Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
×Citrix Virtual Apps and Desktops provide granular access control, advanced system monitoring and an inherently secure architecture by providing remote access to Windows and Linux apps and desktops secured in the datacenter. Citrix Virtual Apps and Desktops enable IT to deliver on-demand apps and desktops to any device.
VDI is a desktop-centric service that hosts user desktop environments on remote servers and storage systems, which are accessed over a network using a remote display protocol. Enterprises are converting physical desktops to Virtual Desktop Infrastructure (VDI) since it provides efficient hardware utilization and centralized management while reducing costs.
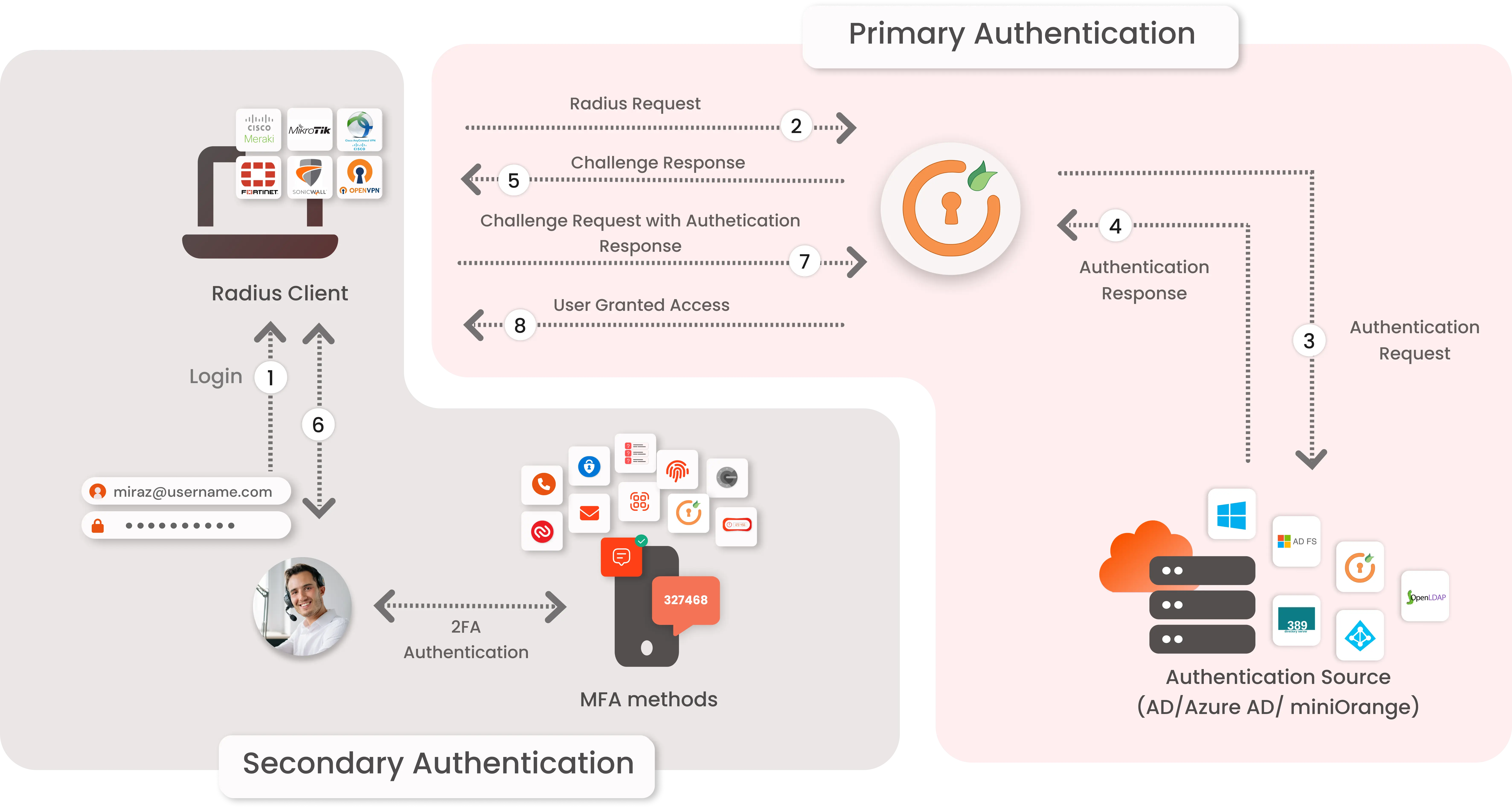
Due to the COVID-19, many companies need to find some ways to enable remote working. VDI solution is one of their choices. Citrix Virtual Apps & Desktops can provide a quick win VDI solution but it still need to spend efforts