Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
×Microsoft Outlook Web App (OWA) MFA/2FA is a security feature requires two factors to log in to your OWA account and Exchange admin center (EAC). The first factor is something you know, such as your username and password. The second factor is something you have, such as a security key or an authenticator app.
miniOrange provides various MFA methods and integrates seamlessly with multiple third-party identity providers, simplifying the setup and usage of OWA MFA.
OWA Multi-Factor Authentication (MFA) offers several benefits, including increased security, reduced risk of data breaches, and increased productivity.
Here are some additional benefits of OWA MFA:
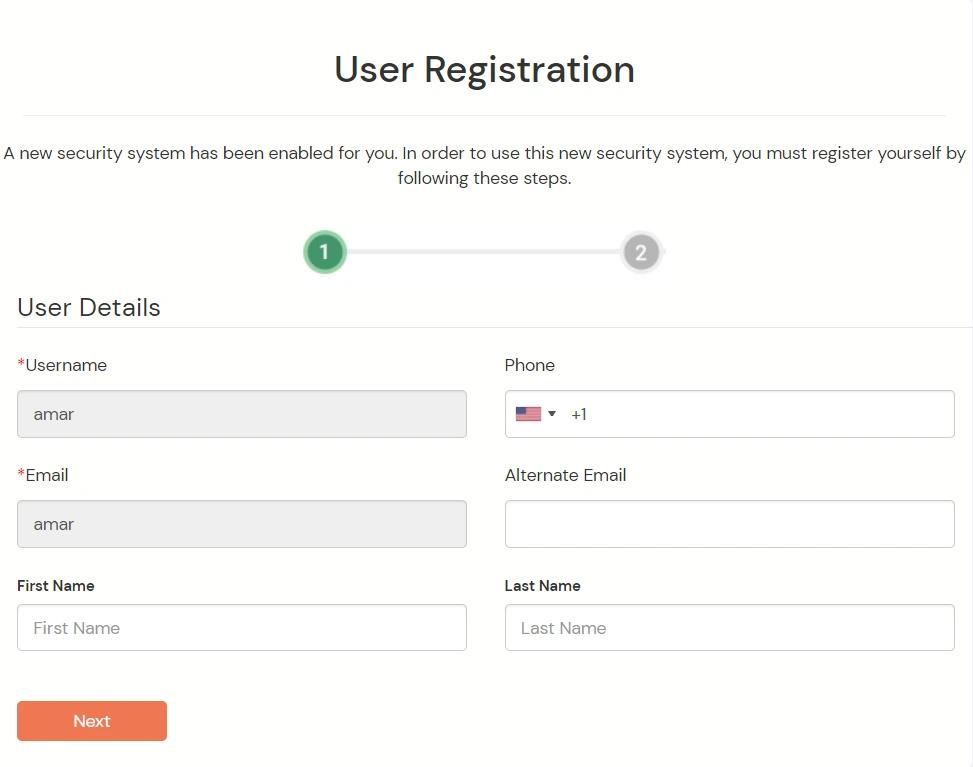
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.

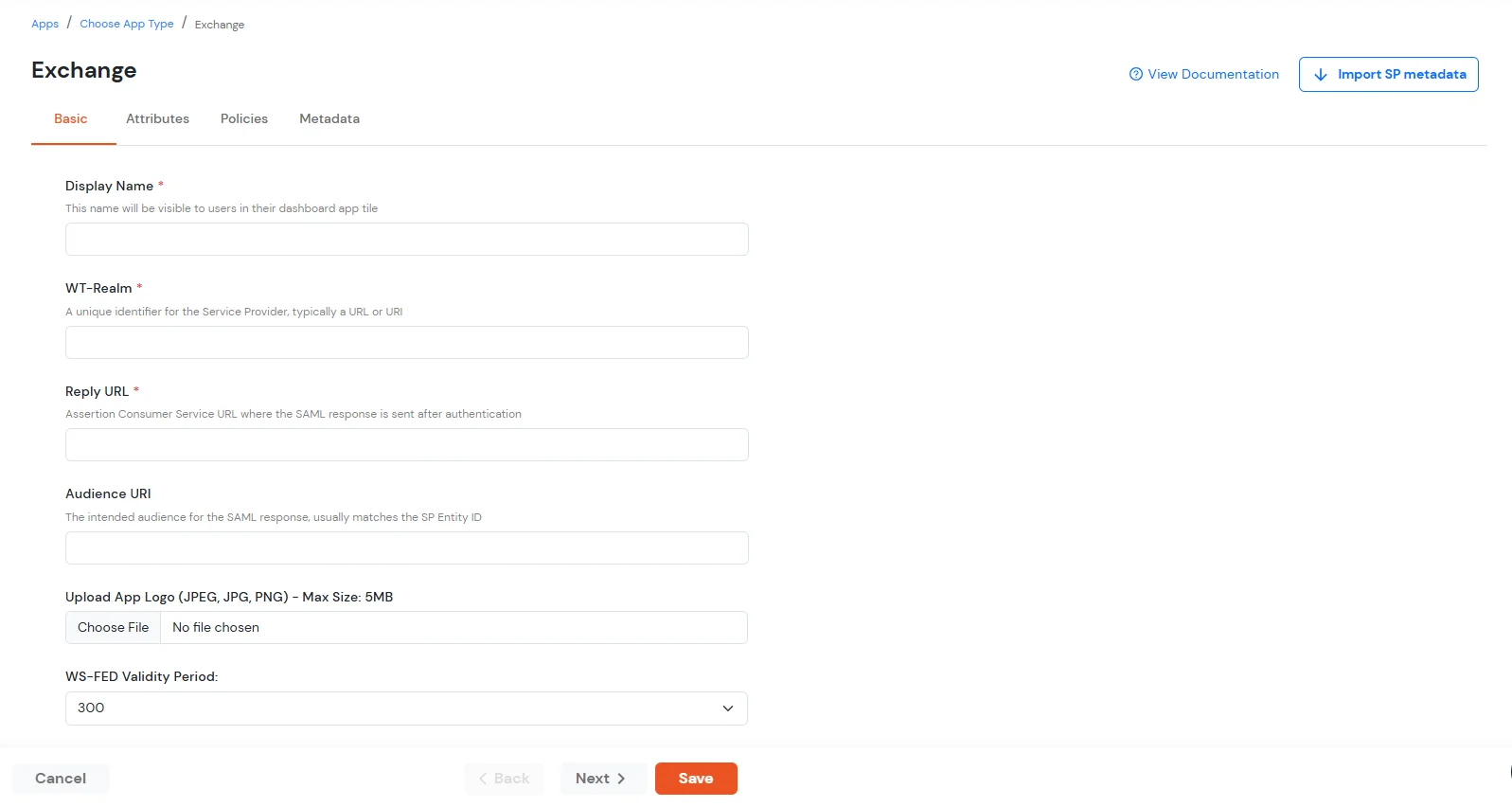
| Display Name | Exchange |
| WT-Realm | https://{owa-url} (e.g., https://mail.example.com/owa) |
| Reply URL | https://{owa-url} (e.g., https://mail.example.com/owa) |
| WS-FED Validity Period | 300s |
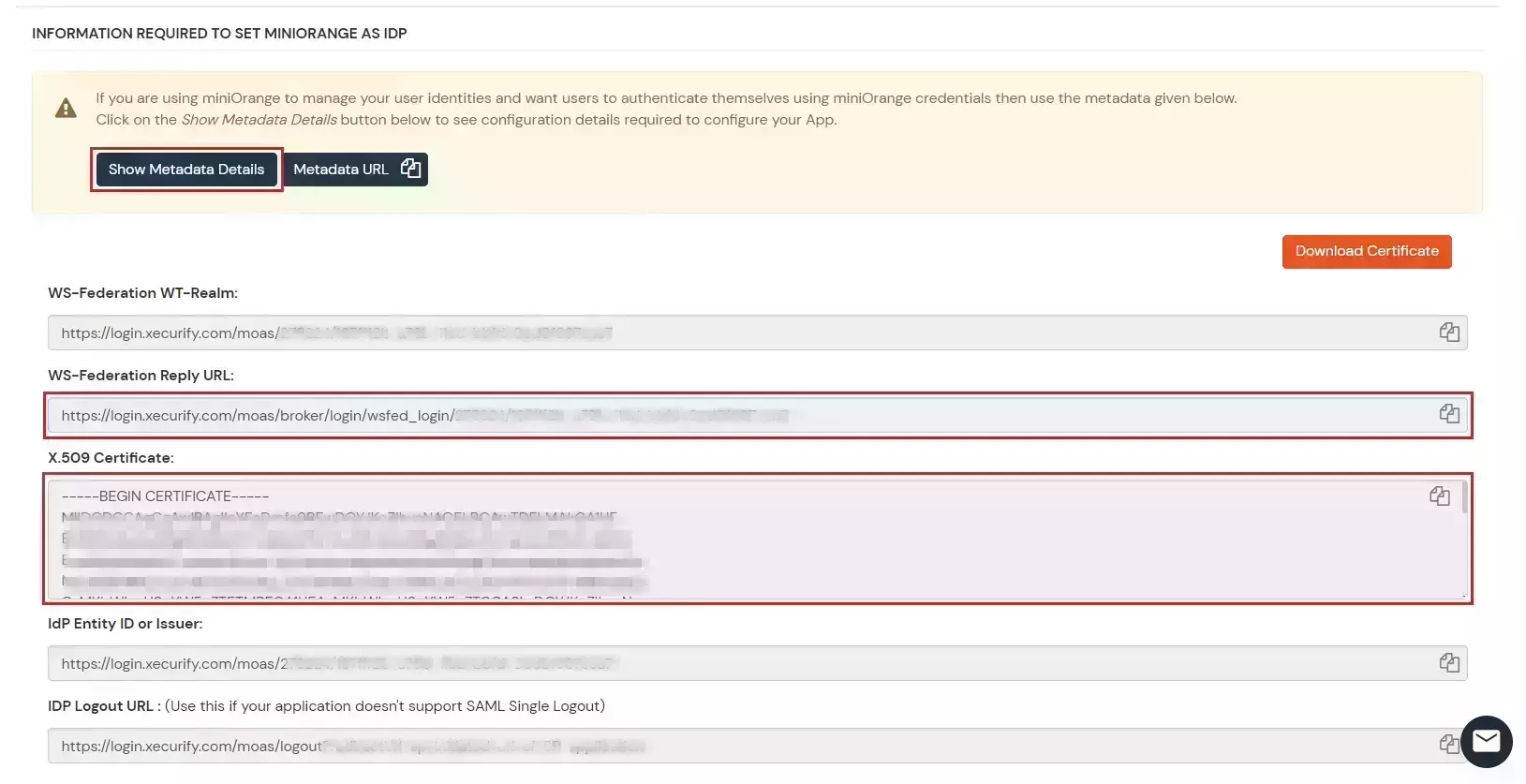
##Base URL## is the exchange/OWA host. The command has both URLs: One ending in / and the other one which does not contain a trailing slash.
$uris=@("https://##Base URL##/owa/","https://##Base URL##/ecp/","https://##Base URL##/owa","https://##Base URL##/ecp")
Note: Make sure the certificate thumb print is in uppercase.
