Websphere Single Sign-On SSO
This document will help you guide setup SSO between Websphere and miniOrange. You can host any number of applications under Websphere and pass the LTPA cookie to access the user information and the session created on the Websphere level.
miniOrange and Websphere Single Sign-On (SSO) integration supports the following features:
- SP Initiated Single Sign-On (SSO)
- IdP Initiated Single Sign-On (SSO)
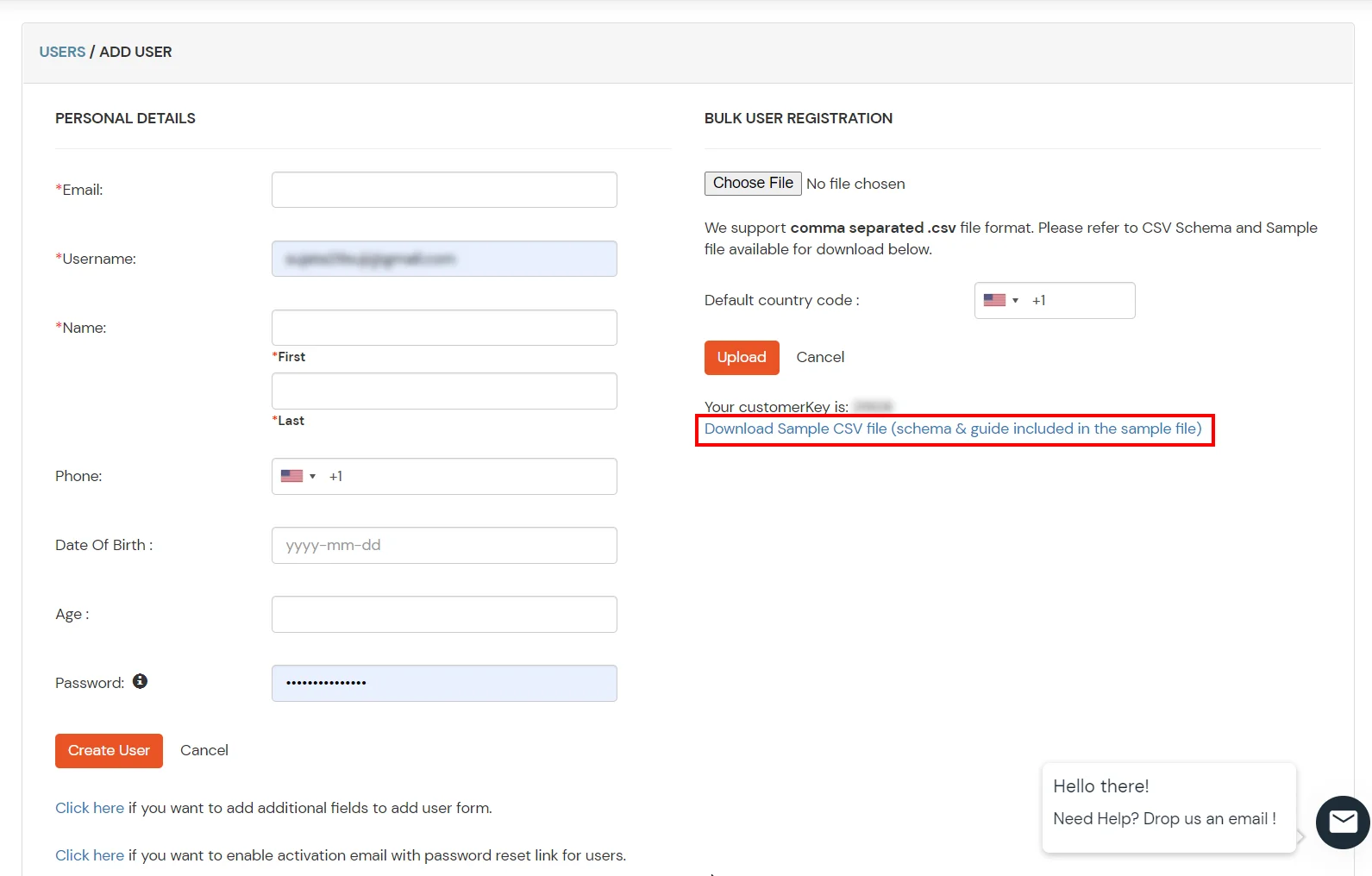
