Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
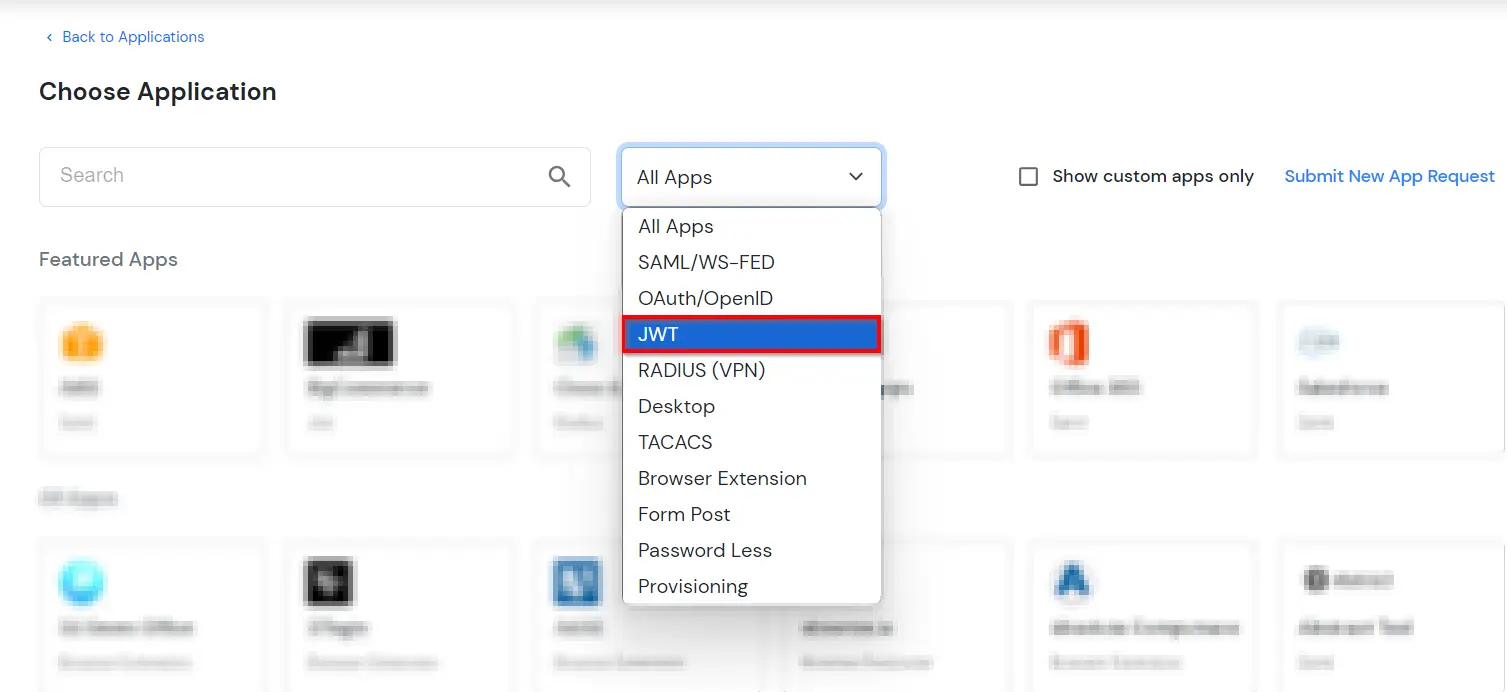
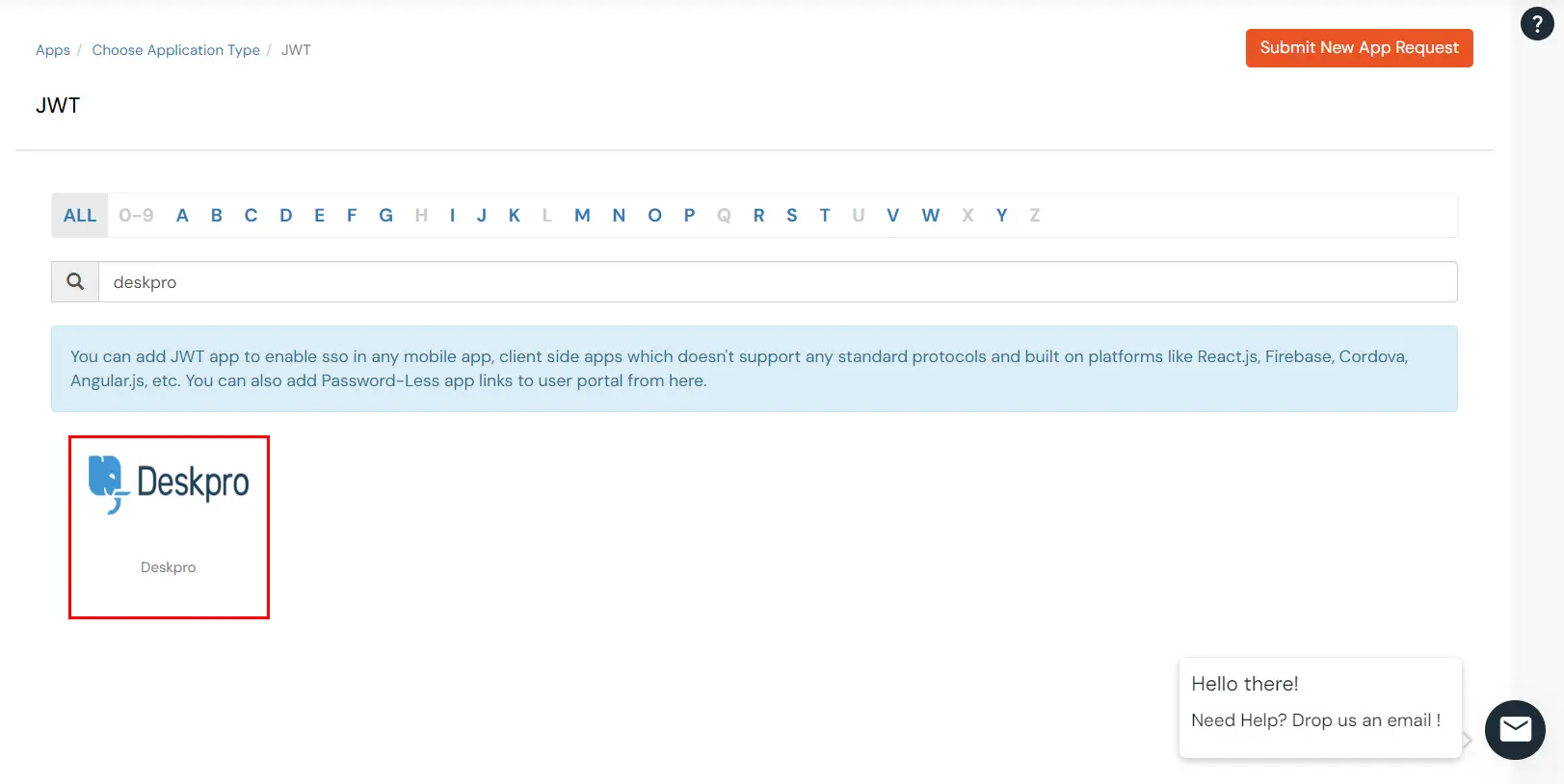
×Deskpro with its adaptable and dynamic helpdesk software can provide you the unforgettable customer experiences to your customers or internal users. miniOrange allows you to setup Single Sign-On(SSO) into using two standard protocols like SAML 2.0 and JSON web Tokens (JWT). Deskpro SSO with JWT is achieved by protocol brokering between JWT and SAML. Deskpro has support for SSO using JSON Web Token (JWT) tokens. miniOrange allows your users to Single Sign-On into Deskpro by verifying Identity with your existing SAML 2.0 compliant Identity Provider and passing JWT tokens to Deskpro.
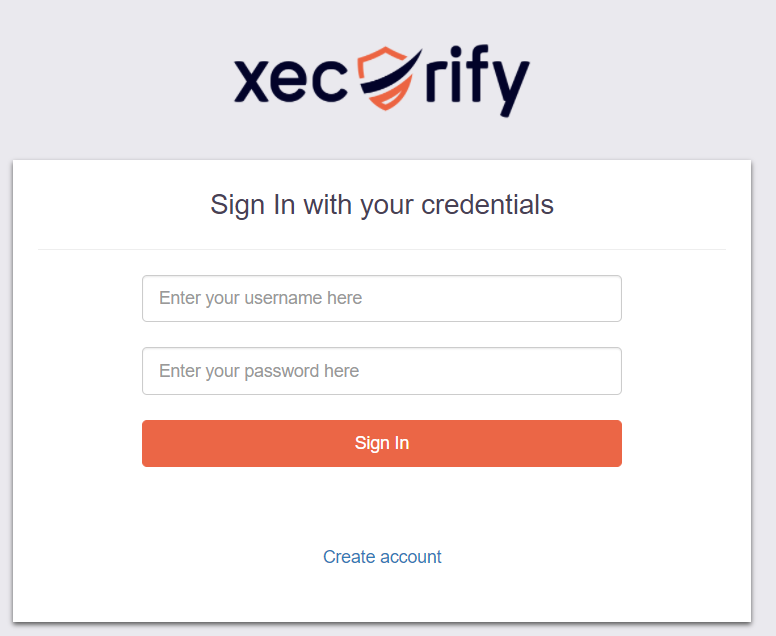
