Wix Single Sign-On (SSO)
Wix provides a platform that allows businesses or people to create responsive websites without any technical expertise. It provides the pre-edited templates of different sites as per users' needs. Wix allows users to accomplish most aspects of web development & website distribution entirely within the application. Therefore,miniOrange has created an interface for admins to enable Single Sign-On (SSO) solution for their Wix website.
Challenge faced by Wix Users
Wix admins demand a continuous & seamless access for their users to access Wix portal via existing credentials. They don't wish for their users to have a separate set of credentials for logging into Wix & other apps. Wix provides a way for its users to allow logging into the platform seamlessly. But, an interface needs to be created which would allow this.
miniOrange provides SSO solution for Wix
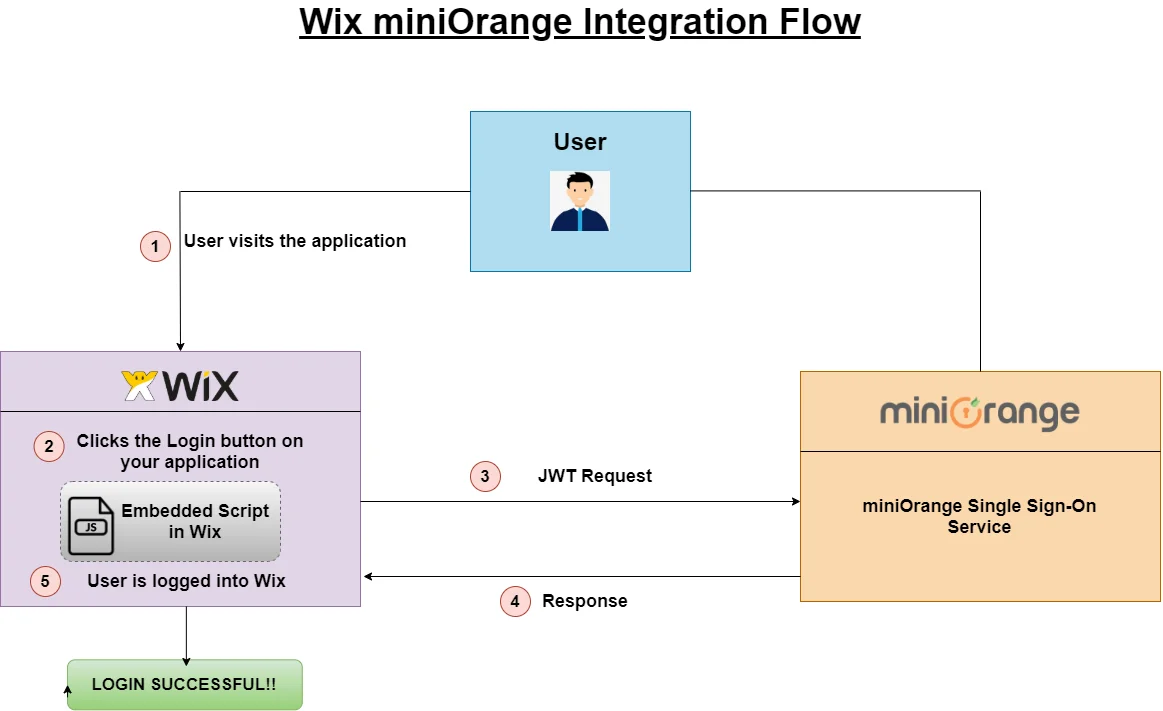
miniOrange provides an integrated SSO solution where a logged-in user's existing session can be used to log the users into Wix & other websites/apps by creating a valid JSON Web Token (JWT). Using this Wix SSO solution, users are relieved from maintaining separate credentials for all its websites.
Prerequisites
Please make sure your organisation branding is already set under Customization >> Login and Registration Branding in the left menu of the dashboard.
Follow the Step-by-Step Guide given below for Wix Single Sign-On (SSO)
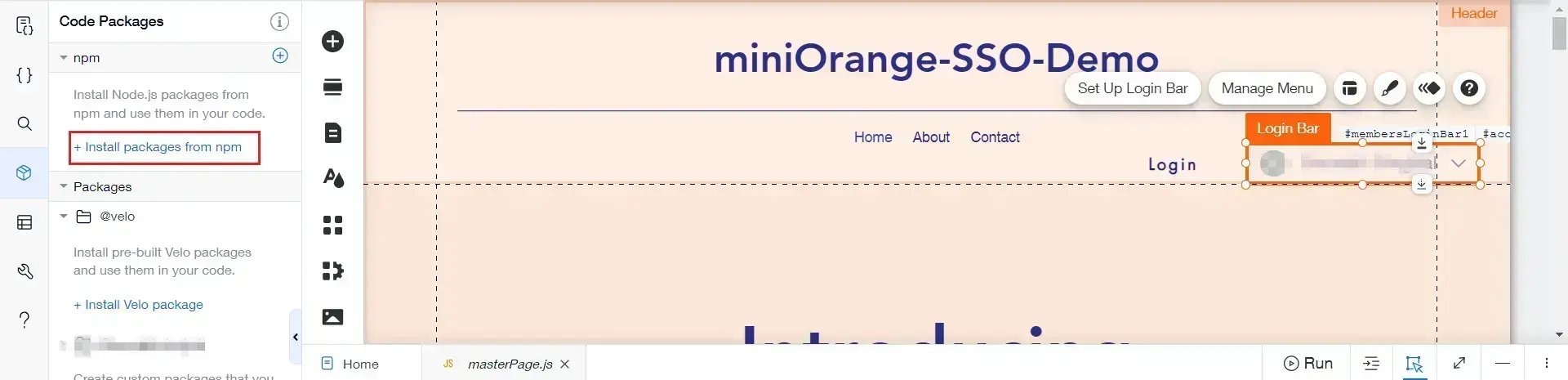
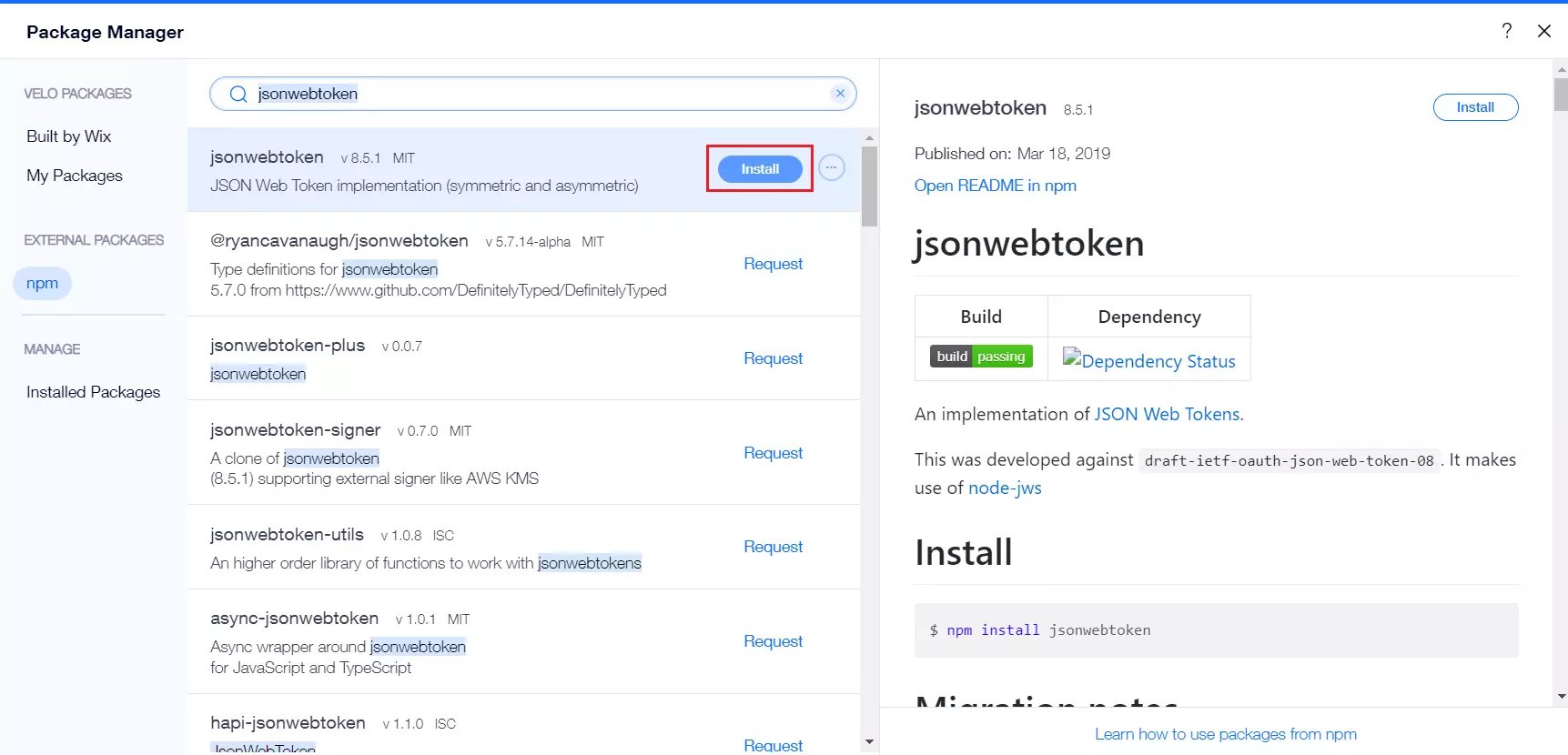
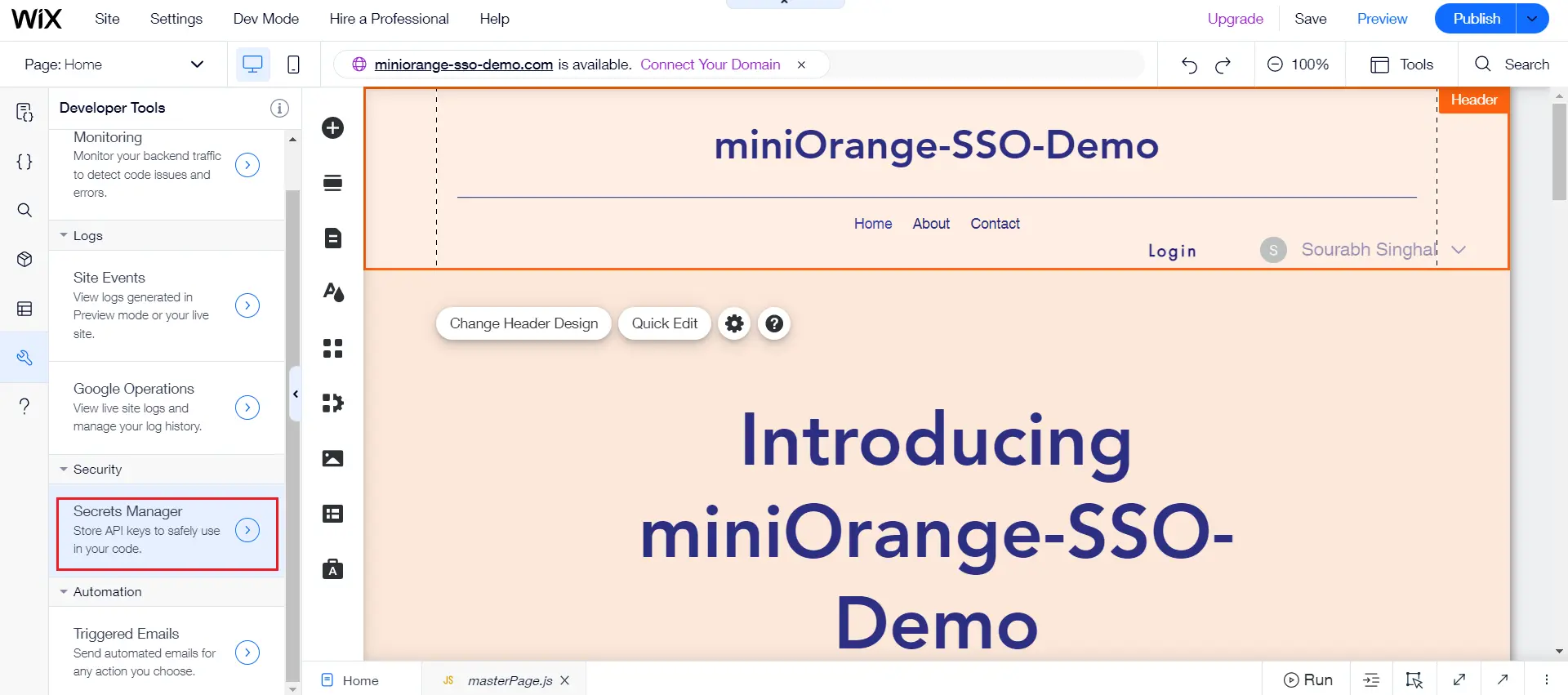
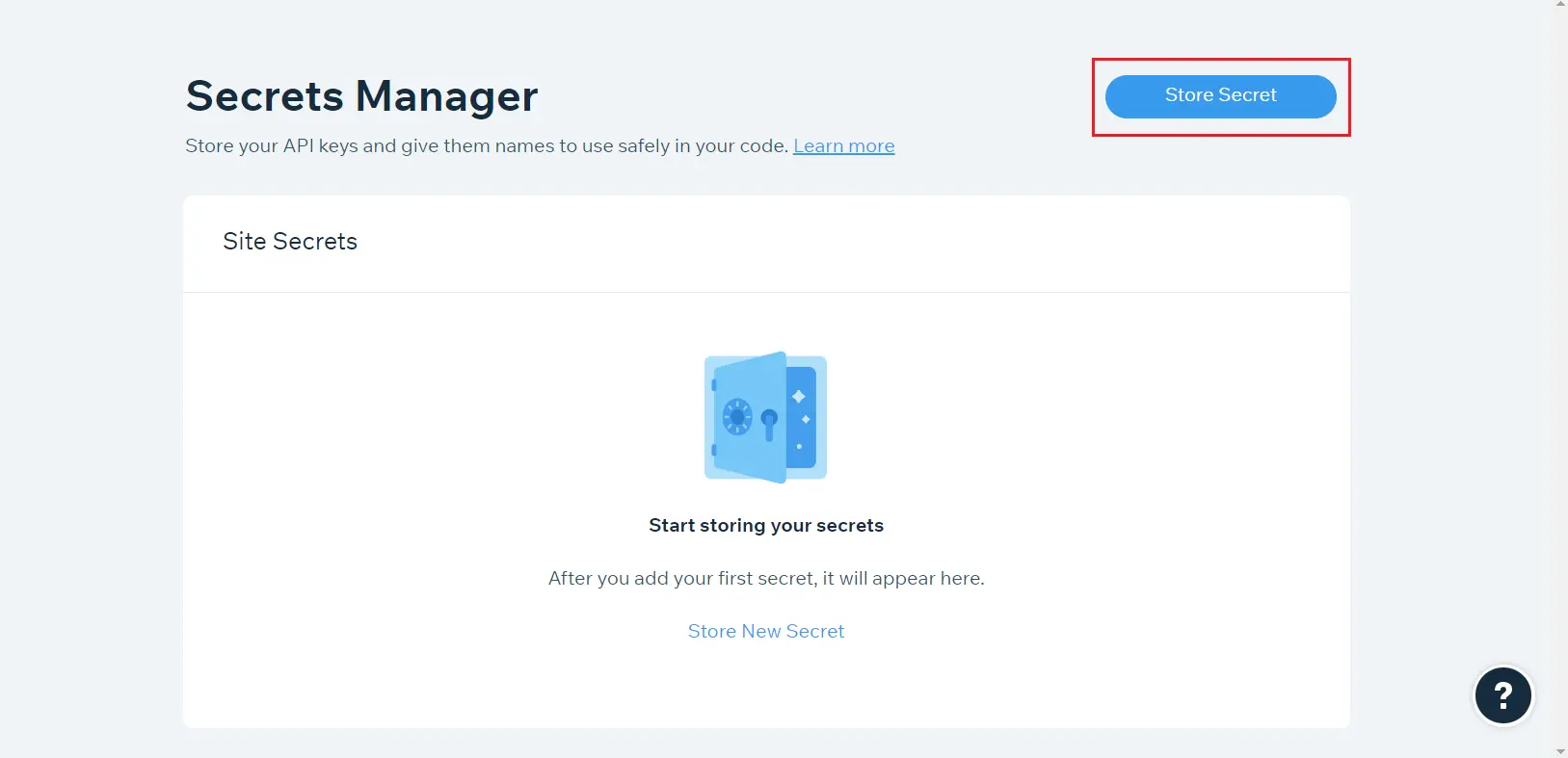
1. Configure Wix to enable SSO
- Log into WIX.
- Create a new site or use an already existing one.
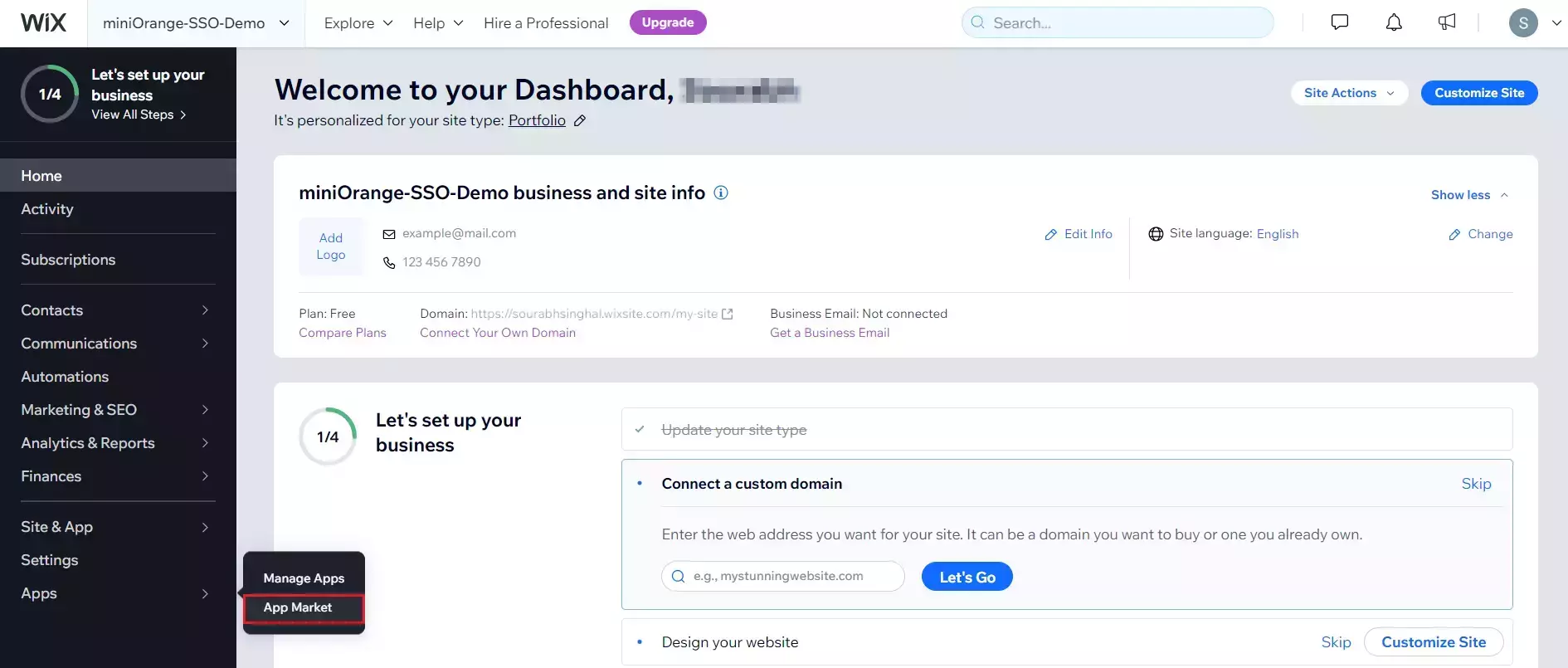
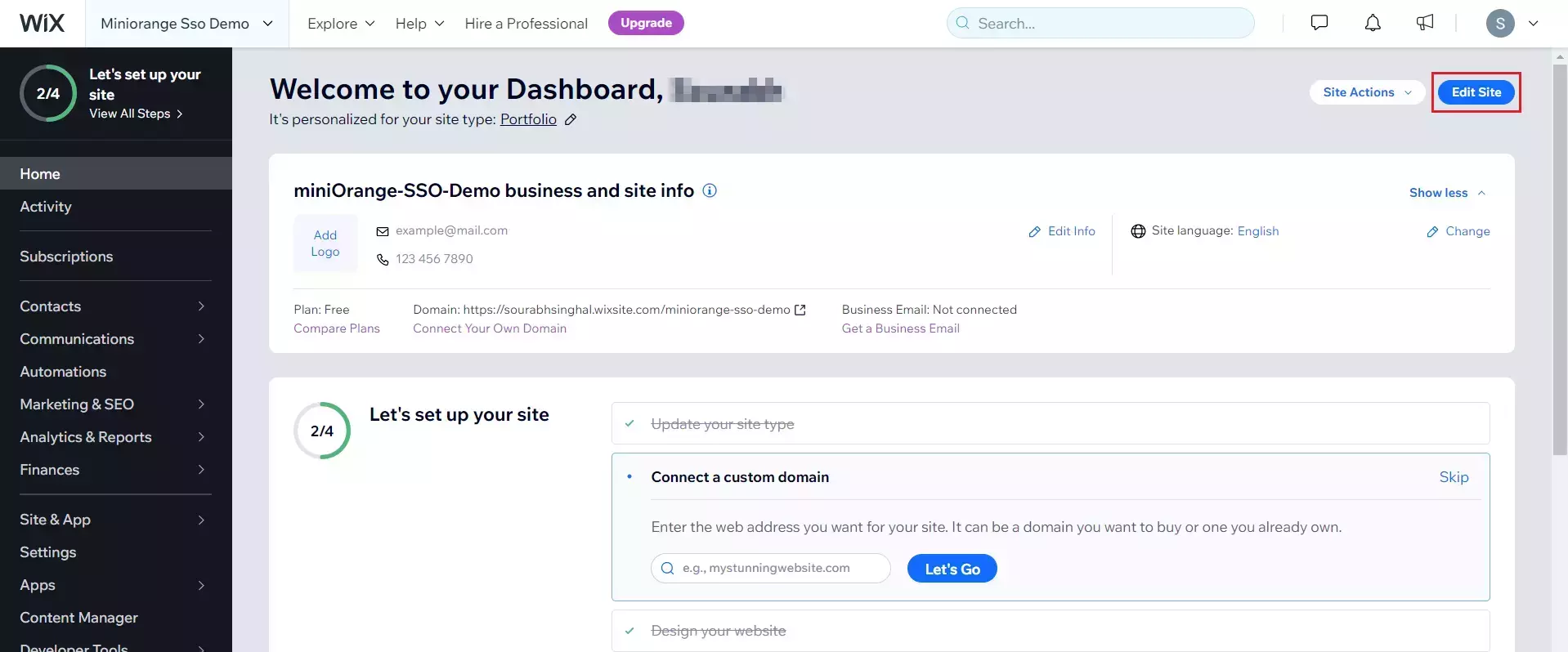
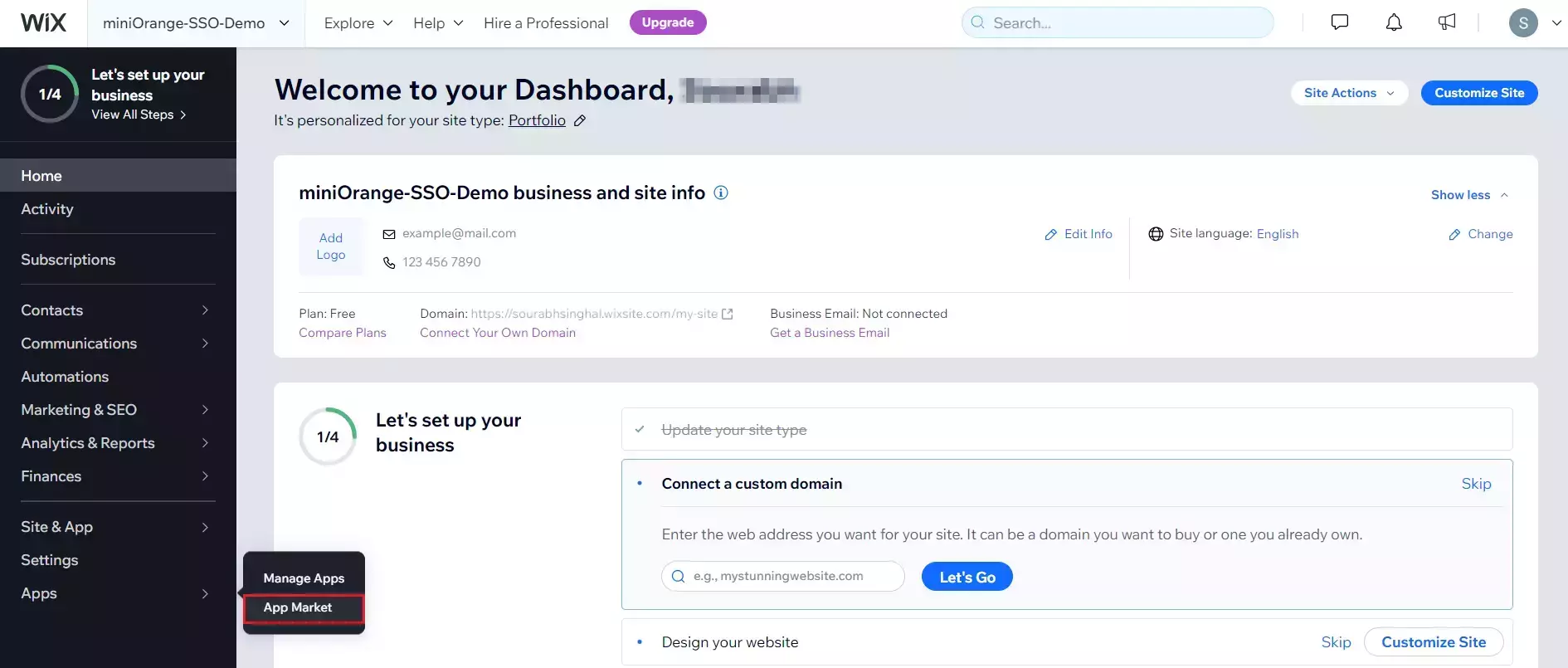
- Go to your website dashboard.
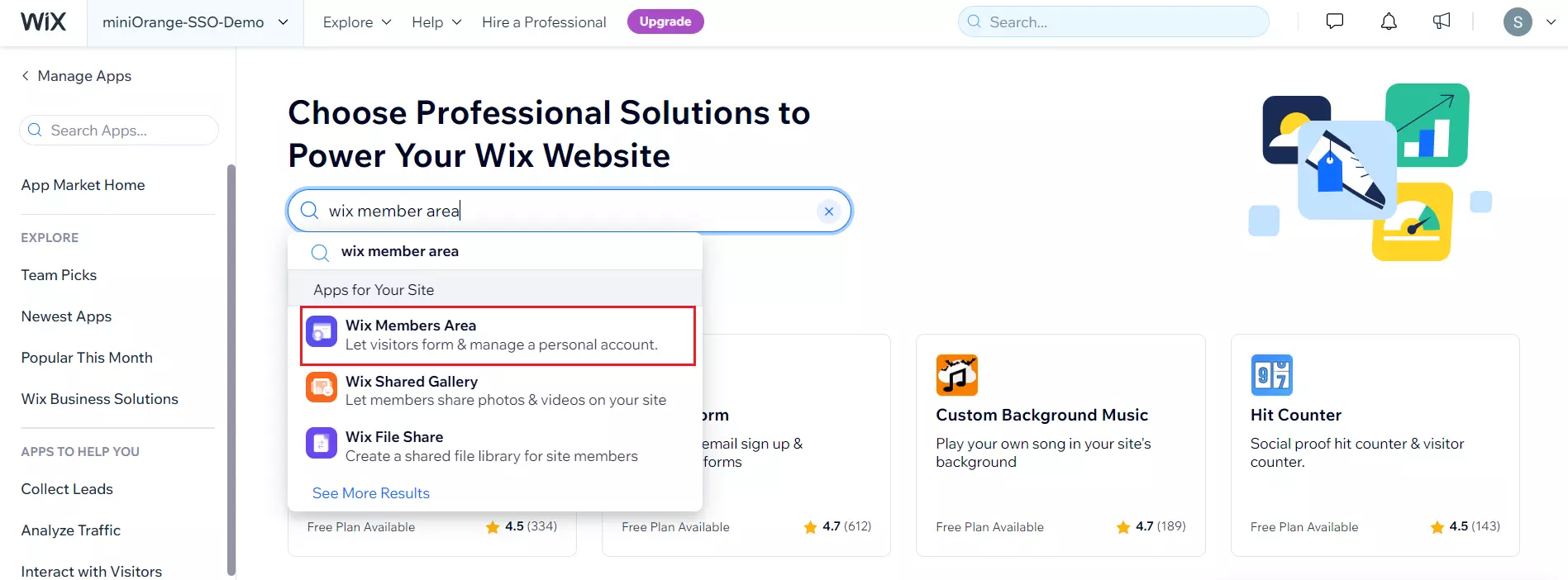
- To add Wix member area App to your website, go to App Market.
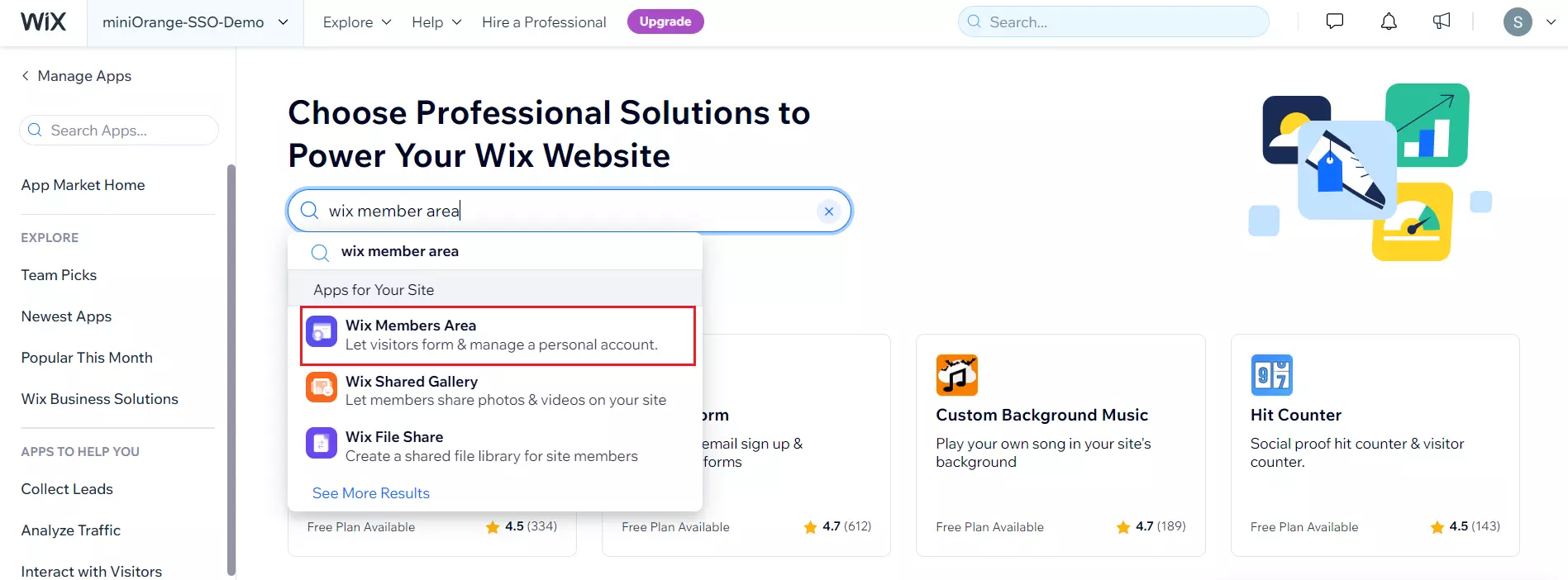
- Search for Wix Member area.
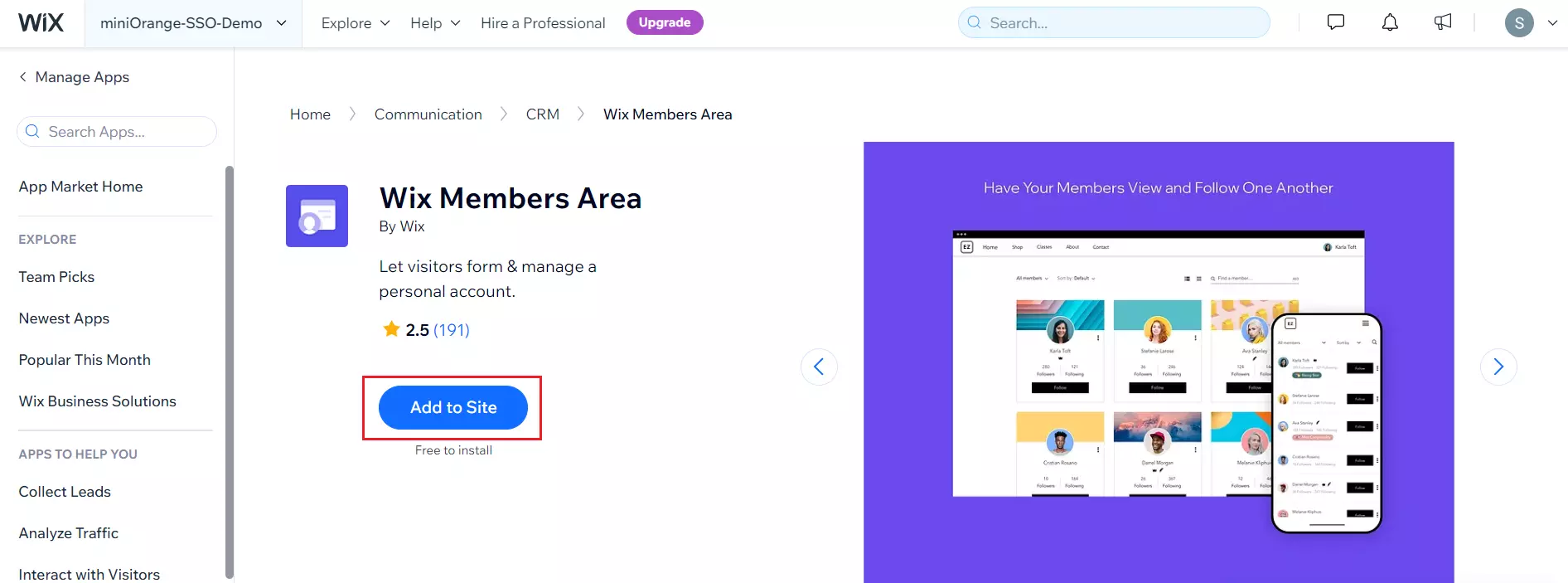
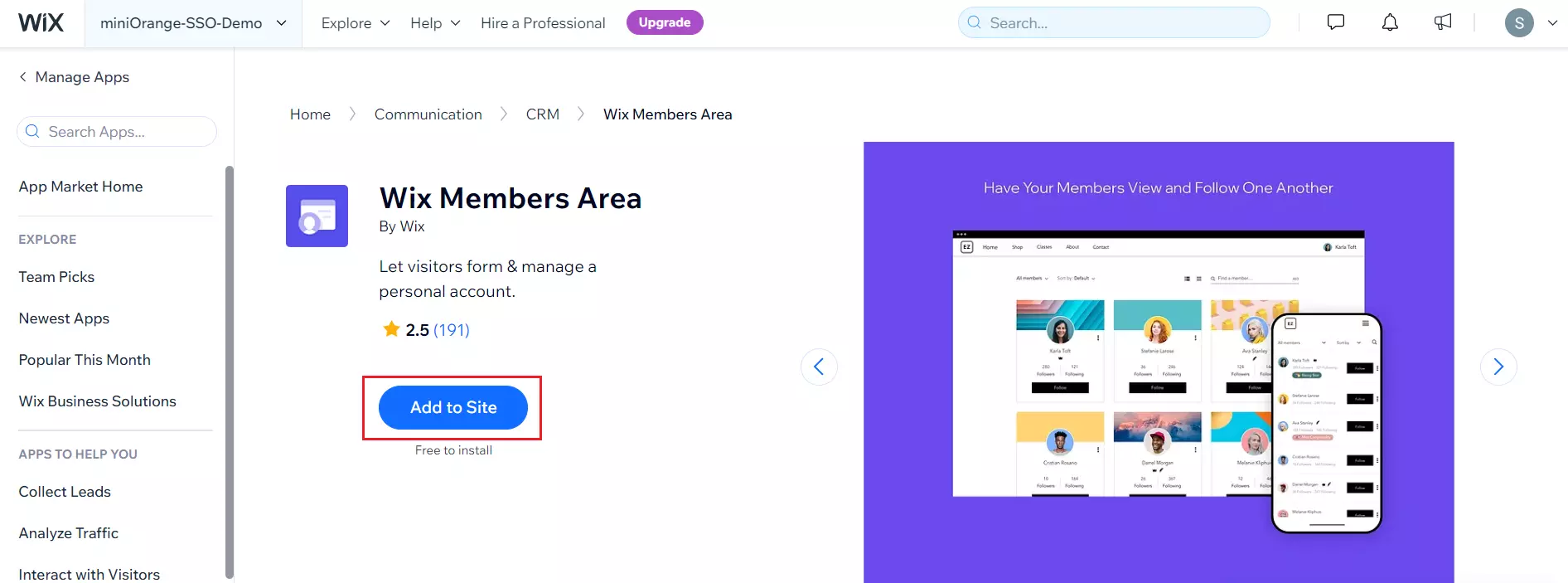
- Open Wix member area app and click on Add to site.
