Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
×SAML - Security Assertion Markup Language, it is an XML standard that allows secure web domains to exchange user authentication and authorization data. Using SAML 2.0, an online service provider (SP) can contact a separate online identity provider to authenticate users who are trying to access secure content.
SAML 2.0 authentication protocol is popular for browser-based enterprise applications. SAML 2.0 uses XML data format to transfer messages between applications. This XML document is digitally signed by the Identity provider and shared with the Service provider (SP) during the user authentication process.
miniOrange offers free help through a consultation call with our System Engineers to Install or Setup Temenos SSO solution in your environment with 30-day free trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you in no time.
SAML Single Sign-On (SSO) is an authentication process in which a user is provided access to multiple applications and/or websites by using only a single set of login credentials (such as username and password). This prevents the need for the user to login separately into the different applications.
The user credentials and other identity information is stored and managed by a centralized system called Identity Provider (IdP). The Identity Provider(IdP) is a trusted system which provides access to other websites and applications.
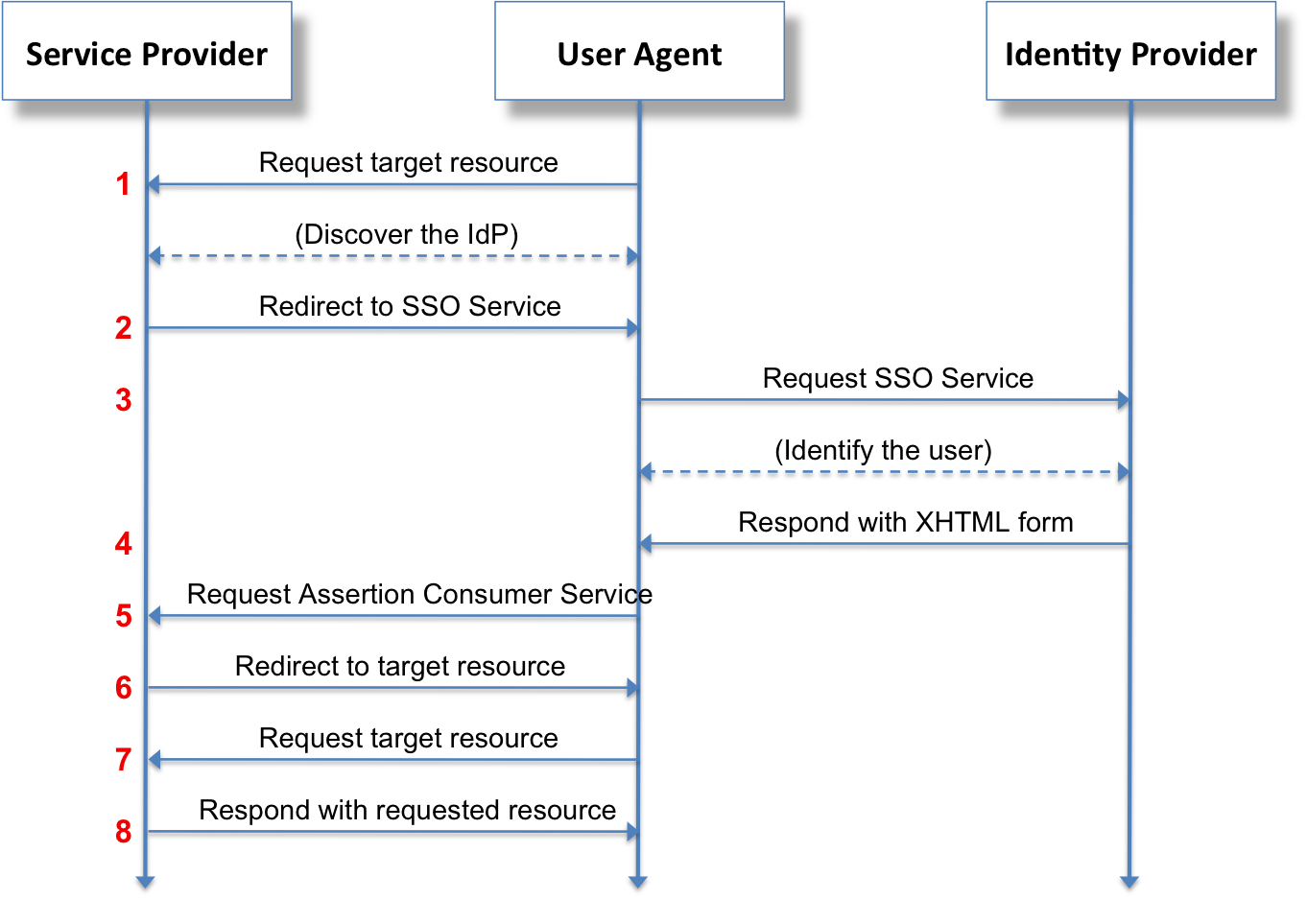
SAML SSO works by transferring the user’s identity from the identity provider (IdP) to the service provider (SP). This is done through an exchange of digitally signed XML documents. Consider the following Use Case: A user is logged into a system that acts as an identity provider (IdP). The user wants to log in to a remote application, i.e. the service provider (SP). The following is the flow taking place :
SAML 2.0 Assertion is a XML document provided by Identity Provider (IdP) to the service provider (SP) which contains the user authorization. SAML 2.0 assertions contain all the information necessary for a Service Provider (SP) to confirm user identity, including the source of the assertion, the time it was issued, and the conditions that make the assertion valid. There are three types of SAML Assertions.
Three different types of SAML Assertions:
An assertion consists of one or more statements. For single sign-on, a typical SAML assertion will contain a single authentication statement and possibly a single attribute statement. Note that a SAML response could contain multiple assertions, although it's more typical to have a single assertion within a response.
The SAML specification defines three roles:
In the use case addressed by SAML, the principal requests a service from the service provider (SP). The service provider requests and obtains an identity assertion from the identity provider (IdP). Based on this assertion, the service provider (SP) can make an access control decision - in other words it can decide whether to perform some service for the connected principal.
How to configure miniOrange Self-Service Console as a service provider by accepting a SAML assertion generated by the miniOrange IDP.
Also, you can configure miniOrange Self-Service Console as a service provider (SP) with Other Identity Providers (IDPs) like Okta, OneLogin, Azure AD, Auth0 etc.
OAuth is a slightly newer standard that was co-developed by Google and Twitter to enable streamlined internet logins. OAuth uses a similar methodology as SAML to share login information. SAML 2.0 provides more control to enterprises to keep their SSO logins more secure, whereas OAuth is better on mobile and uses JSON. Facebook and Google are two OAuth providers that you might use to log into other internet sites.
| Feature | SAML 2.0 | OAuth |
|---|---|---|
| Protocol | SAML is an authentication protocol. | OAuth is an authorization protocol. |
| Usage Scenario | SAML 2.0 will be used by those who are looking for federation and identity management. They will use this identity to login the users to different applications. | OAuth will be used by those who are not looking to maintain identities but are rather trying to leverage the implementation of secure protocol by applications such as Google, Microsoft, Paypal, who ensure that the identities are authentic. |
| Suitable Application | SAML 2.0 is popular for browser-based applications. | OAuth is suitable for both browser and mobile applications. |
| Commonly Used By | SAM 2.0 is widely used for enterprise applications. | OAuth is widely used for customer applications and API access. |
| Data Format | SAML 2.0 uses XML to transfer messages between applications. | OAuth uses JSON to transfer messages between applications. |