to setup for some authentications and security settings, e.g. MFA. For some SME companies, they may not have their own RADIUS (Remote Authentication Dial-In User Service) server and OTP (one-time password) server to enable 2FA/MFA. miniOrange provides a ready to use Two-Factor Authentication - 2FA solution for Sangfor aDesk VDI using RADIUS Server which enables an extra layer of authentication to VDI logins & ensures that you roll out secure access to your employees within minutes.
To use miniOrange Two-FActor Authentication (2FA) you can enable RADIUS authentication in Citrix Virtual Apps & Desktops and configure policies in miniOrange to enable or disable 2FA for users.
The 2-factor authentication can be of two types depending on the Application.
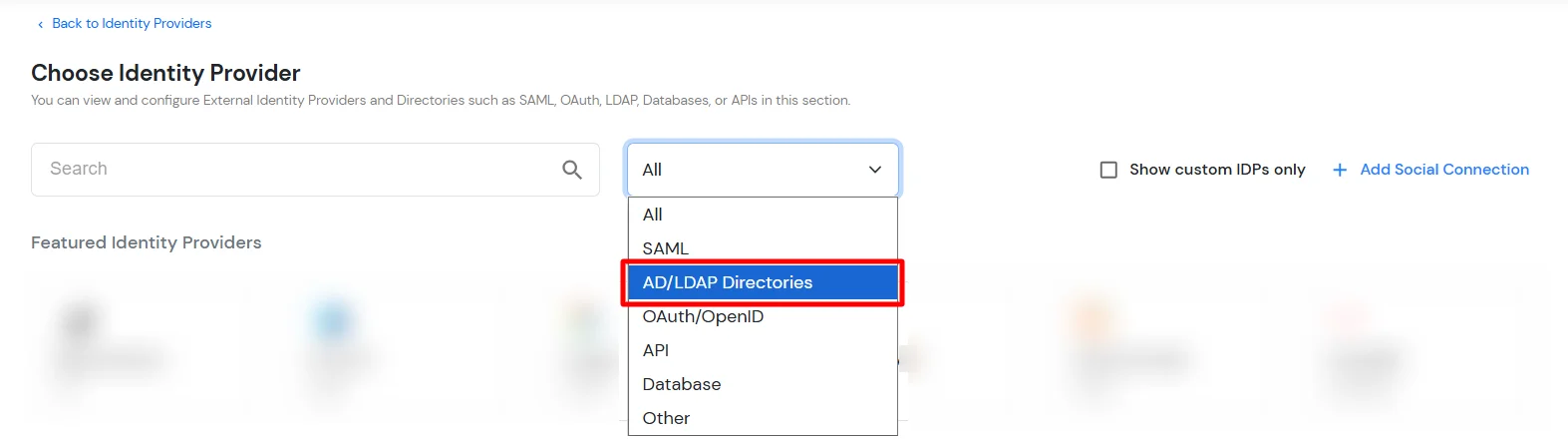
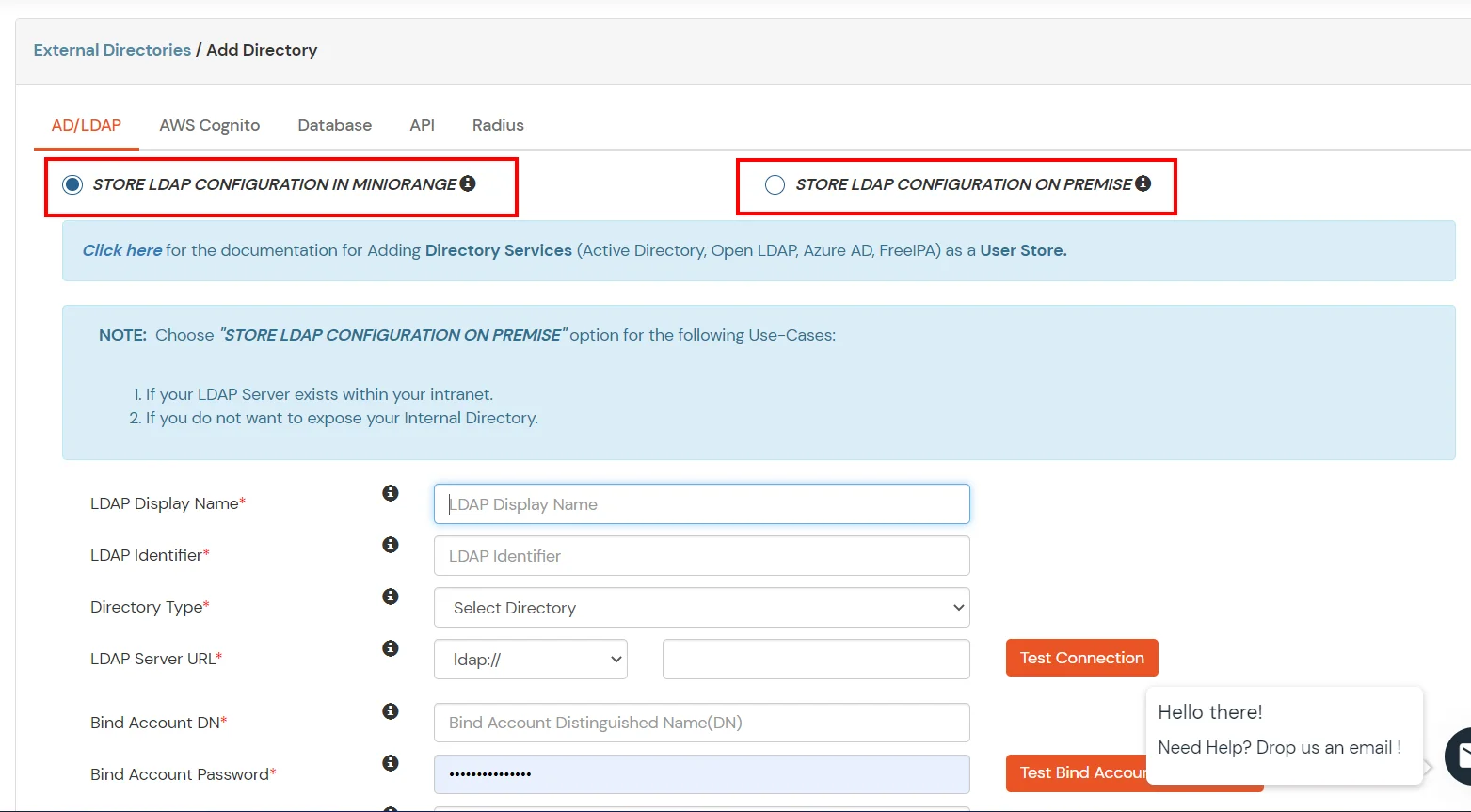
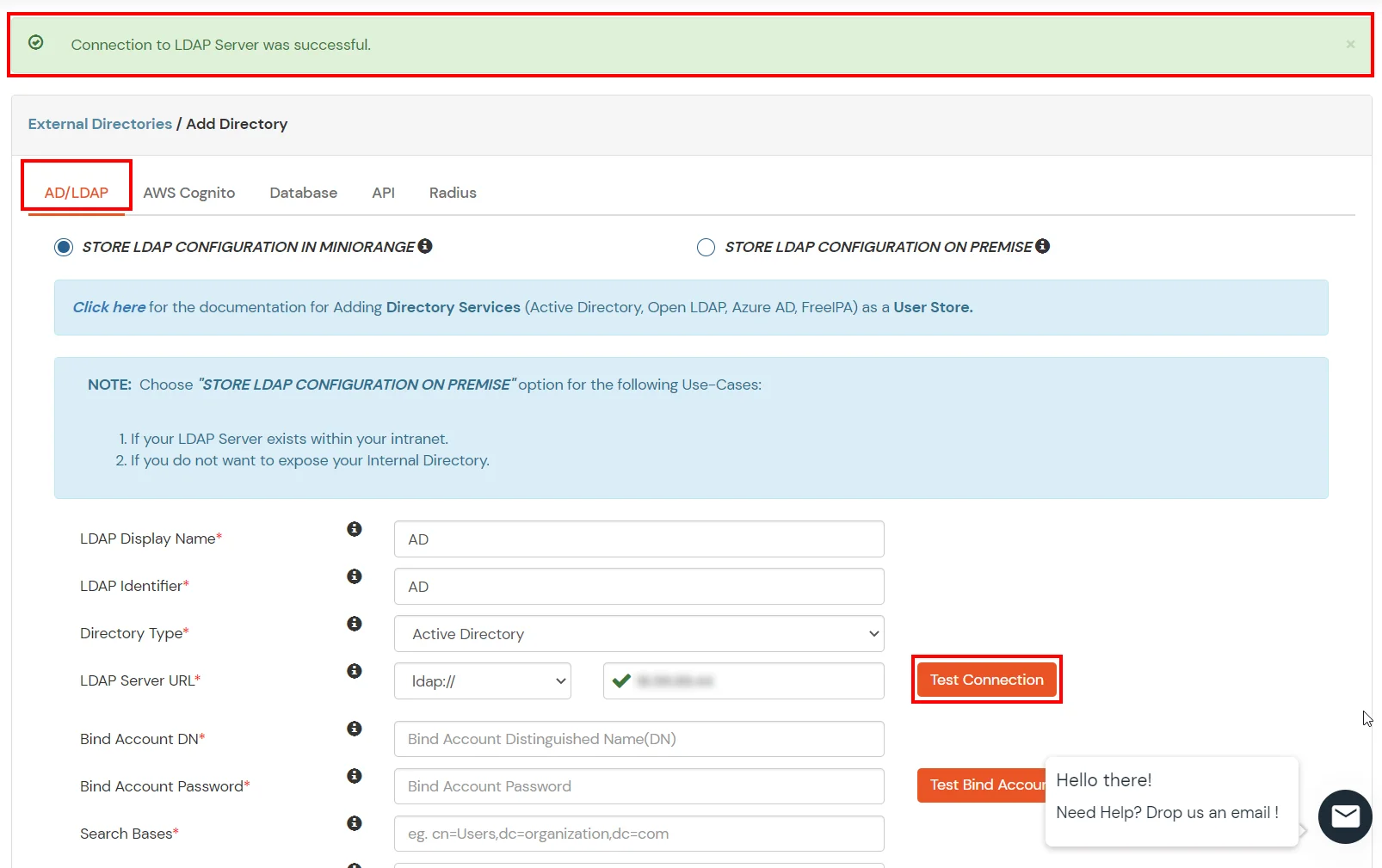
miniOrange provides user authentication from various external directories such as miniOrange Directory, Microsoft AD, Microsoft Entra ID/LDAP, AWS Cognito and many more.