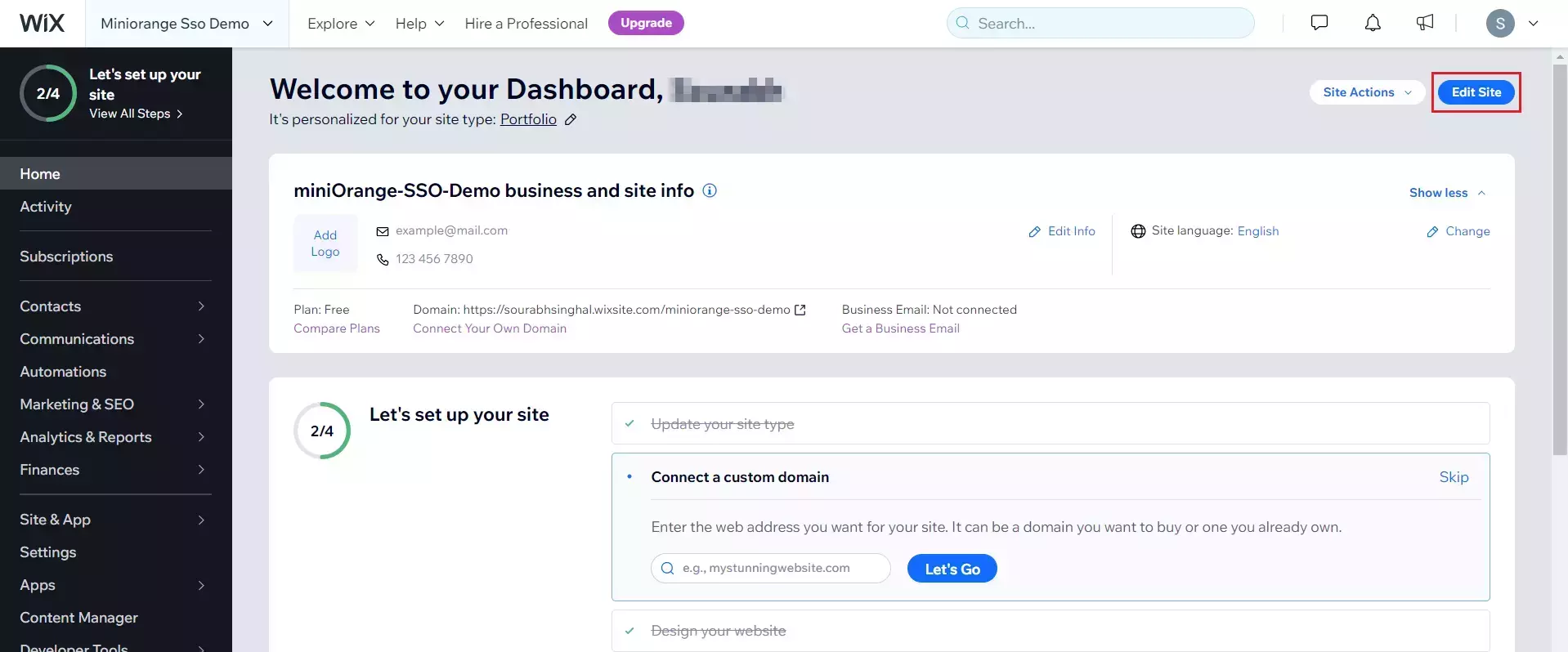
- Navigate to your Website dashboard >> Home tab and click on Edit site.
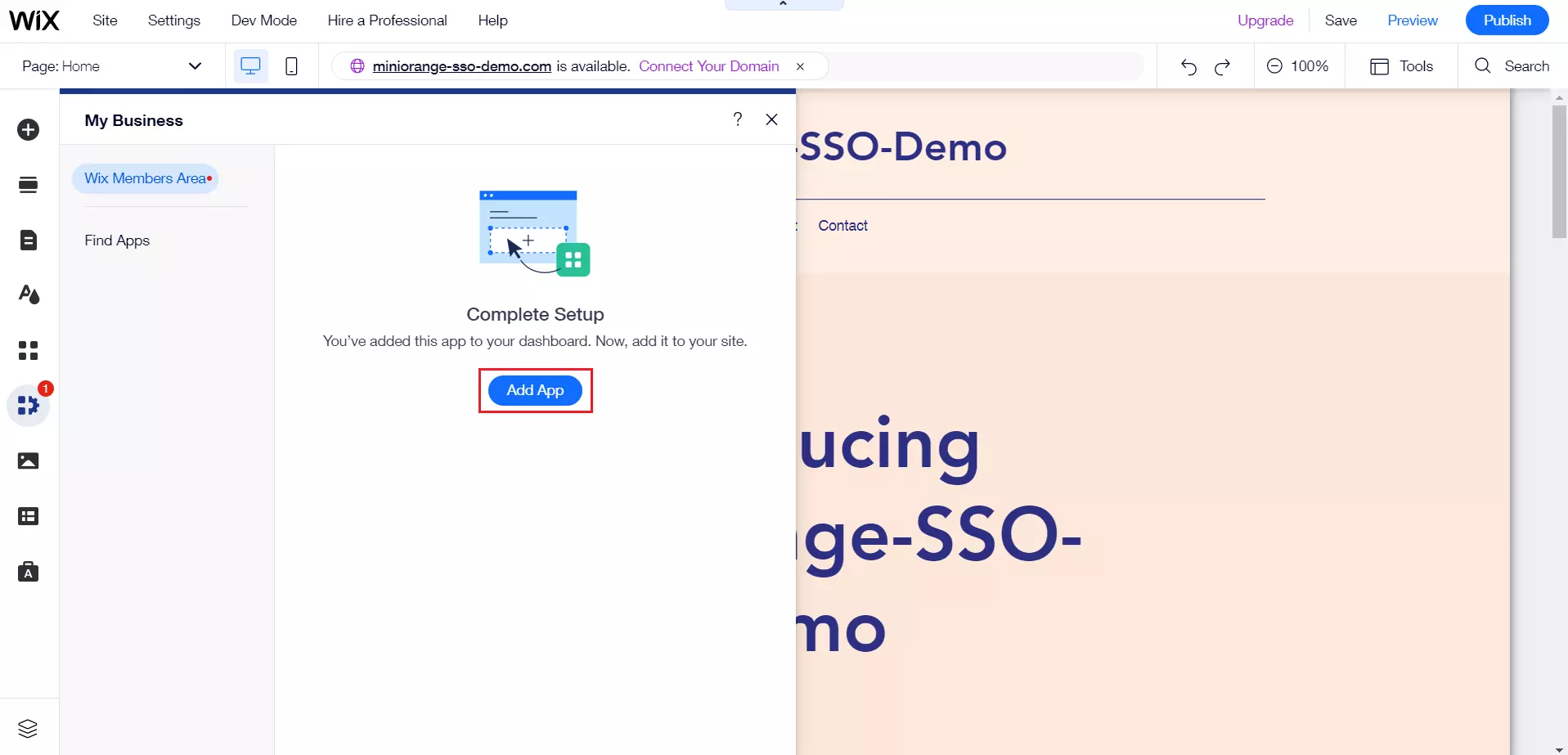
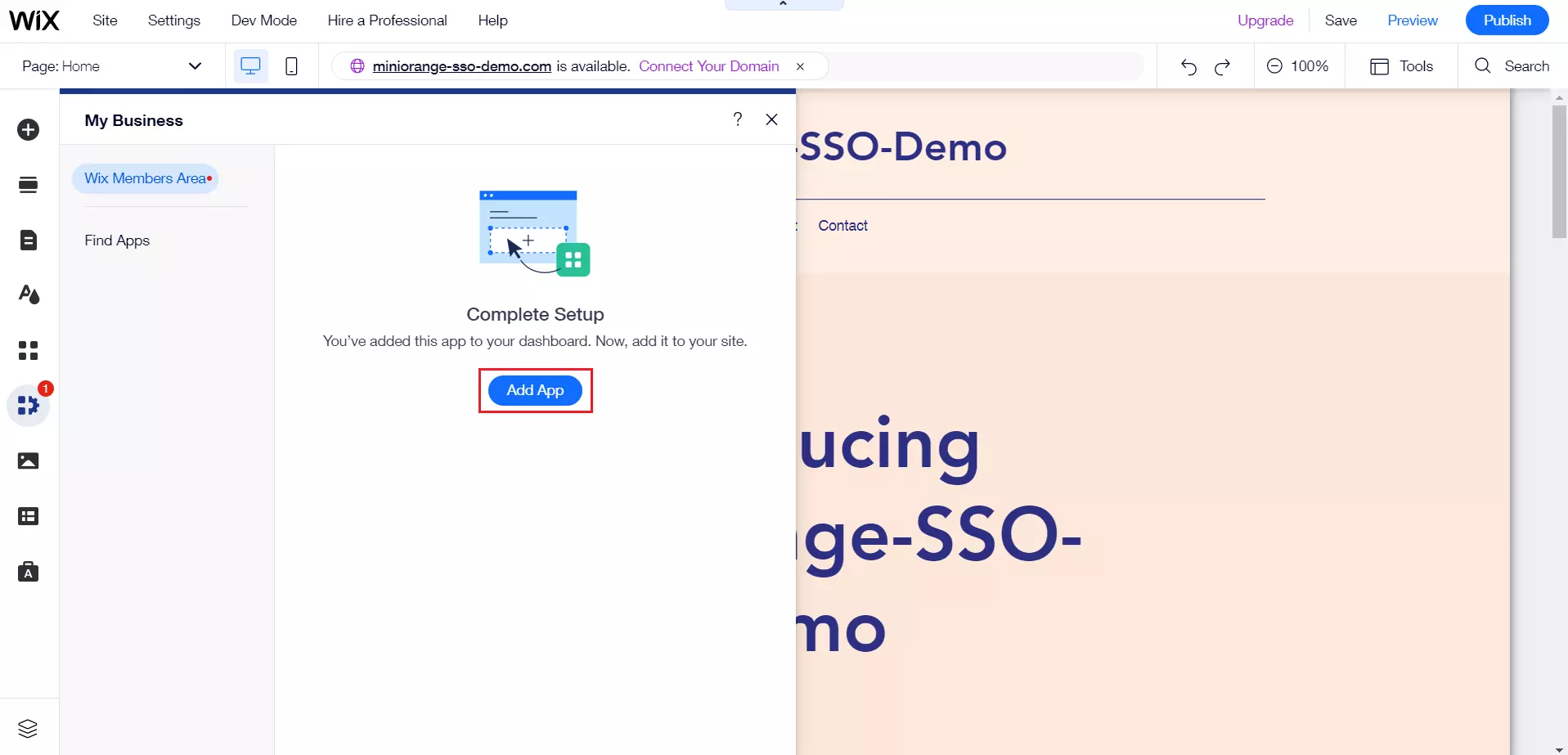
- Go to My business tab in the edit site page and select Wix Member Area.
- Click on Add App.
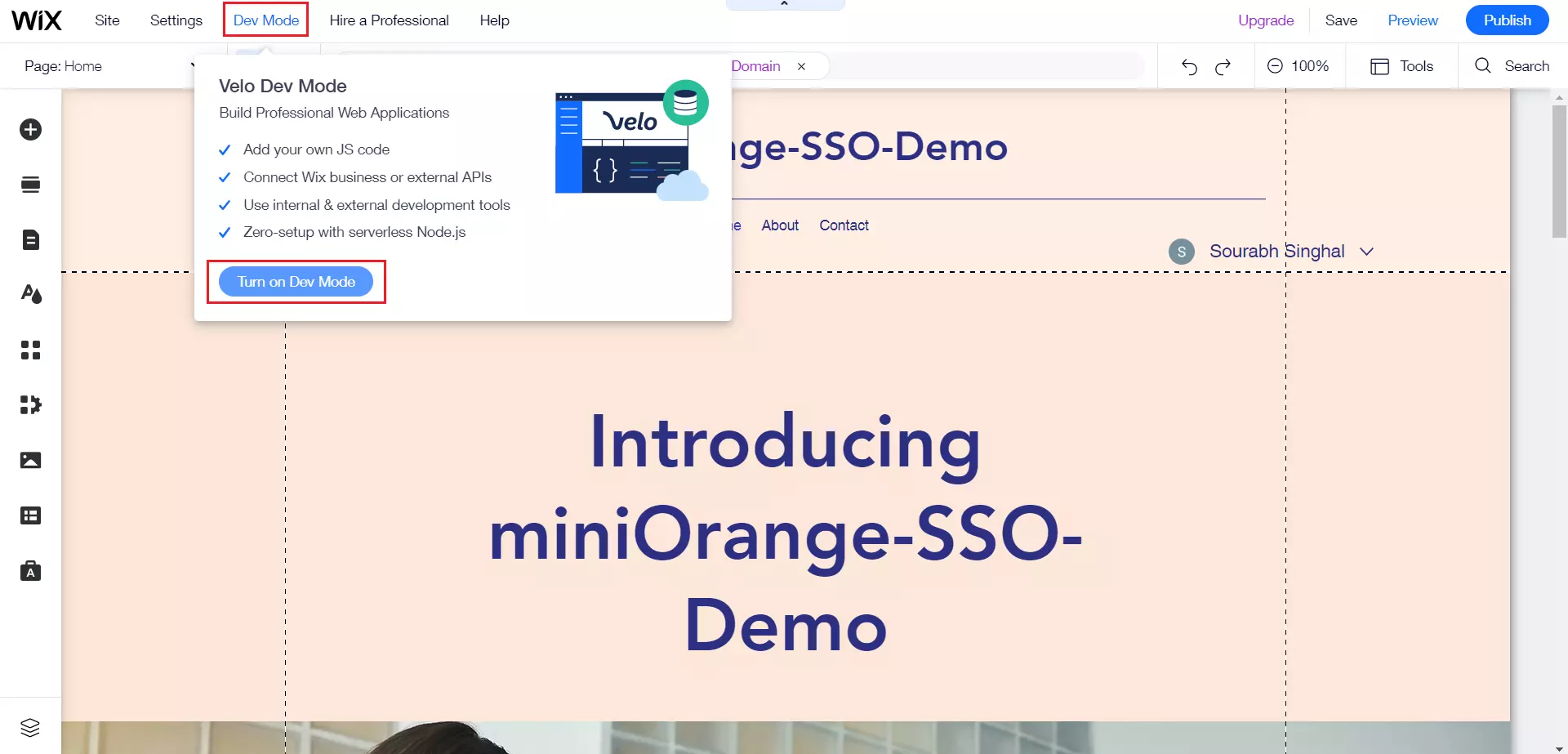
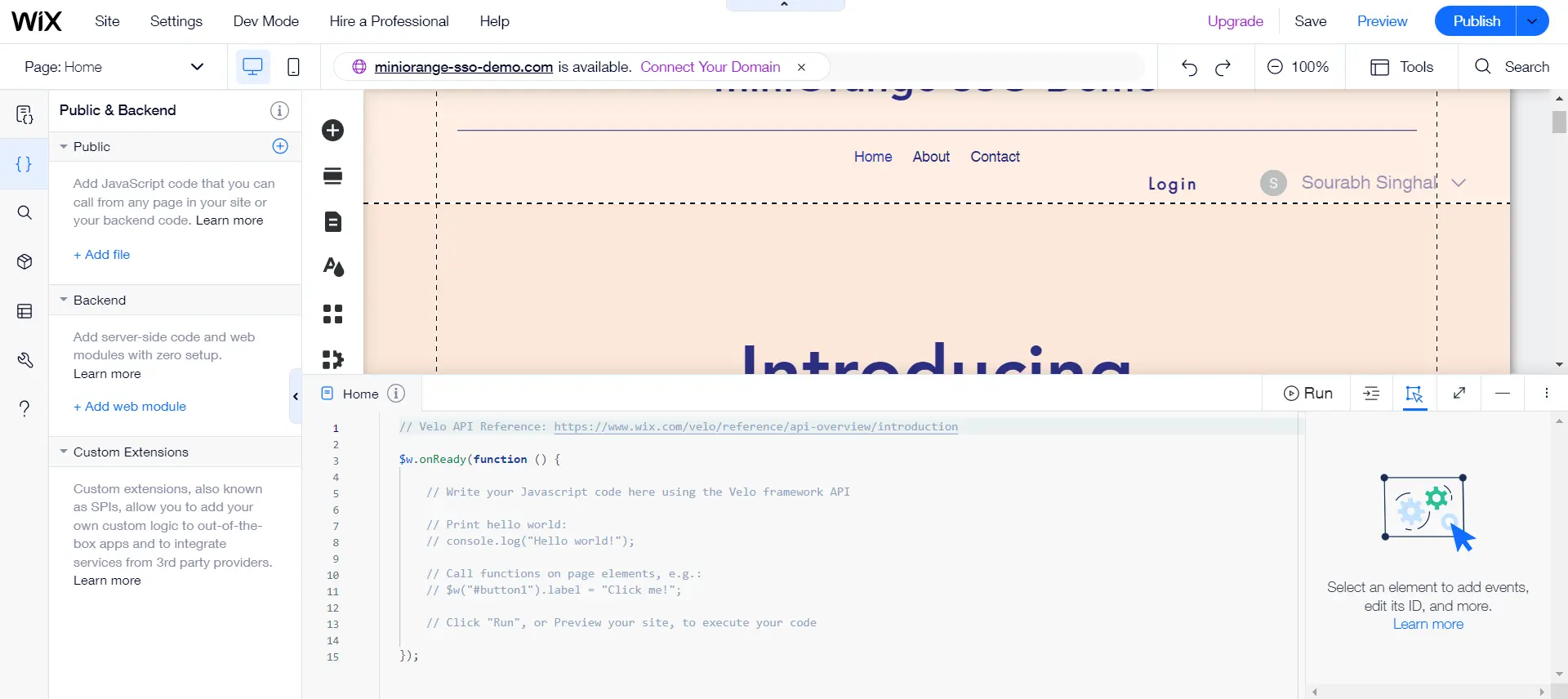
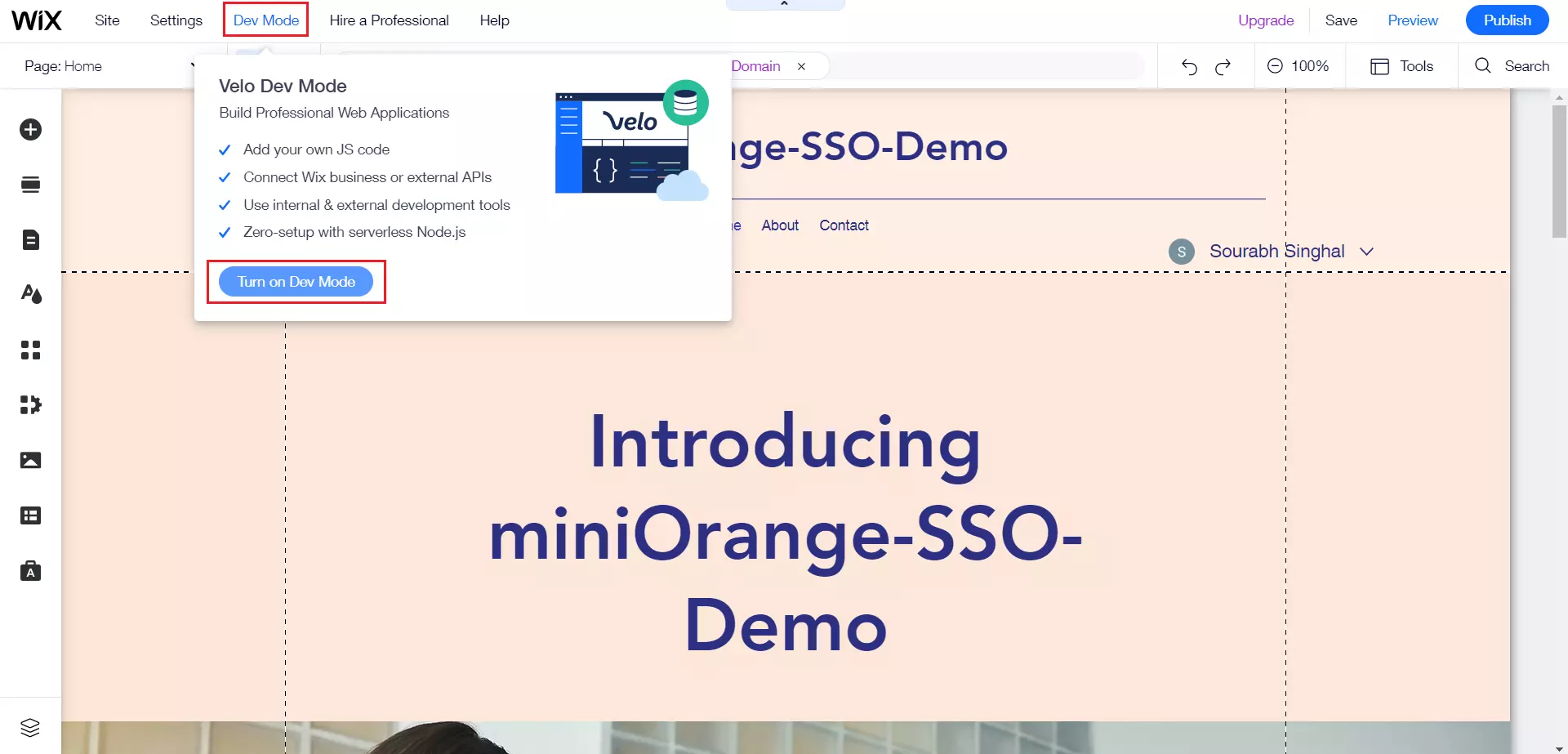
- Click on Turn on Dev Mode.
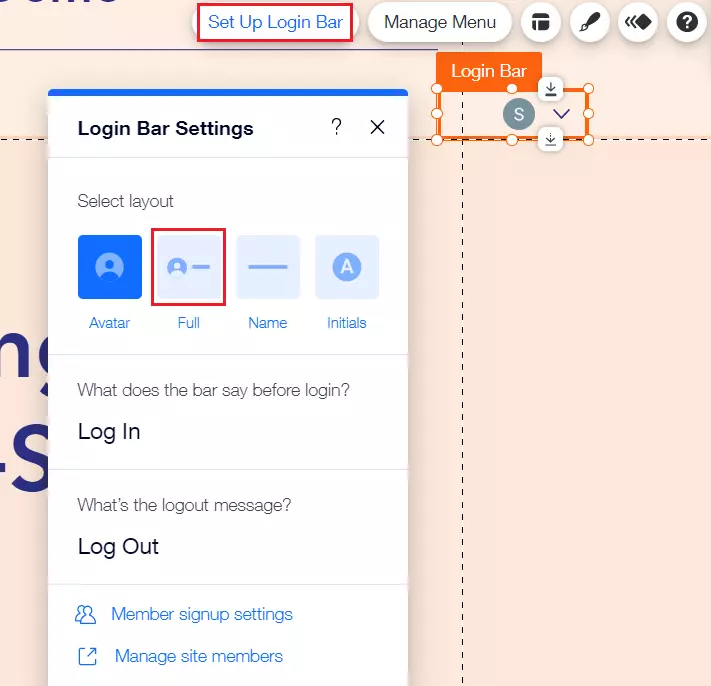
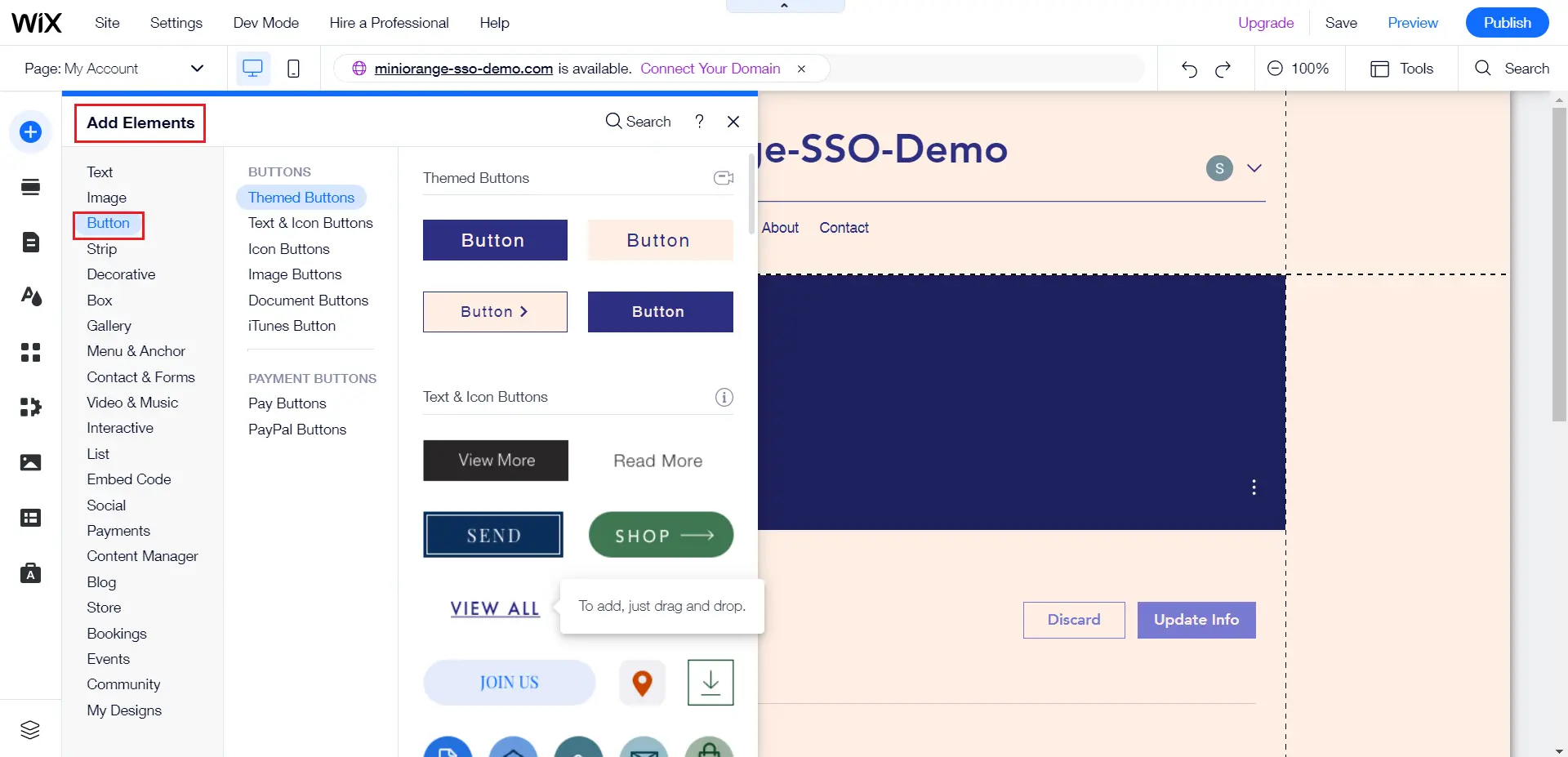
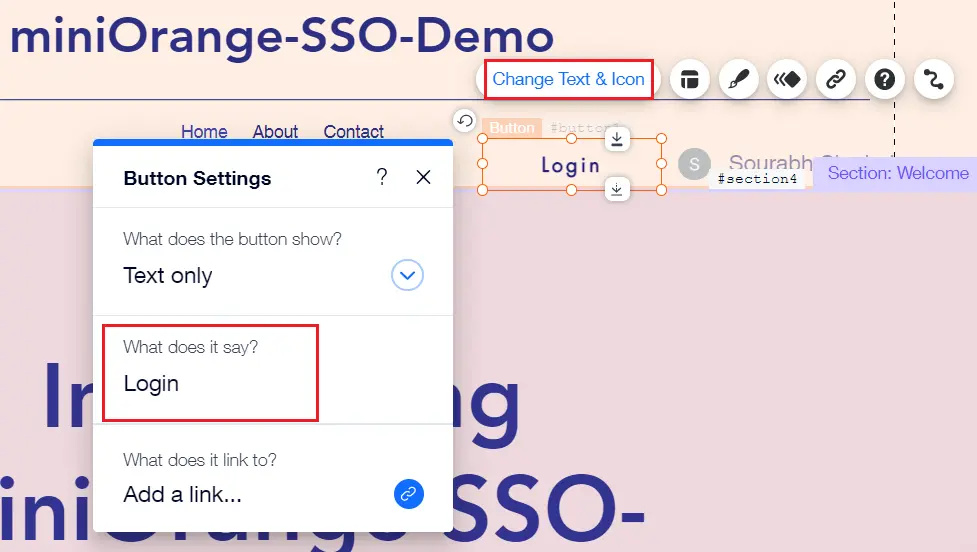
- Edit Login Bar.
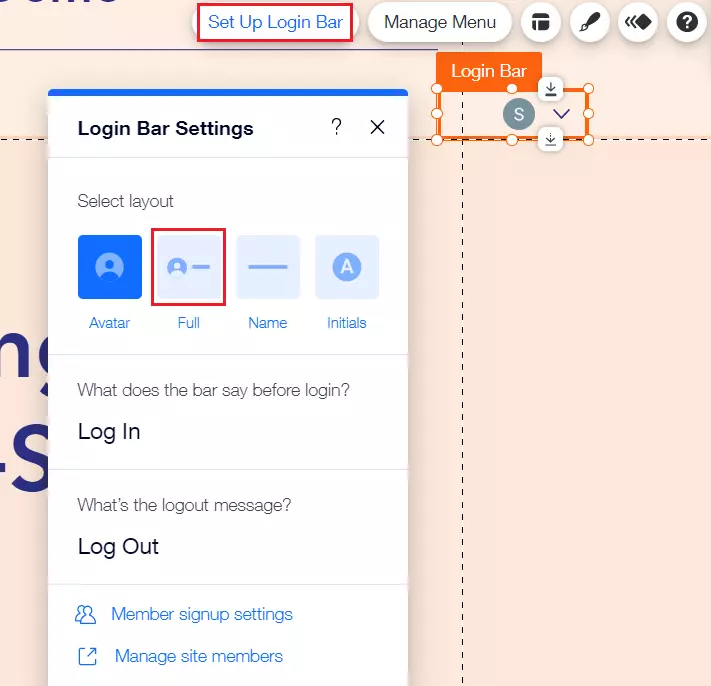
- Click on setup login bar and Select Full, then Drag and resize the login bar as per your requirements.
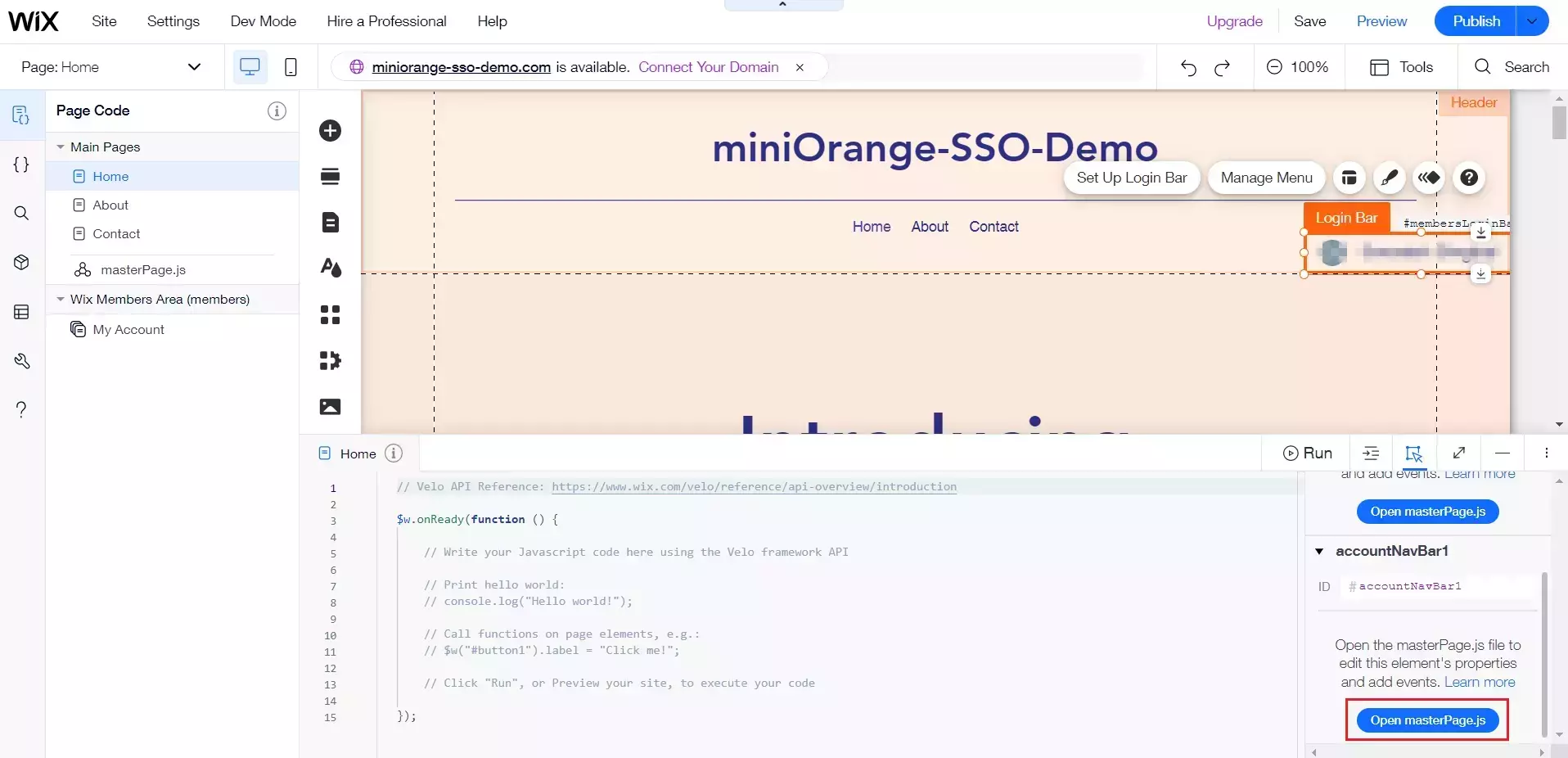
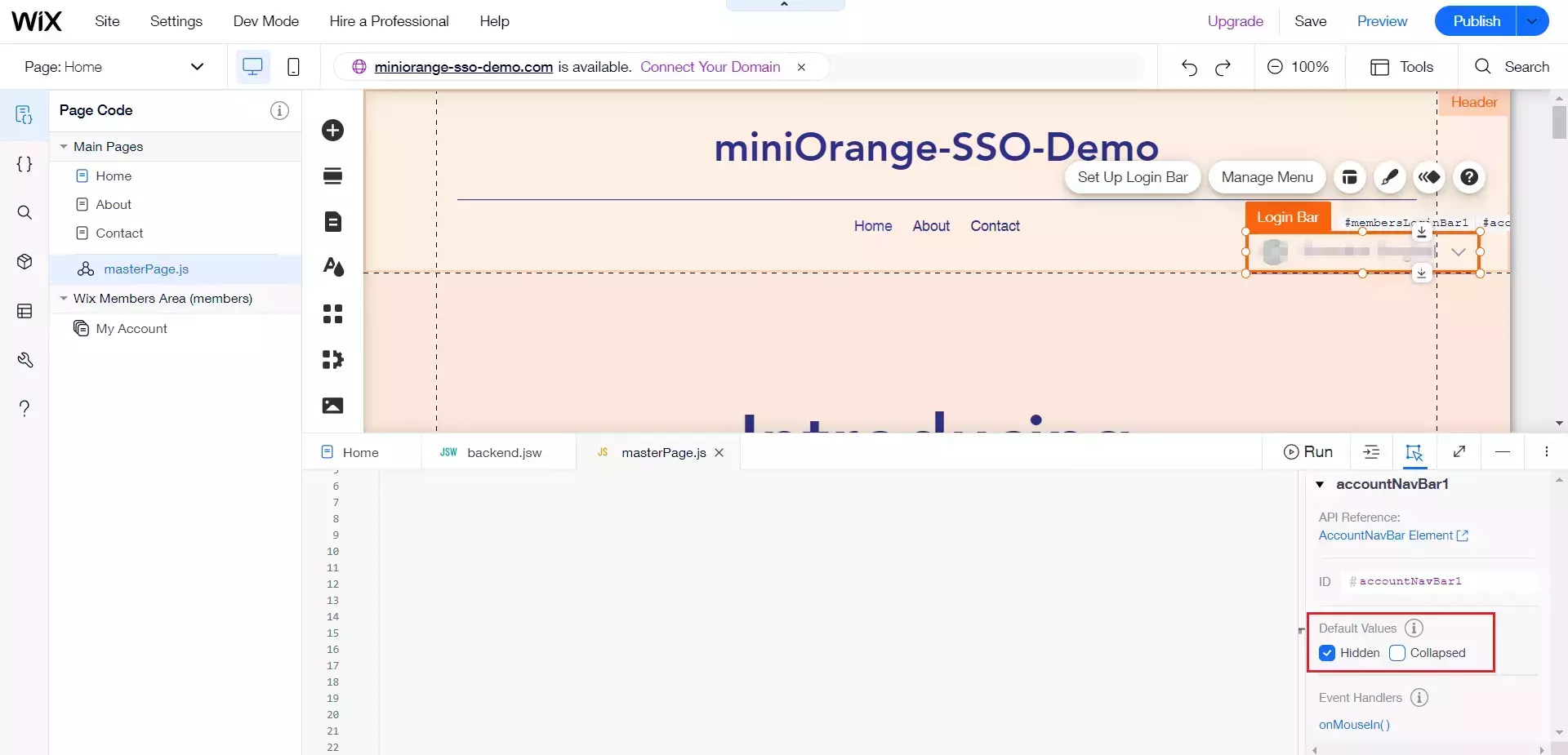
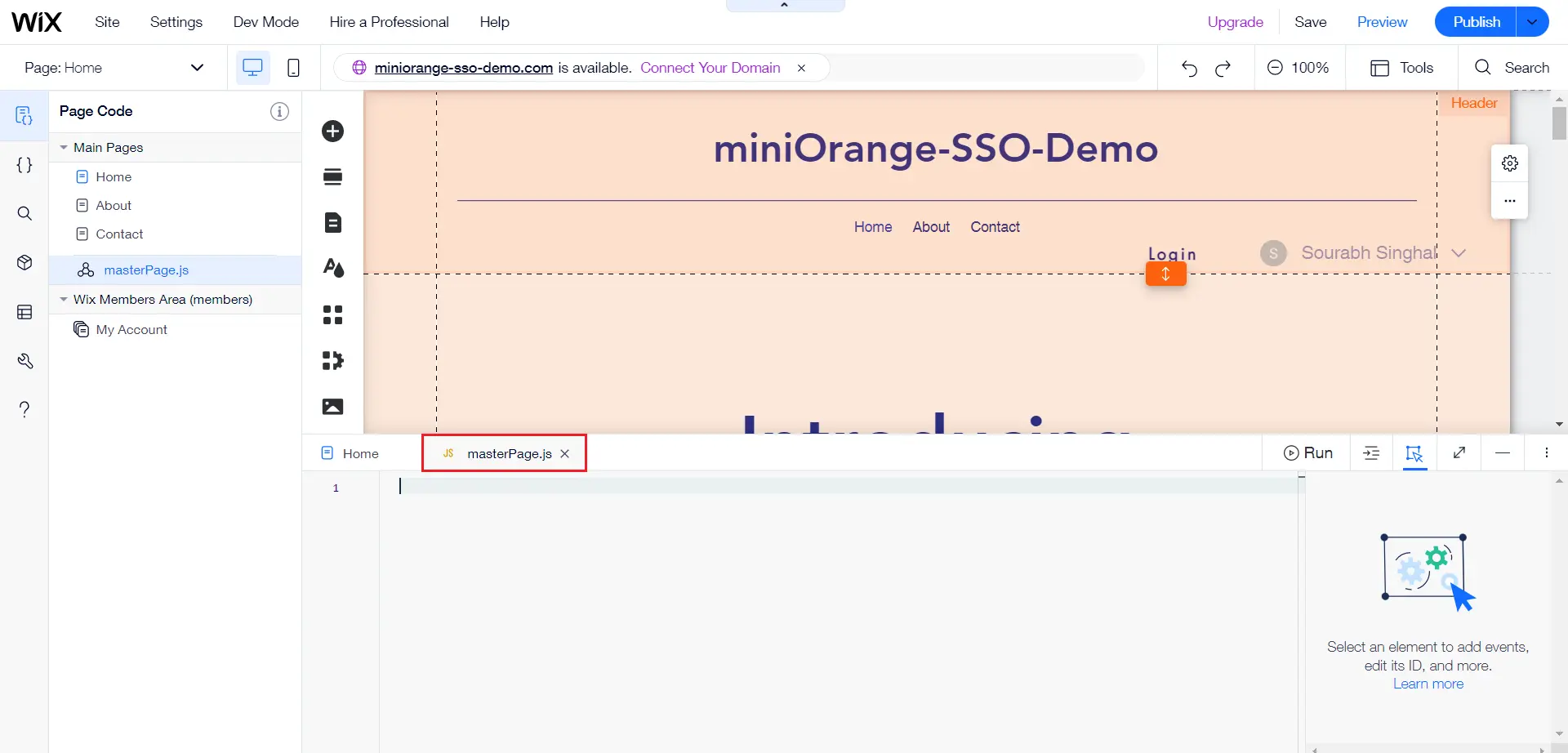
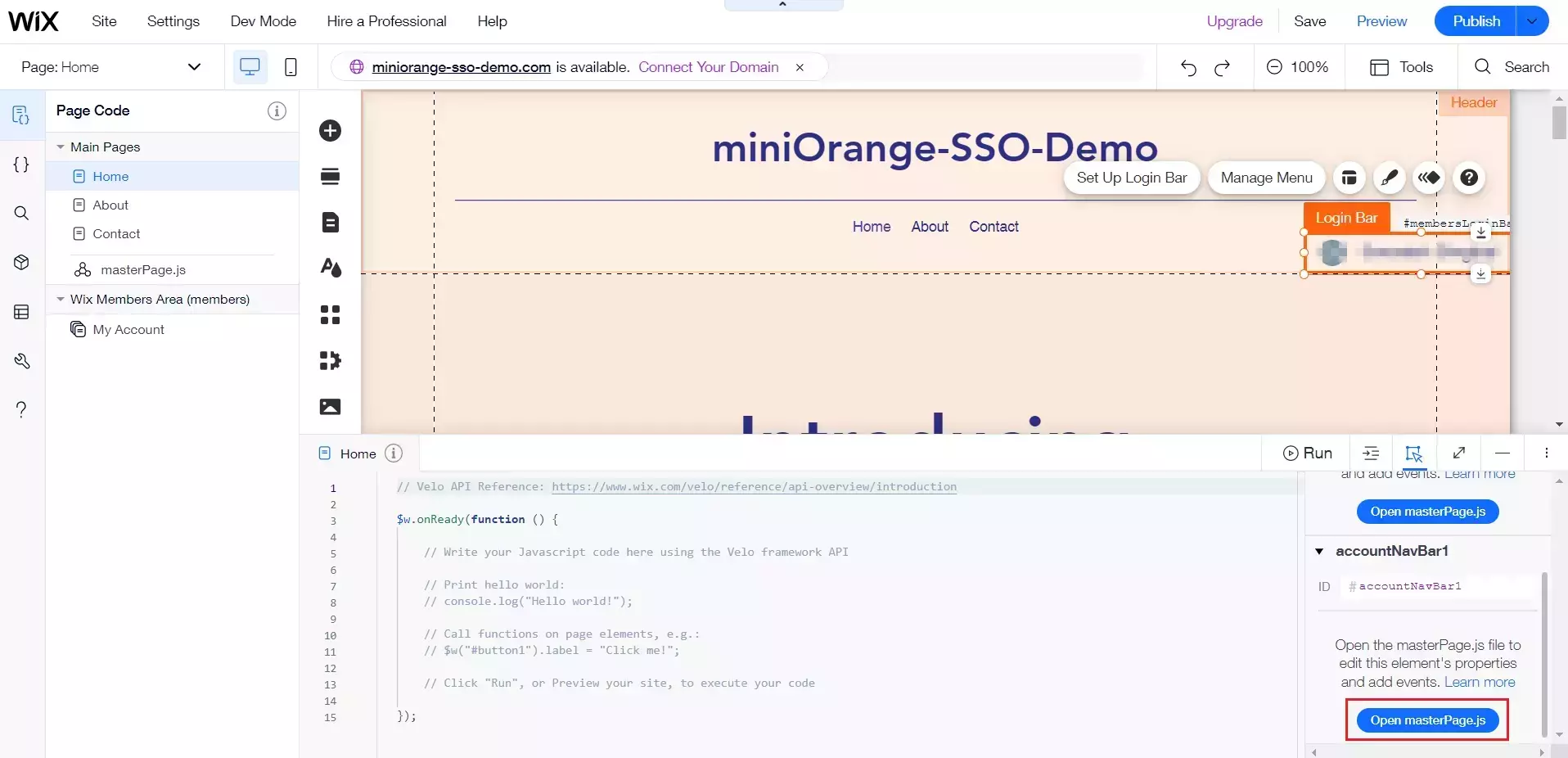
- Click on Open masterPage.js for accountNavBar1.
