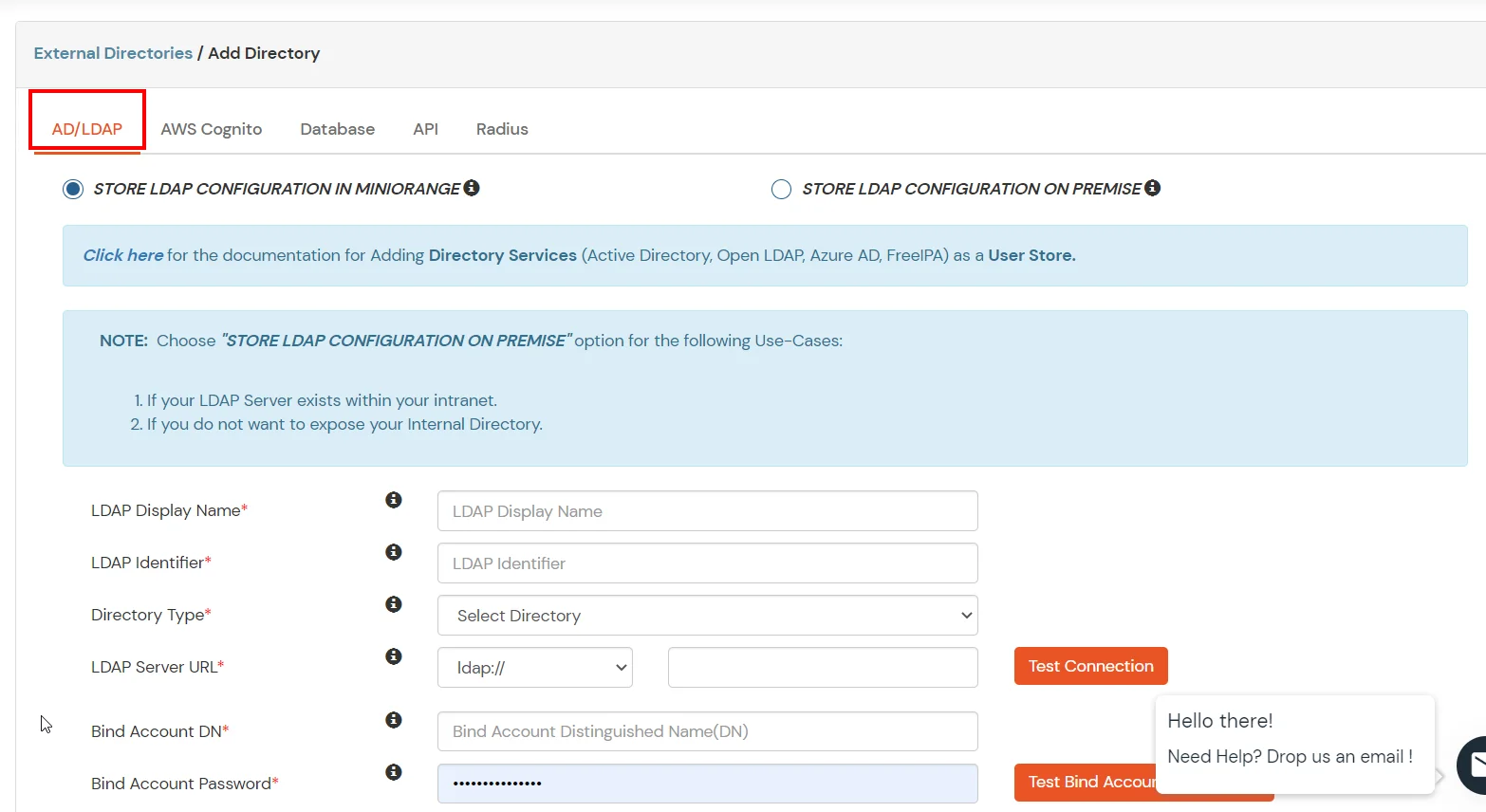
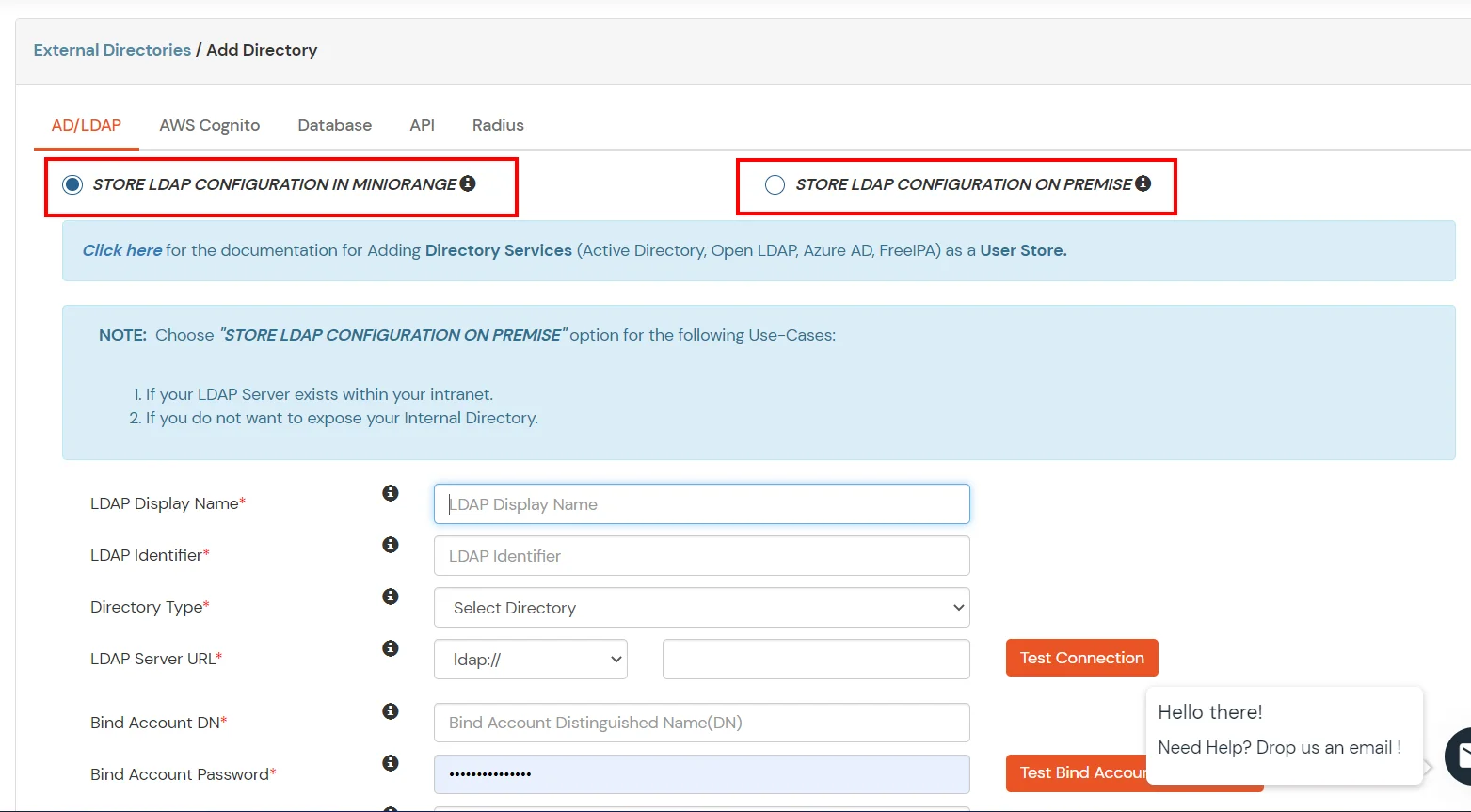
- STORE LDAP CONFIGURATION IN MINIORANGE: Choose this option if you want to keep your configuration in miniOrange. If the active directory is behind a firewall, you will need to open the firewall to allow incoming requests to your AD.
- STORE LDAP CONFIGURATION ON PREMISE: Choose this option if you want to keep your configuration in your premise and only allow access to AD inside premises. You will have to download and install miniOrange gateway on your premise.
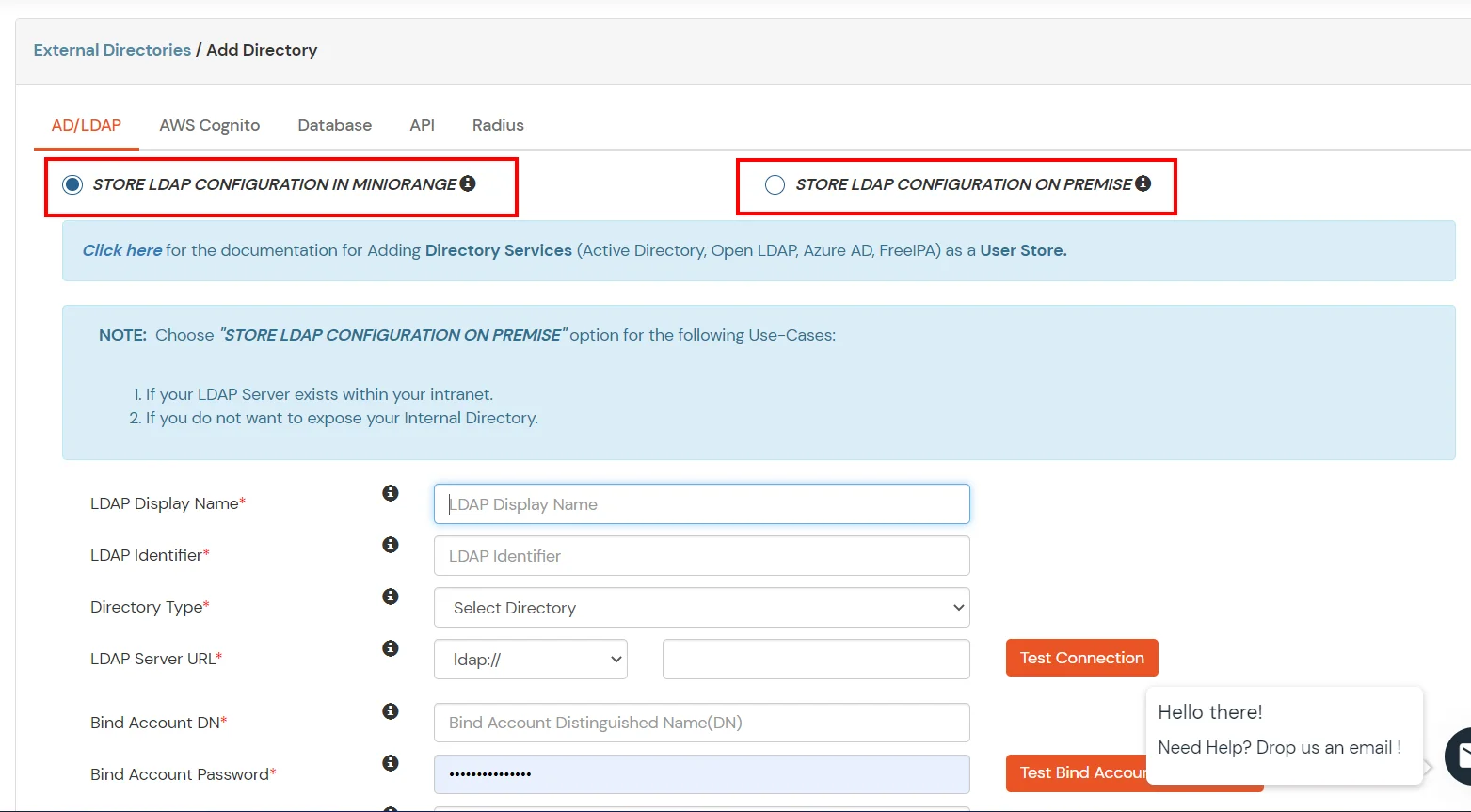
- Enter AD/LDAP Display Name and Identifier name.
- Select Directory Type as Active Directory.