Can't find your Directory? Contact us on idpsupport@xecurify.com

| Client Name: | Any name for your reference. |
| Client IP: | IP address of VPN server which will send Radius authentication request. |
| Shared Secret: | Security key. For Eg. "sharedsecret" (Keep this with you, you will need to configure same on VPN Server). |
| Do not Support Challenge: | Keep this Unchecked. |
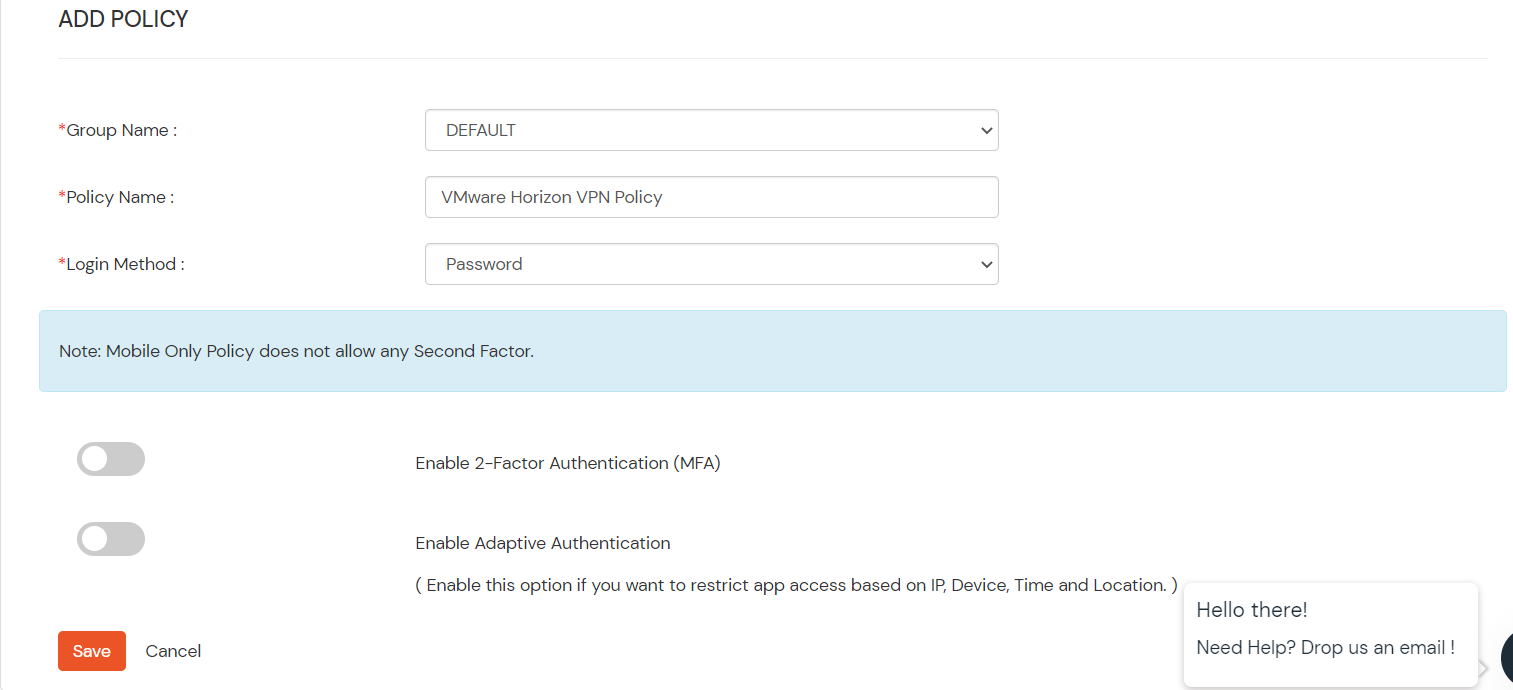
| Group Name: | Group for which the policy will apply. |
| Policy Name: | Any Identifier that specifies policy name. |
| Login Method | Login Method for the users associated with this policy. |
| Enable 2-Factor Authentication | Enables Second Factor during Login for users associated with this policy. |
| Enable Adaptive Authentication | Enables Adaptive Authentication for Login of users associated with this policy. |
Only For On-Premise Version
Step 1: Open Firewall Ports.
| Label | The name of this configuration. Eg:miniOrange Radius |