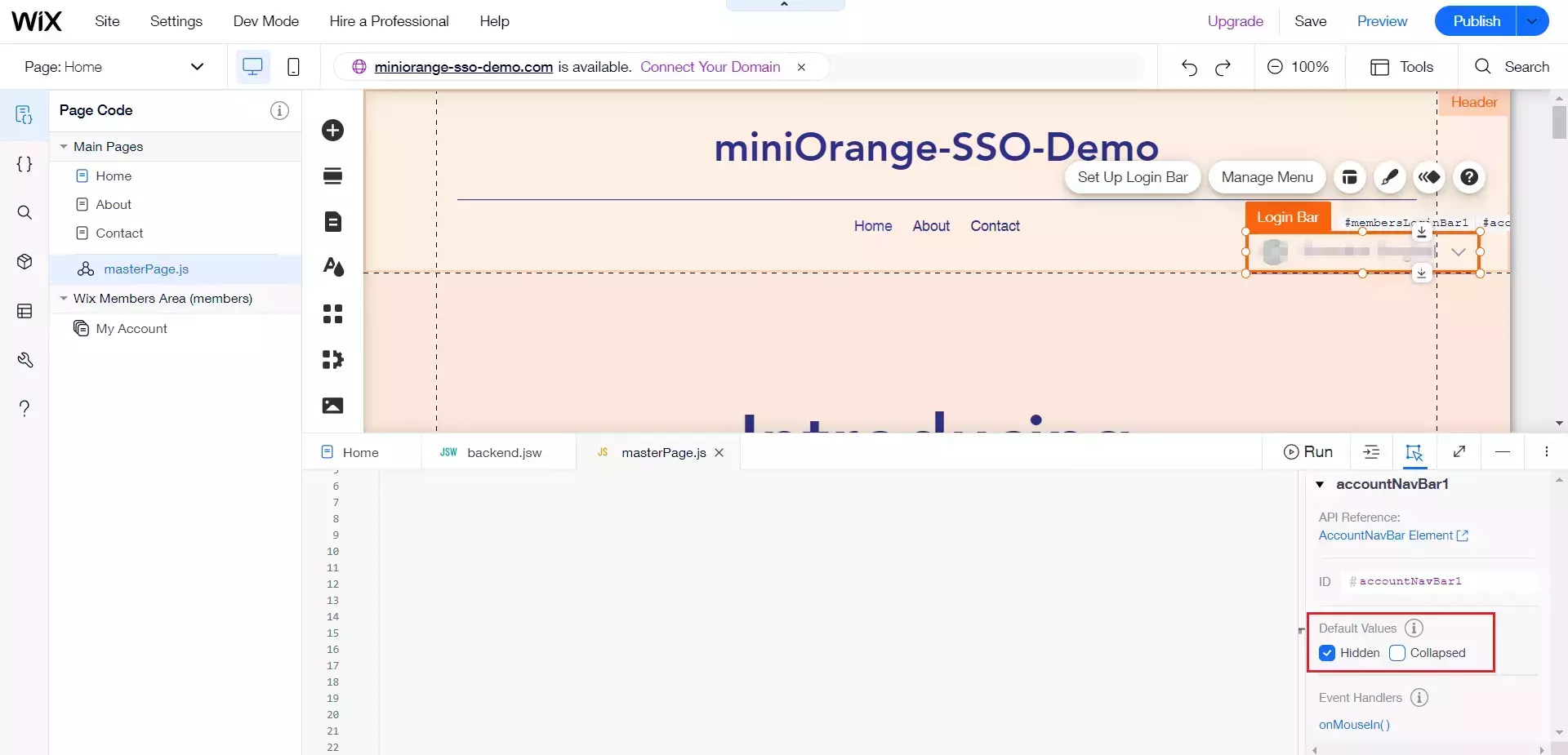
- Enable hidden for accountNavBar1 Default values.
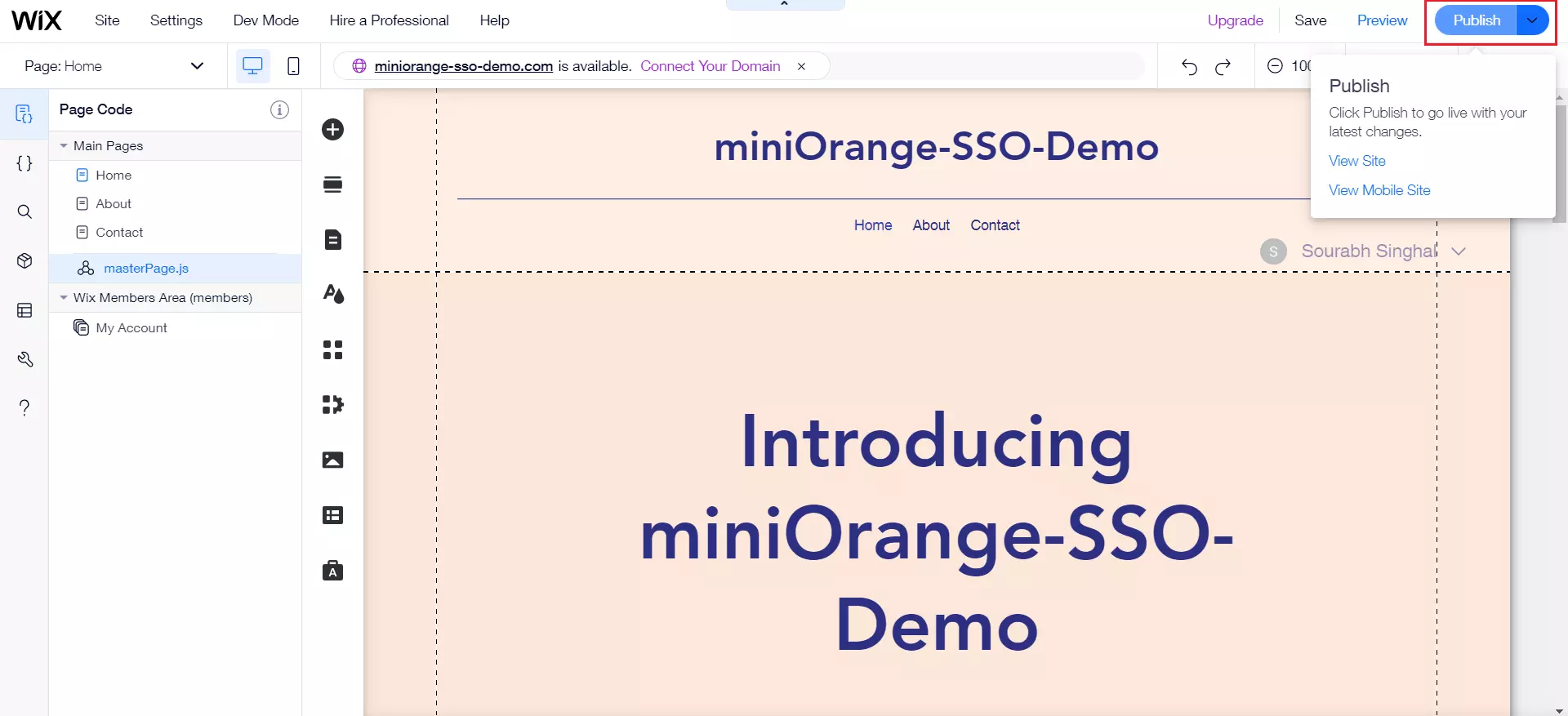
- Now to publish the website, click on Publish.
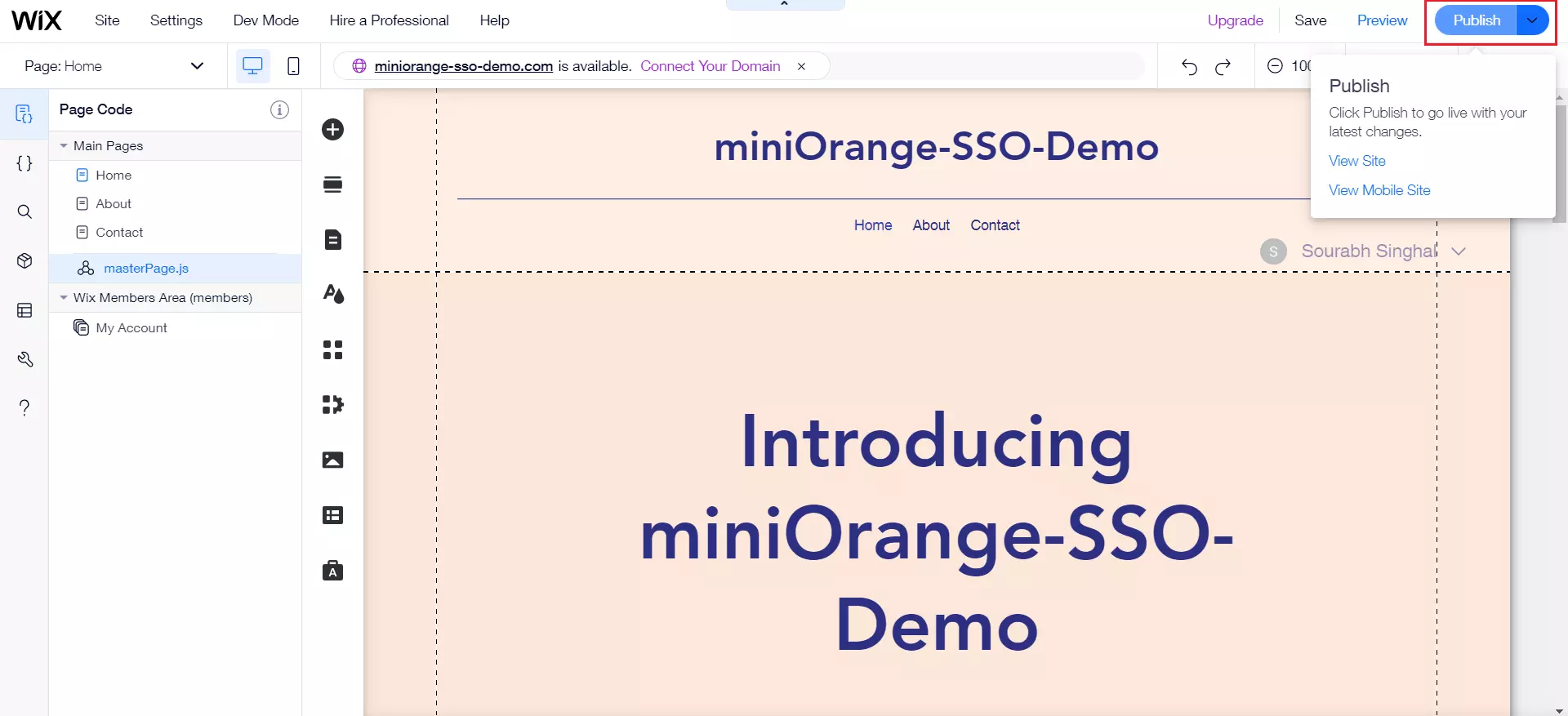
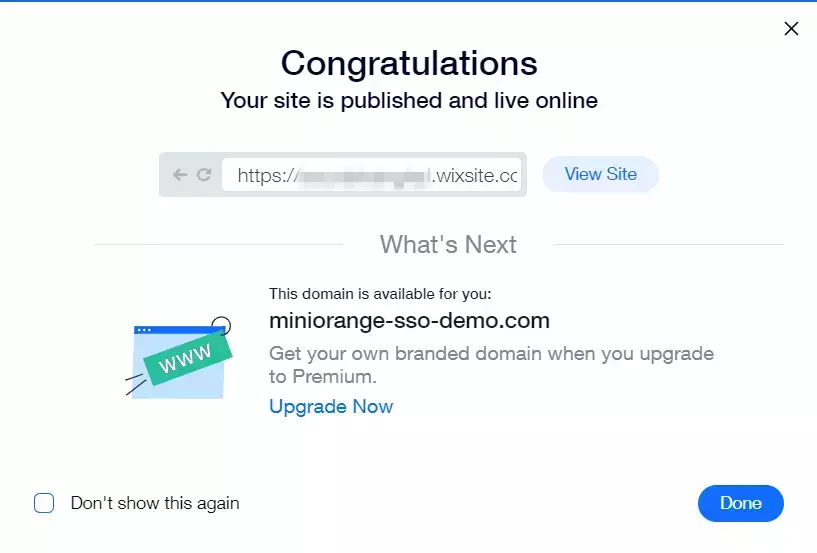
- After publishing is successful, a dialog box will open. Copy your site link from this dialog box.
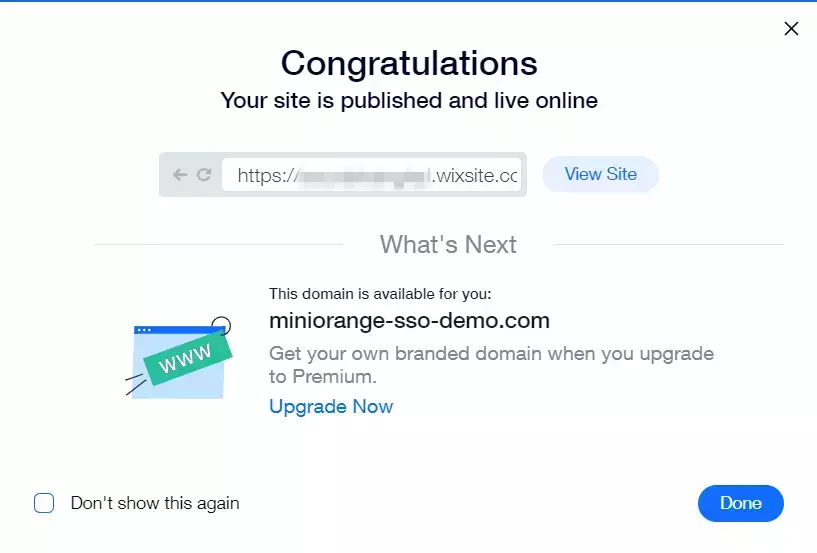
2. Configure Wix in miniOrange
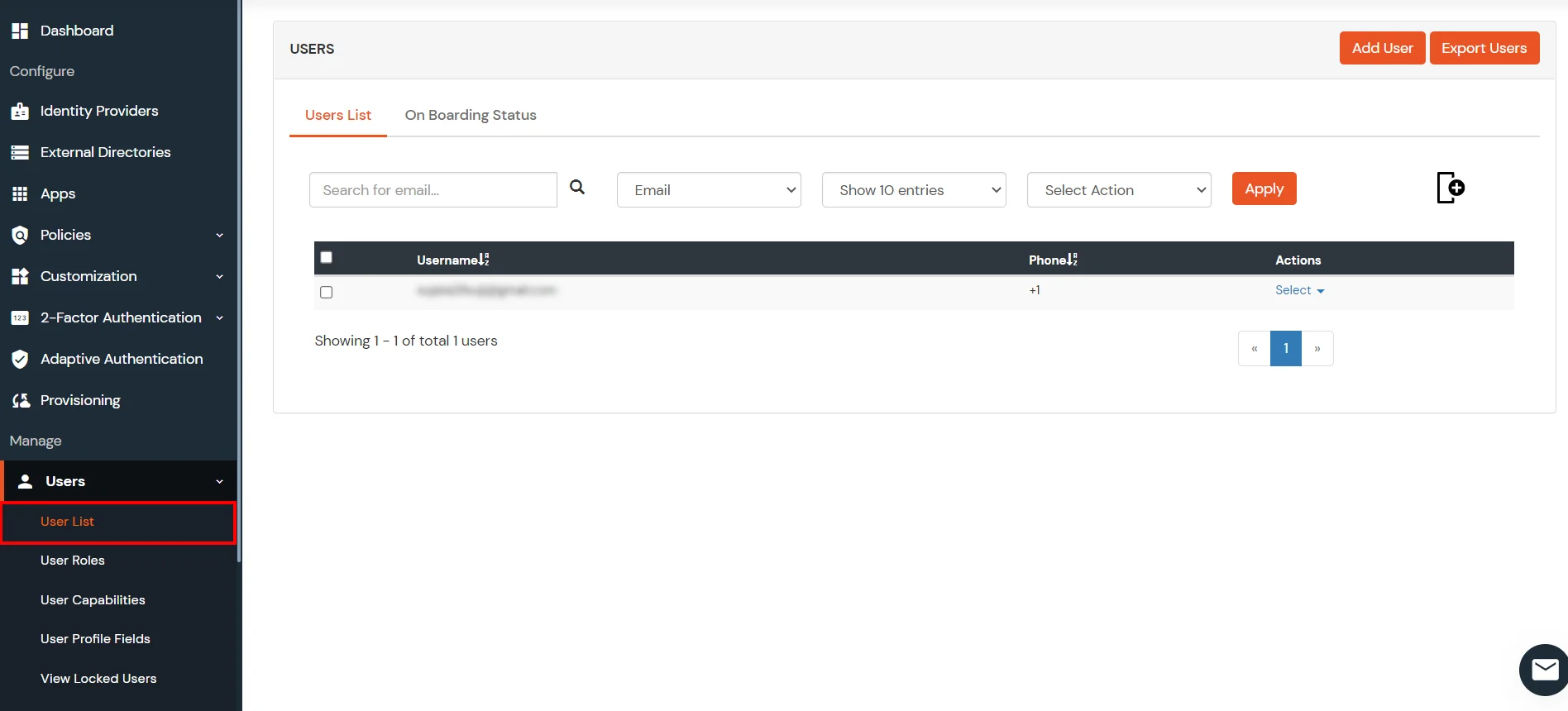
- Login to miniOrange Admin Console.
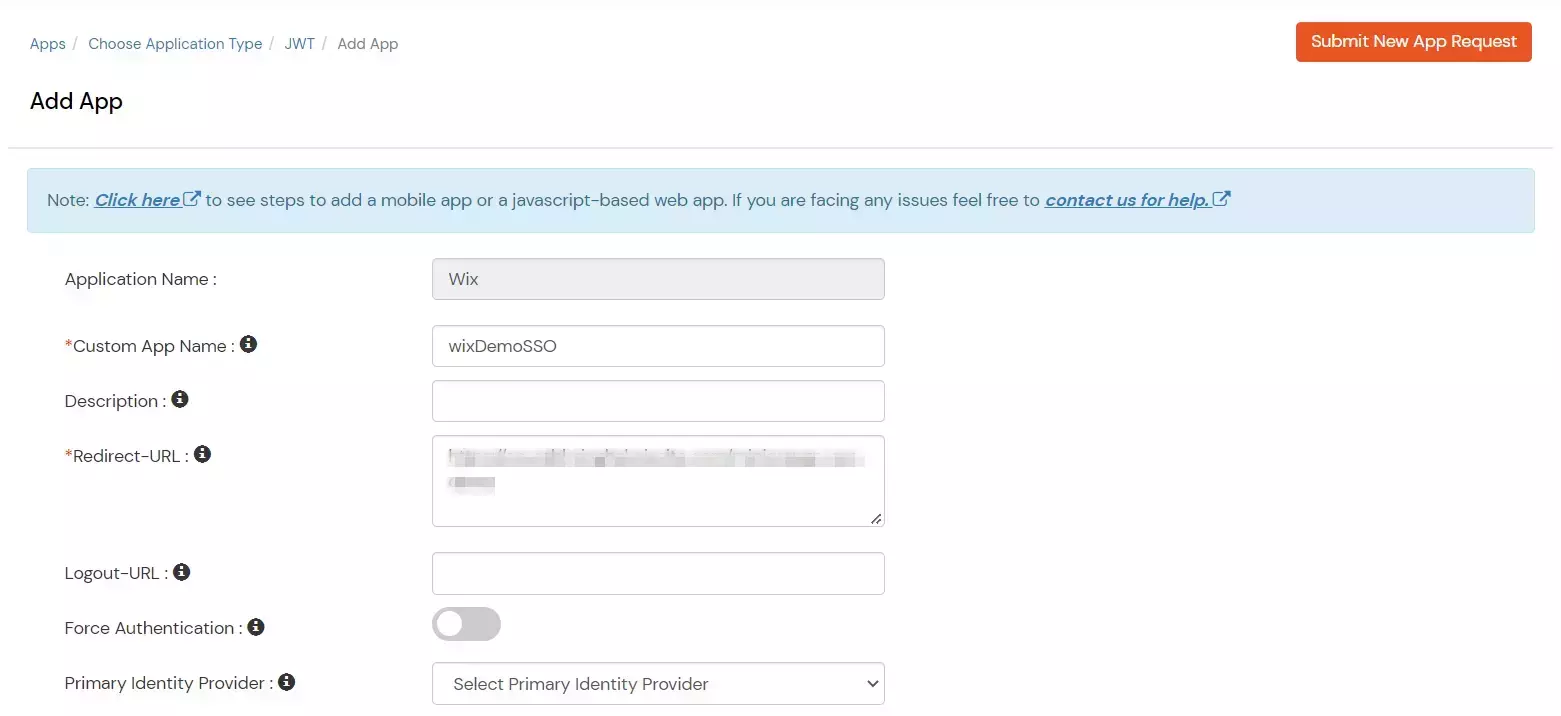
- Go to Apps Click on Add Application button.

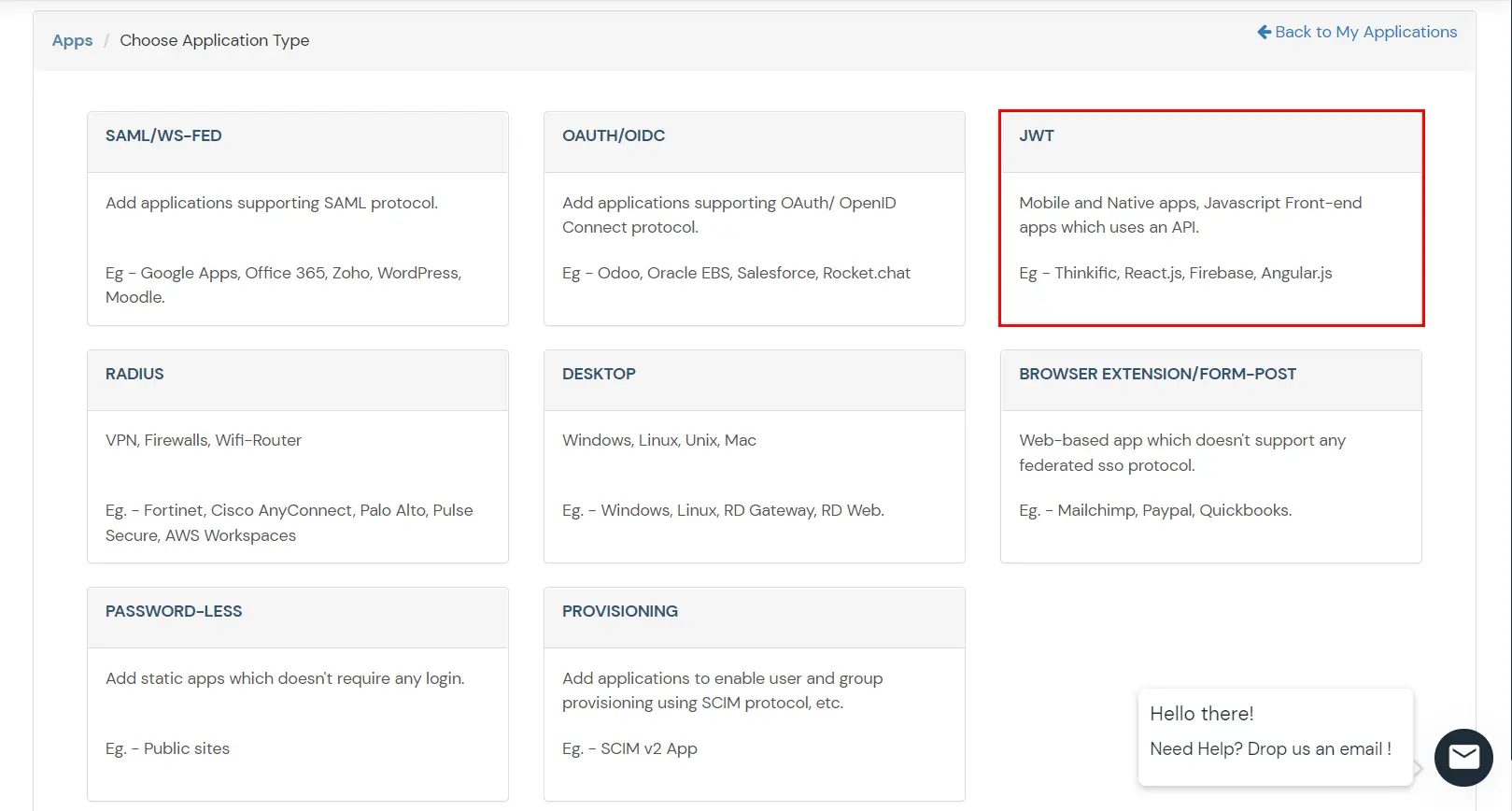
- Under the Choose Application Type, click on JWT.
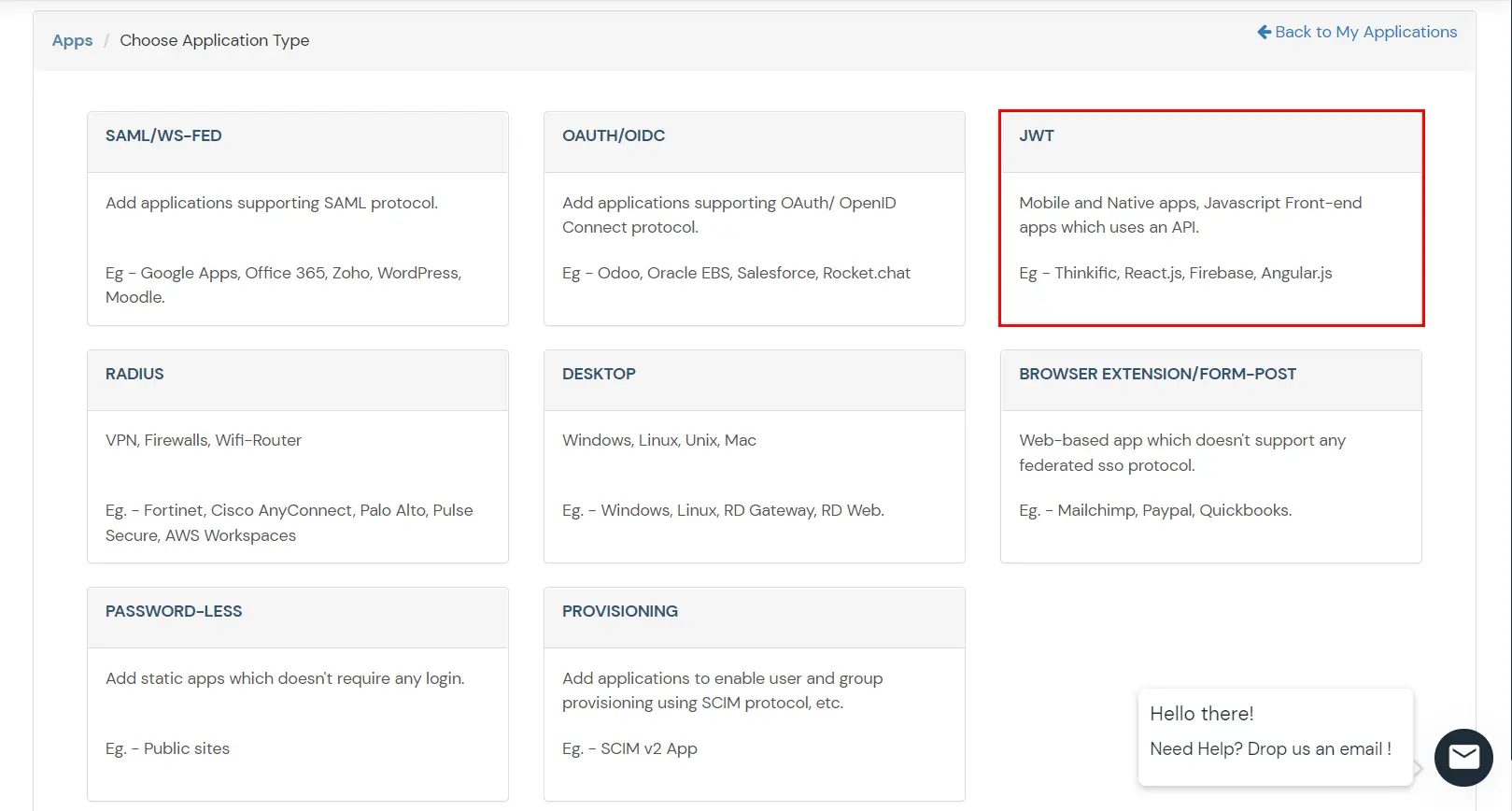
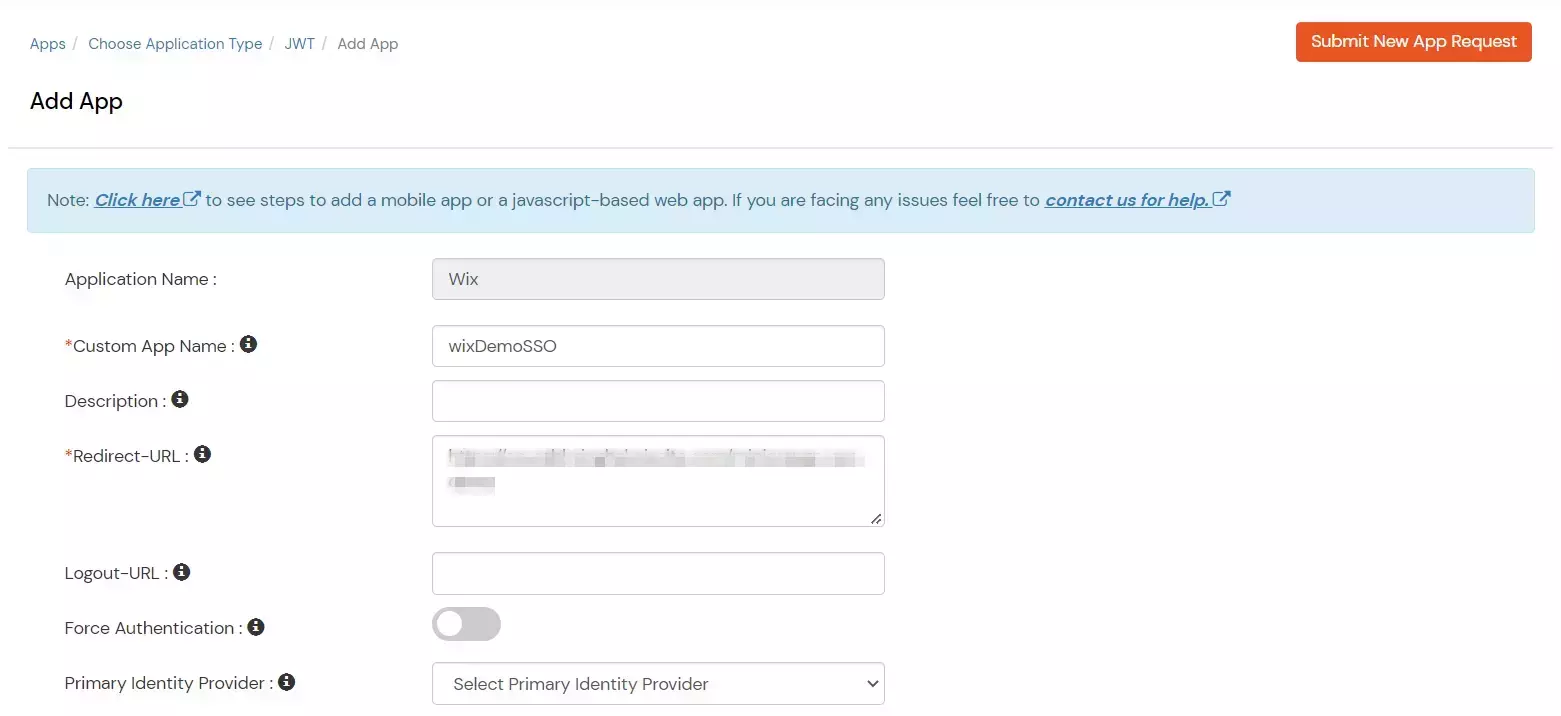
- In Add Apps tab enter the values and click on Save.