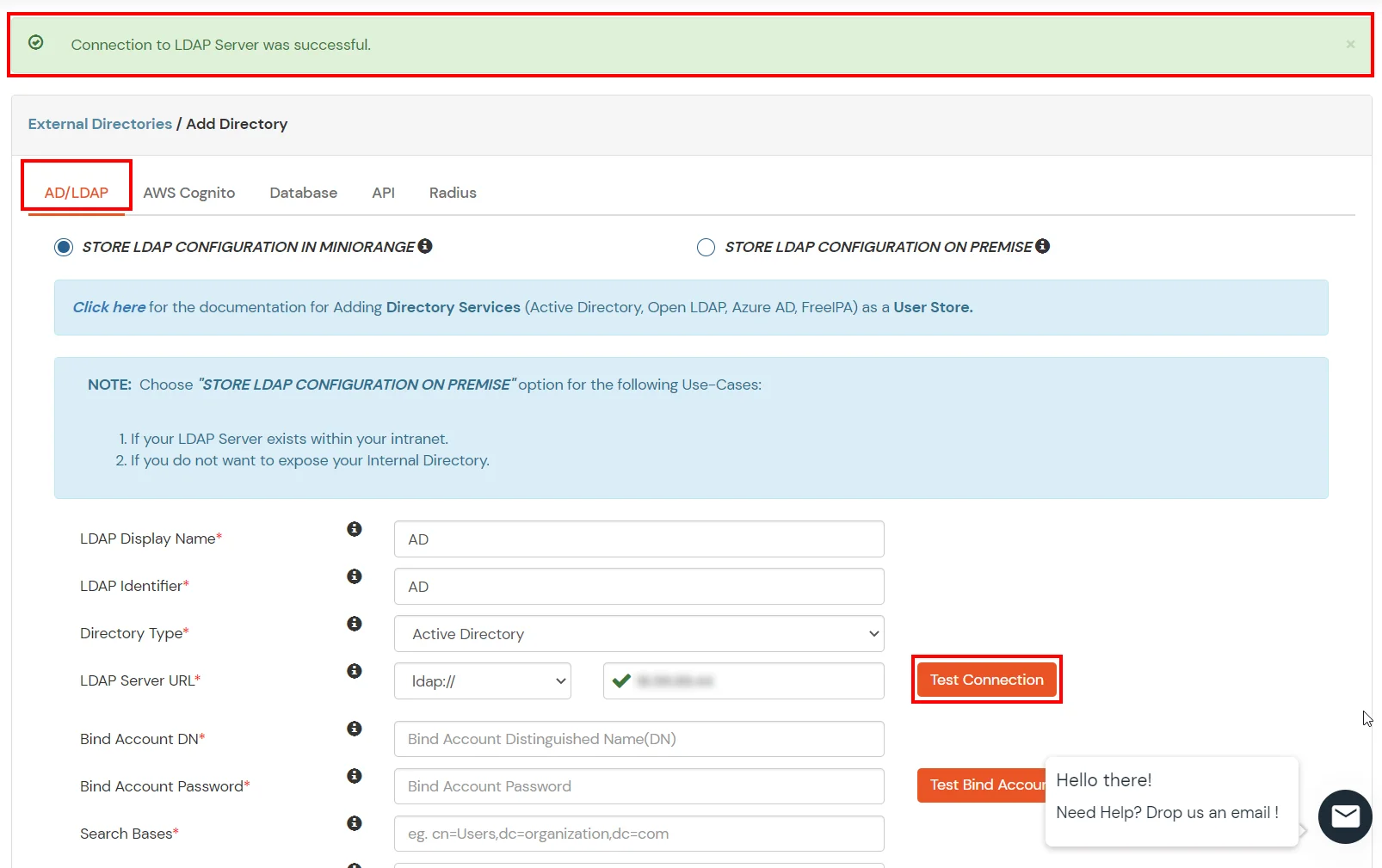
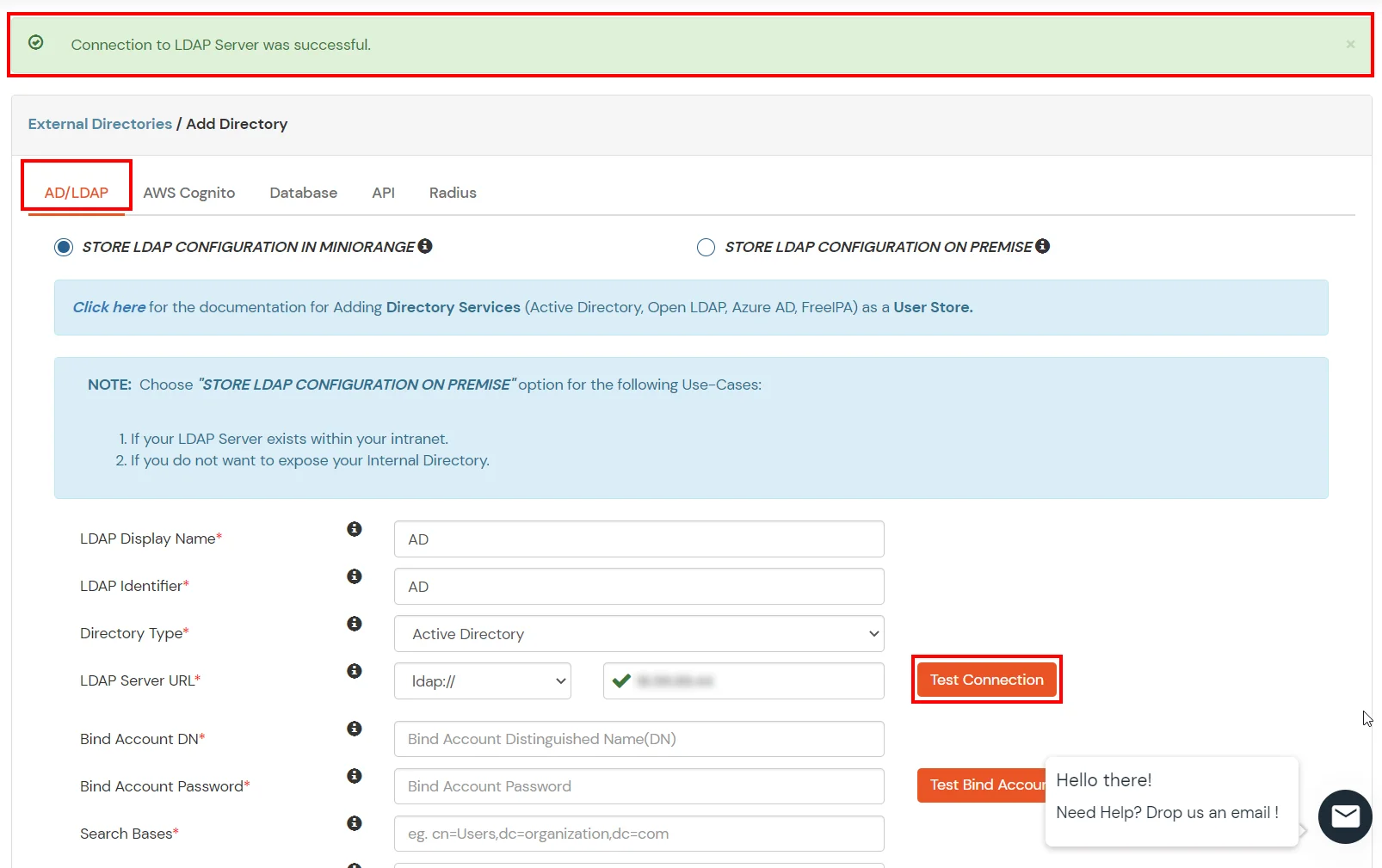
- Enter the LDAP Server URL or IP Address against the LDAP Server URL field.
- Click on the Test Connection button to verify if you have made a successful connection with your LDAP server.
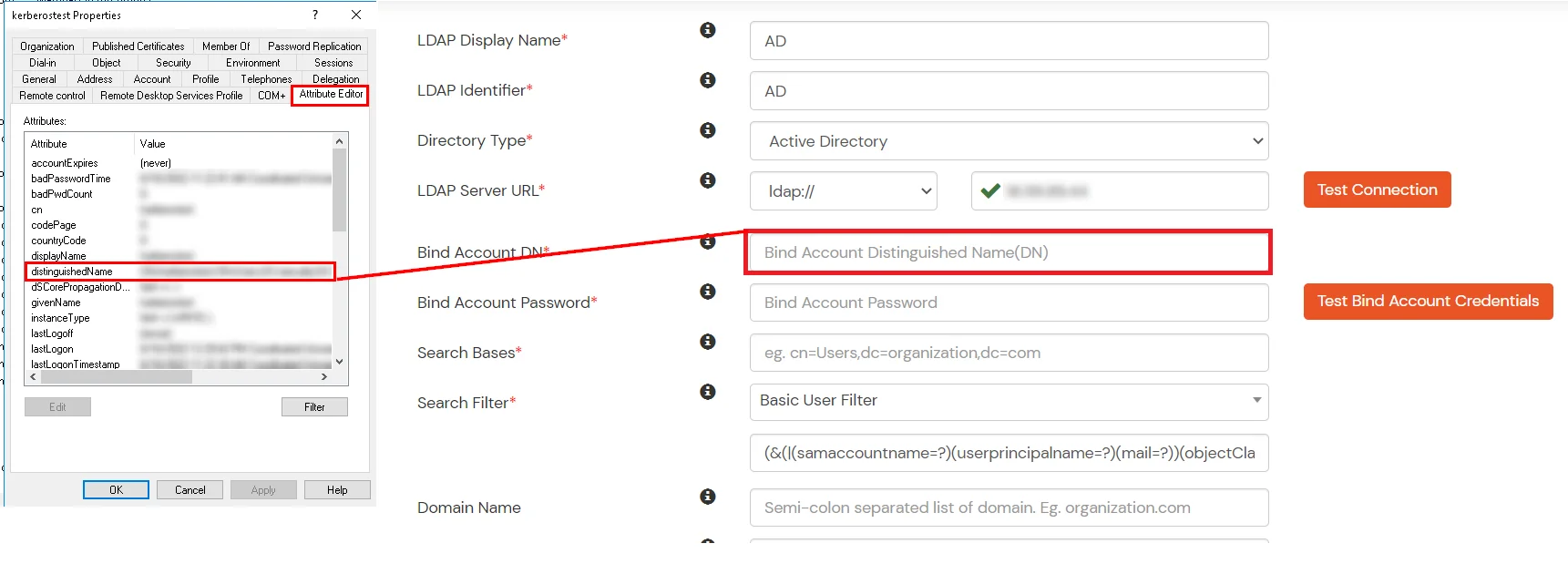
- In Active Directory, go to the properties of user containers/OU's and search for the Distinguished Name attribute. The bind account should have minimum required read privileges in Active Directory to allow directory lookups. If the use case involves provisioning (such as creating, updating, or deleting users or groups), the account must also be granted appropriate write permissions.