| Hostname/Address | For on-premise version: IP of server where IDP(miniOrange) is installed For cloud version: Contact us at info@xecurify.com to get the IP |
| Authentication Port | Enter 1812 (or whichever port configured on your miniOrange Authentication Proxy). |
| Authentication type | Must be PAP. |
| Shared secret code | Enter the Shared secret that we used to configure RADIUS app in miniOrange IDP. In step 1 we configured the shared secret as "sharedsecret" |
| Server timeout (in seconds) | Increase the timeout to 90 seconds. |
| Max attempts | Number of times to send authentication request. Must be 1. |
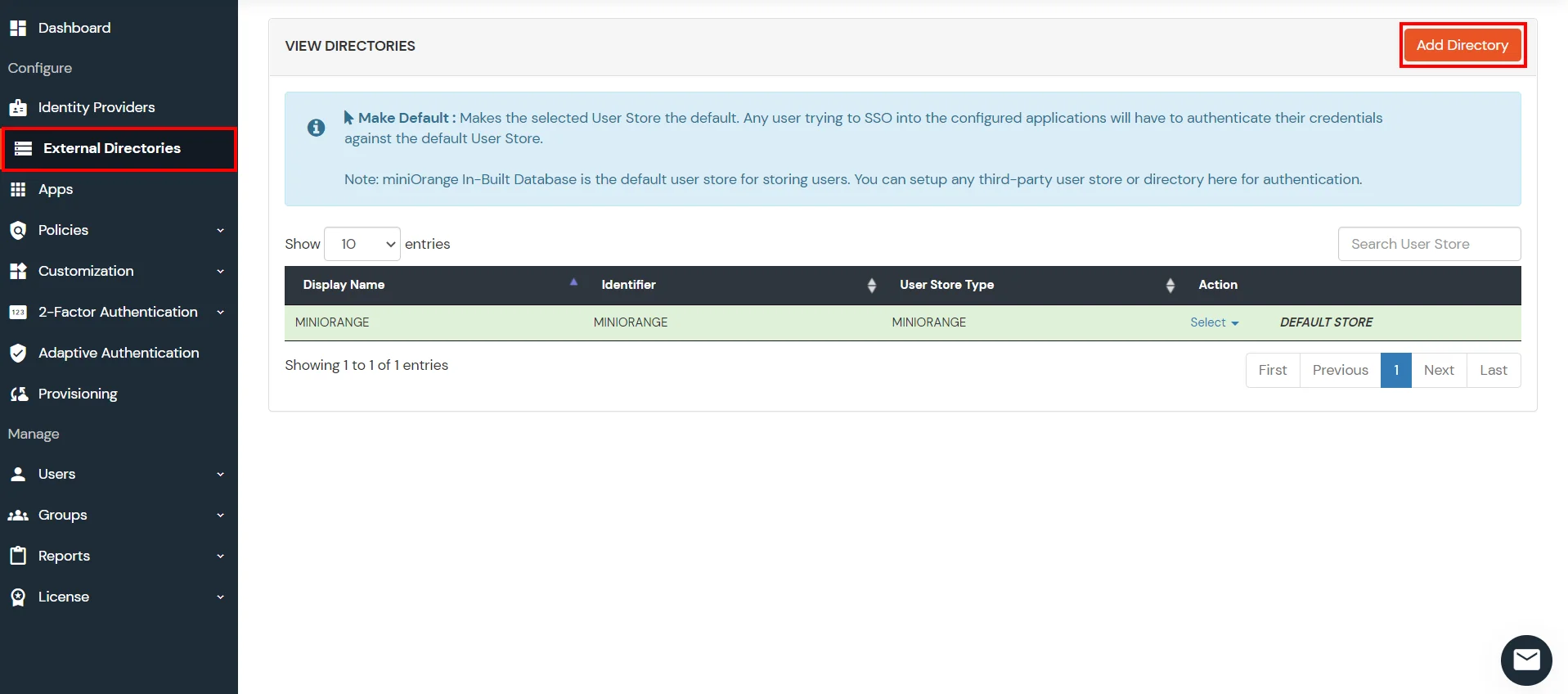
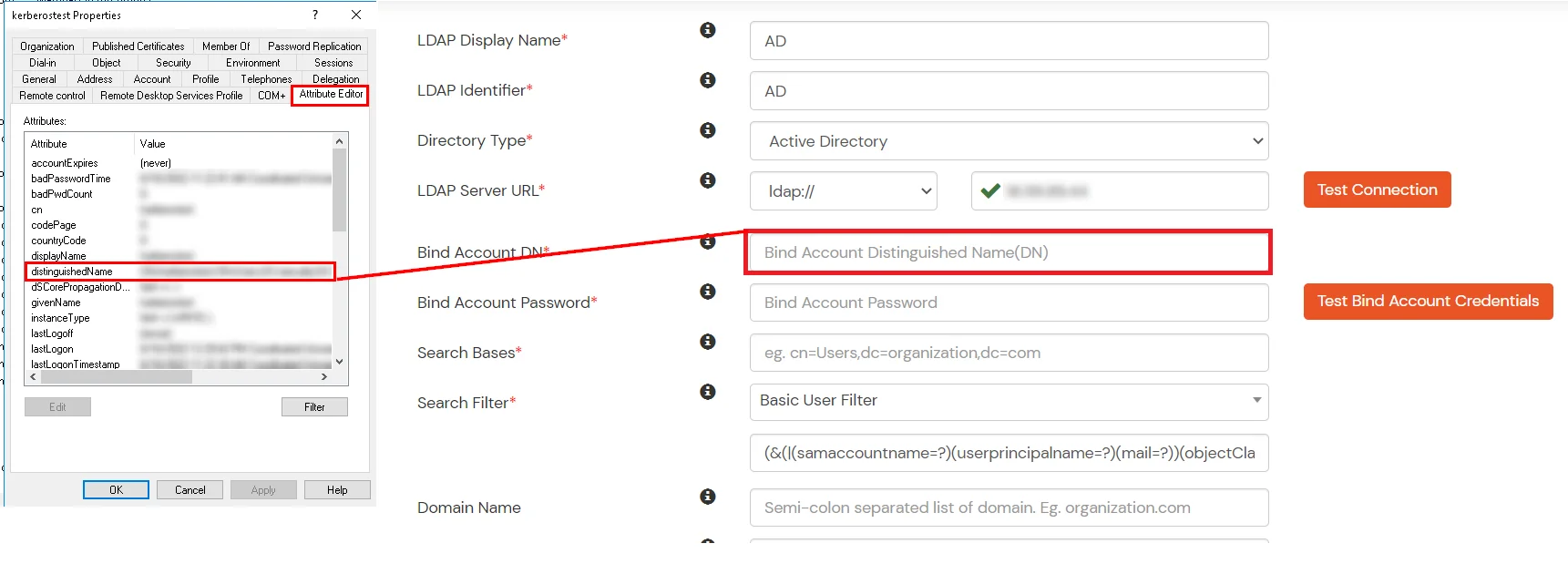
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
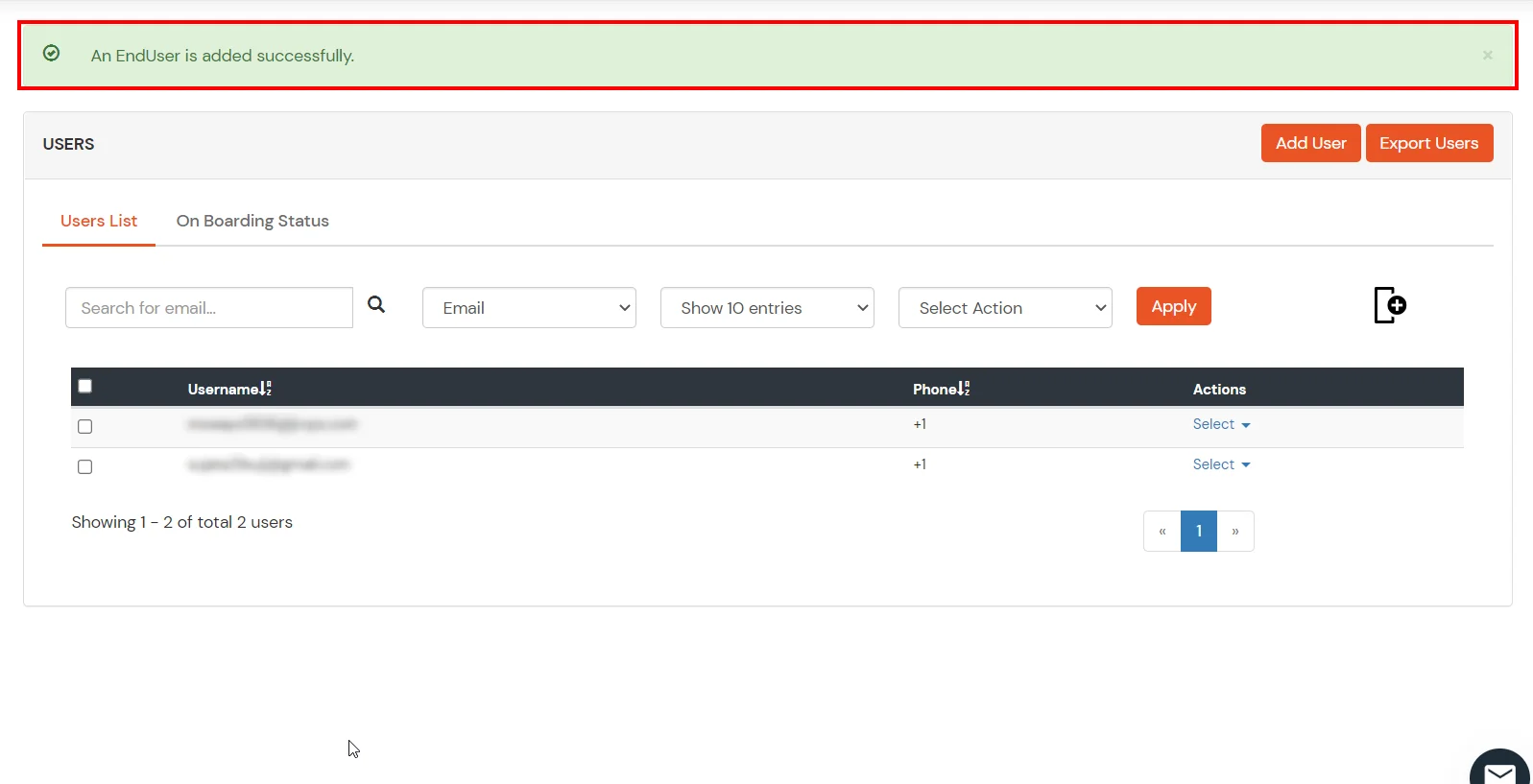
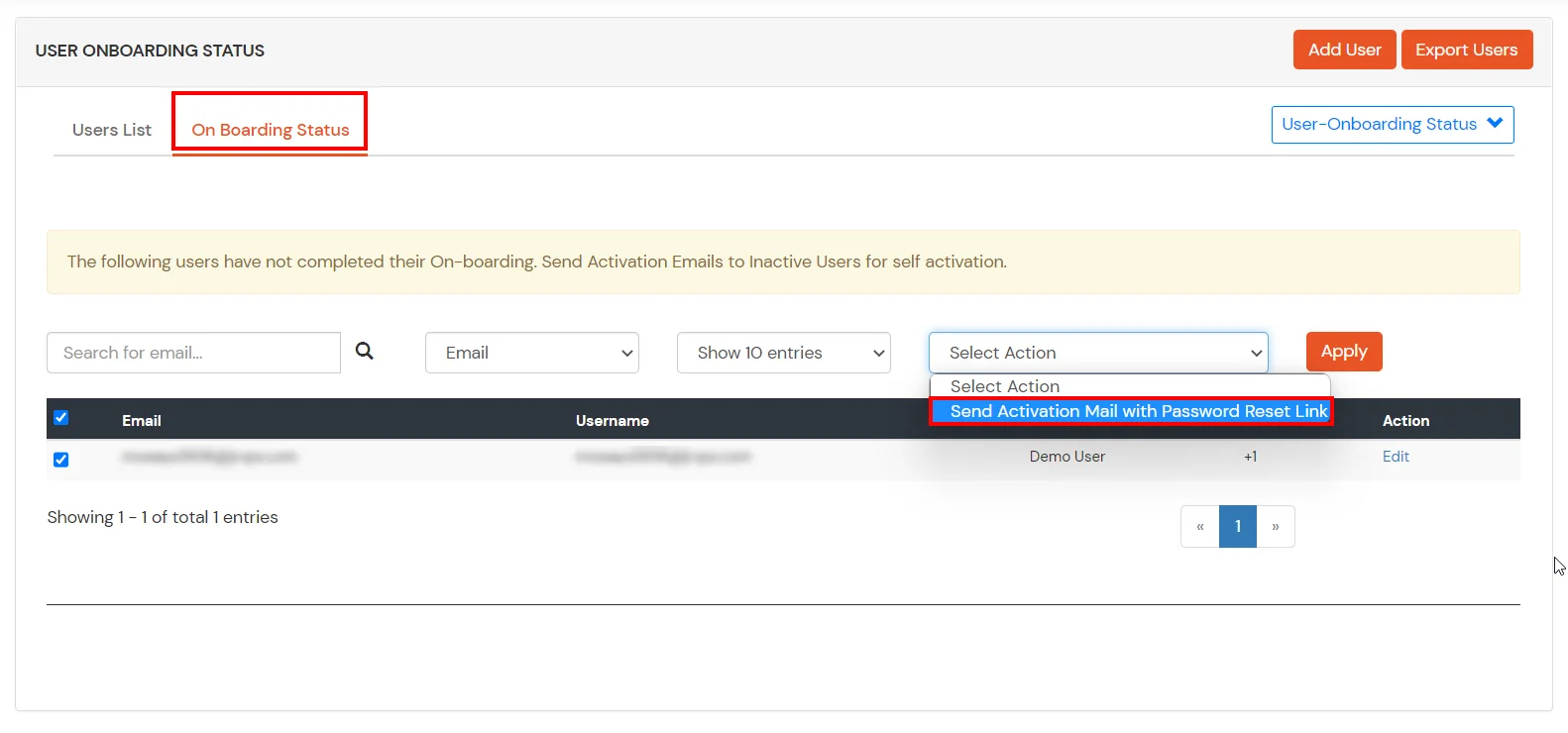
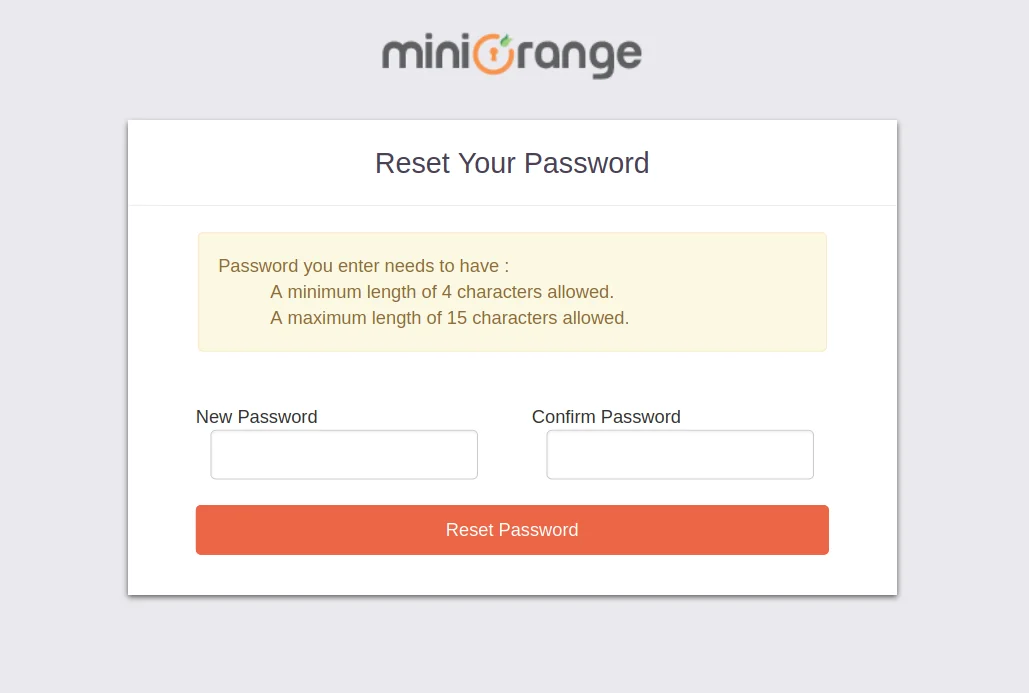
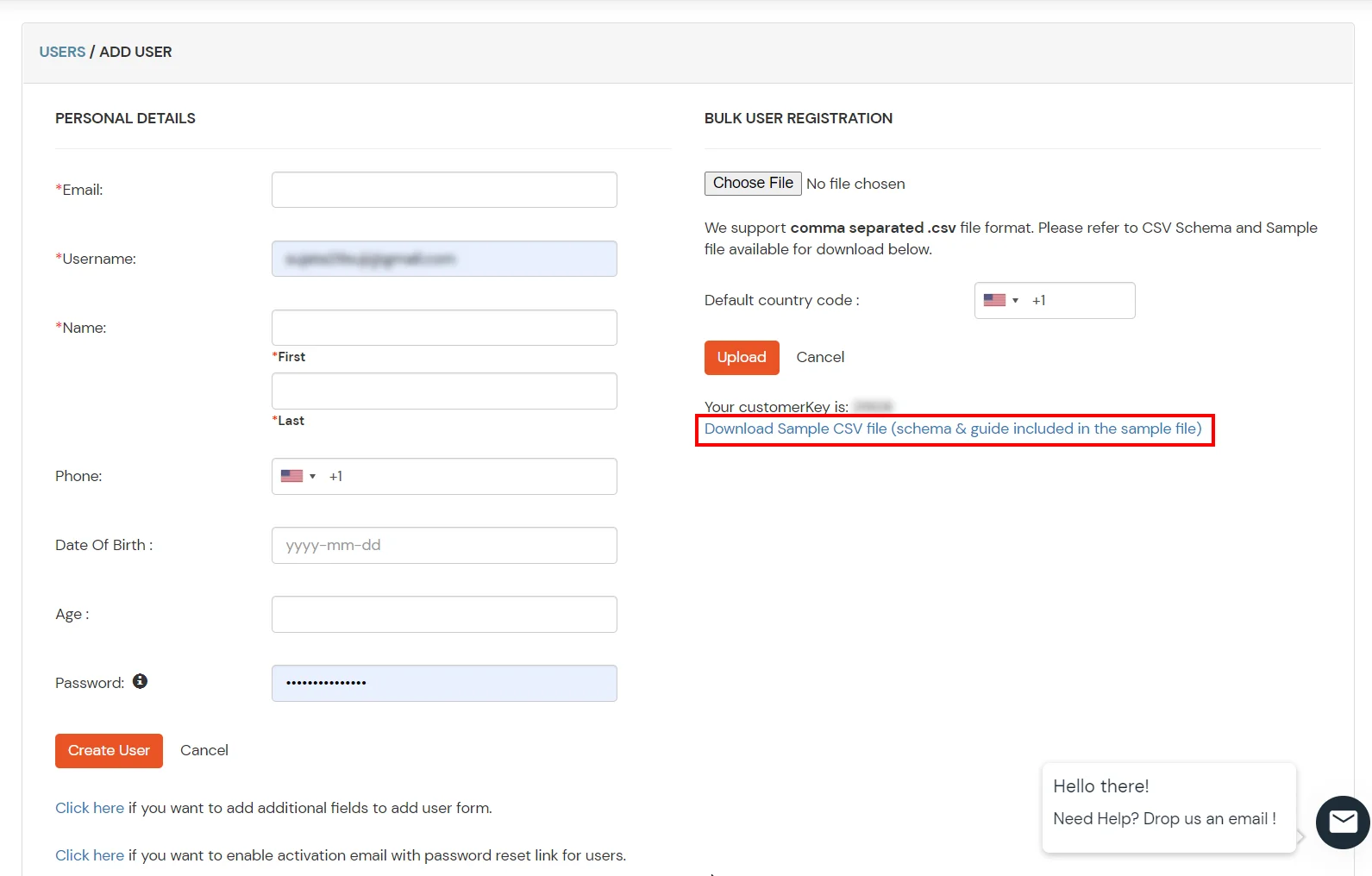
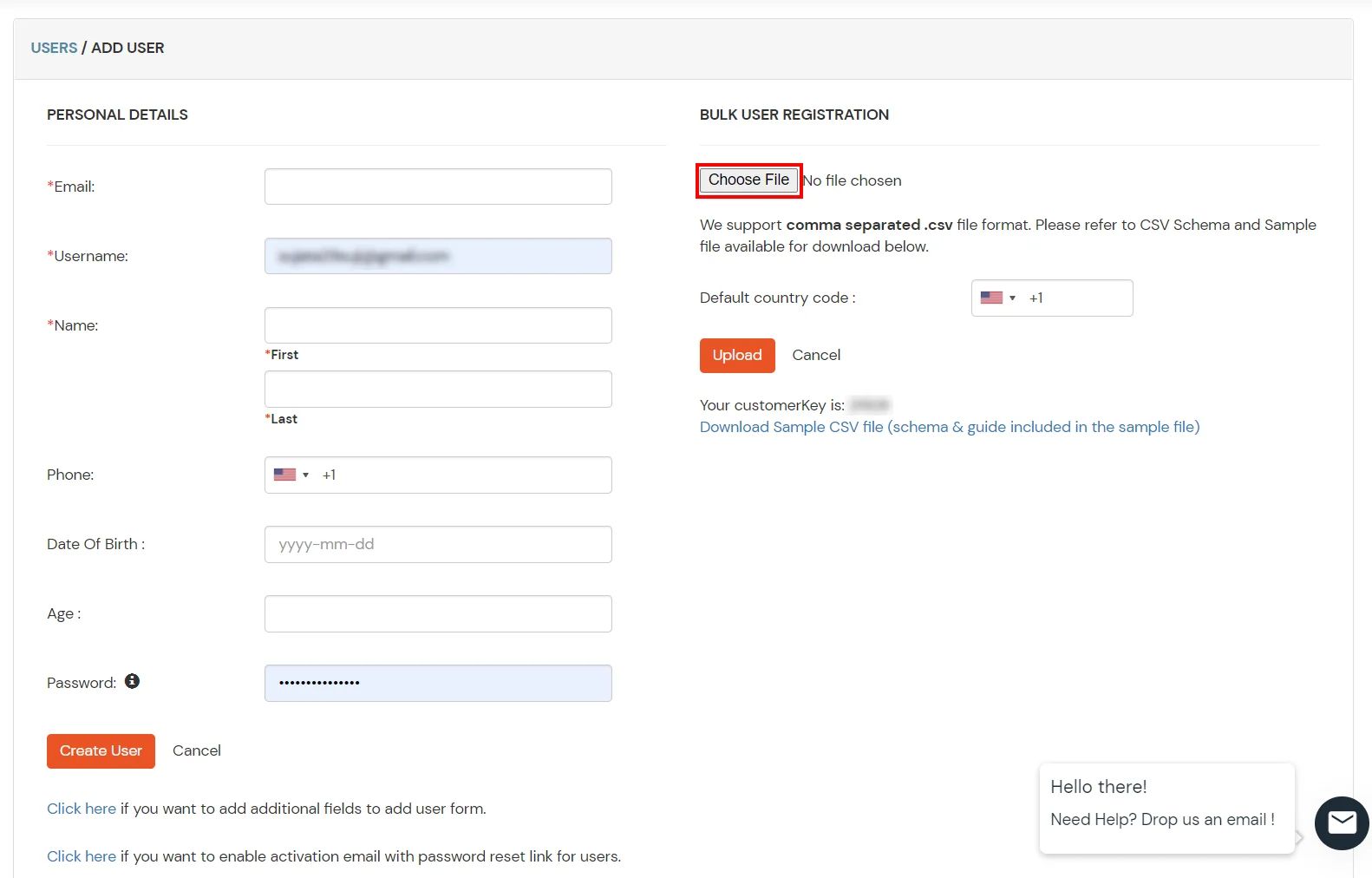
1. Create User in miniOrange