| Custom Application Name |
Choose appropriate name according to your choice. |
| Description |
Add appropriate description according to your choice. |
| Redirect-URL |
Please paste this link copied in the previous step |
| Group Name |
Default |
| Policy Name |
Add policy name according to your Preference. |
| Login Method |
Password. |
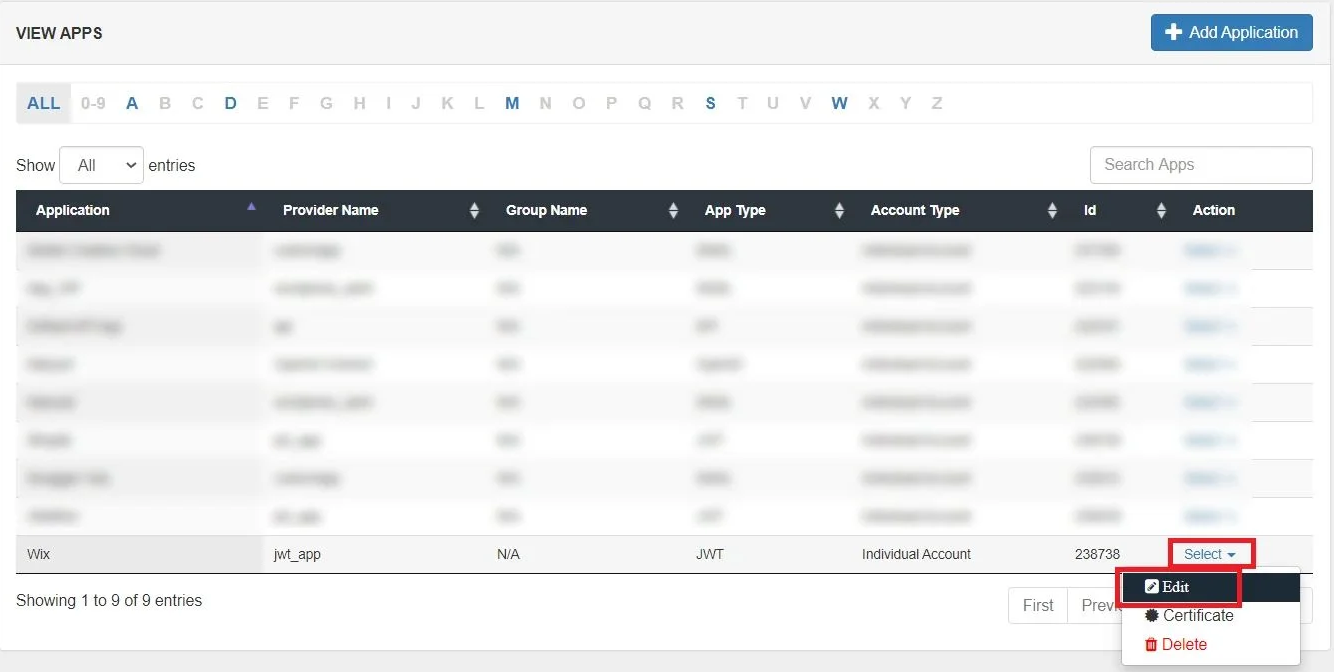
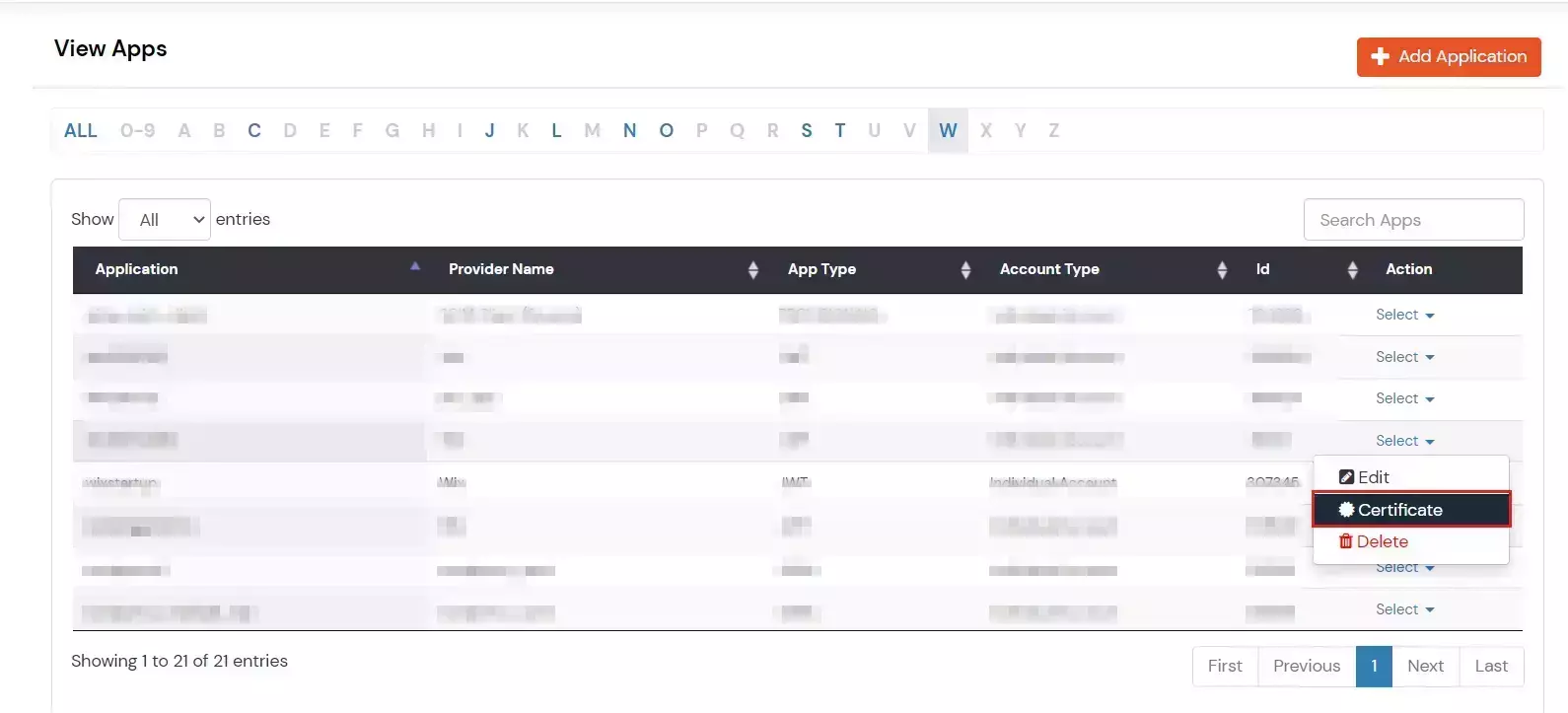
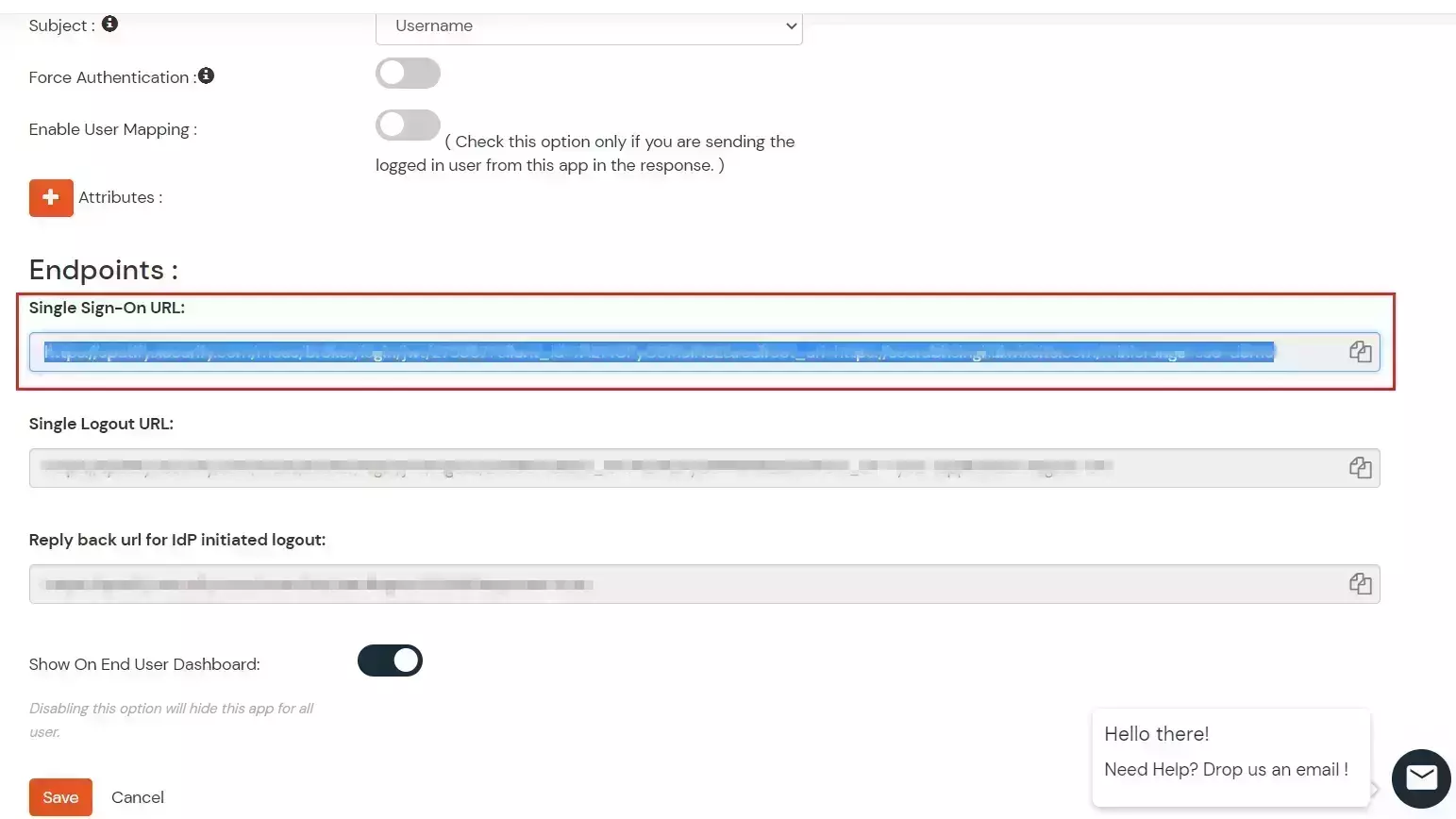
- Edit your recently created App by going to Apps >> Select option under Action dropdown >> Edit.
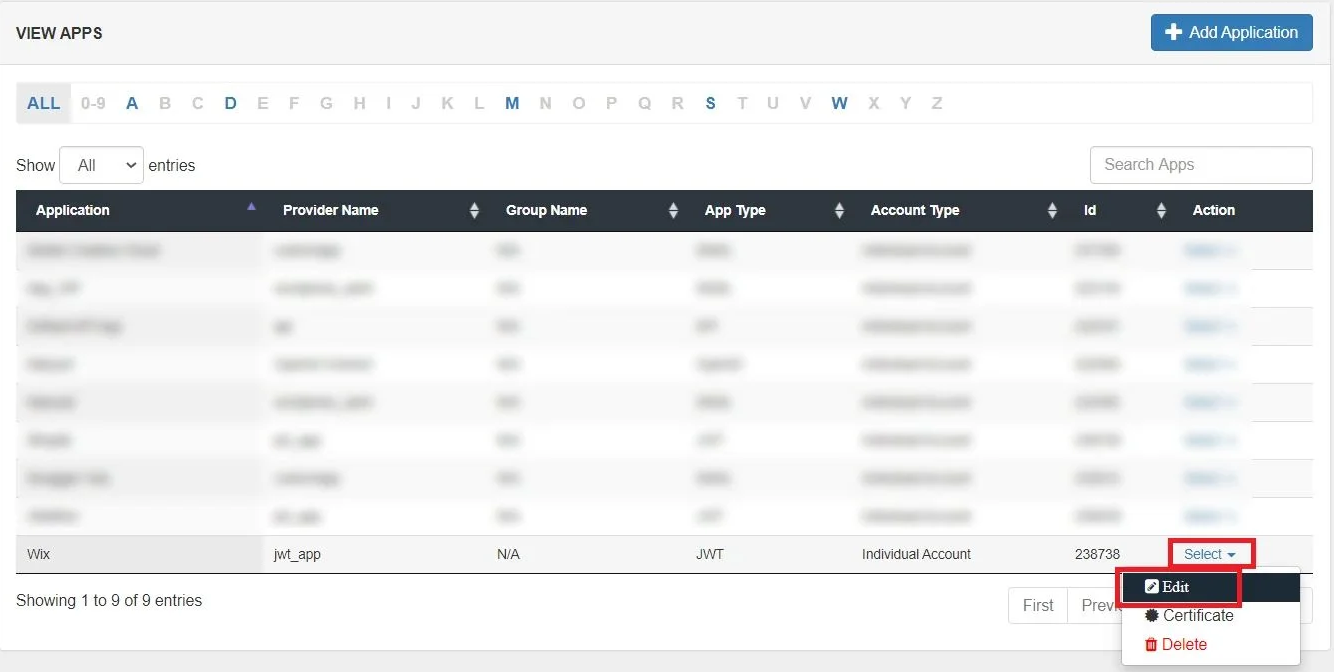
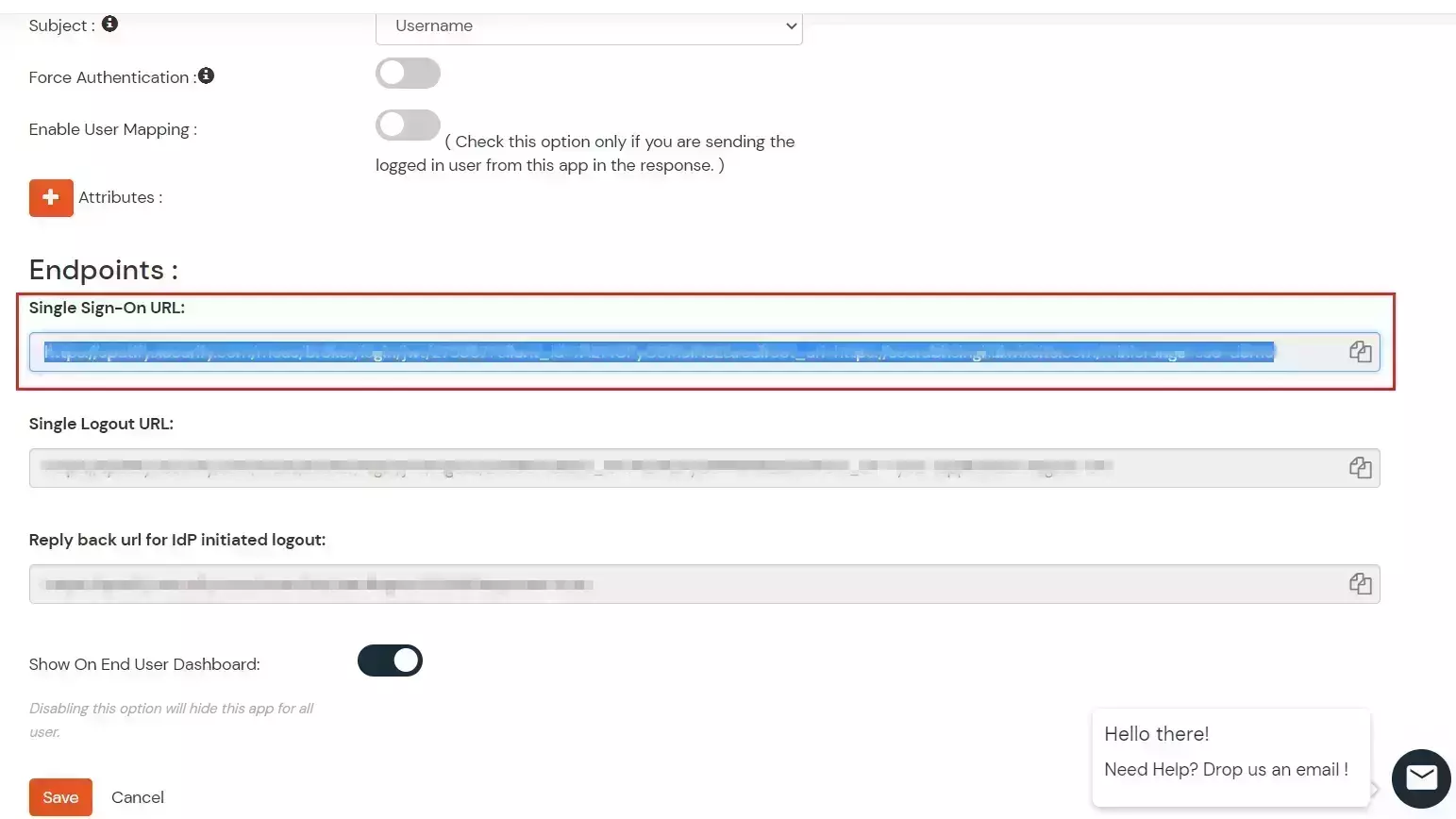
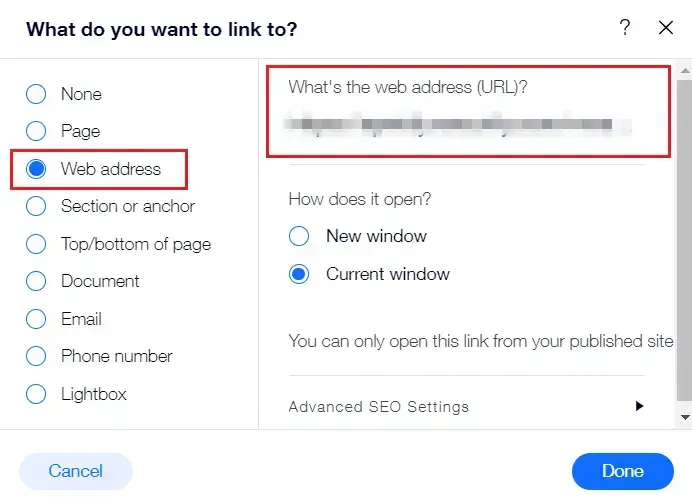
- Copy the Single Sign-On URL from the edit app page and click on save.
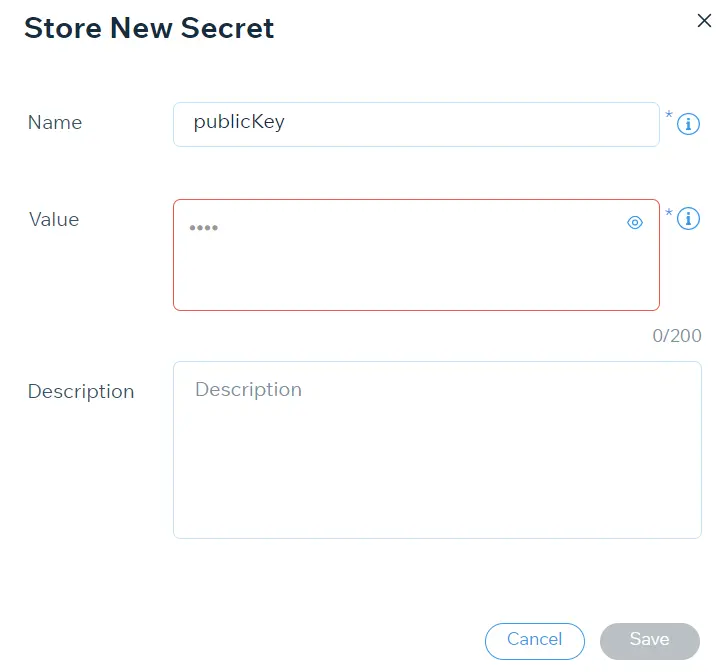
- To download App certificate, Go Apps >> Select option under Action dropdown >> Certificate
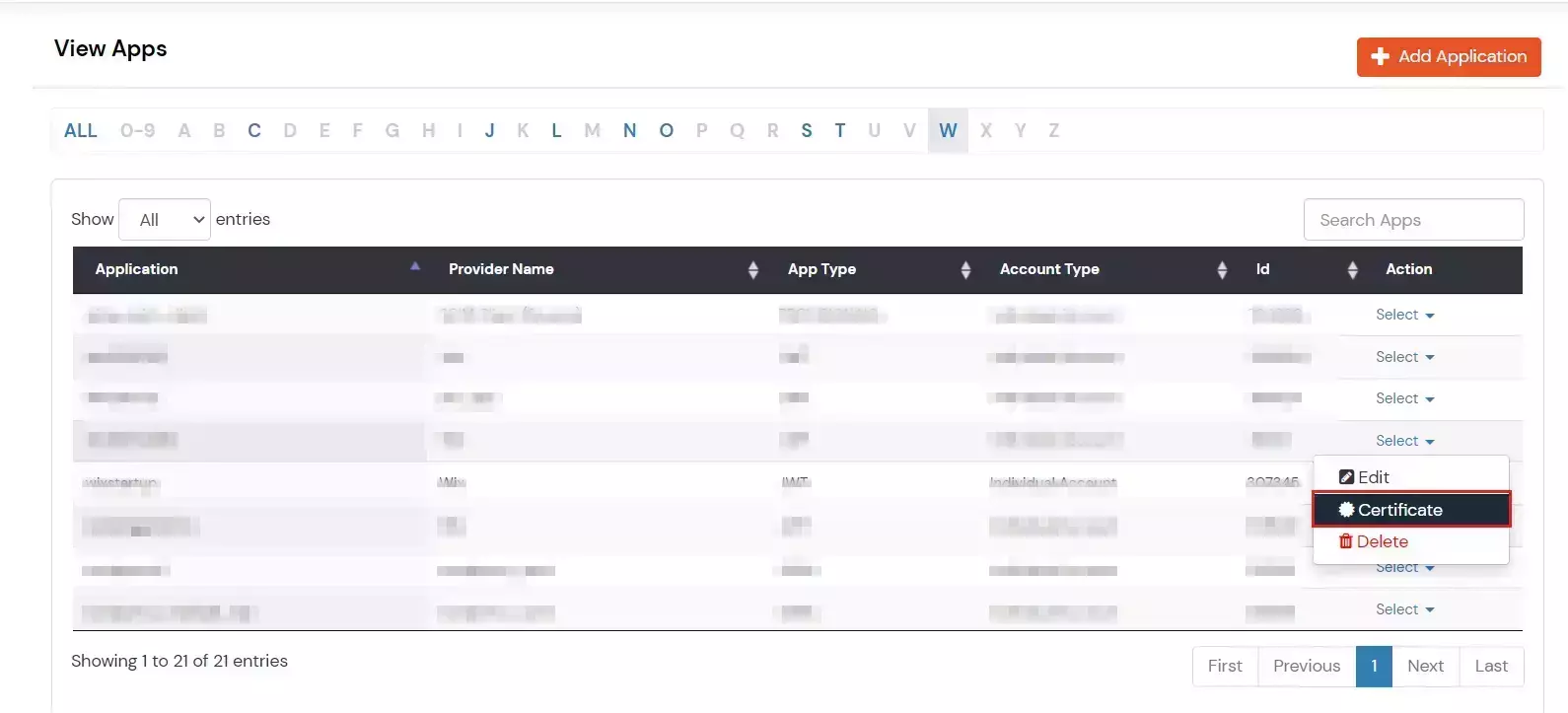
- Download the Certificate.
Go to your Wix site to continue editing.
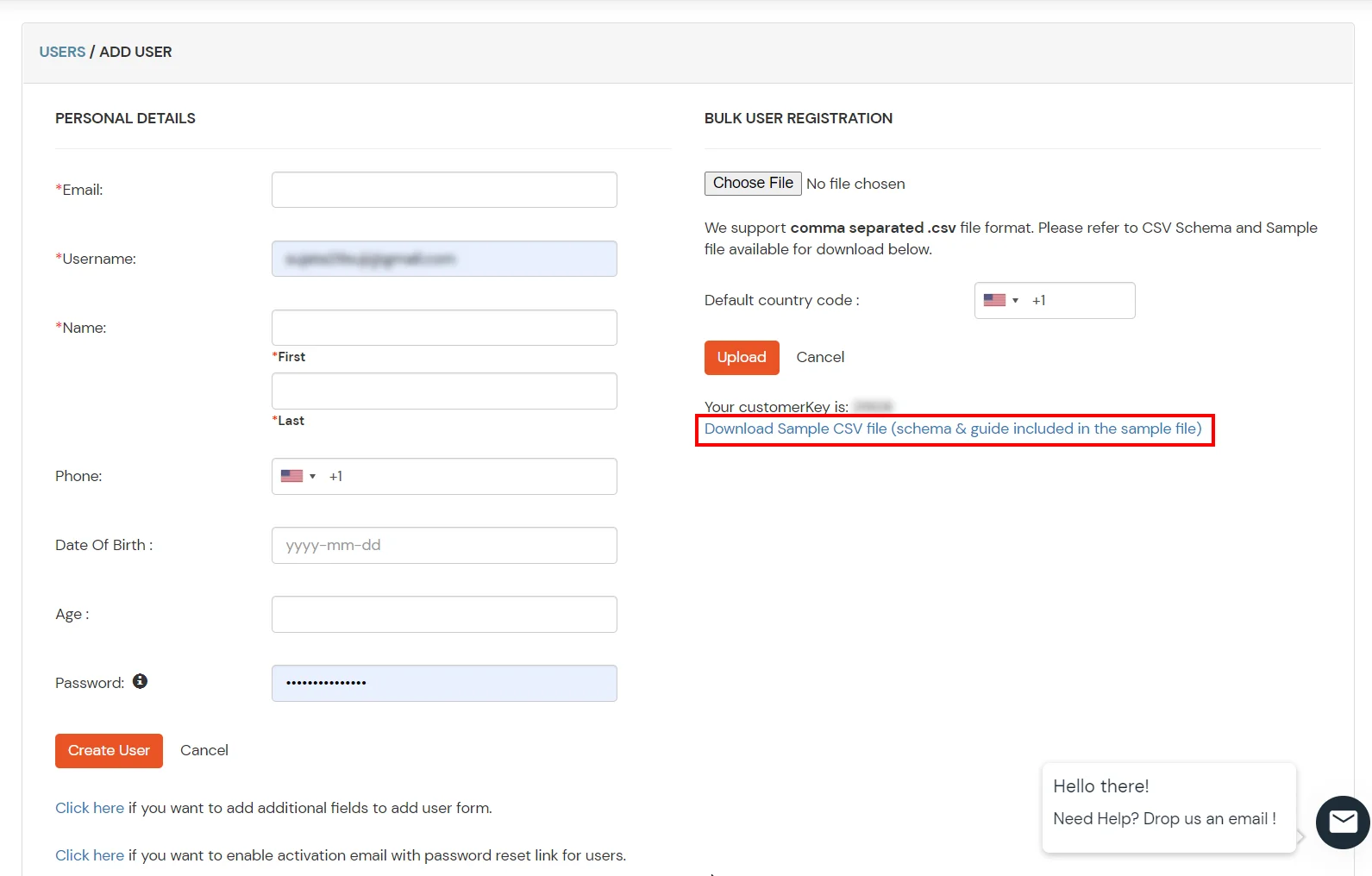
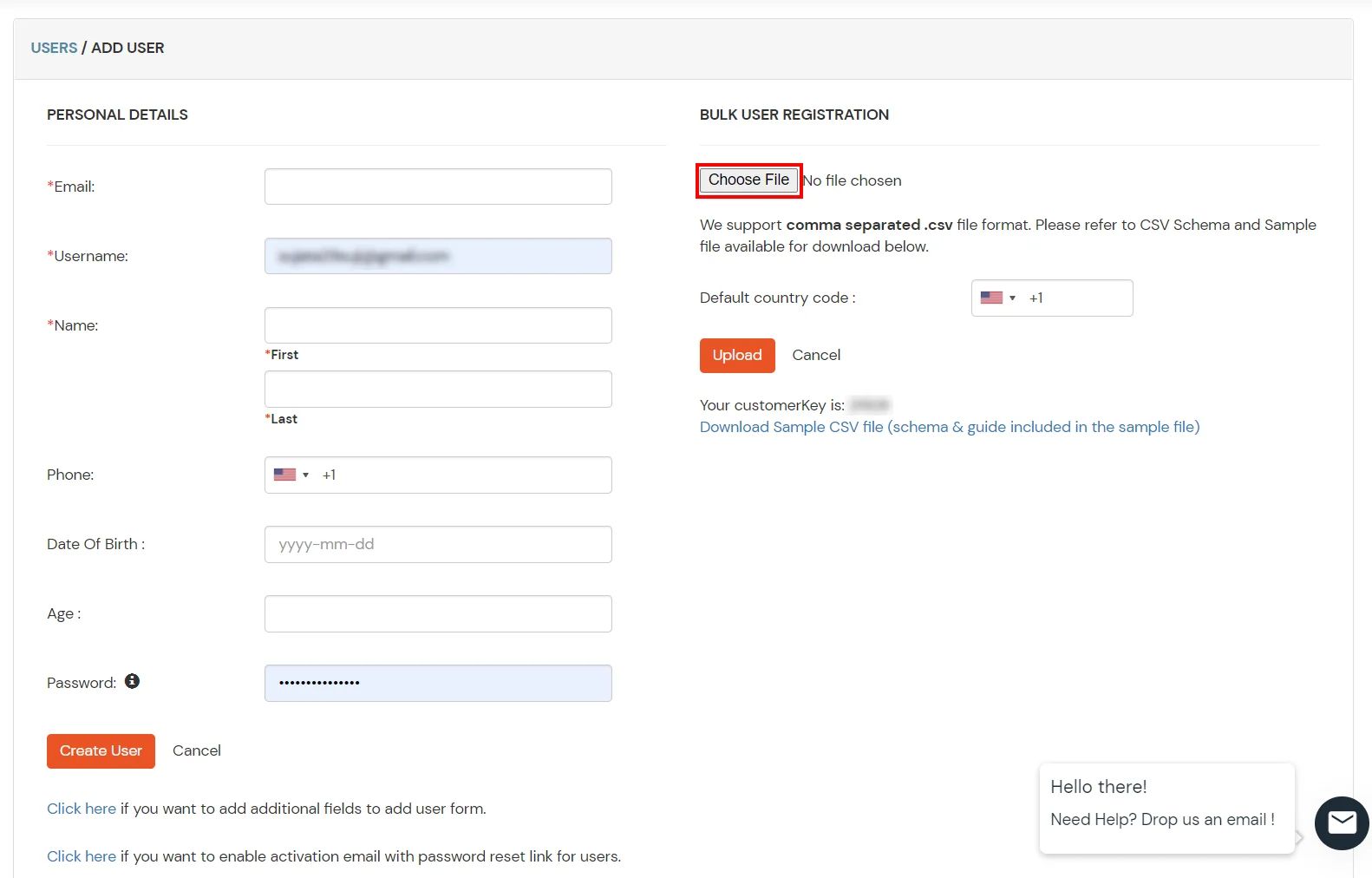
Connect with External Source of Users
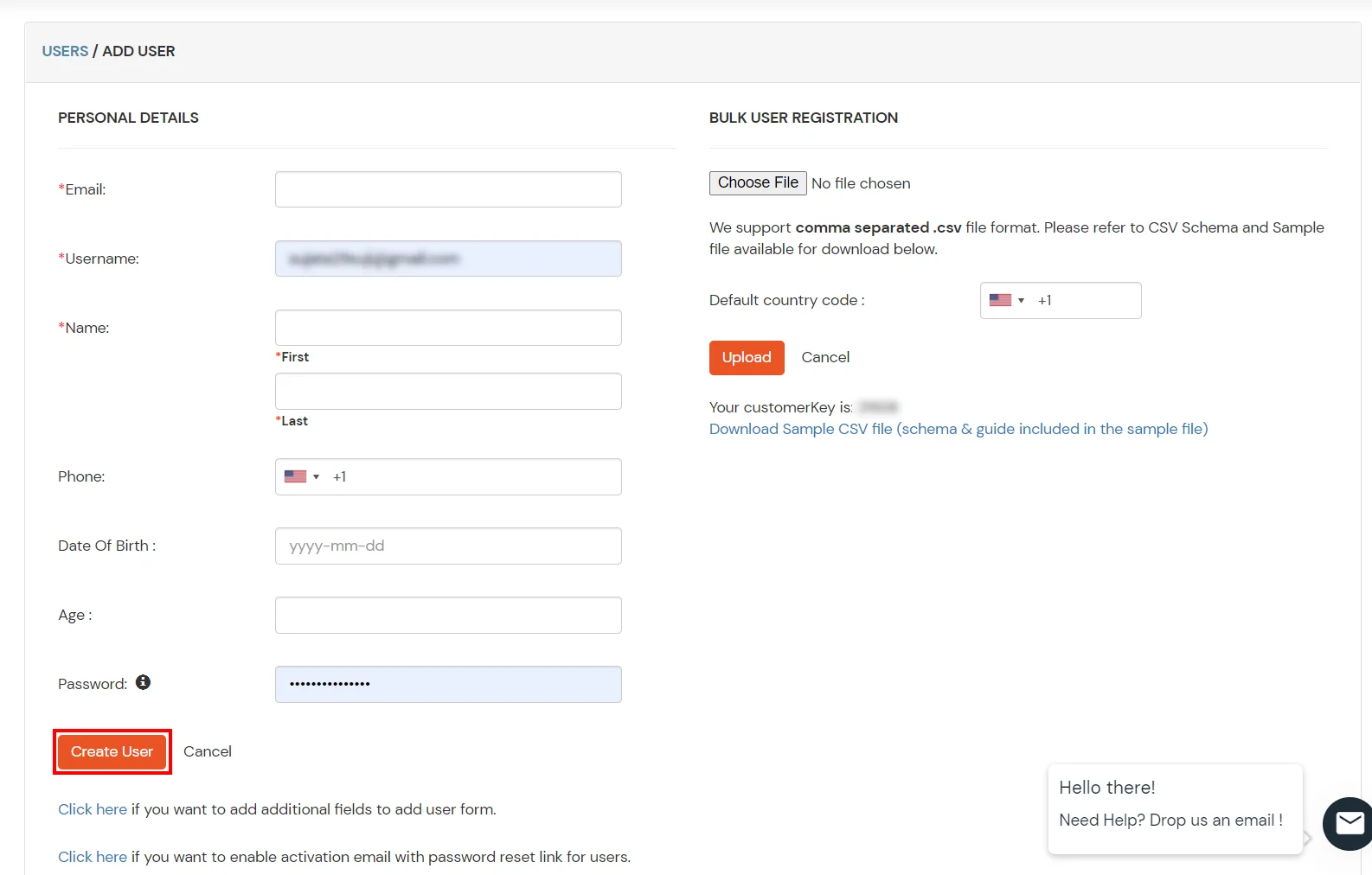
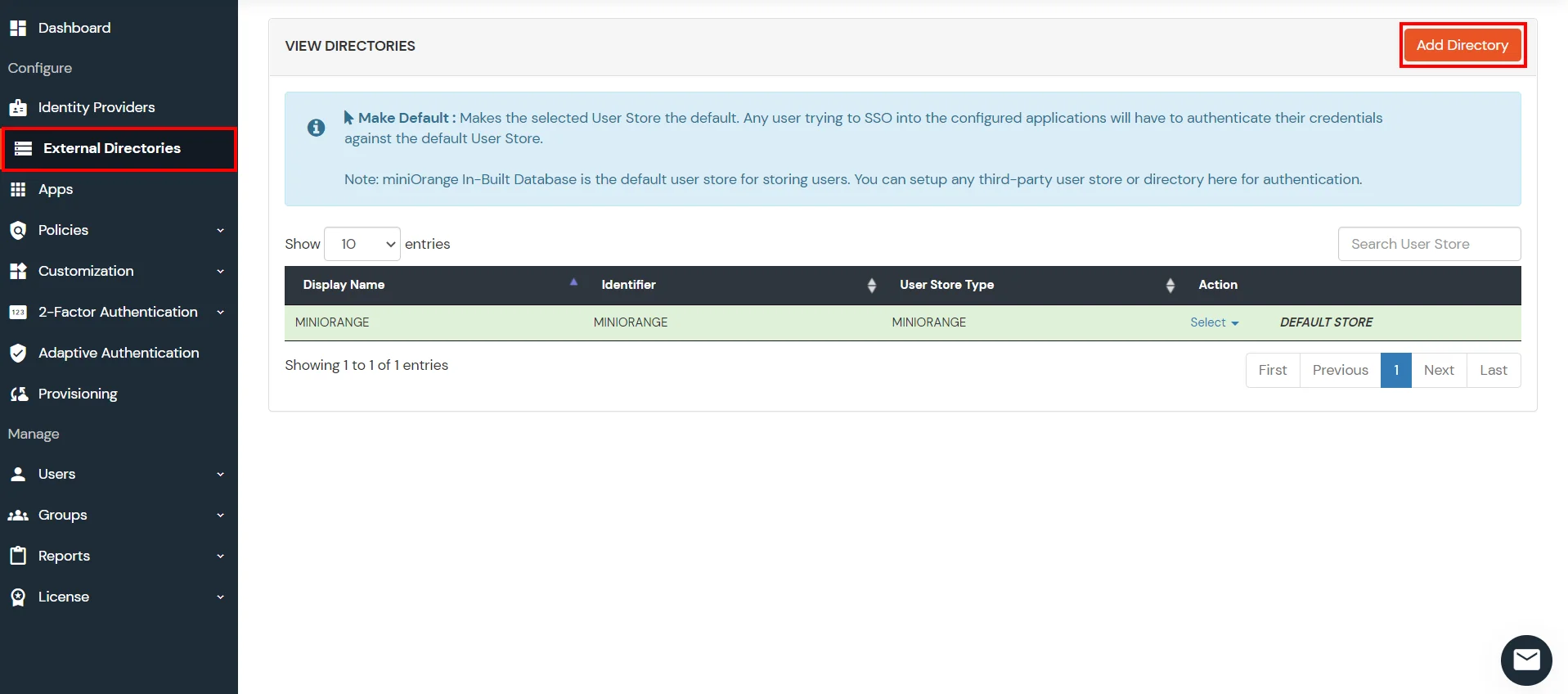
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
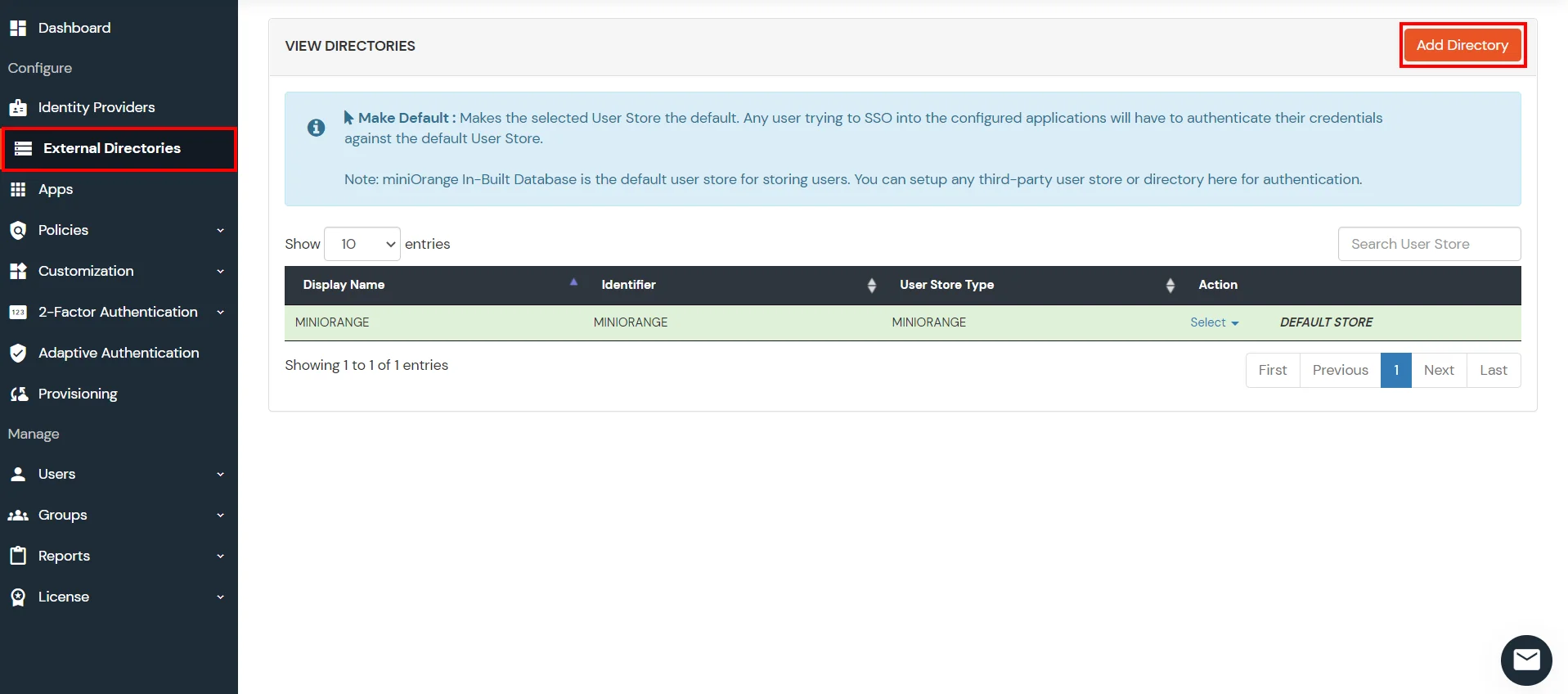
3. Configure Your User Directory
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
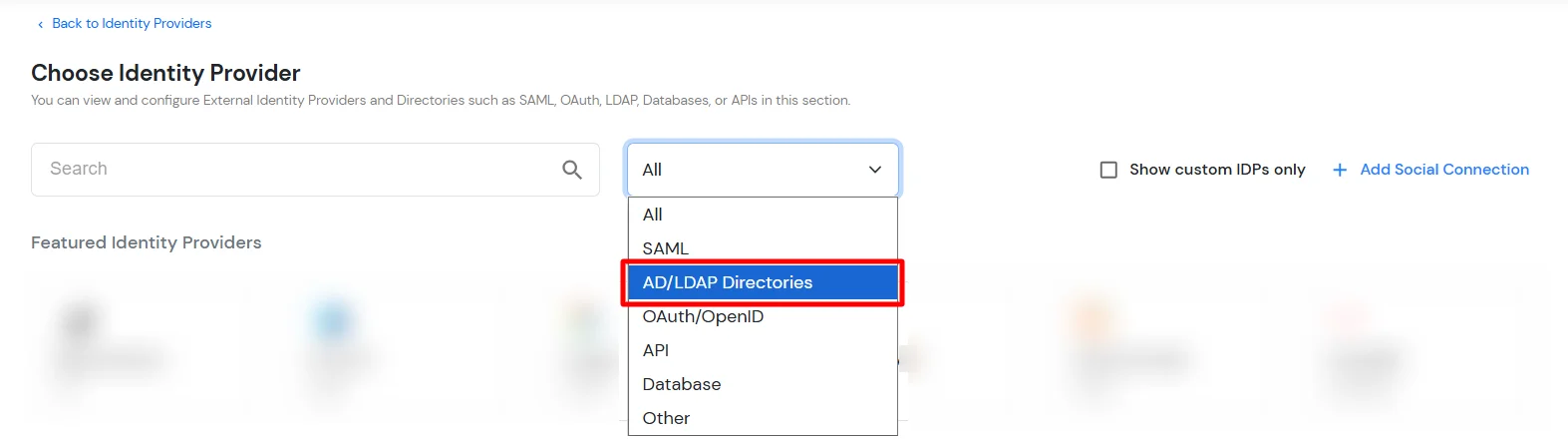
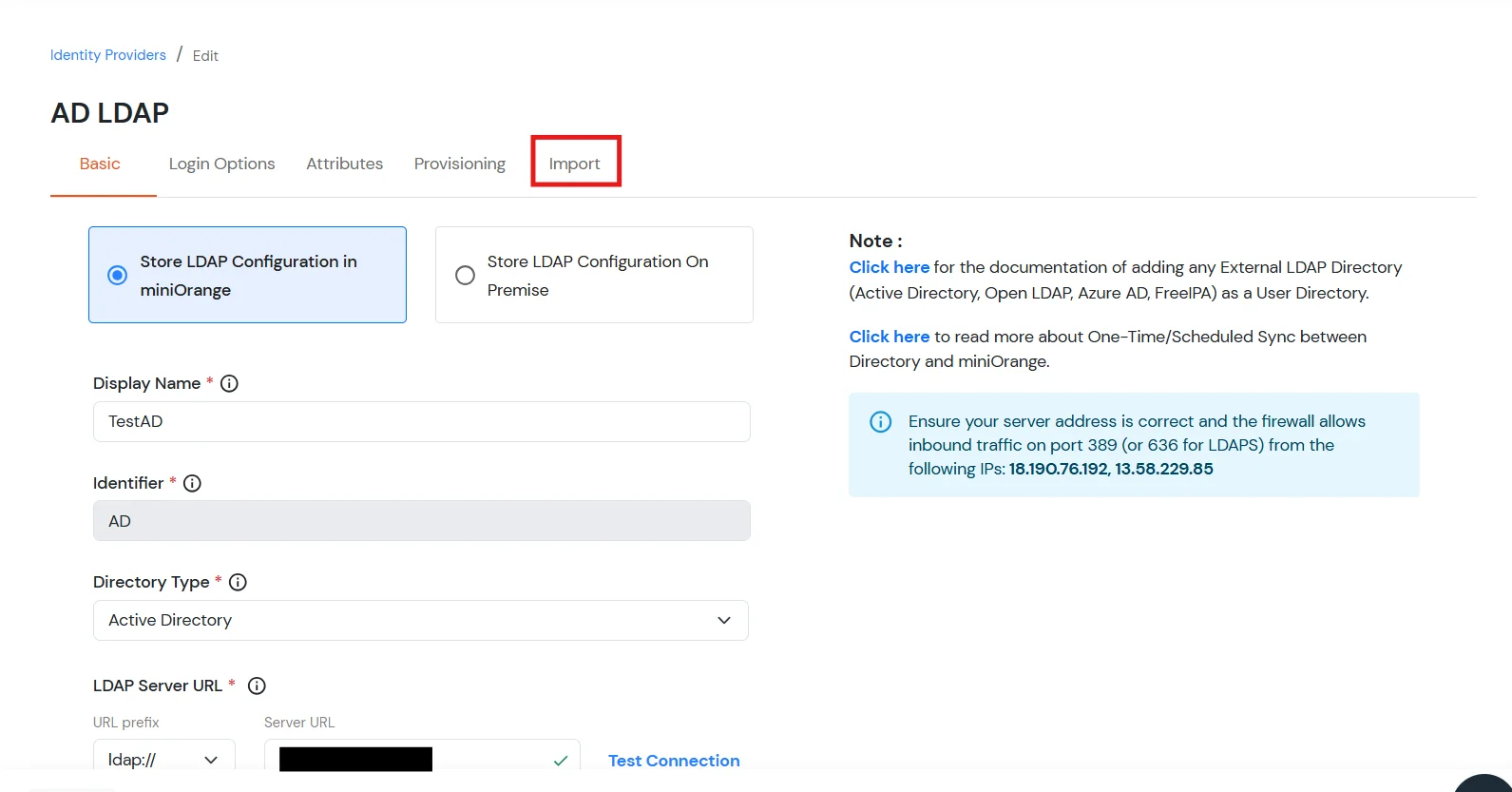
- Click on Identity Providers >> Add Identity Provider in the left menu of the dashboard.