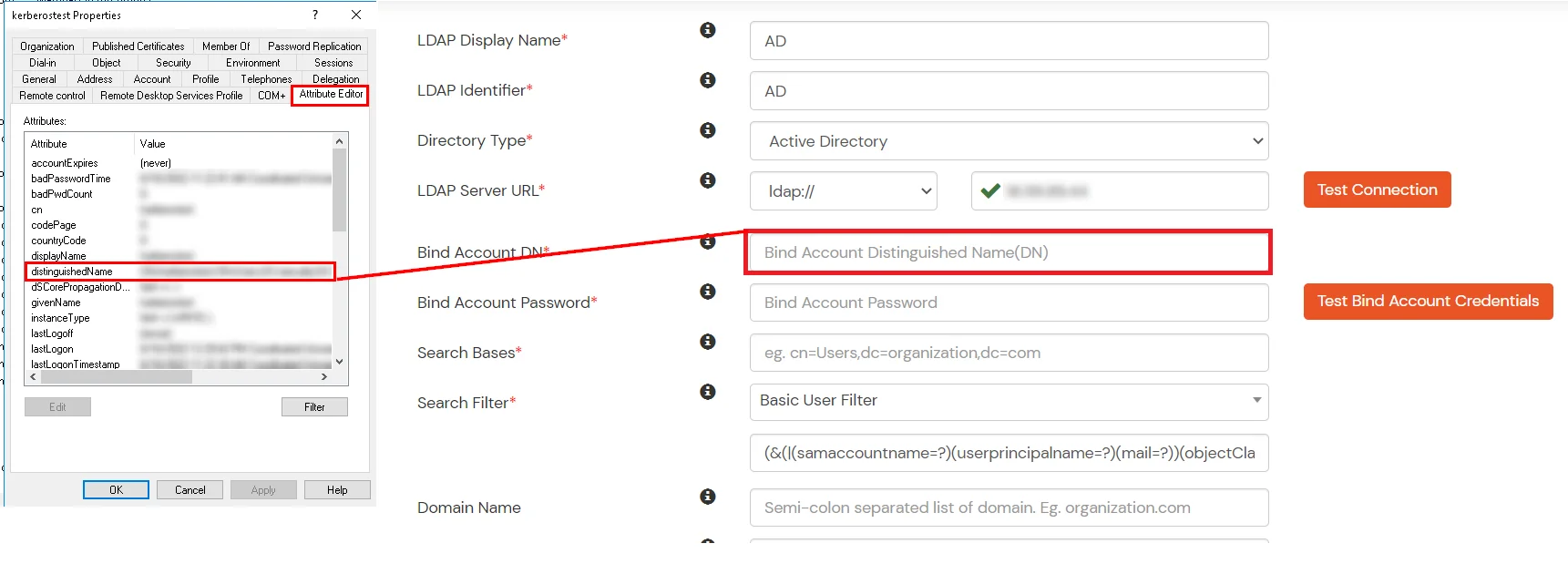
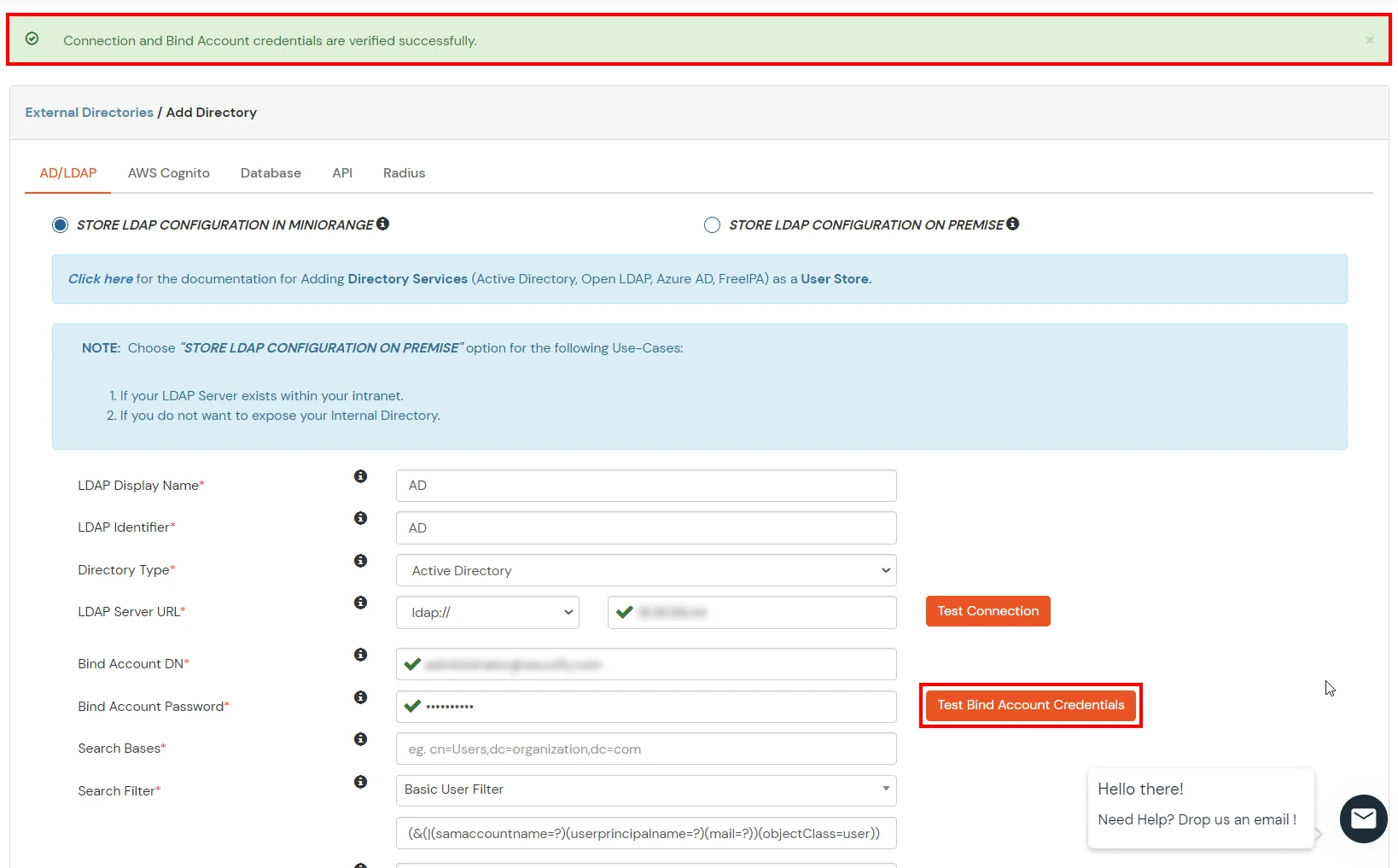
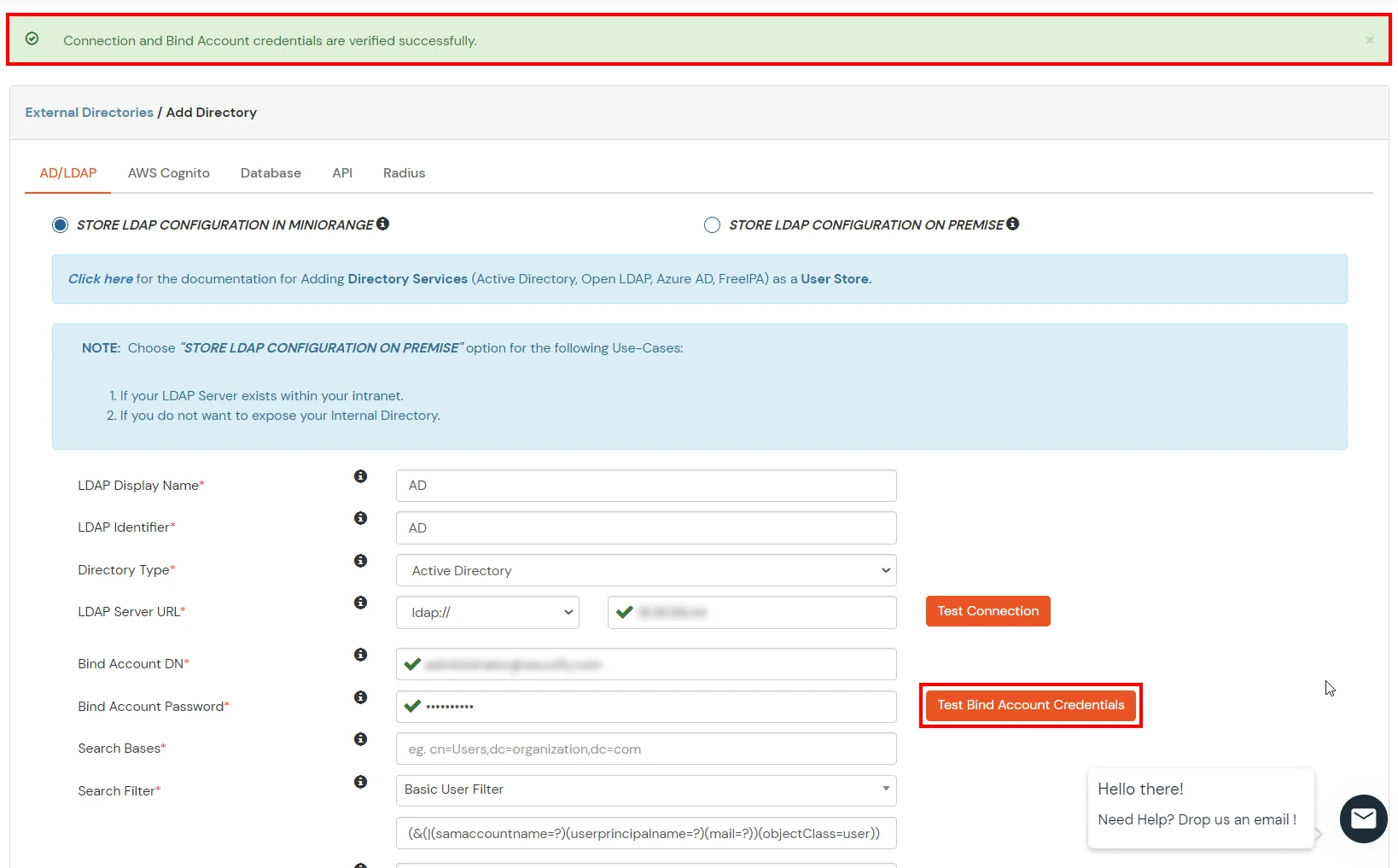
- Enter the valid Bind account Password.
- Click on the Test Bind Account Credentials button to verify your LDAP Bind credentials for LDAP connection.
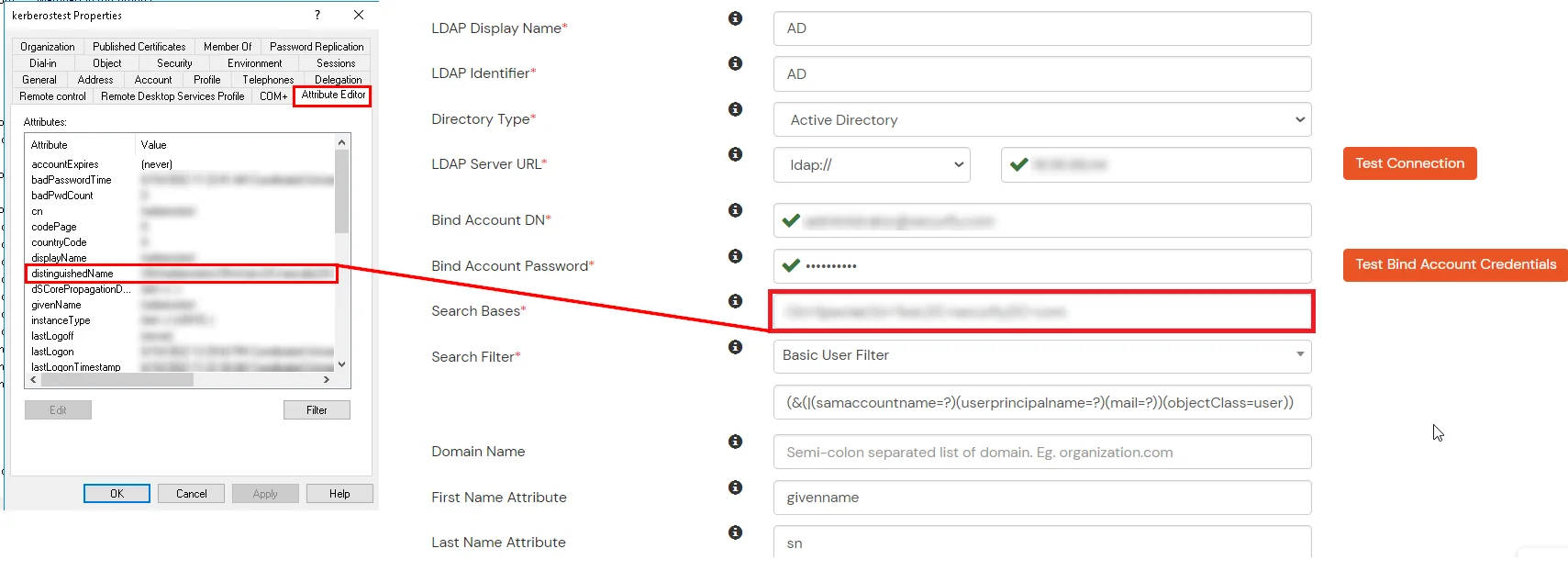
- Search Base is the location in the directory where the search for a user begins. You will get this from the same place you got your Distinguished name.