Please make sure your organisation branding is already set under Customization >> Login and Registration Branding in the left menu of the dashboard.
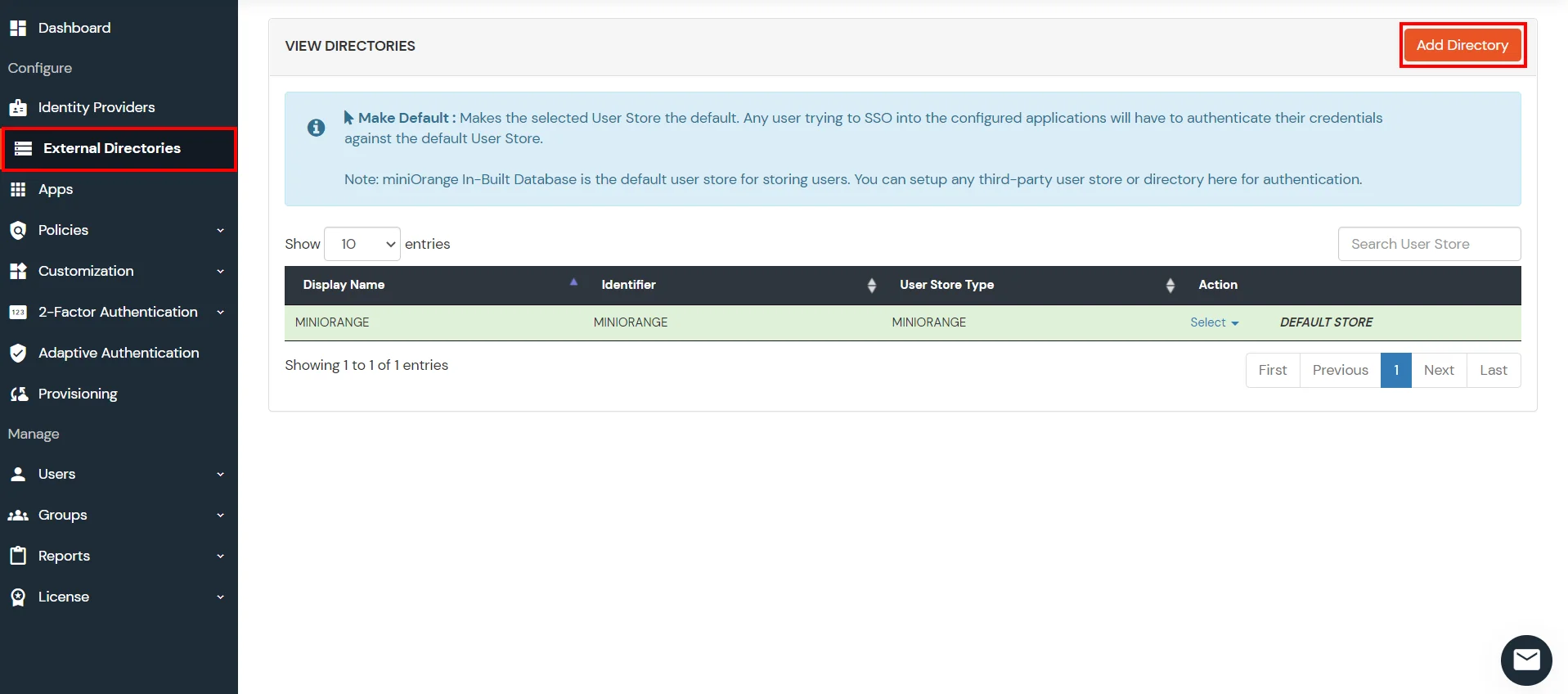
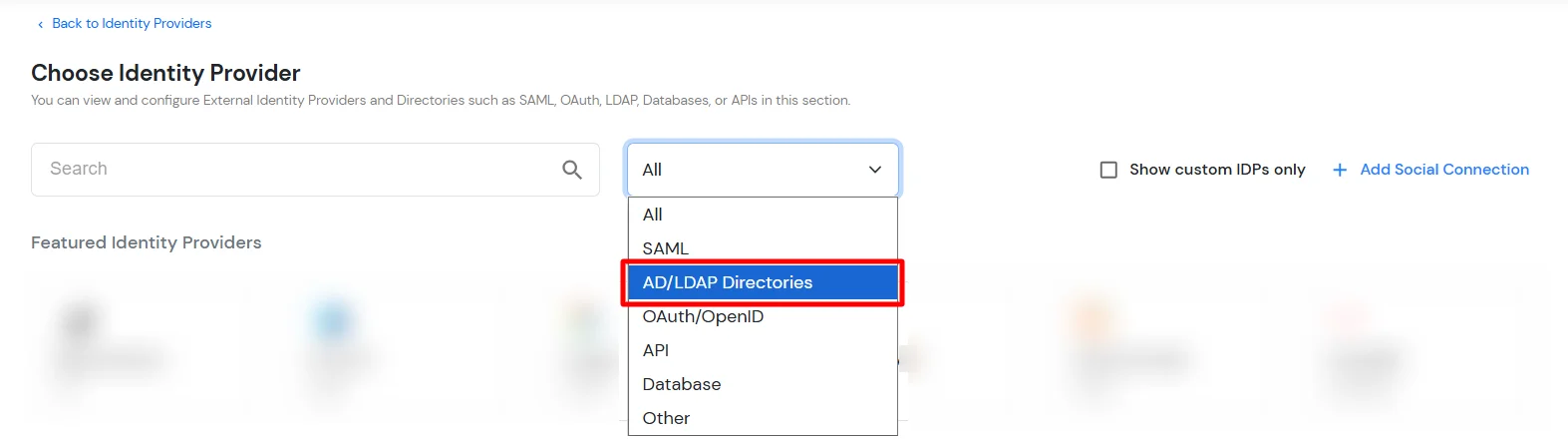
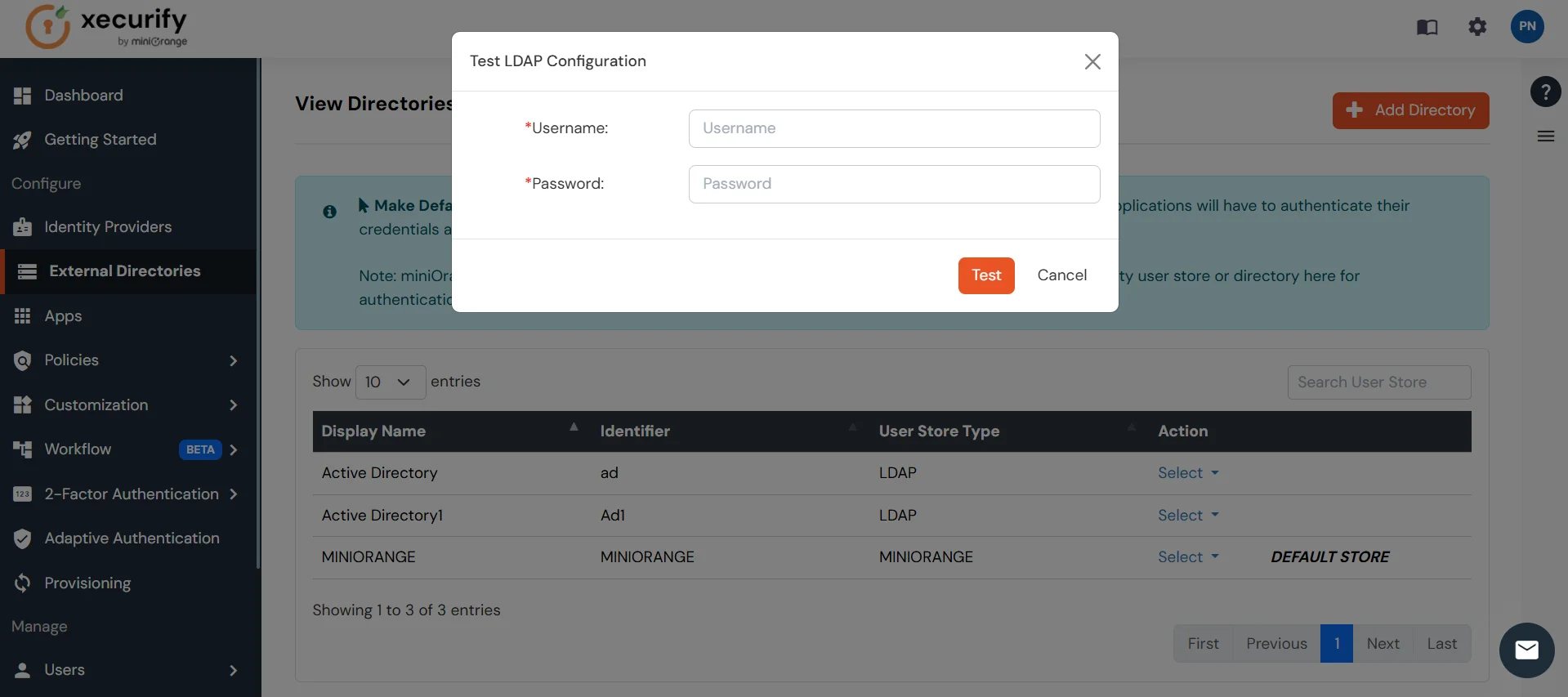
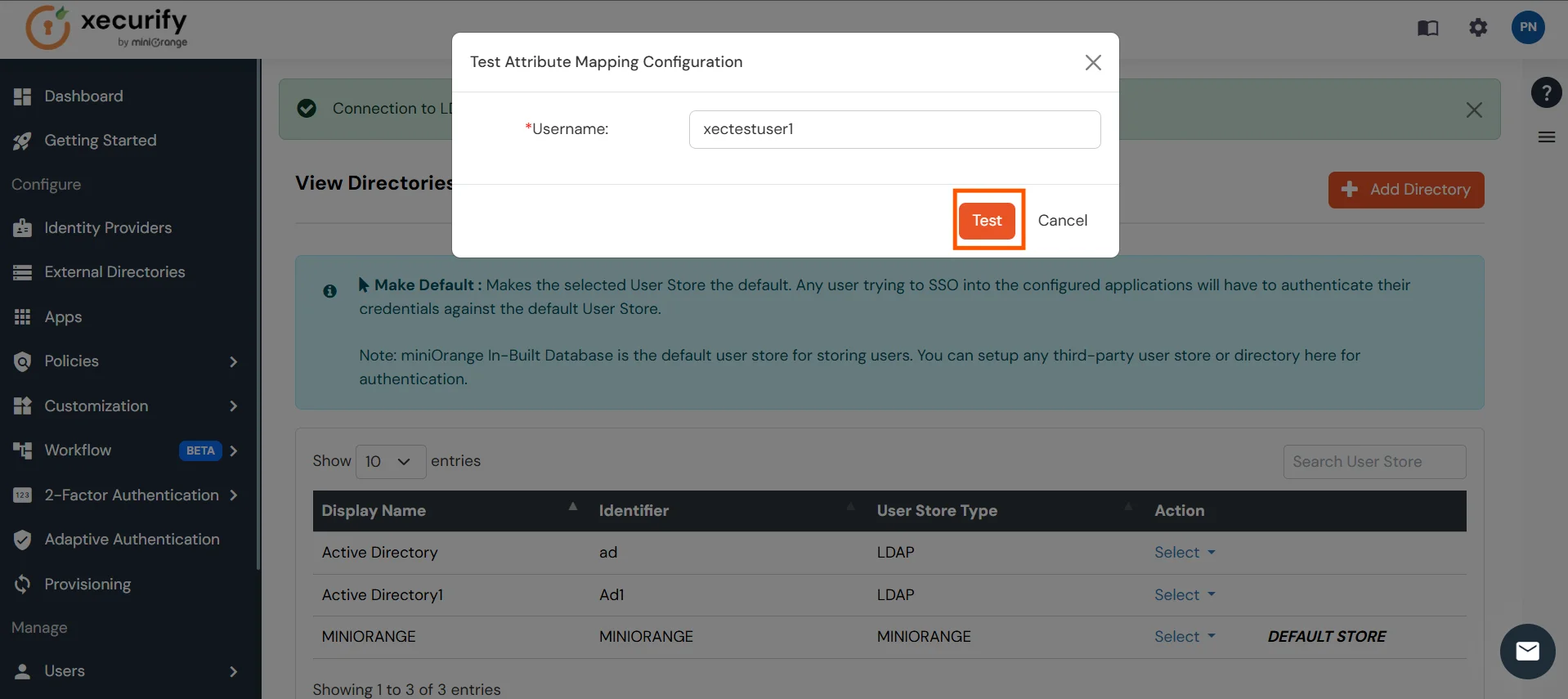
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.

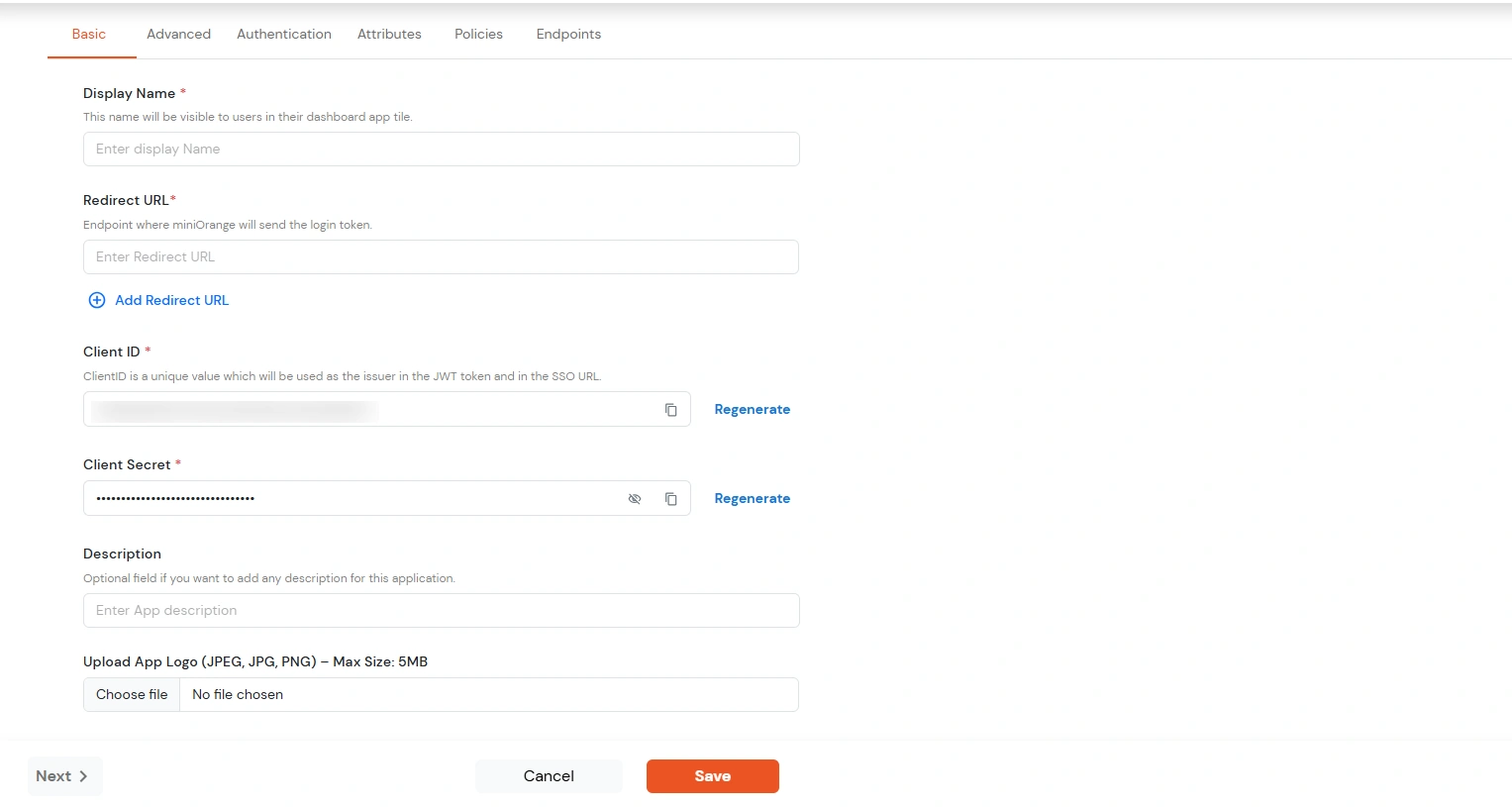
| Display Name | Enter the Display Name (i.e. the name for this application) |
| Redirect URL | Enter the Redirect URL (i.e. the endpoint where you want to send/post your JWT token). You can add multiple redirect URLs by separating them with a ‘;’.E.g. abc.com;xyz.com |
| Client ID | The Client ID is shown in the field below. Click the clipboard icon to copy it. |
| Client Secret | Client Secret is hidden by default. Click the eye icon to reveal it and use the clipboard icon to copy it. This is used in the HS256 signature algorithm for generating the signature. |