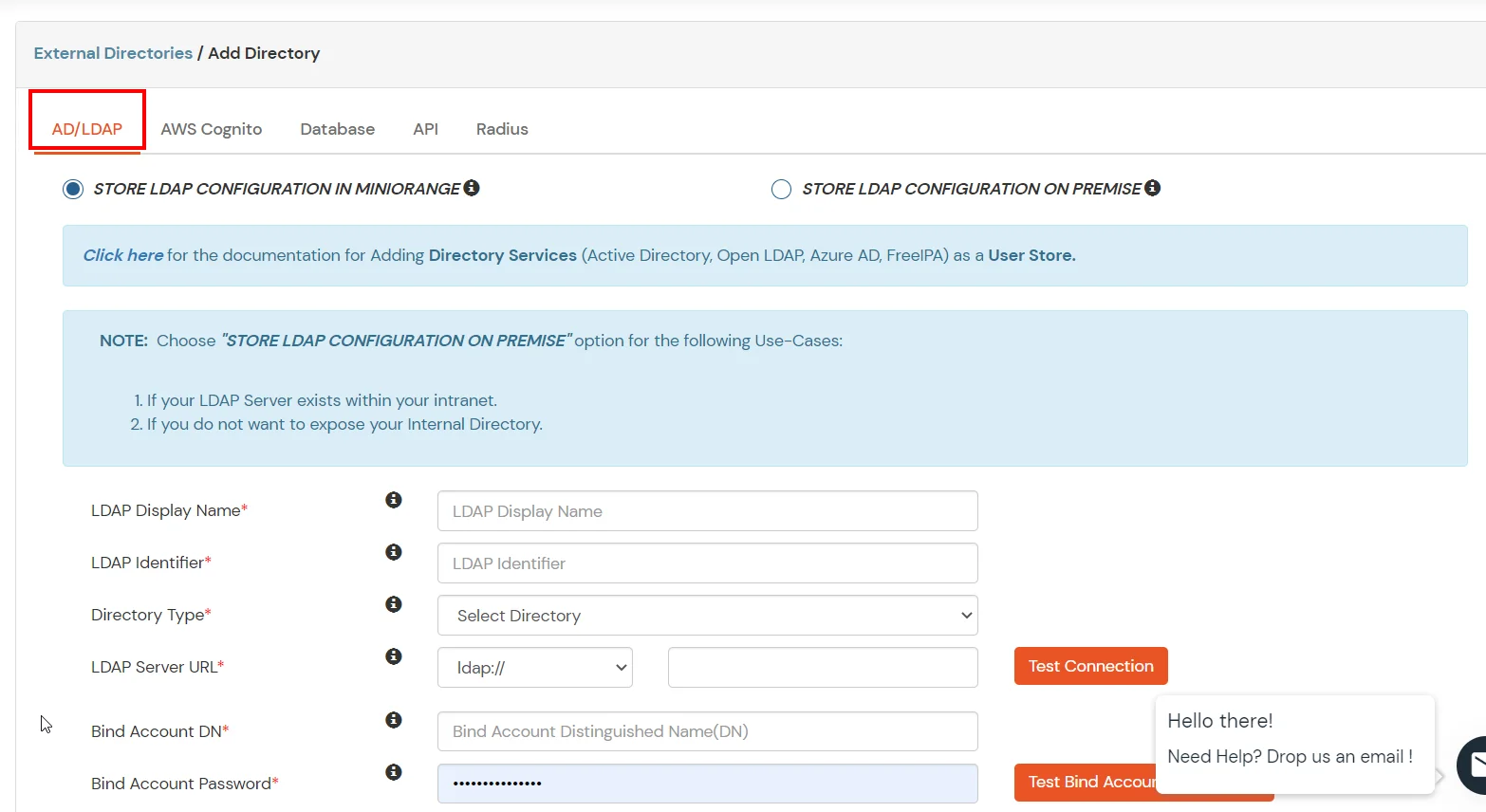
- In Choose Identity Provider, select AD/LDAP Directories from the dropdown.
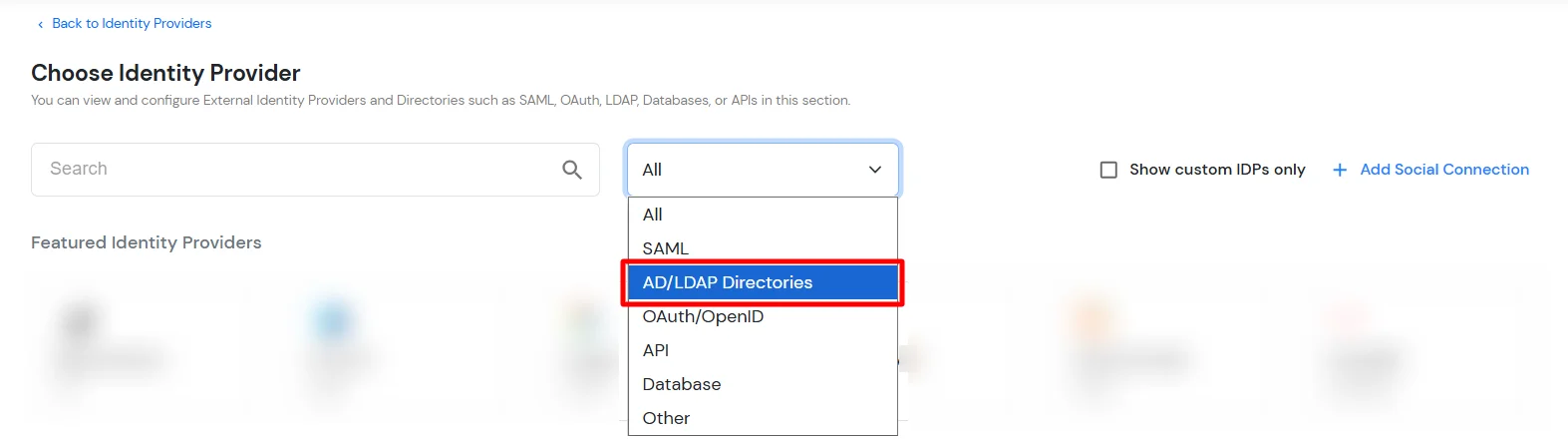
- Then search for AD/LDAP and click it.
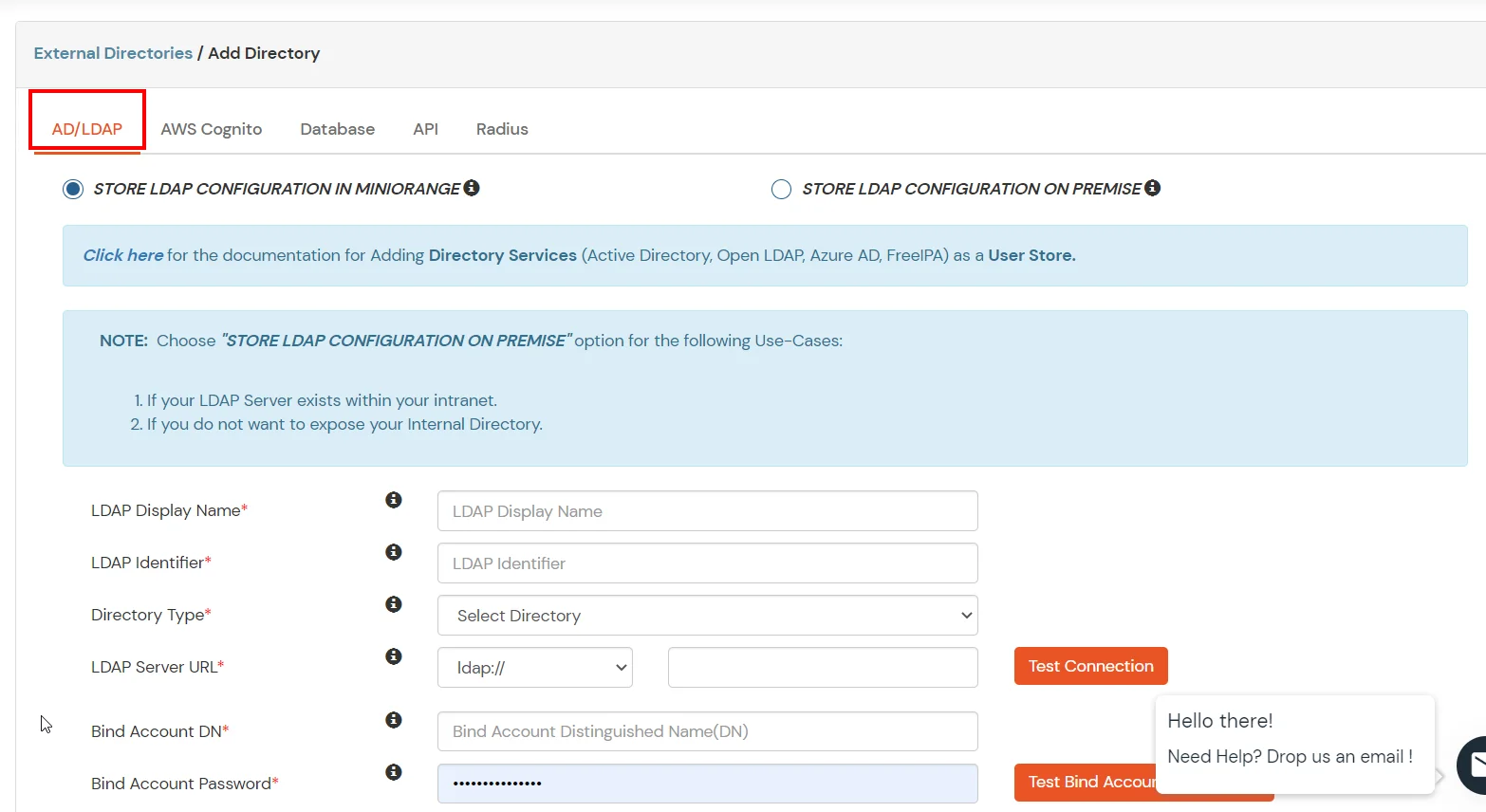
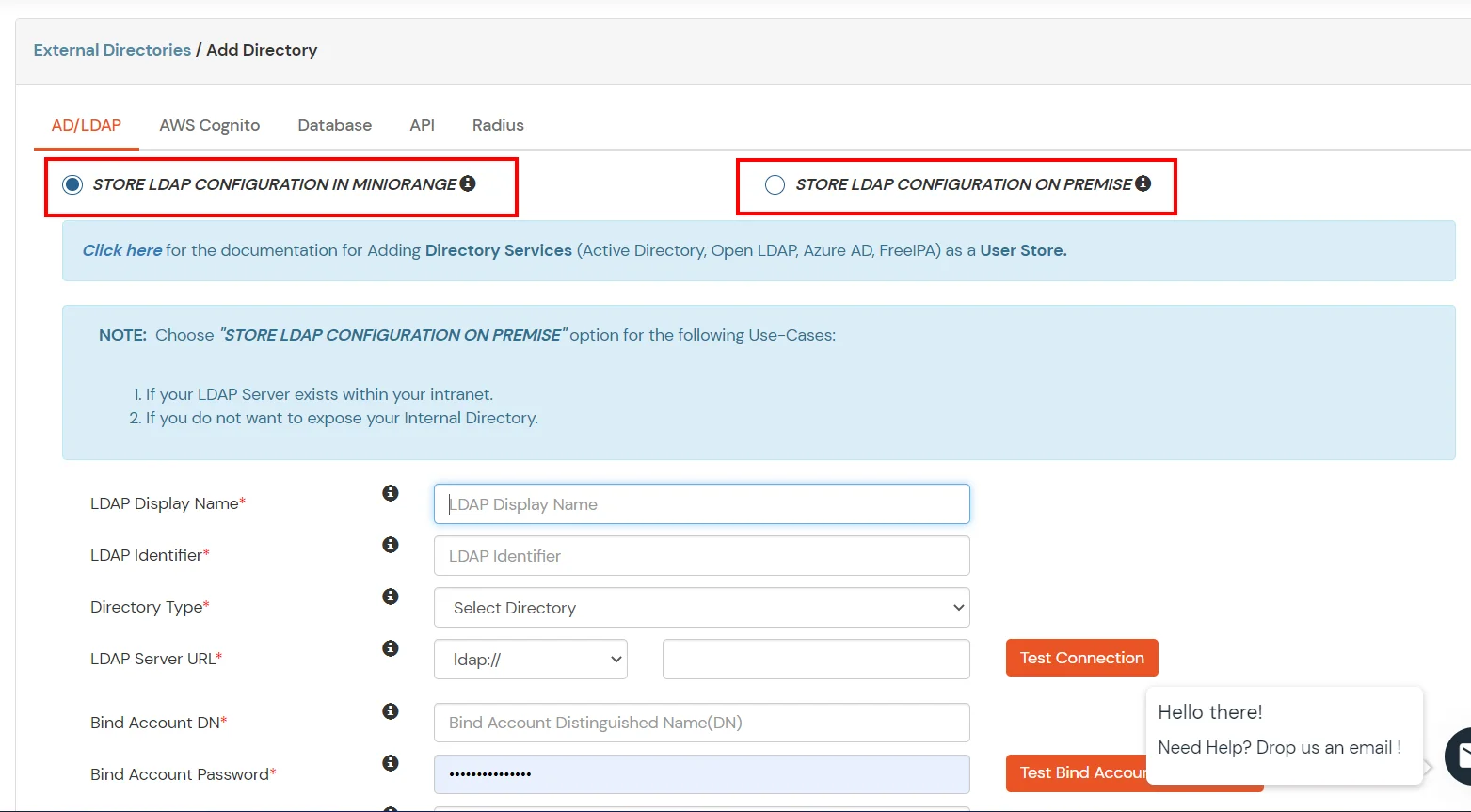
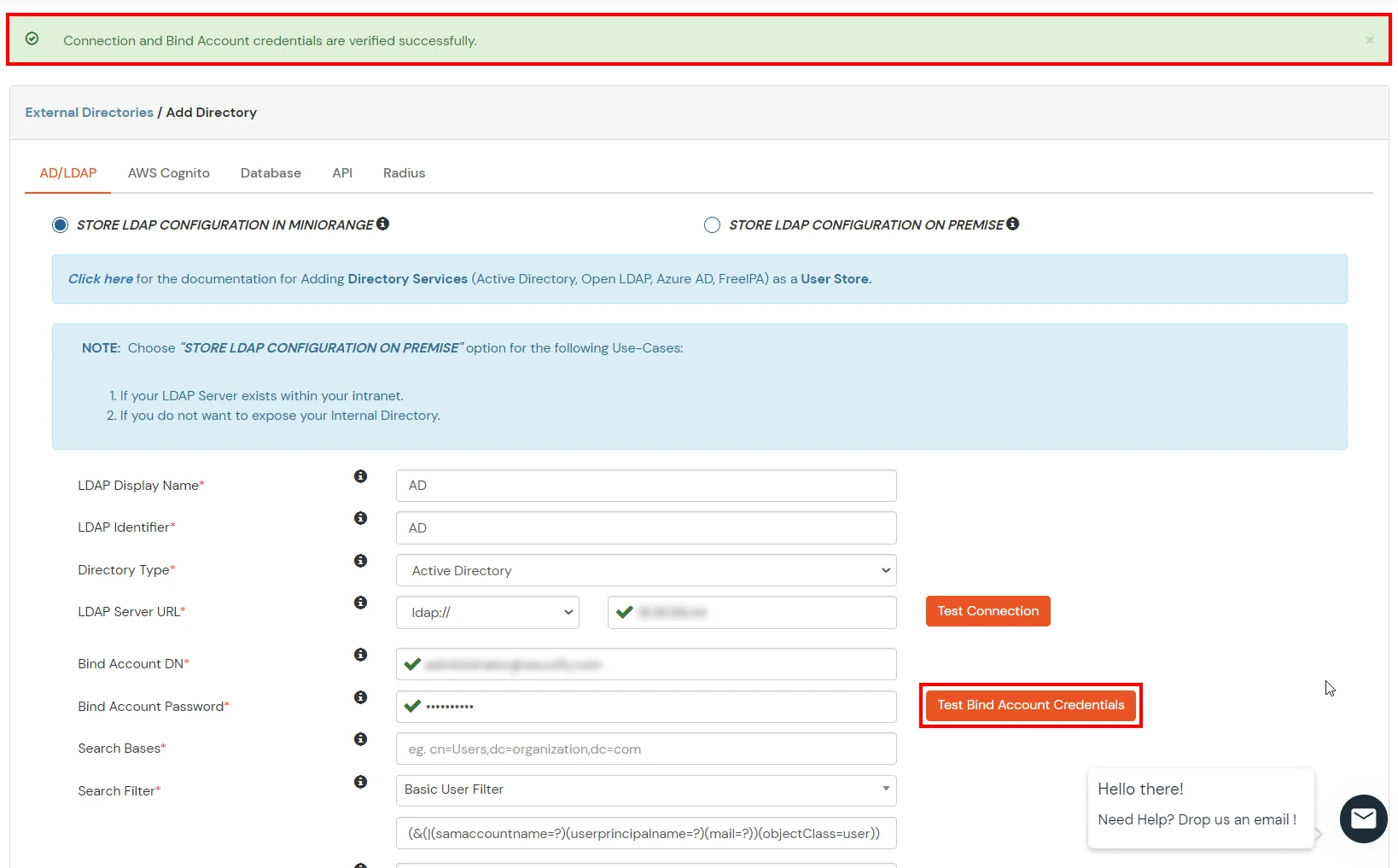
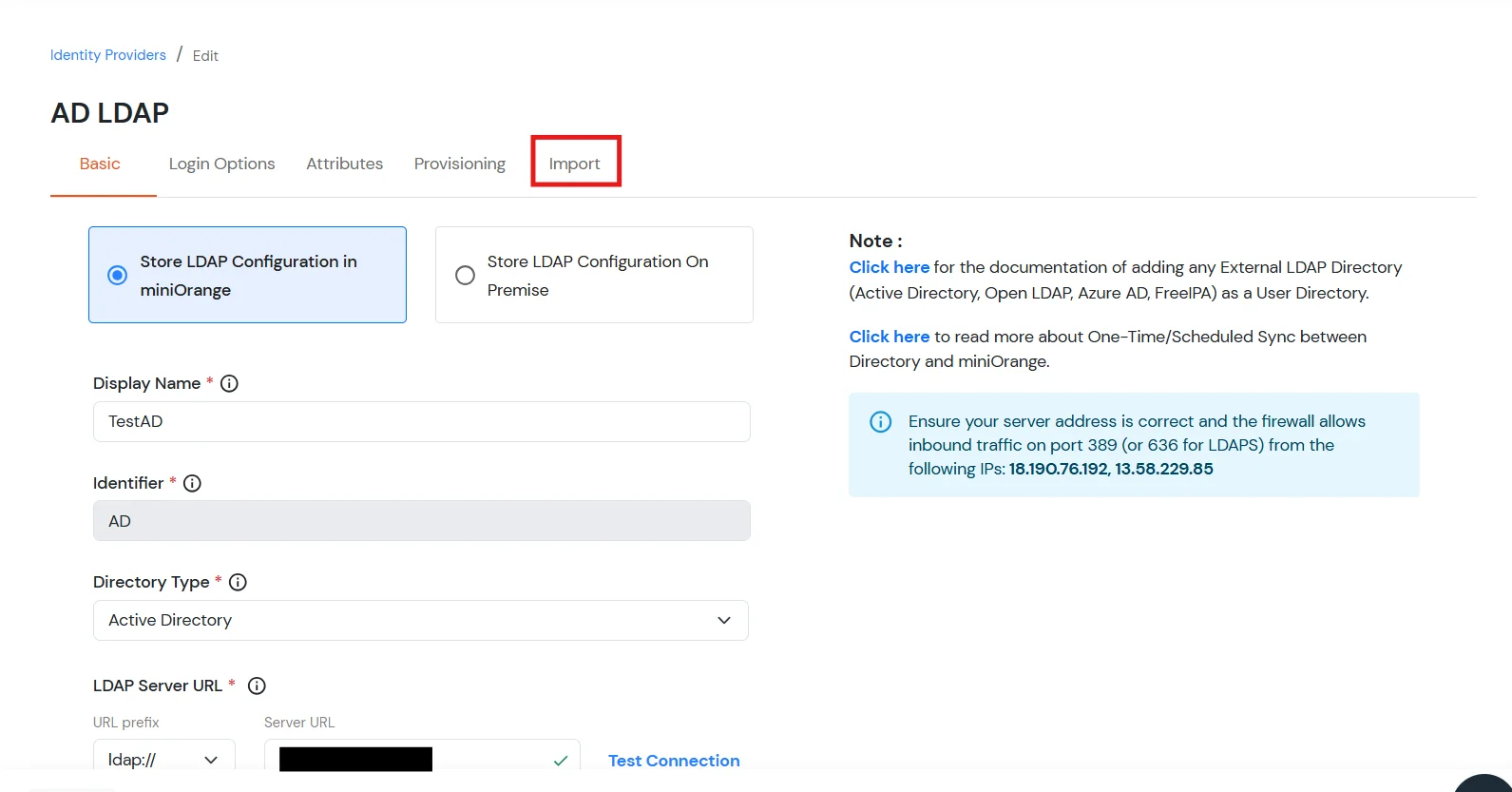
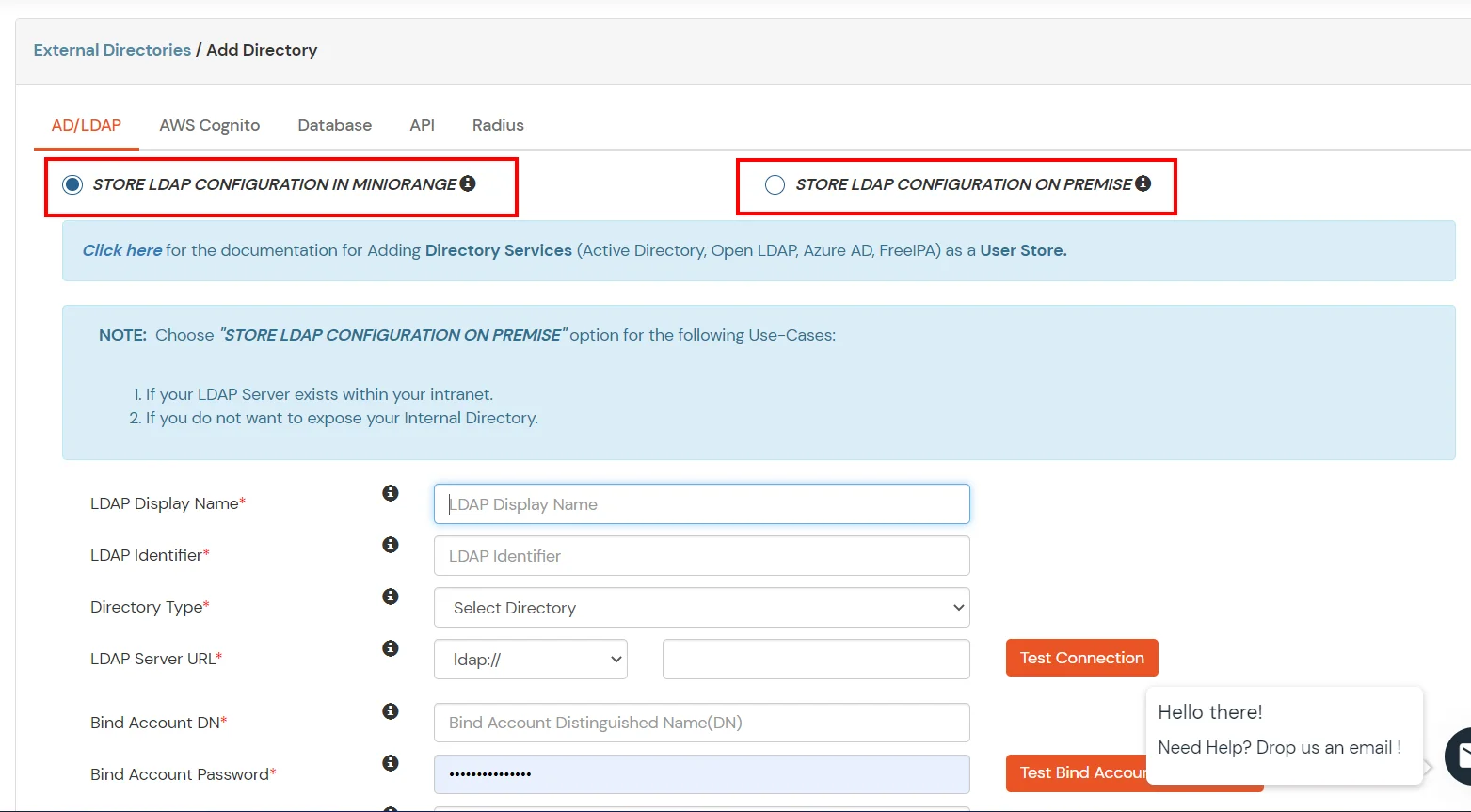
- STORE LDAP CONFIGURATION IN MINIORANGE: Choose this option if you want to keep your configuration in miniOrange. If the active directory is behind a firewall, you will need to open the firewall to allow incoming requests to your AD.
- STORE LDAP CONFIGURATION ON PREMISE: Choose this option if you want to keep your configuration in your premise and only allow access to AD inside premises. You will have to download and install miniOrange gateway on your premise.
- Enter LDAP Display Name and Identifier name.
- Select Directory Type as Active Directory.
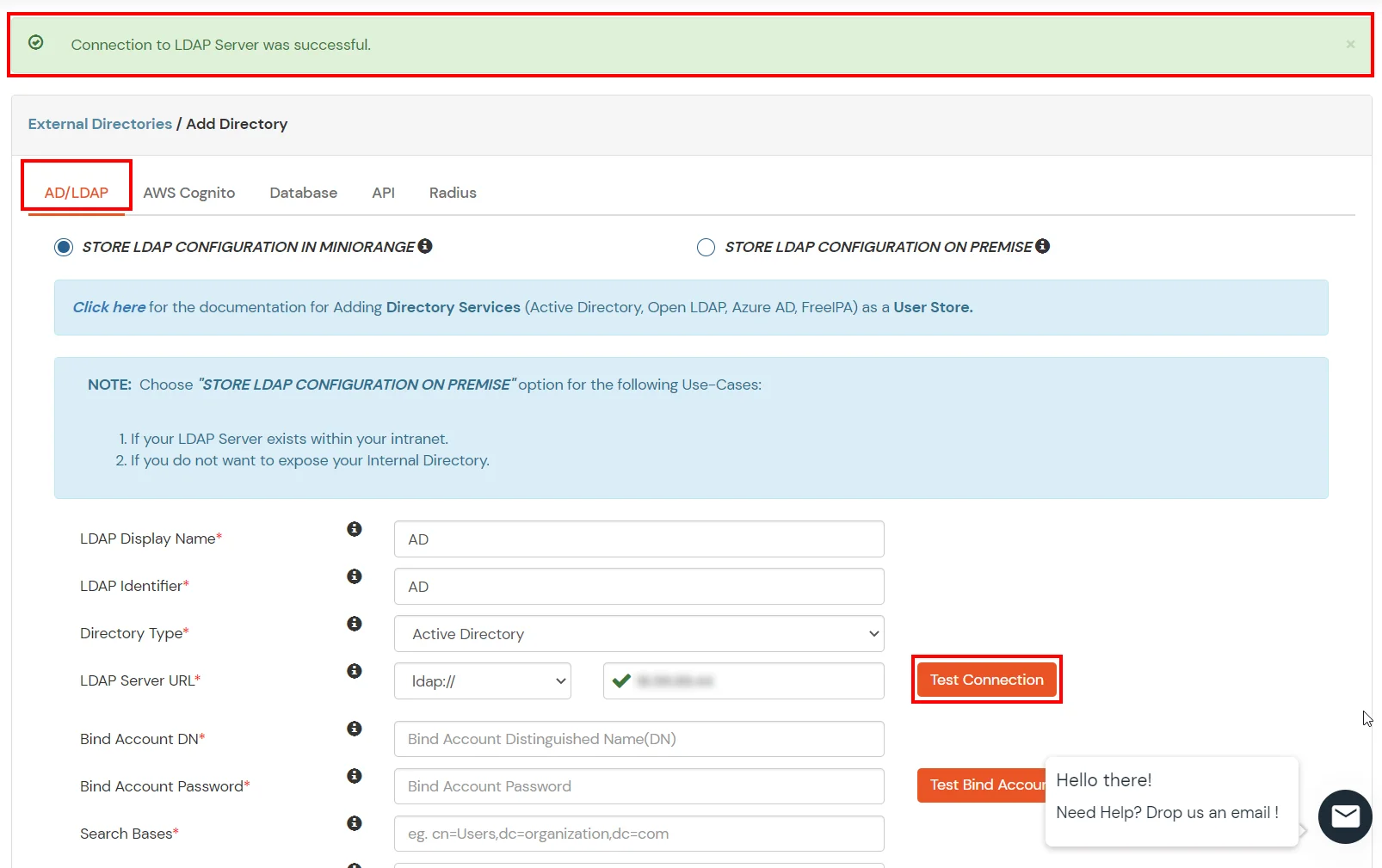
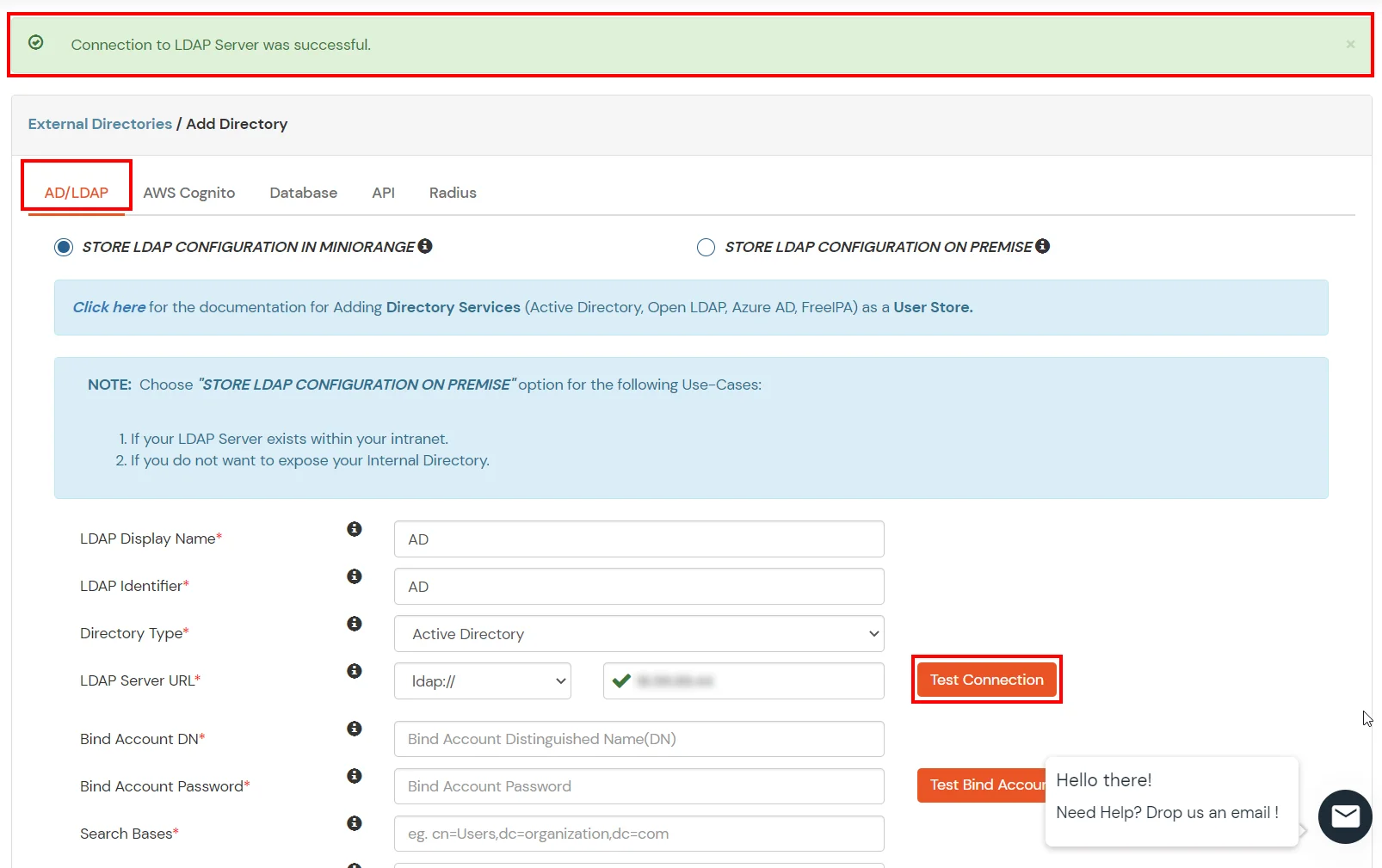
- Enter the LDAP Server URL or IP Address against the LDAP Server URL field.
