Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
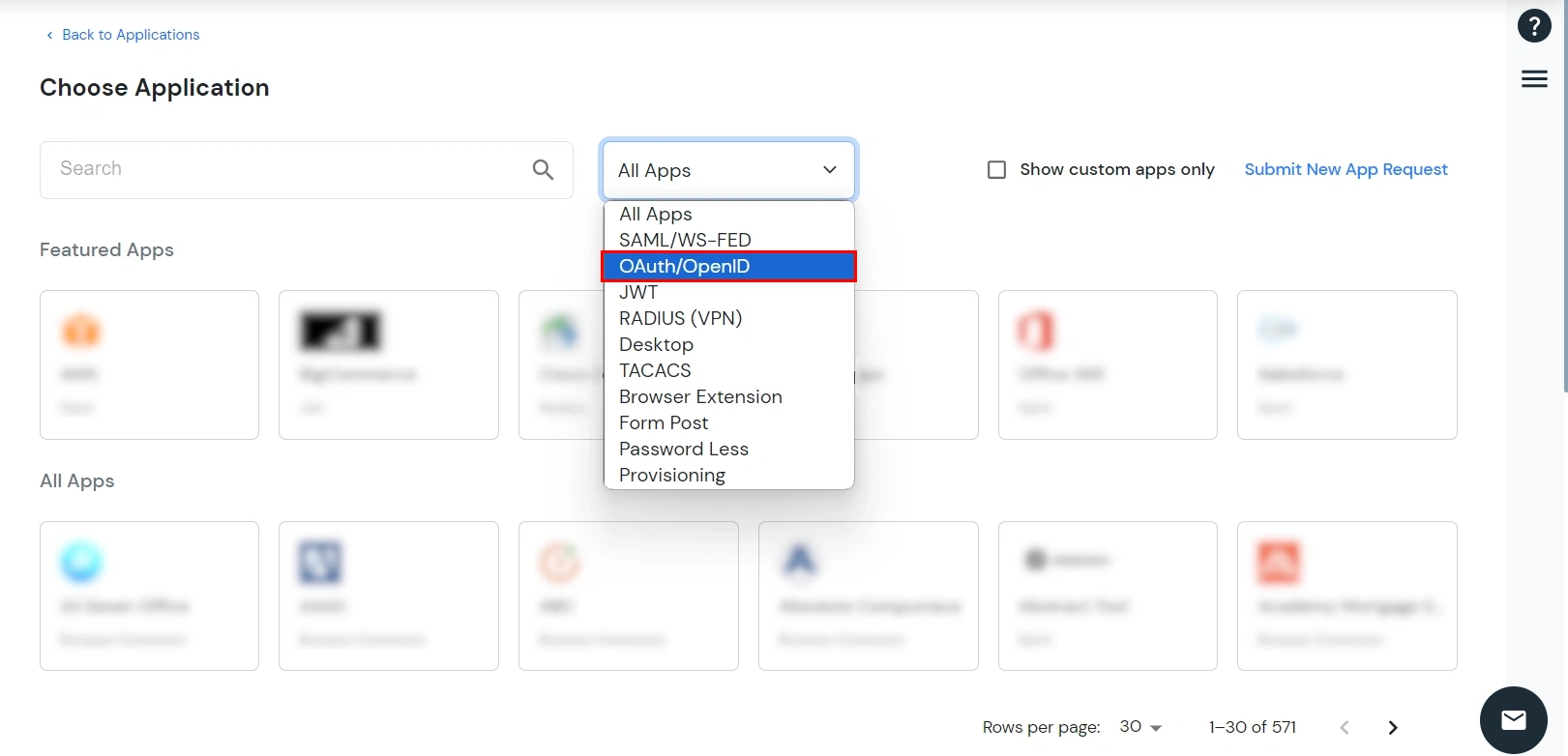
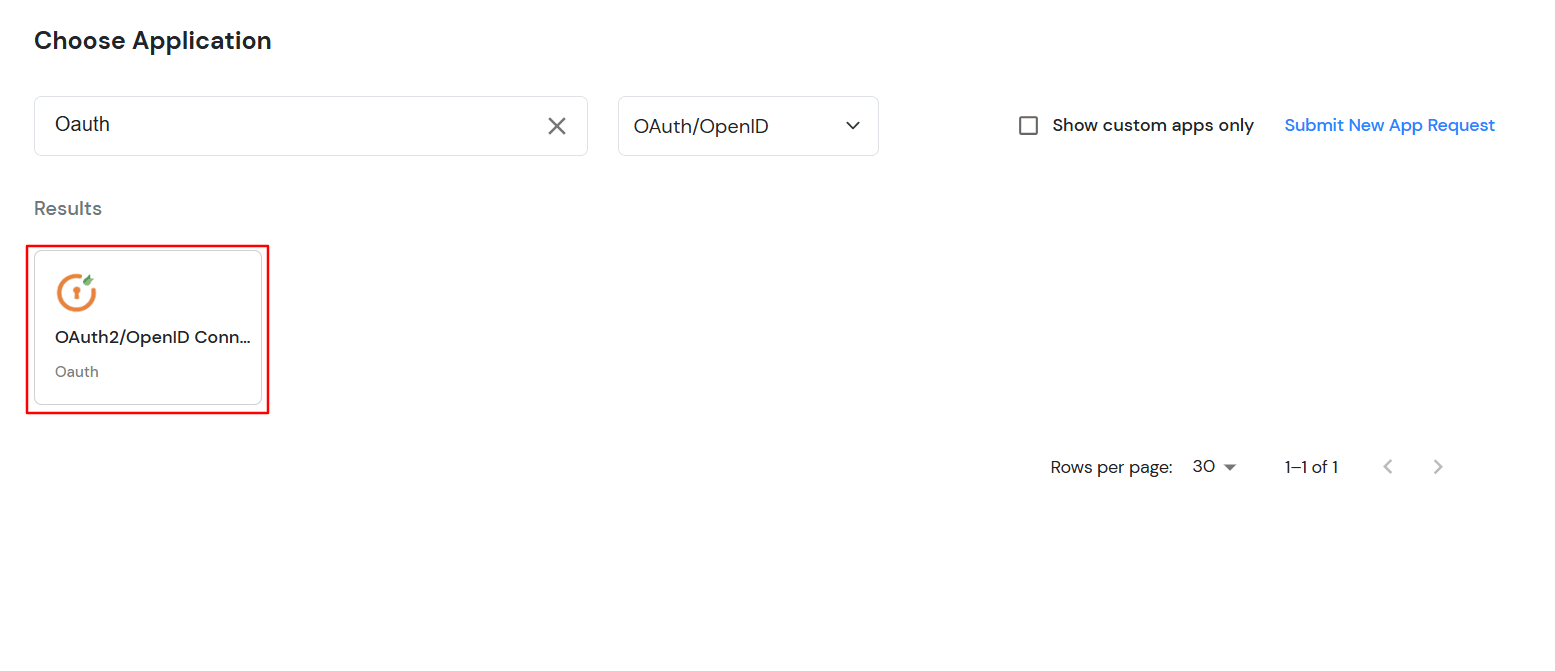
×Wickr is an OAuth supported open source communication hub. The Wickr instant messaging apps helps organizations to allow users to exchange end-to-end encrypted and content-expiring messages, including photos, videos, and file attachments. Based on different customer needs Wickr has developed several secure messaging apps: Wickr Me, Wickr Pro, Wickr RAM, and Wickr Enterprise.
OAuth (Open Authorization) is an open standard for token-based authentication and authorization which is used to provide single sign-on (SSO). OAuth doesn’t share password data but instead uses authorization tokens to prove an identity between consumers and service providers. OAuth is an authentication protocol that allows you to approve one application interacting with another on your behalf without giving away your password.
Applications that support login using third party services generally prompt the user to authenticate themselves by giving options like “Login With Facebook” or “Login With Google” etc. thus, allowing the user to use their credentials to login with the third party service. In response, the service sends the access token to the requesting application which proves the authenticity of the user who is requesting access. The token is then used for making requests to resources required by the end-user.OAuth is suitable for both browser and mobile applications and it is widely used for customer application and API access. Baically, OAuth uses JSON to transfer messages between applications & uses HTTP for requesting and receiving tokens.
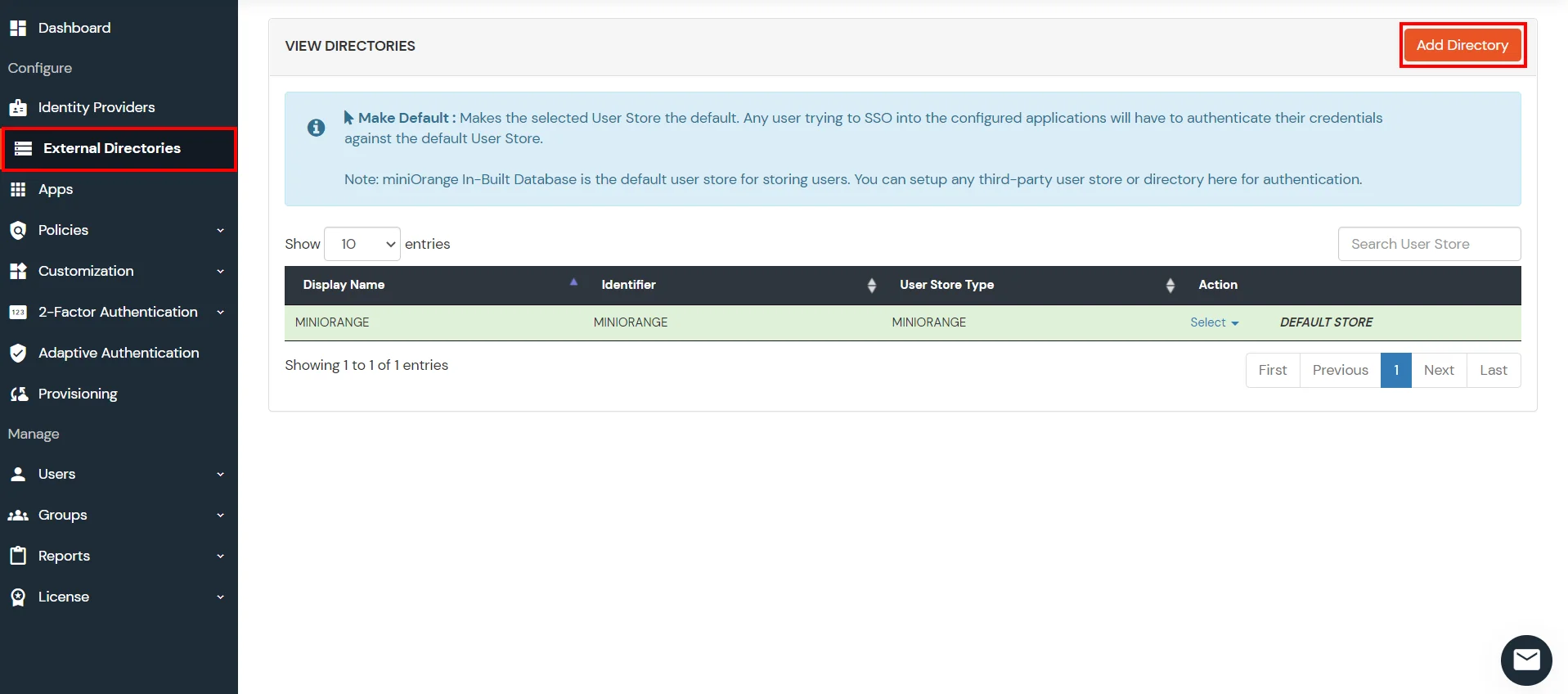
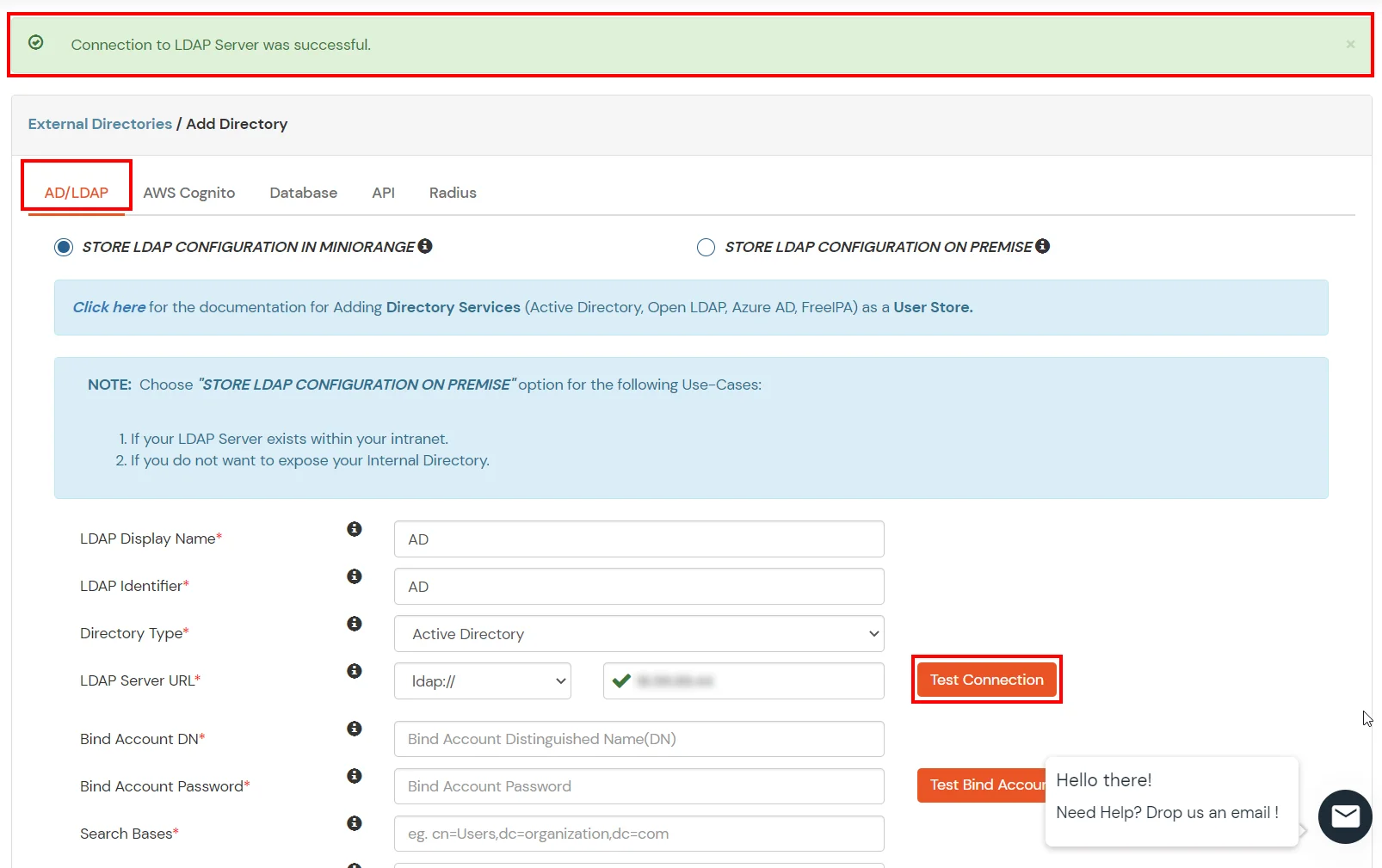
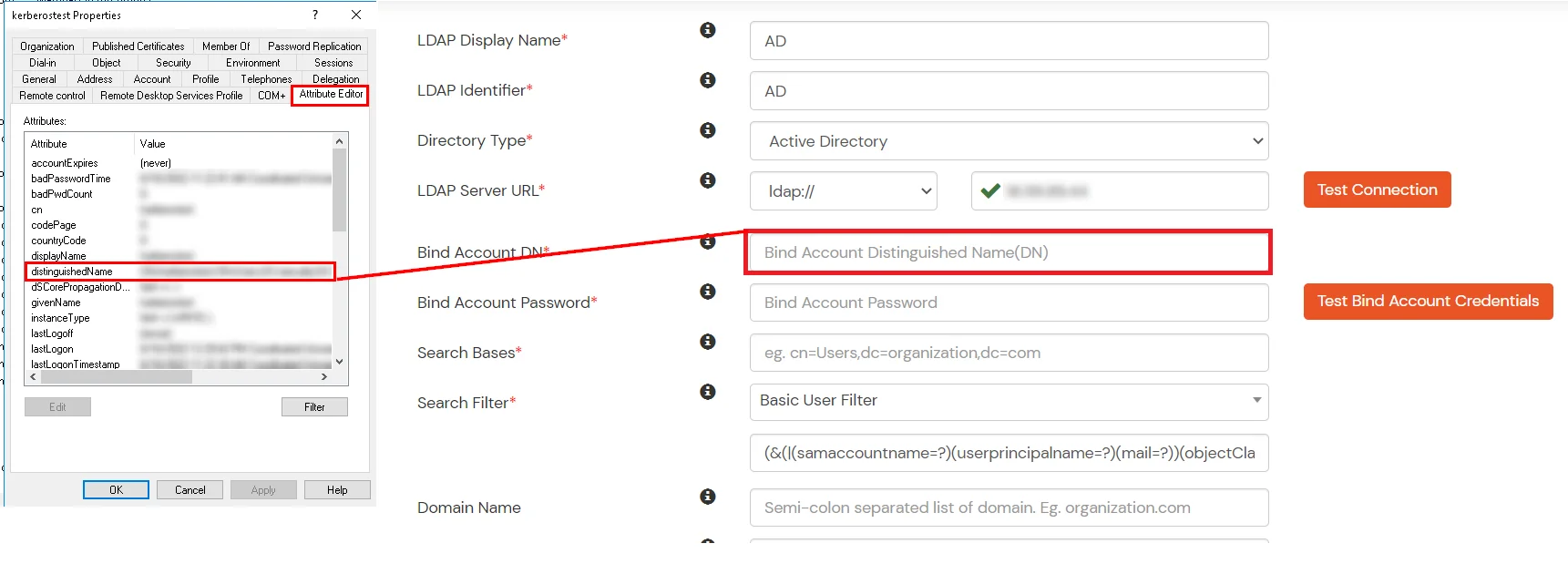
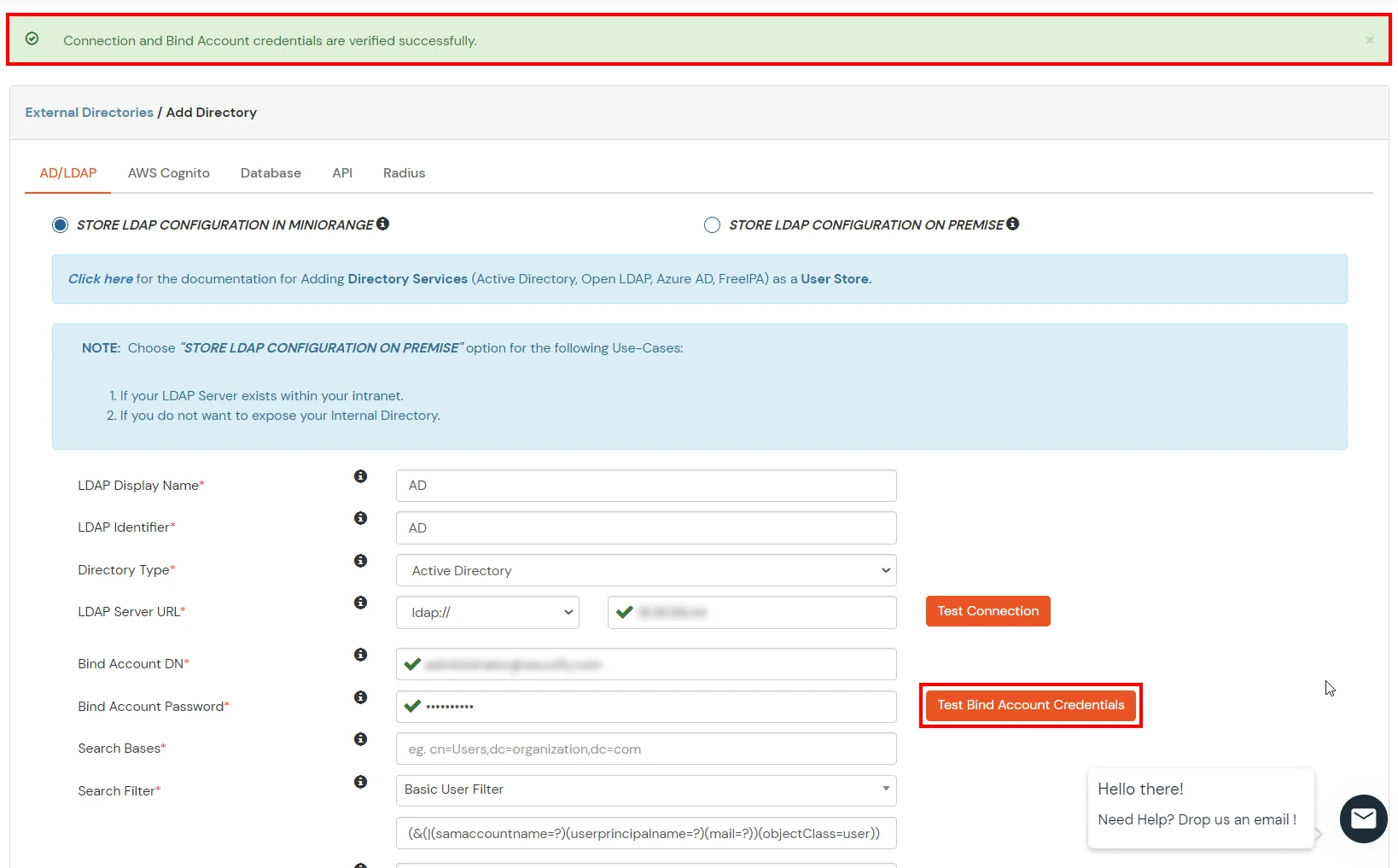
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.