| Description (Optional) | Add a description if required. |
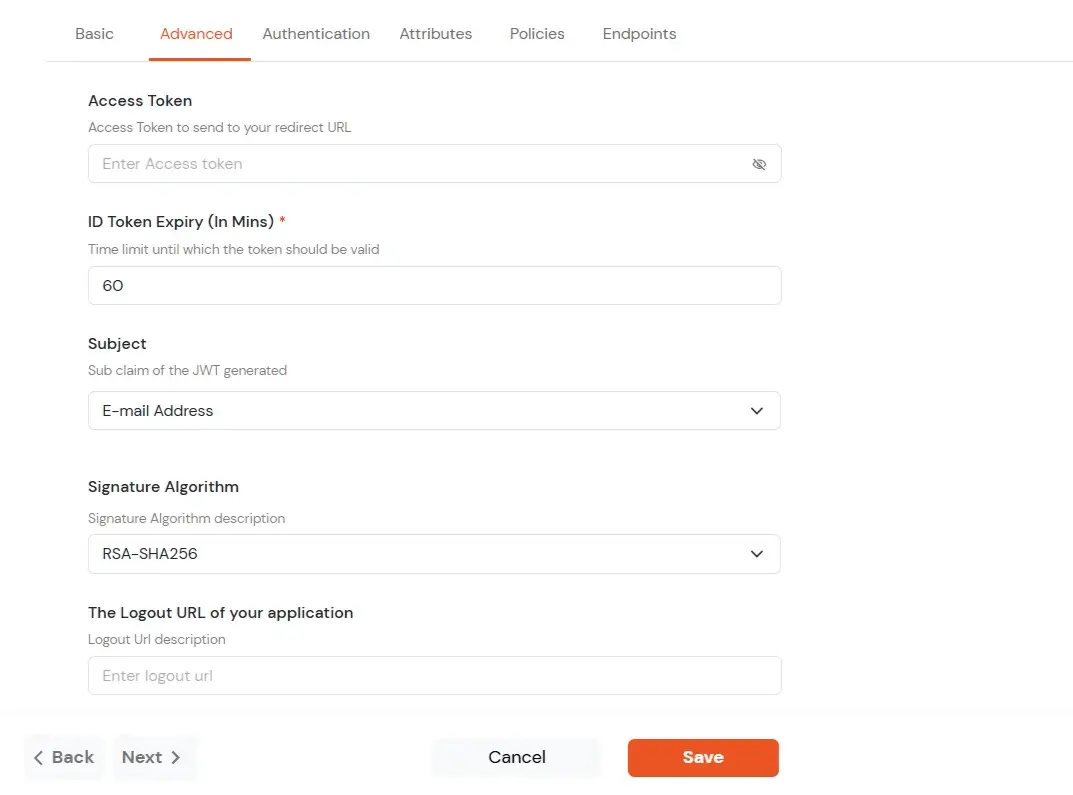
| Access Token | Enter the access token that will be sent to your redirect URL after a user logs in. This token helps your app know the user is allowed to access certain features. |
| ID Token Expiry (In Mins) | Set how long (in minutes) the ID token will be valid. After this time, the user will need to log in again to get a new token. |
| Subject | Choose what information, like the user’s email address, will be used to identify them in the token. This helps your app know which user is logged in. |
| Signature Algorithm | Select your signature algorithm from the dropdown. |