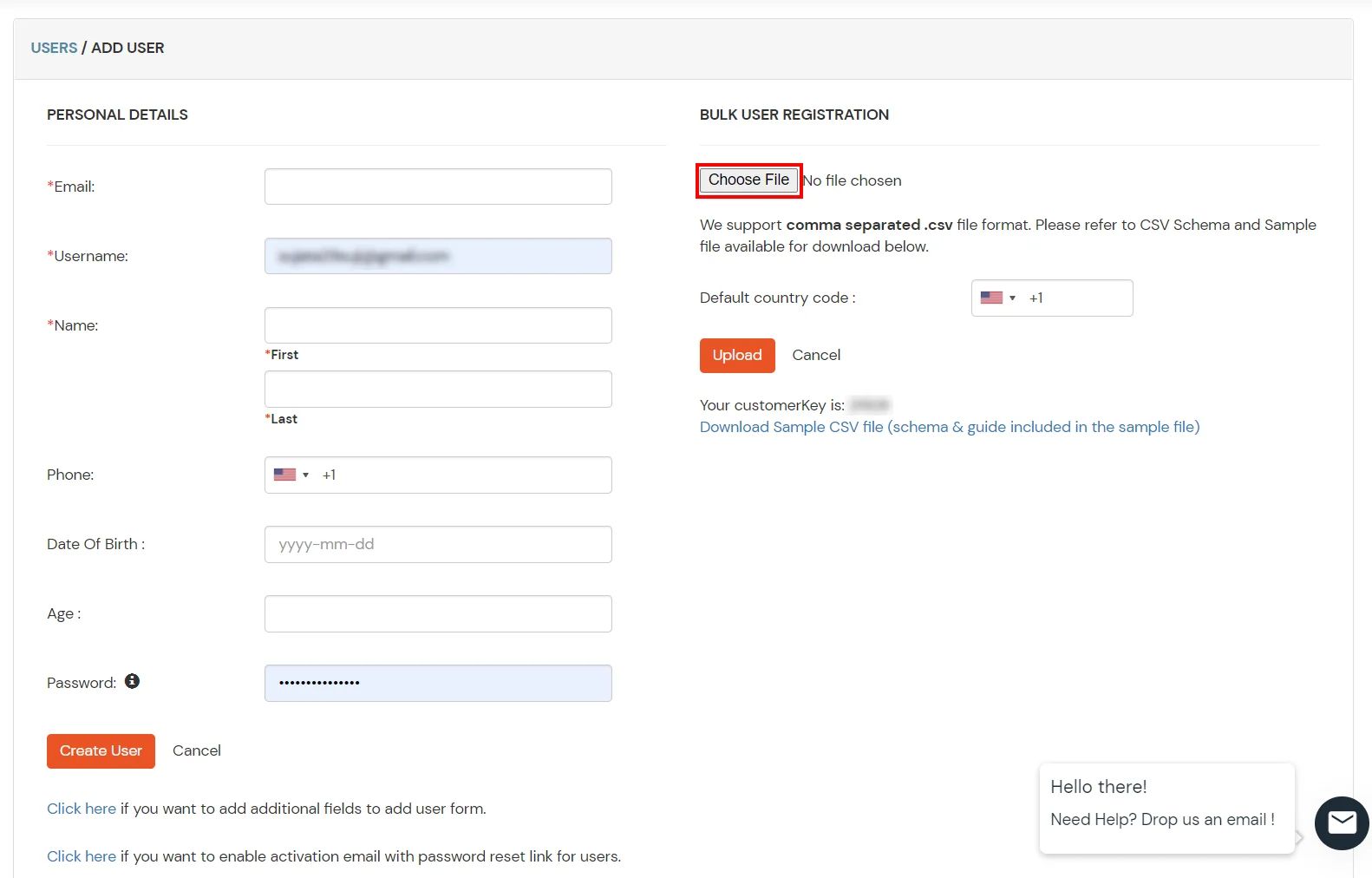
Connect with External Source of Users
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, OpenLDAP, AWS etc), Identity Providers (like Microsoft Entra ID, Okta, AWS), and many more. You can configure your existing directory/user store or add users in miniOrange.
Follow the Step-by-Step Guide given below for Websphere Single Sign-On (SSO)
1. Configure Websphere in miniOrange
- Login into miniOrange Admin Console.
- Go to Apps and click on Add Application button.