Set-OrganizationConfig -AdfsIssuer "##miniOrange URL##" -AdfsAudienceUris $uris -AdfsSignCertificateThumbprint ##Cert Thumbprint##
Get-EcpVirtualDirectory | Set-EcpVirtualDirectory -AdfsAuthentication $true
-BasicAuthentication $false -DigestAuthentication $false -FormsAuthentication $false
-WindowsAuthentication $false
Get-OwaVirtualDirectory | Set-OwaVirtualDirectory -AdfsAuthentication $true
-BasicAuthentication $false -DigestAuthentication $false -FormsAuthentication $false
-WindowsAuthentication $false -OAuthAuthentication $false
# Restart w3svc and was
net stop was /y
net start w3svc
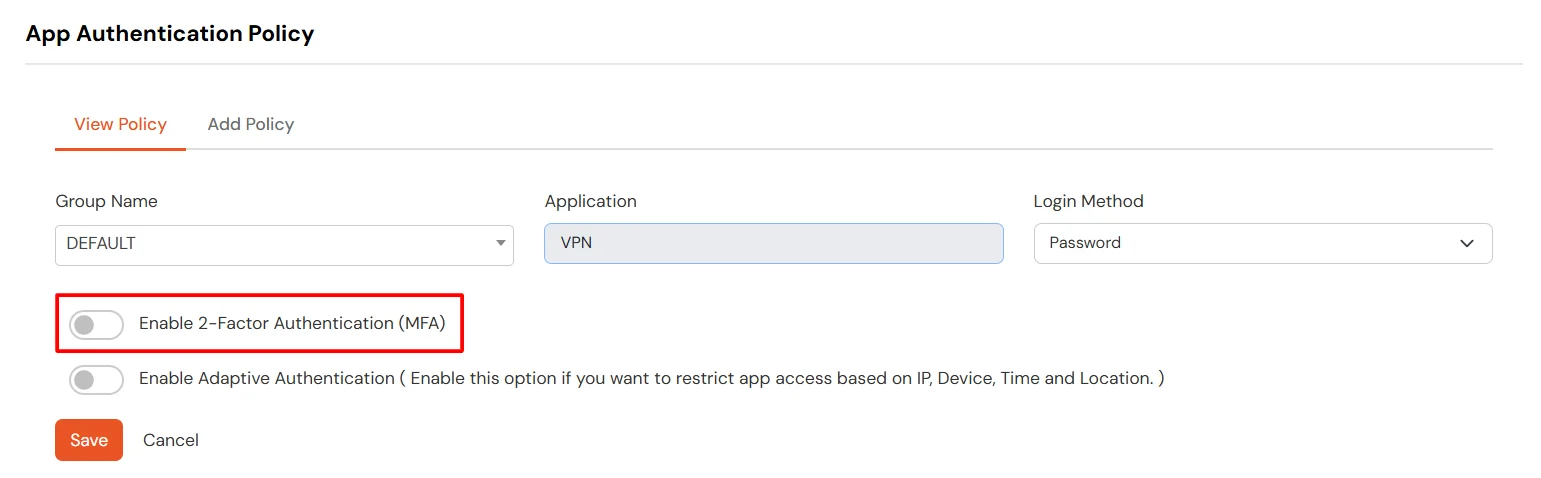
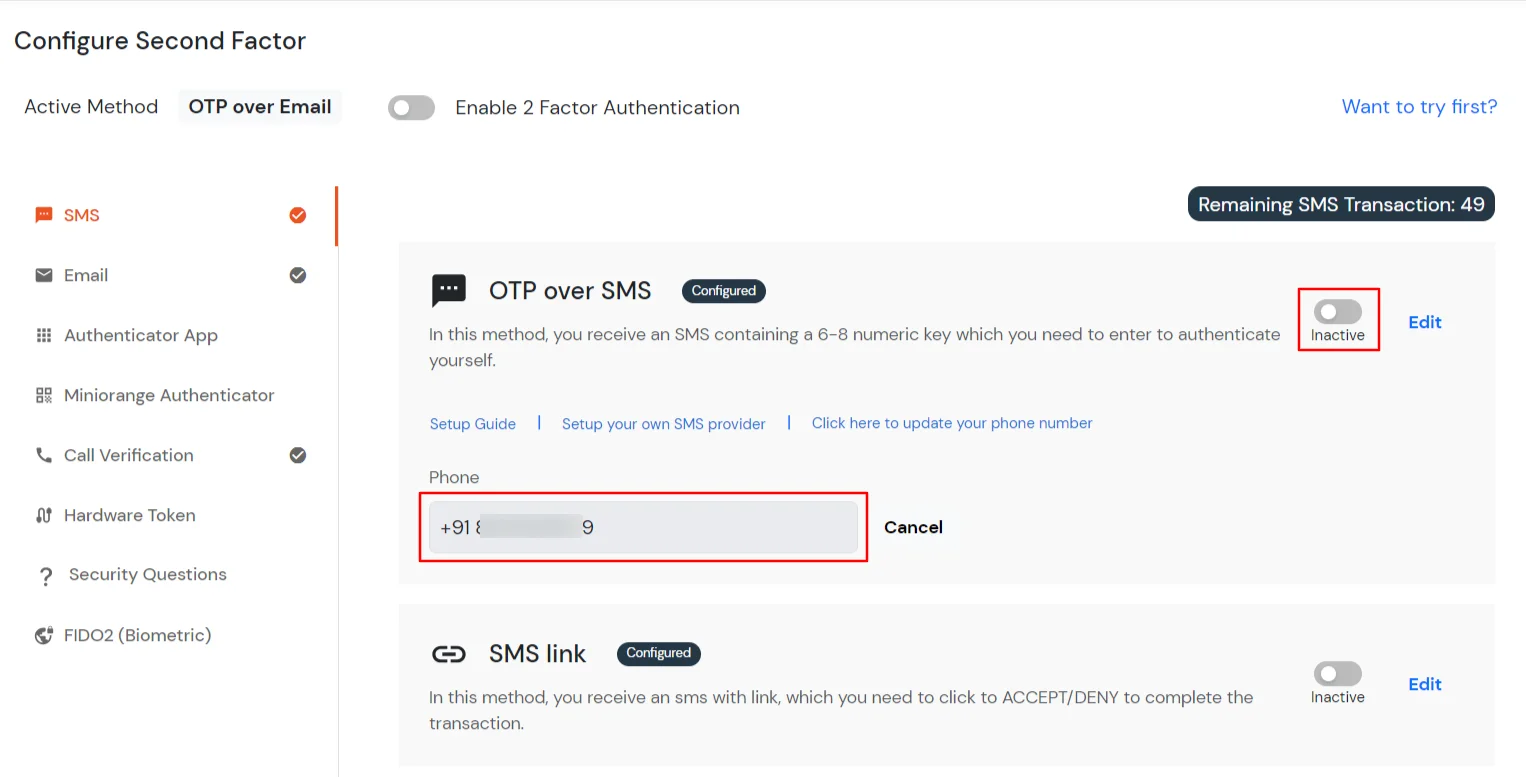
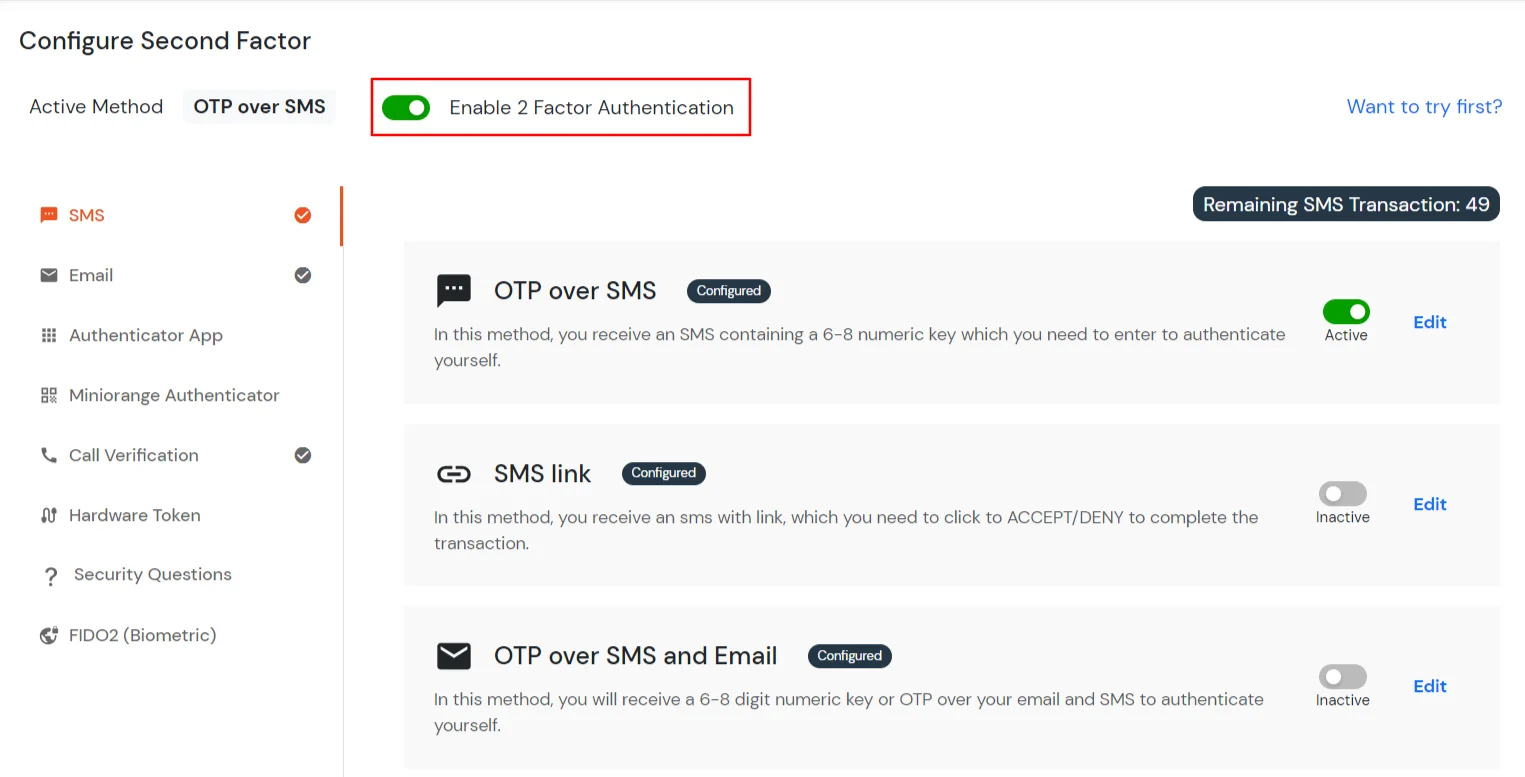
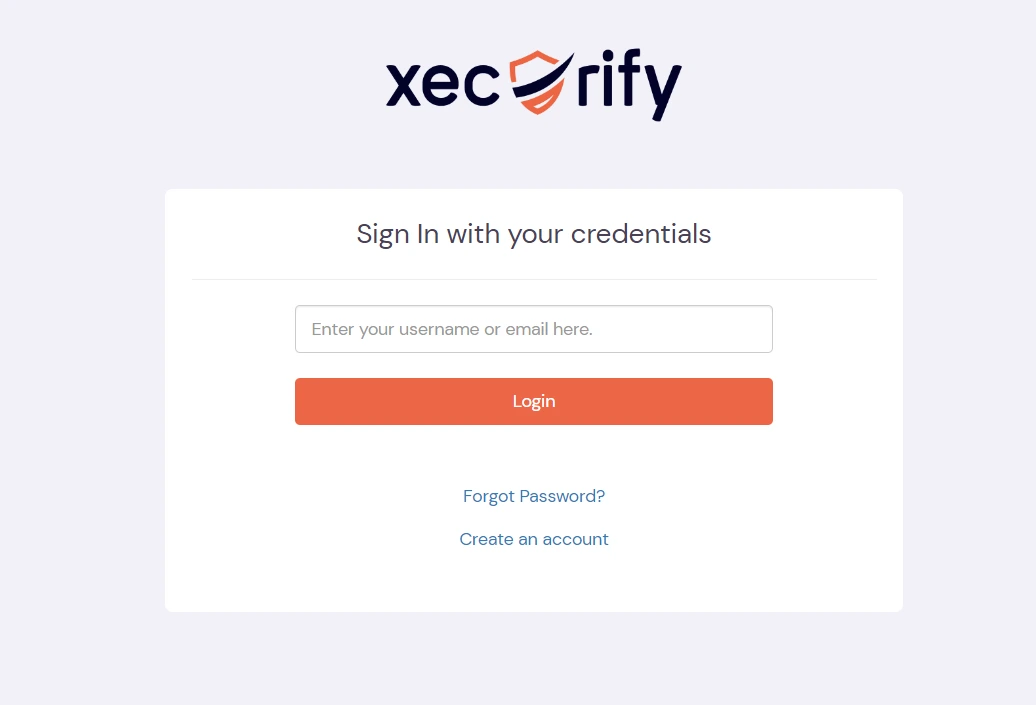
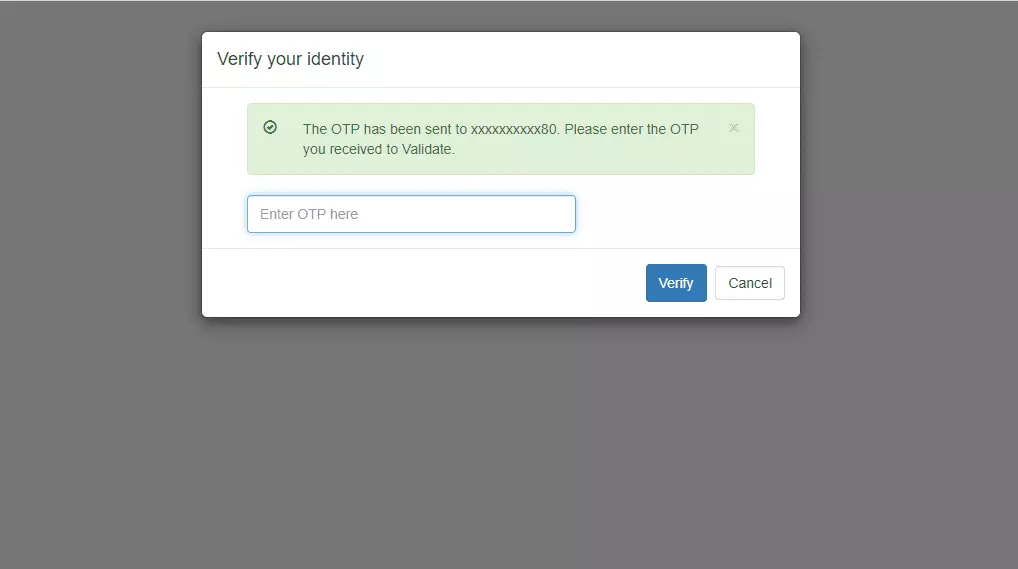
3.1: Enable 2FA for Users of Exchange app