| The Logout URL of your application | Enter the web address where users should be sent after they log out. |
| Enable Shared Identity | This feature lets you control whether a specific application can be accessed by shared user or not. |
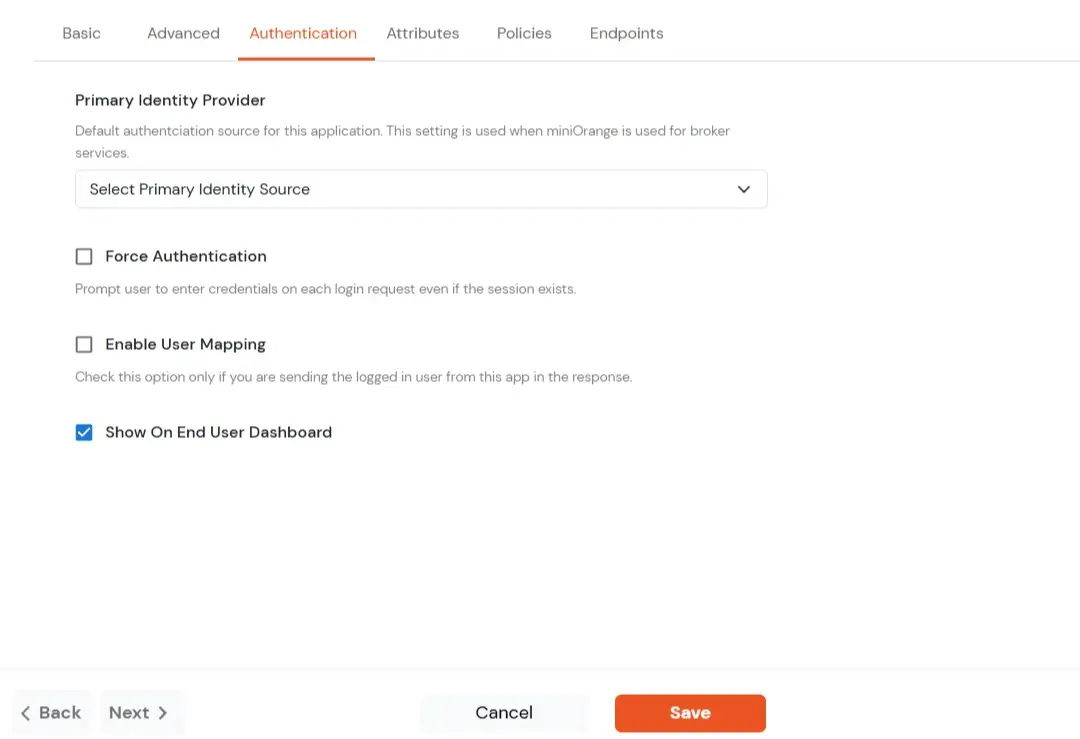
| Primary Identity Provider | Select the default ID source from the dropdown for the application. If not selected, users will see the default login screen and can choose their own IDP. [Choose miniOrange in this case.] |
| Force Authentication | If you enable this option, users will have to log in every time, even if their session already exists. |
| Enable User Mapping | Enable this option, if you want the app to show which user is signed in when it responds. |
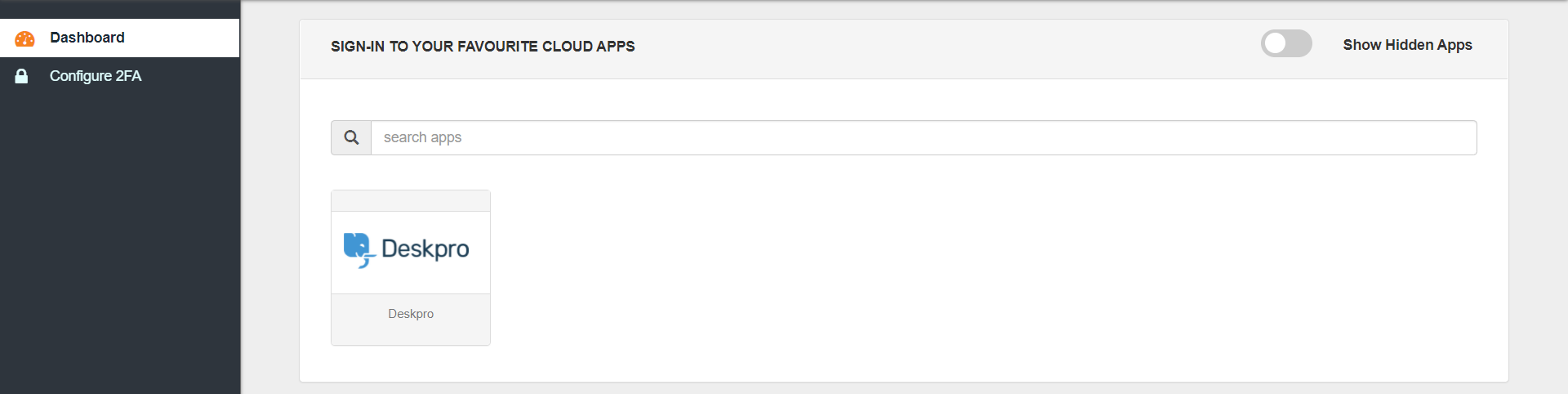
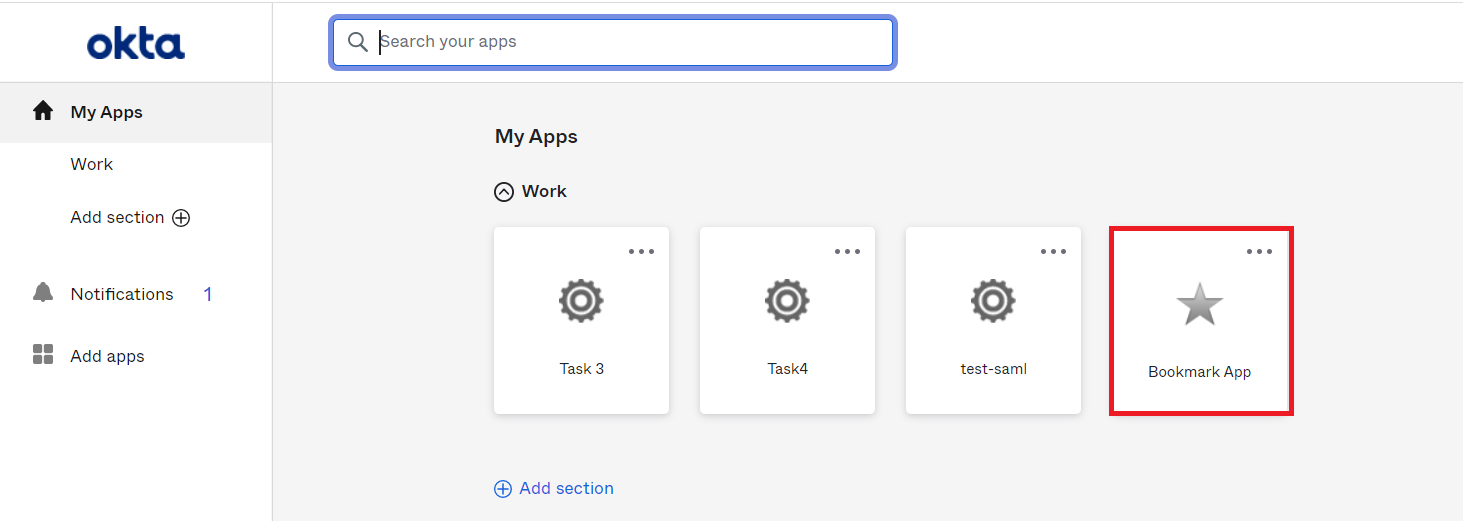