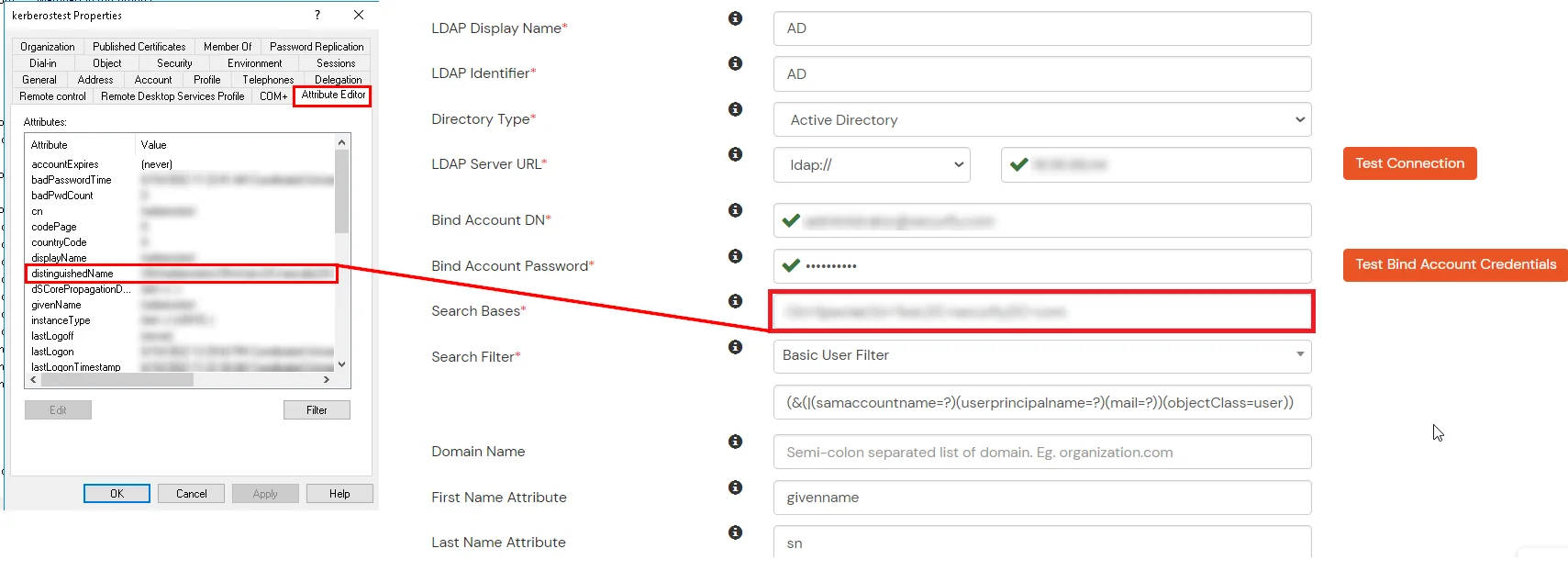
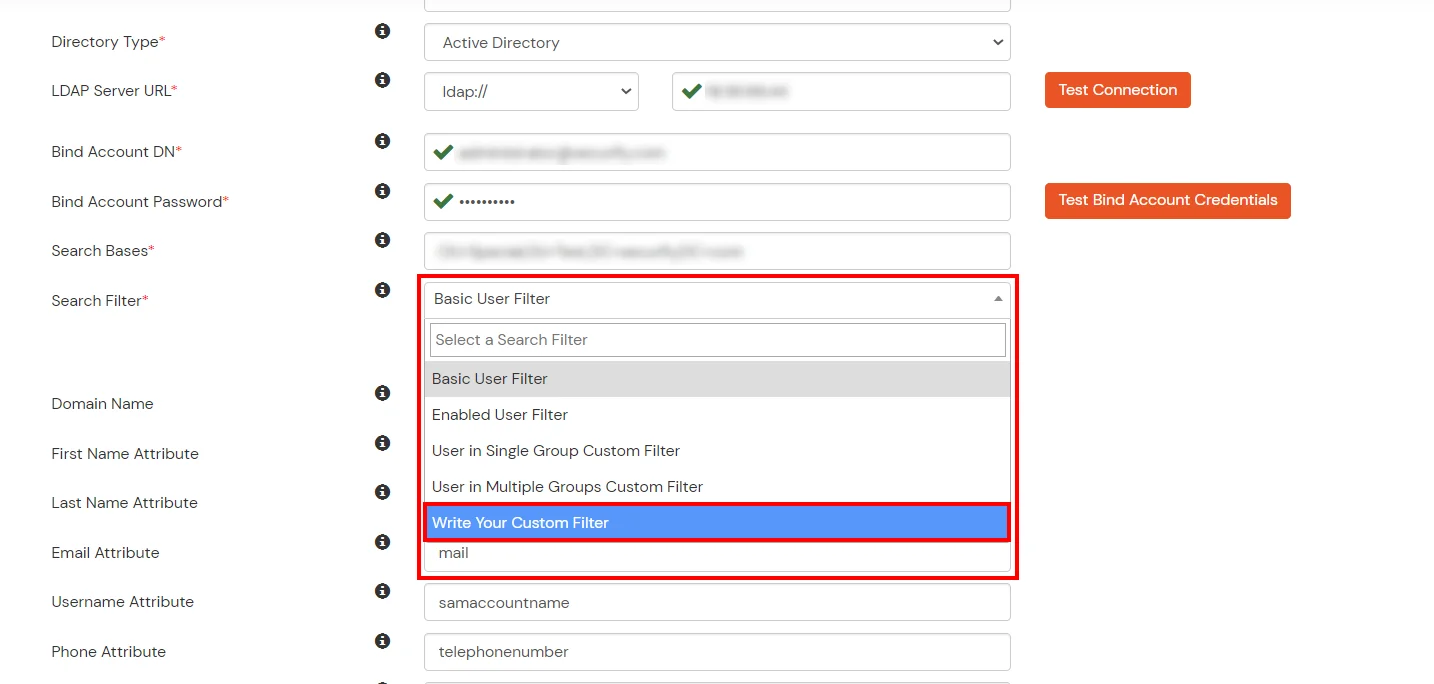
- Select a suitable Search filter from the drop-down menu. If you use User in Single Group Filter or User in Multiple Group Filter, replace the <group-dn> in the search filter with the distinguished name of the group in which your users are present. To use custom Search Filter select "Write your Custom Filter" option and customize it accordingly.
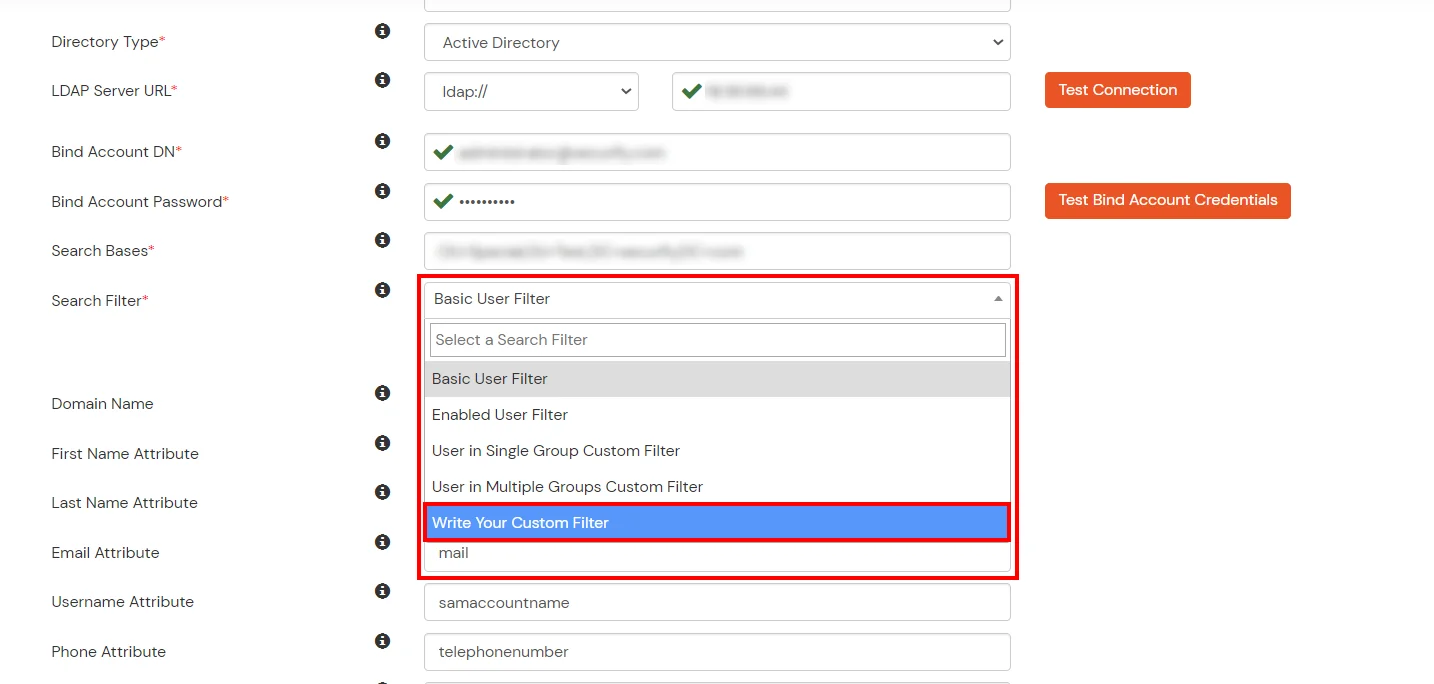
- Click on the Next button, or go to the Login Options tab.
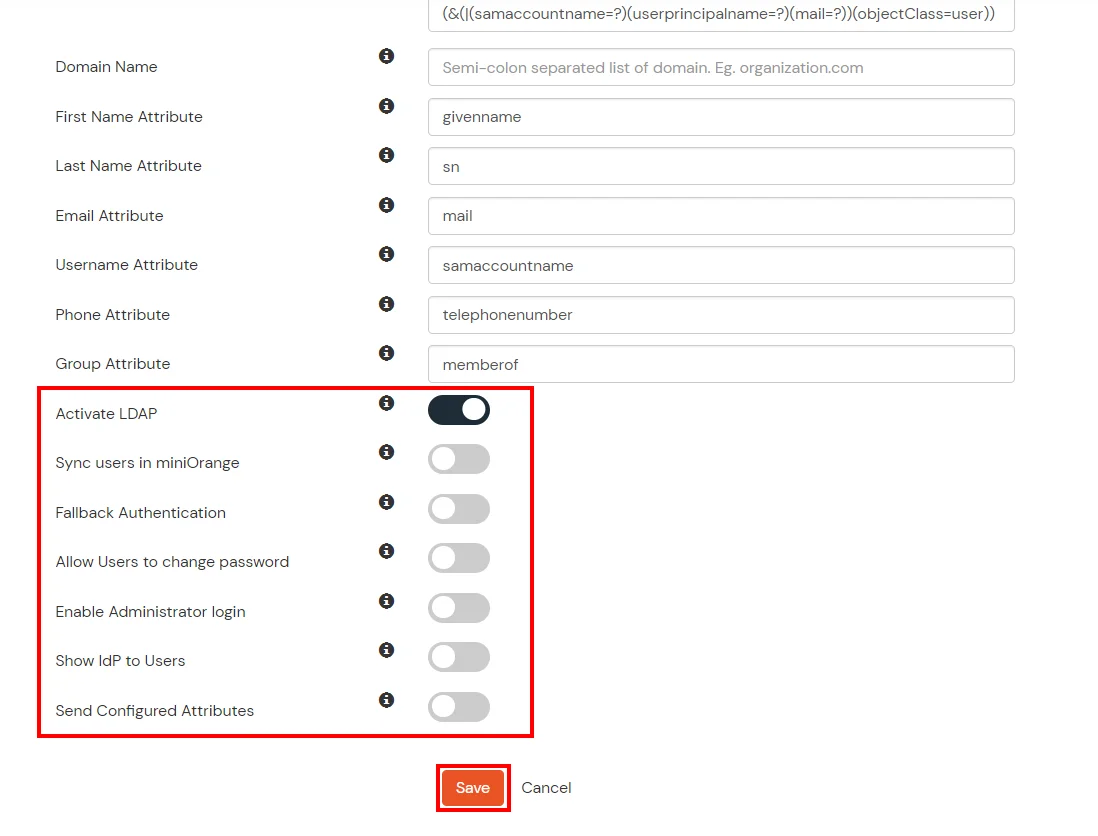
- You can also configure following options while setting up AD. Enable Activate LDAP in order to authenticate users from AD/LDAP. Click on the Next button to add user store.