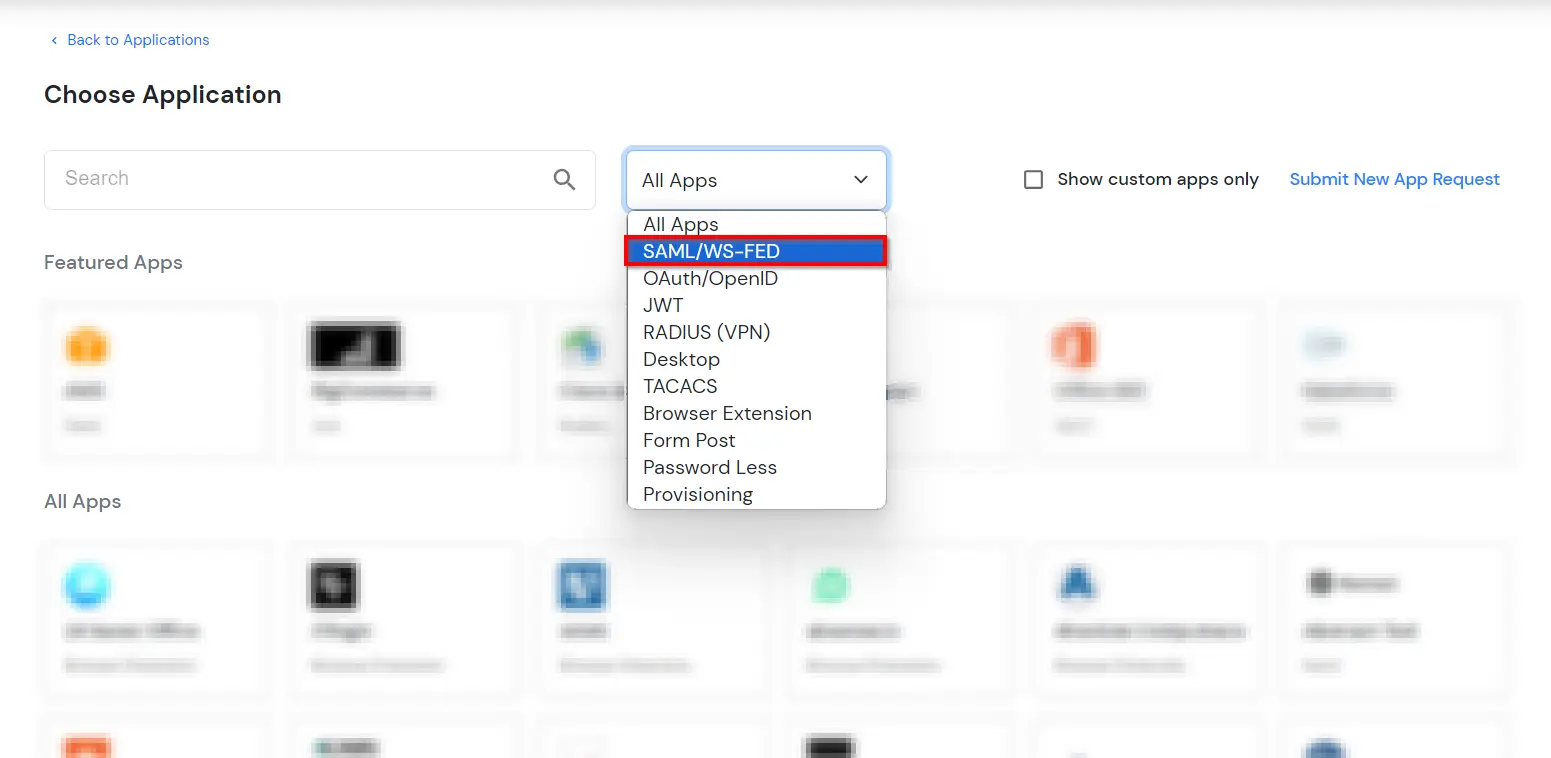
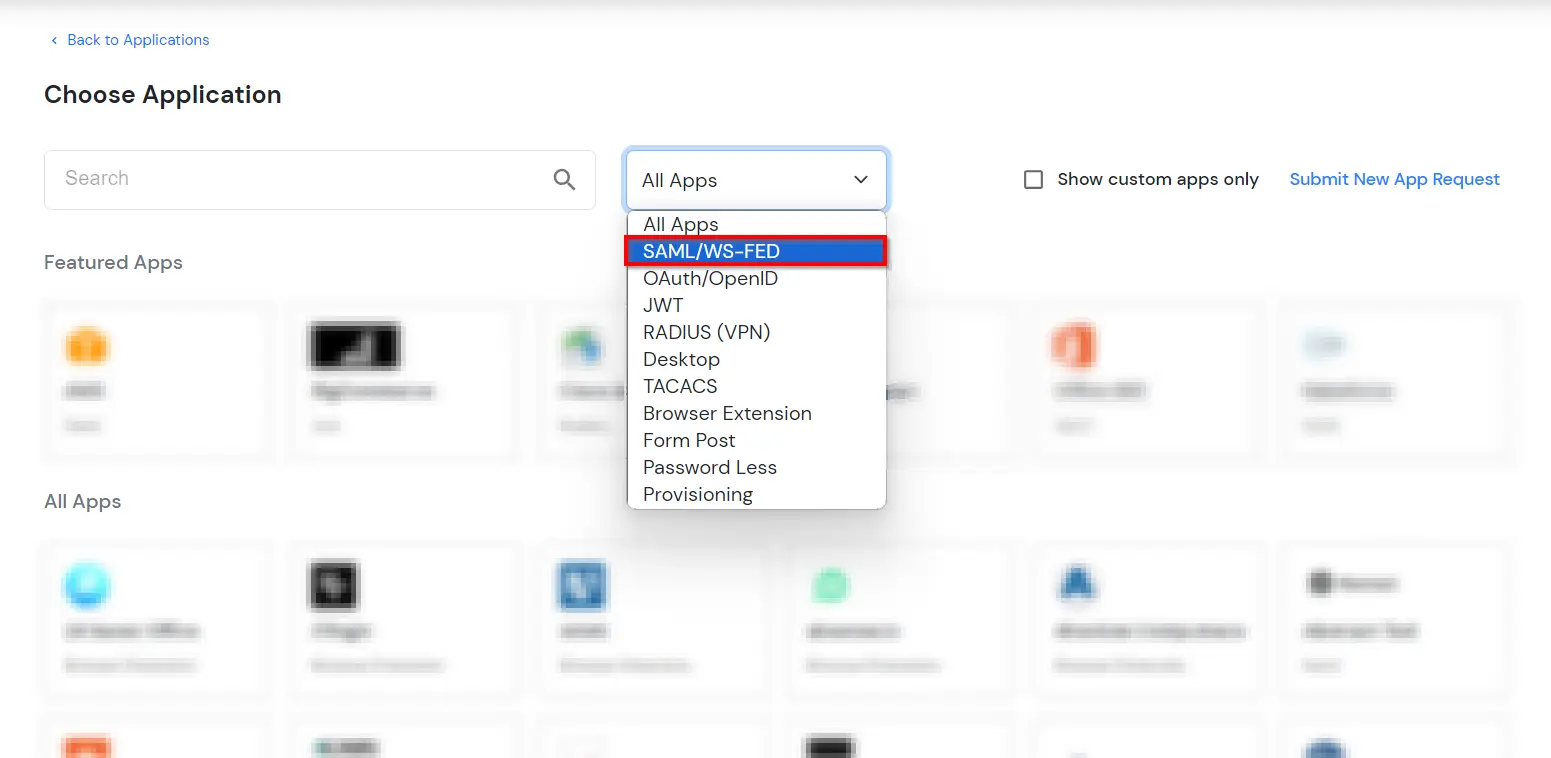
- In Choose Application Type, select SAML/WS-FED