| Show On End User Dashboard | Enable this option if you want to show this app in the end-user dashboard. |
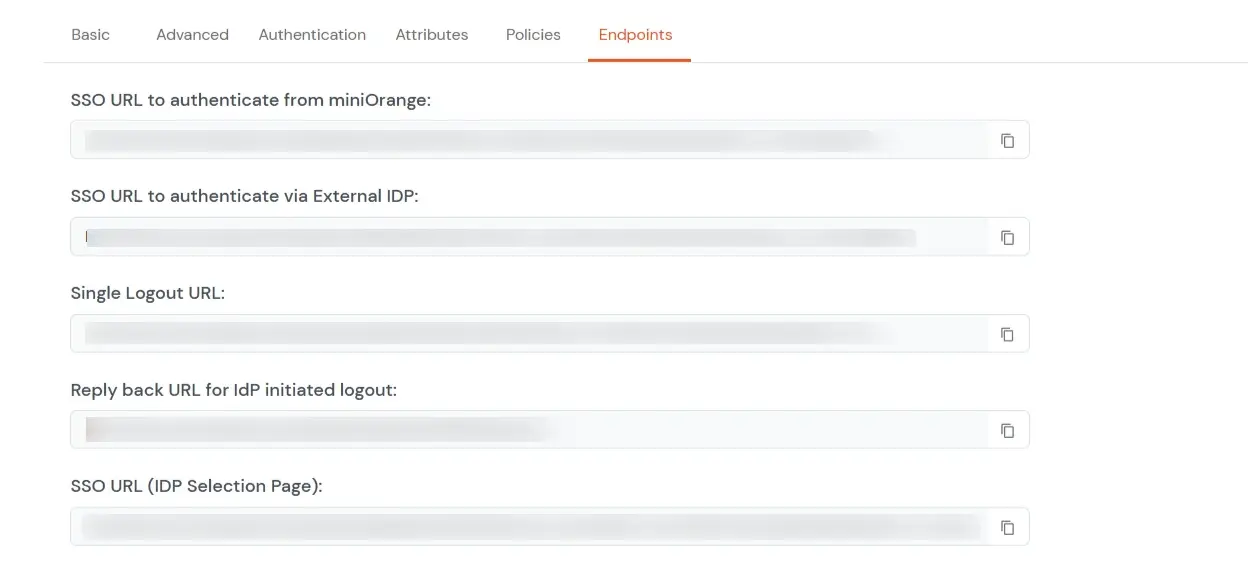
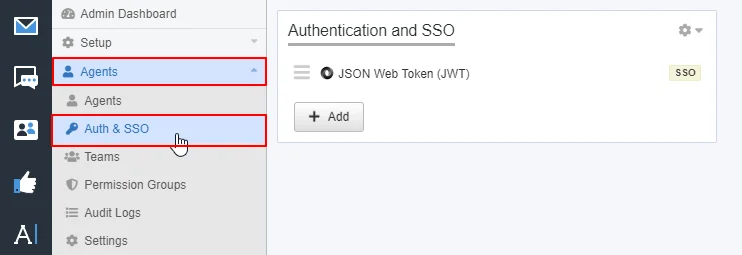
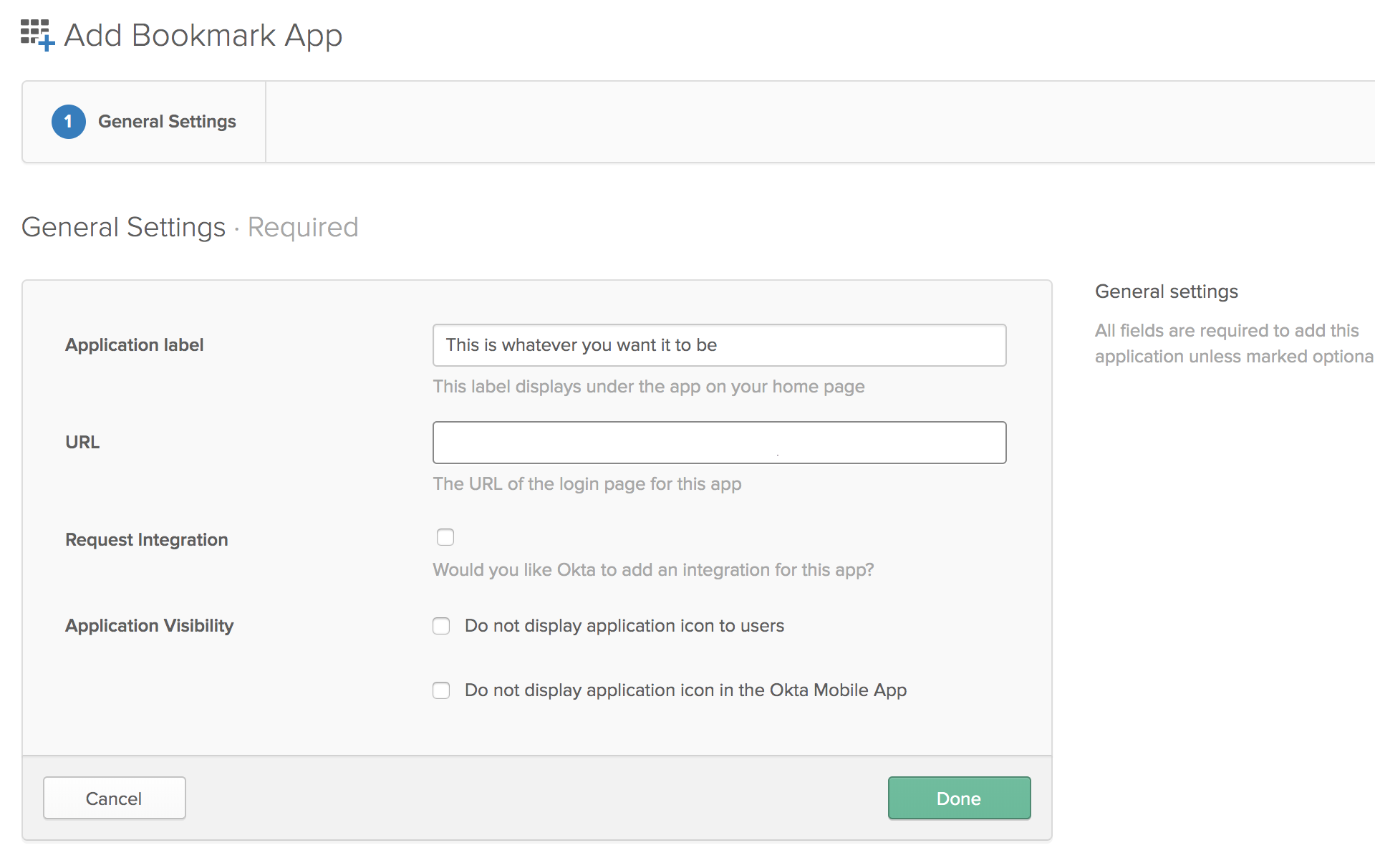
https://login.xecurify.com/moas/broker/login/jwt/<customer-id>?client_id=<client-id>&redirect_uri=<your_domain>.deskpro.com and JWT Secret Code that you get from the above step.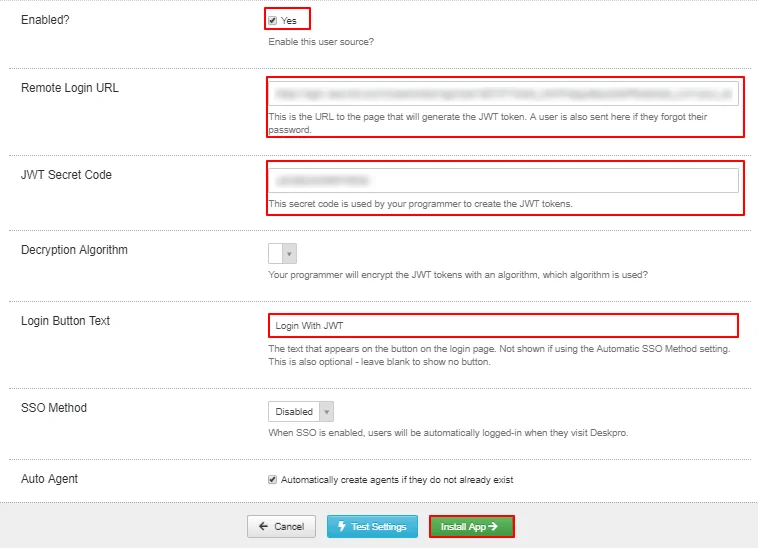

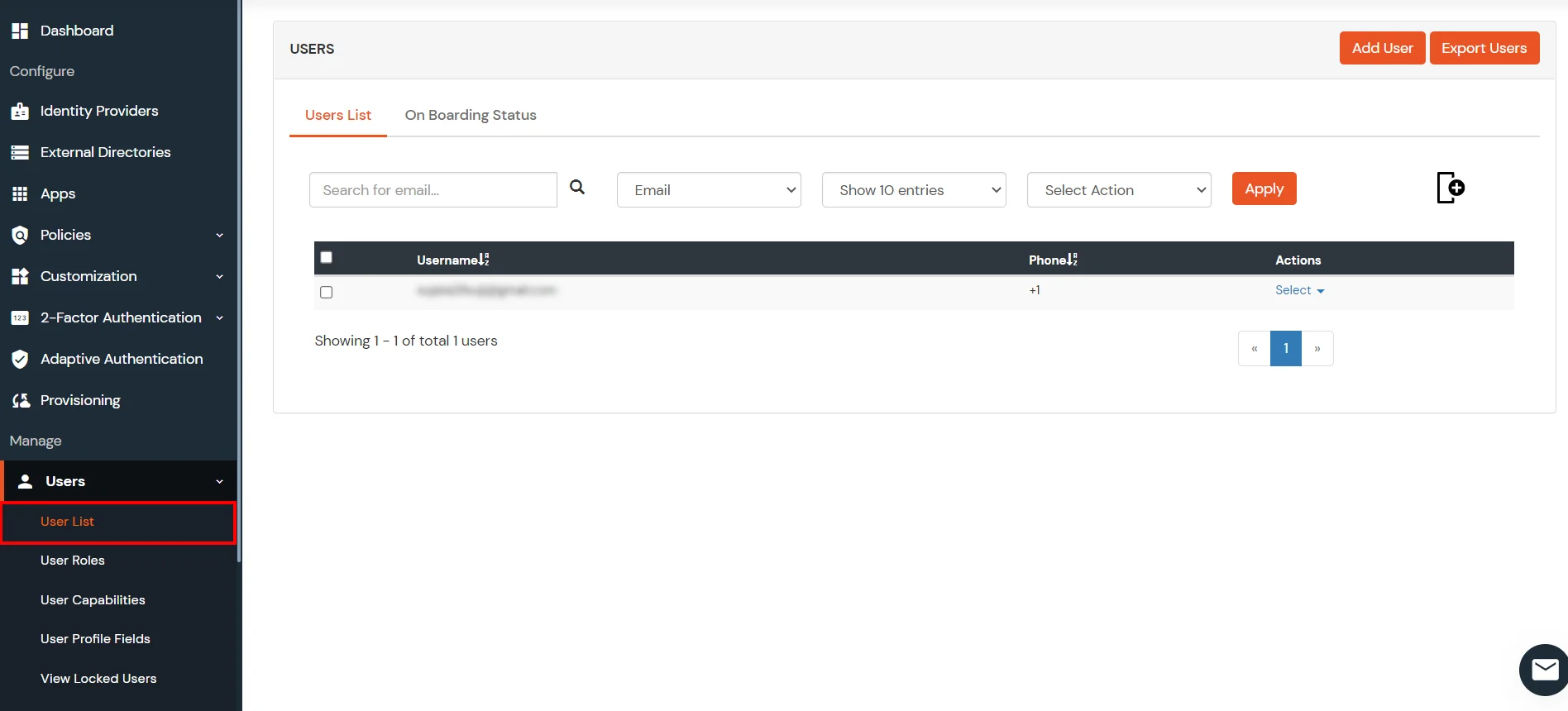
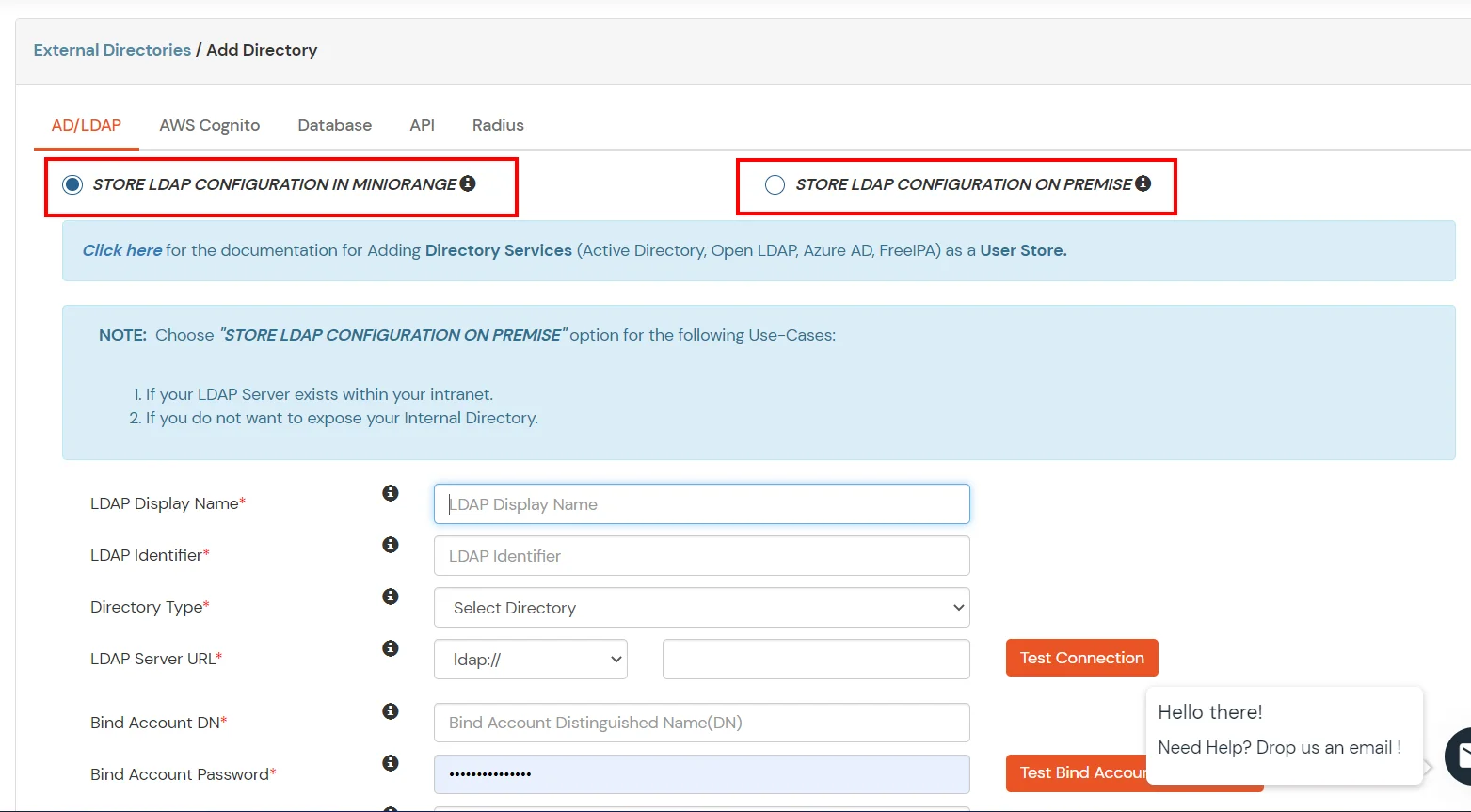
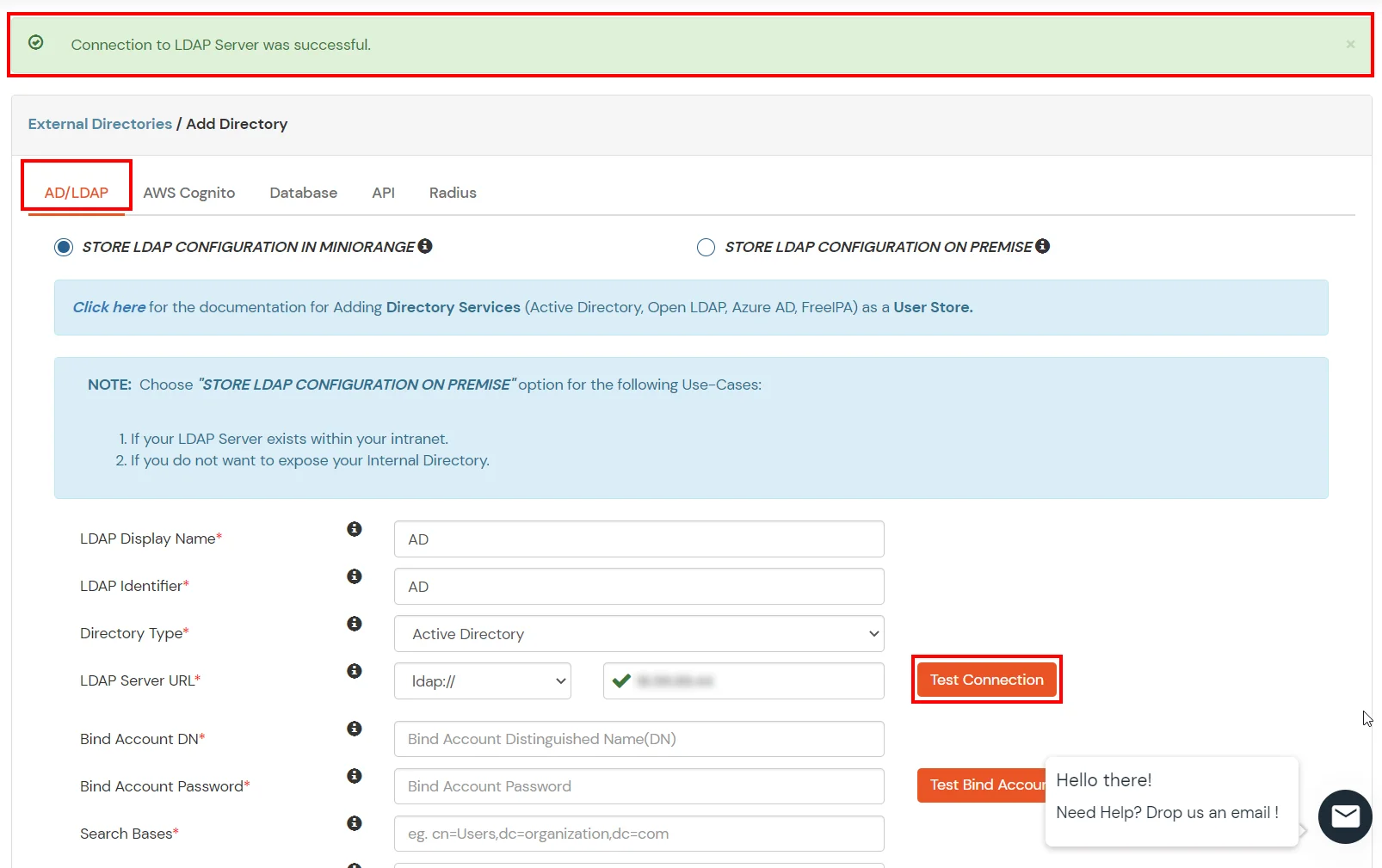
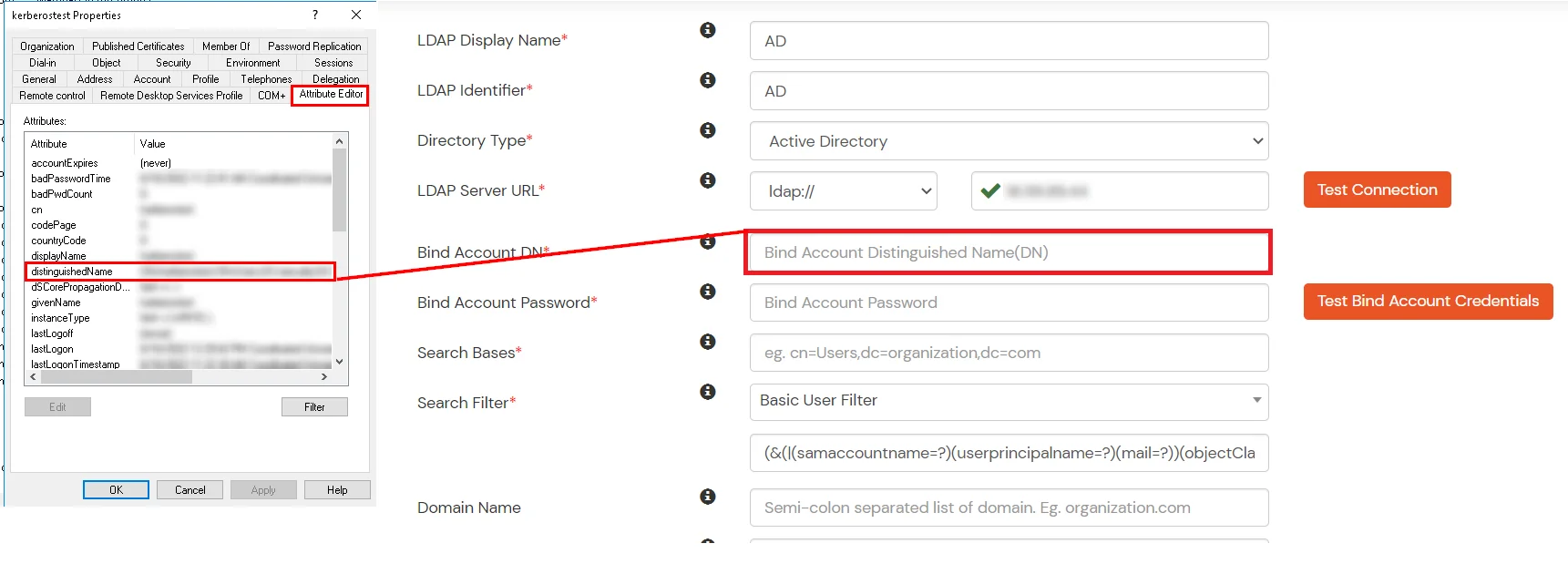
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
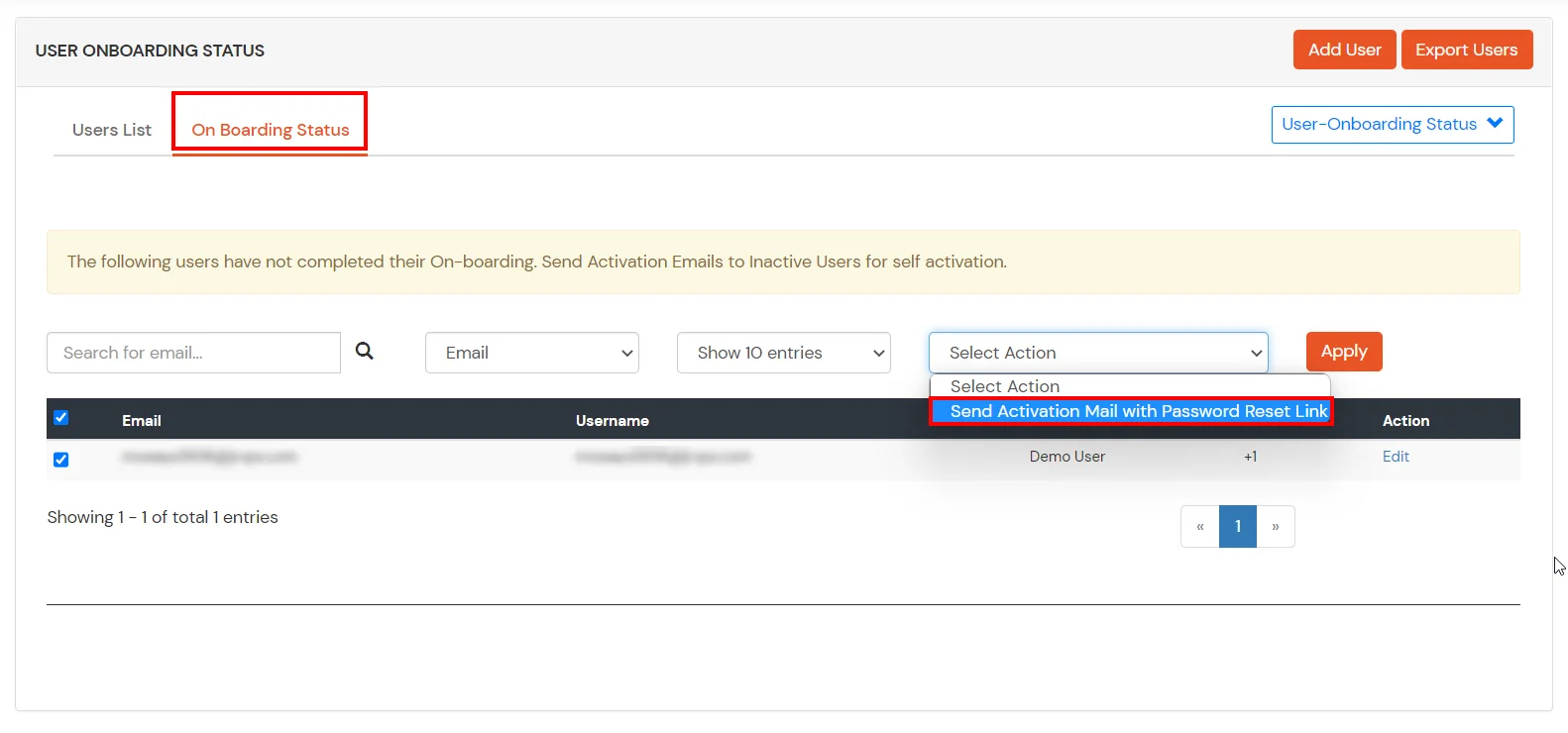
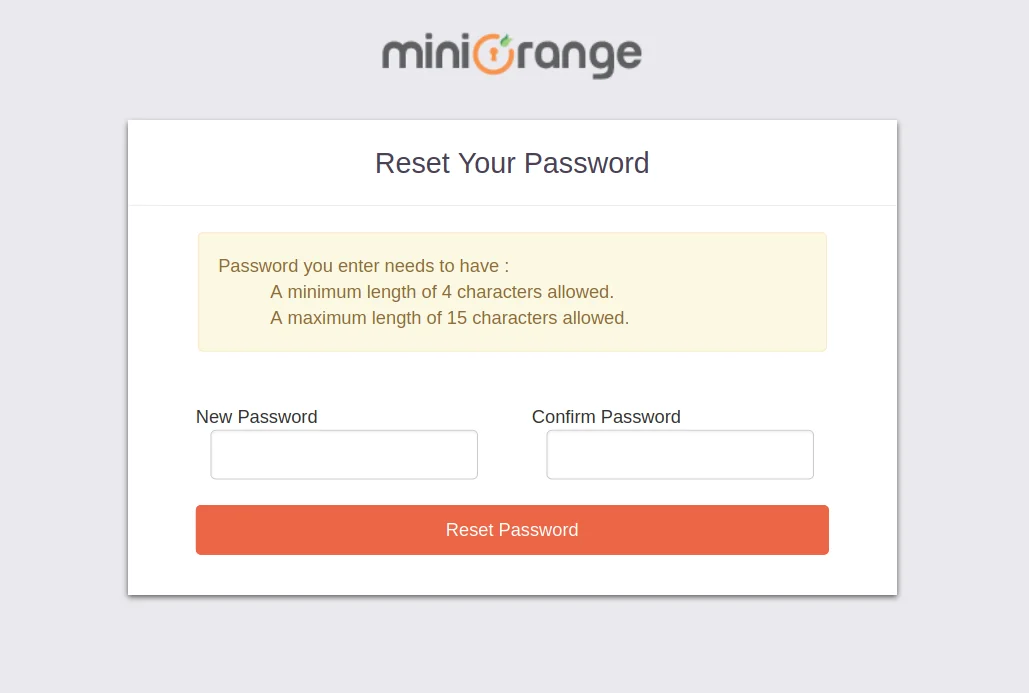
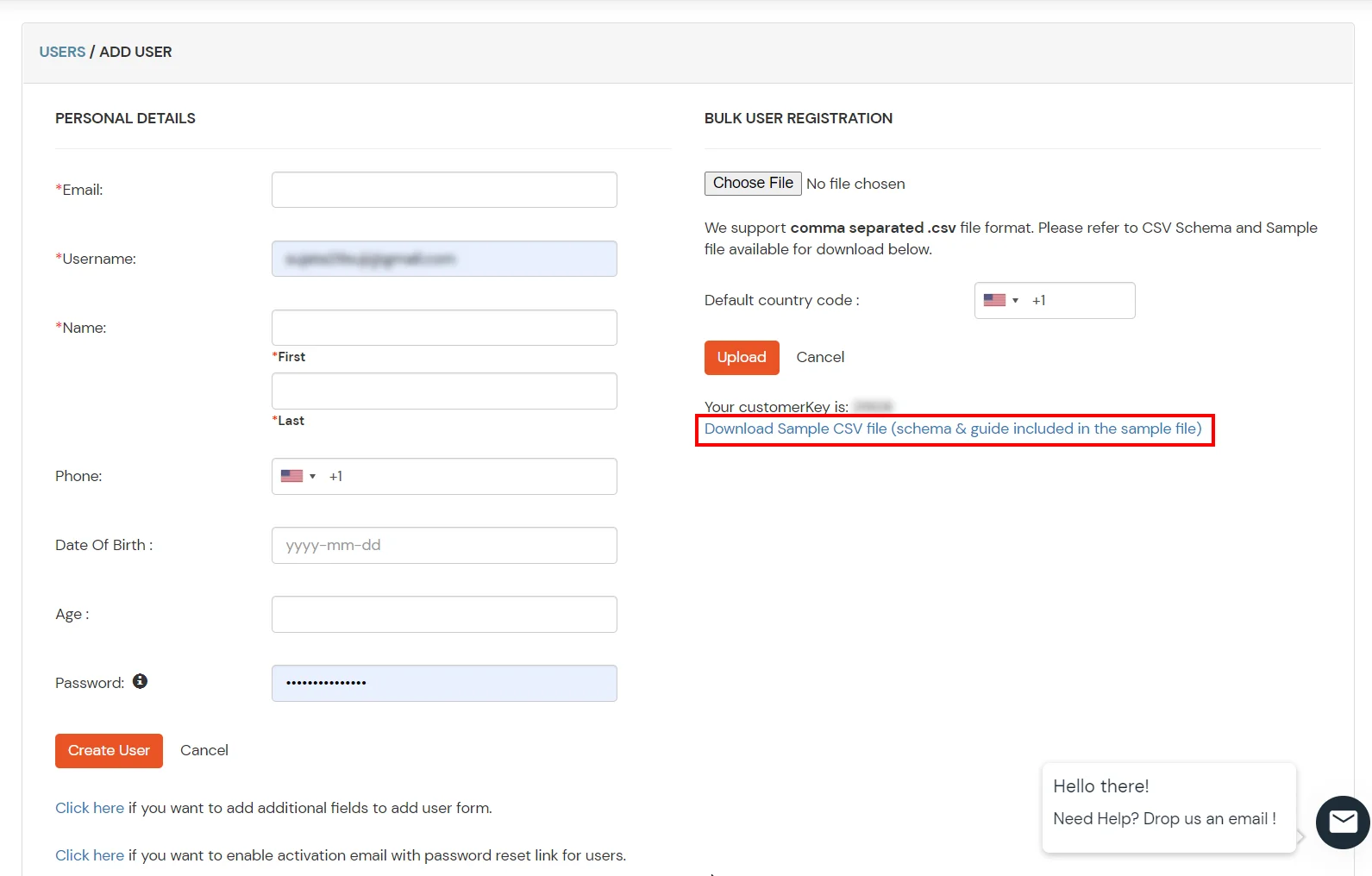
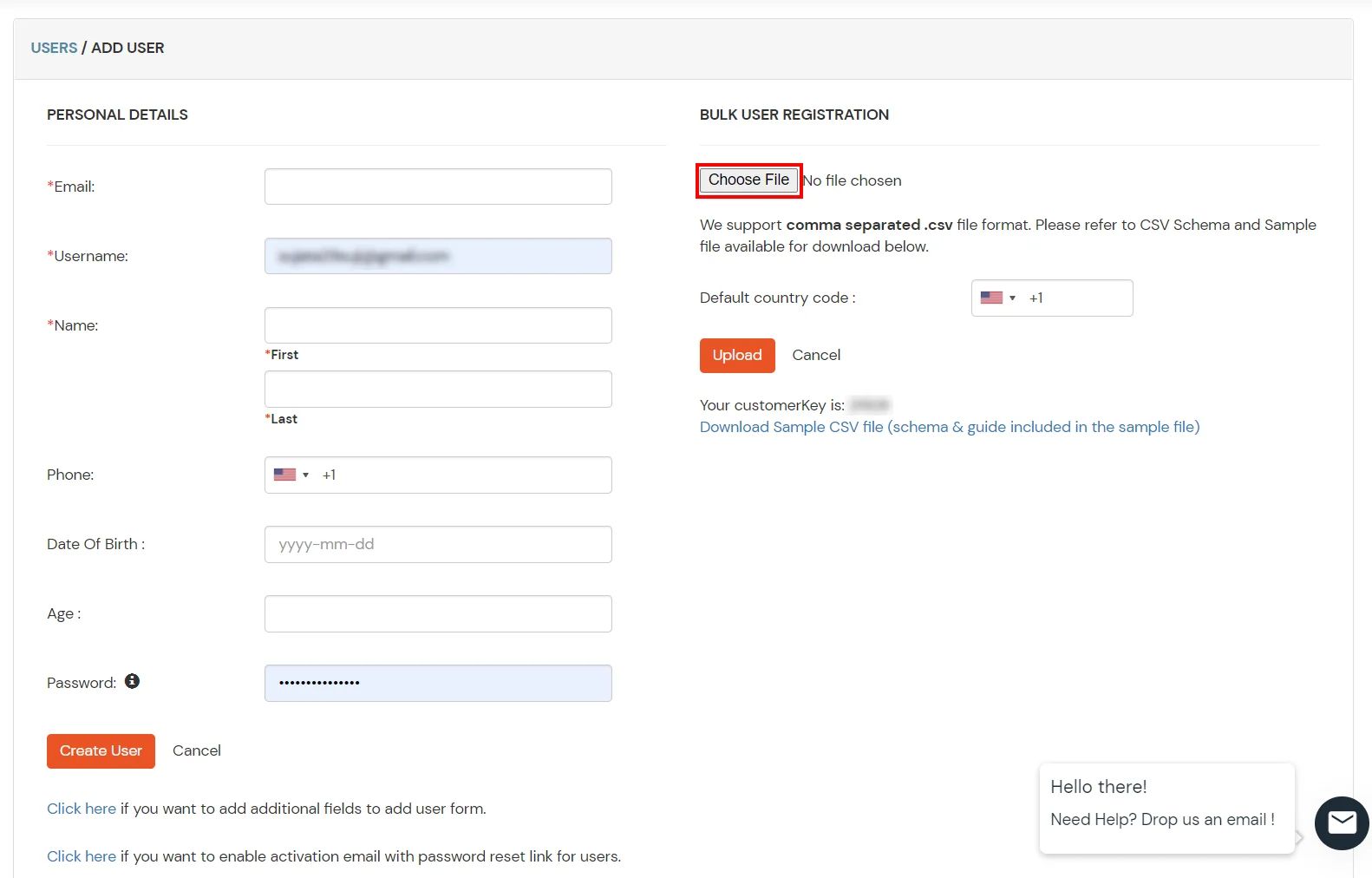
1. Create User in miniOrange