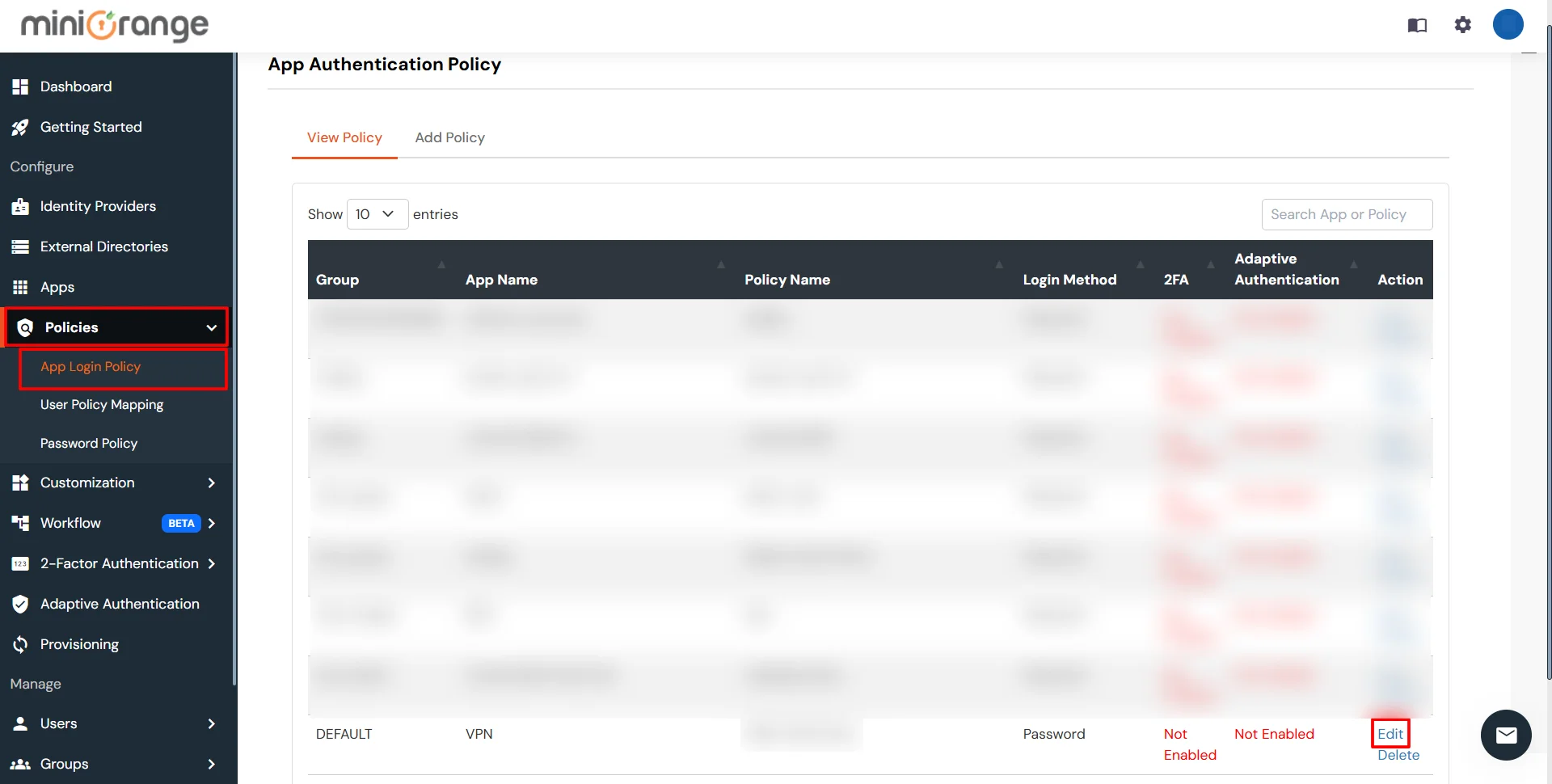
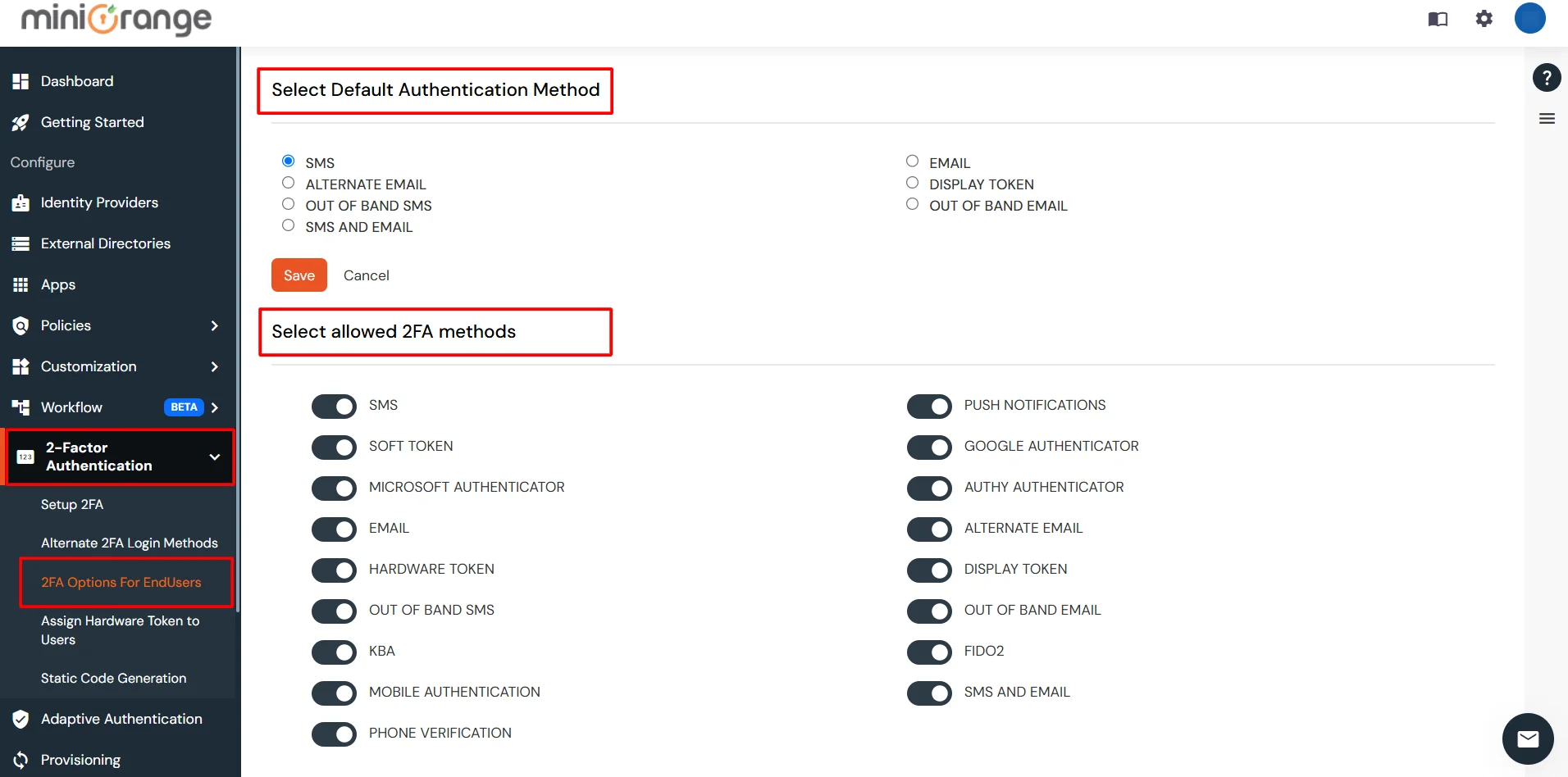
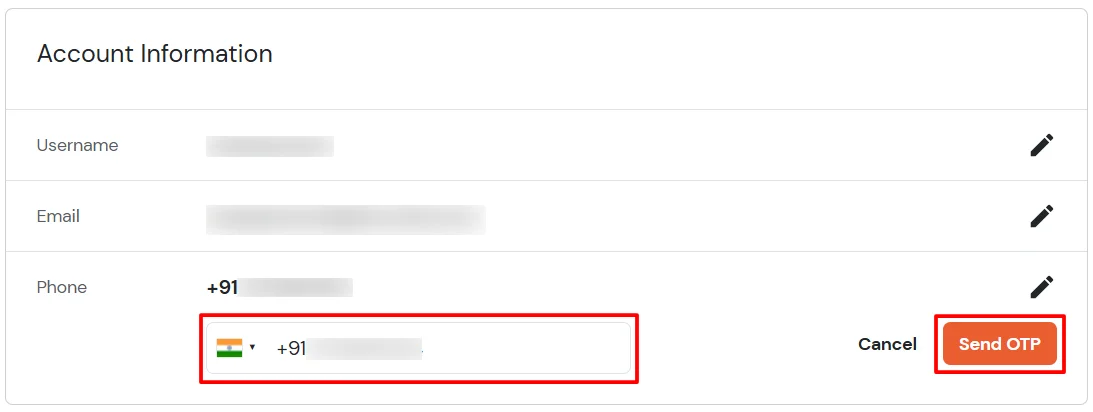
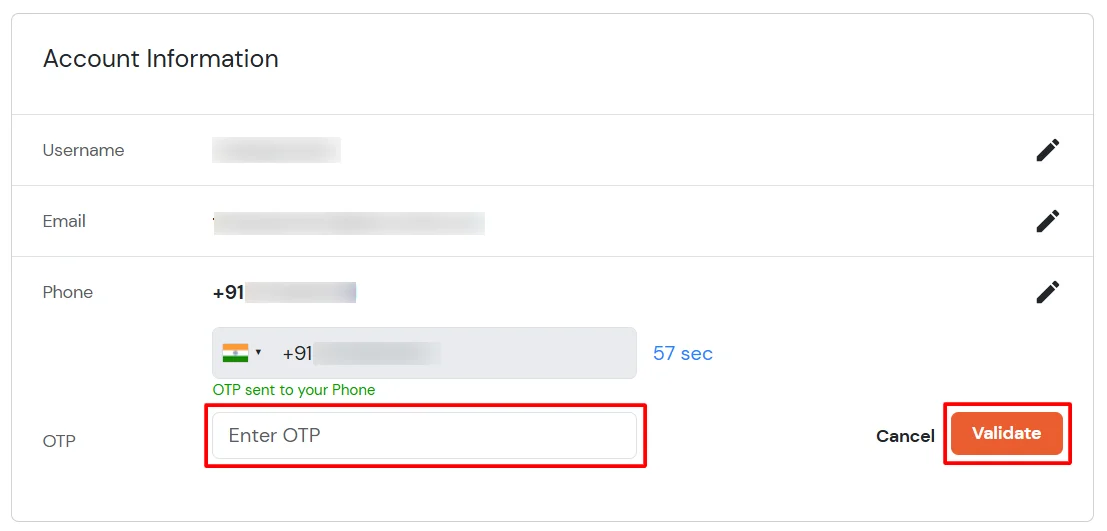
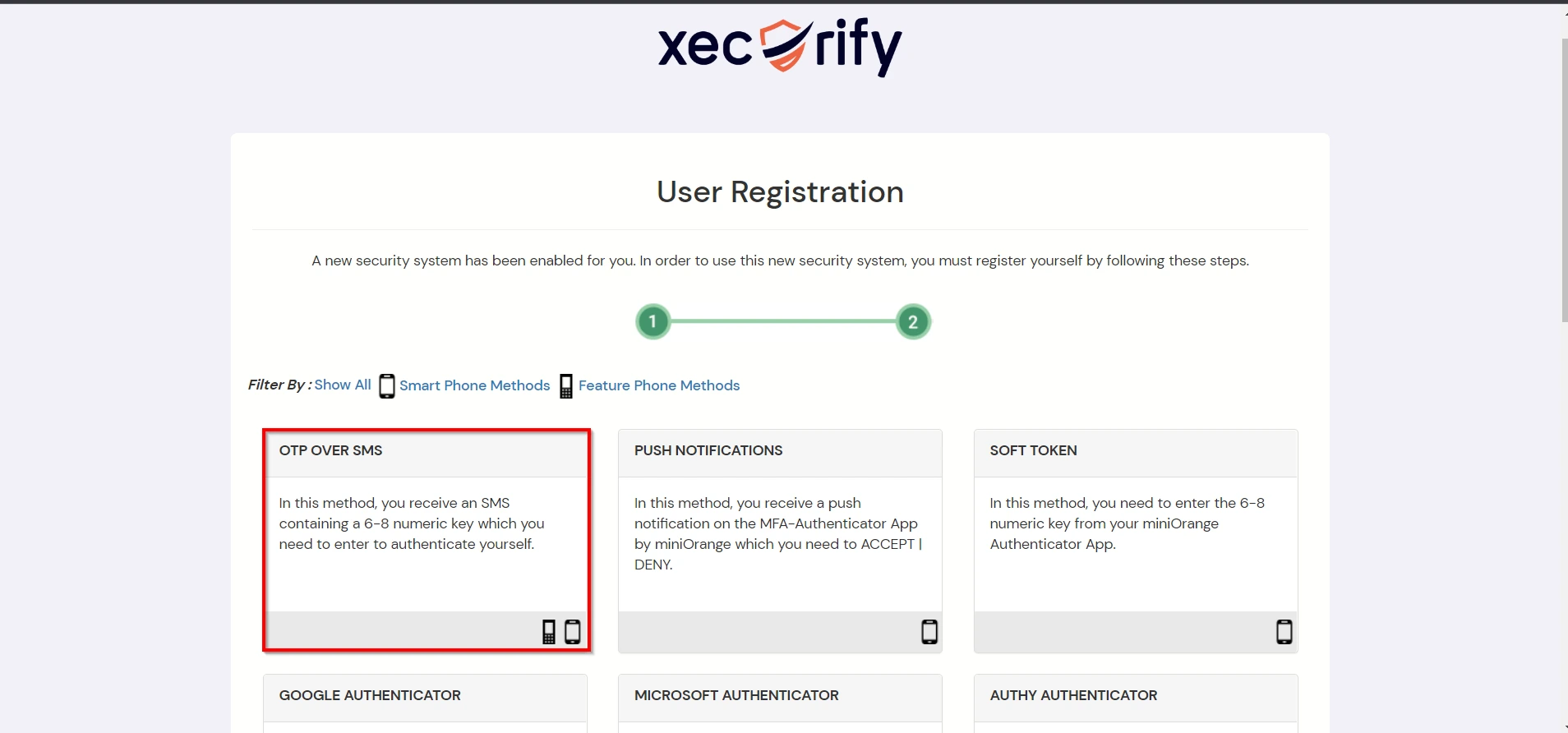
3.2: Configure 2FA for your Endusers
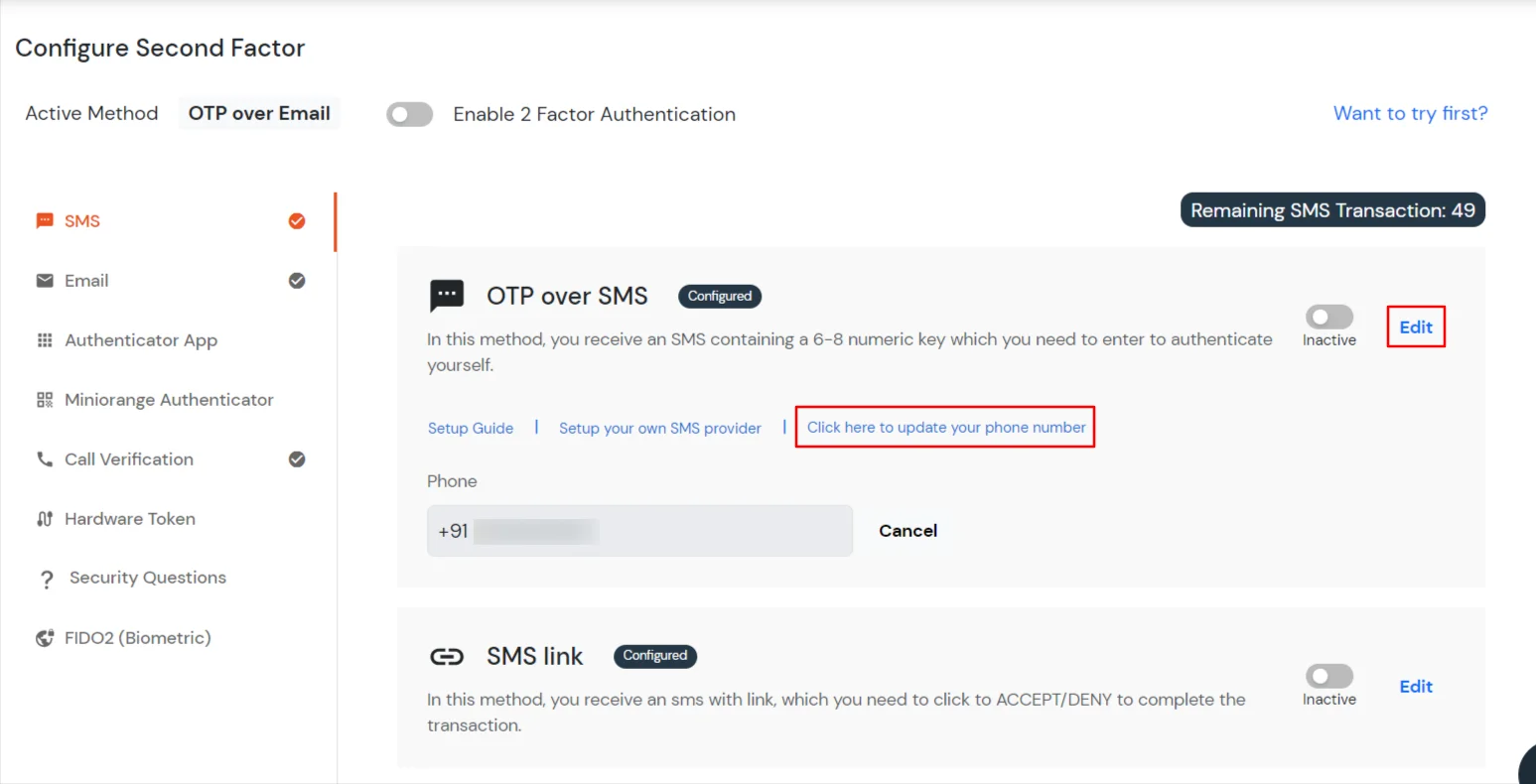
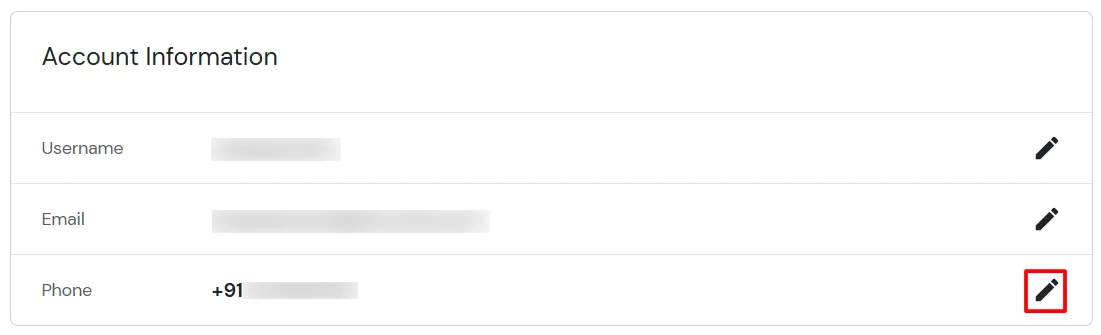
3.3: Enduser 2FA Setup
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.