from the All Apps dropdown.
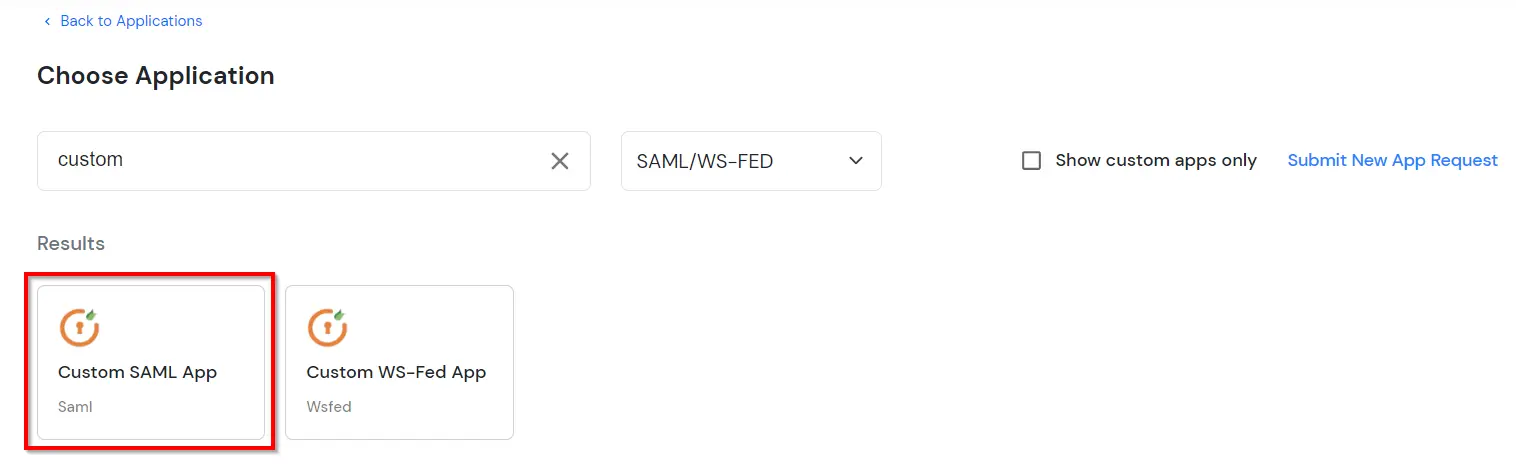
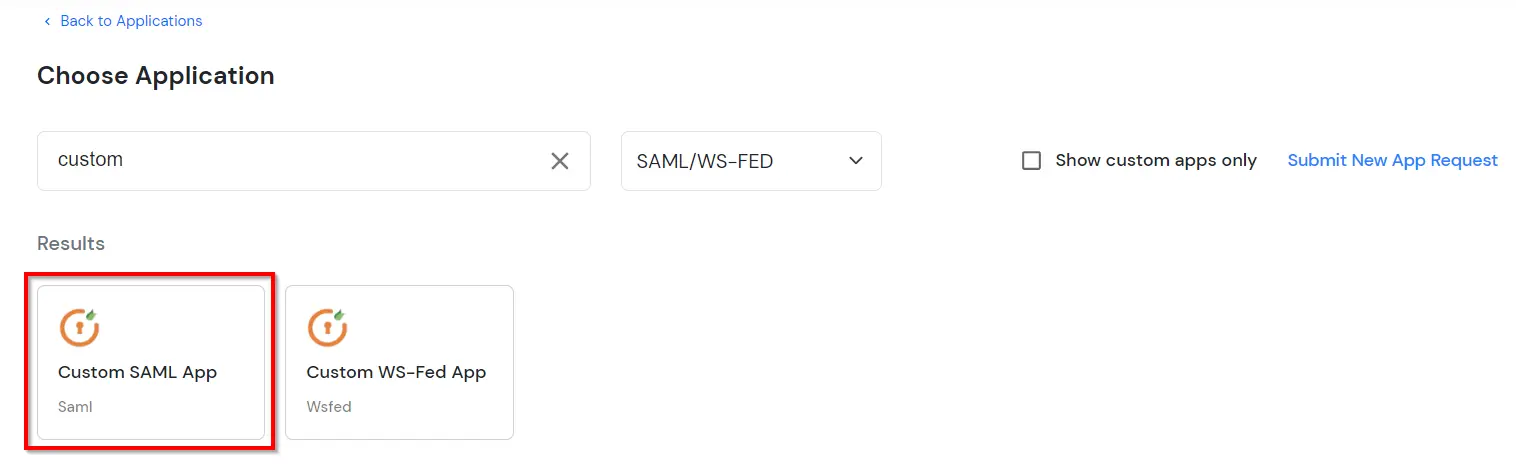
- Search for Websphere in the list, if you don't find Websphere in the list then, search for custom and you can set up your application in Custom SAML App.