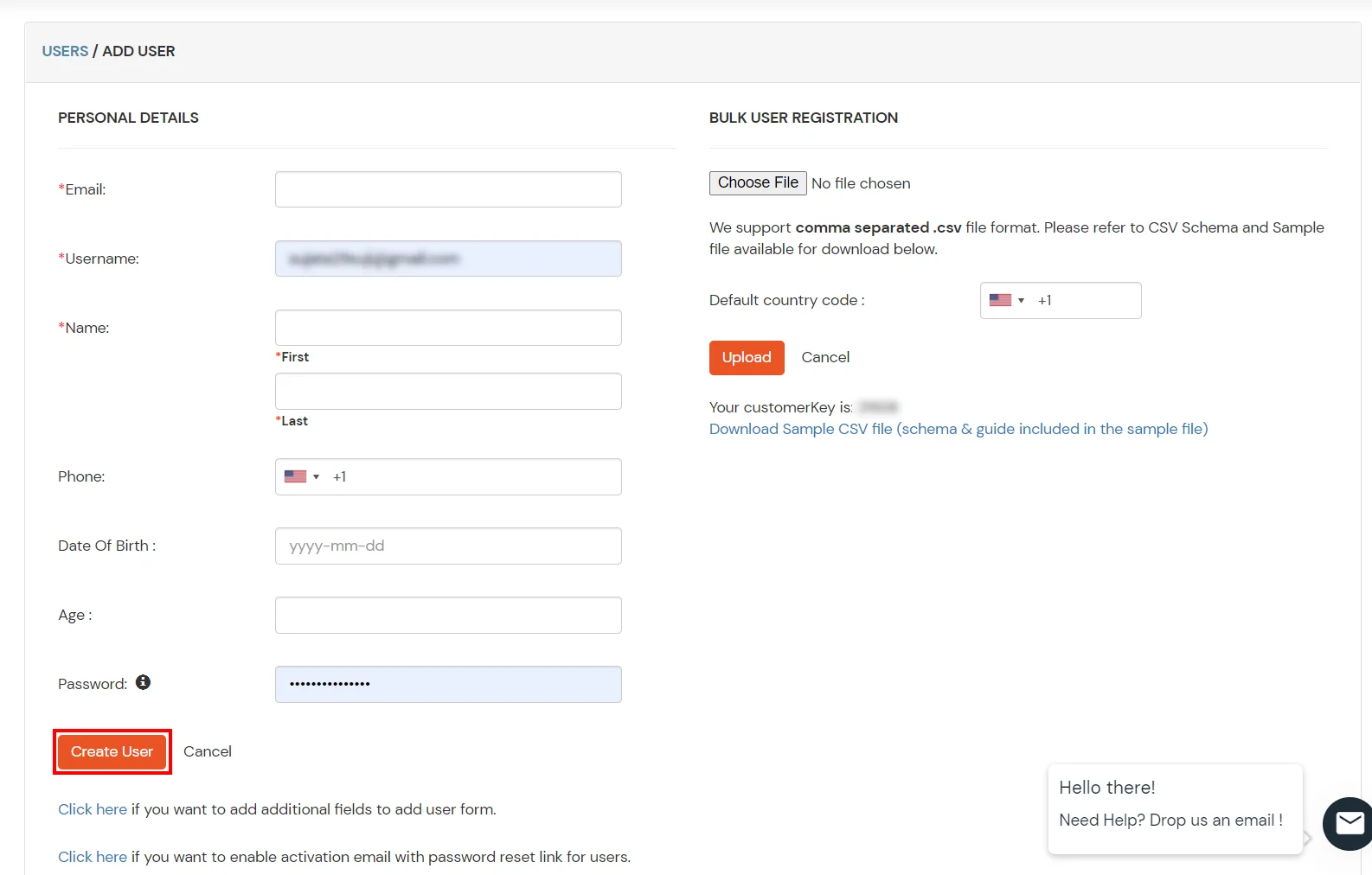
2. Bulk Upload Users in miniOrange via Uploading CSV File.

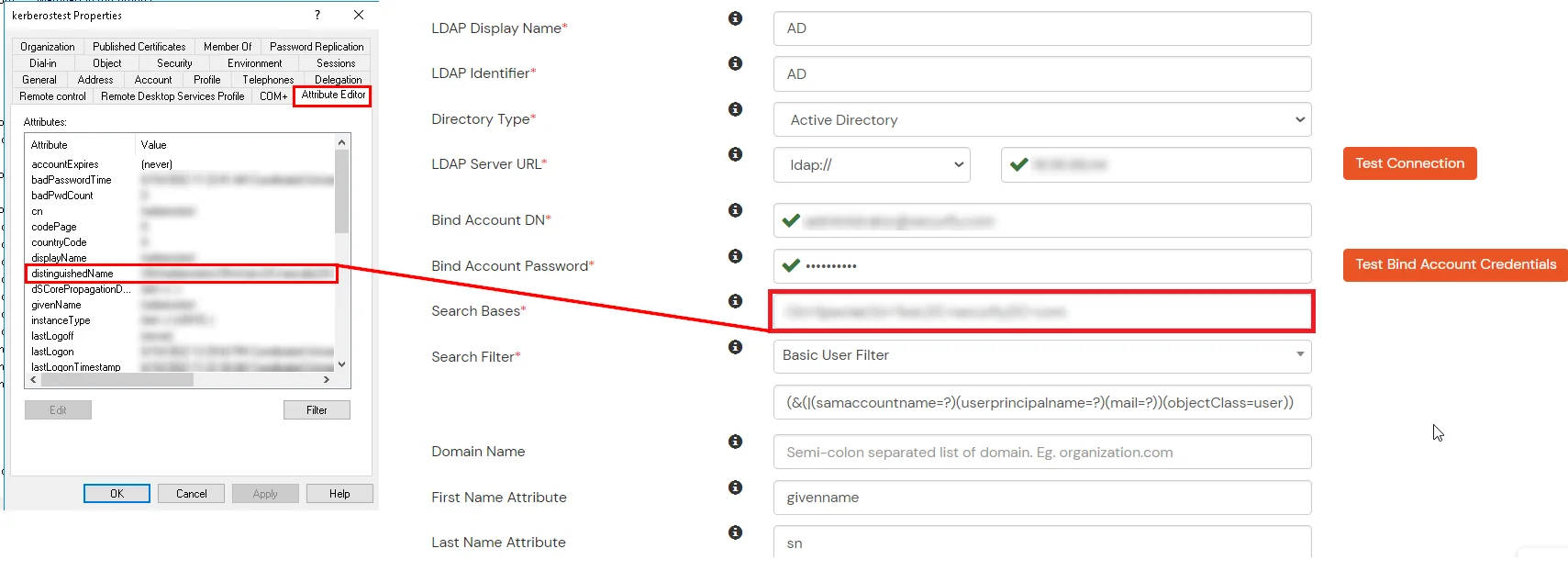
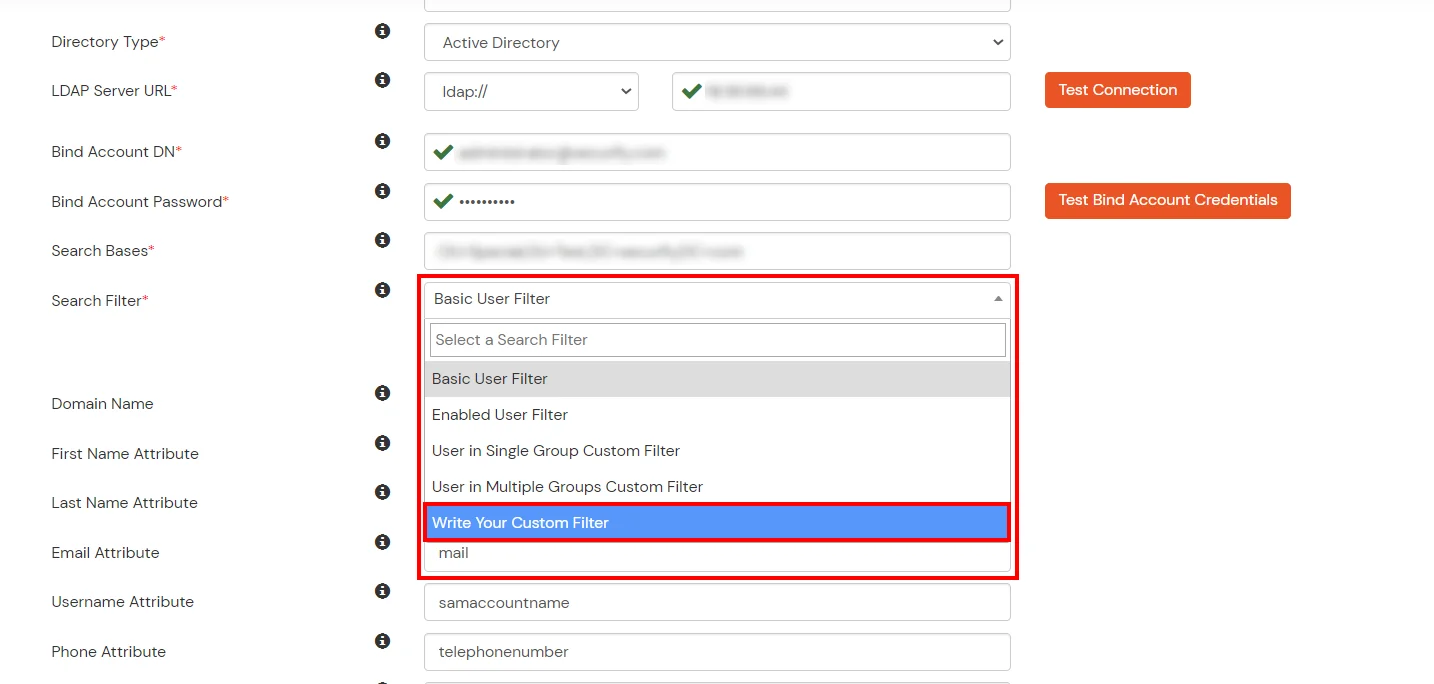
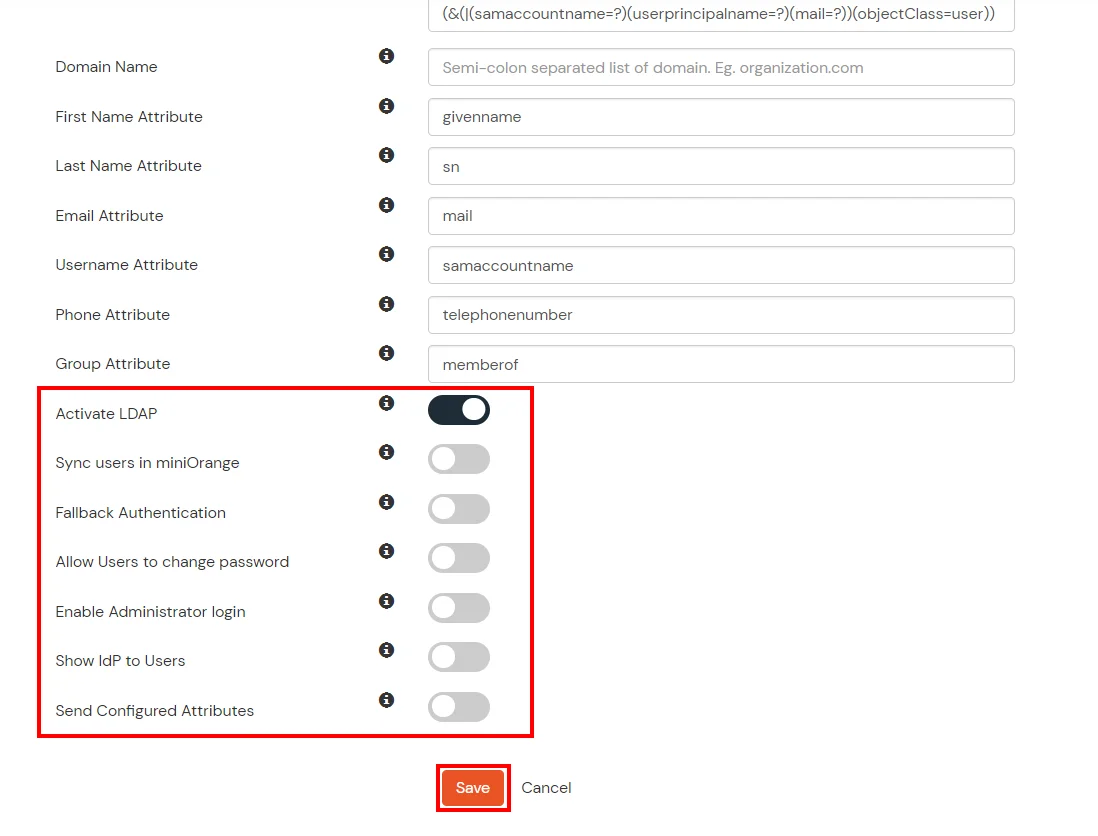
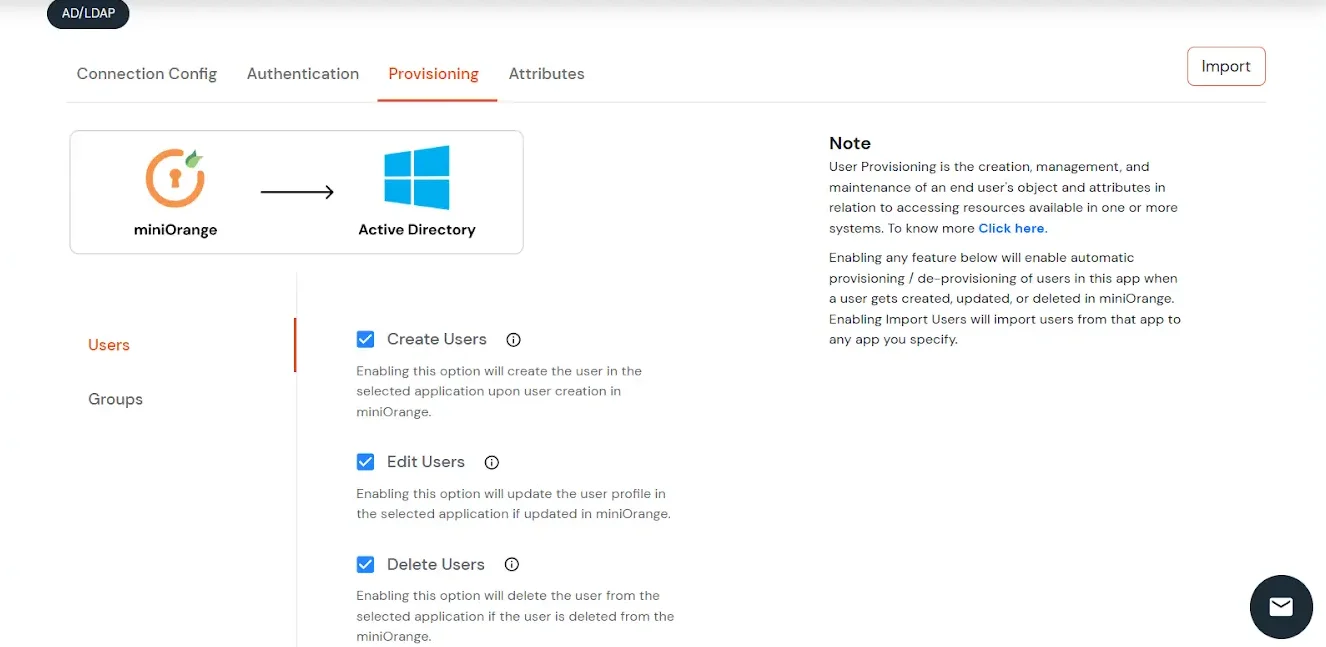
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute | Description |
|---|---|