Authorization
Grant

Password
Grant

Implicit
Grant

Refresh Token
Grant

Client Credentials
Grant

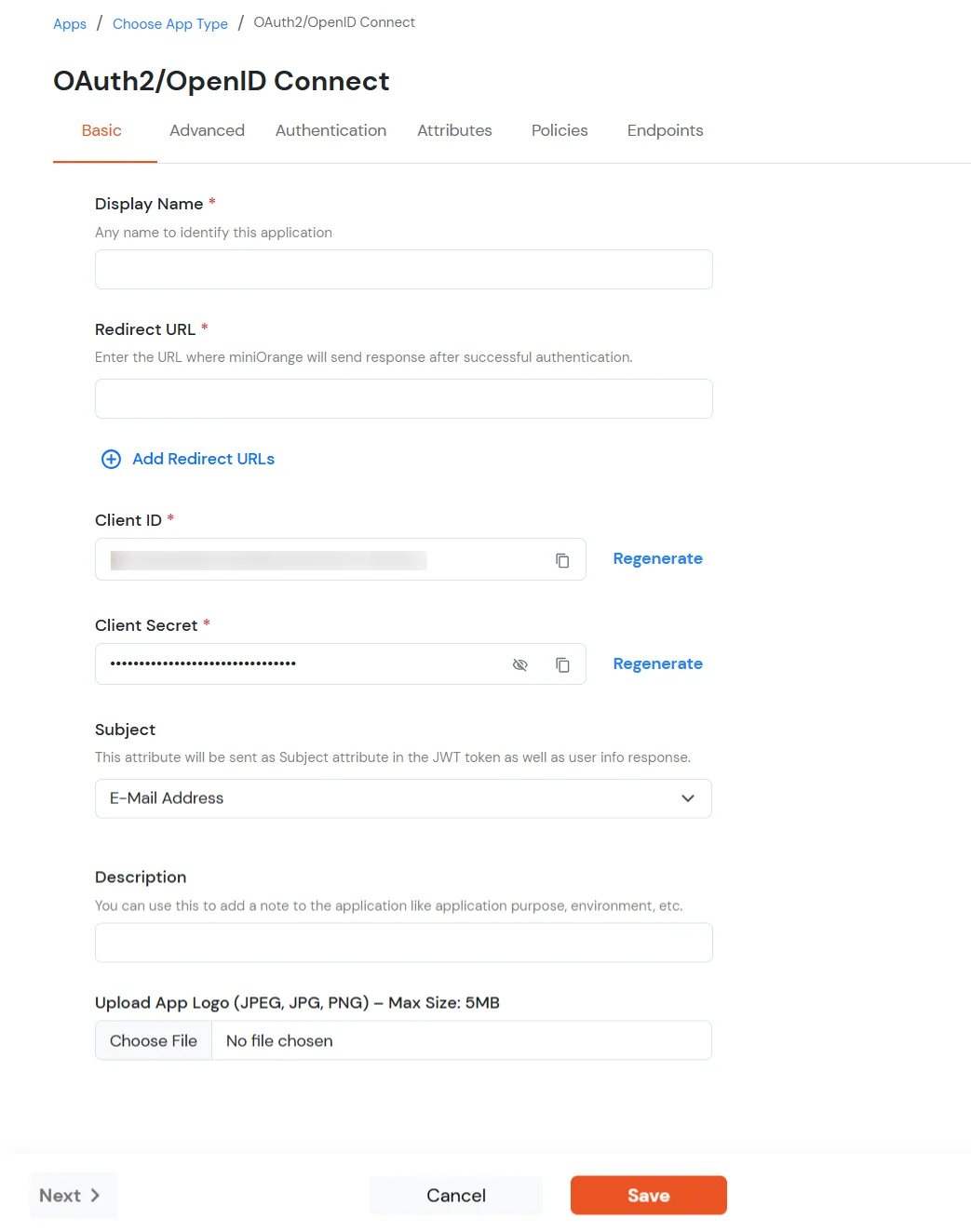
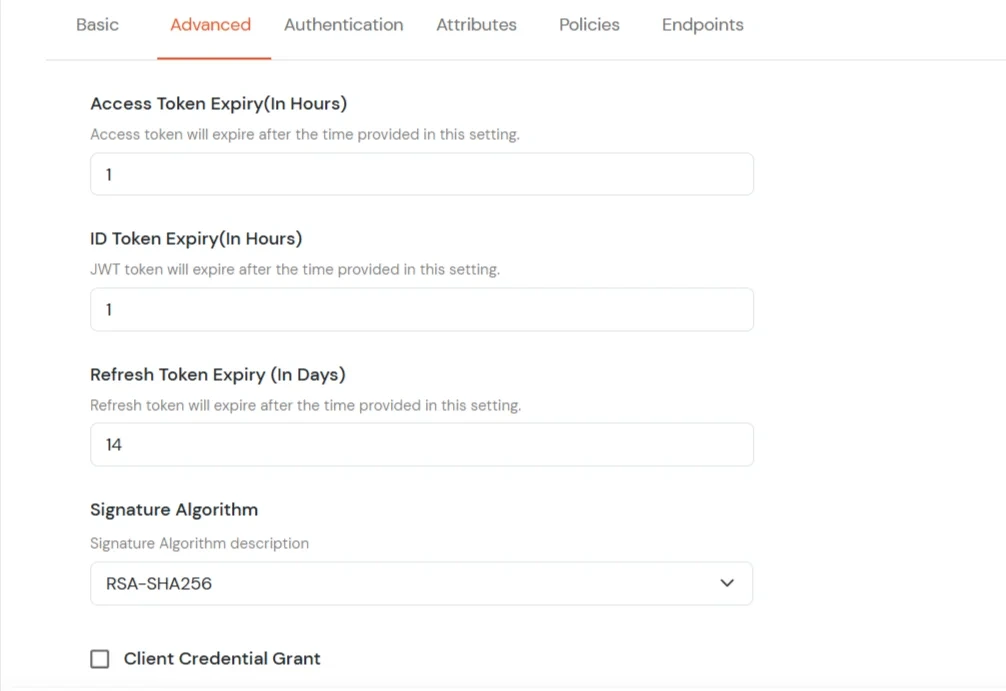
| Basic Tabs | Description |
|---|---|
| Display Name | Enter the Display Name (i.e., the name for this application). |
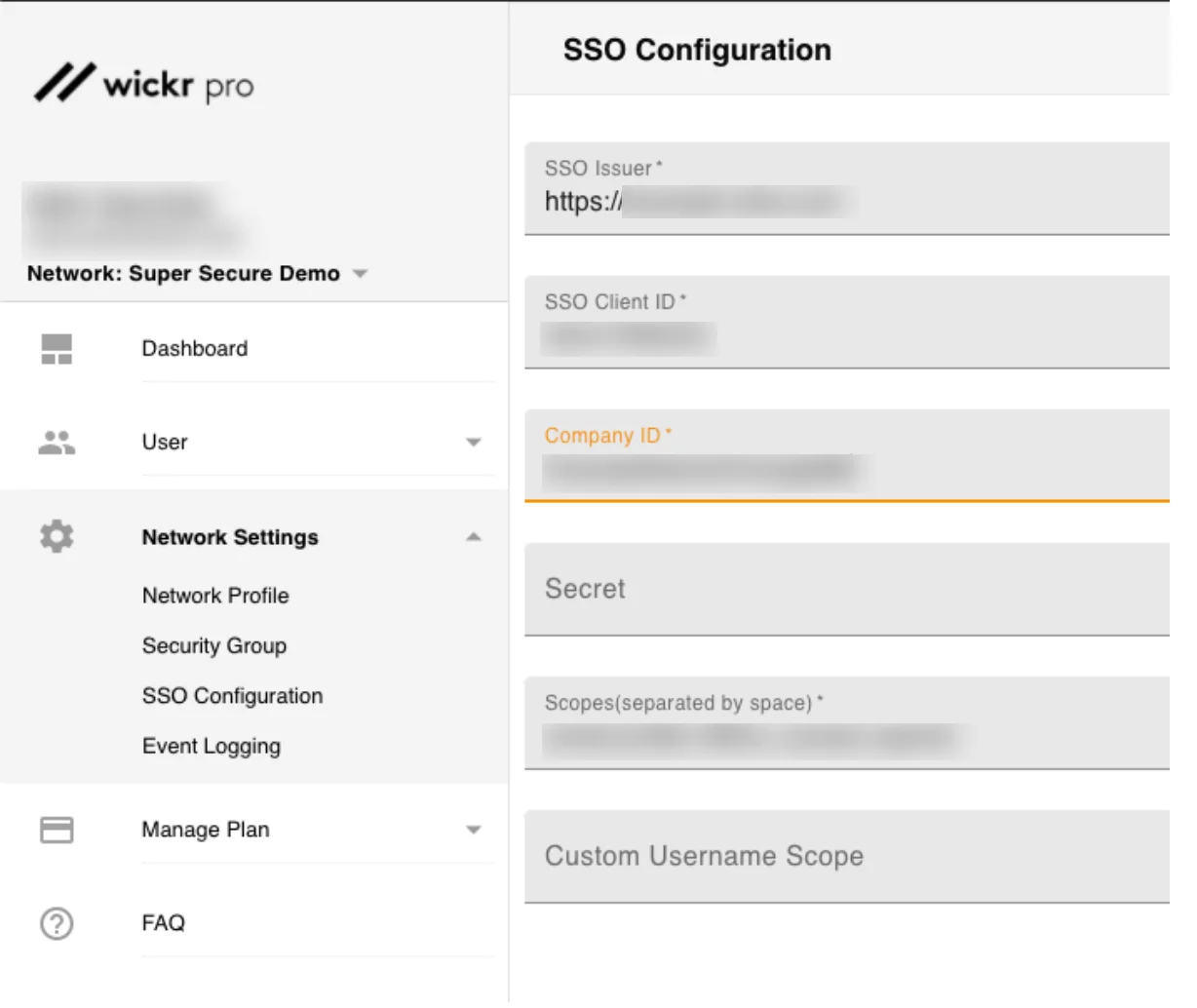
| Redirect URL | Copy the Redirect-URL from Wickr Application. You will get this URL when you create an application in the Wickr admin console. |
| Client ID | You can find Client ID by clicking the icon as shown below. |
| Client Secret | You can find Client Secret by clicking the icon as shown below. |
| Description (Optional) | Add a description if required. |
| Upload App Logo (Optional) | Upload an app logo (Optional). The app will be shown in the end-user dashboard with the logo that you configure here. |
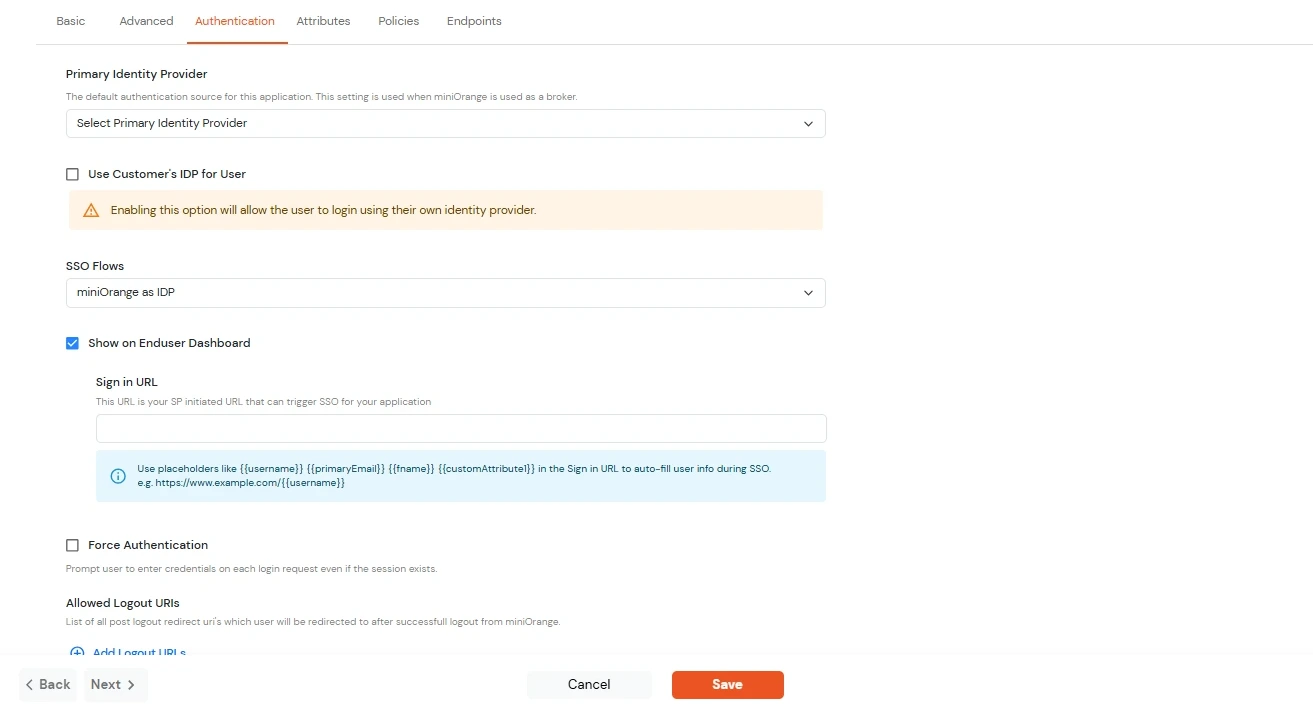
| Primary Identity Provider | Select the default ID source from the dropdown for the application. If not selected, users will see the default login screen and can choose their own IDP. [Choose miniOrange in this case.] |
| SSO FLows | Select the desired SSO flow from the dropdown, such as miniOrange as IDP, miniOrange as Broker, or miniOrange as Broker with Discovery Flow. |
| Show on Enduser Dashboard | Enable this option if you want to show this app in the end-user dashboard. |
| Force Authentication | If you enable this option, users will have to log in every time, even if their session already exists. |
| Allowed Logout URIs | Click the Allowed Logout URIs link to add a list of post-logout redirect URIs. Users will be redirected to one of these URIs after a successful logout from miniOrange. |
| Single Logout Enabled | Enable this option to send logout requests to other applications when logging out from this app. |