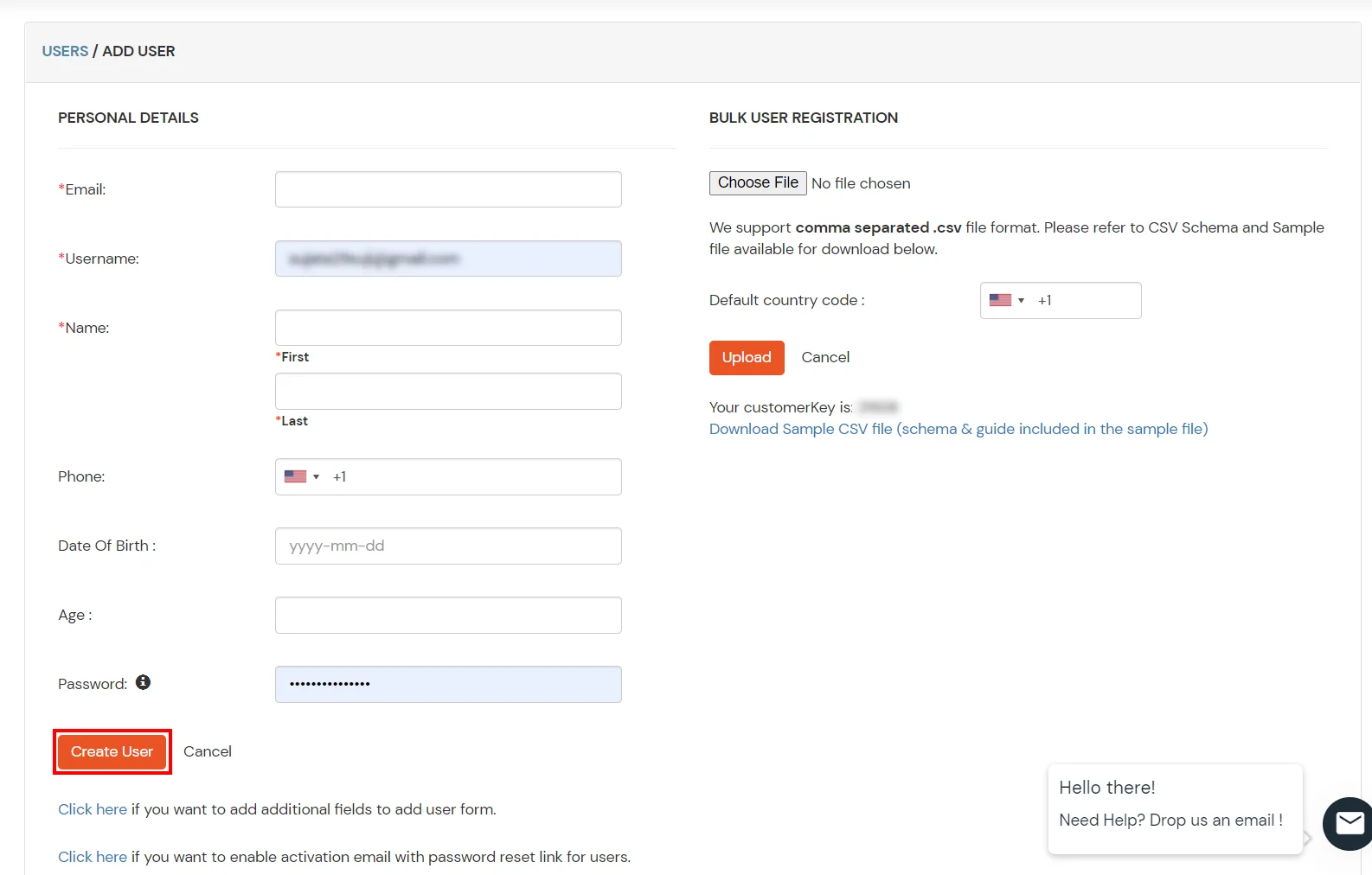
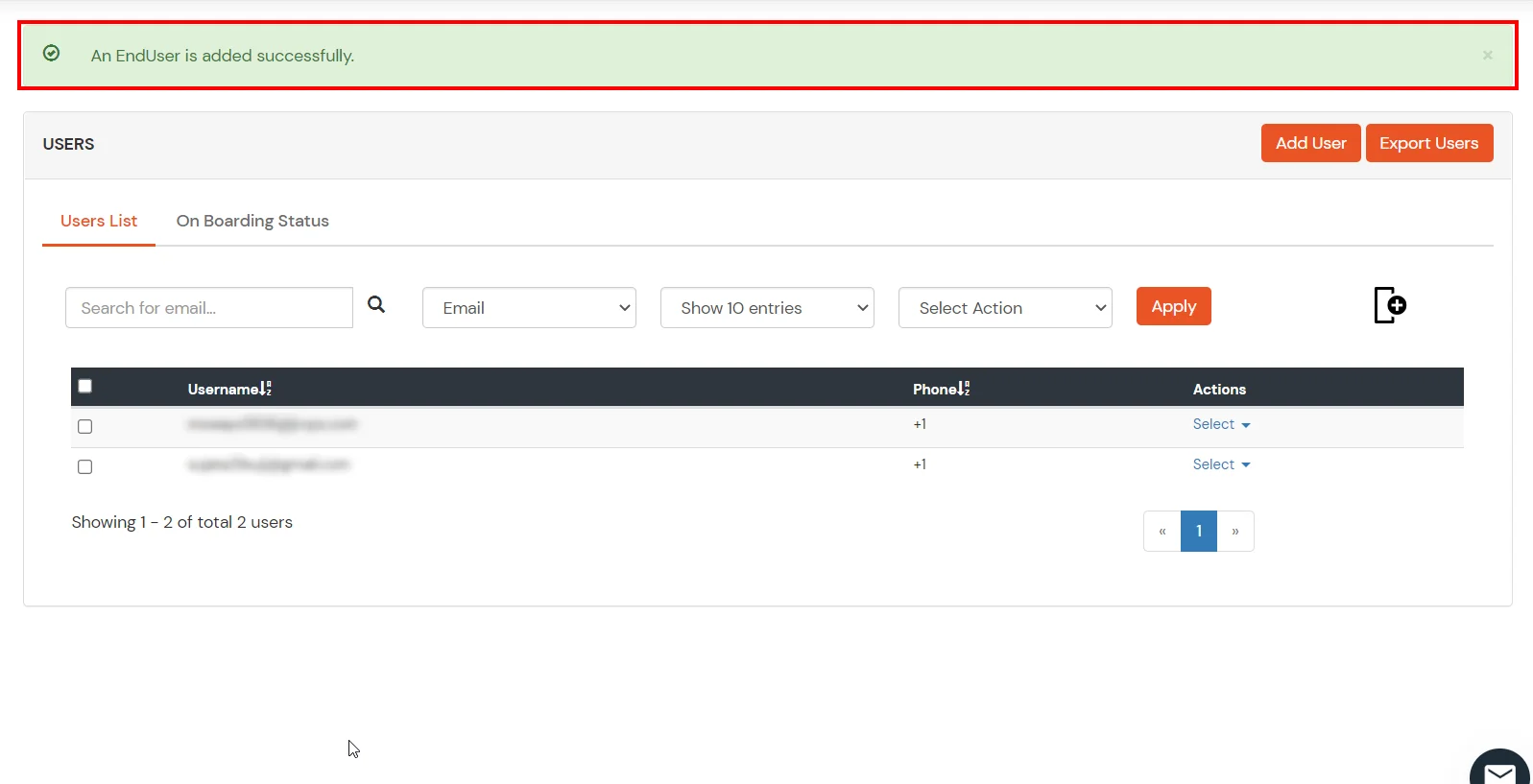
2. Bulk Upload Users in miniOrange via Uploading CSV File.
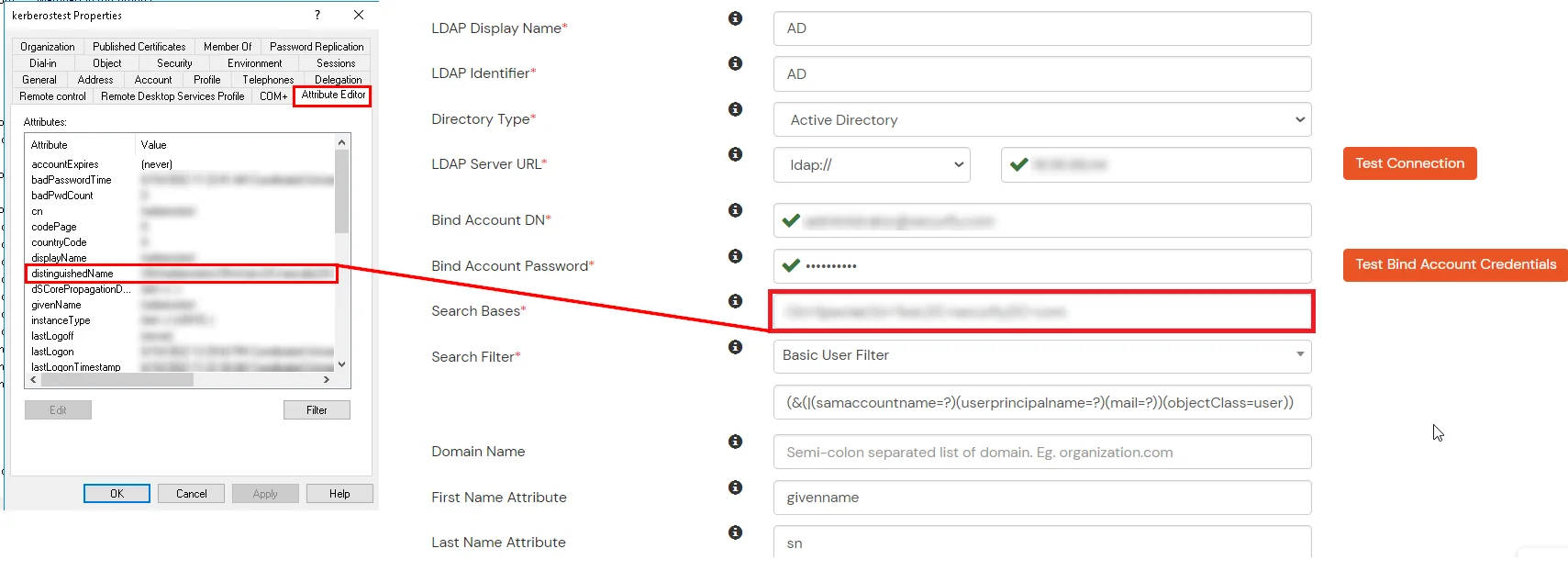
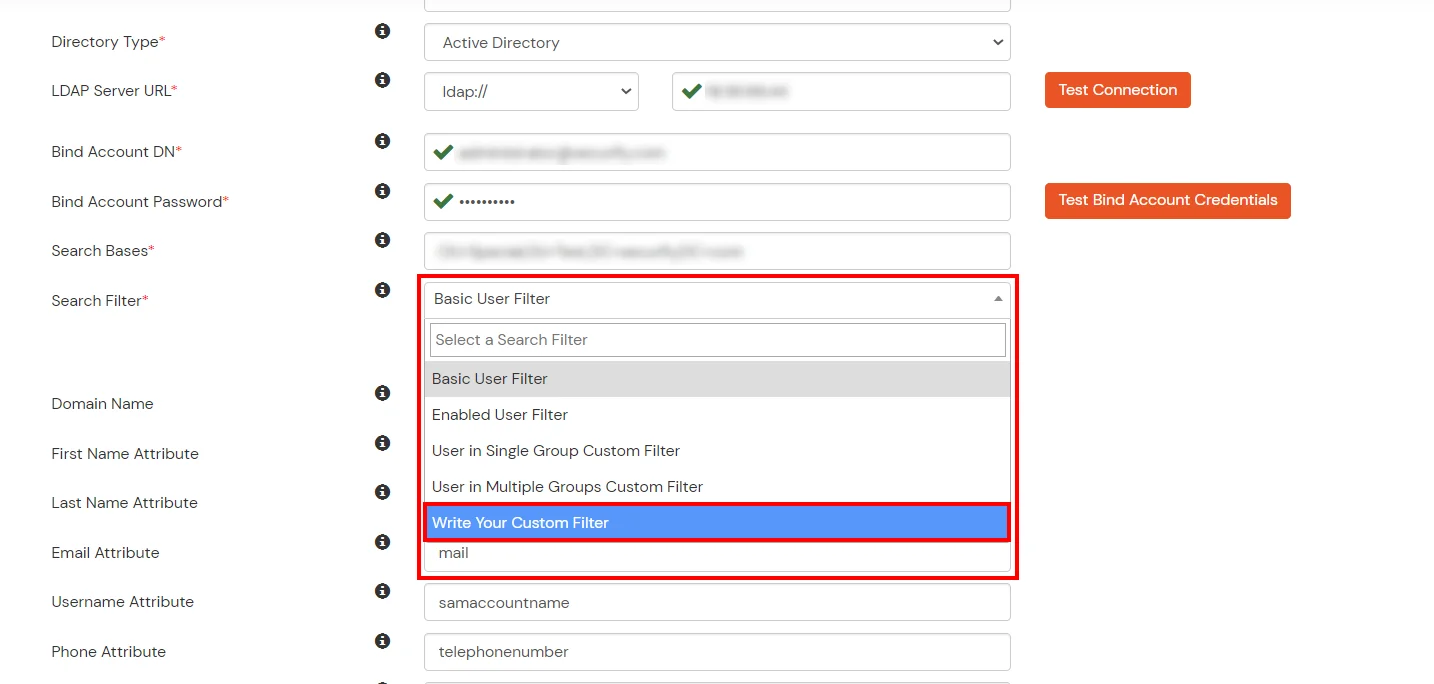
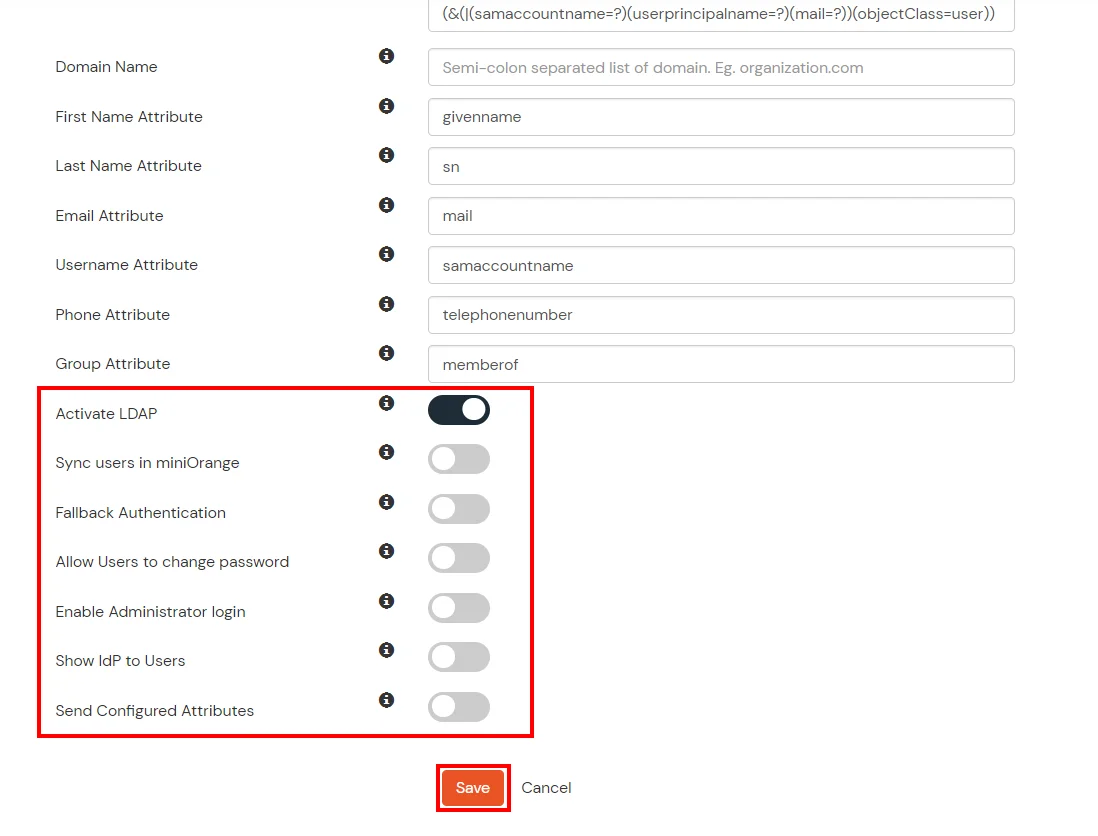
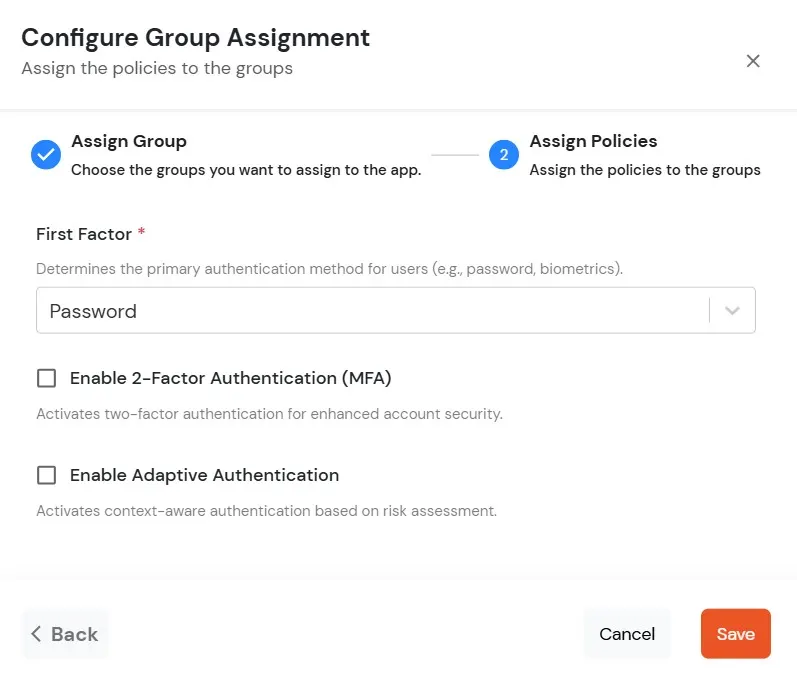
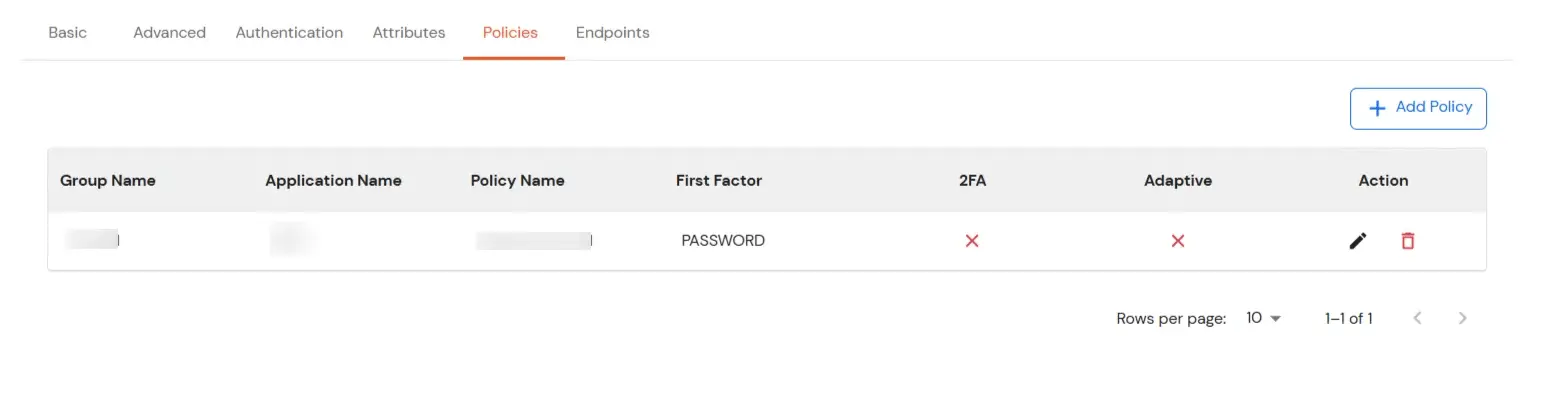
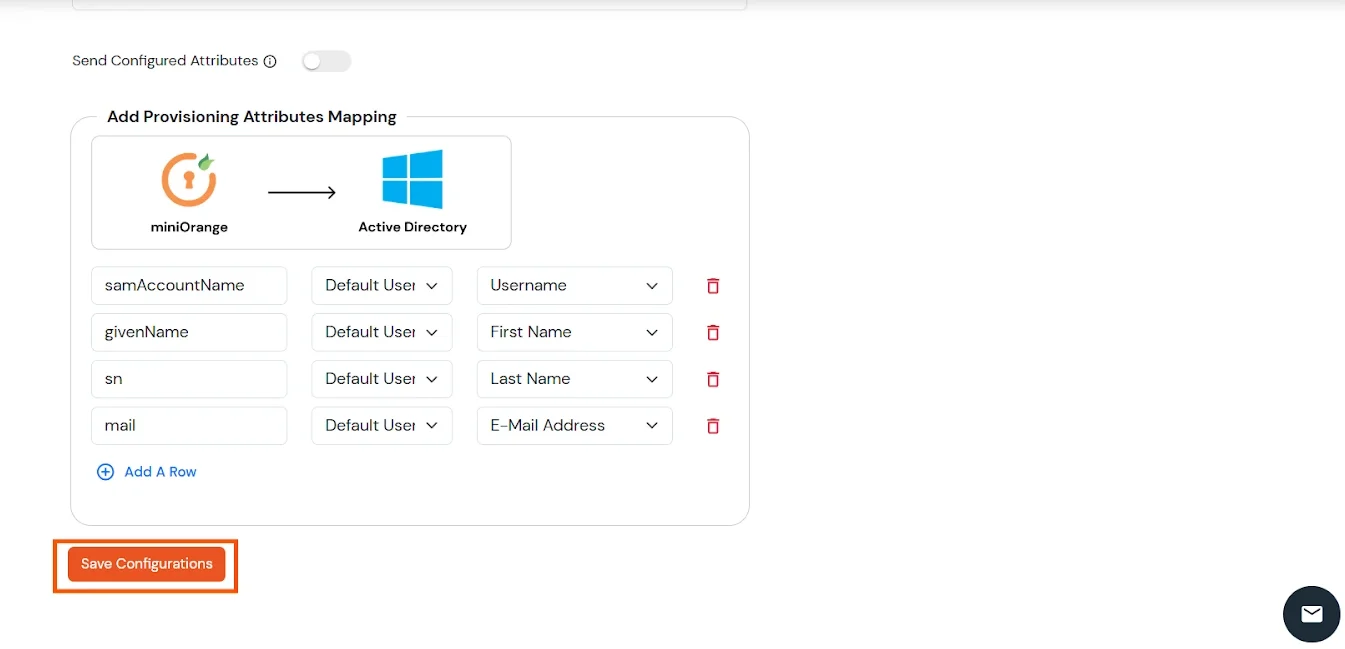
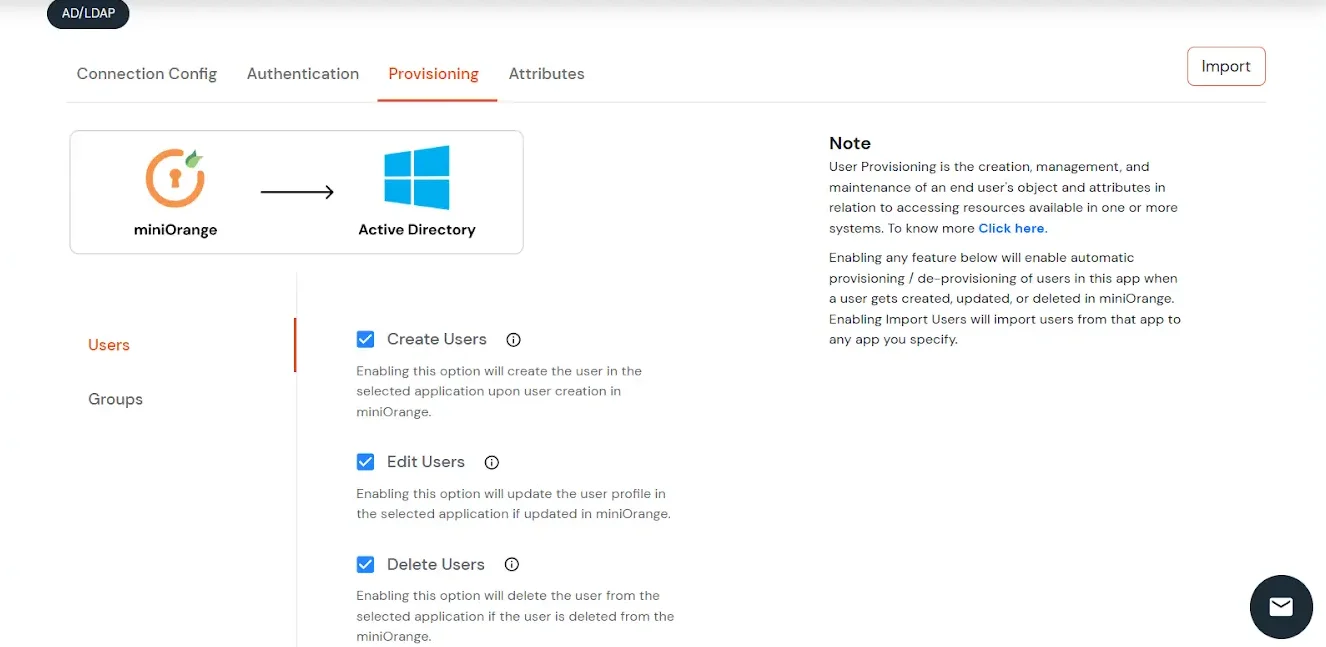
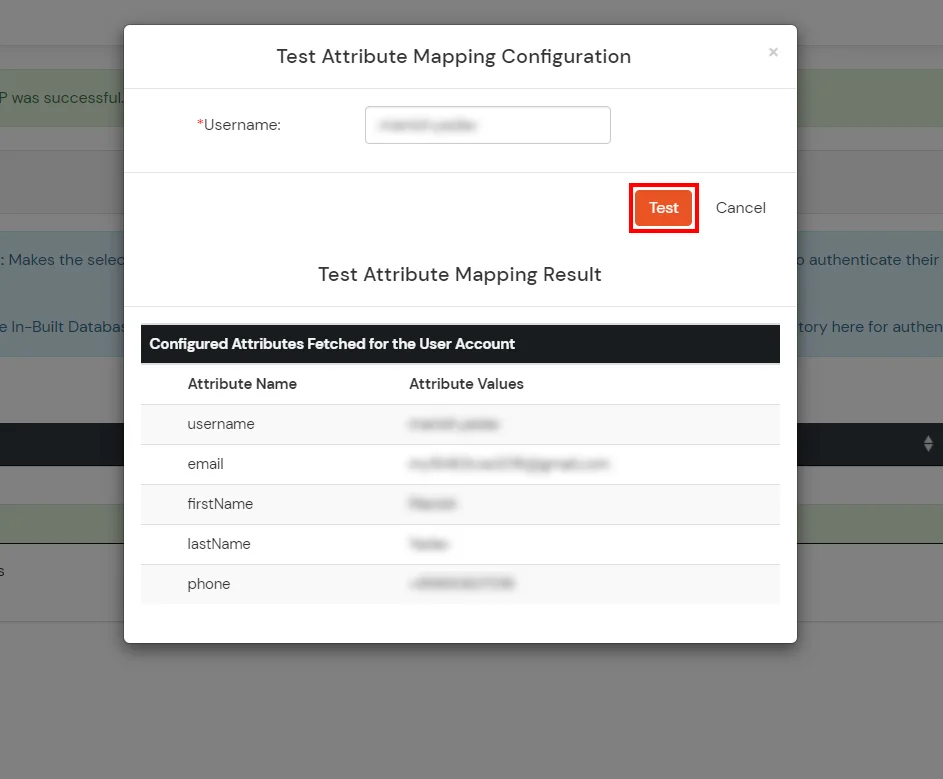
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute | Description |
|---|---|
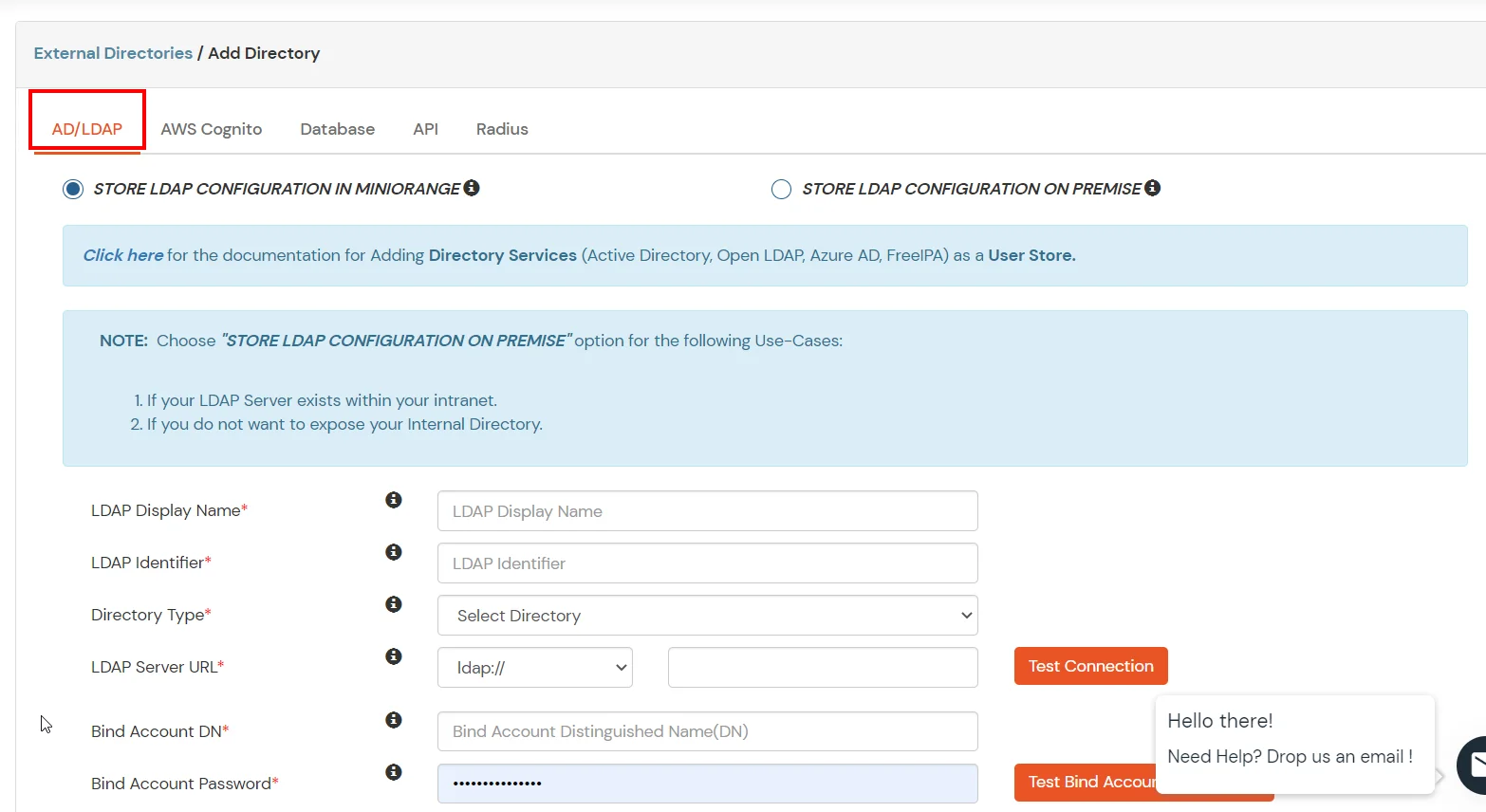
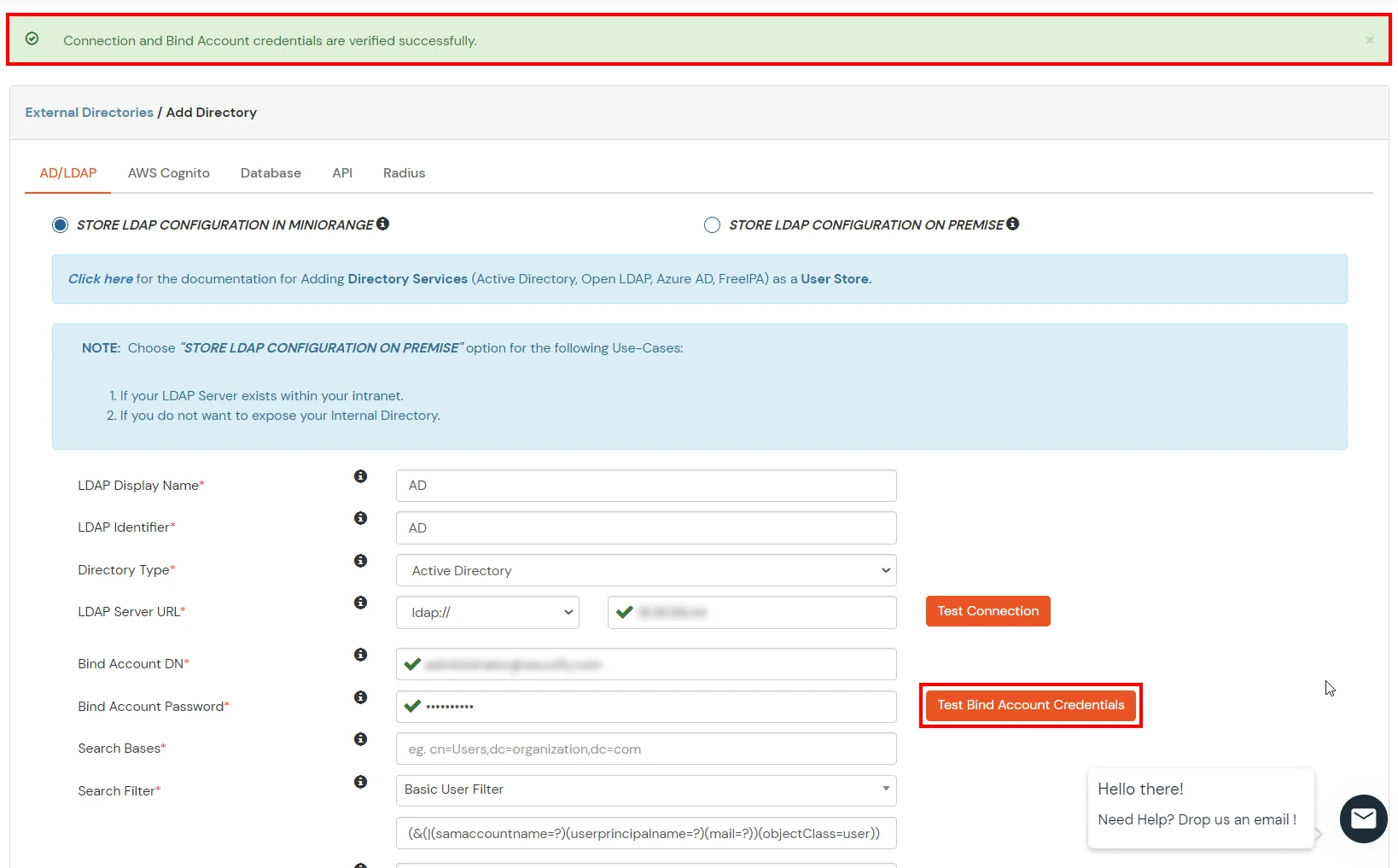