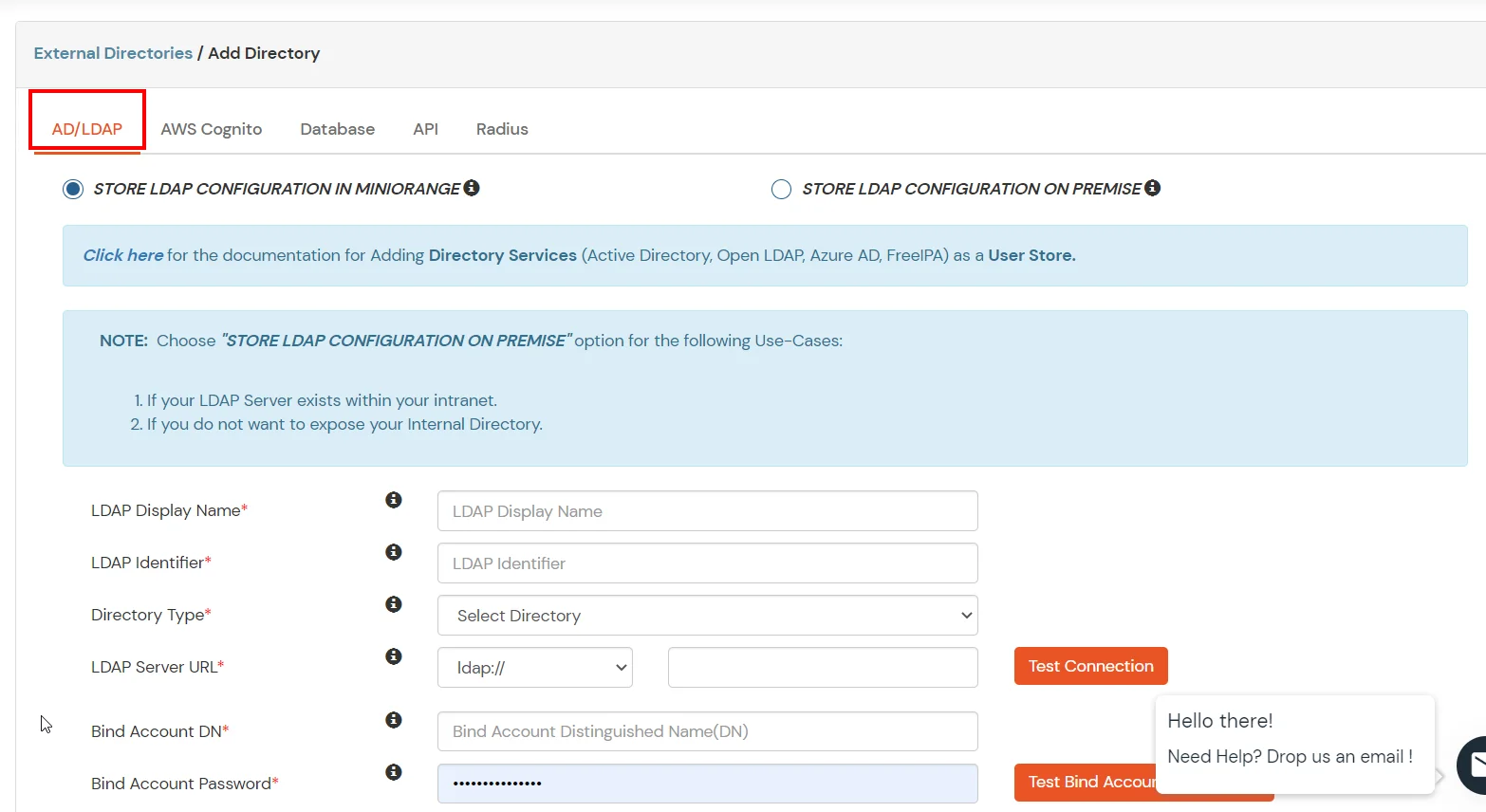
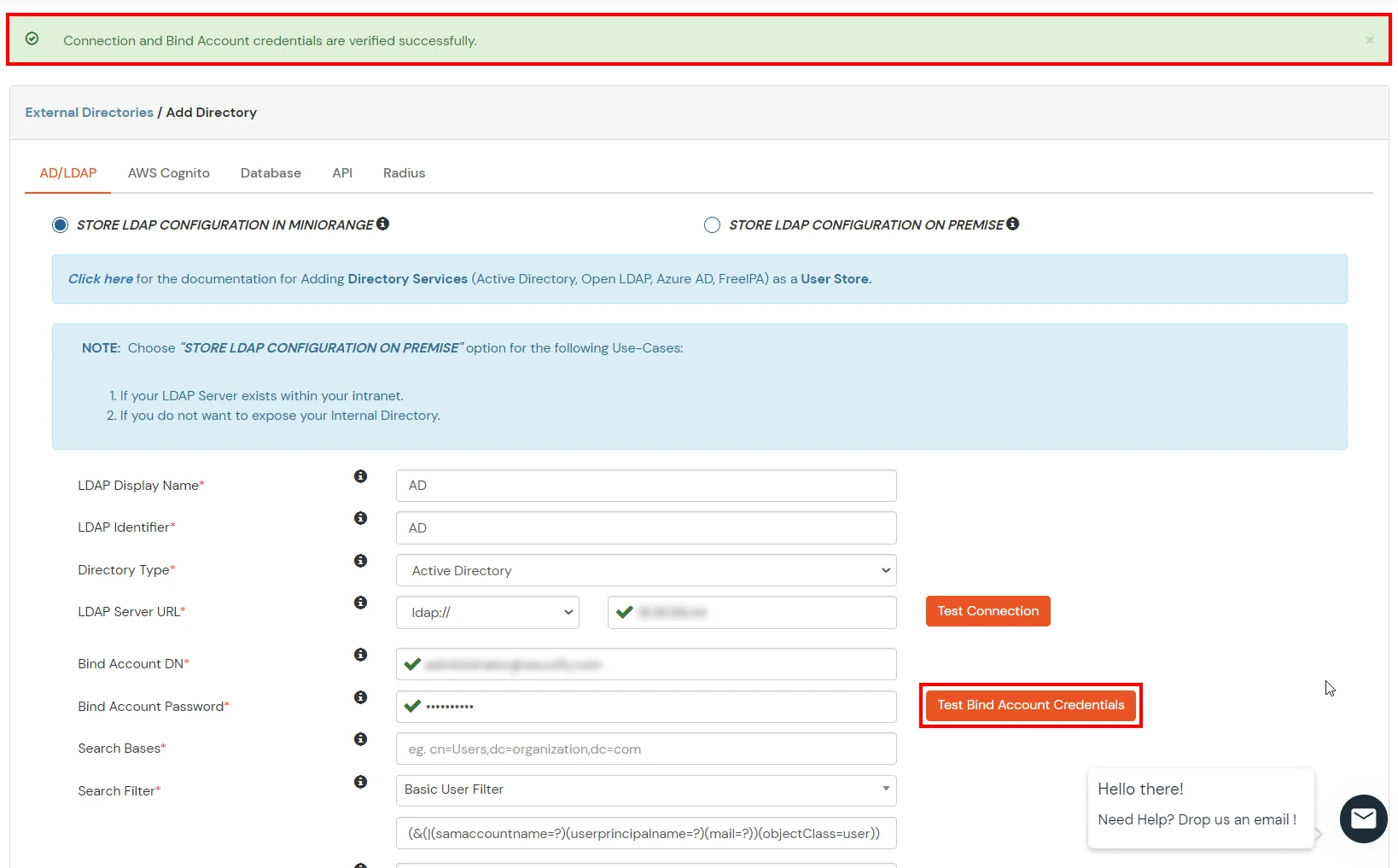
| Activate LDAP | All user authentications will be done with LDAP credentials if you Activate it |
| Fallback Authentication | If LDAP credentials fail then user will be authenticated through miniOrange |
| Enable administrator login | On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users | If