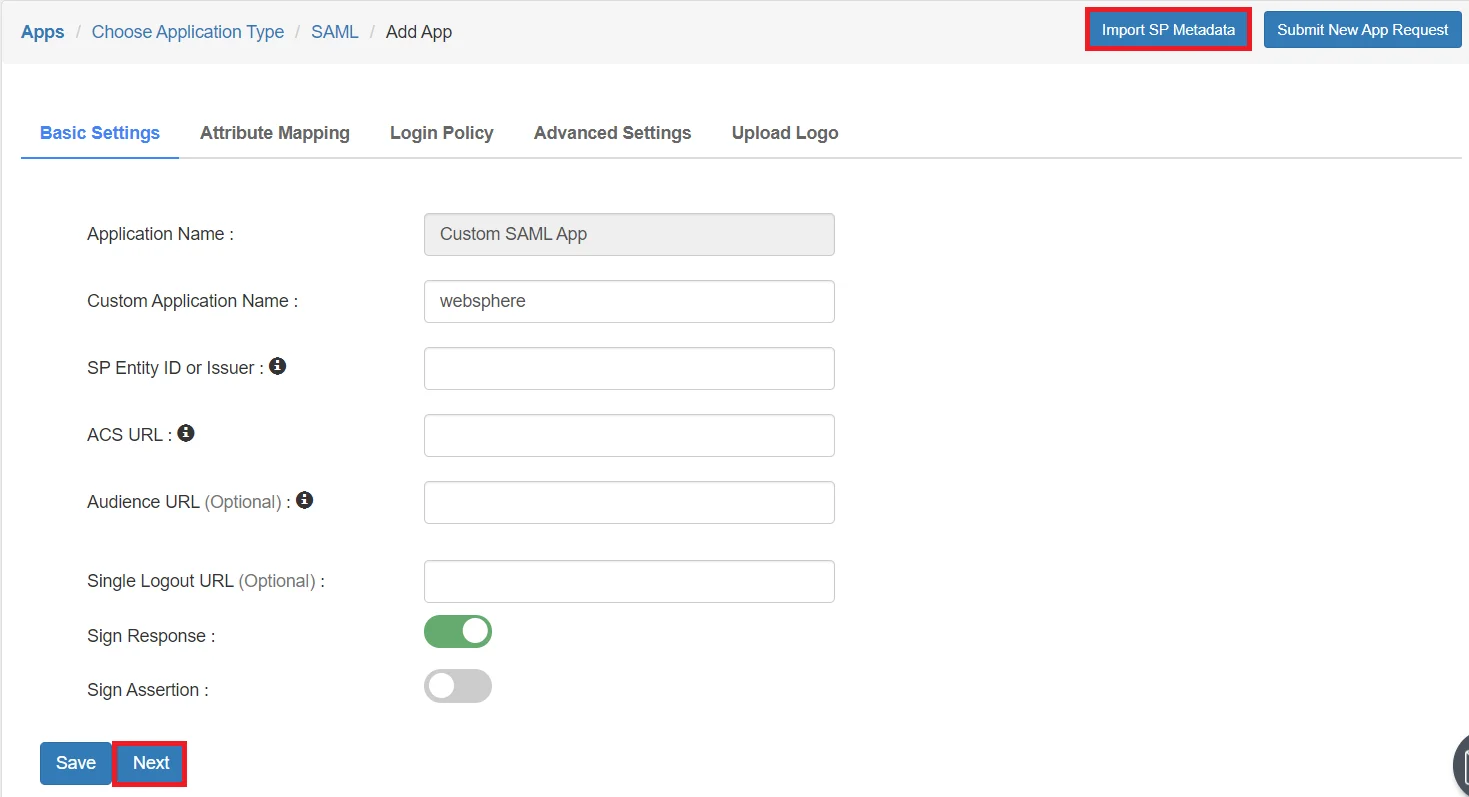
- Click on Import SP Metadata button to upload the metadata which is downloaded from SAML TAI and upload your metadata.
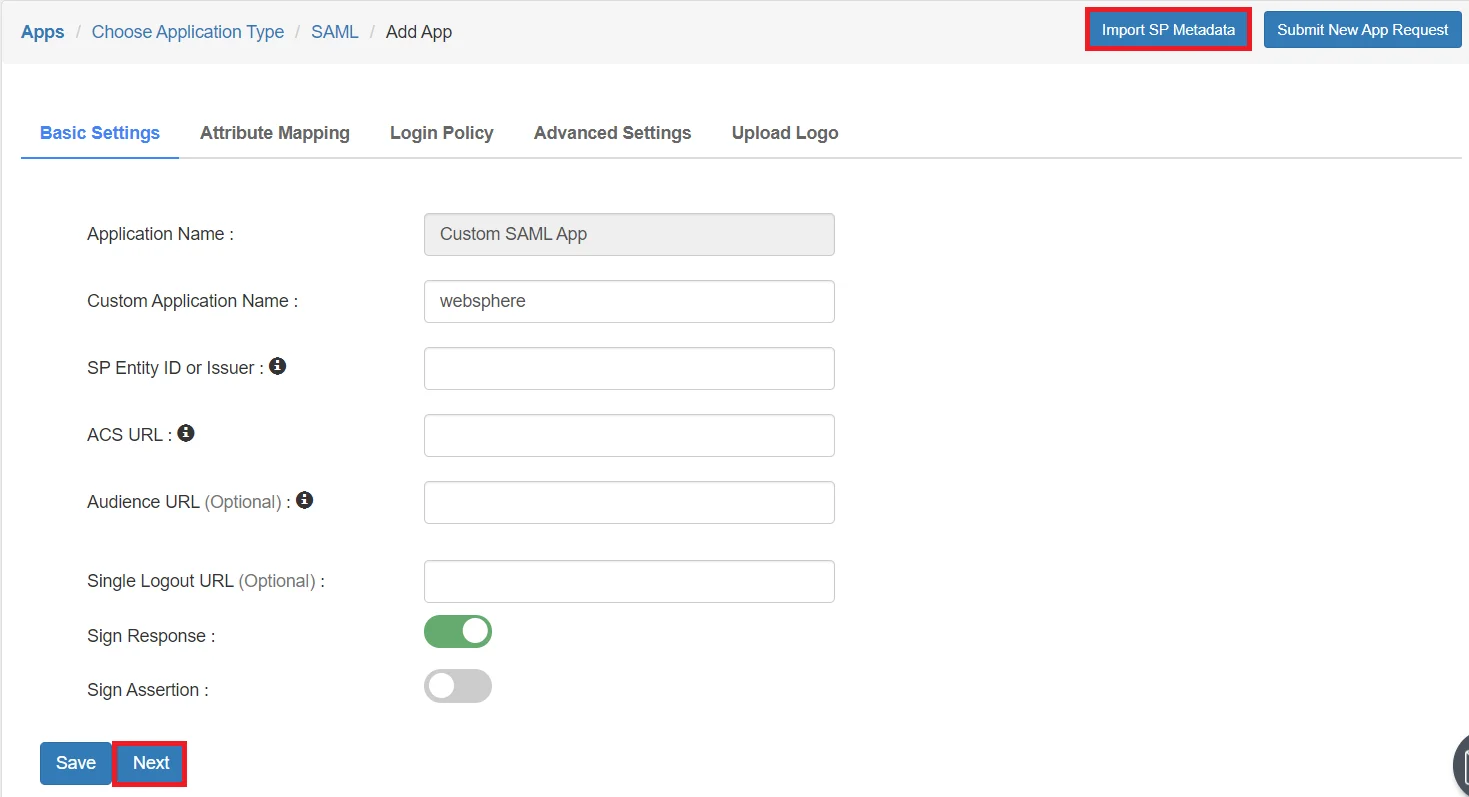