A. Restricting access to Exchange with IP Configuration
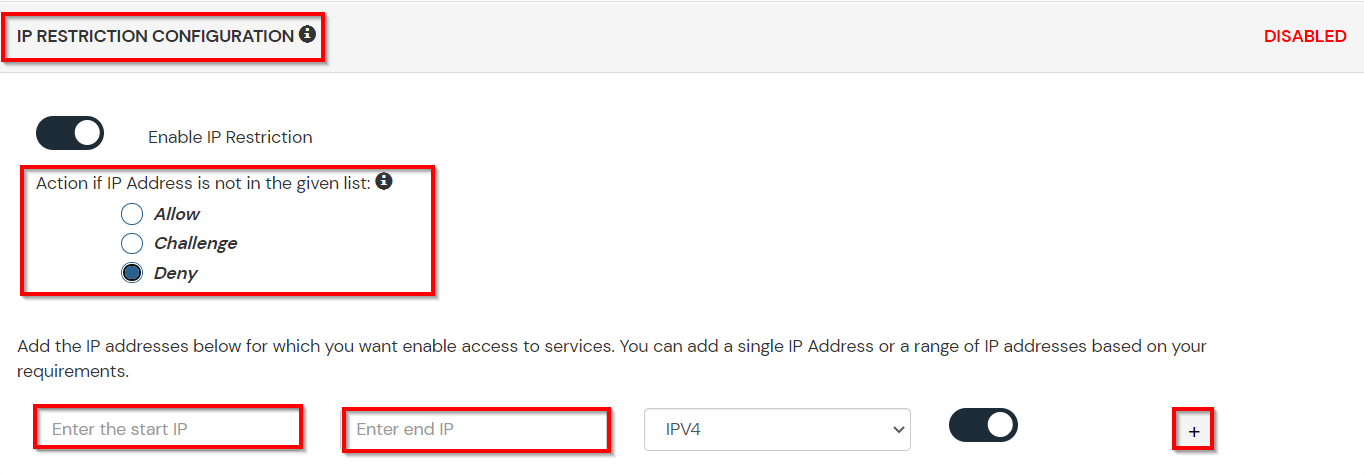
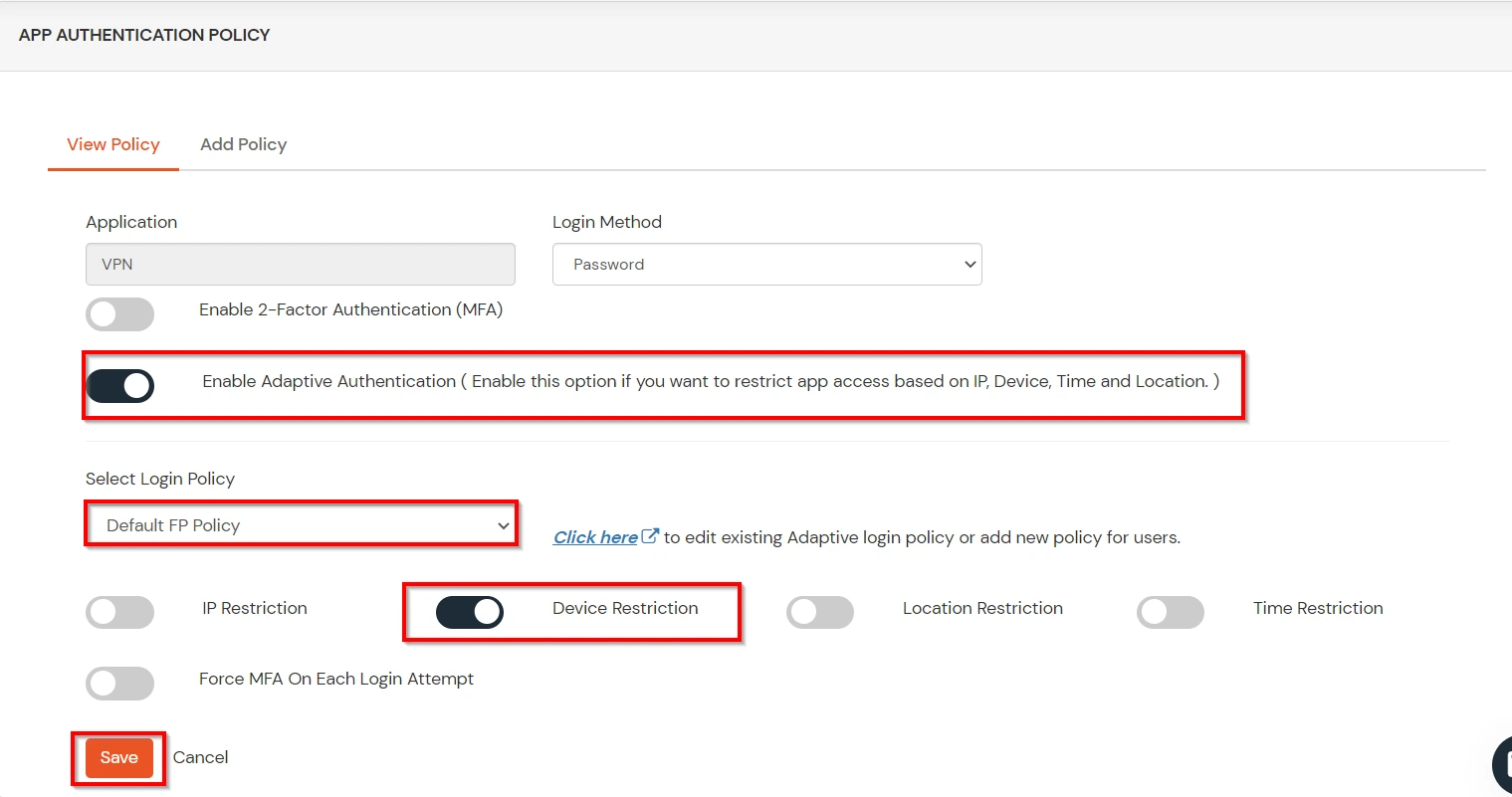
You can use adaptive authentication with Exchange Single Sign-On (SSO) to improve the security and functionality of Single Sign-On. You can allow a IP Address in certain range for SSO or you can deny it based your requirements and you can also challenge the user to verify his authenticity. Adaptive authentication manages the user authentication bases on different factors such as Device ID, Location, Time of Access, IP Address and many more.
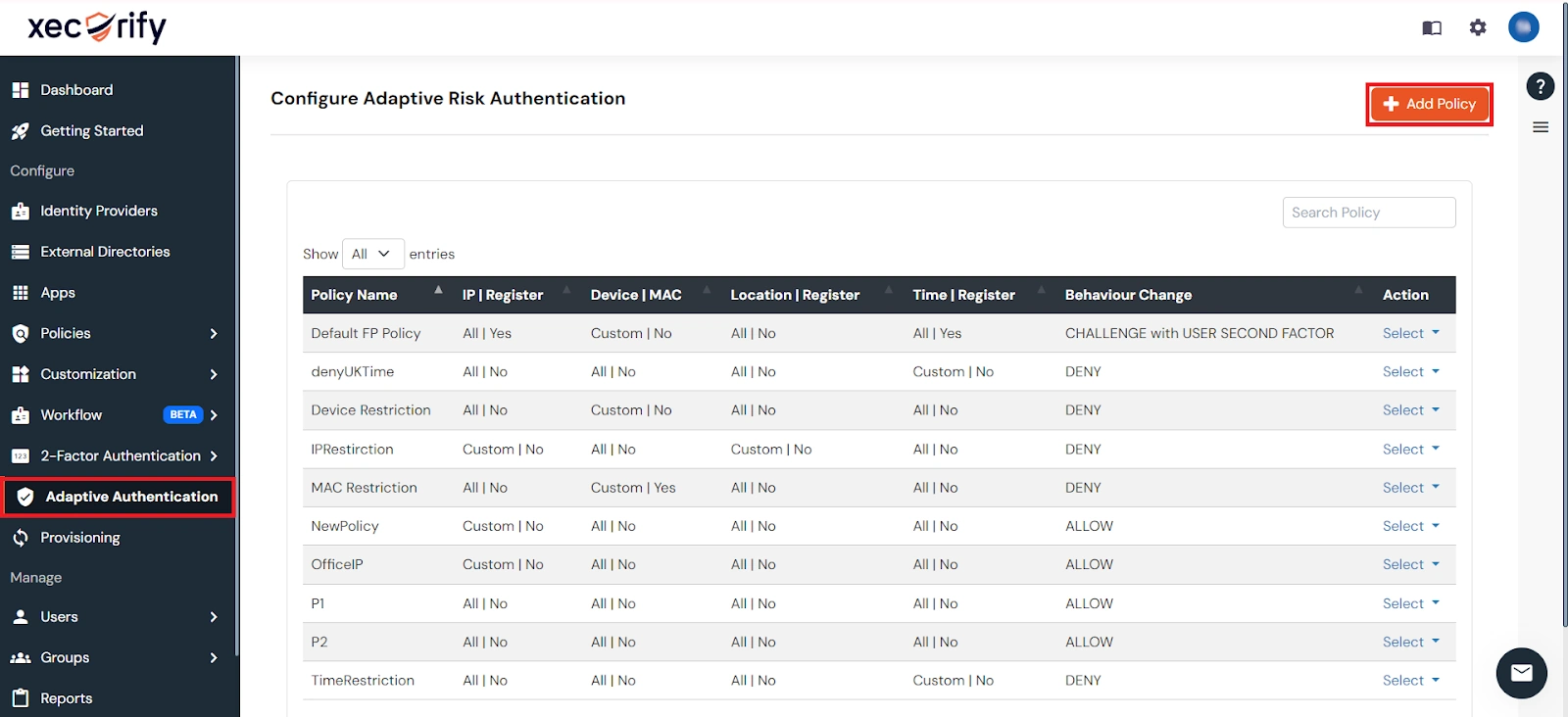
You can configure Adaptive Authentication with IP Blocking in following way :
| Attribute | Description |
|---|---|
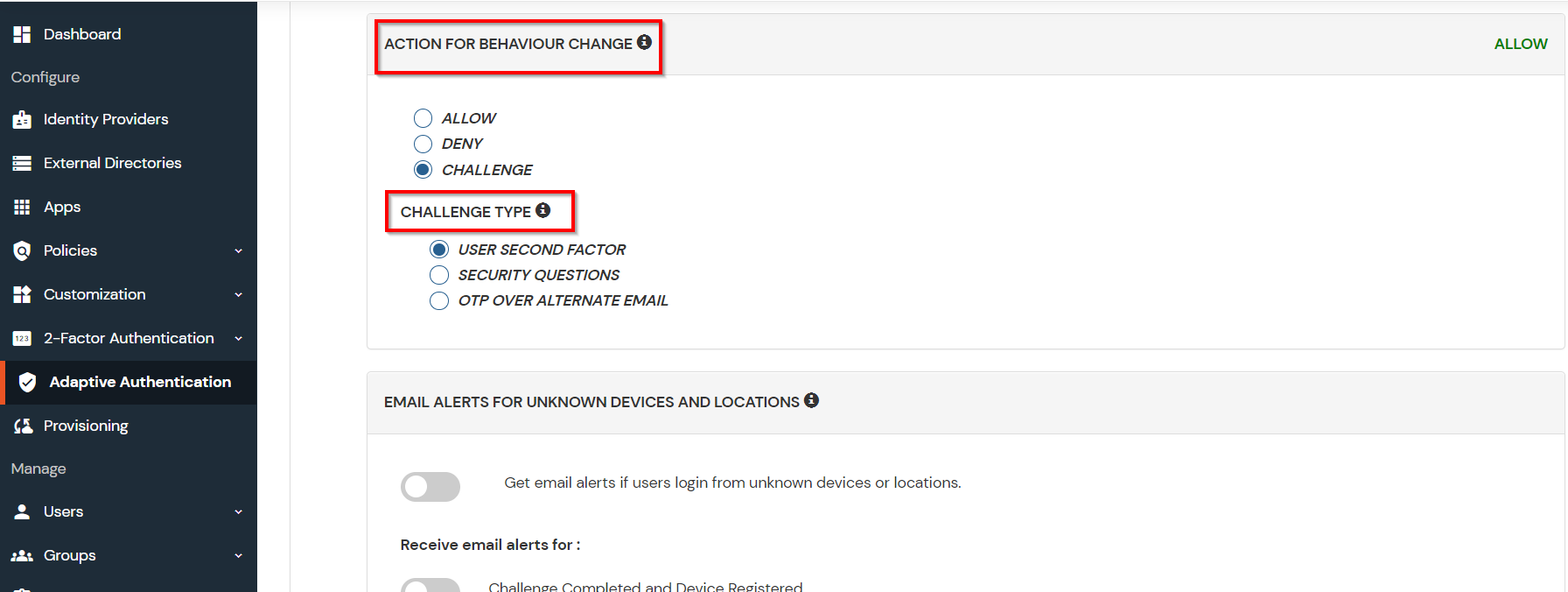
| Allow | Allow users to authenticate and use services if Adaptive authentication condition is true. |
| Deny | Deny user authentications and access to services if Adaptive authentication condition is true. |
| Challenge | Challenge users with one of the three methods mentioned below for verifying user authenticity. |
| Attribute | Description |
|---|---|
| User second Factor | The User needs to authenticate using the second factor he has opted or assigned for such as
|
| KBA (Knowledge-based authentication) | The System will ask the user for 2 of 3 questions he has configured in his Self-Service Console. Only after the right answer to both questions is the user allowed to proceed further. |
| OTP over Alternate Email | User will receive an OTP on the alternate email they have configured through the Self Service Console. Once the user provides the correct OTP, they are allowed to proceed further. |
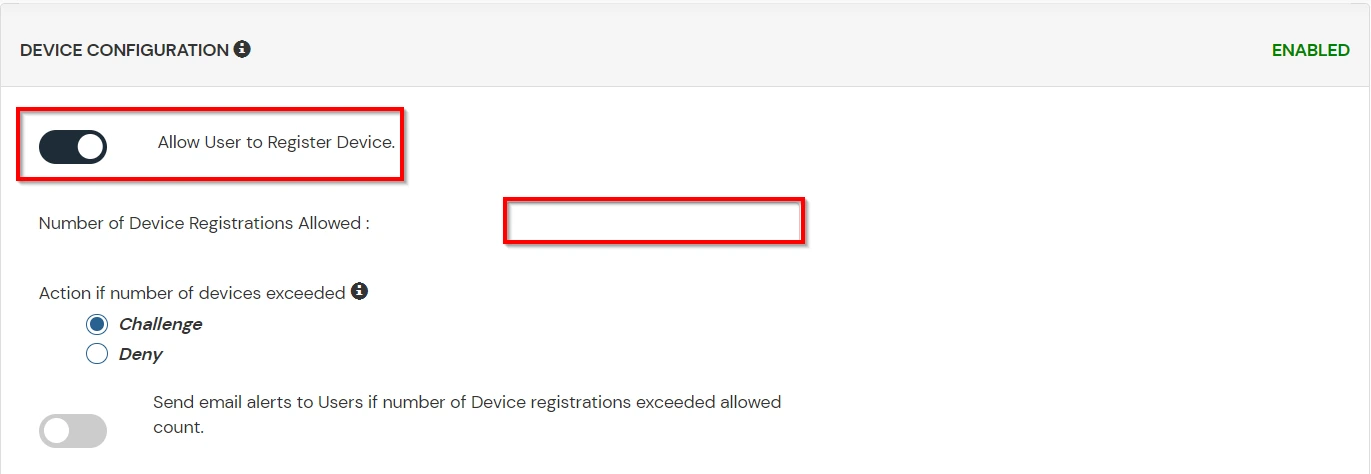
B. Adaptive Authentication with Limiting number of devices
Using Adaptive Authentication you can also restrict the number of devices the end user can access the Services on. You can allow end users to access services on a fixed no. of devices. The end users will be able to access services provided by us on this fixed no. of devices.