you enable this option, this IdP will be visible to users |
| Sync users in miniOrange | Users will be created in miniOrange after authentication with LDAP |
Attribute Name sent to SP = organization
Attribute Name from IDP = company
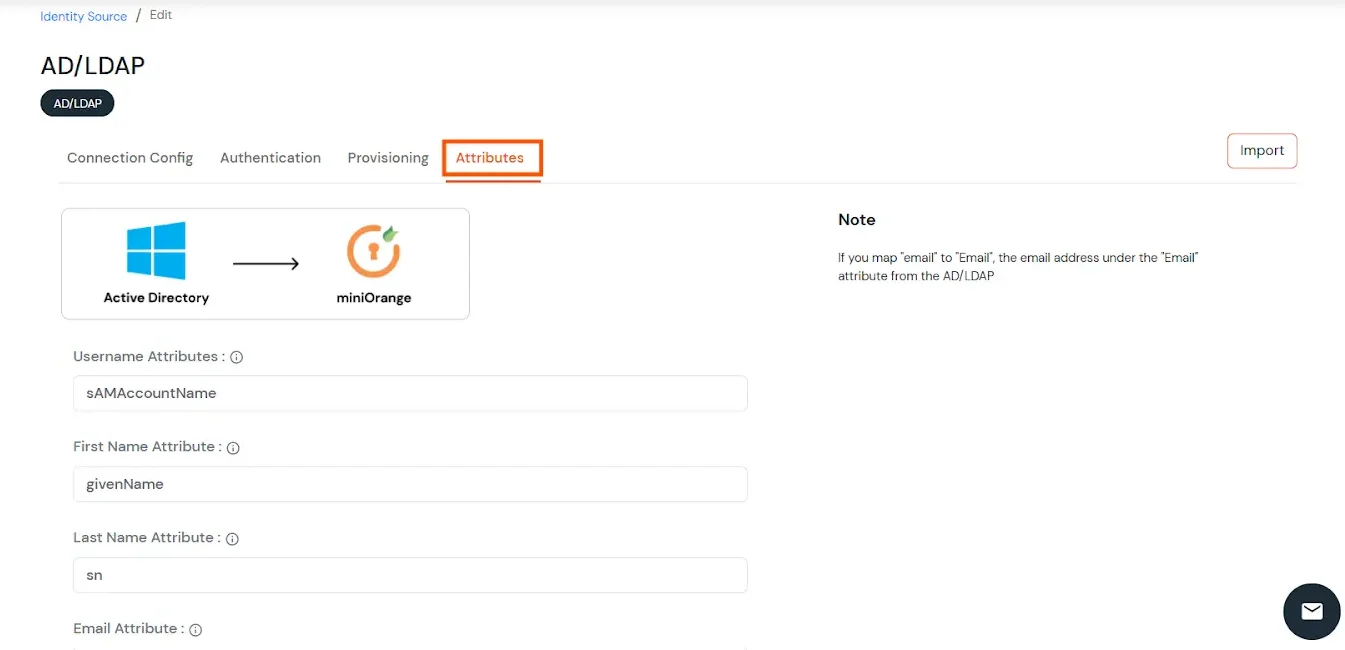
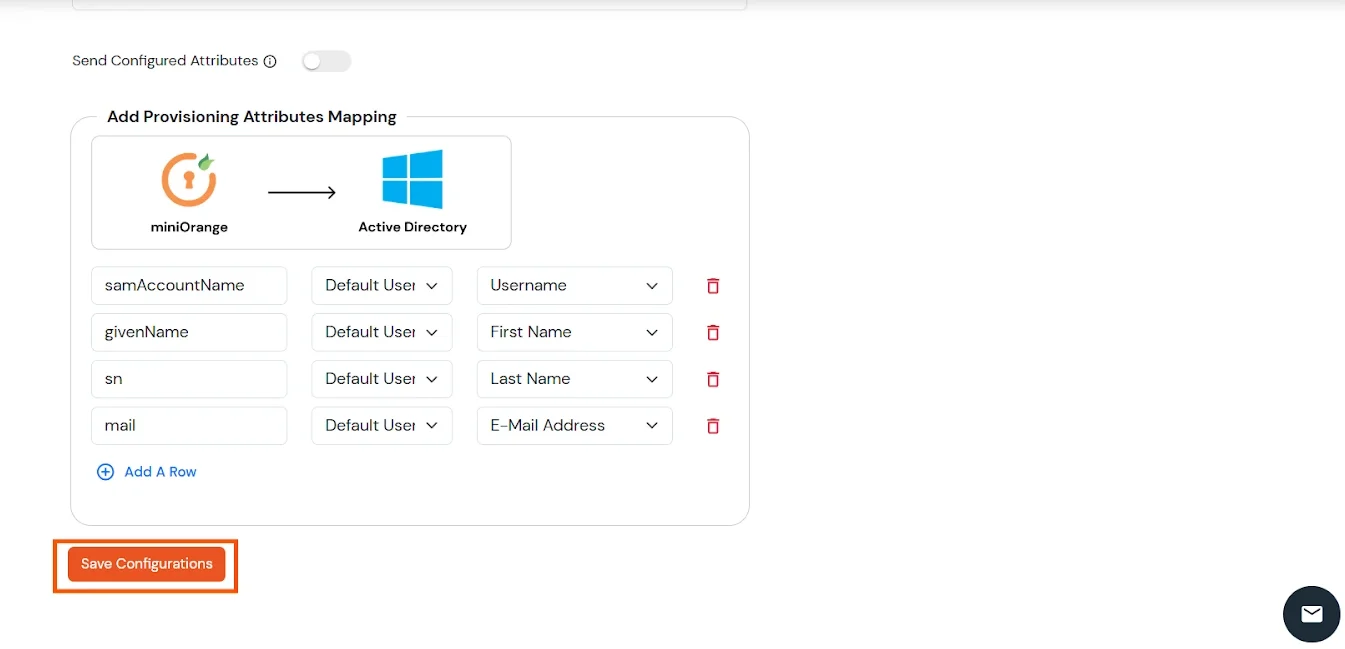
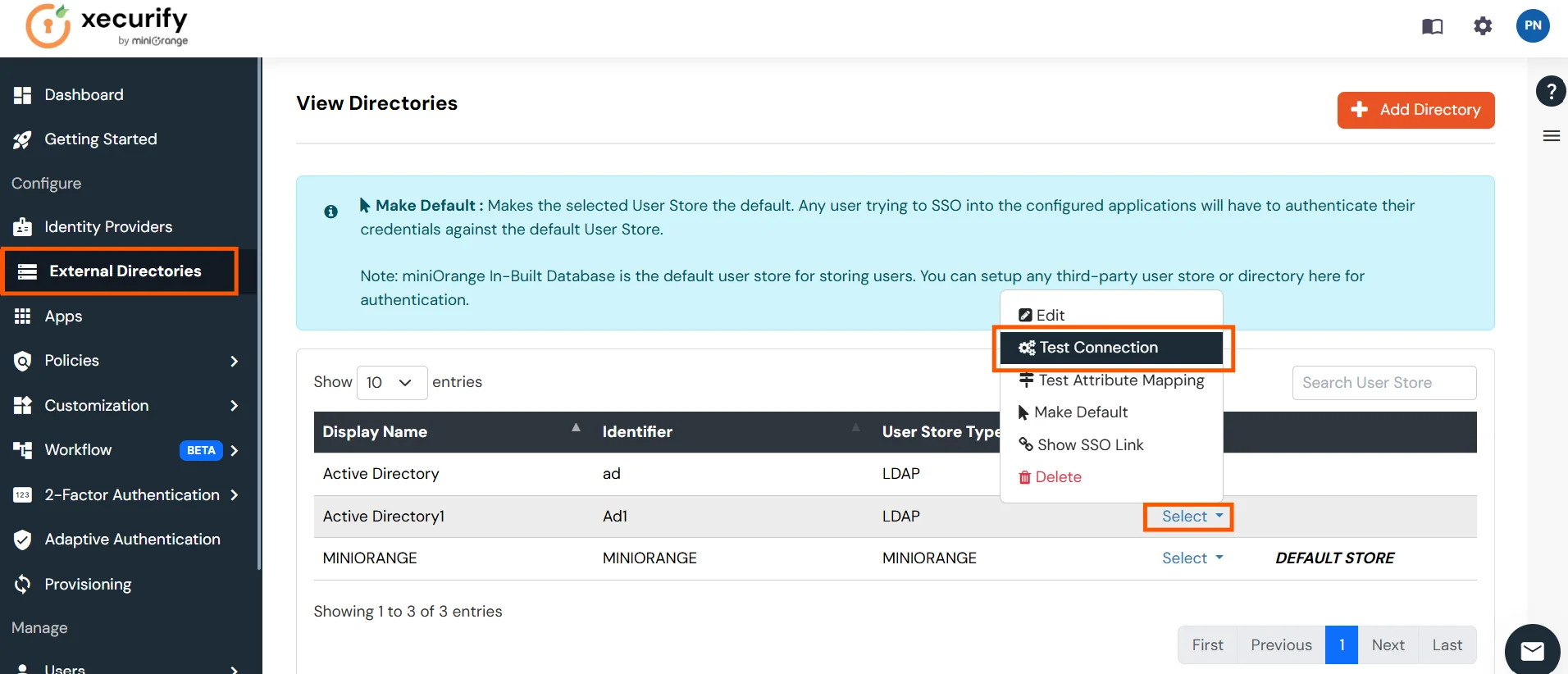