| Sign in URL | You can include user attributes in the sign-in URL using placeholders like {{username}}, {{primaryEmail}}, {{customAttribute1}}, etc. These placeholders will be dynamically replaced with the actual user values during the IdP-initiated SSO flow. You can generate url using following attributes: username, primaryEmail, alternateEmail, fname, lname, primaryPhone and customAttribute1. The url could be like this https://<sso-url>>?username={{username}}
https://<sso-url>>?username={{username}}&email={{primaryEmail}}https://<sso-url>>/{{customAttribute1}}/{{customAttribute2}}/?username={{username}} |
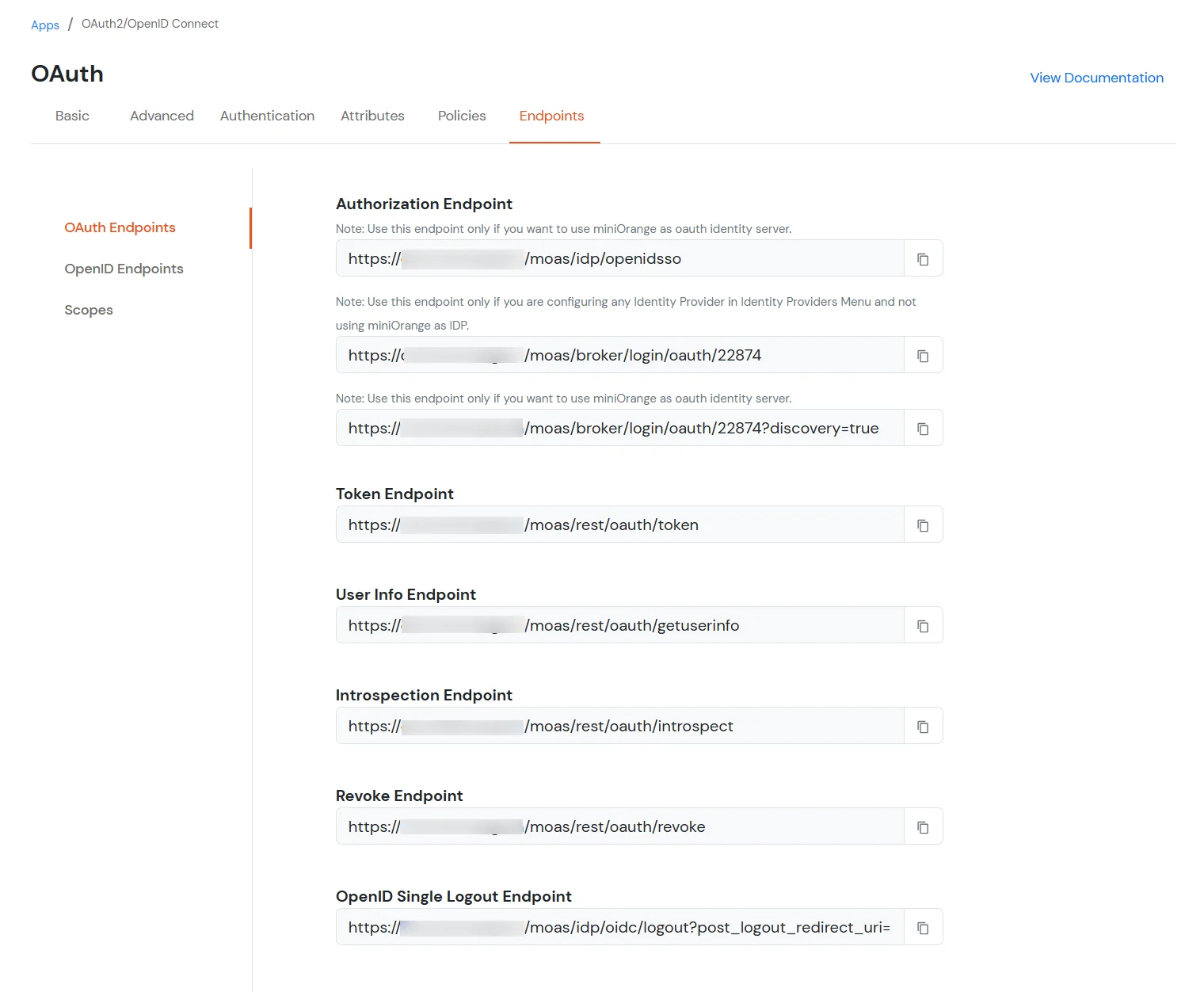
| Authorization Endpoint: | https://login.xecurify.com/moas/idp/openidsso
(Note: Use this endpoint only if you want to use miniorange as oauth identity server.) https://login.xecurify.com/moas/broker/login/oauth/260174 (Note: Use this endpoint only if you are configuring any Identity Provider in Identity Providers Menu and not using miniorange as IDP.) |
| Token Endpoint: | https://login.xecurify.com/moas/rest/oauth/token |
| User Info Endpoint: | https://login.xecurify.com/moas/rest/oauth/getuserinfo |
| Introspection Endpoint: | https://login.xecurify.com/moas/rest/oauth/introspect |
| Revoke Endpoint: | https://login.xecurify.com/moas/rest/oauth/revoke |
| OpenID Single Logout Endpoint: | https://login.xecurify.com/moas/idp/oidc/logout?post_logout_redirect_uri= |
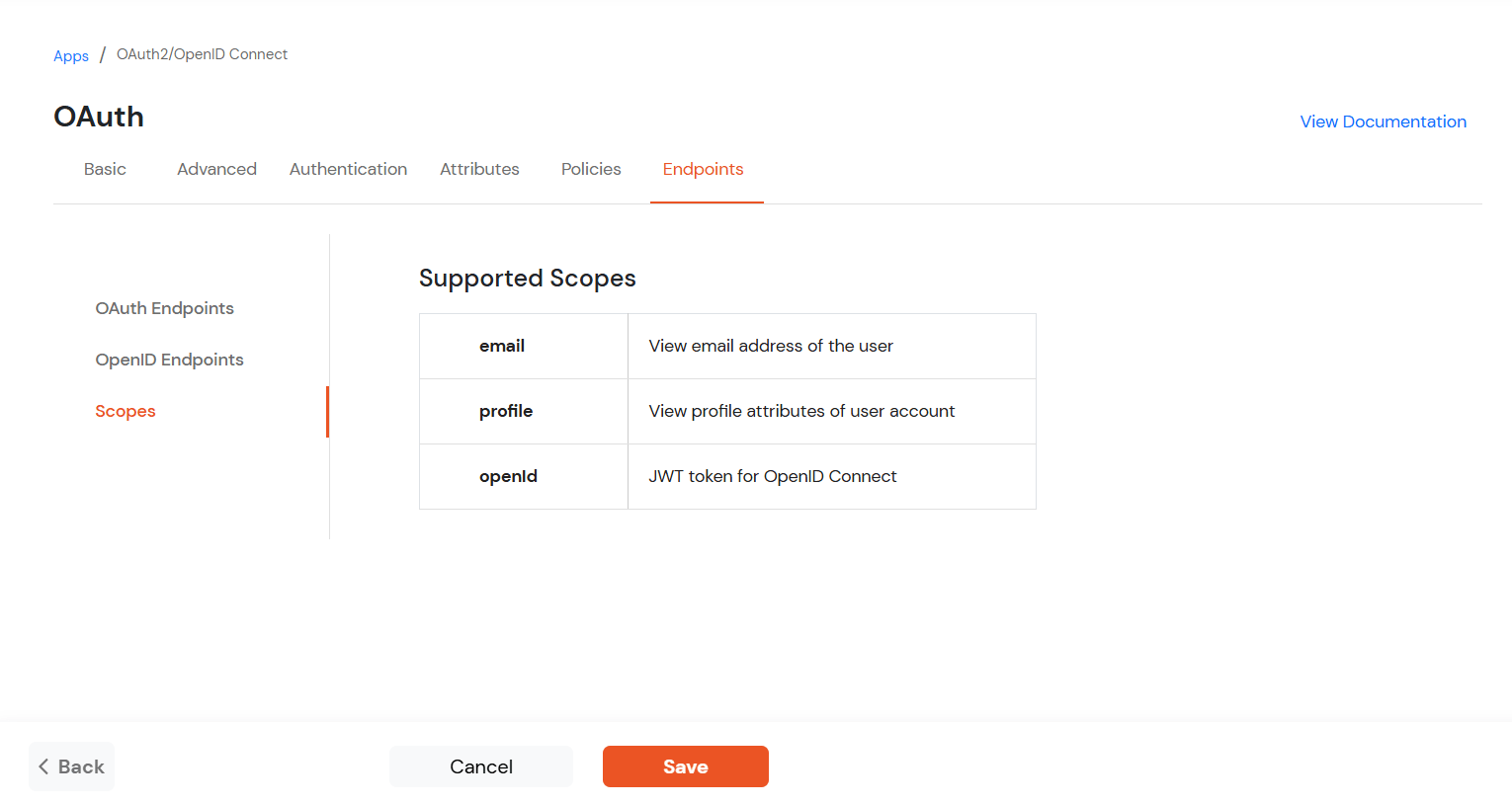
| email : | View email address of the user |
| profile : | View profile attributes of the user account |
| openid : | Retrieve JWT token for OpenID Connect |
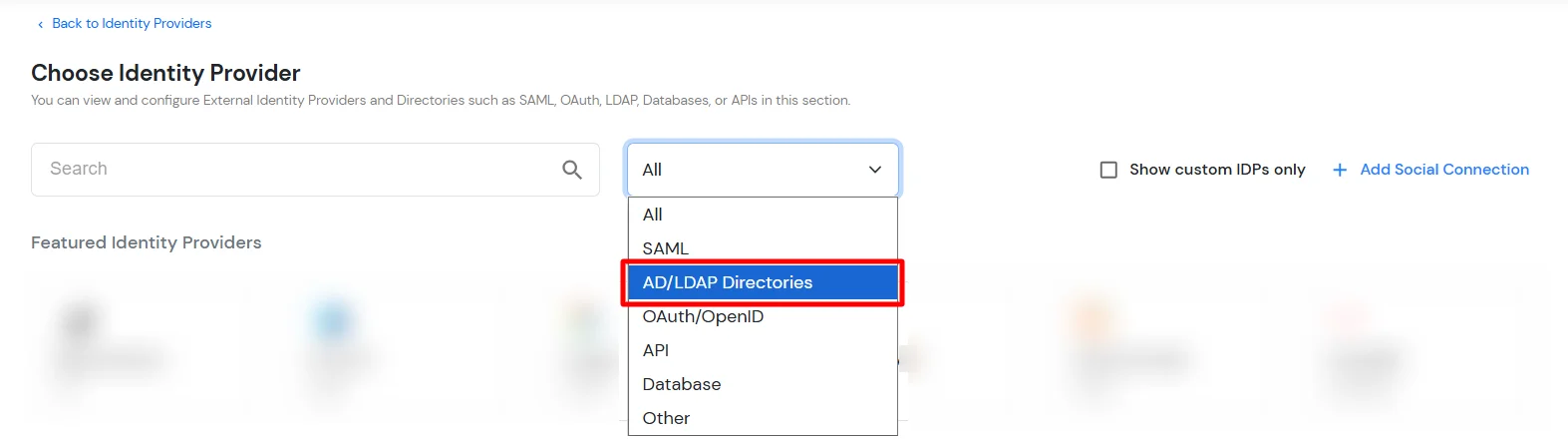
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
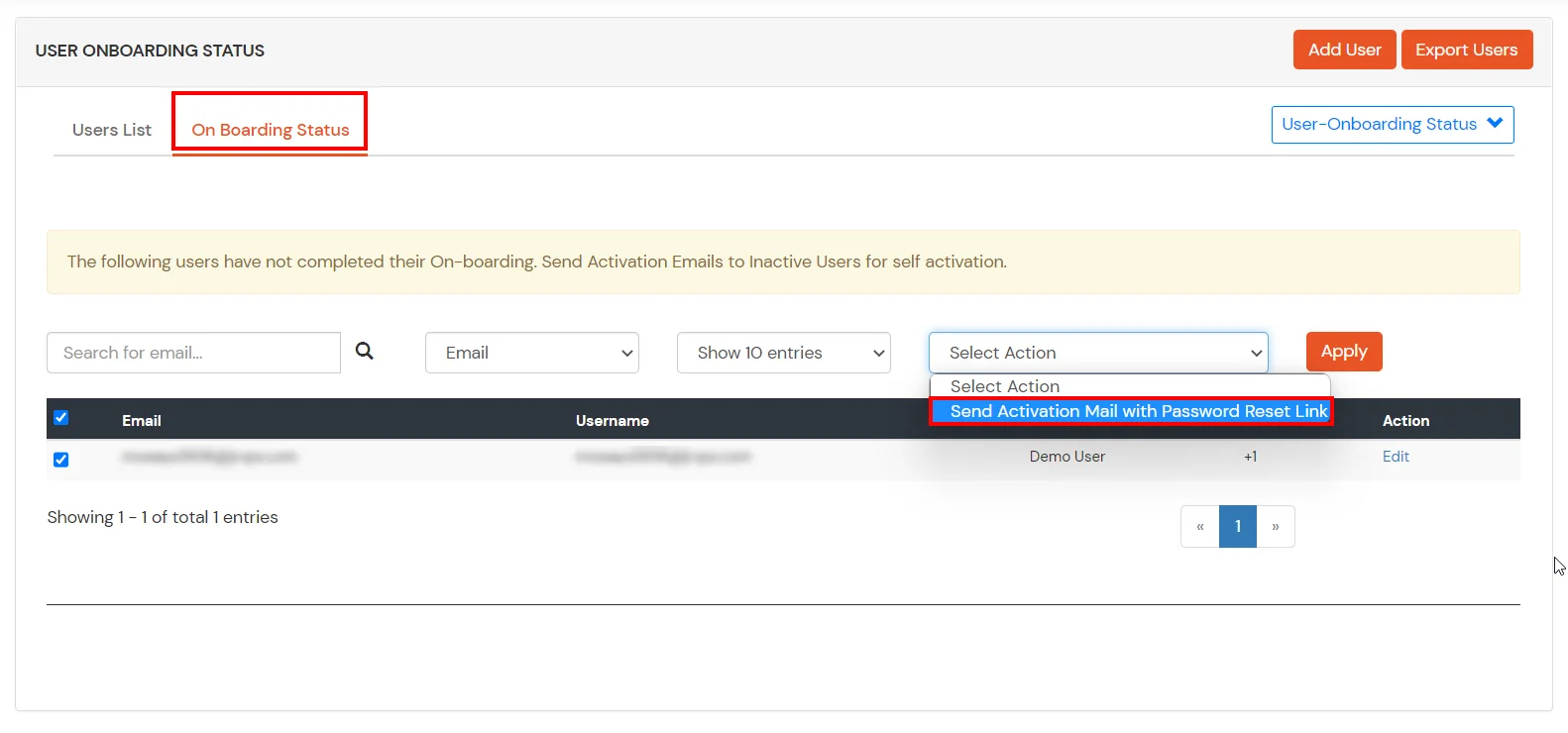
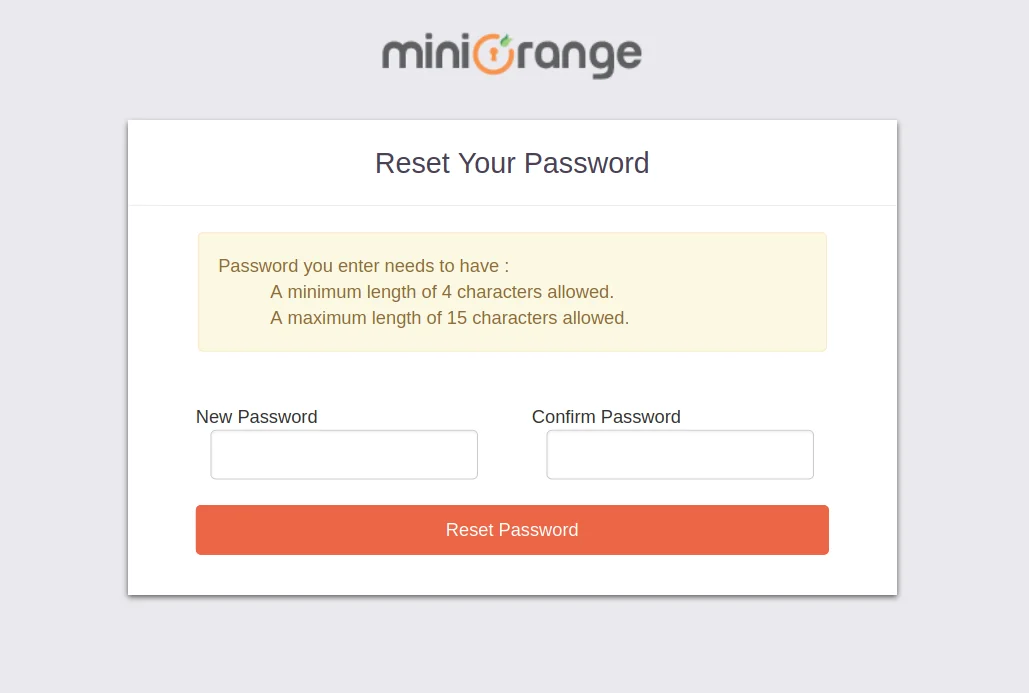
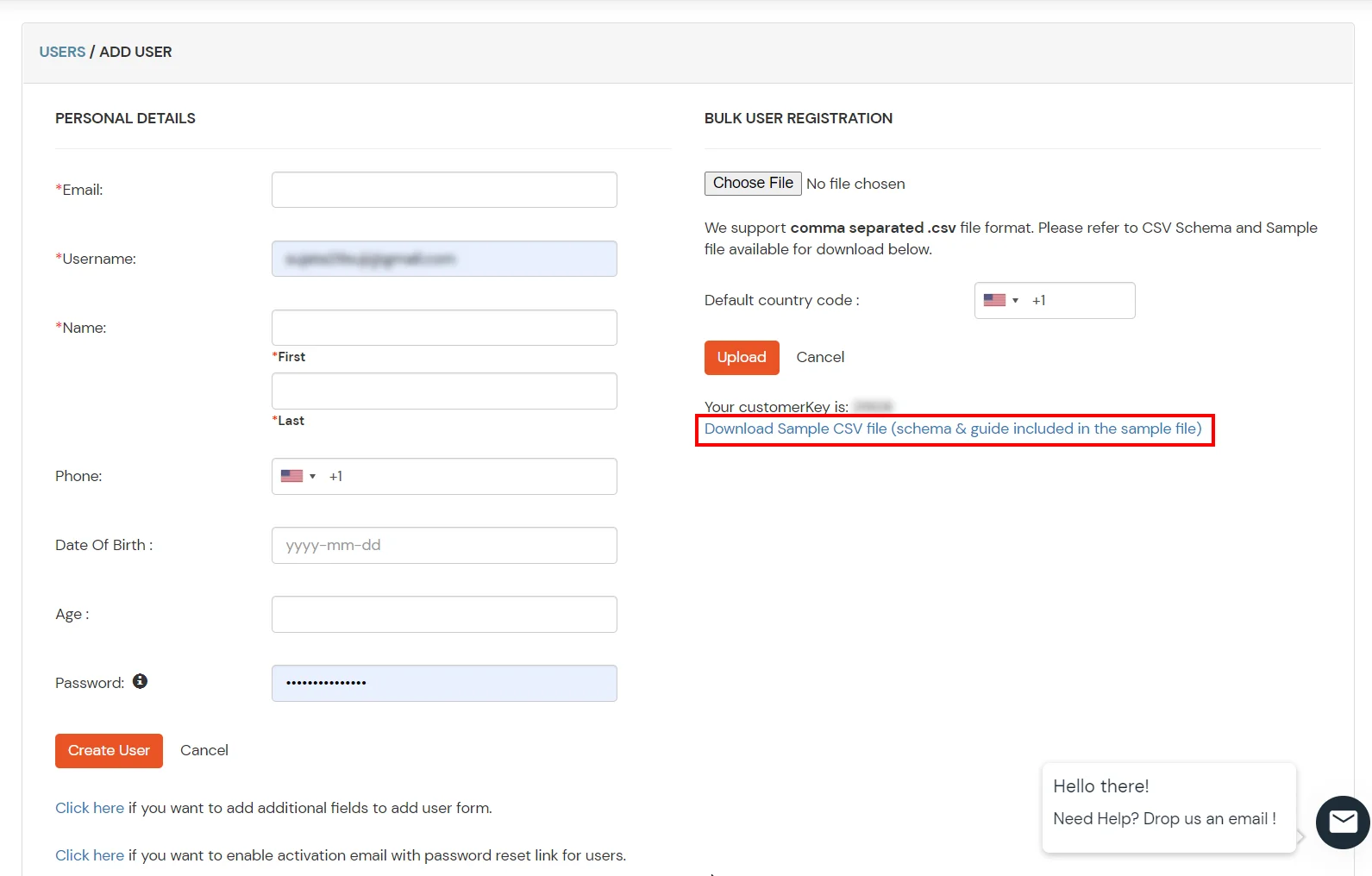
1. Create User in miniOrange