You can configure Adaptive Authentication with Device Restriction in following way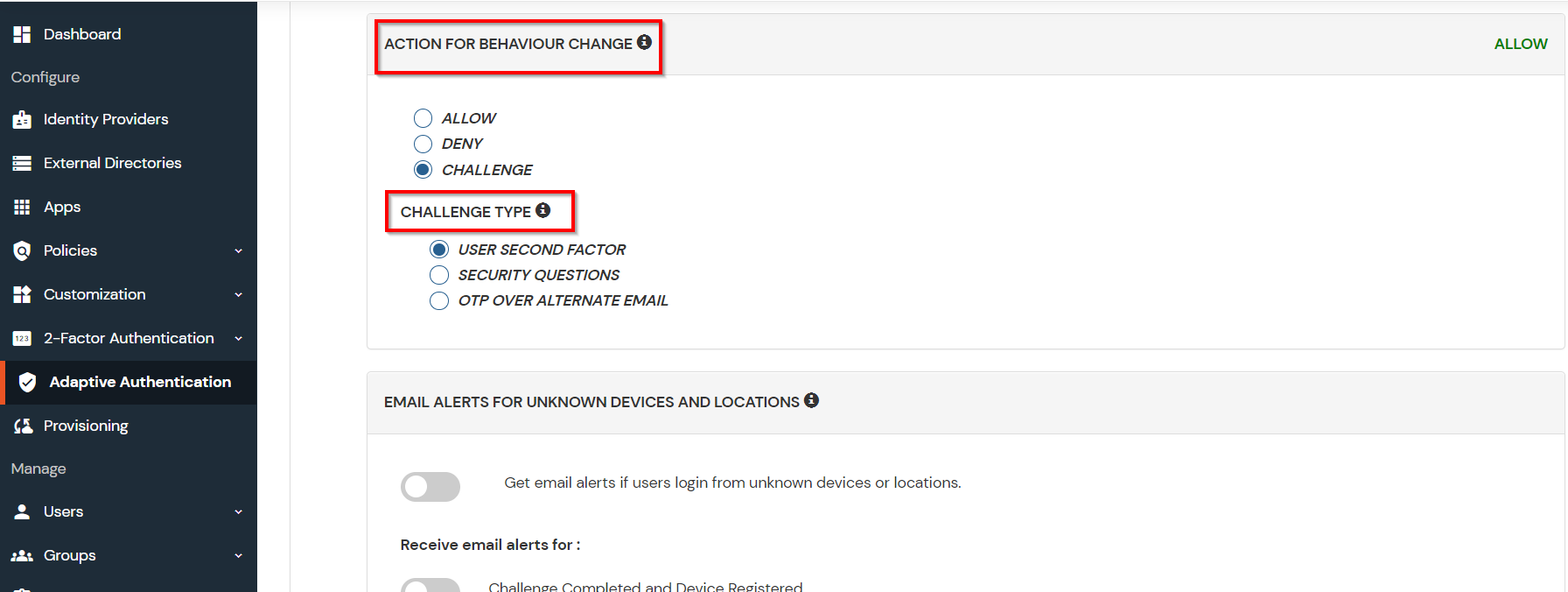