| Activate LDAP | All user authentications will be done with LDAP credentials if you Activate it |
| Fallback Authentication | If LDAP credentials fail then user will be authenticated through miniOrange |
| Enable administrator login | On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users | If you enable this option, this IdP will be visible to users |
| Sync users in miniOrange | Users will be created in miniOrange after authentication with LDAP |
Attribute Name sent to SP = organization
Attribute Name from IDP = company
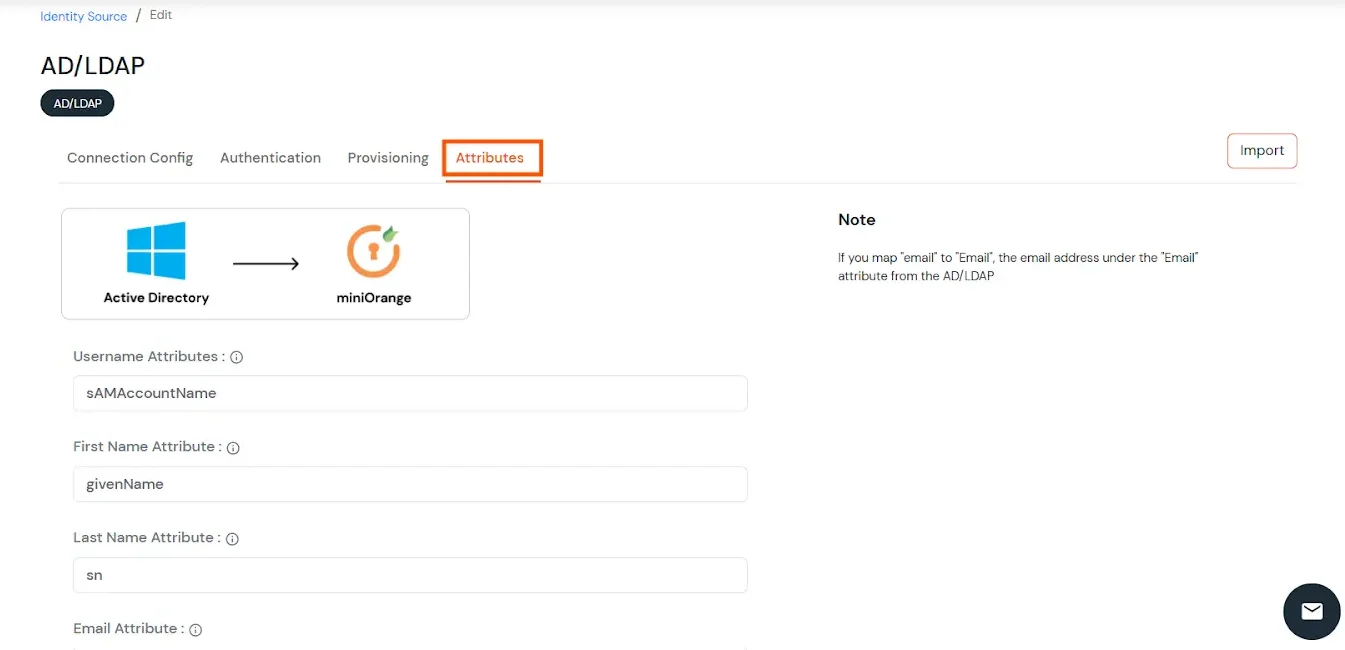
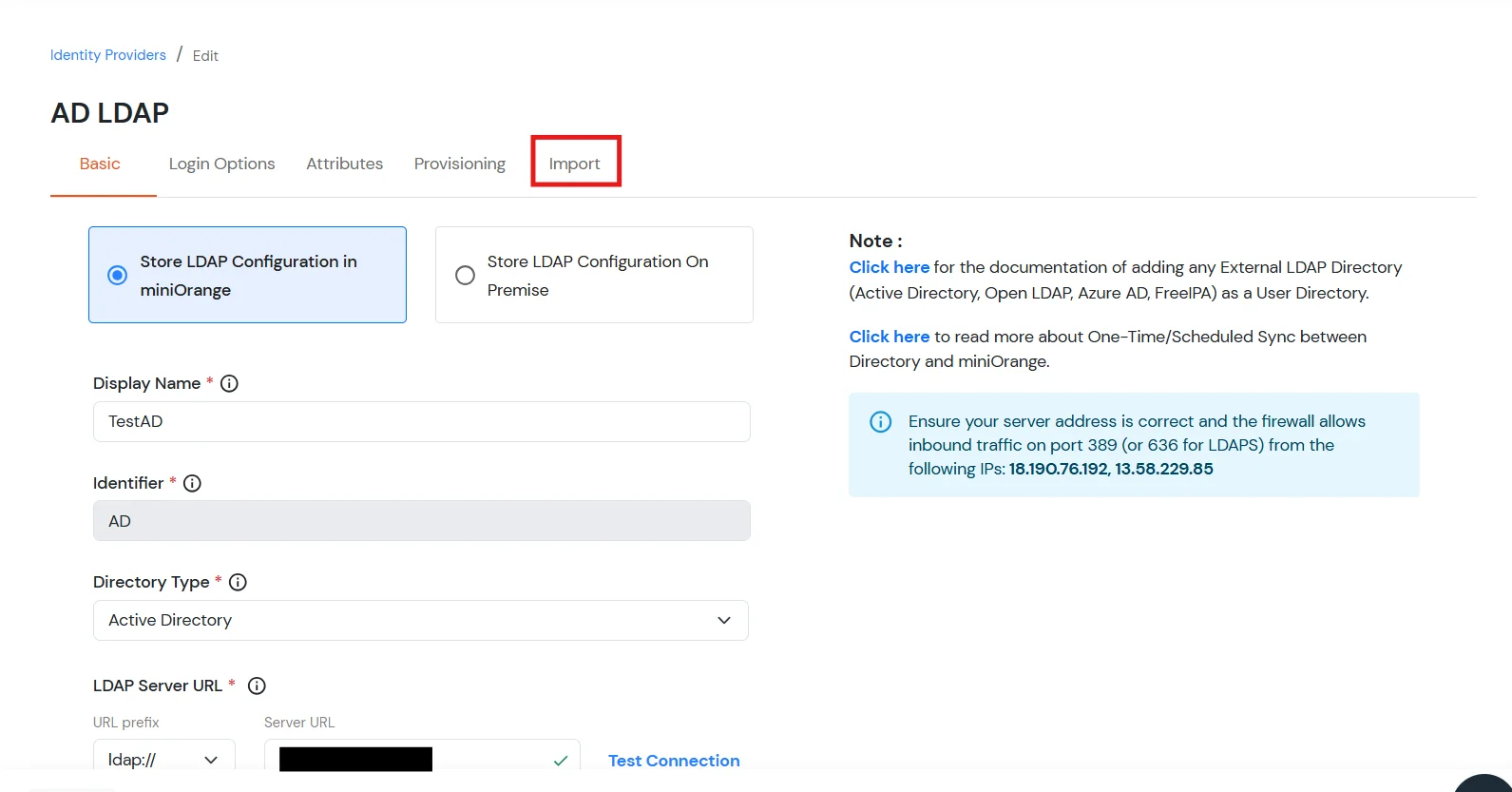
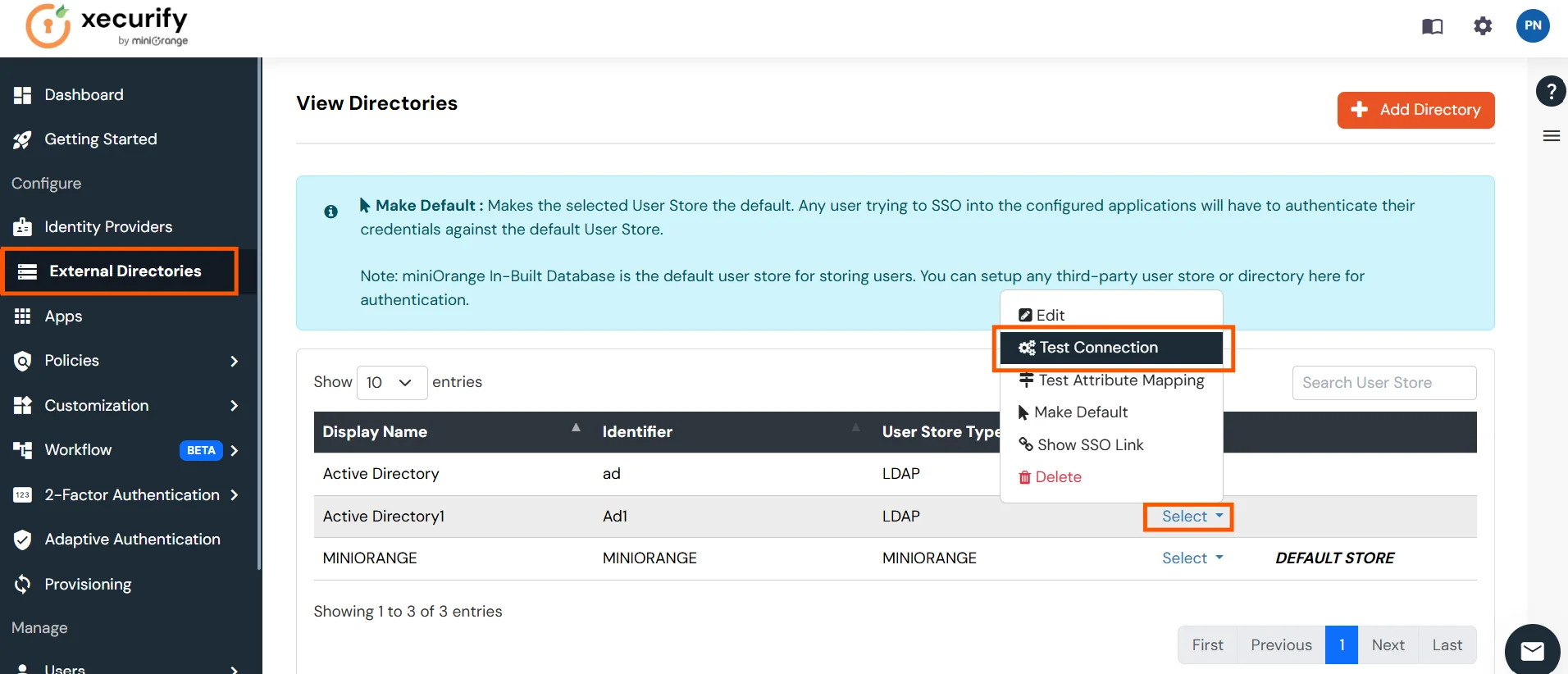
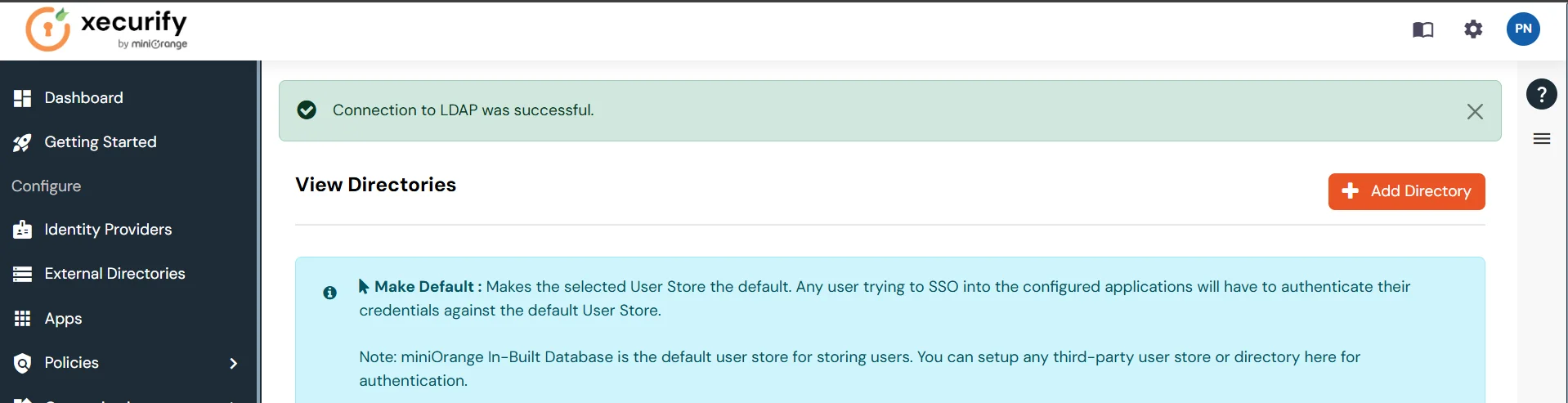