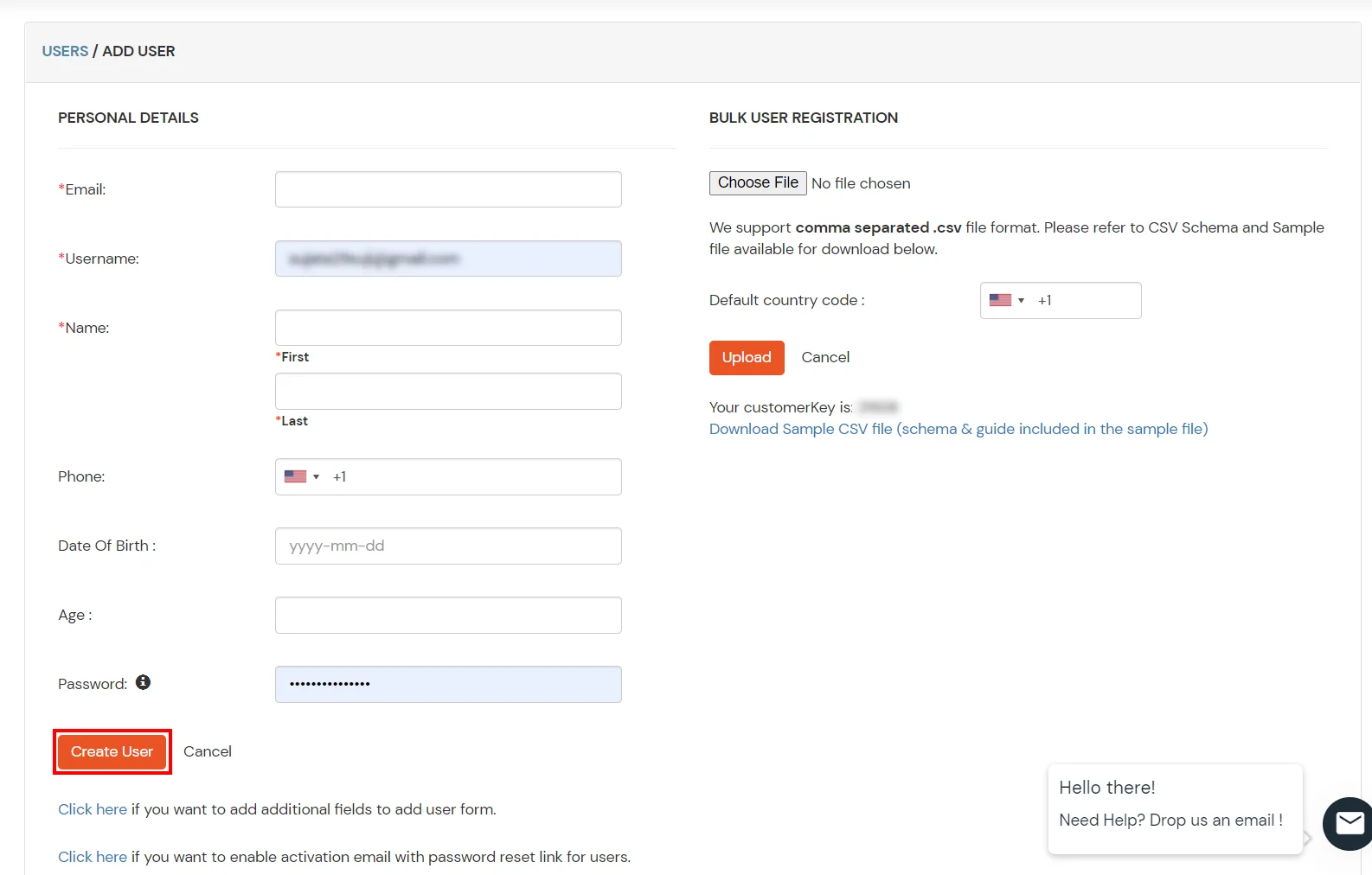
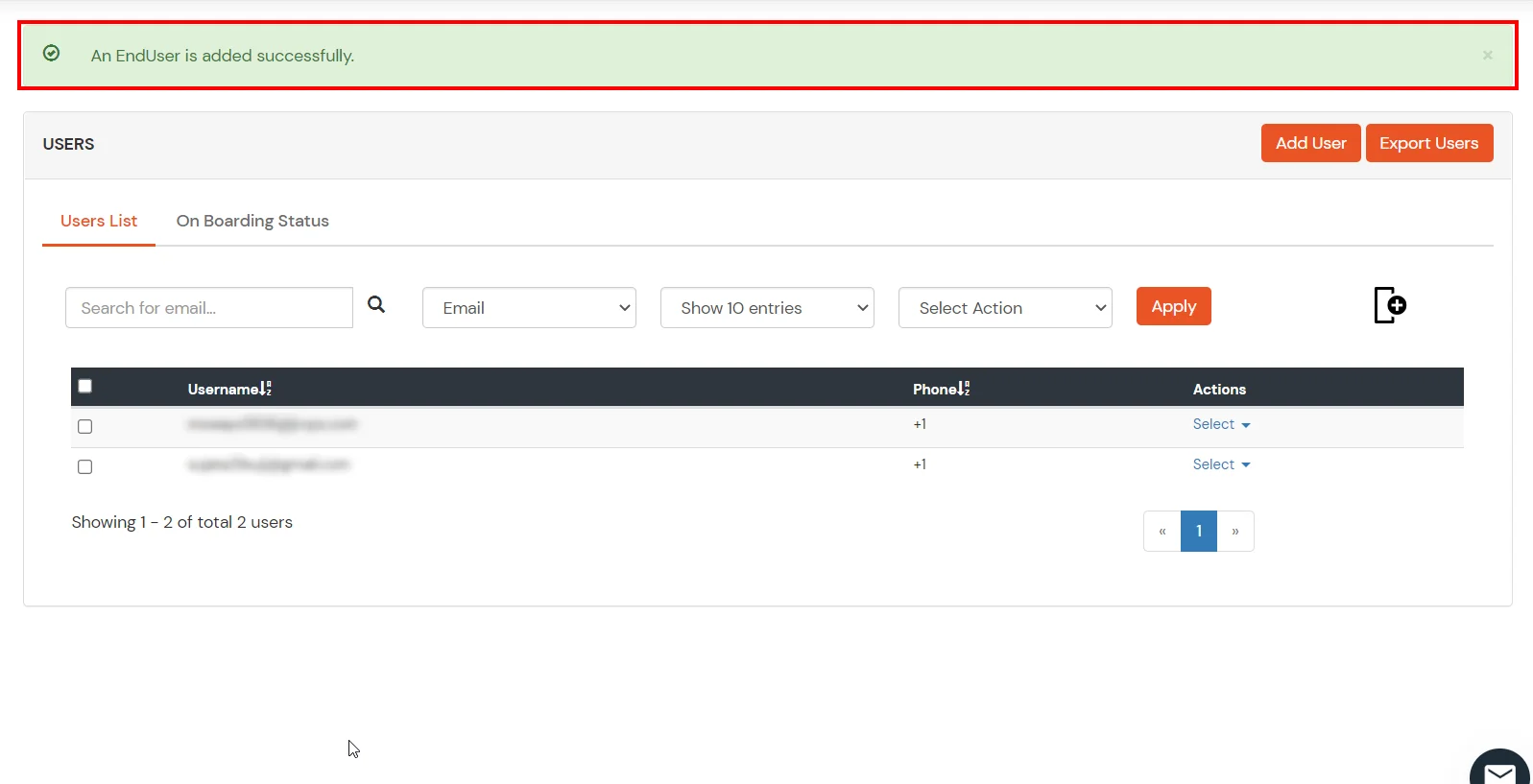
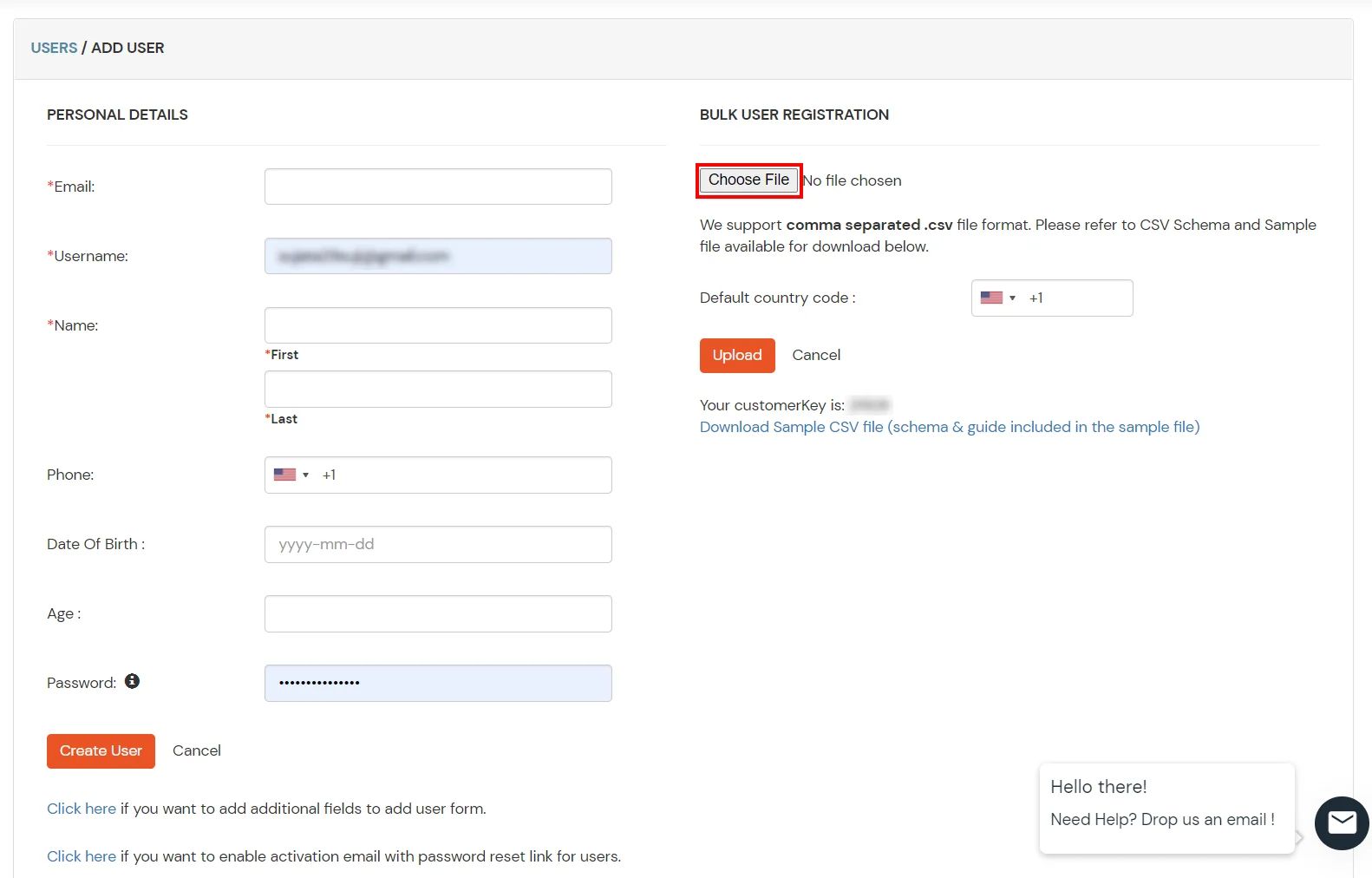
2. Bulk Upload Users in miniOrange via Uploading CSV File.

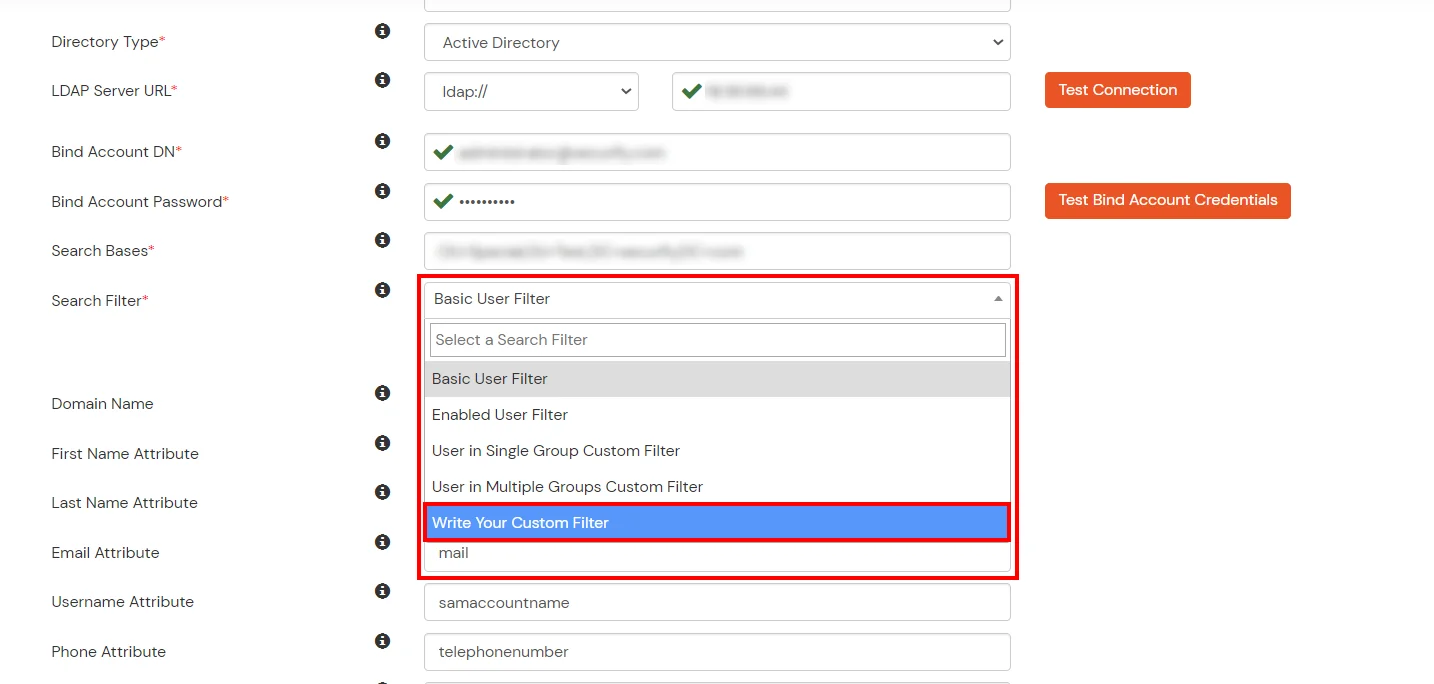
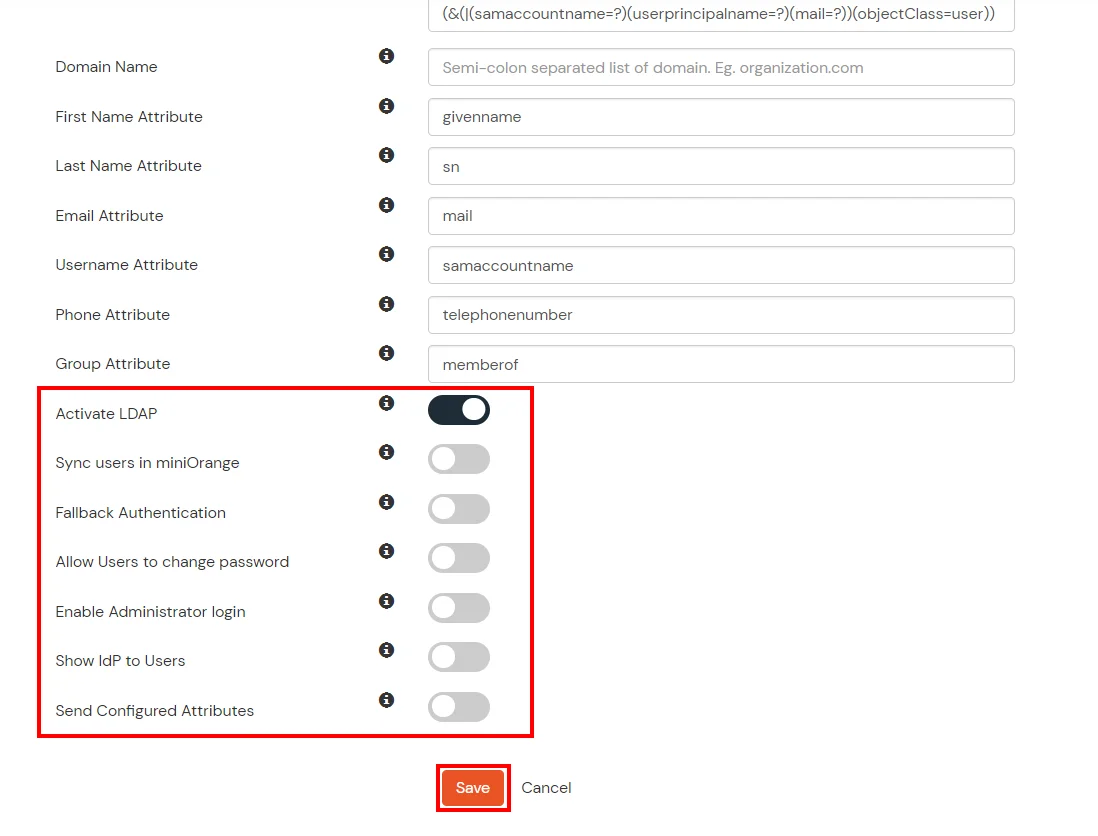
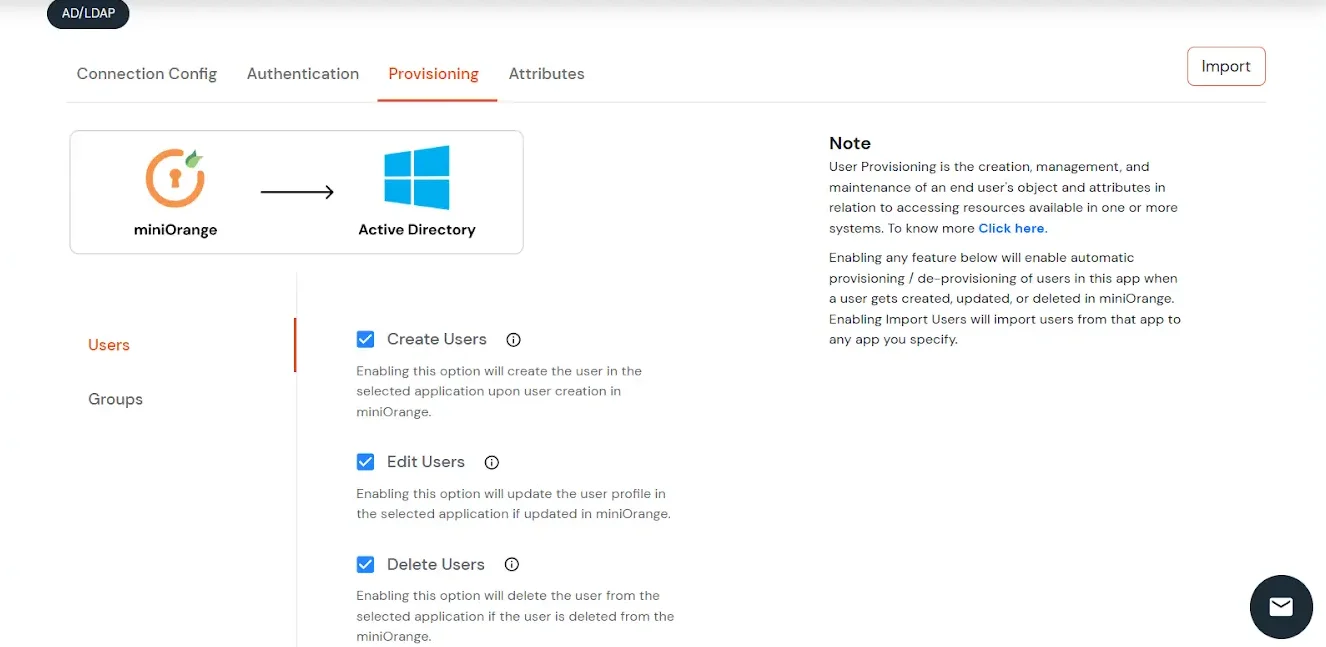
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute | Description |
|---|---|
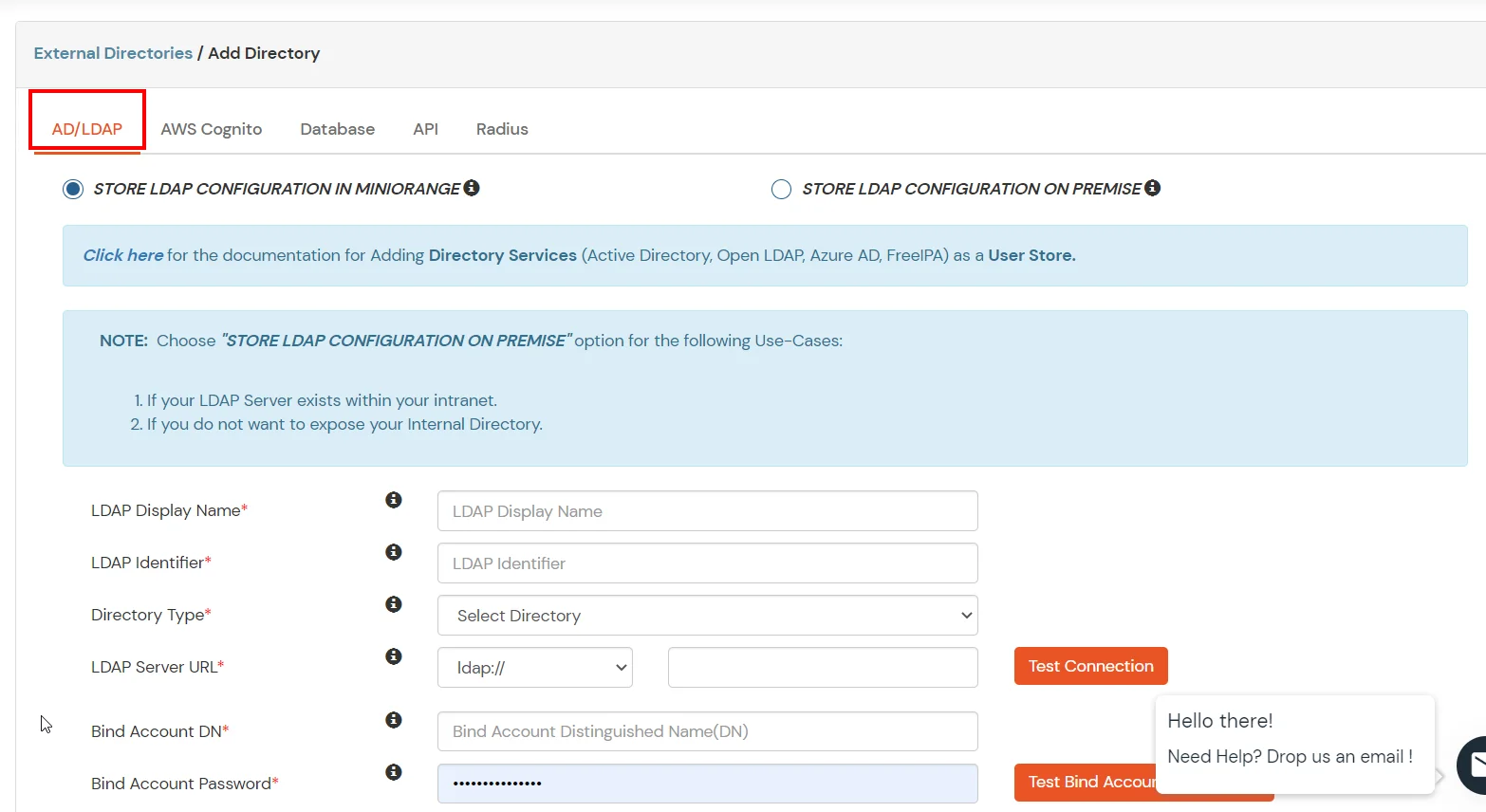
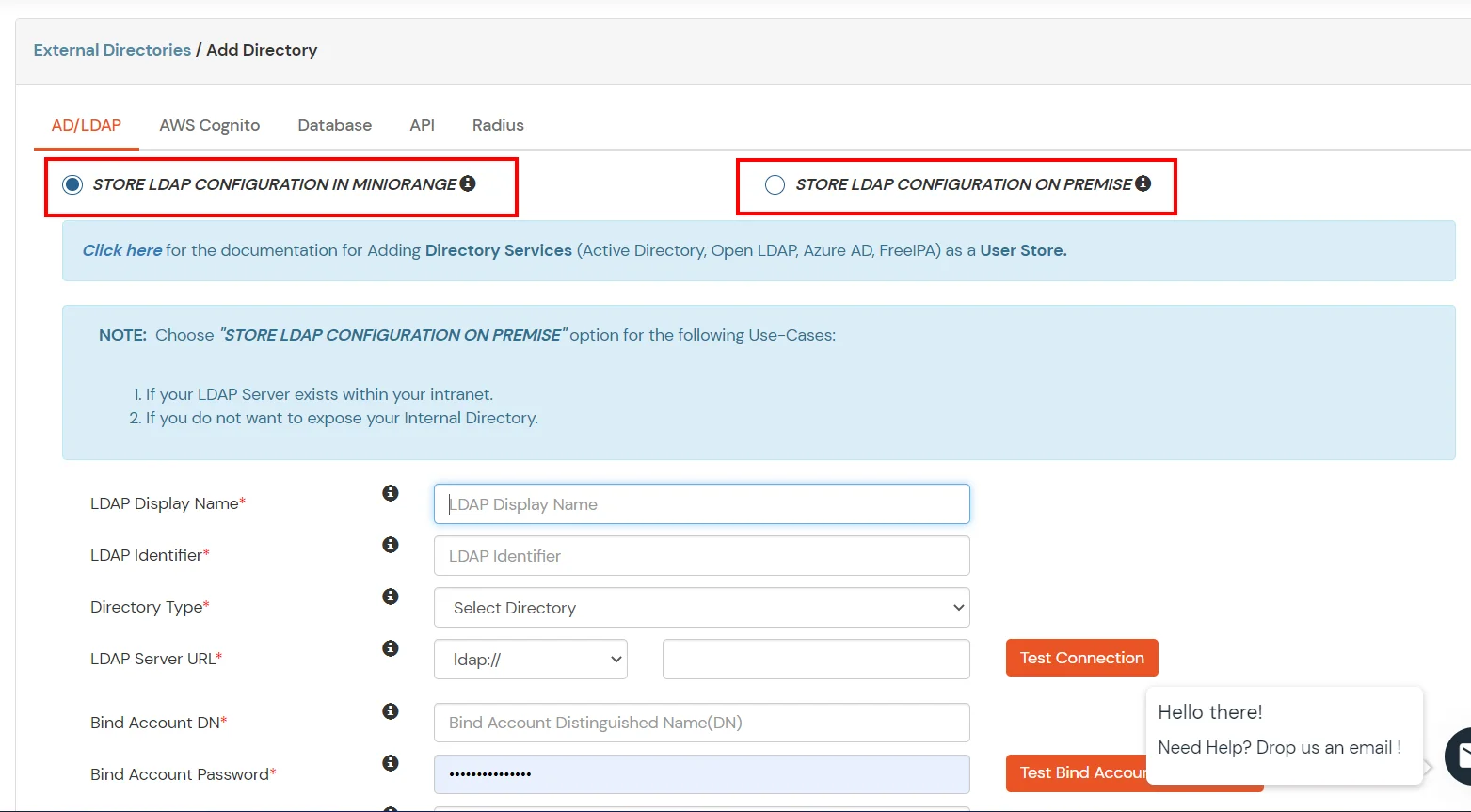