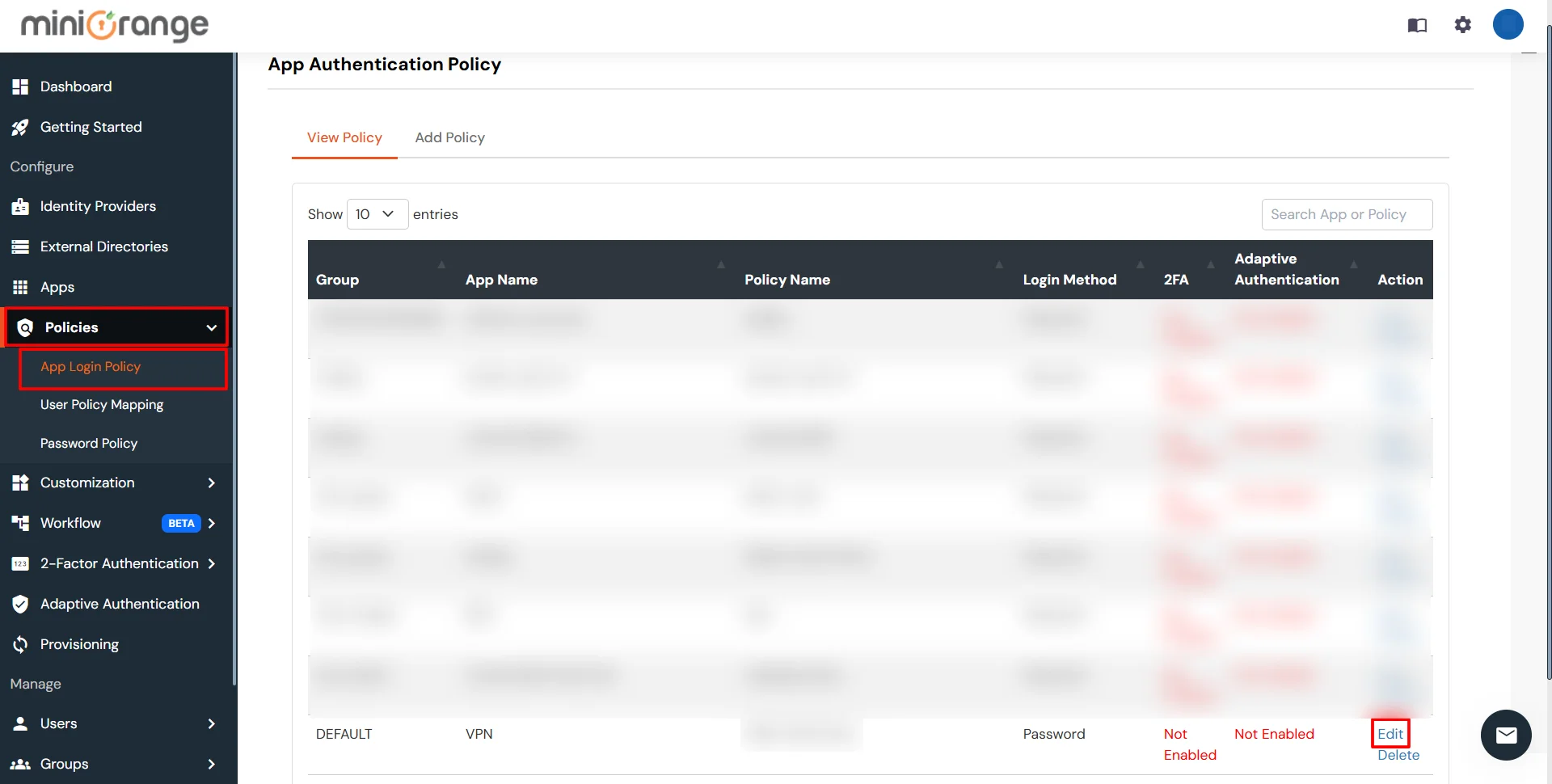
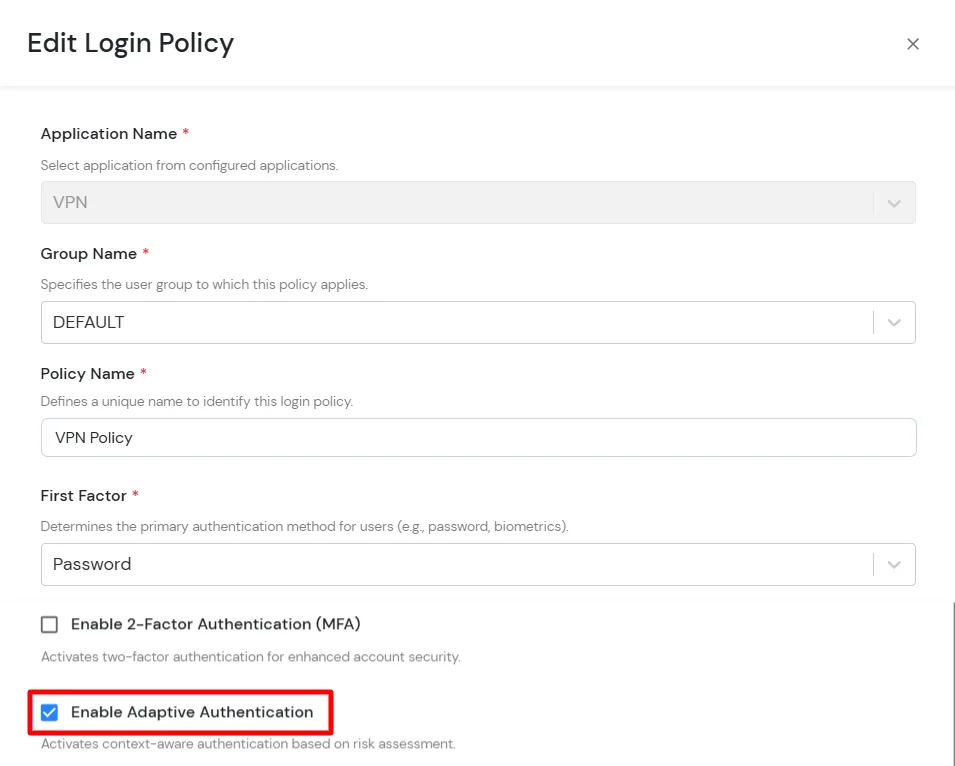
C. Add Adaptive Authentication policy to Exchange
D. Notification and Alert Message.
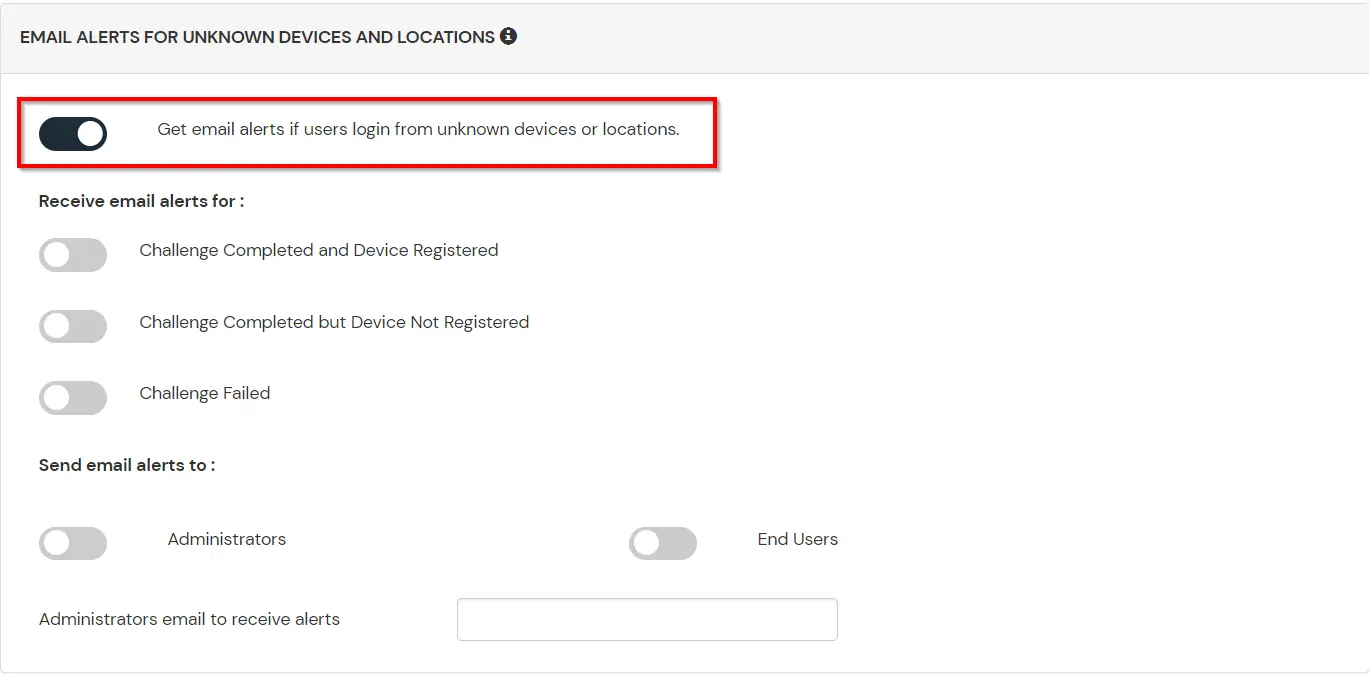
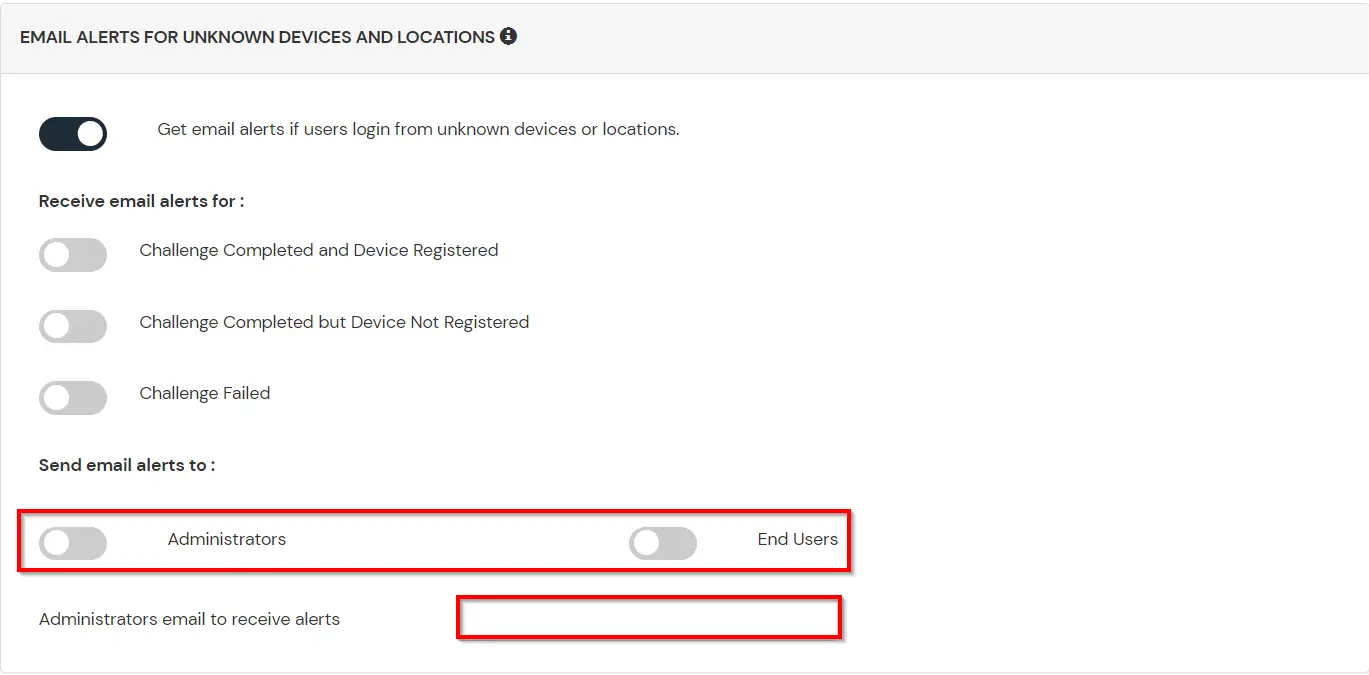
This section handles the notifications and alerts related to Adaptive Authentication. It provides the following options :
| Option | Description |
|---|---|
| Users login from unknown IP addresses, devices or locations | Enabling this option allows you to login from unknown IP addresses or devices and even locations. |
| Number of Device registrations exceeded allowed count | This option will allow you to register more devices than the devices you have numbered. |
| Challenge Completed and Device Registered | Enabling this option allows you to send an email alert when an end-user completes a challenge and registers a device. |
| Challenge Completed but Device Not Registered | Enabling this option allows you to send an email alert when an end-user completes a challenge but do not registers the device. |
| Challenge Failed | Enabling this option allows you to send an email alert when an end-user fails to complete the challenge. |
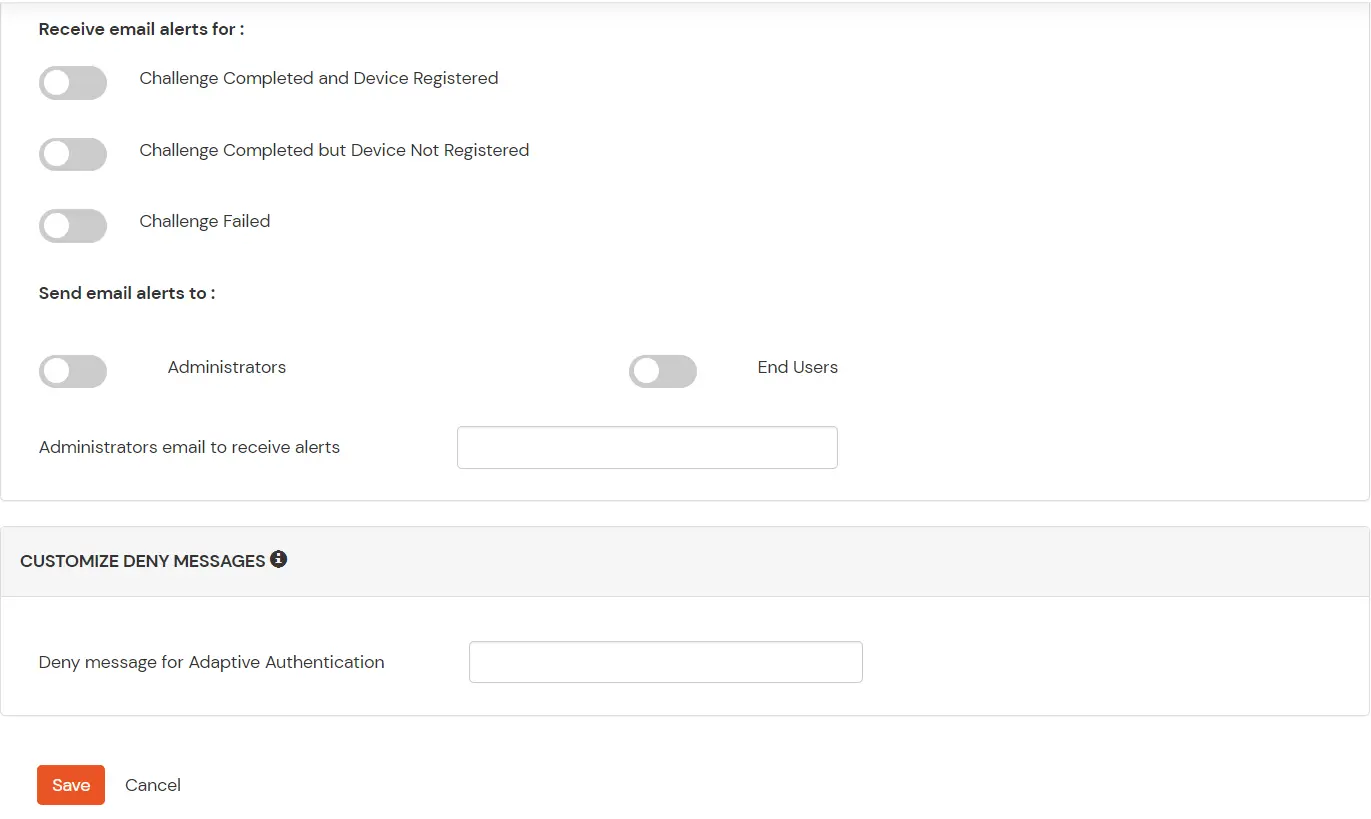
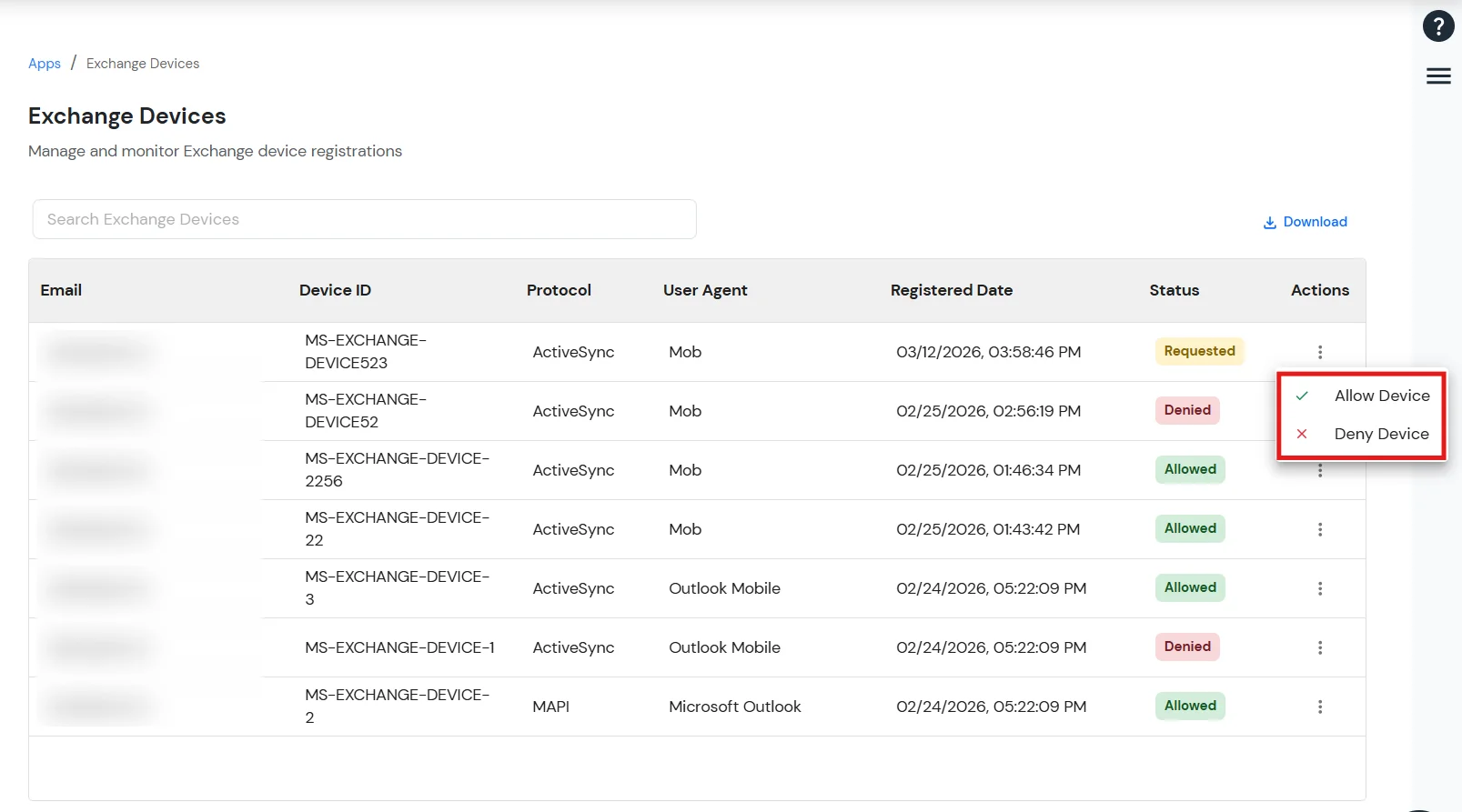
The Manage Exchange Devices feature allows administrators to control which devices are permitted to access the Exchange ActiveSync application.