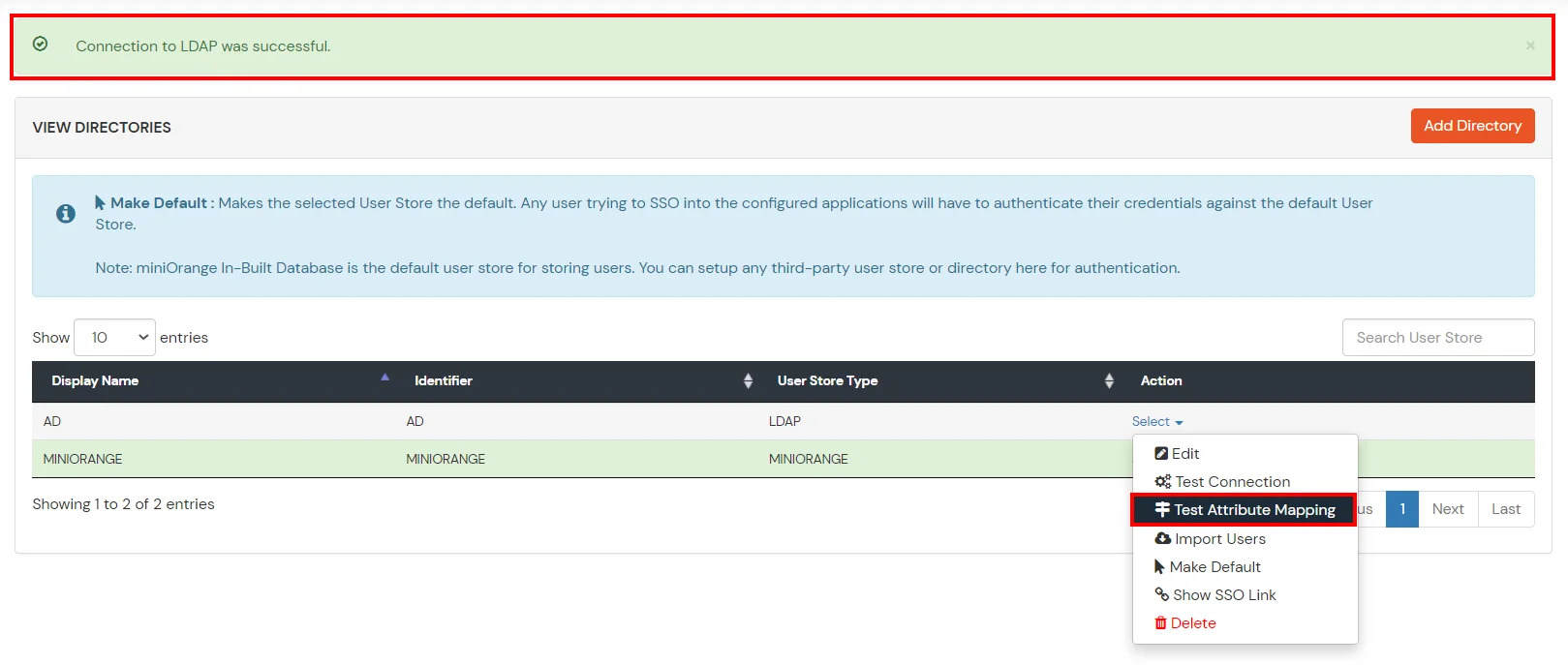
Set up AD as External Directory configuration is complete.
Note: Refer our guide to setup LDAP on windows server.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
Contact us or email us at idpsupport@xecurify.com and we'll help you setting it up in no time.
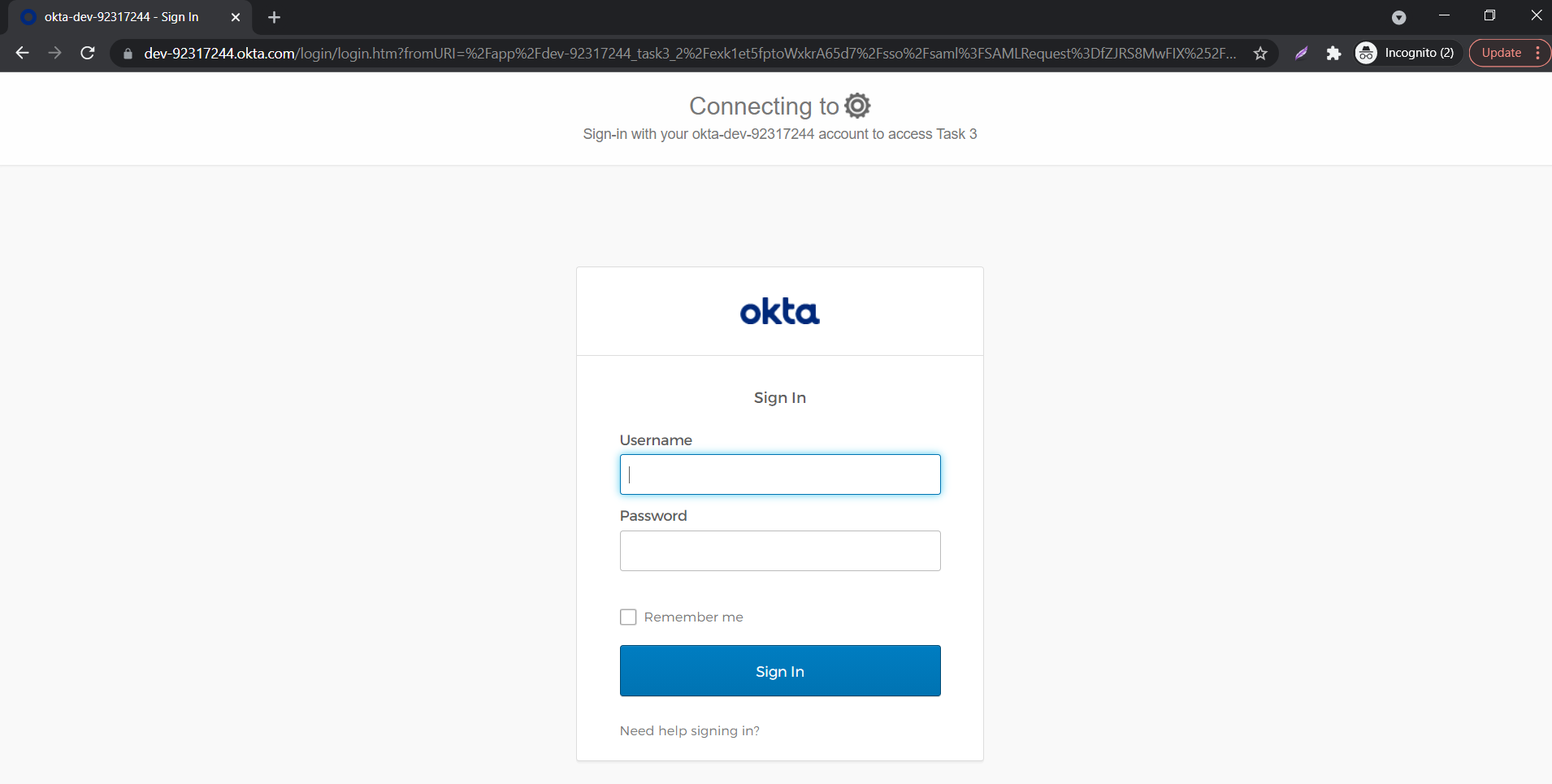
Yes, you can connect any external IdP like Gsuite, Okta, AzureAD etc or authenticate from any user store like miniOrange, Active Directory, Database etc and SSO into Deskpro. After authentication miniOrange would send a JWT token to Deskpro which is used by Deskpro for logging the user in. You can read about it here.