| Activate LDAP | All user authentications will be done with LDAP credentials if you Activate it |
| Fallback Authentication | If LDAP credentials fail then user will be authenticated through miniOrange |
| Enable administrator login | On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users | If you enable this option, this IdP will be visible to users |
| Sync users in miniOrange | Users will be created in miniOrange after authentication with LDAP |
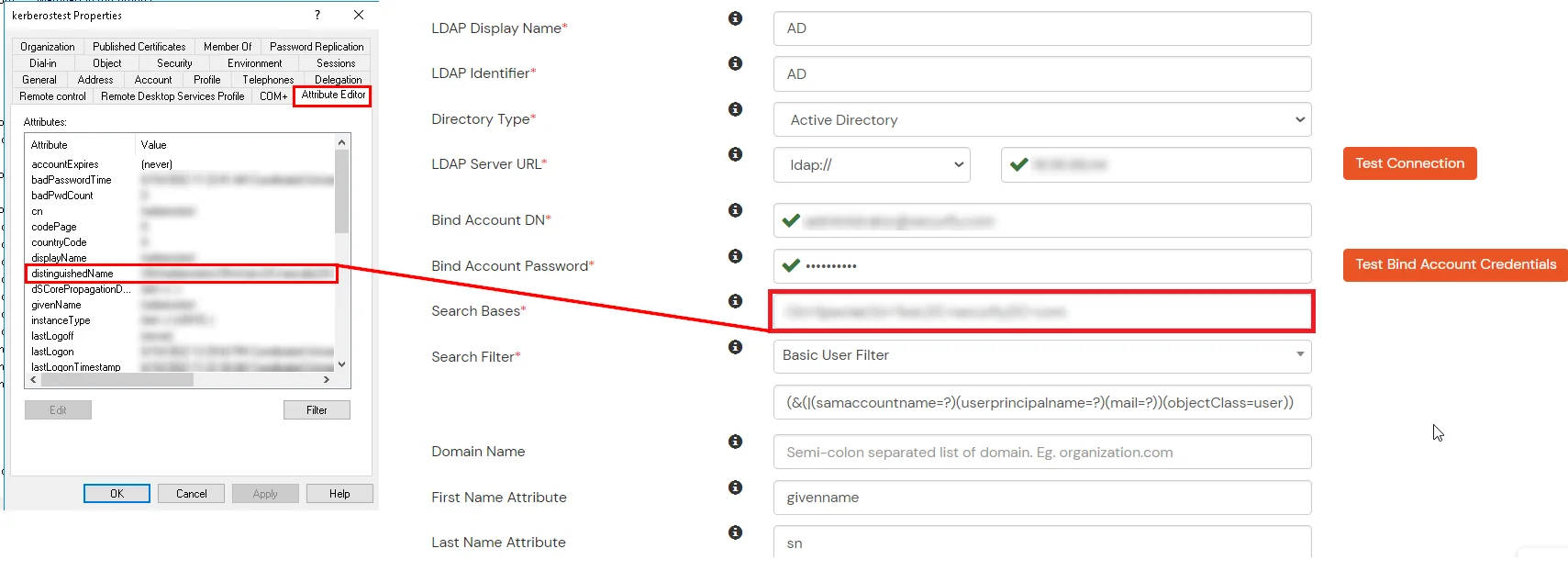
