Need Help? We are right here!
Search Results:
×






Data loss prevention software features designed to detect, control, and stop data leakage before sensitive information leaves your organization.

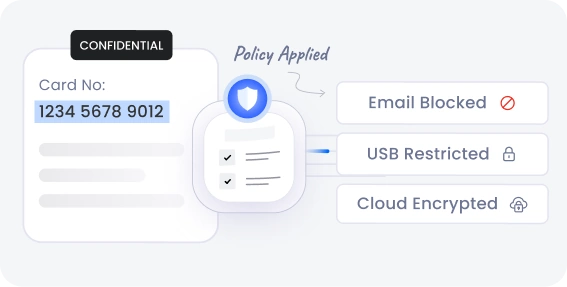
Apply precise data access rules based on file types, data sensitivity, user roles, locations, or behavior. Stop unauthorized sharing at every level, internal or external, using intelligent Data Leakage Prevention policies.

Get instant alerts for suspicious behavior. Monitor anomalies, track file flows, and take action before minor issues turn into major breaches.

Scan emails, attachments, and outbound domains in Gmail, Outlook, and Office 365. Automatically block or quarantine content that violates your data leakage prevention policies

Prevent confidential data from being uploaded to non-compliant websites or apps. Maintain control even when employees are working beyond your perimeter with continuous Data Leakage Prevention enforcement.
Scan data in motion across uploads, downloads, and transfers using deep content inspection. Monitor context and automatically block file transfers that violate data protection policies.

Manage USB drives, external storage, and peripheral ports with detailed device-level restrictions. Allow or block devices based on vendor ID, product ID, serial number, and approved policies.
Gain deeper visibility and control over sensitive data with intelligent capabilities designed to identify, classify, and protect data across your organization.
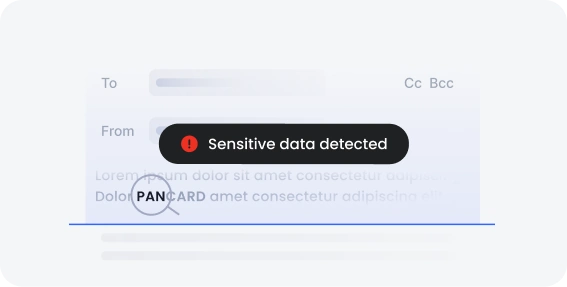
Automatically locate sensitive data across endpoints, cloud apps, storage, and databases. miniOrange identifies and classifies data like PII, PCI, financial records, and customer information to keep it protected.
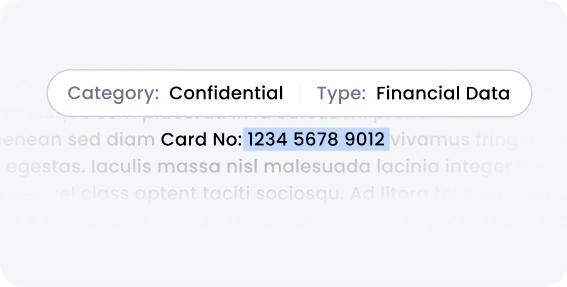
Organize sensitive data based on importance and compliance needs. miniOrange helps identify high-risk data and apply the right protection policies to reduce exposure.
Apply consistent labels to sensitive data for better visibility and control. miniOrange enables policy enforcement, restricts unauthorized sharing, and supports compliance handling.
Keep your business data under your control with Data Loss Prevention solution and Data Leakage Prevention solution.

Secure Endpoints & Block Unauthorized Devices
Secure Emails & Prevent Data Leaks


Protect Cloud Apps & Data
Secure sensitive data across Windows, macOS, Android, and iOS with miniOrange DLP software designed to monitor, control, and prevent data leaks across all operating systems.
Deploy miniOrange DLP software with flexible deployment models that align with your organization's security,
compliance, and infrastructure requirements.

Protect sensitive data across cloud platforms with a scalable deployment. miniOrange secures cloud apps and supports remote work without the need for on-site infrastructure.

Deploy DLP within your internal systems for greater control and data security. miniOrange helps monitor and protect sensitive data while meeting strict compliance needs.

Combine cloud flexibility with on-premise control for complete data protection. miniOrange ensures visibility and consistent policies across all systems with a unified approach.
Protect sensitive business data across critical sectors with the best DLP software
designed to prevent data leaks, ensure compliance, and secure confidential information.
Banks and fintech companies handle sensitive customer and transaction data daily. DLP software prevents unauthorized sharing of financial records and supports compliance with regulations like PCI DSS.

Healthcare organizations manage protected health information (PHI) across systems and devices. DLP software helps prevent unauthorized sharing of patient records while supporting HIPAA compliance.

Technology companies store intellectual property, source code, and confidential customer data. DLP software monitors file transfers, prevents code leaks, and secures collaboration across distributed teams.

Government agencies handle classified information and sensitive citizen data. DLP software prevents unauthorized transfers, internal or external leaks, and strengthens data governance and regulatory compliance.
Answers to the most frequently asked questions about Data Loss Prevention (DLP) solutions.