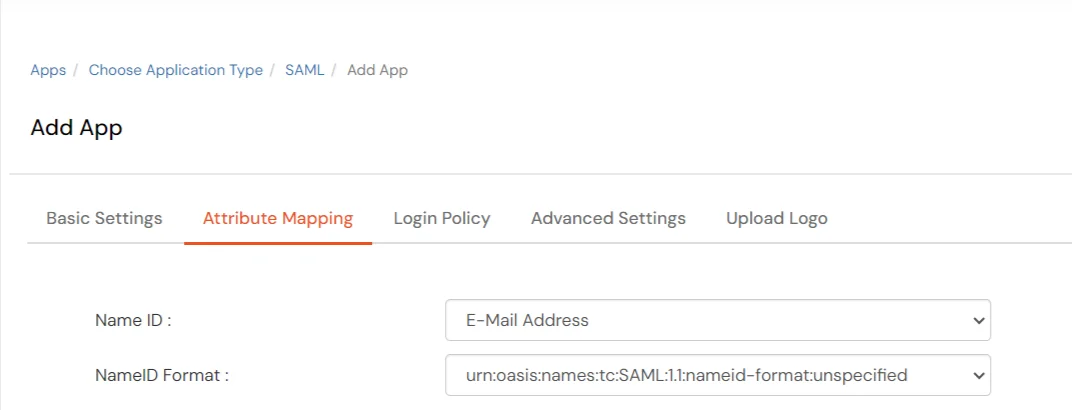
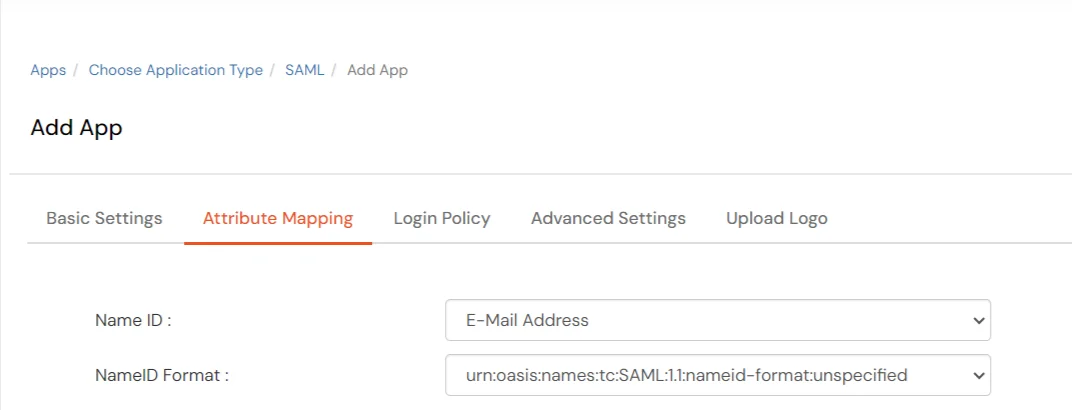
- Click Next, now in the Attribute Mapping configure the following attributes as shown in the image below.