- Click on the Test Connection button to verify if you have made a successful connection with your LDAP server.
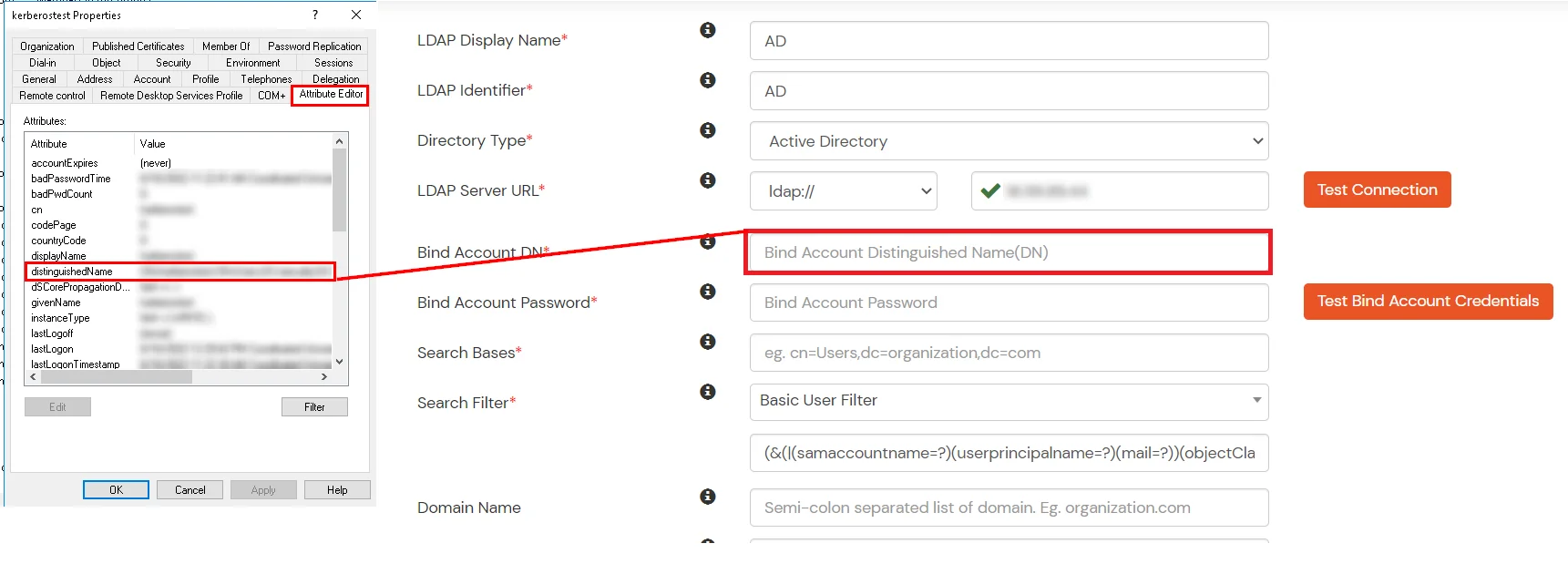
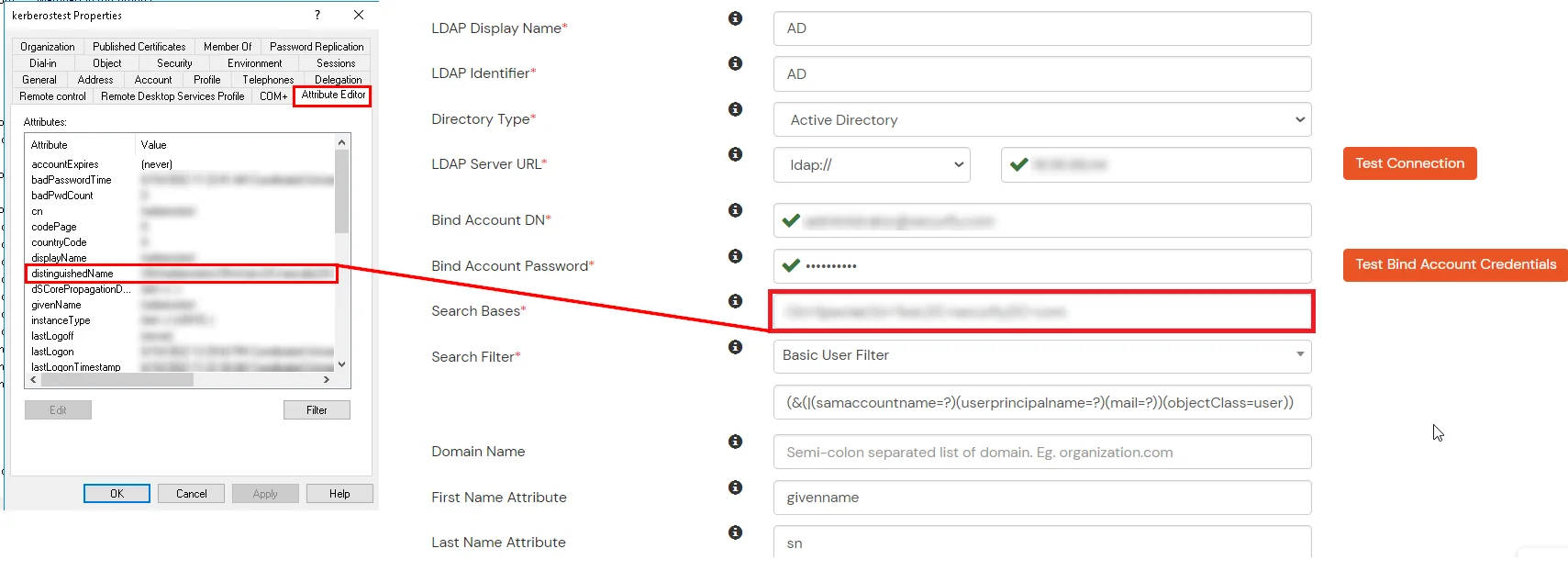
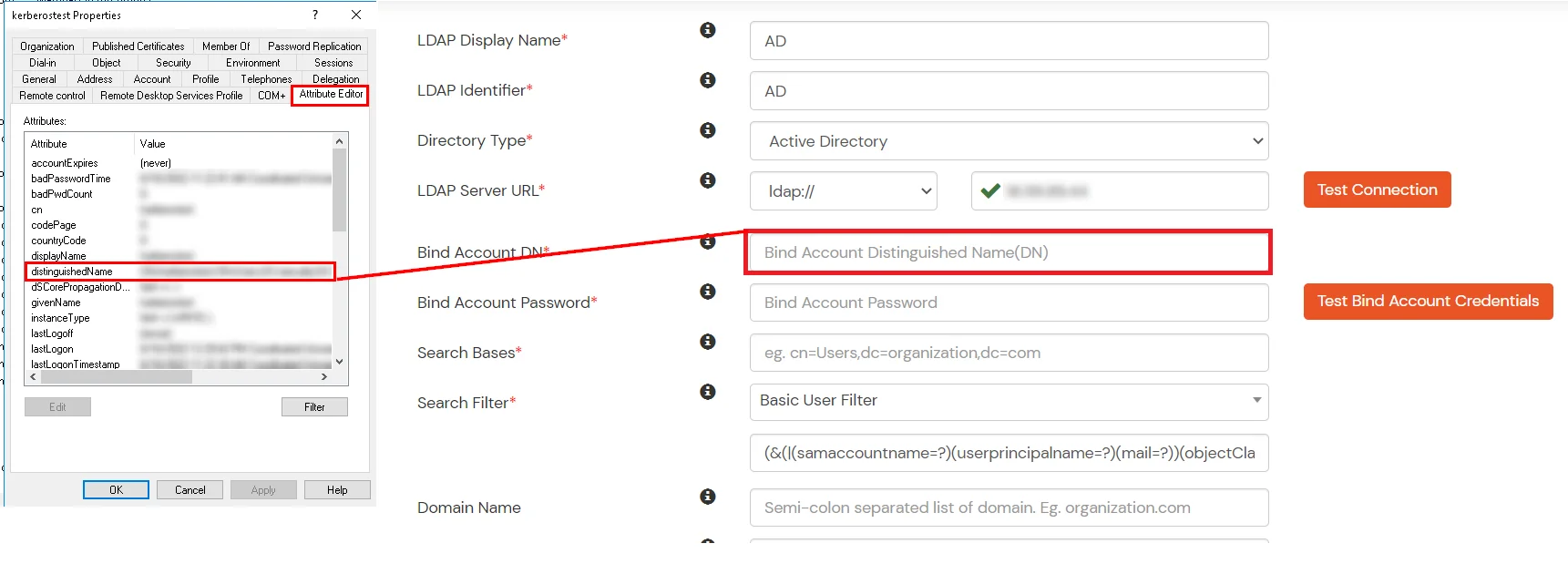
- In Active Directory, go to the properties of user containers/OU's and search for the Distinguished Name attribute. The bind account should have minimum required read privileges in Active Directory to allow directory lookups. If the use case involves provisioning (such as creating, updating, or deleting users or groups), the account must also be granted appropriate write permissions.
- Enter the valid Bind account Password.
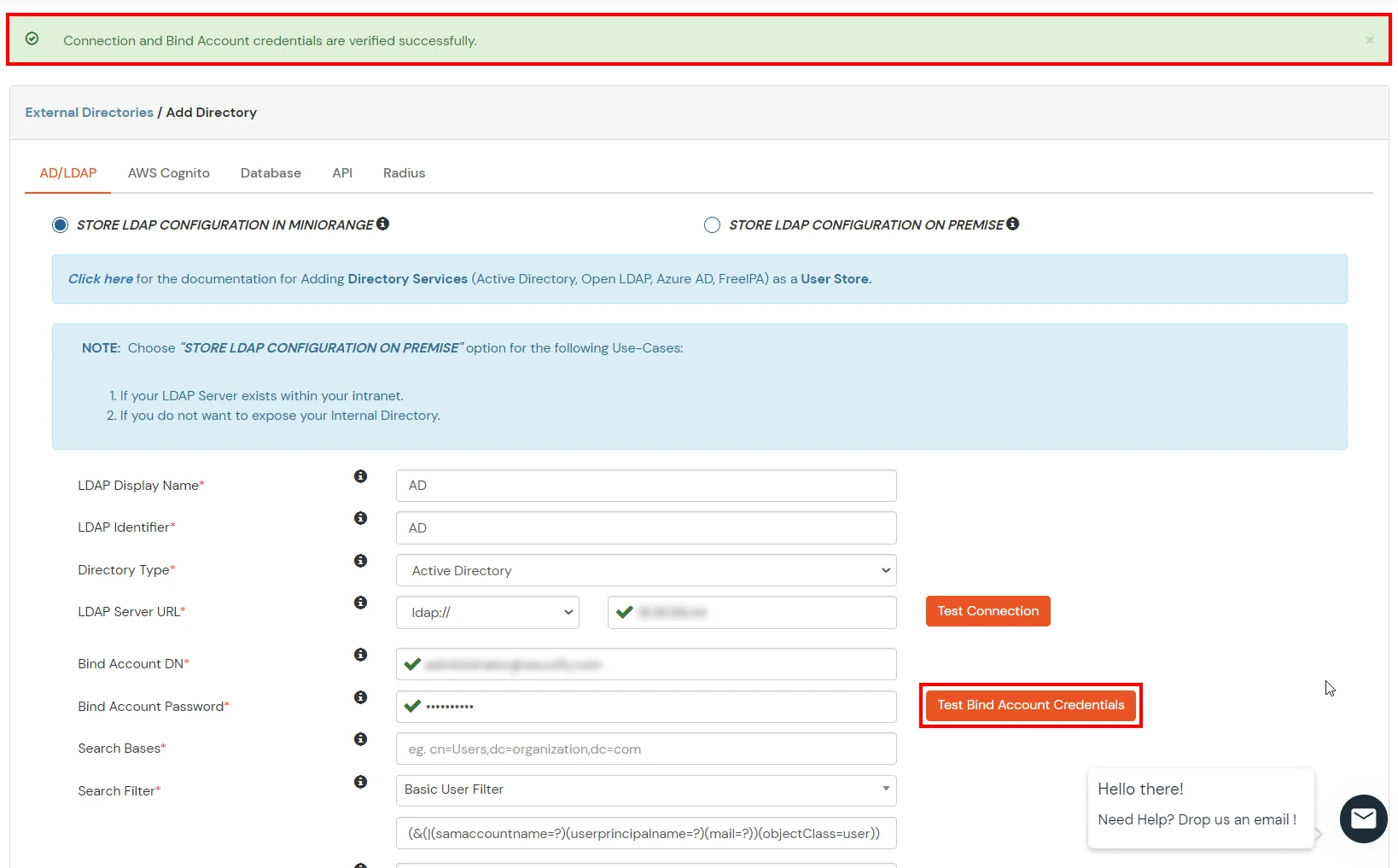
- Click on the Test Bind Account Credentials button to verify your LDAP Bind credentials for LDAP connection.
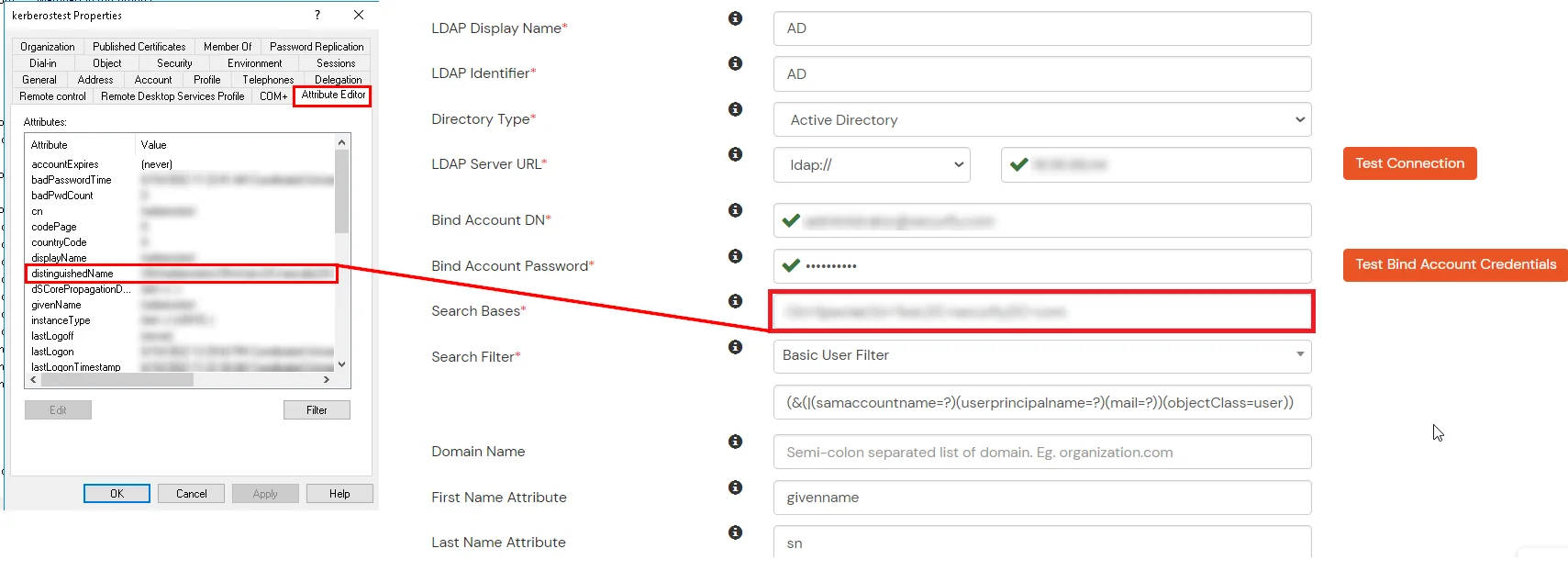
- Search Base is the location in the directory where the search for a user begins. You will get this from the same place you got your Distinguished name.
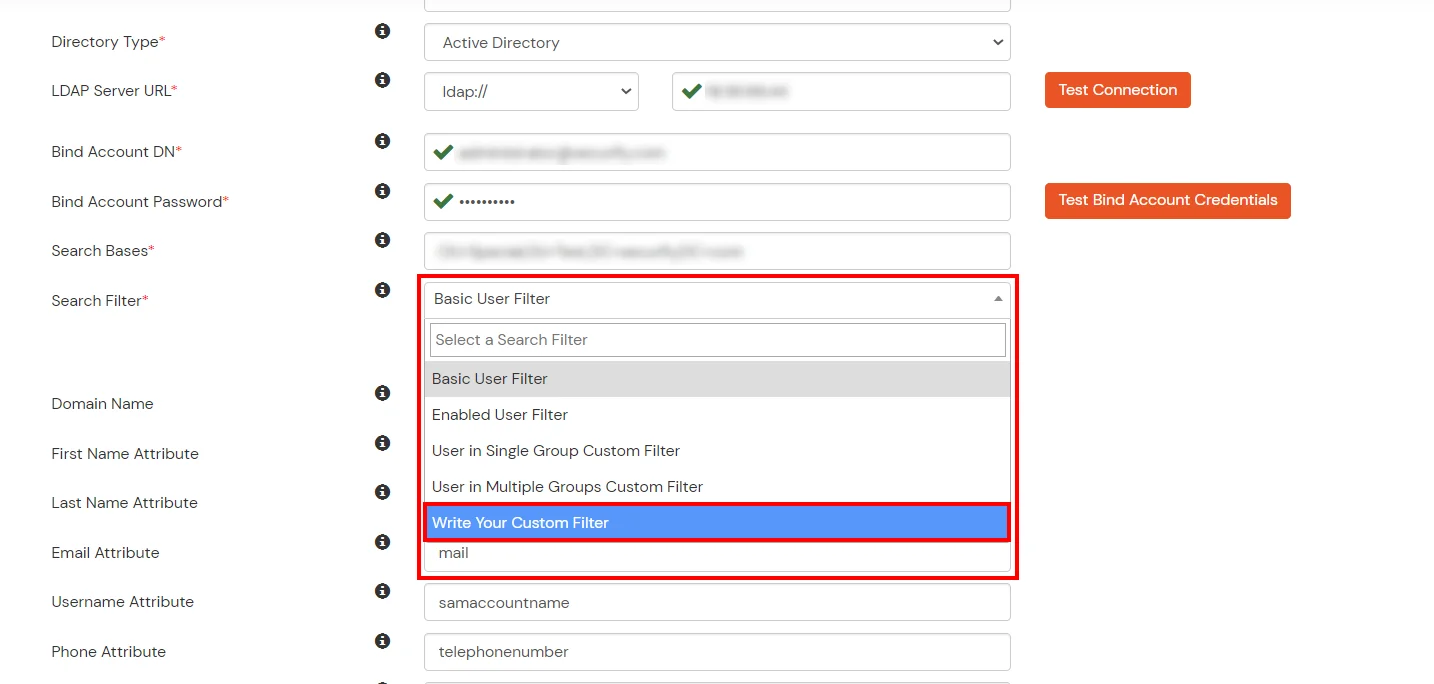
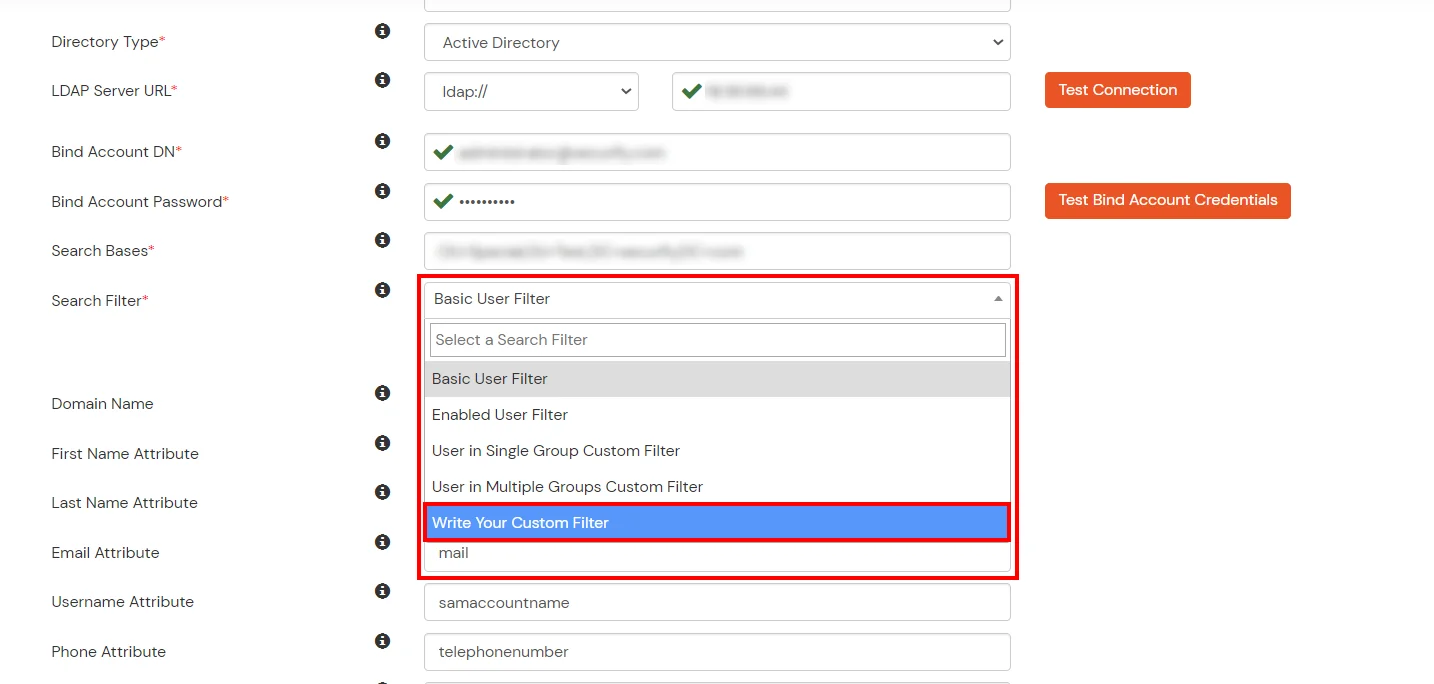
- Select a suitable Search filter from the drop-down menu. If you use User in Single Group Filter or User in Multiple Group Filter, replace the <group-dn> in the search filter with the distinguished name of the group in which your users are present. To use custom Search Filter select "Write your Custom Filter" option and customize it accordingly.
- Click on the Next button, or go to the Login Options tab.
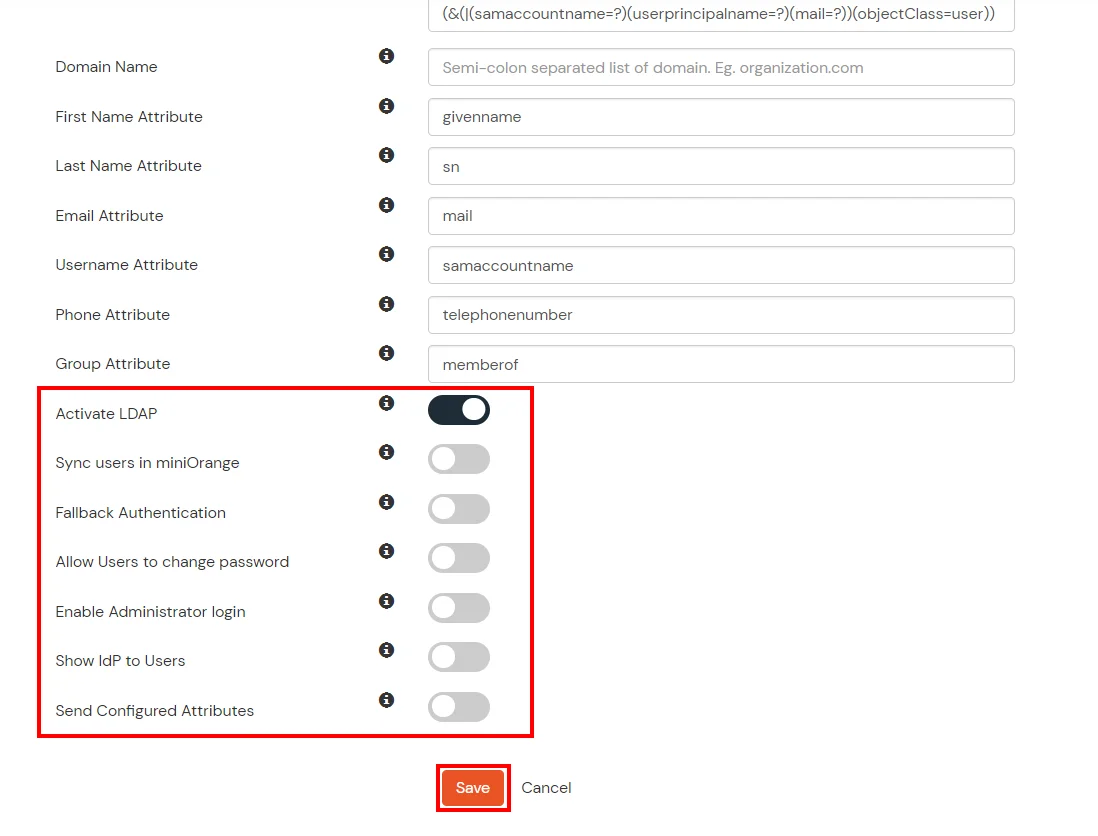
- You can also configure following options while setting up AD. Enable Activate LDAP in order to authenticate users from AD/LDAP. Click on the Next button to add user store.
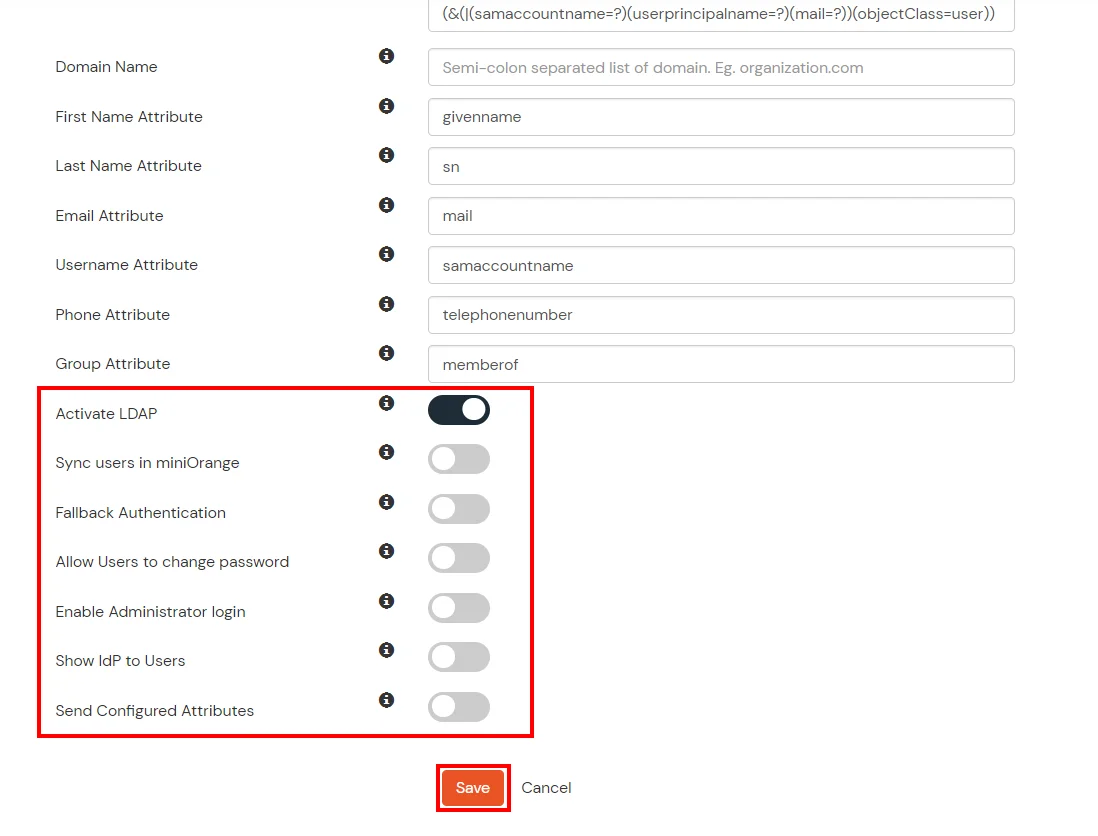
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute |
Description |
| Activate LDAP |
All user authentications will be done with LDAP credentials if you Activate it |
| Fallback Authentication |
If LDAP credentials fail then user will be authenticated through miniOrange |
| Enable administrator login |
On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users |
If you enable this option, this IdP will be visible to users |
| Sync users in miniOrange |
Users will be created in miniOrange after authentication with LDAP |
- Click on the Next button, or go to the Attributes tab.
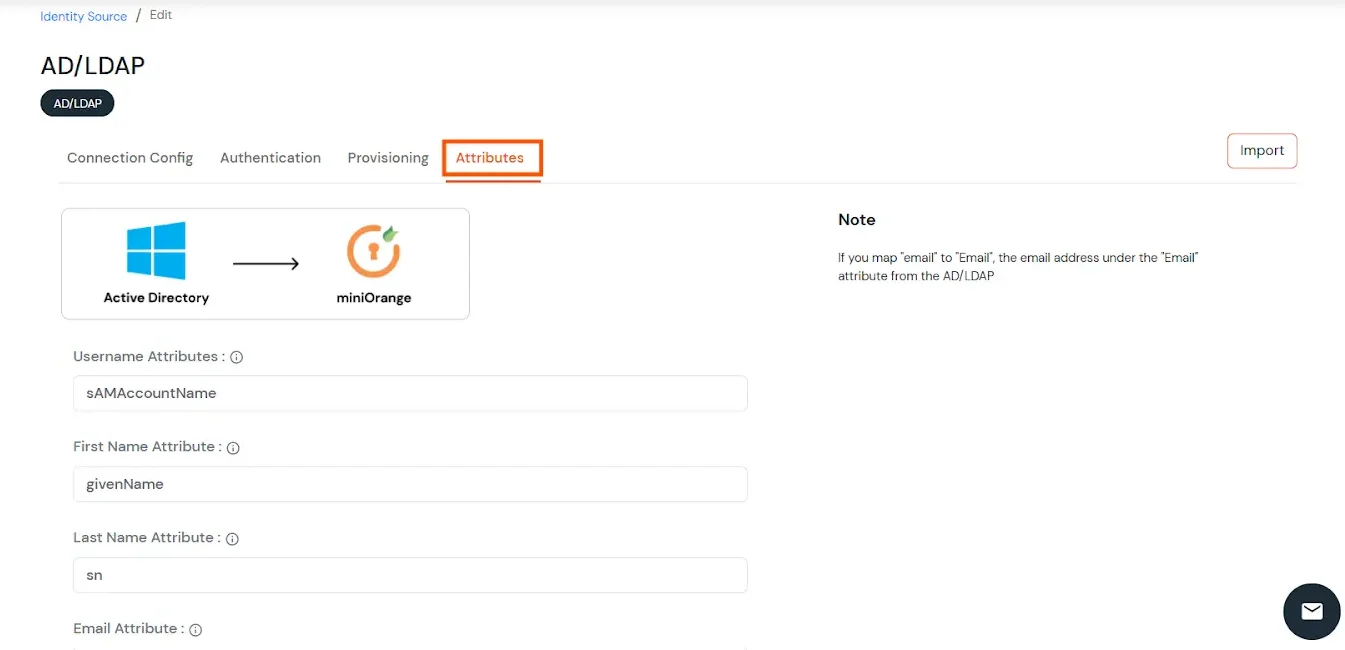
Attributes Mapping from AD
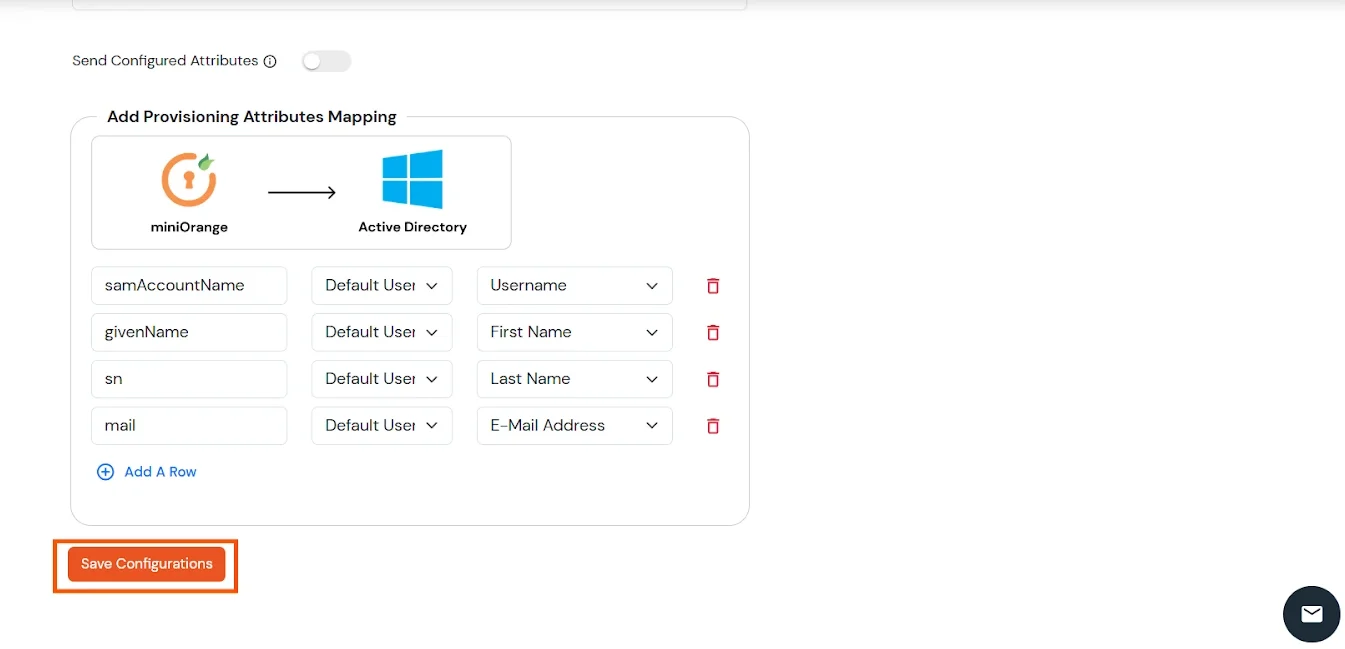
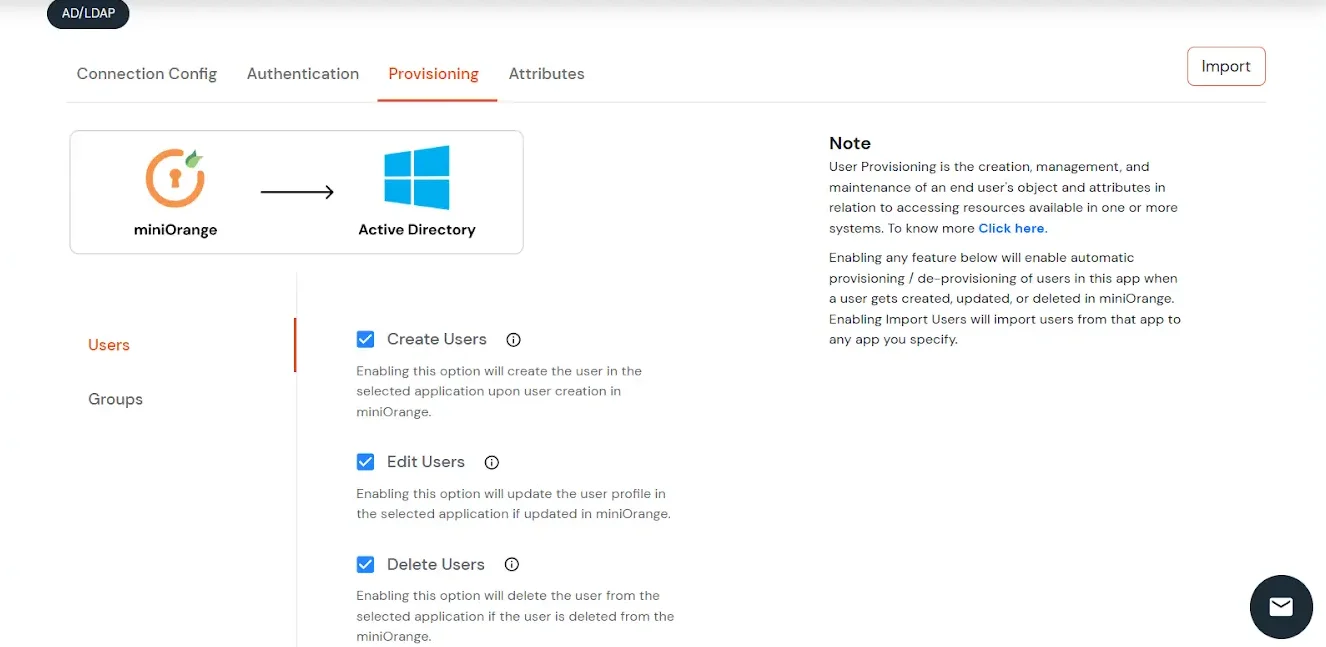
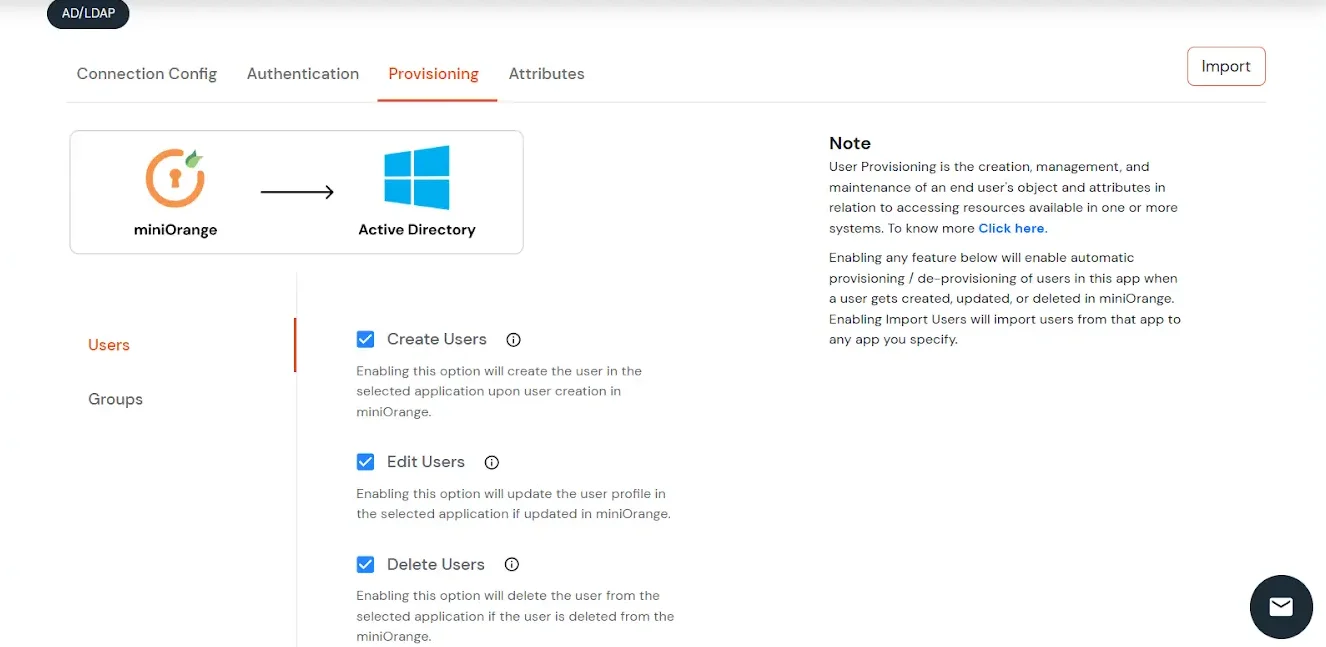
User Import and Provisioning from AD
- If you want to set up provisioning, click here for detailed information. We will skip this step for now.