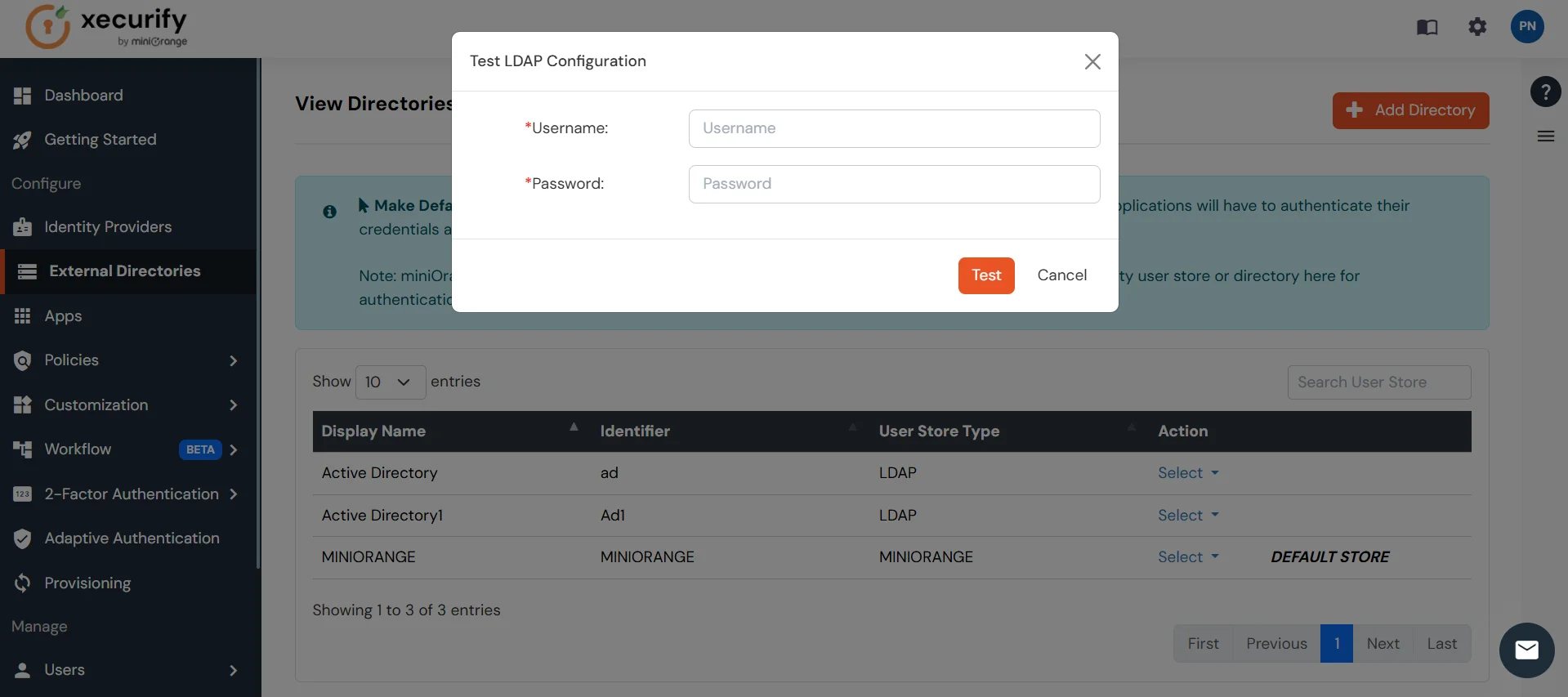
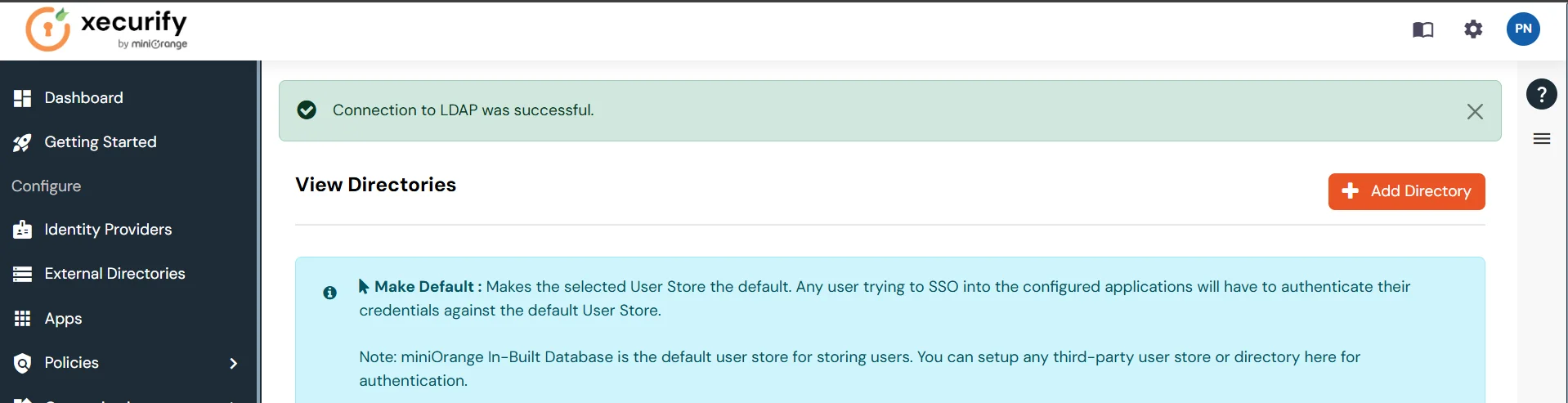
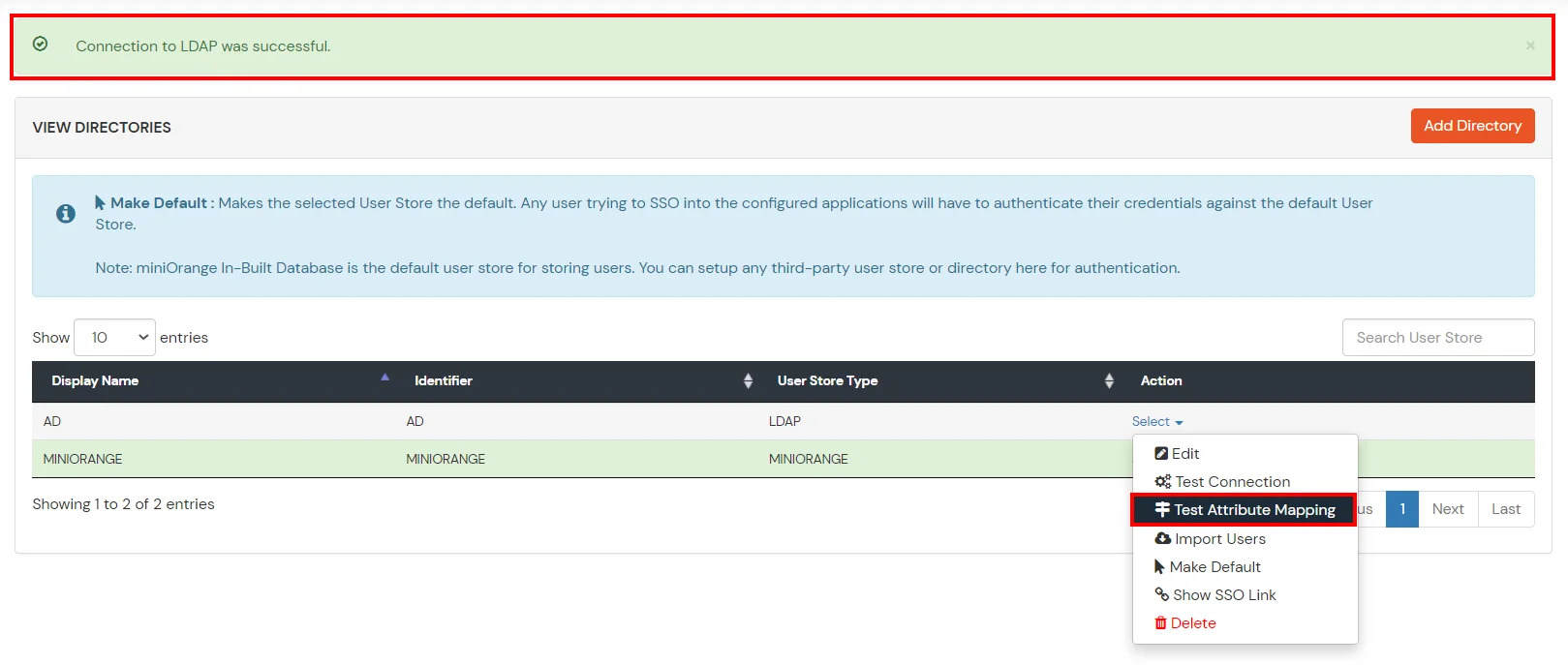
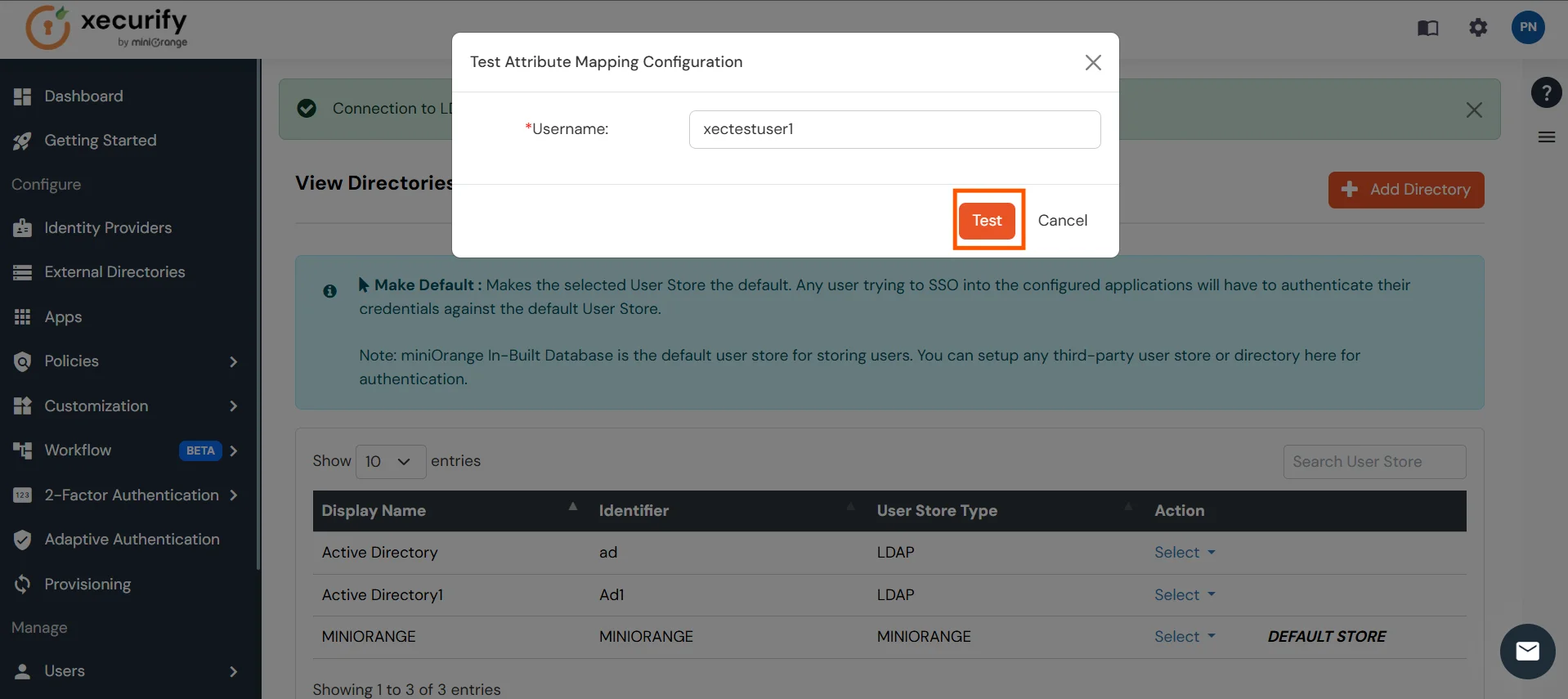
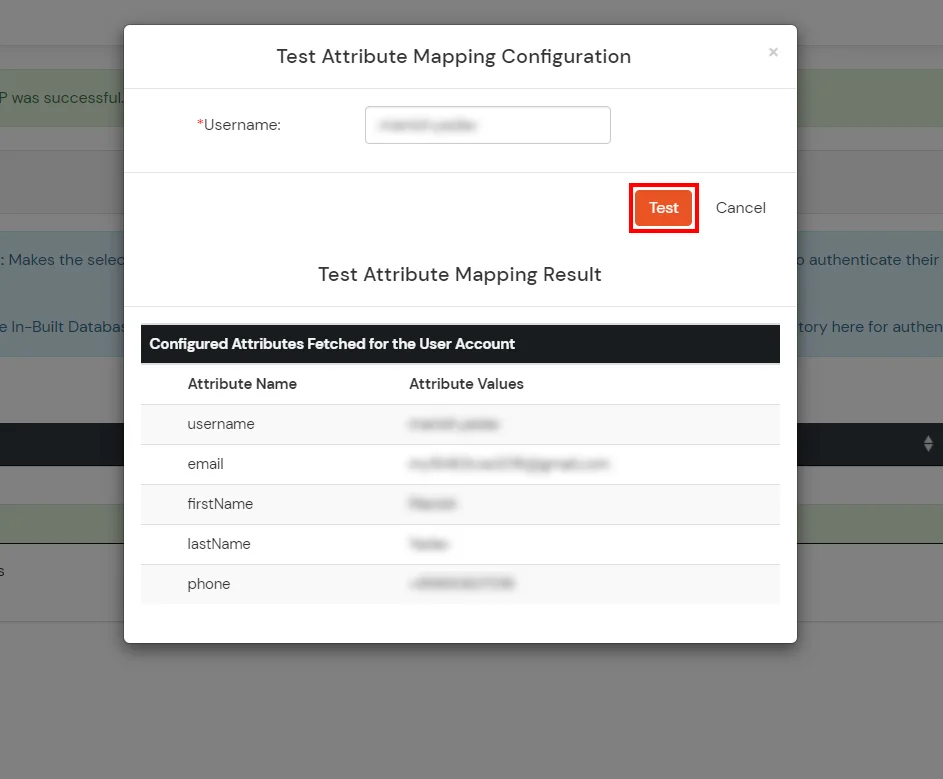
Set up AD as External Directory configuration is complete.
Note: Refer our guide to setup LDAP on windows server.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.