Attribute Name sent to SP = organization
Attribute Name from IDP = company
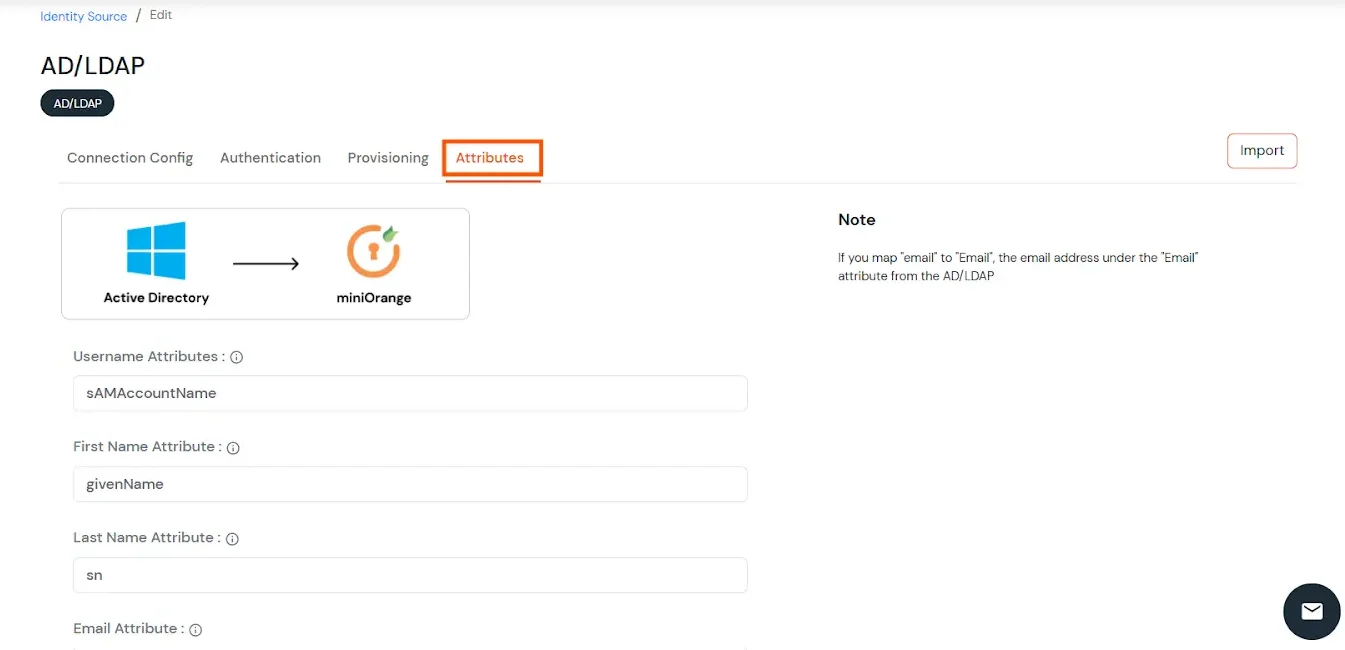
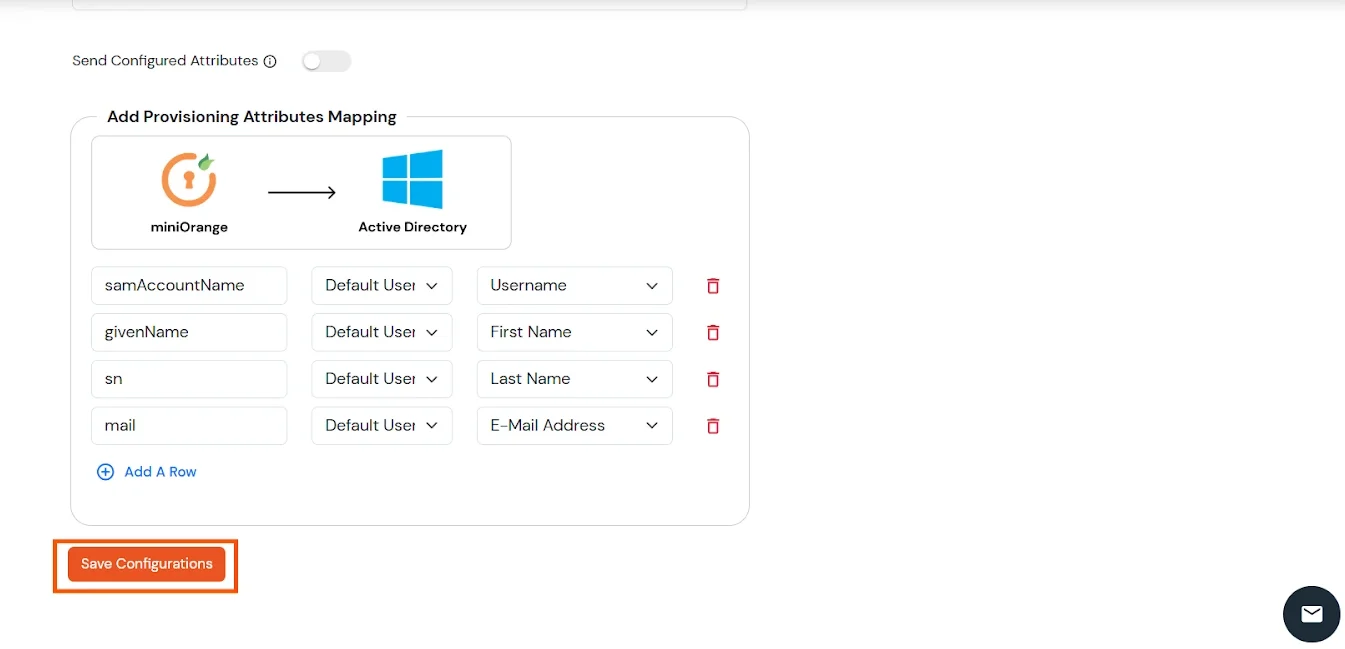
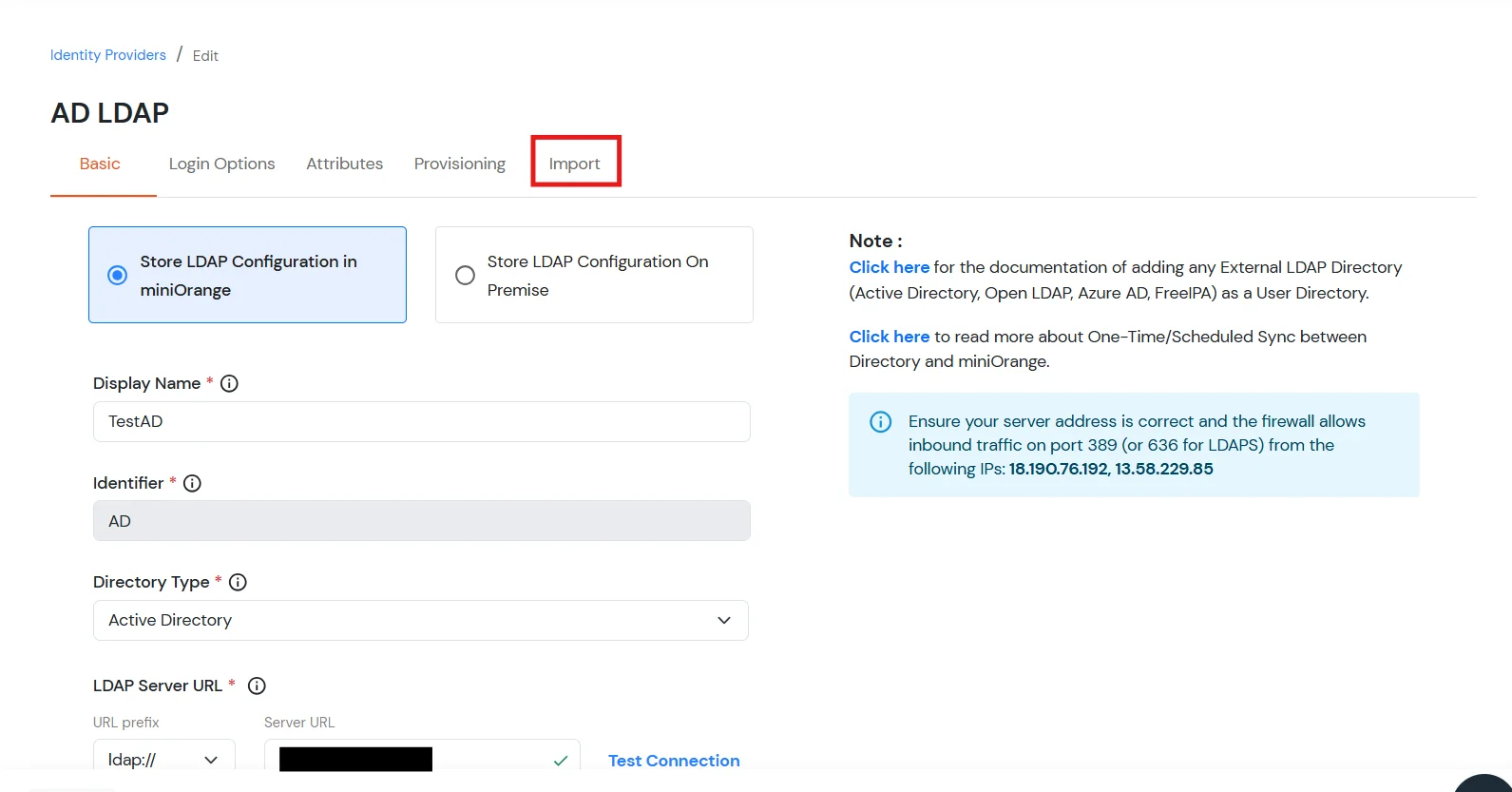
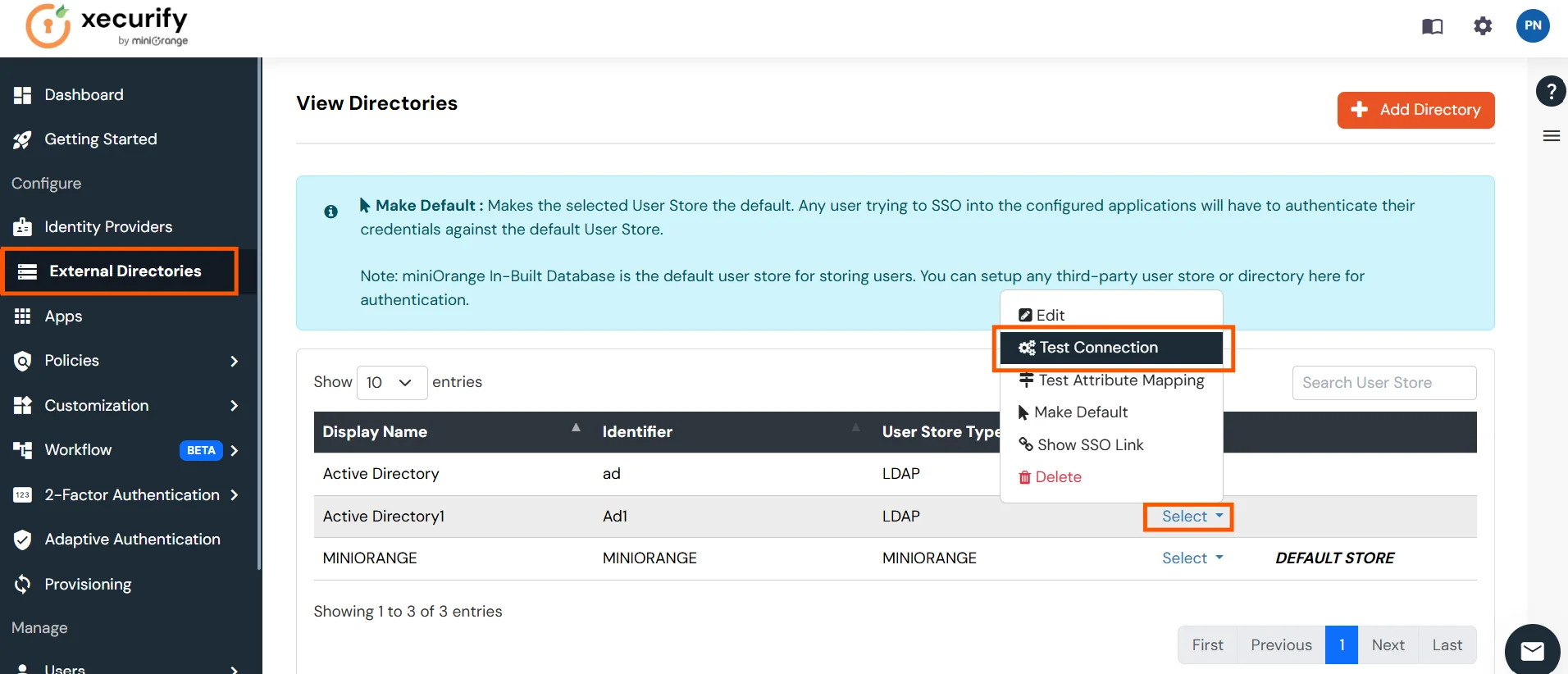
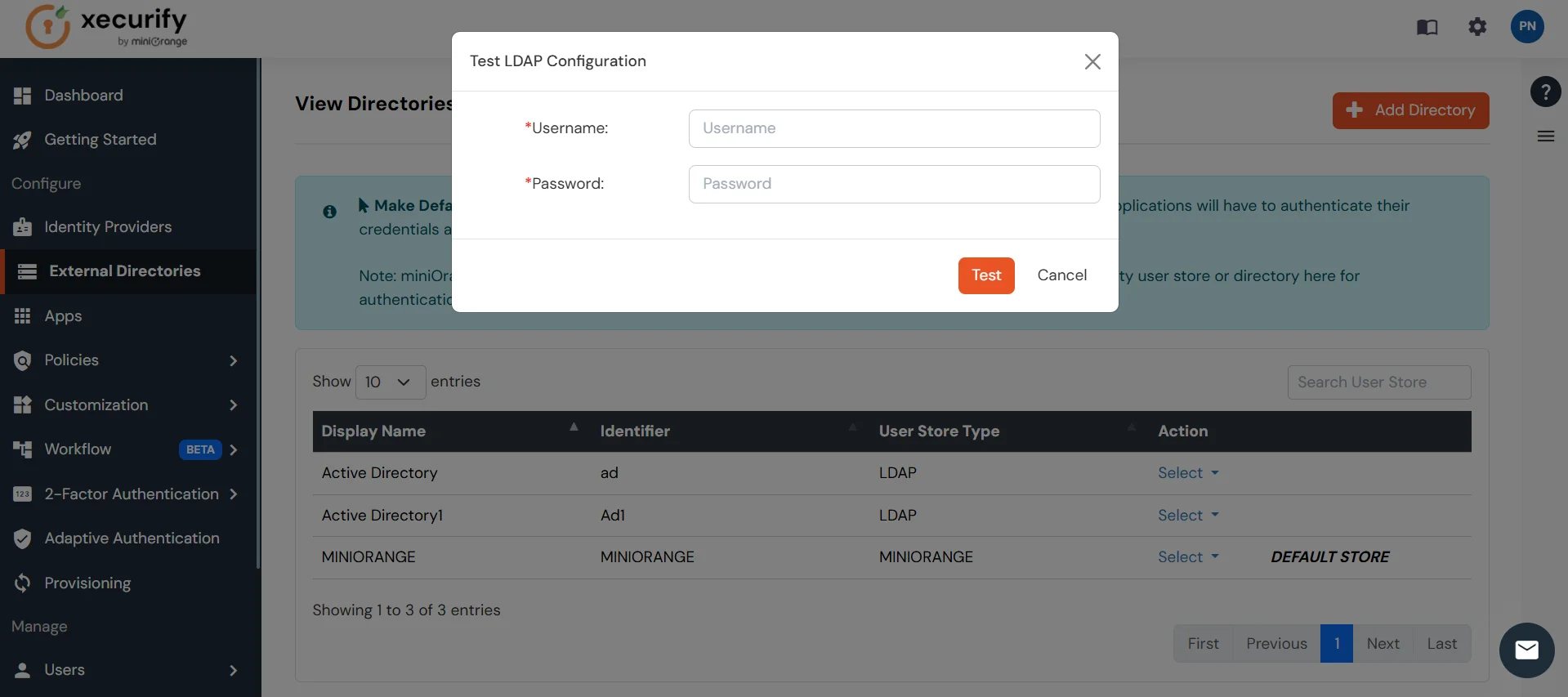
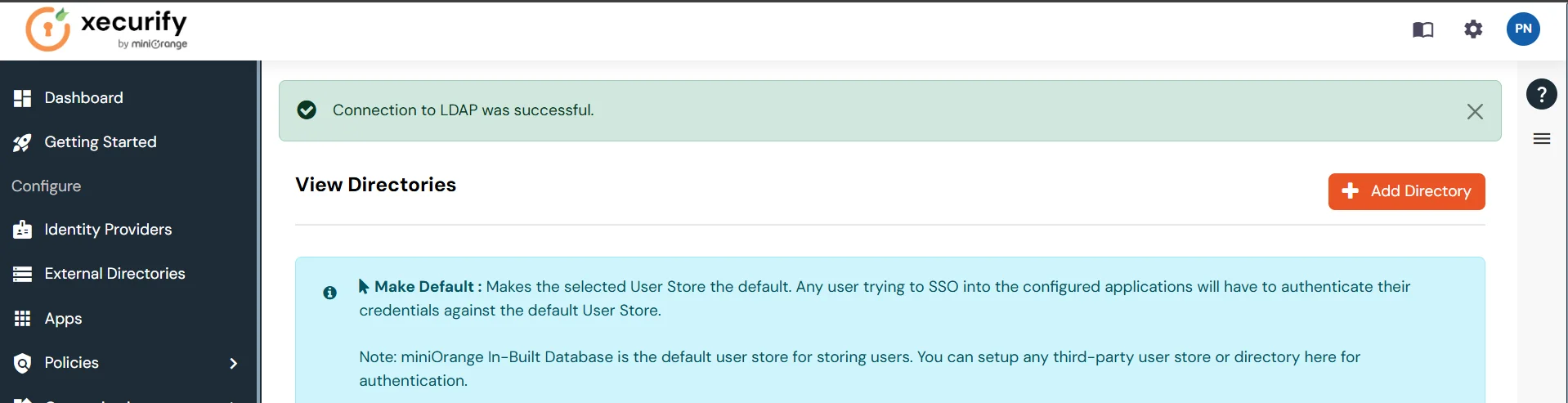
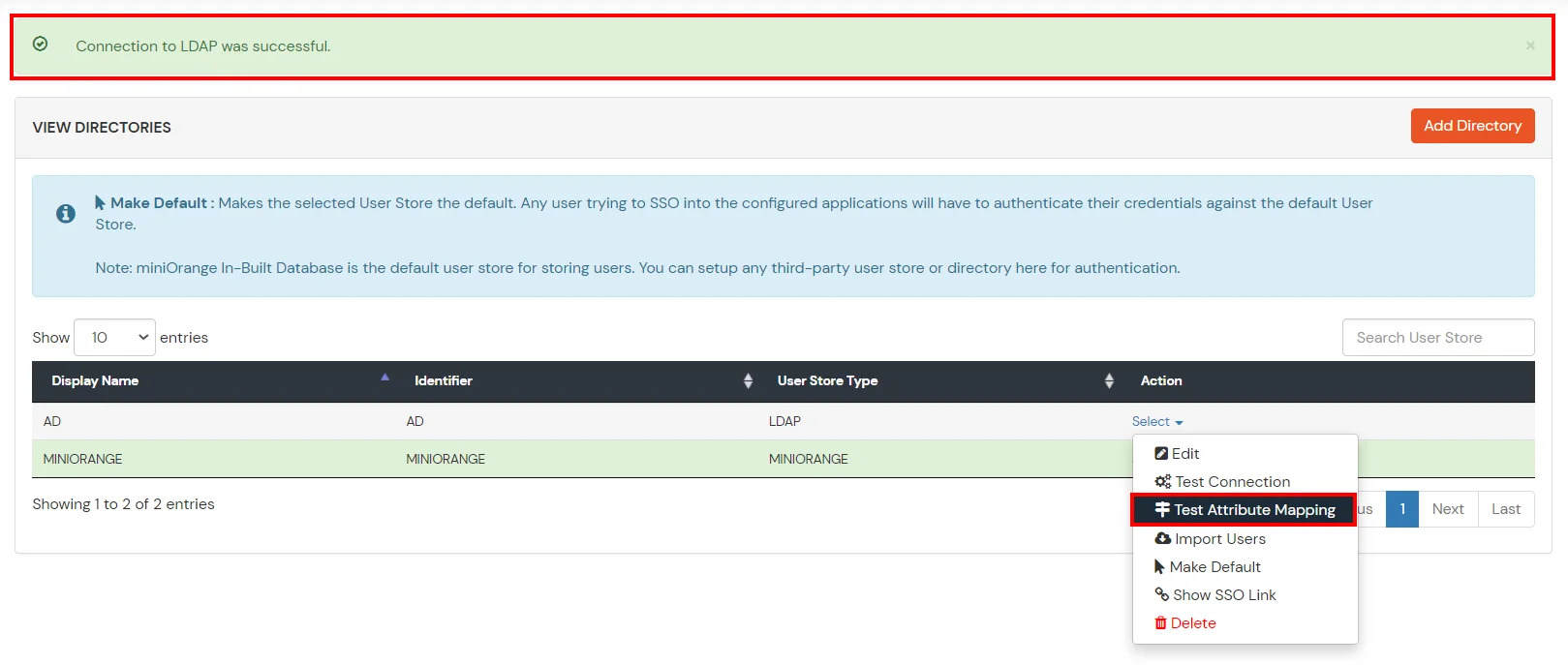
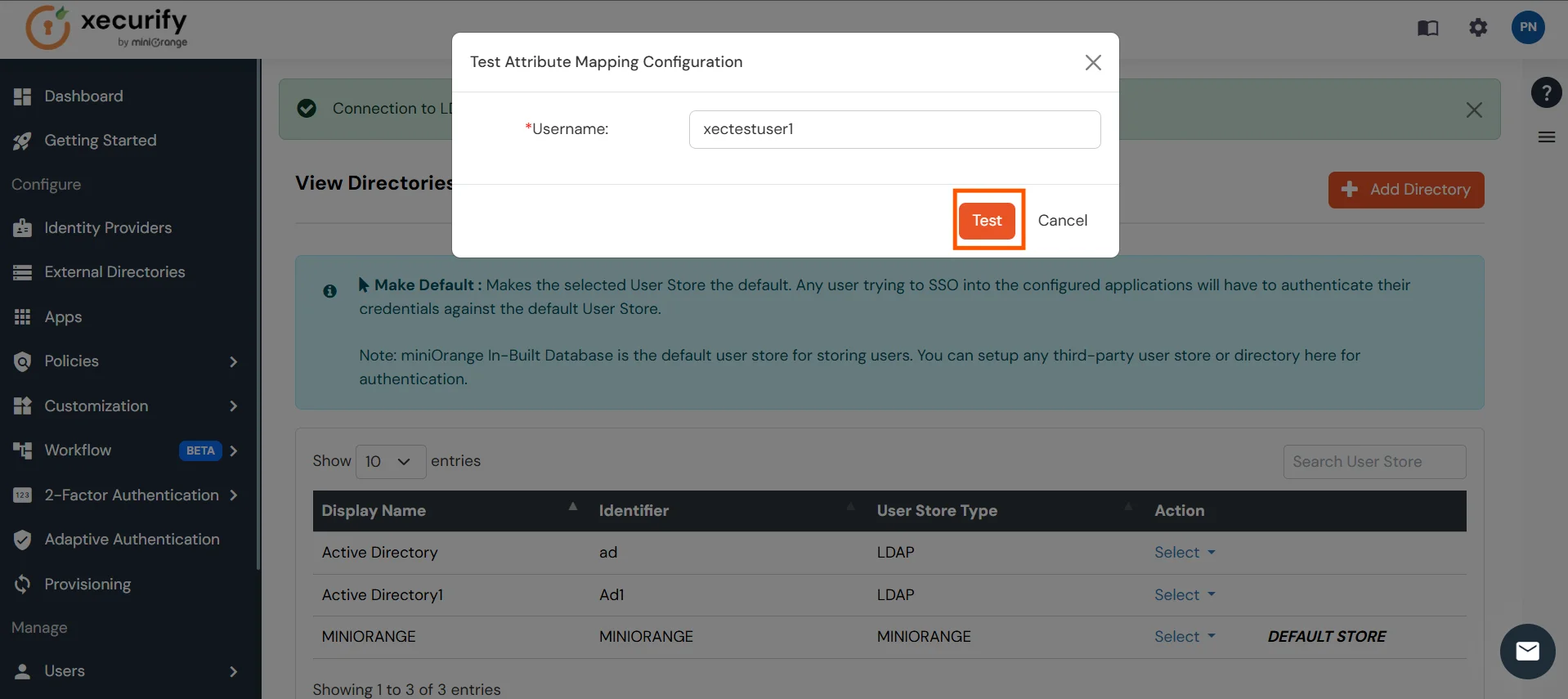
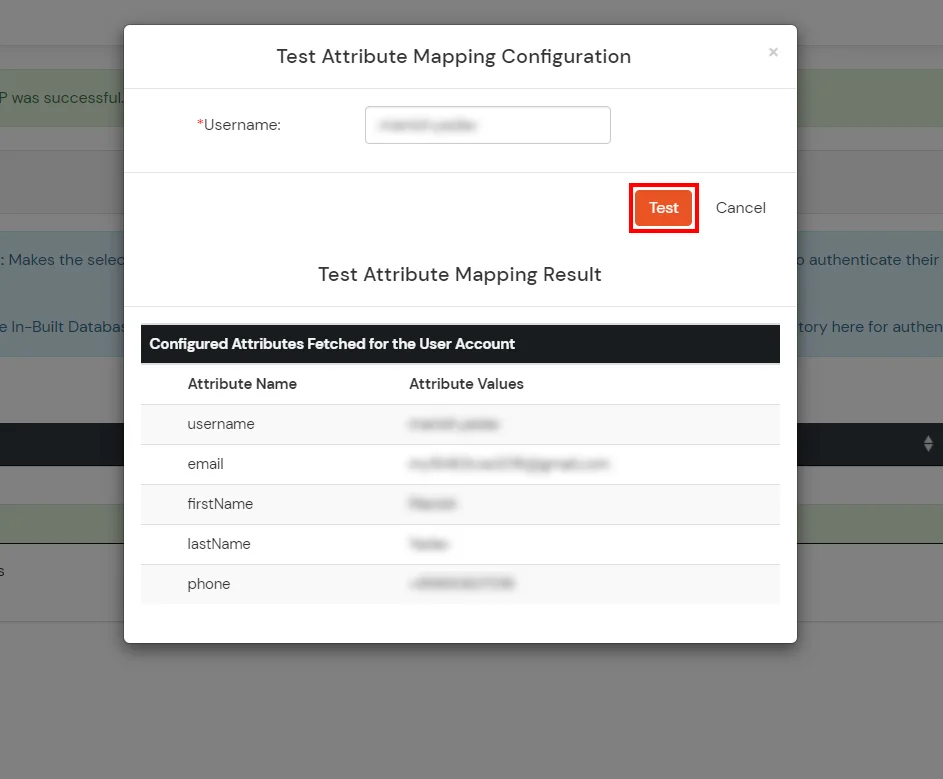
Set up AD as External Directory configuration is complete.