Import Password Policy from AD
- If you want to import your Active Directory password policy into miniOrange, click here for detailed information. We will skip this step for now.
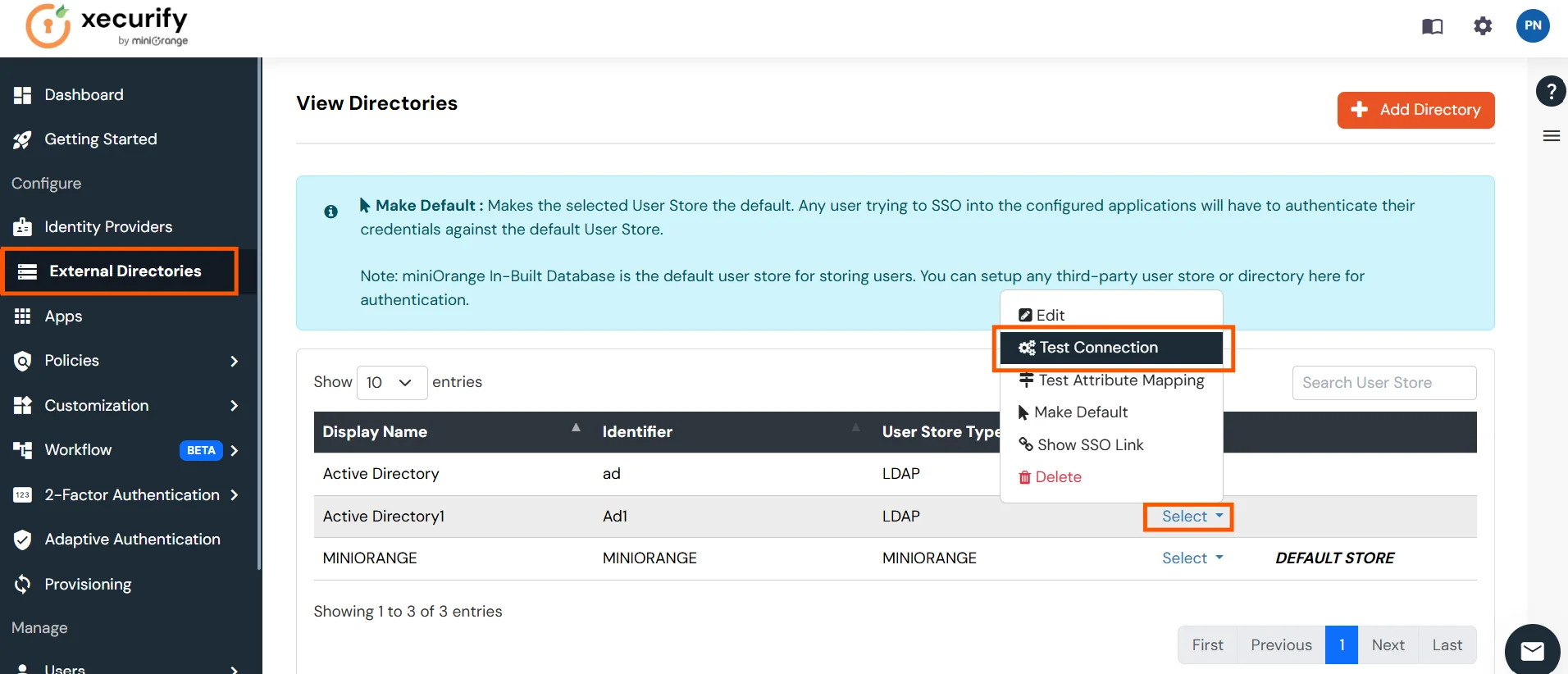
Test Connections
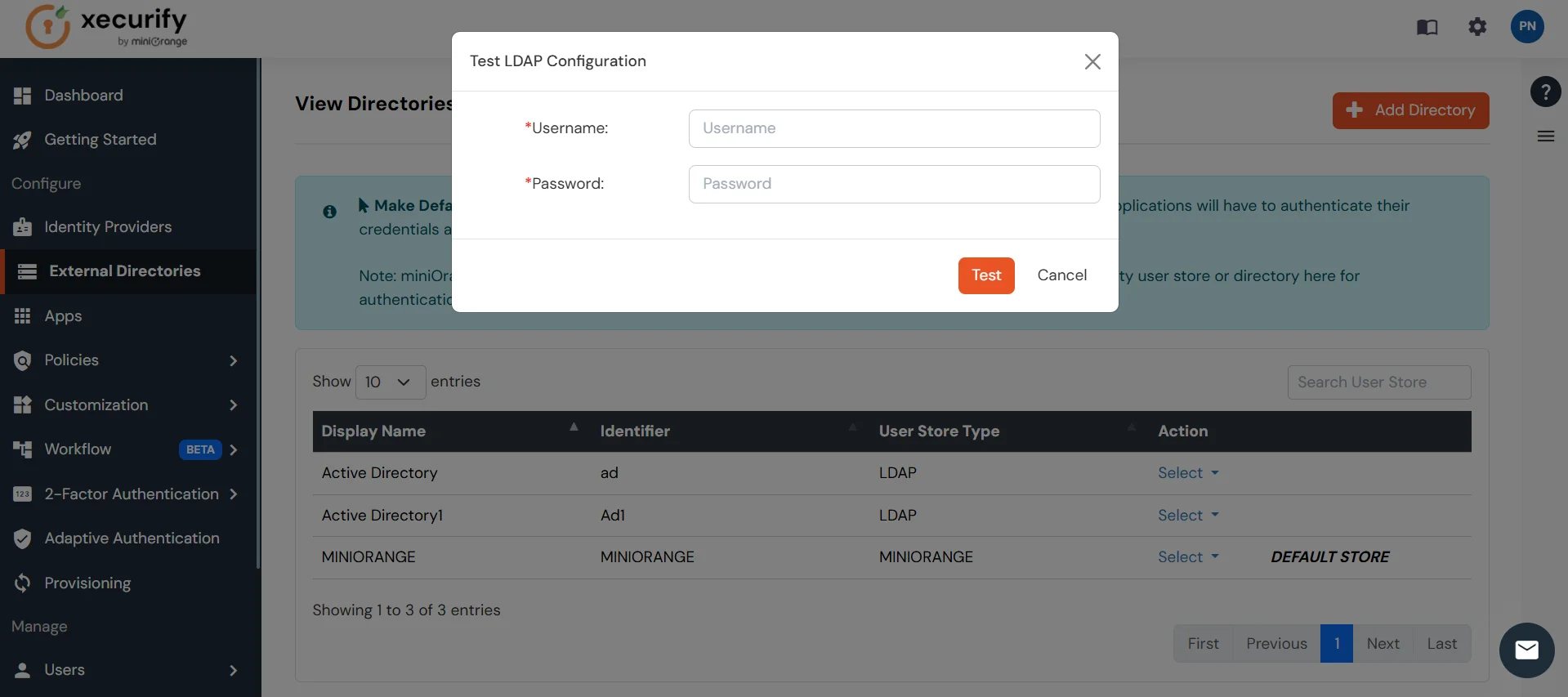
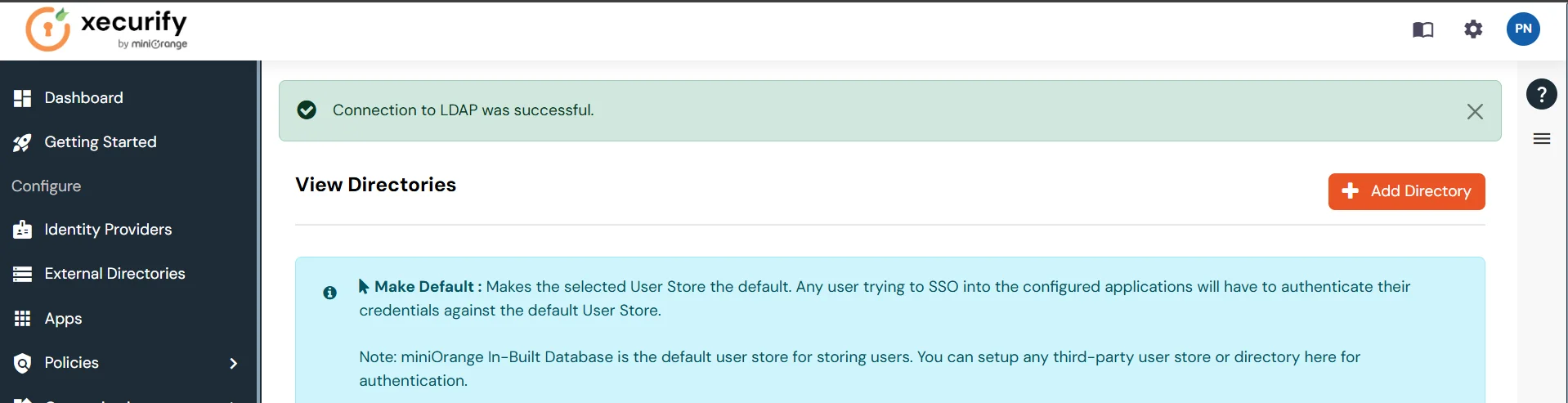
- You will see a list of directories under Identity Providers. From the dropdown, select AD/LDAP Directories, search for your configured directory, click the three dots next to it, and select Test Connection.
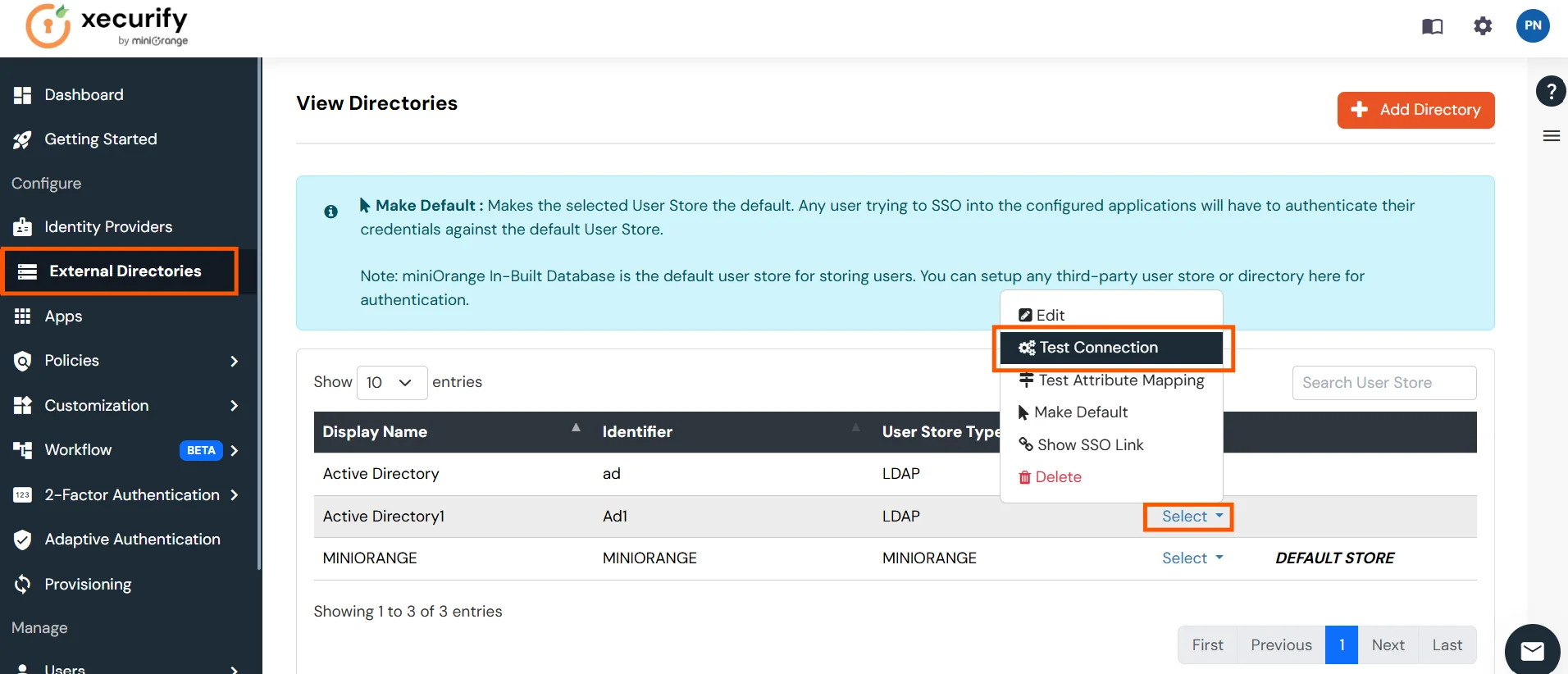
- A pop-up appears prompting you to enter a username and password to verify your LDAP configuration.
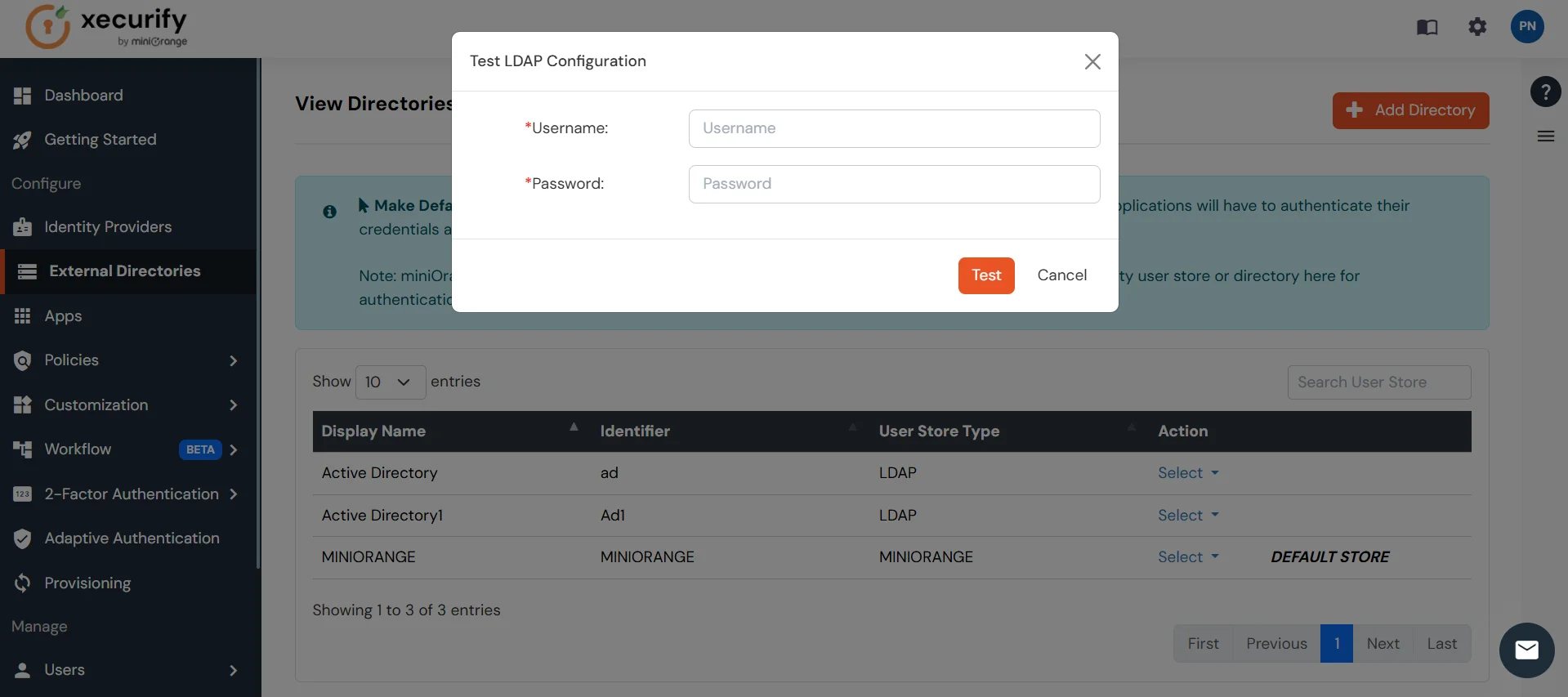
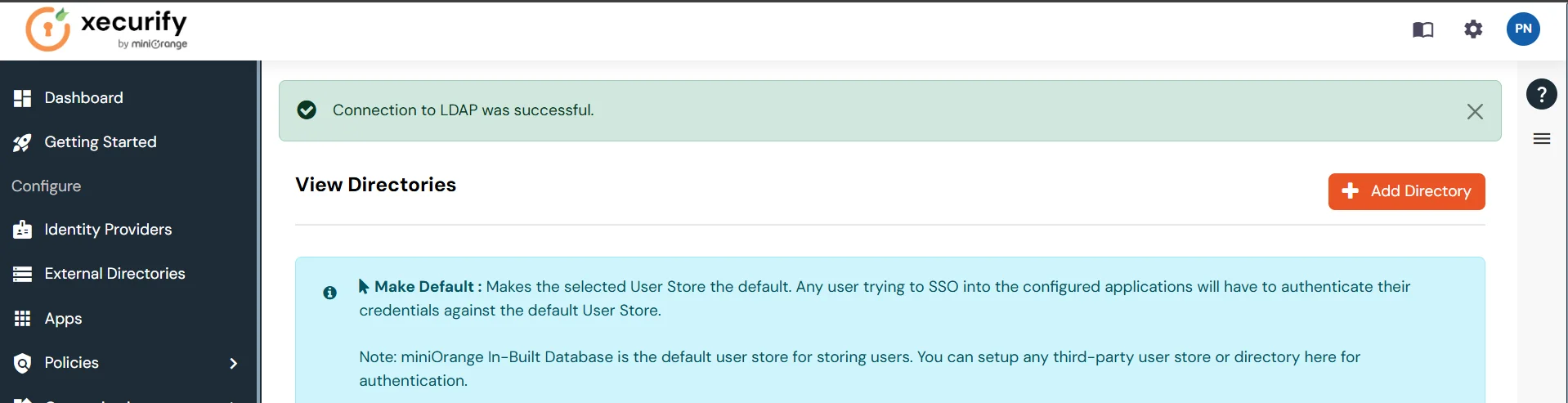
- On Successful connection with LDAP Server, a success message is shown.
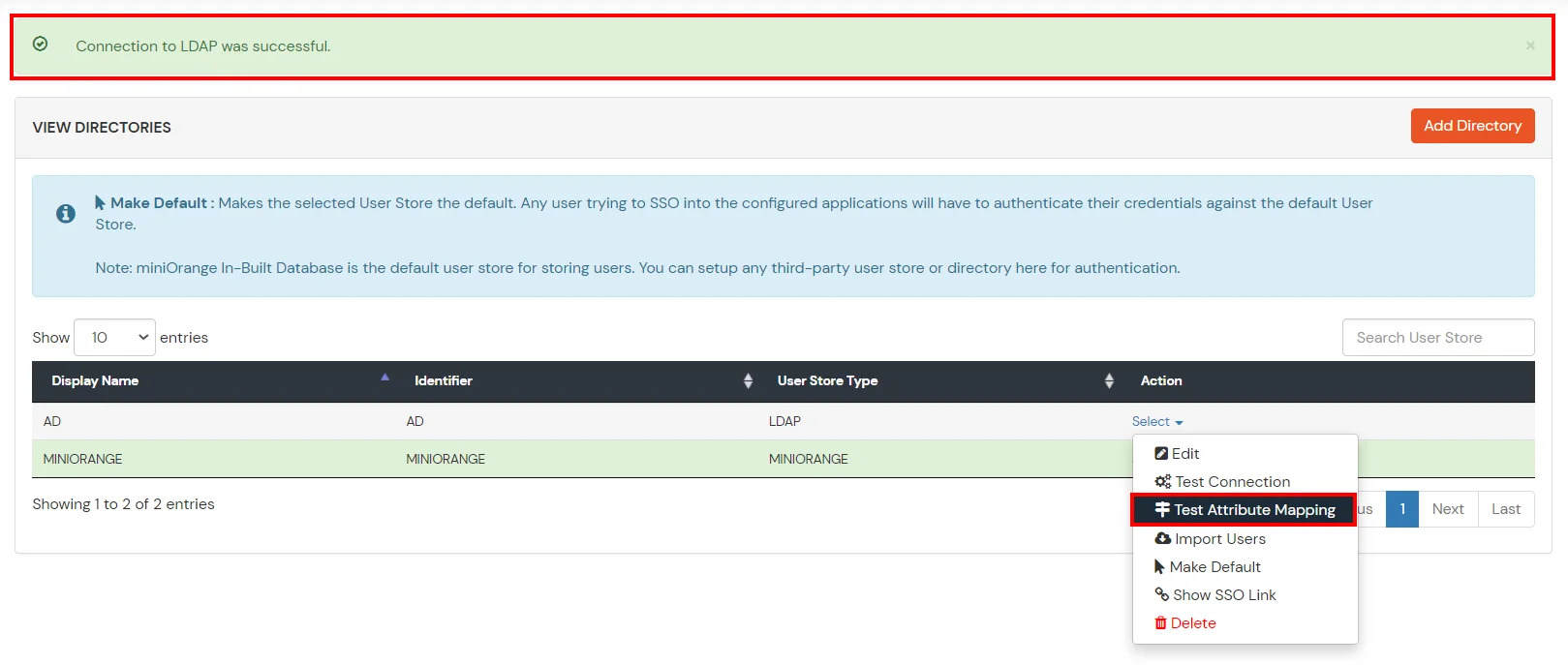
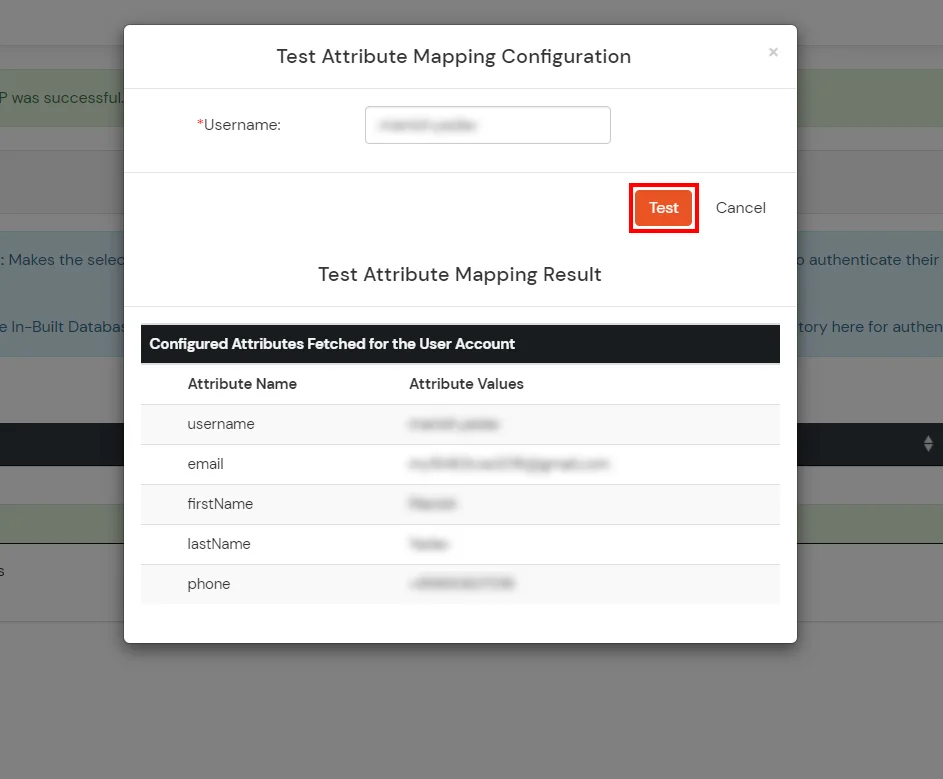
Test Attribute Mapping
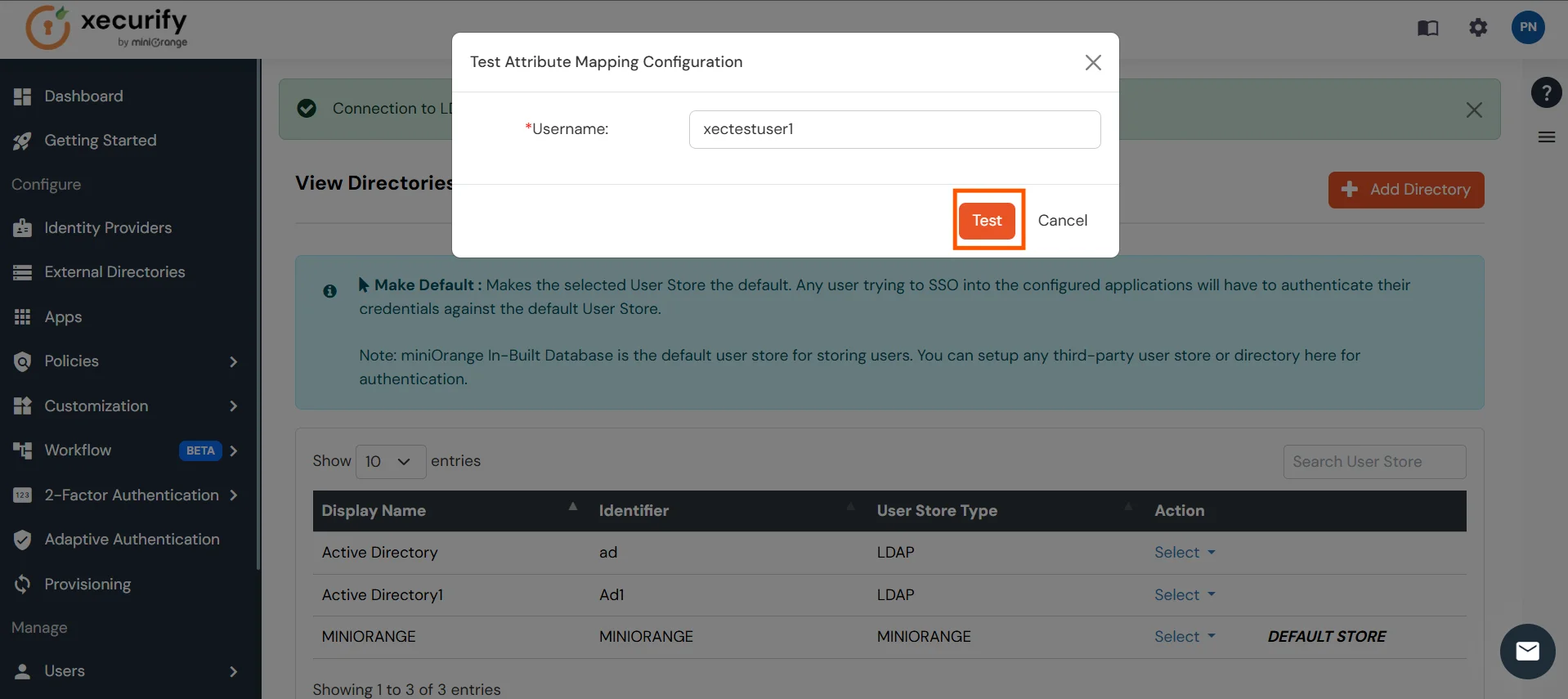
- You will see a list of directories under Identity Providers. From the dropdown, select AD/LDAP Directories, search for your configured directory, click the three dots next to it, and select Test Attribute Mapping.
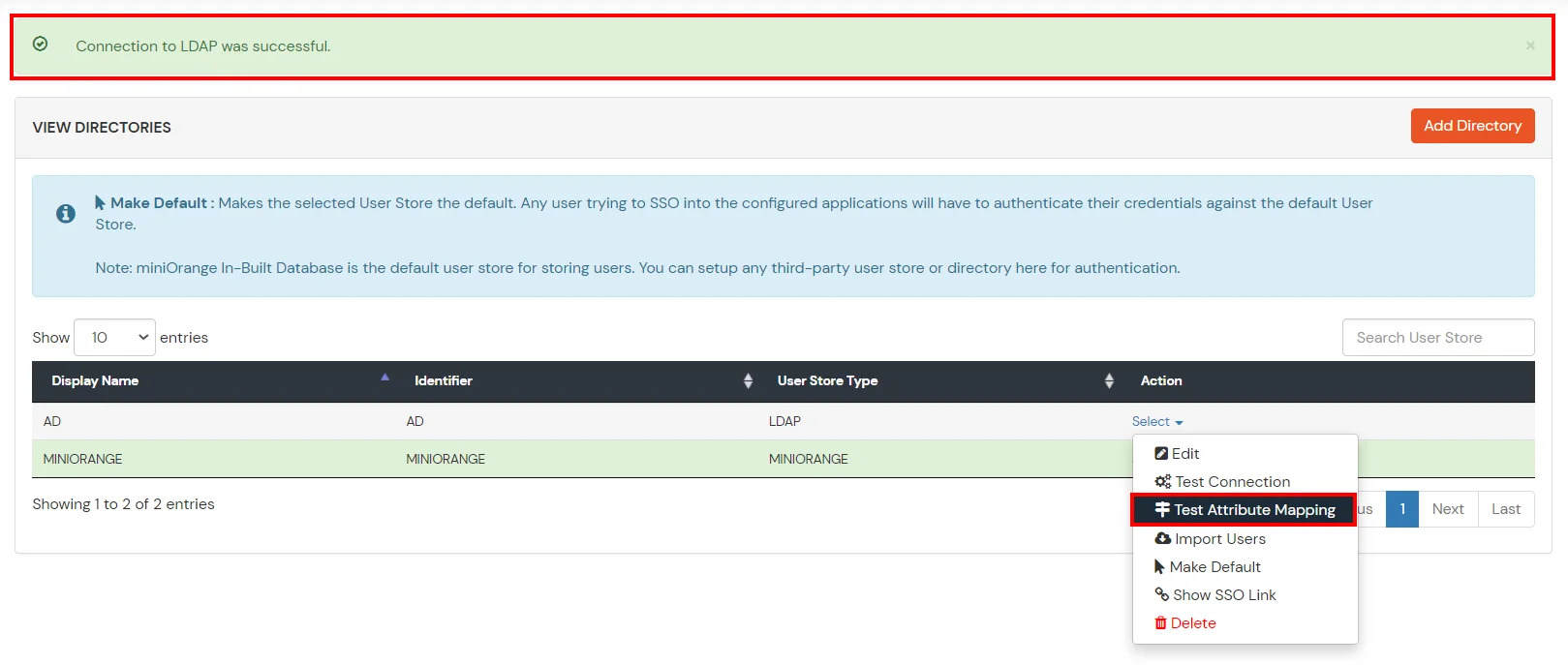
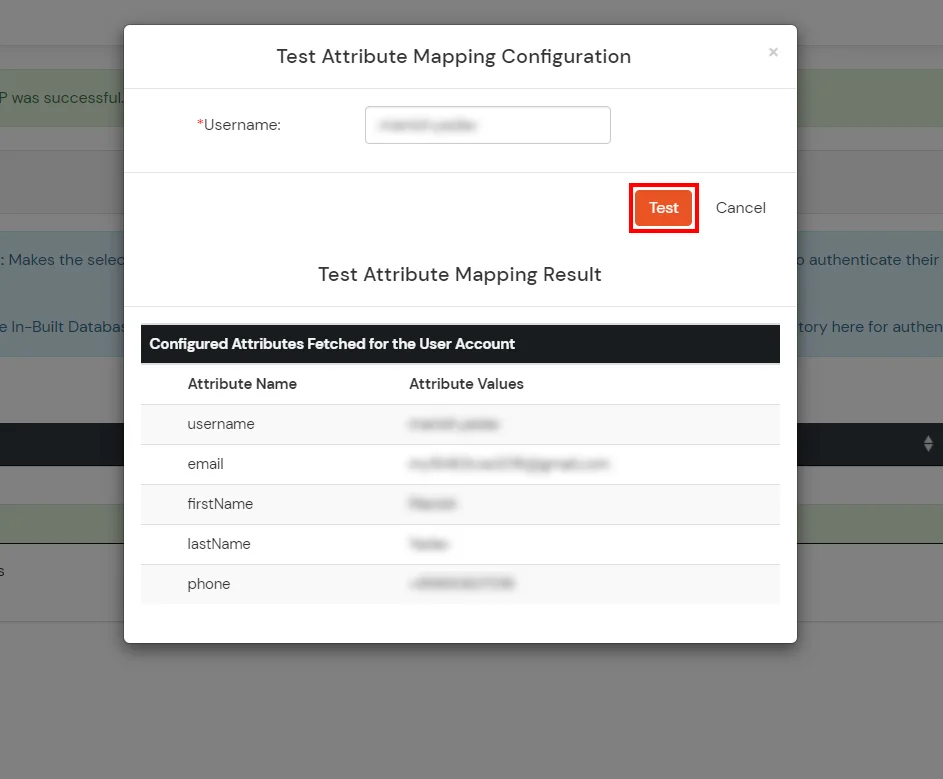
- A pop‑up appears to enter a username and click Test.
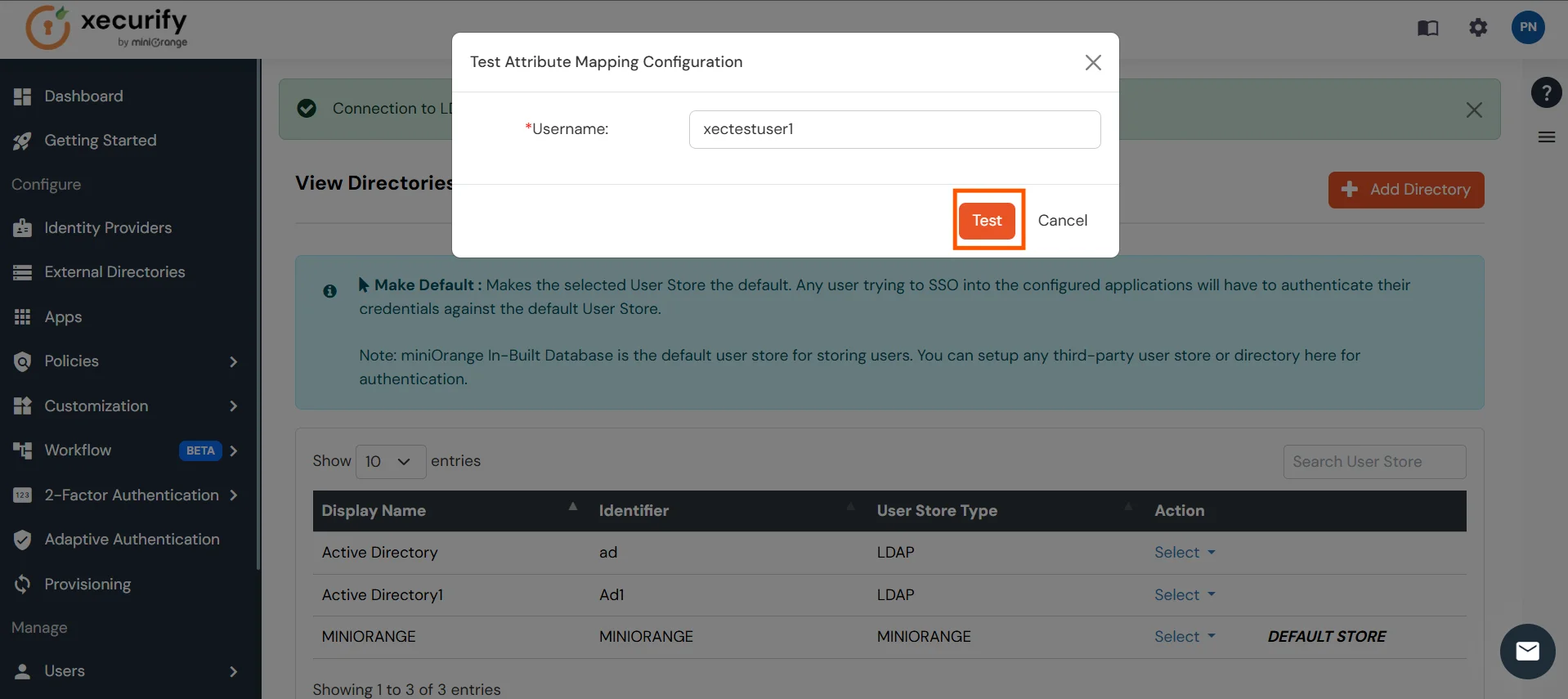
- The Test Attribute Mapping Result will be displayed.