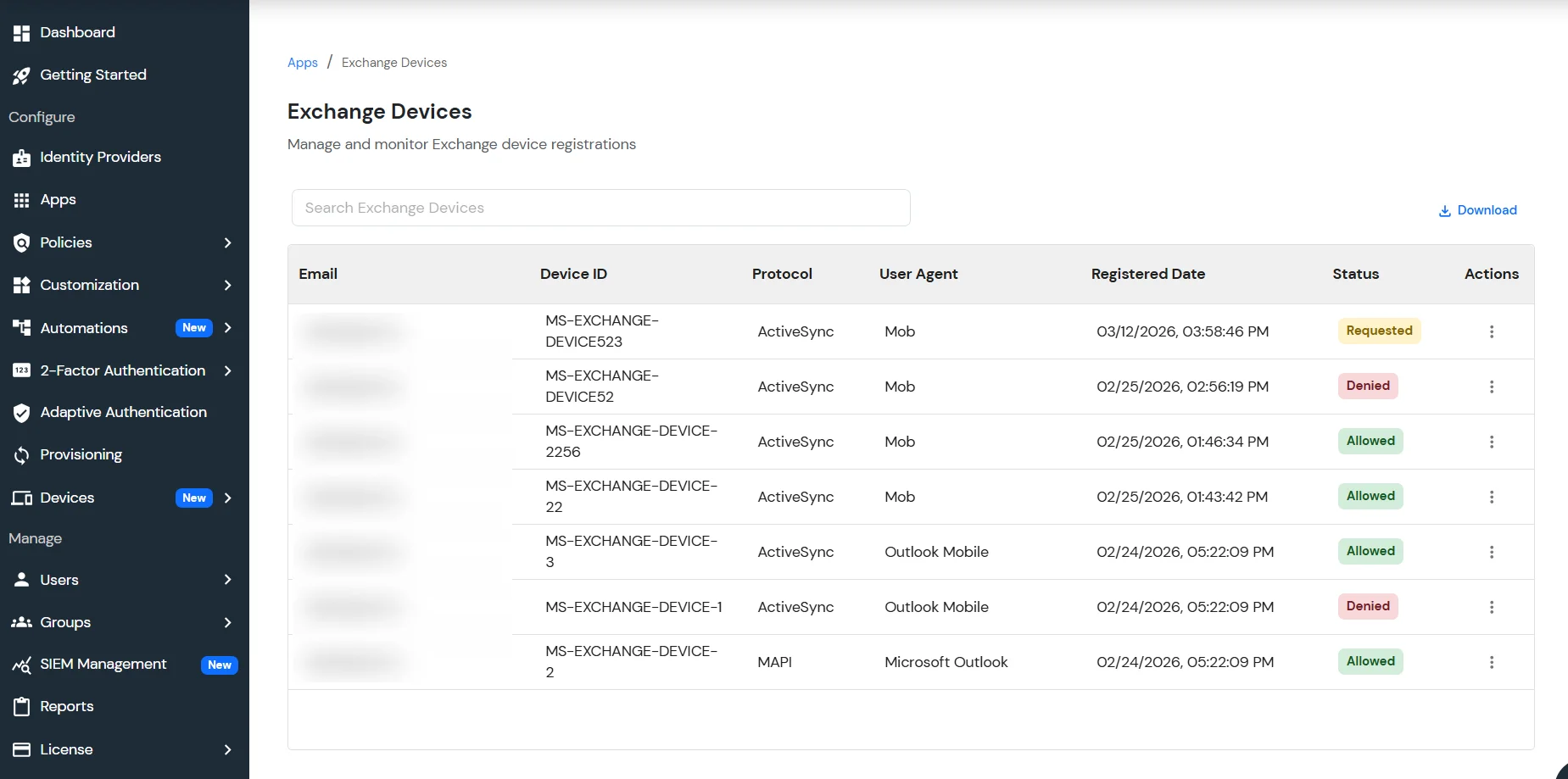
Each device is assigned a status based on its access level:
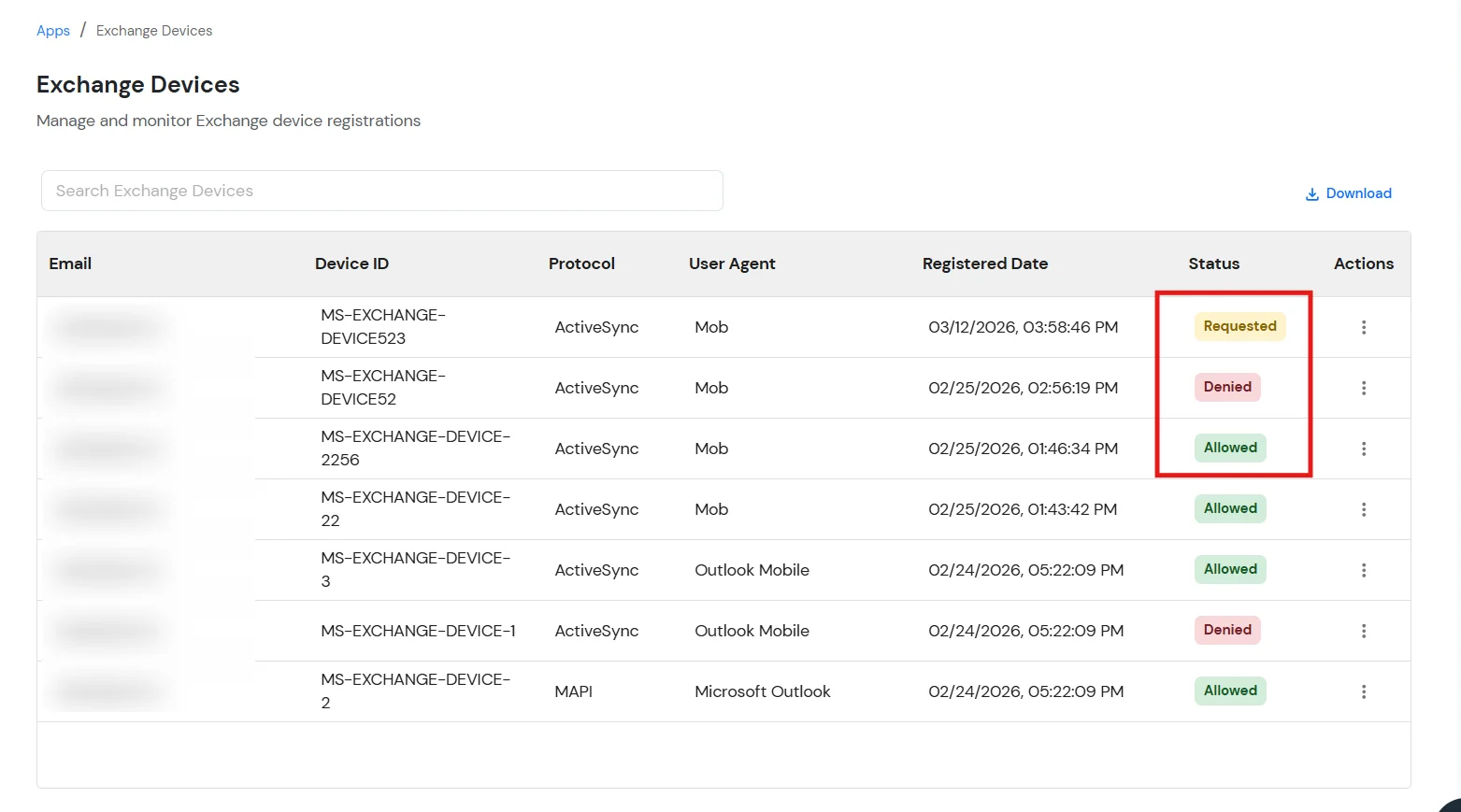
Administrators can take the following actions:
This ensures that only authorized devices can connect to the Exchange environment.
Get-OwaVirtualDirectory | Set-OwaVirtualDirectory -AdfsAuthentication $false
-BasicAuthentication $false -DigestAuthentication $false -FormsAuthentication $true
-WindowsAuthentication $false -OAuthAuthentication $falseGet-EcpVirtualDirectory | Set-EcpVirtualDirectory -AdfsAuthentication $false
-BasicAuthentication $false -DigestAuthentication $false -FormsAuthentication $true
-WindowsAuthentication $false# Restart w3svc and was
net stop was /y
net start w3svc