Note: Refer our guide to setup LDAP on windows server.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.
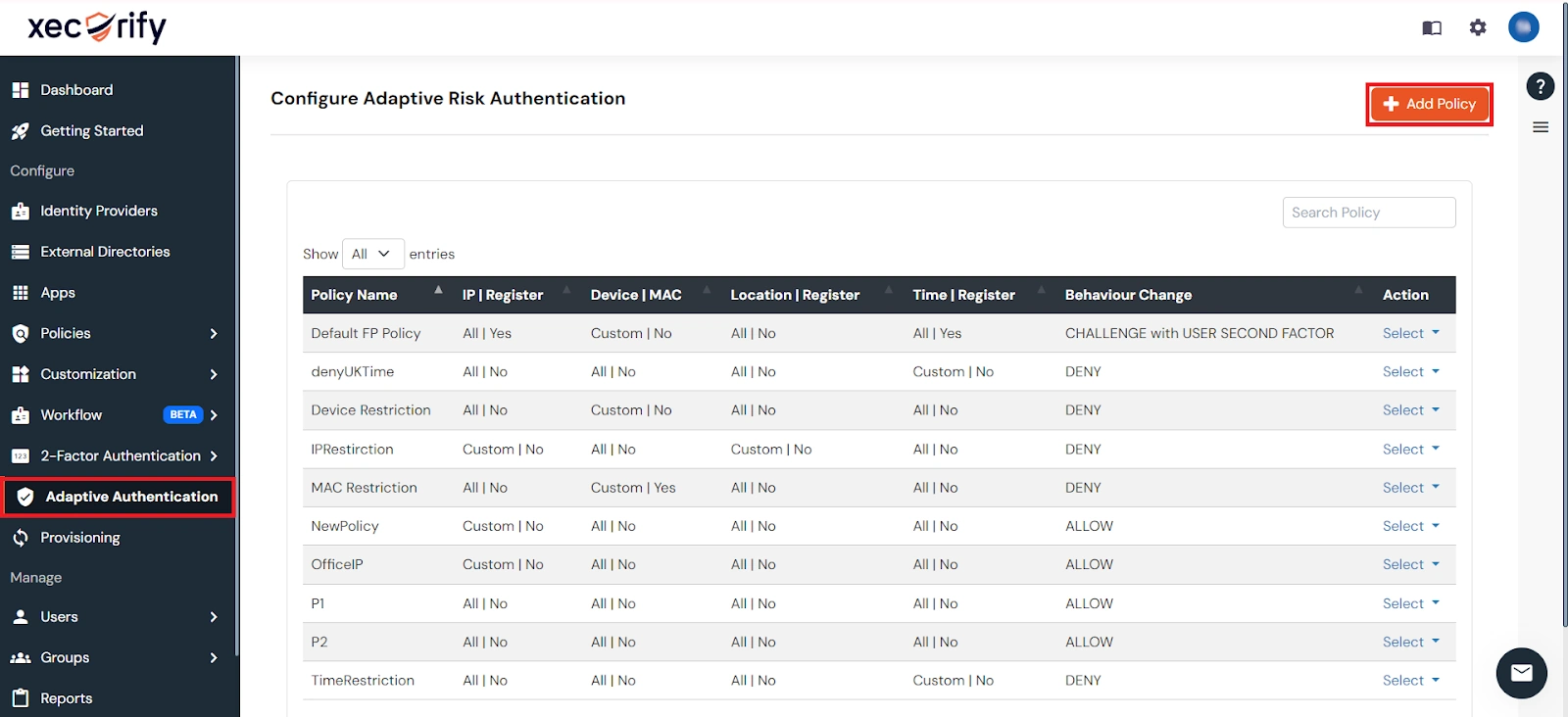
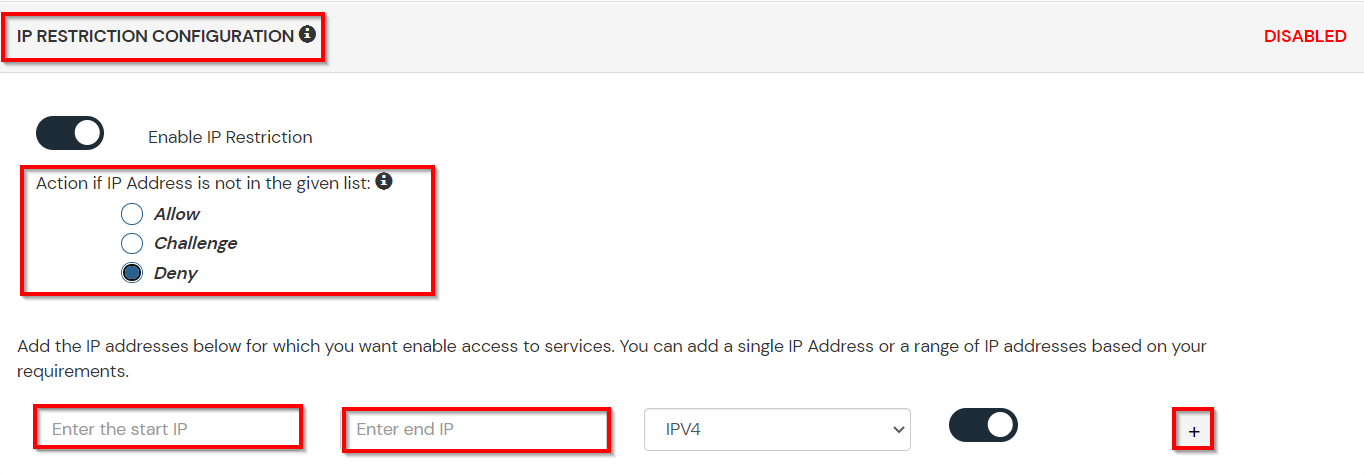
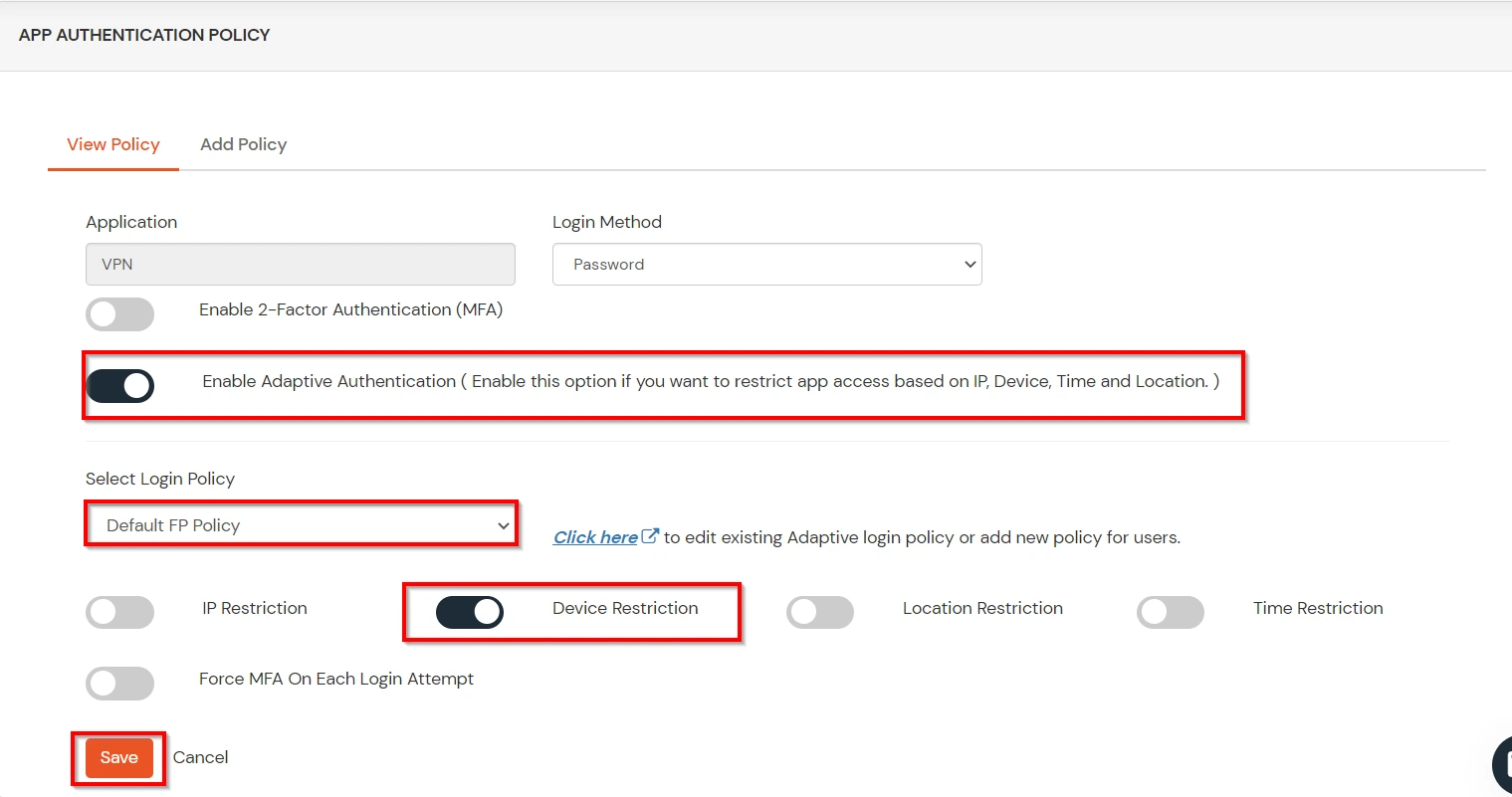
A. Restricting access to Wickr with IP Configuration
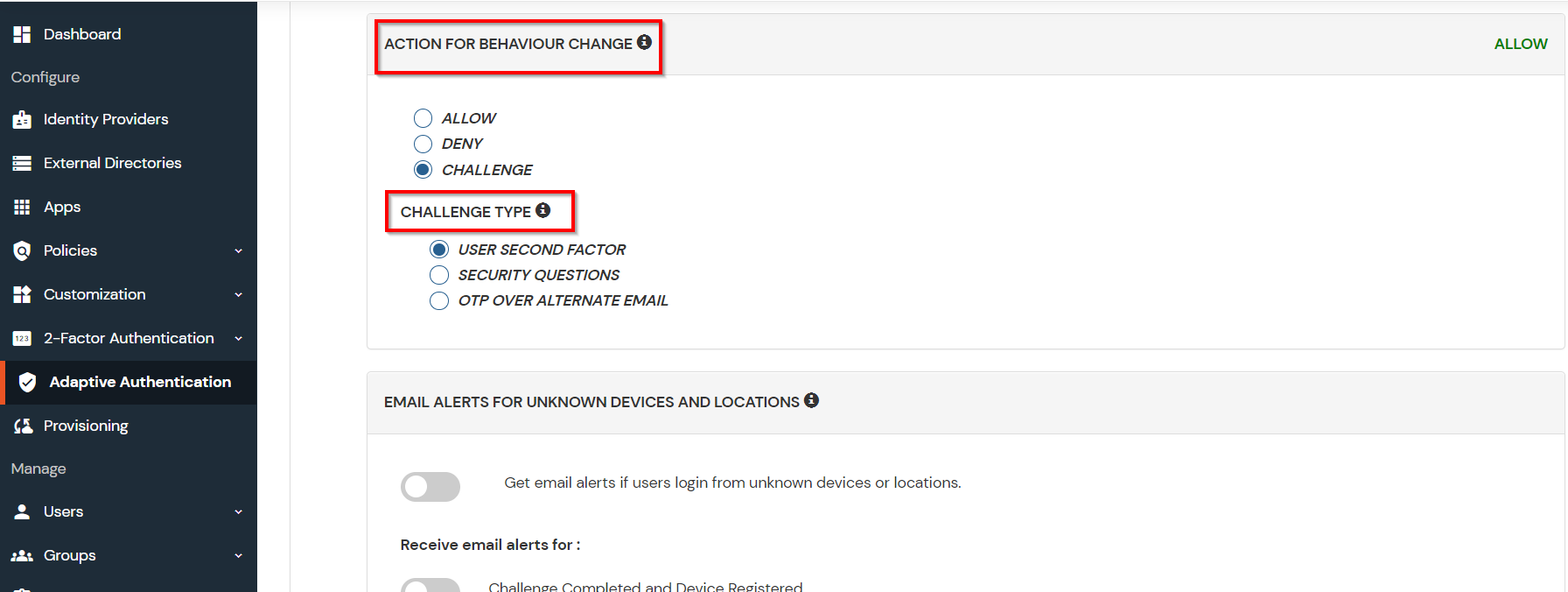
You can use adaptive authentication with Wickr Single Sign-On (SSO) to improve the security and functionality of Single Sign-On. You can allow a IP Address in certain range for SSO or you can deny it based your requirements and you can also challenge the user to verify his authenticity. Adaptive authentication manages the user authentication bases on different factors such as Device ID, Location, Time of Access, IP Address and many more.