Set up AD as External Directory configuration is complete.
Note: Refer our guide to setup LDAP on windows server.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
4. Test SSO Configuration
Using SP Initiated Login
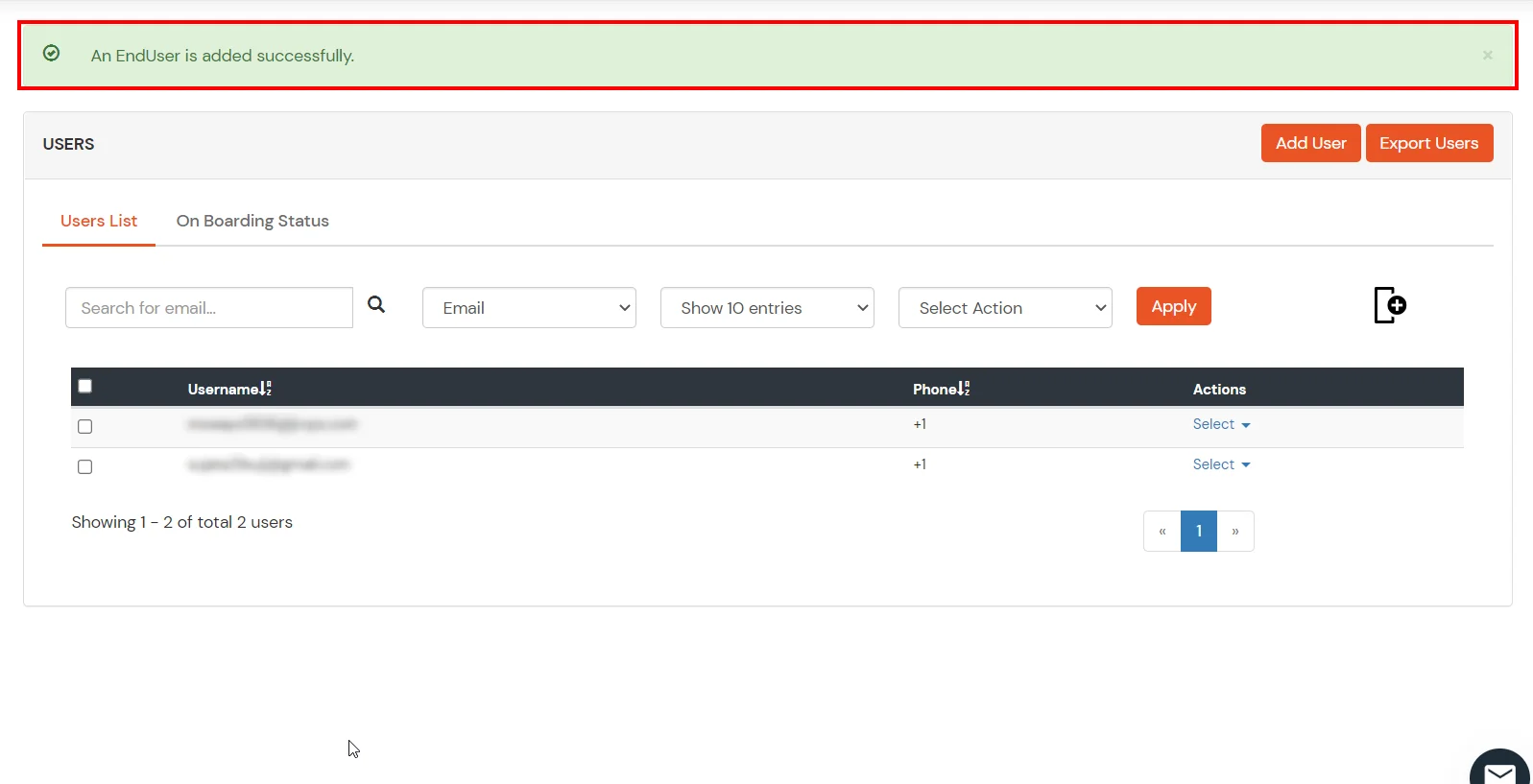
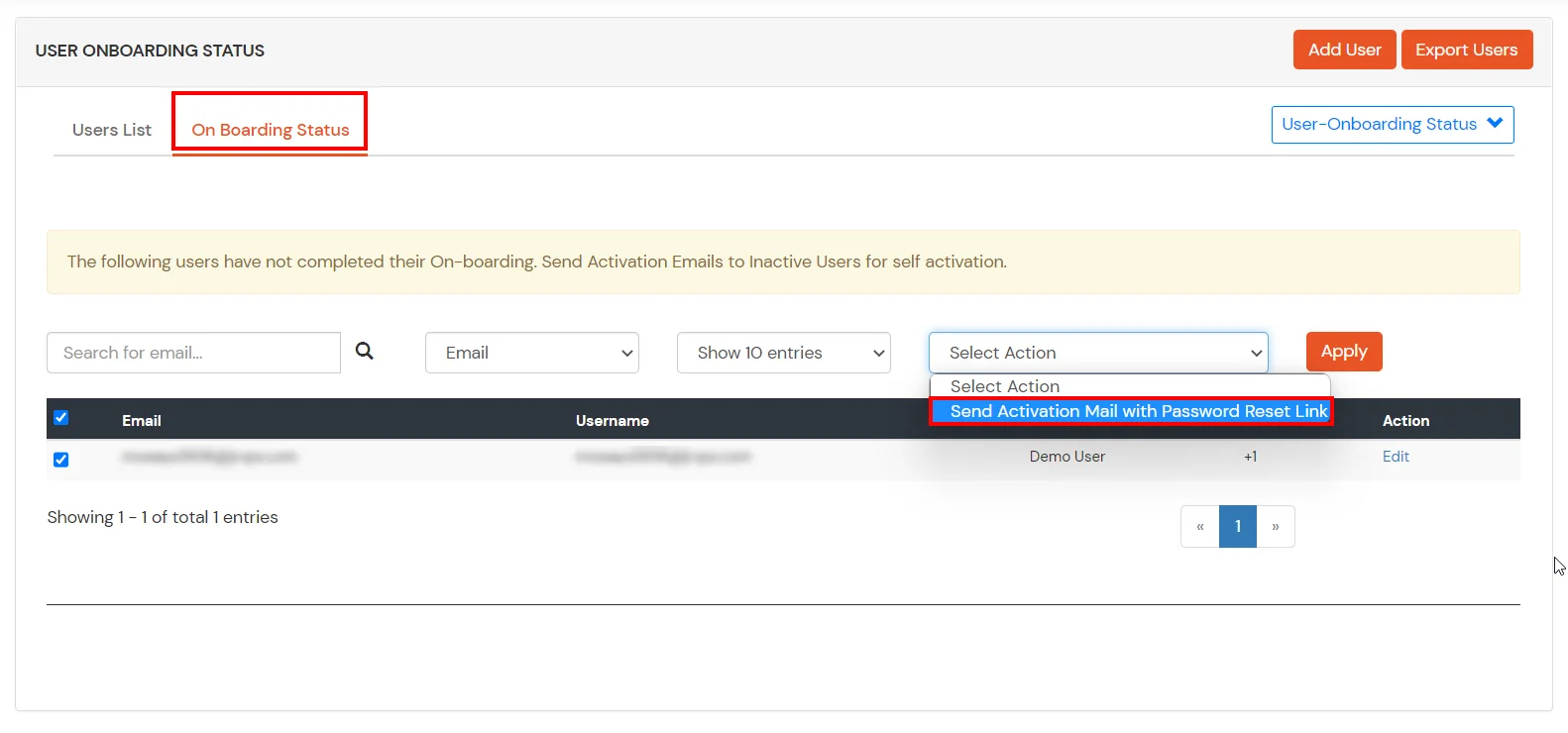
- Lets say you have configured miniOrange as your userstore.
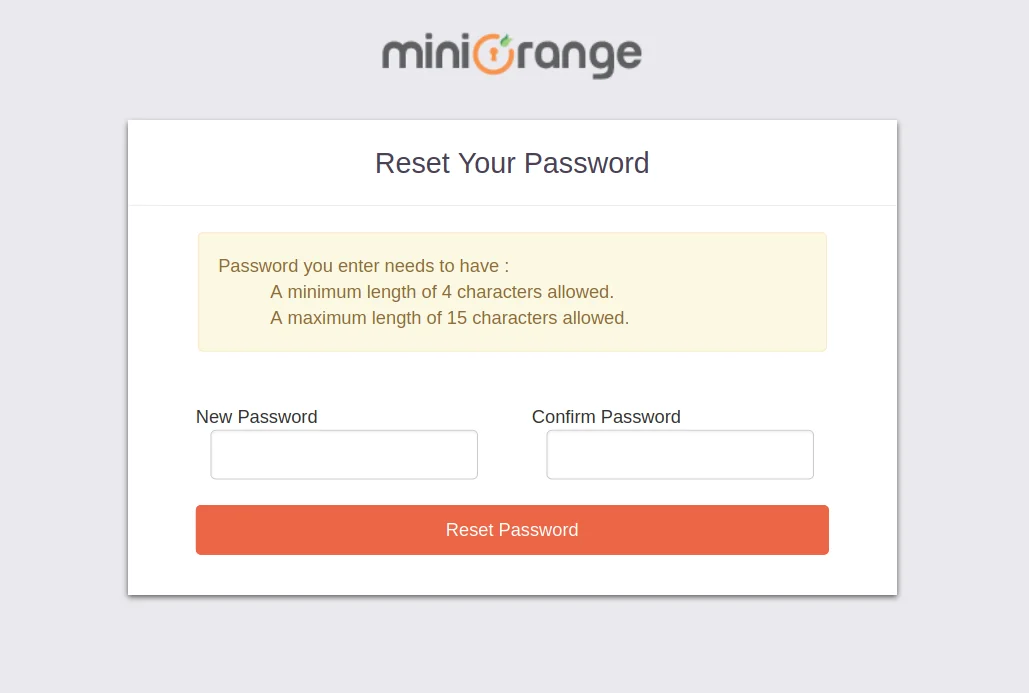
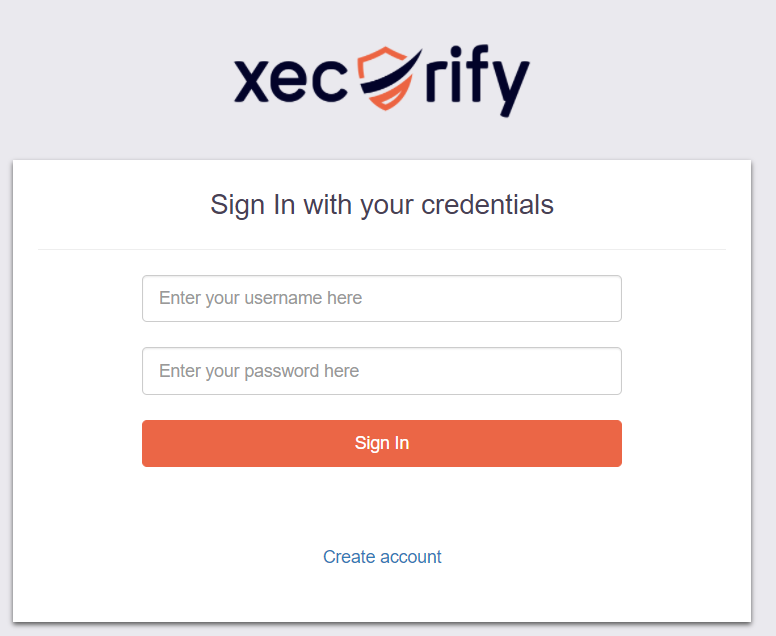
- On accessing the Single sign-On URL as mentioned in the second step, you will be asked for miniOrange credentials.
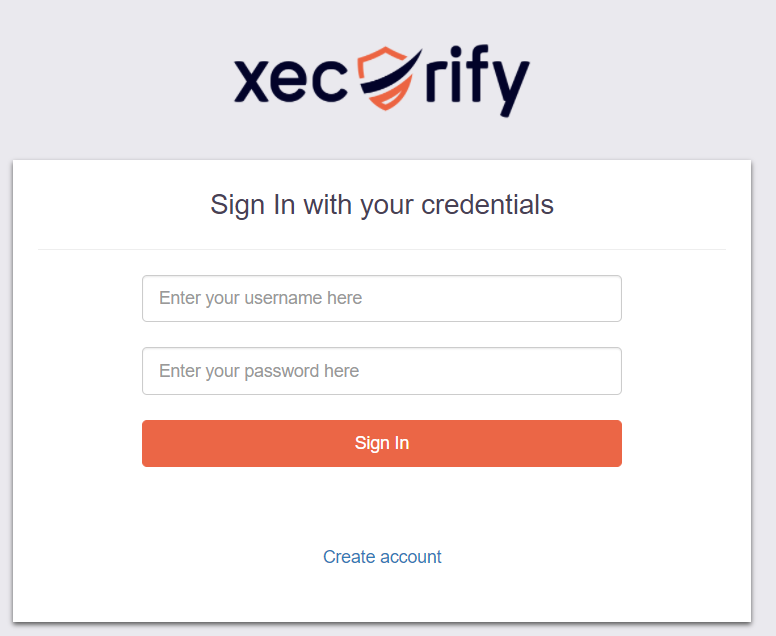
- On entering the valid credentials, you will be successfully logged into Wix.
Using IDP Initiated Login
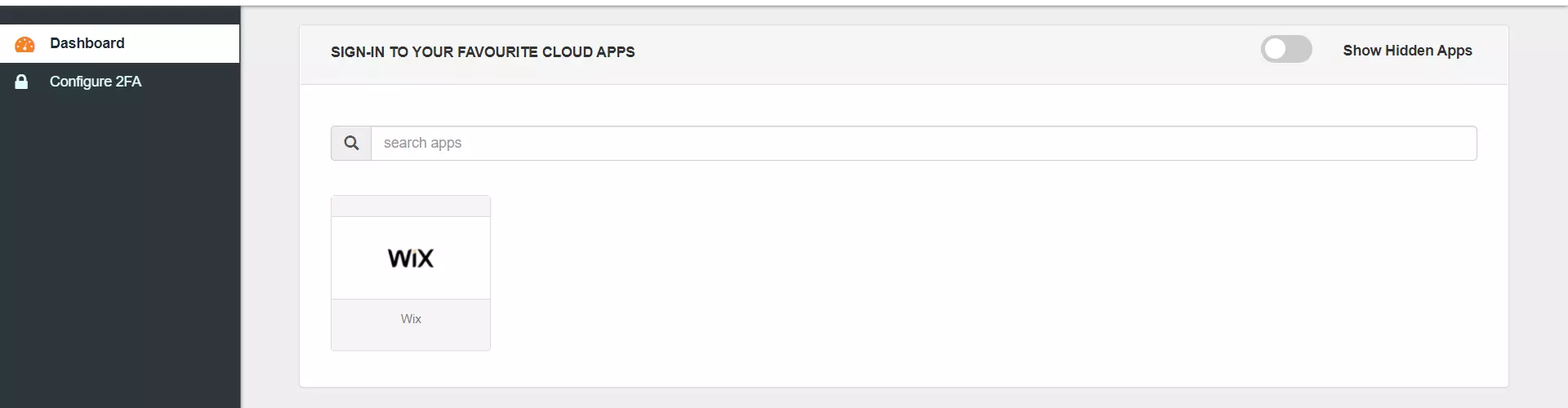
- Log into miniOrange IdP using your credentials.
- On the End User-Dashboard, click on the Wix application configured, to test the SSO flow.
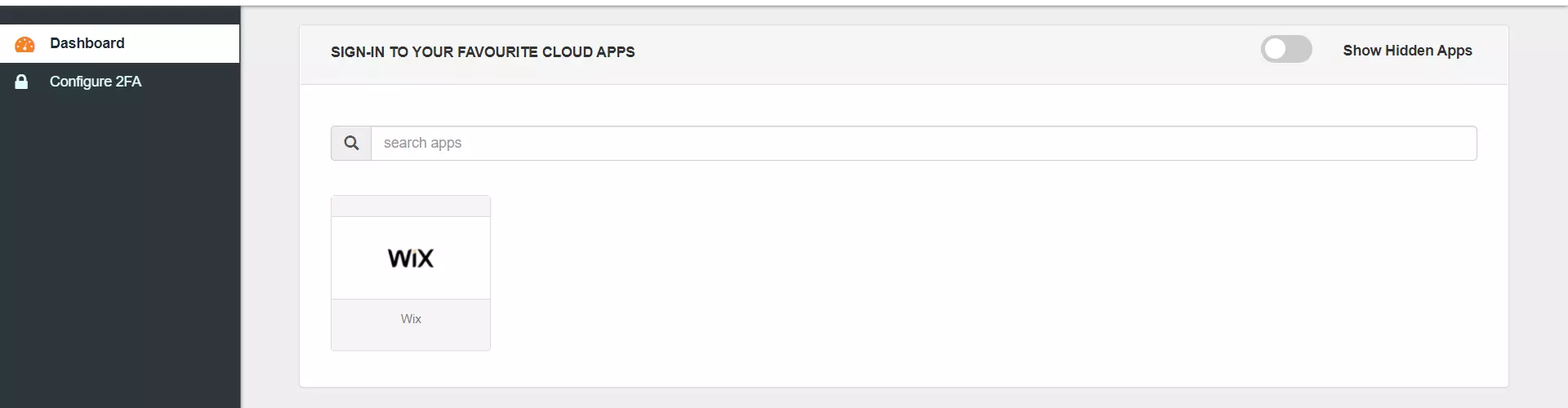
- You will be successfully logged into Wix site.
Using SP Initiated Login
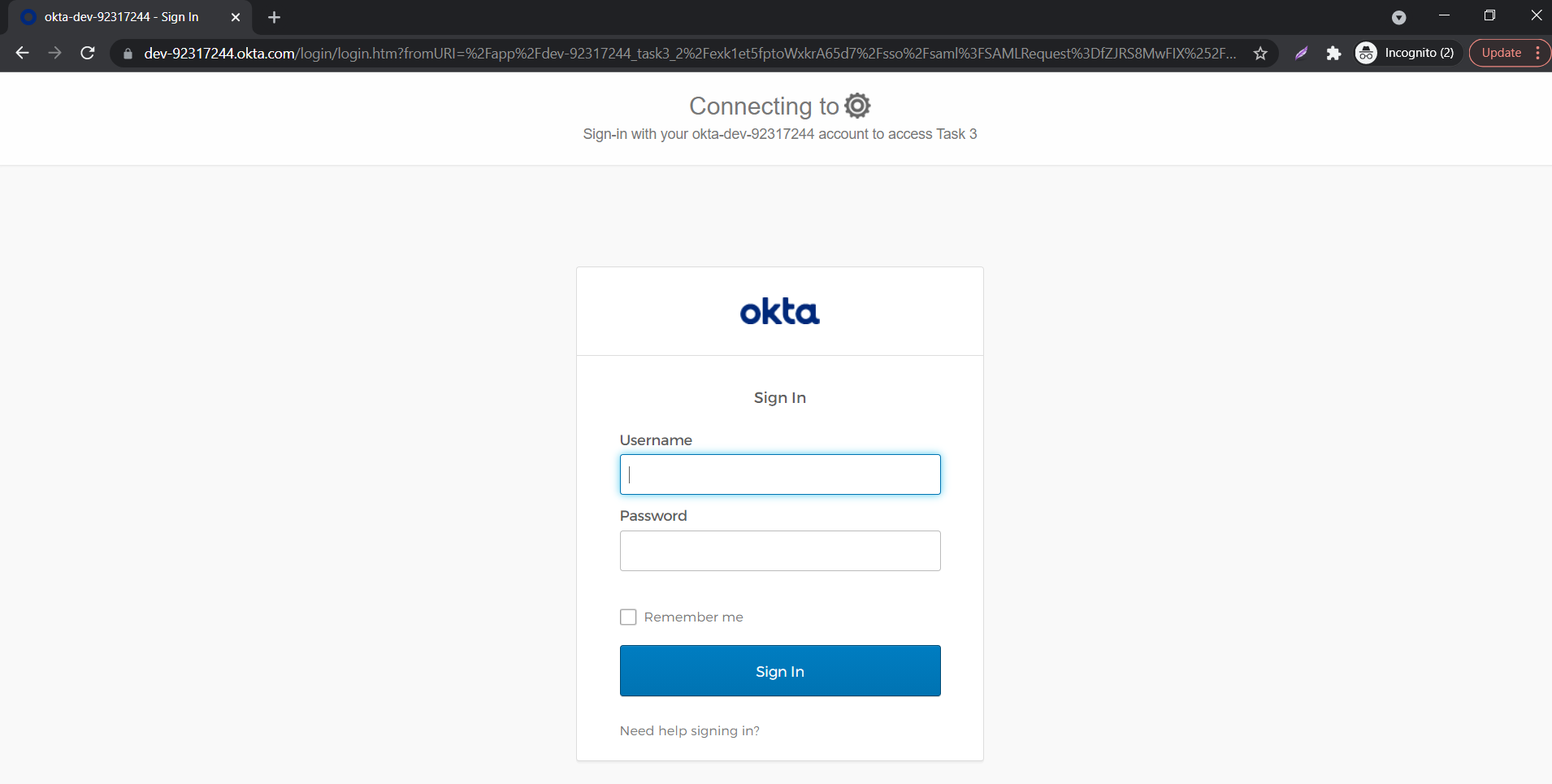
- Lets say you have configured Okta as IDP.
- On accessing the Single sign-On URL as mentioned in the second step, you will be asked to enter your Okta credentials.
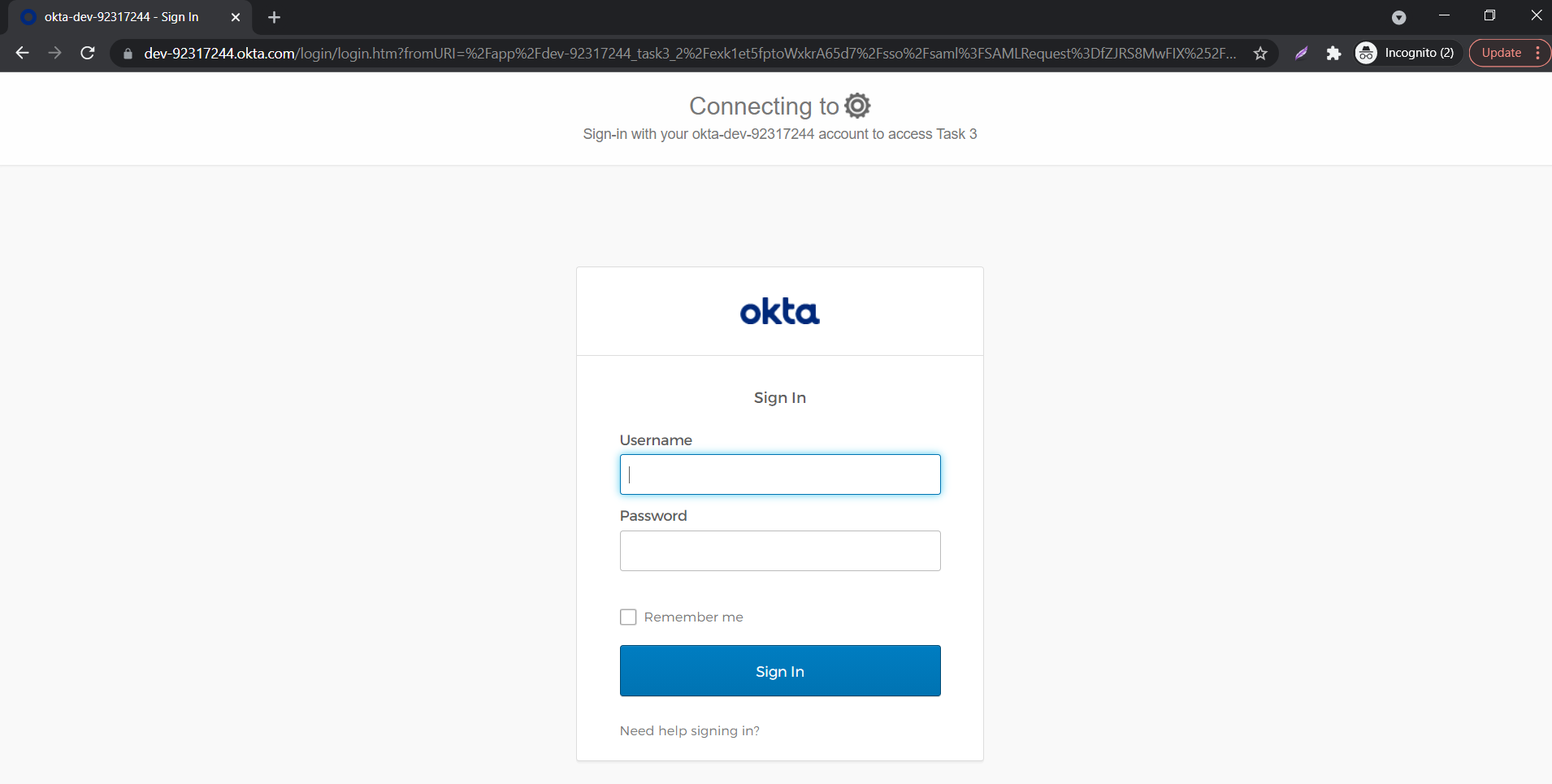
- On entering the valid credentials, you will be successfully logged into Wix site.
![Wix Single Sign-On (SSO): Wix Login]()
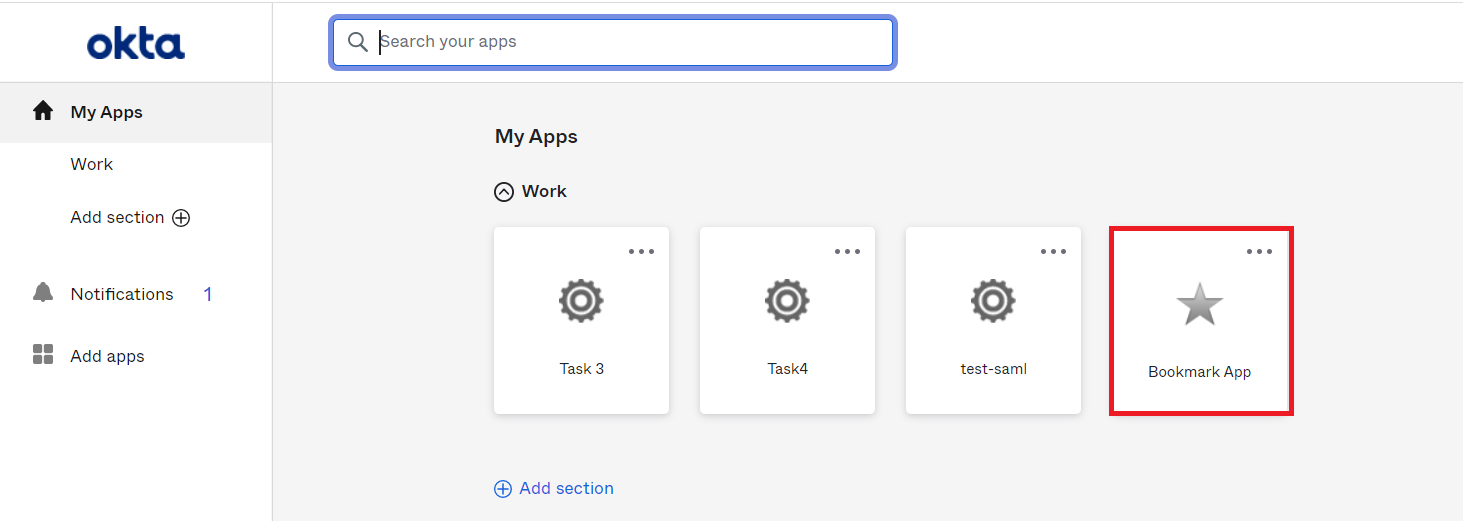
Using IDP Initiated Login
- Log into Okta using your credentials.
- Click on Admin to access the Admin Console, then click on Applications.
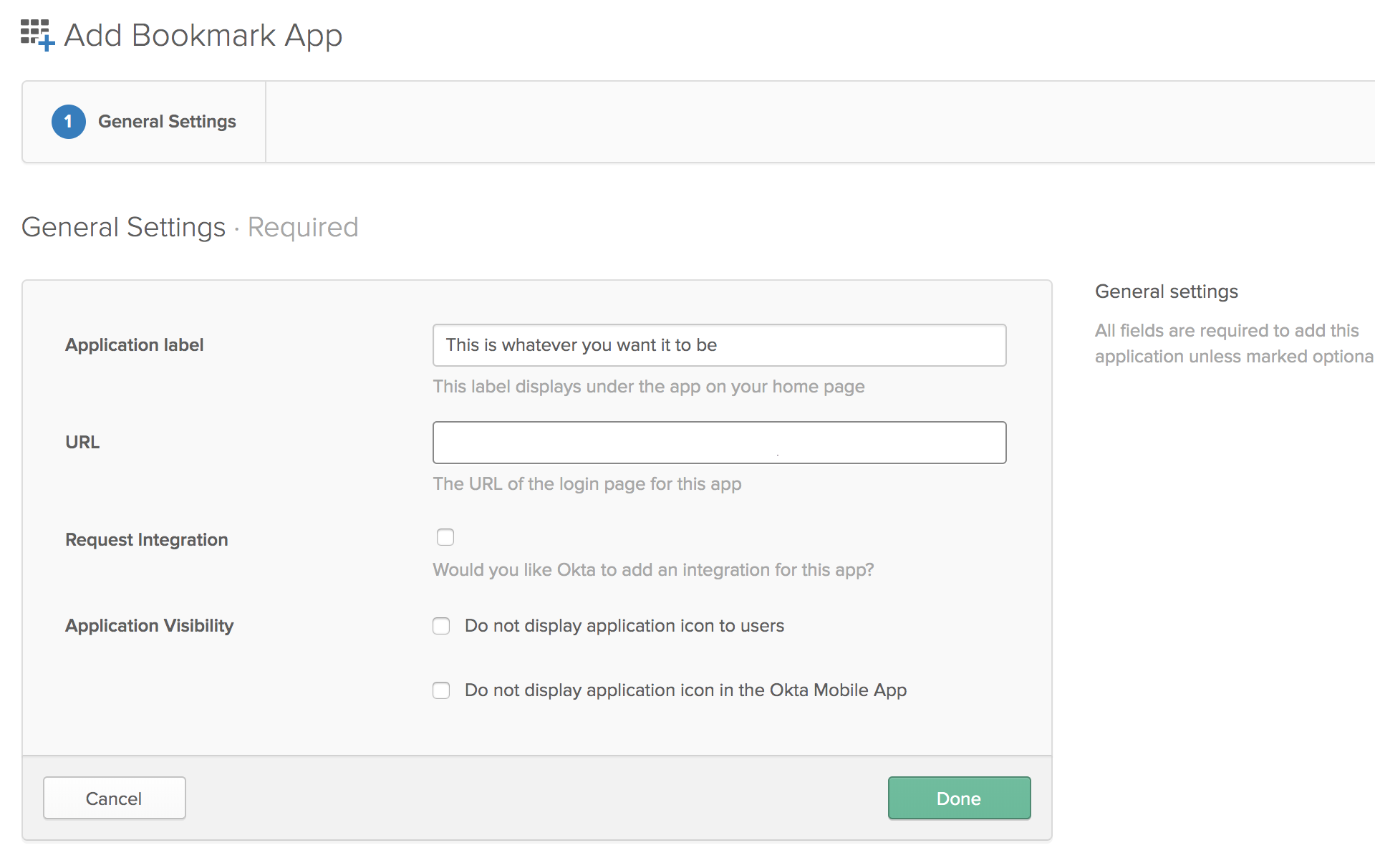
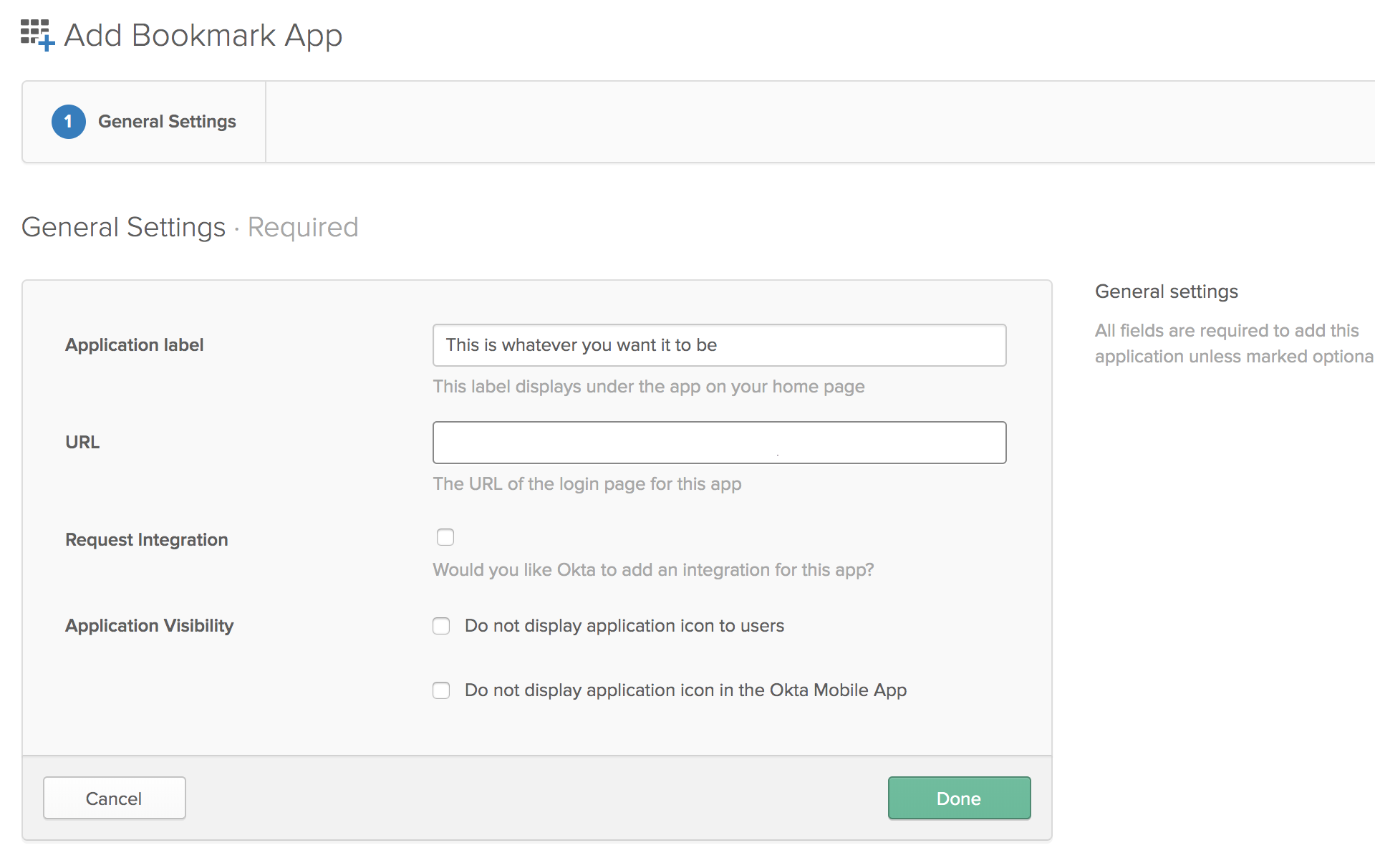
- Click on Add Application and search for "Bookmark App", and Click Add in the left pane.
- Choose an app name of your choice which will be the display name.
- In the URL section, enter the SSO URL that is given in the JWT app.
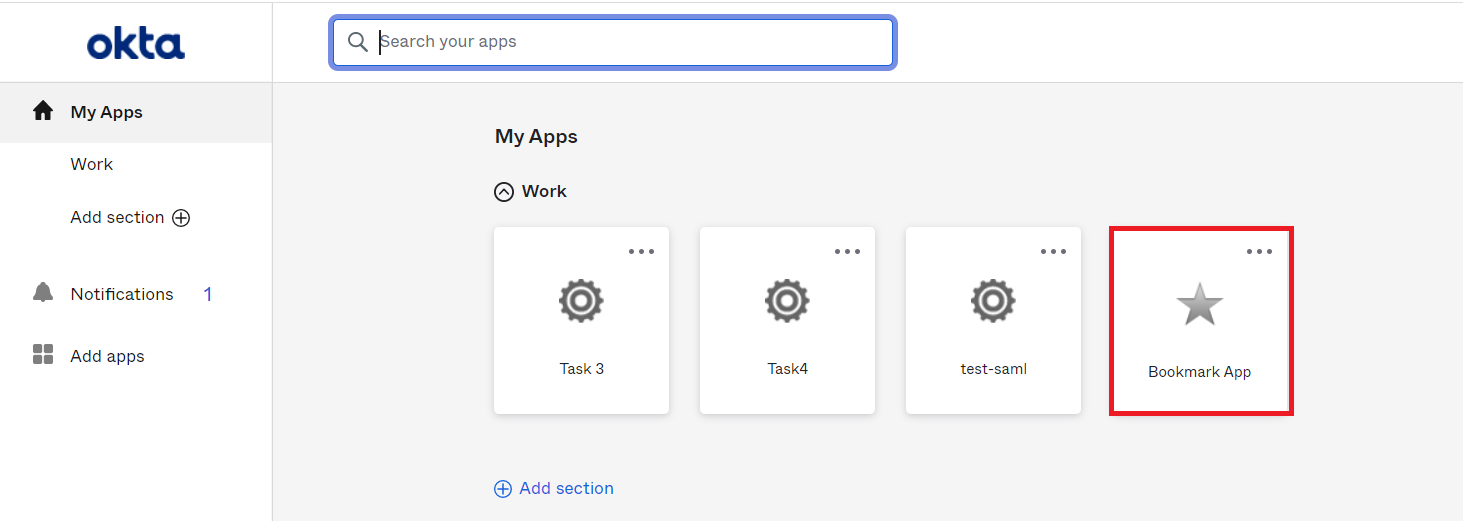
- Click on Save.
- On the End User-Dashboard, click on the Wix bookmark application configured, to test the SSO flow.
- You will be successfully logged into Wix.
External References
Frequently Asked Questions
Yes, that is absolutely possible with the current miniOrange Wix SSO solution.
You can enable SSO into Wix using Okta or any other IDP as the primary authentication source. We can do this using miniOrange Broker Service.
Yes, even if you have configured SSO, existing users’ data will not be lost. They can continue logging in. Our solution makes use of the user’s email address. In other words, if the same user logs into Wix using the same email address as before, he will see his personal data as it was before