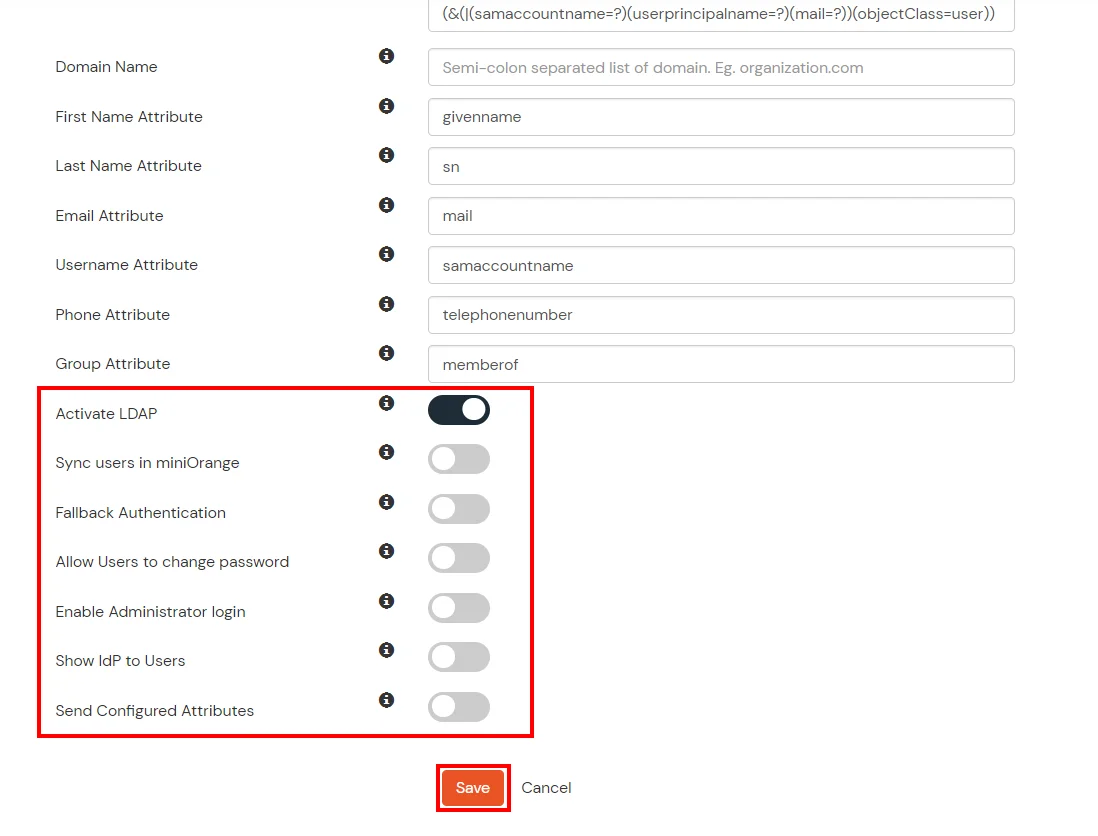
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute |
Description |
| Activate LDAP |
All user authentications will be done with LDAP credentials if you Activate it |
| Fallback Authentication |
If LDAP credentials fail then user will be authenticated through miniOrange |
| Enable administrator login |
On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users |
If you enable this option, this IdP will be visible to users |
| Sync users in miniOrange |
Users will be created in miniOrange after authentication with LDAP |
- Click on the Next button, or go to the Attributes tab.
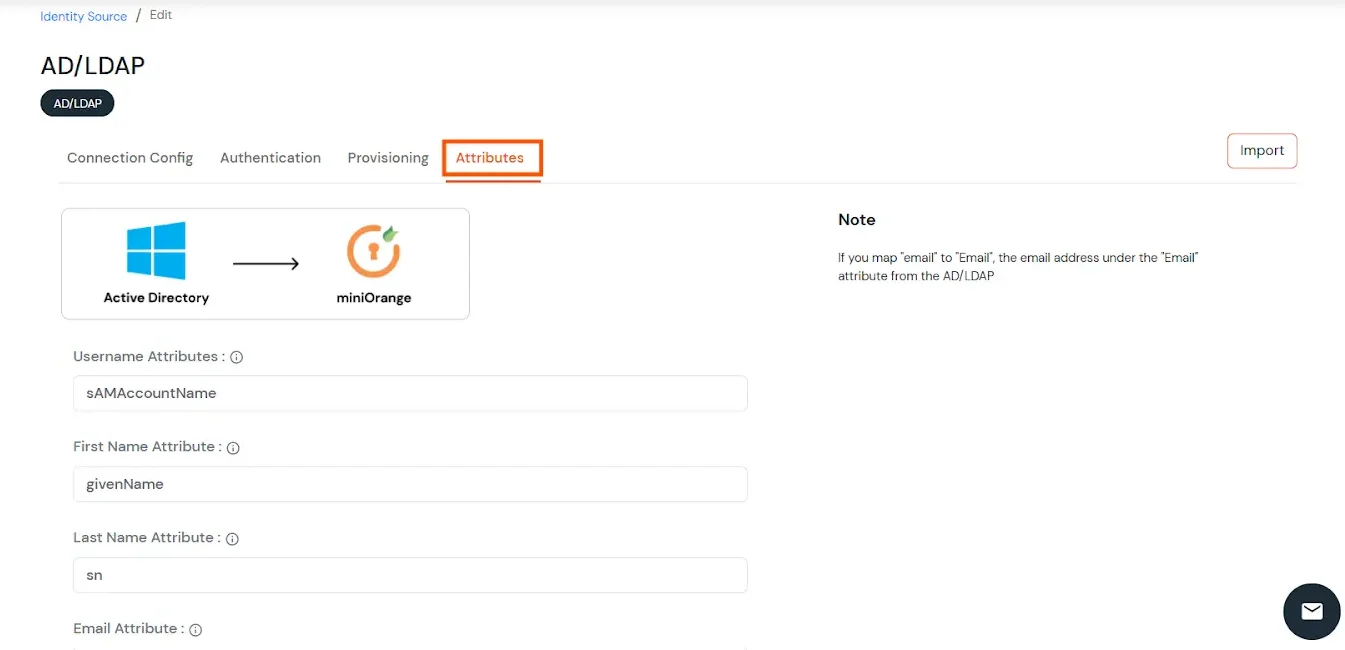
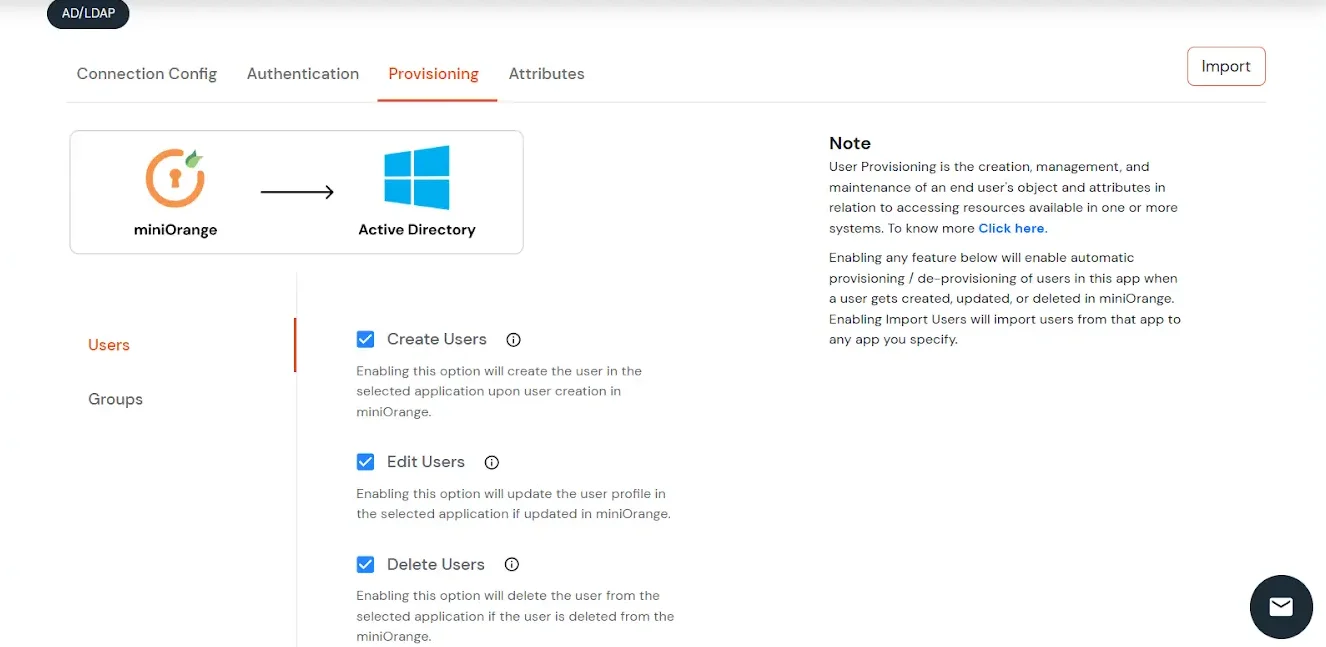
Attributes Mapping from AD
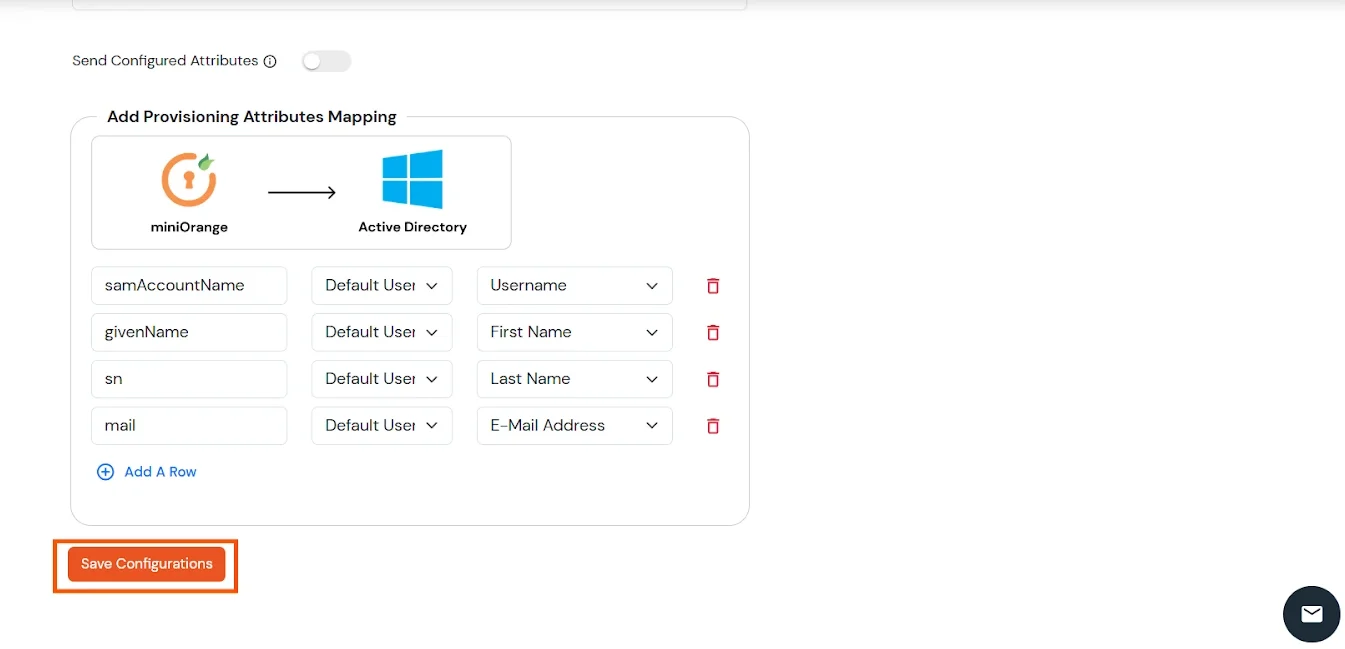
User Import and Provisioning from AD
- If you want to set up provisioning, click here for detailed information. We will skip this step for now.