You can configure Adaptive Authentication with IP Blocking in following way :
| Attribute | Description |
|---|---|
| Allow | Allow users to authenticate and use services if Adaptive authentication condition is true. |
| Deny | Deny user authentications and access to services if Adaptive authentication condition is true. |
| Challenge | Challenge users with one of the three methods mentioned below for verifying user authenticity. |
| Attribute | Description |
|---|---|
| User second Factor | The User needs to authenticate using the second factor he has opted or assigned for such as
|
| KBA (Knowledge-based authentication) | The System will ask the user for 2 of 3 questions he has configured in his Self-Service Console. Only after the right answer to both questions is the user allowed to proceed further. |
| OTP over Alternate Email | User will receive an OTP on the alternate email they have configured through the Self Service Console. Once the user provides the correct OTP, they are allowed to proceed further. |
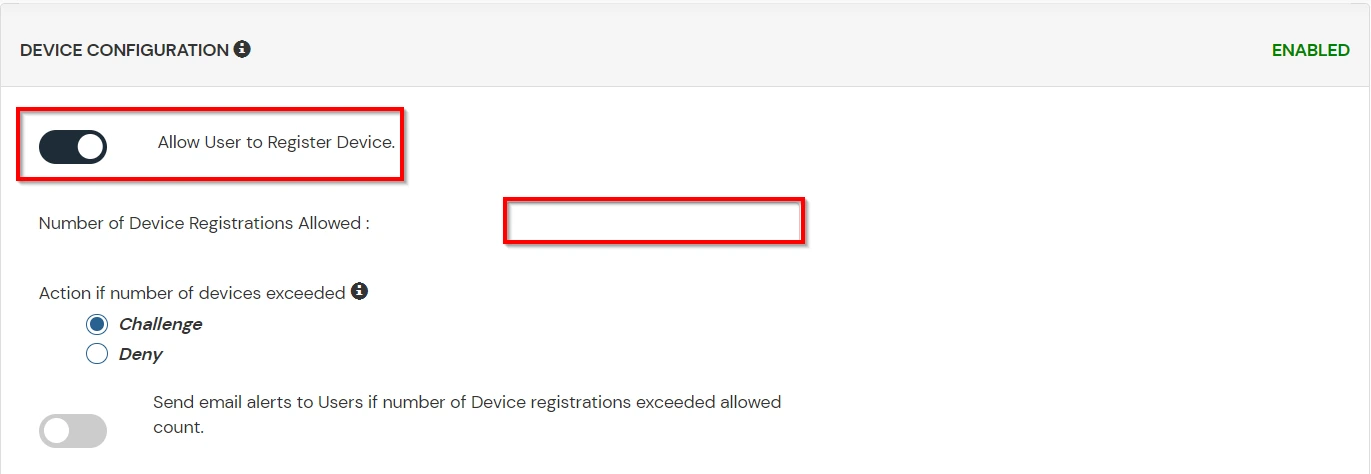
B. Adaptive Authentication with Limiting number of devices
Using Adaptive Authentication you can also restrict the number of devices the end user can access the Services on. You can allow end users to access services on a fixed no. of devices. The end users will be able to access services provided by us on this fixed no. of devices.
You can configure Adaptive Authentication with Device Restriction in following way
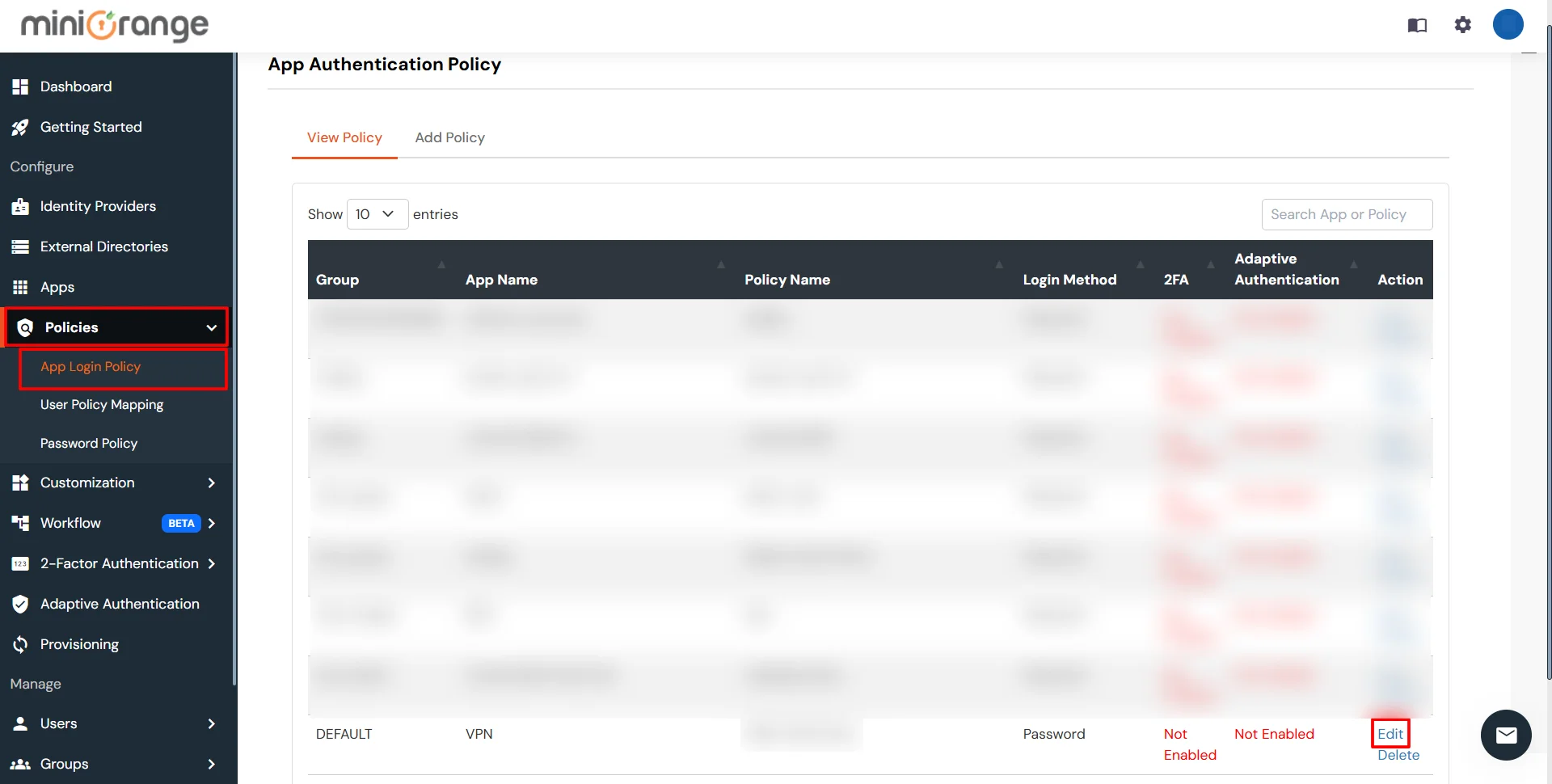
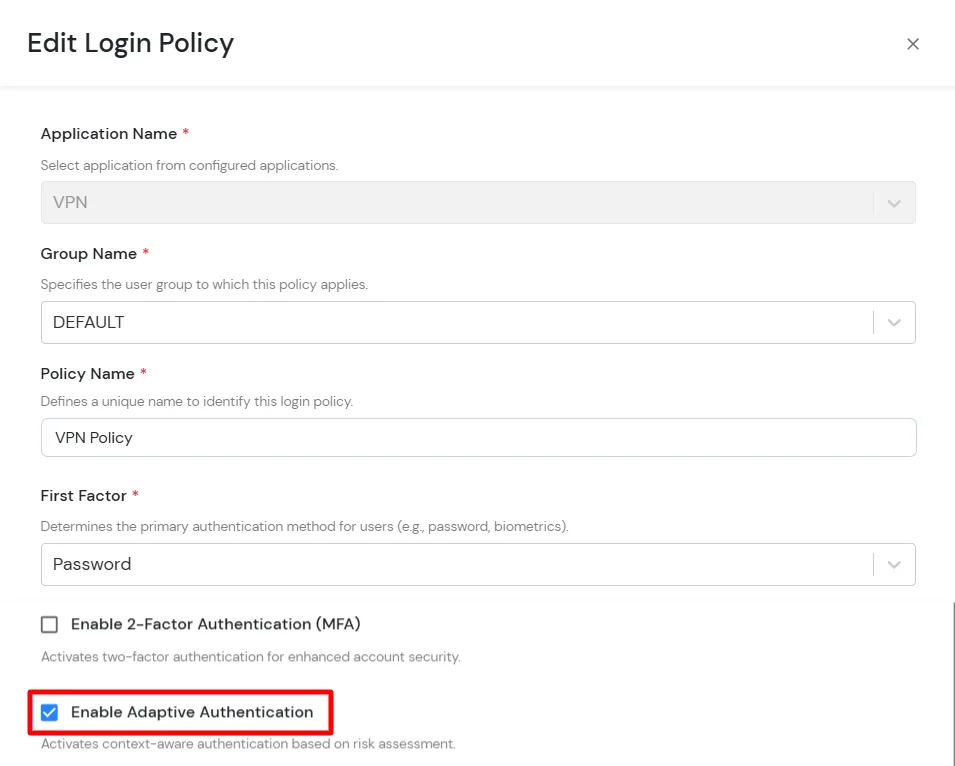
C. Add Adaptive Authentication policy to Wickr
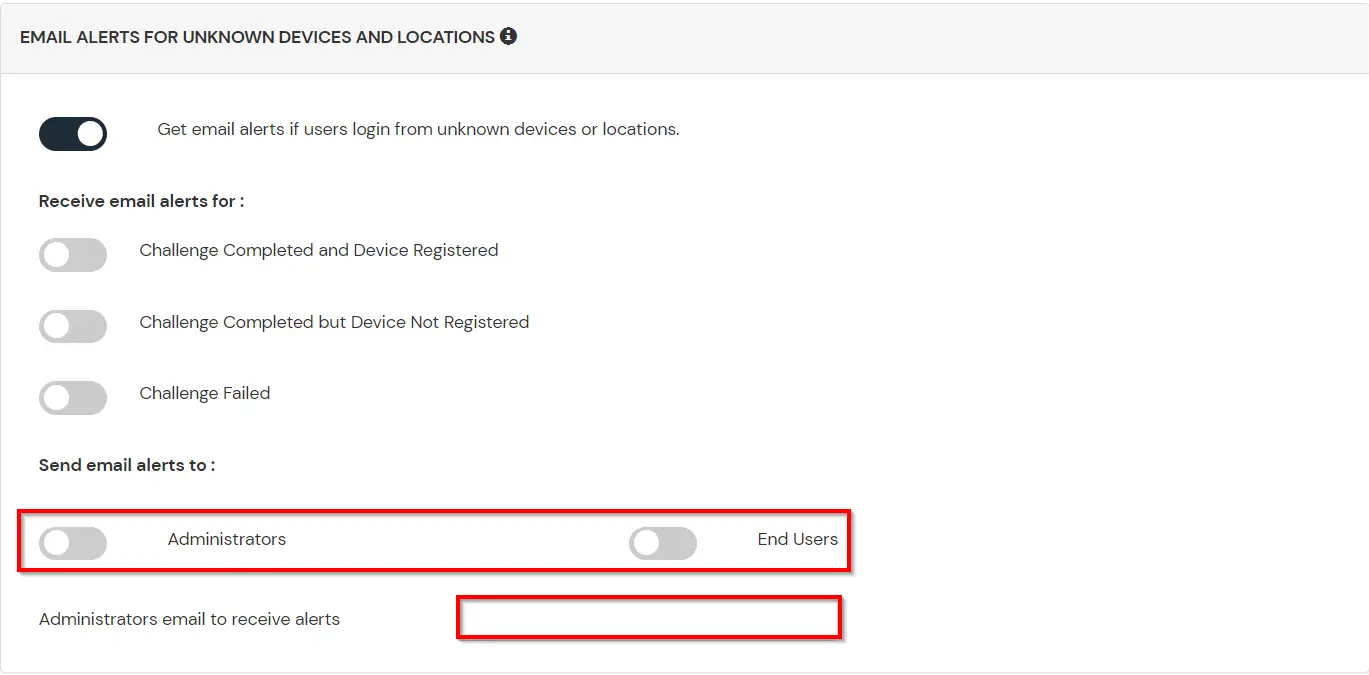
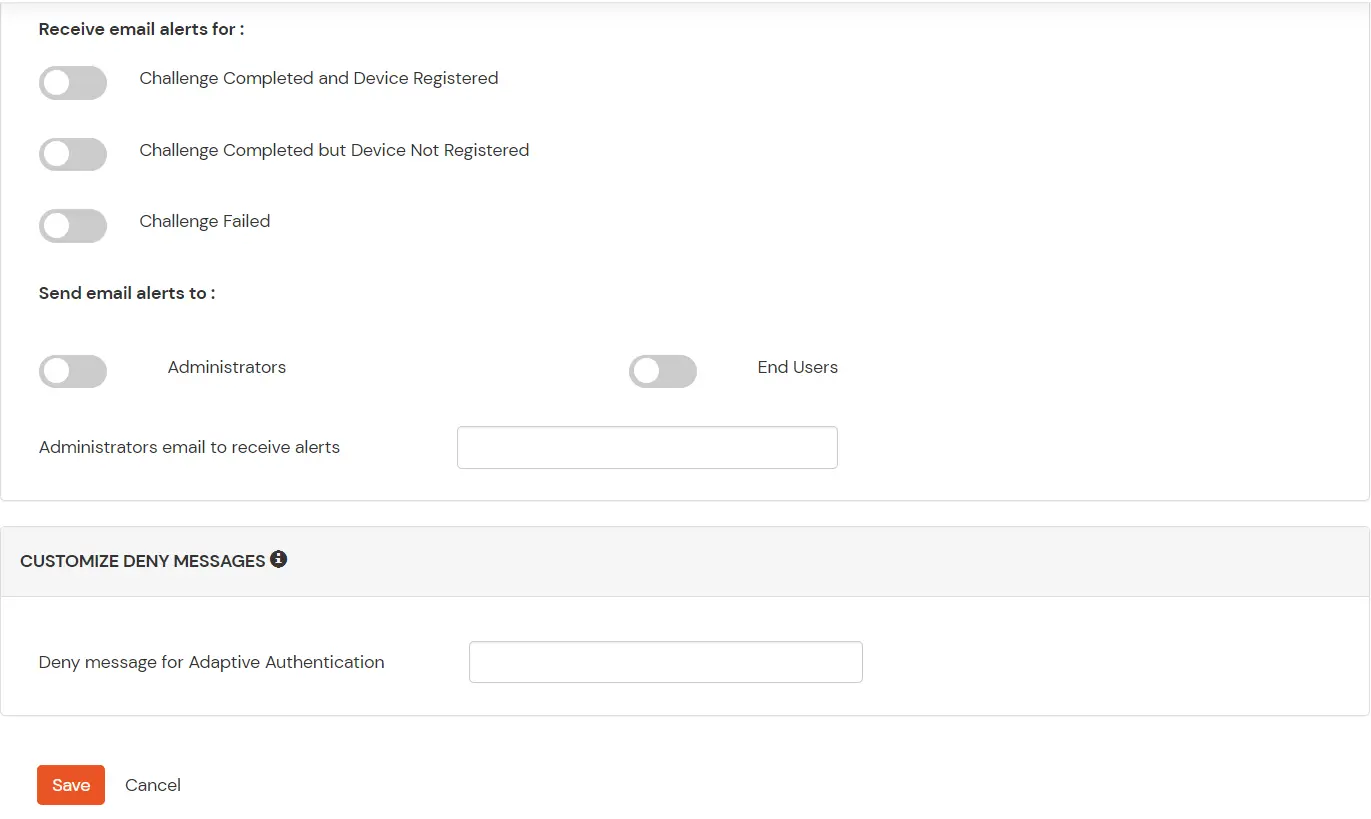
D. Notification and Alert Message.
This section handles the notifications and alerts related to Adaptive Authentication. It provides the following options :
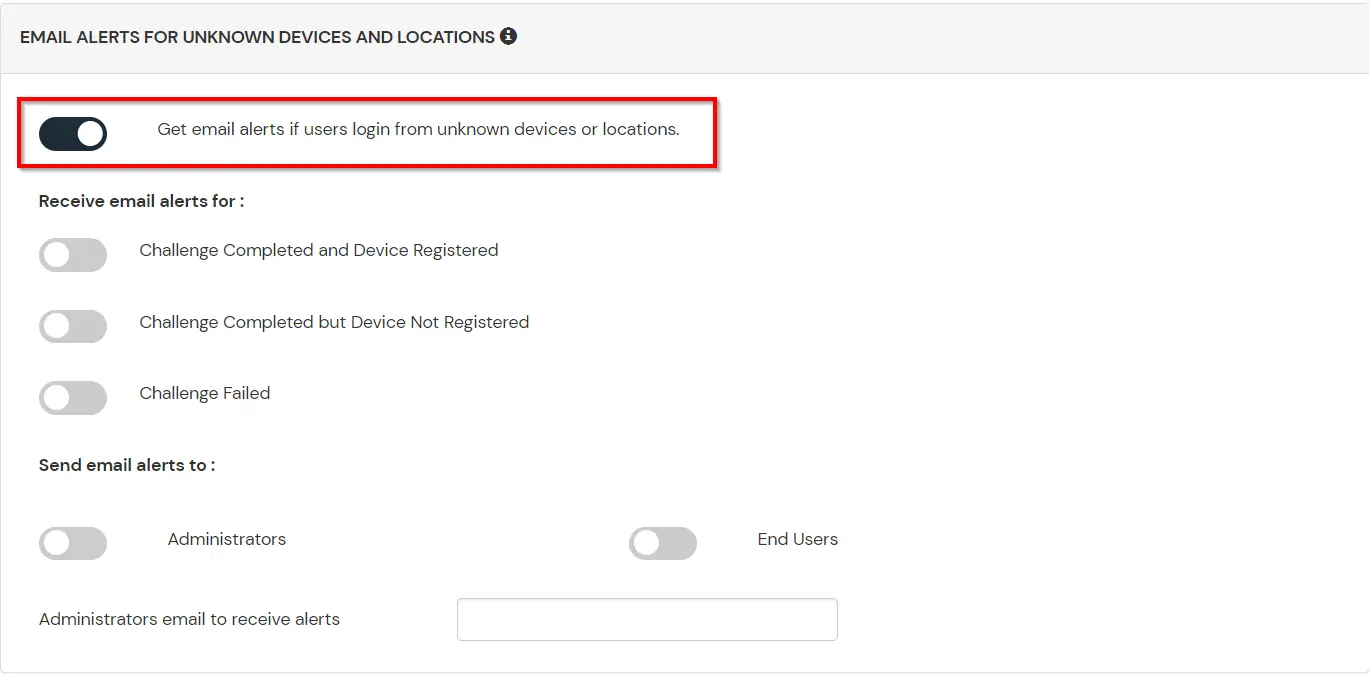
| Option | Description |
|---|---|
| Users login from unknown IP addresses, devices or locations | Enabling this option allows you to login from unknown IP addresses or devices and even locations. |
| Number of Device registrations exceeded allowed count | This option will allow you to register more devices than the devices you have numbered. |
| Challenge Completed and Device Registered | Enabling this option allows you to send an email alert when an end-user completes a challenge and registers a device. |
| Challenge Completed but Device Not Registered | Enabling this option allows you to send an email alert when an end-user completes a challenge but do not registers the device. |
| Challenge Failed | Enabling this option allows you to send an email alert when an end-user fails to complete the challenge. |