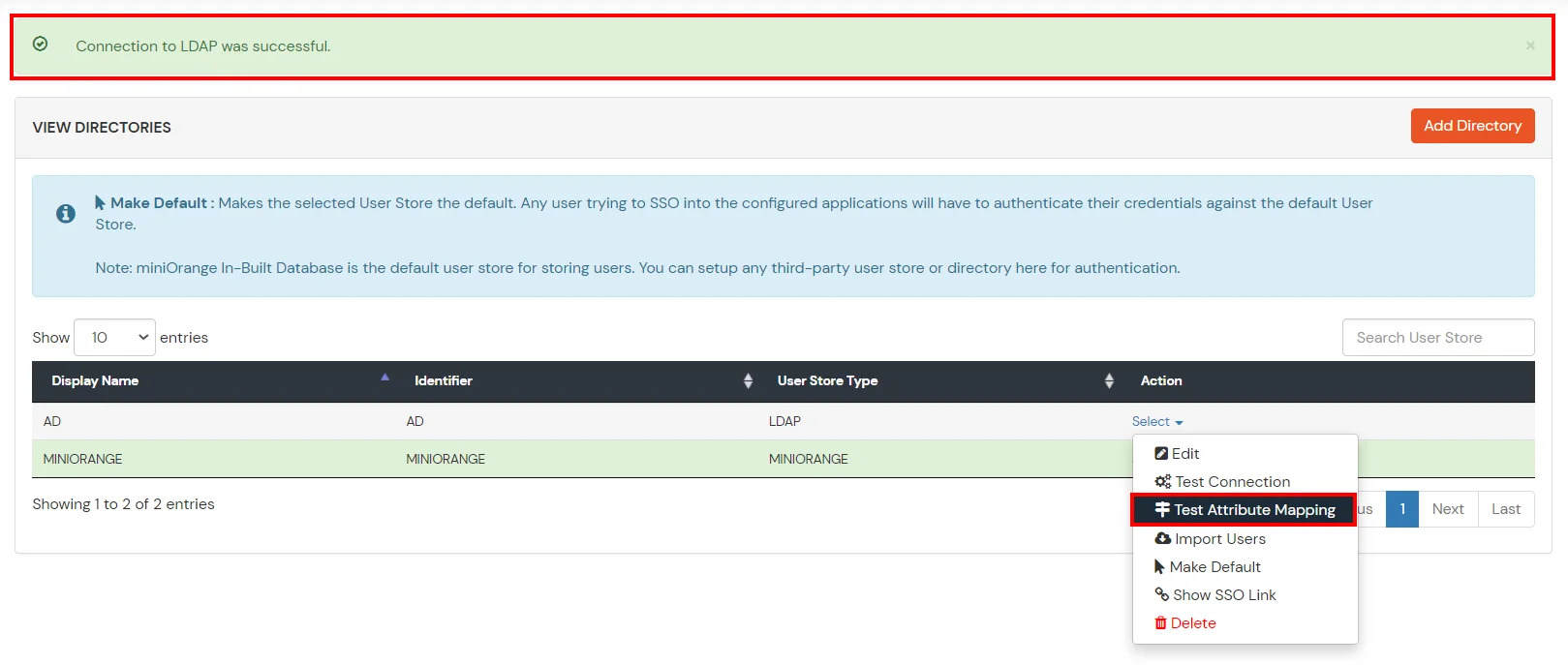
Test Connections
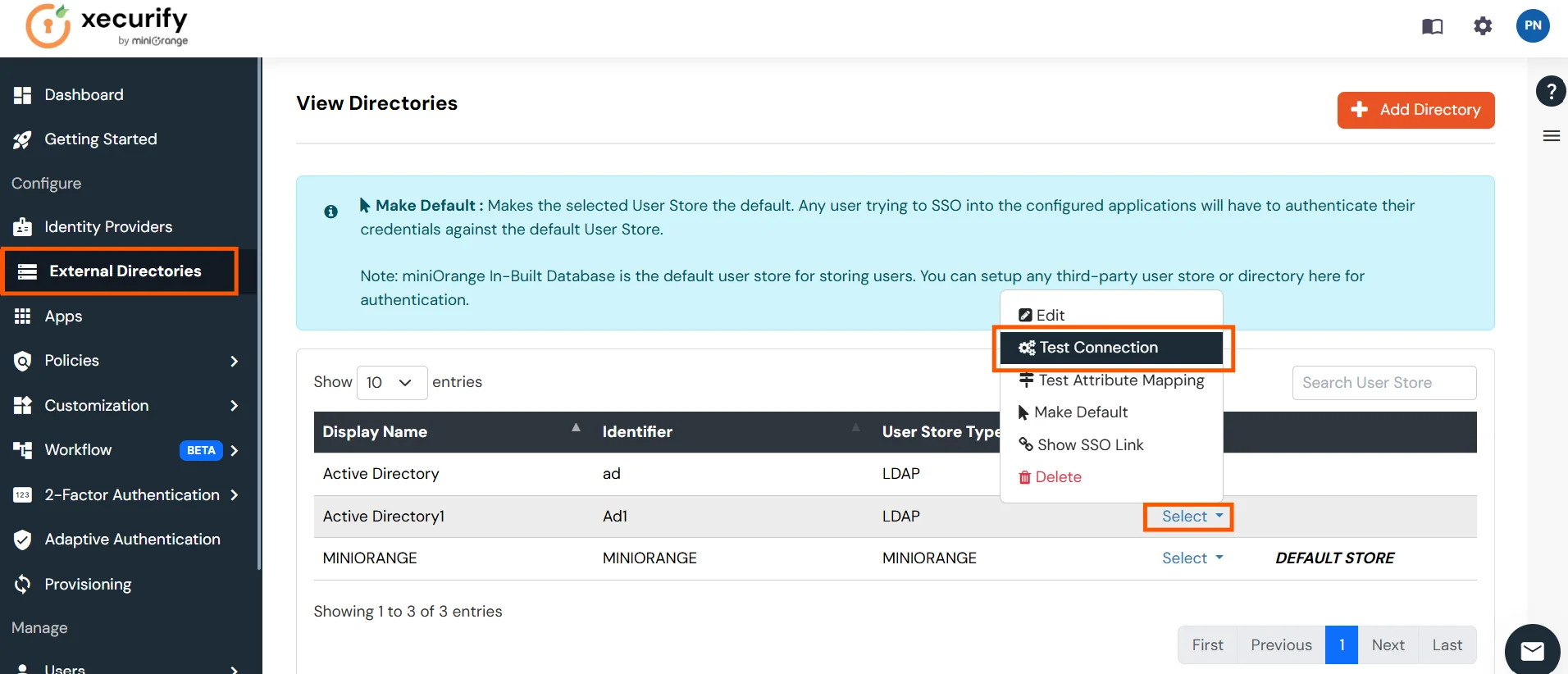
- You will see a list of directories under Identity Providers. From the dropdown, select AD/LDAP Directories, search for your configured directory, click the three dots next to it, and select Test Connection.
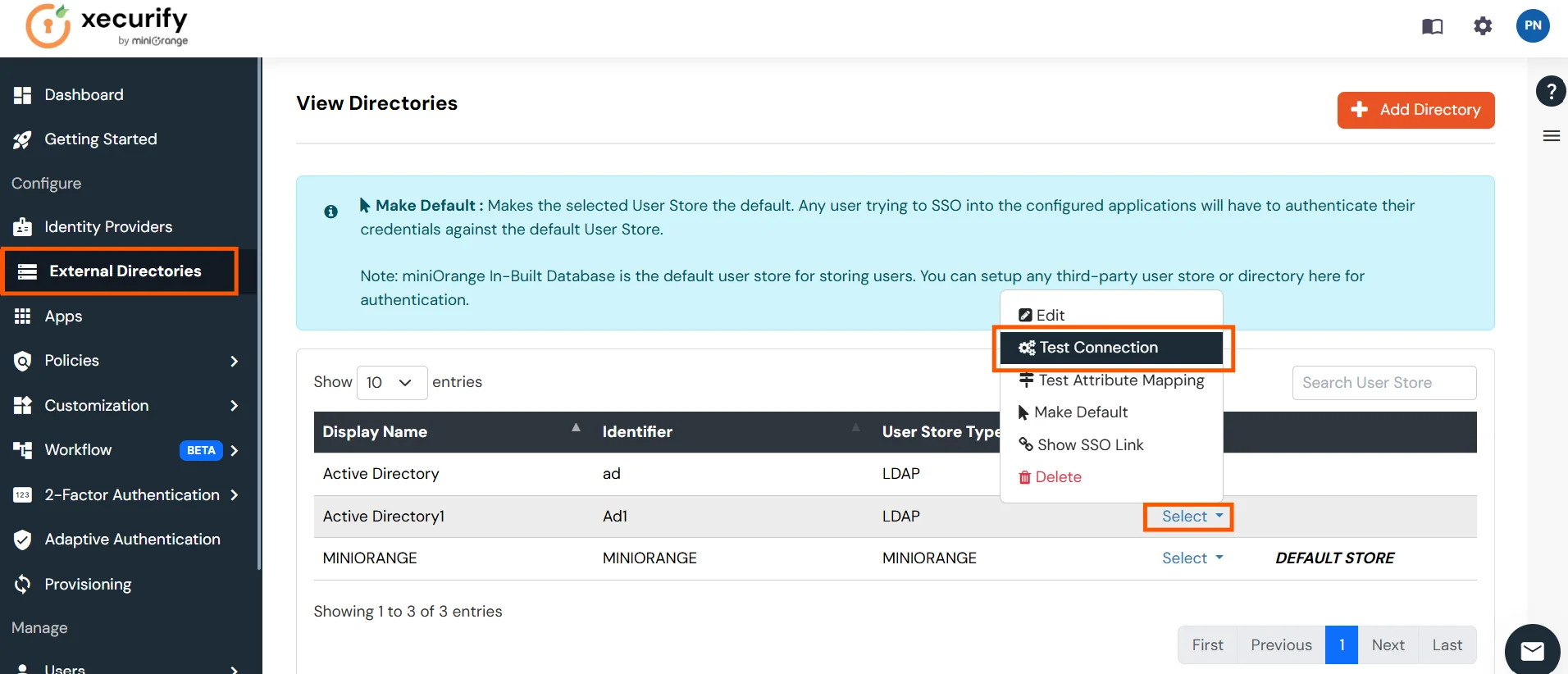
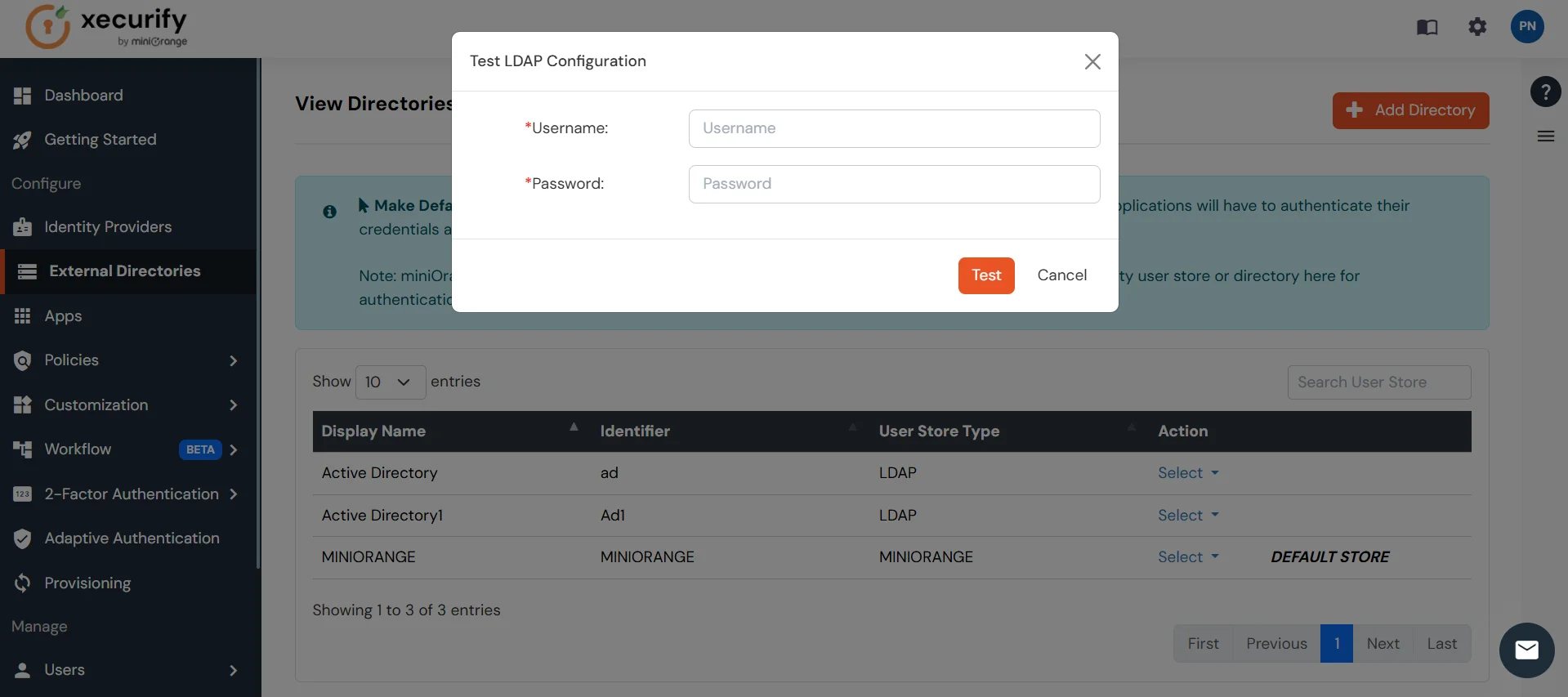
- A pop-up appears prompting you to enter a username and password to verify your LDAP configuration.
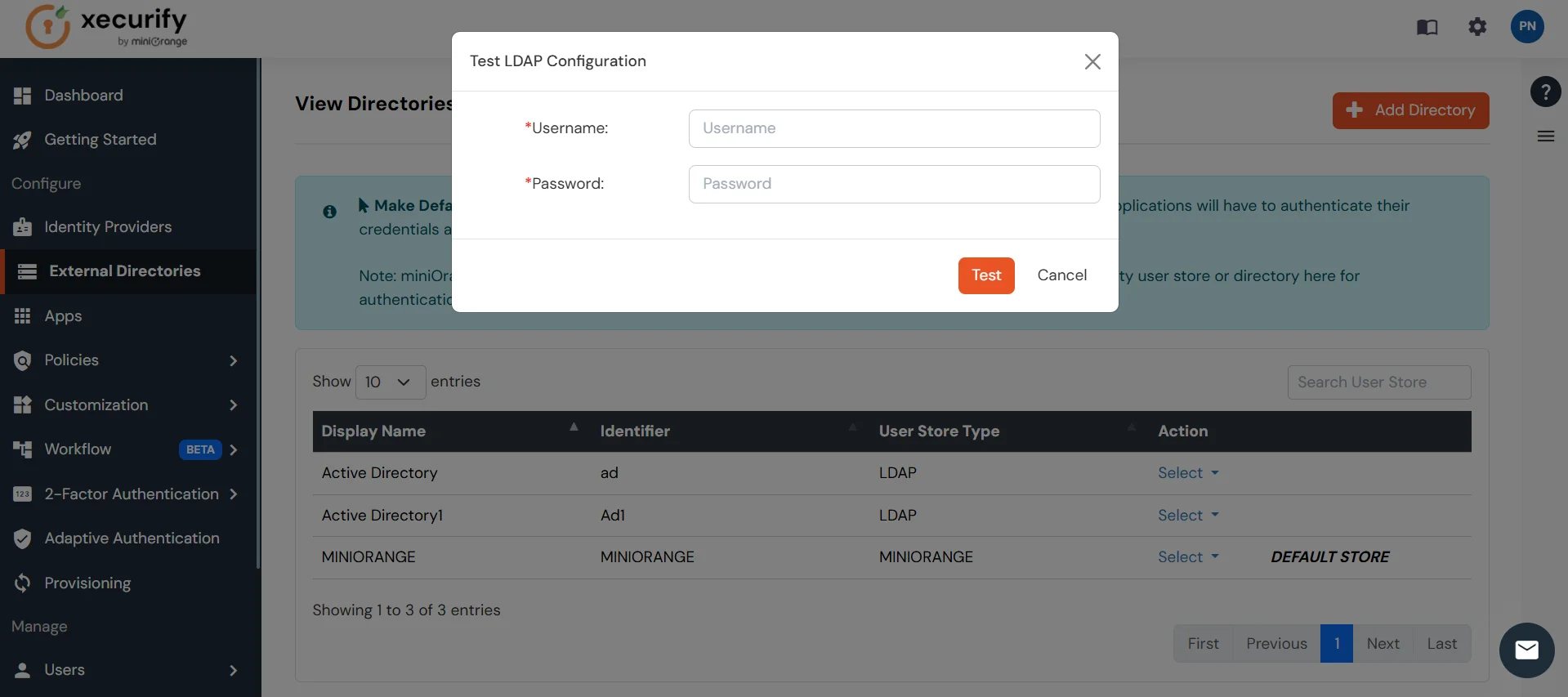
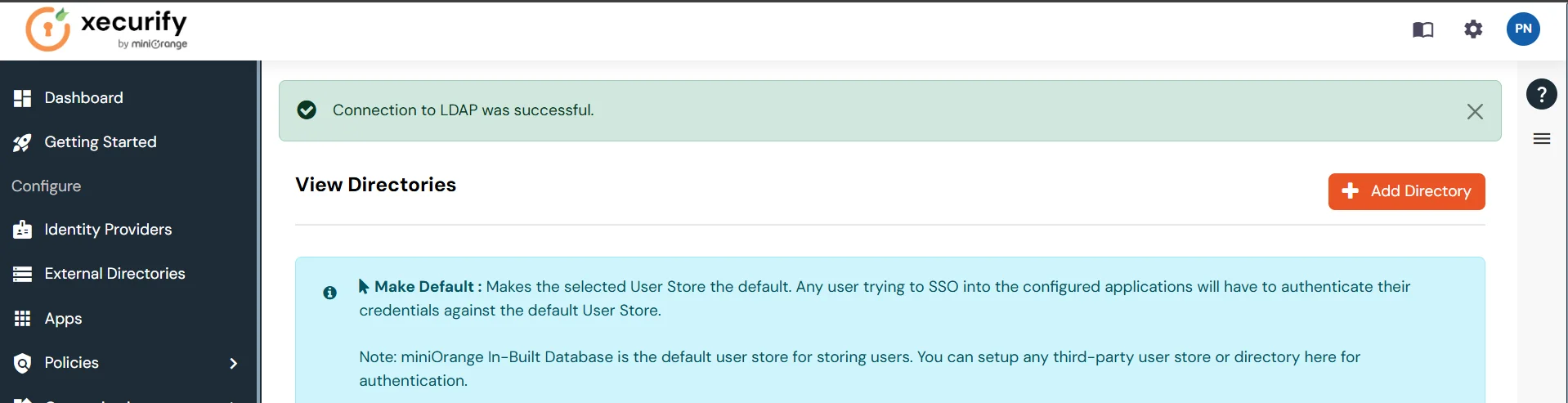
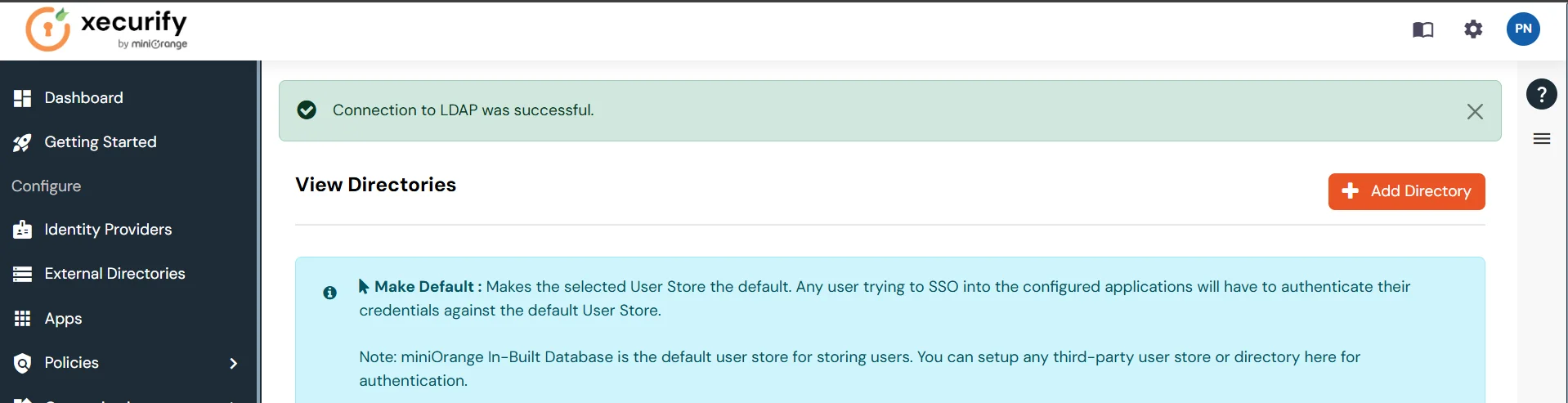
- On Successful connection with LDAP Server, a success message is shown.
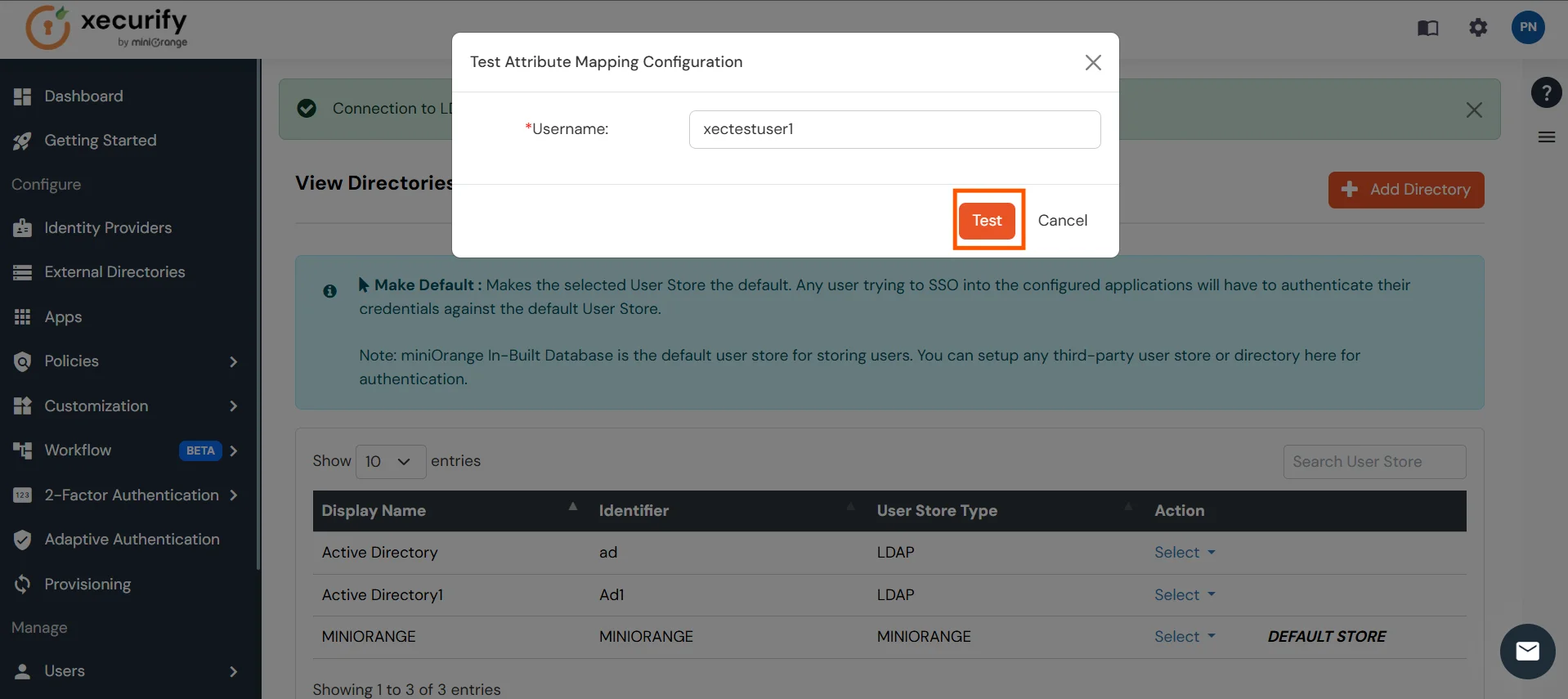
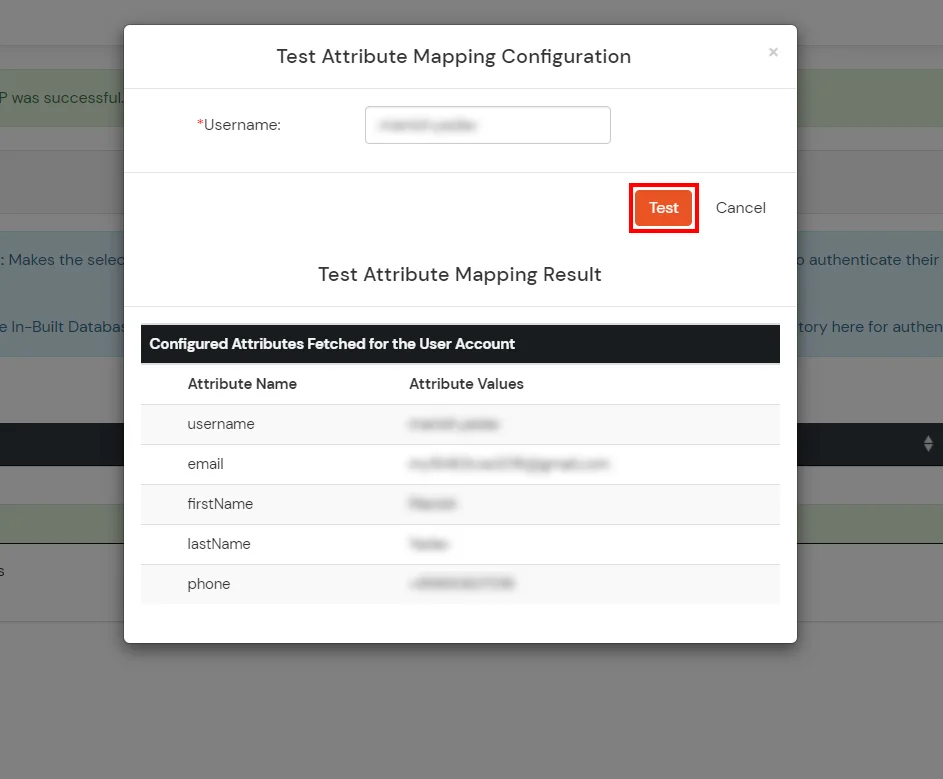
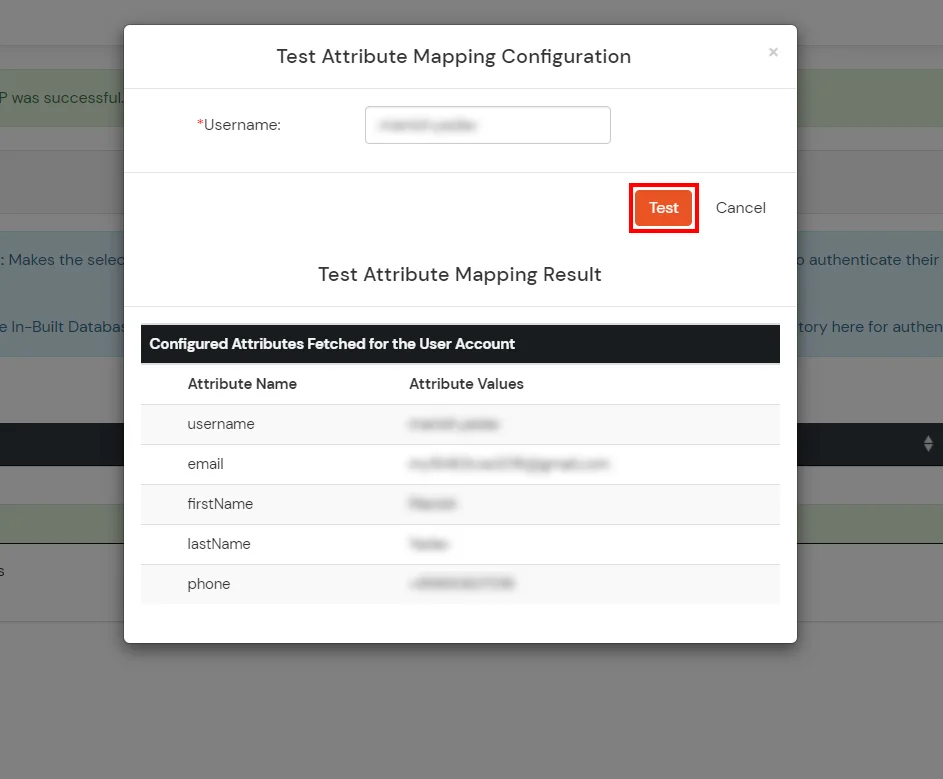
Test Attribute Mapping
- You will see a list of directories under Identity Providers. From the dropdown, select AD/LDAP Directories, search for your configured directory, click the three dots next to it, and select Test Attribute Mapping.
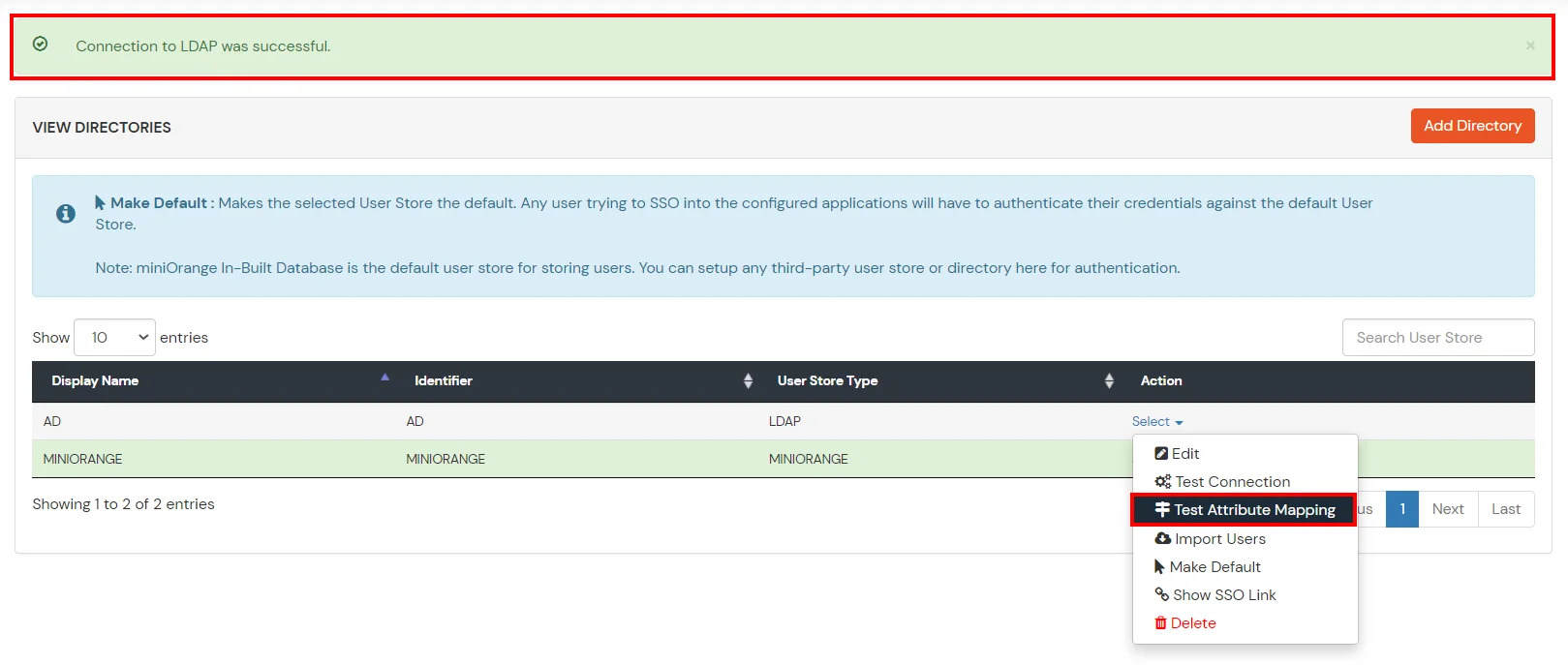
- A pop‑up appears to enter a username and click Test.
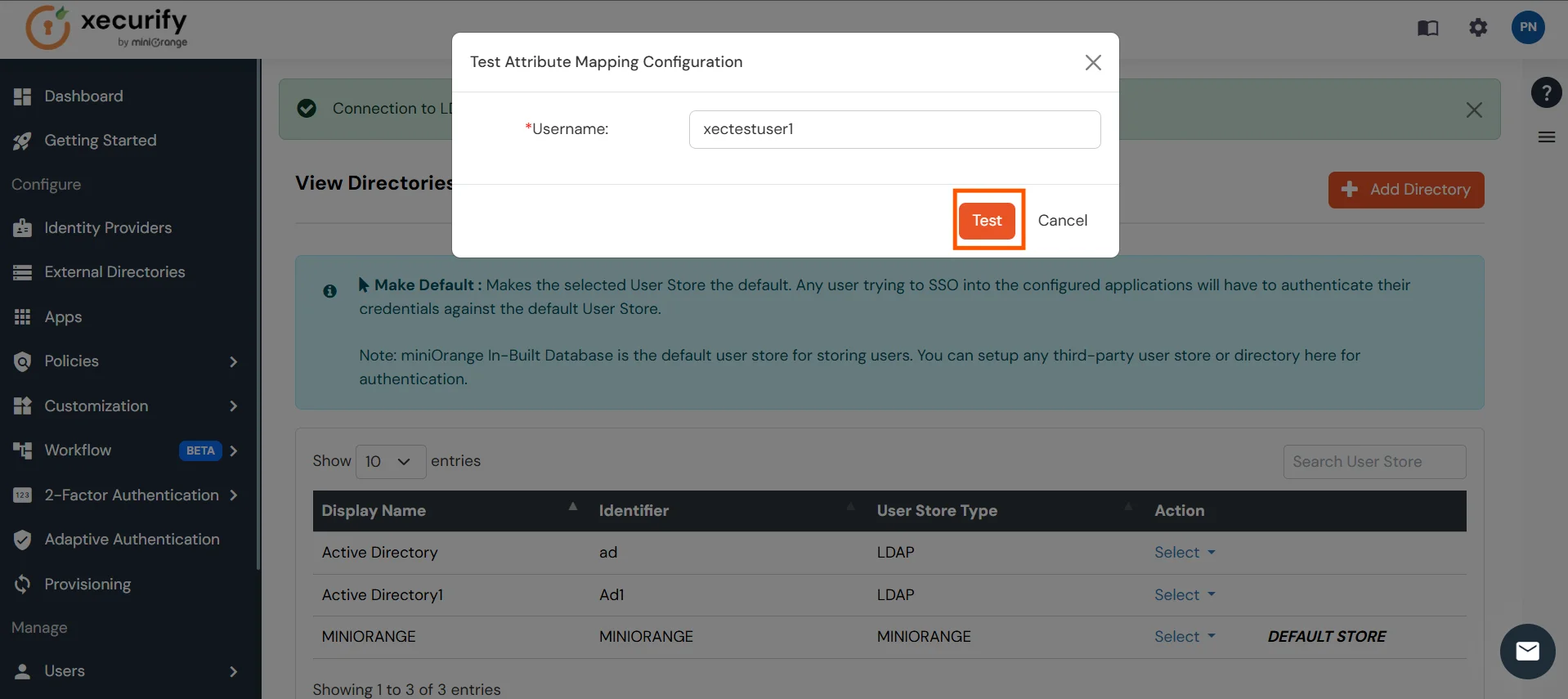
- The Test Attribute Mapping Result will be displayed.
Set up AD as External Directory configuration is complete.
Note: Refer our guide to setup LDAP on windows server.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
Need help to configure IP / Device / Location / Time Restriction for Office 365?
Contact us or email
us at idpsupport@xecurify.com and we'll help
you setting it up
in no time.
External References