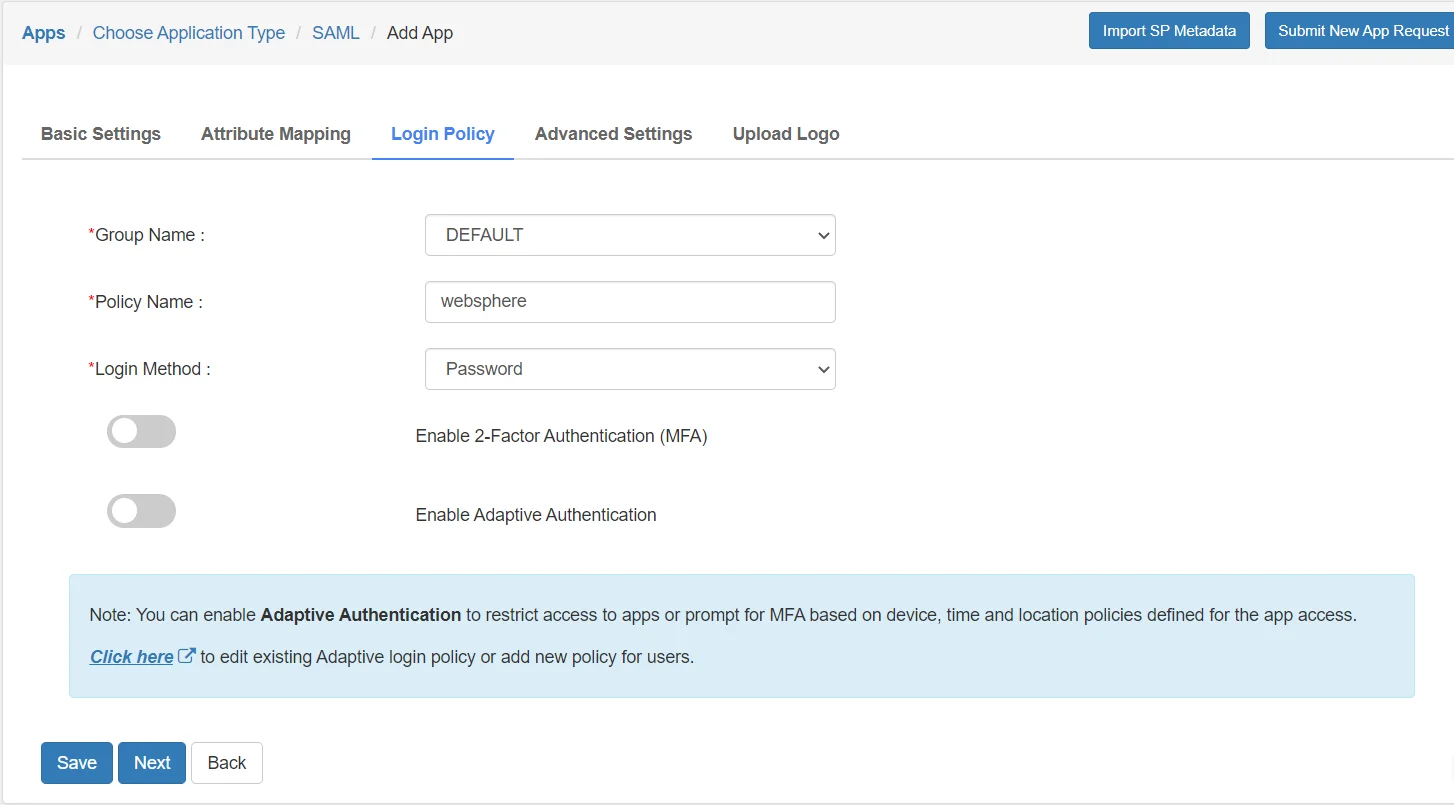
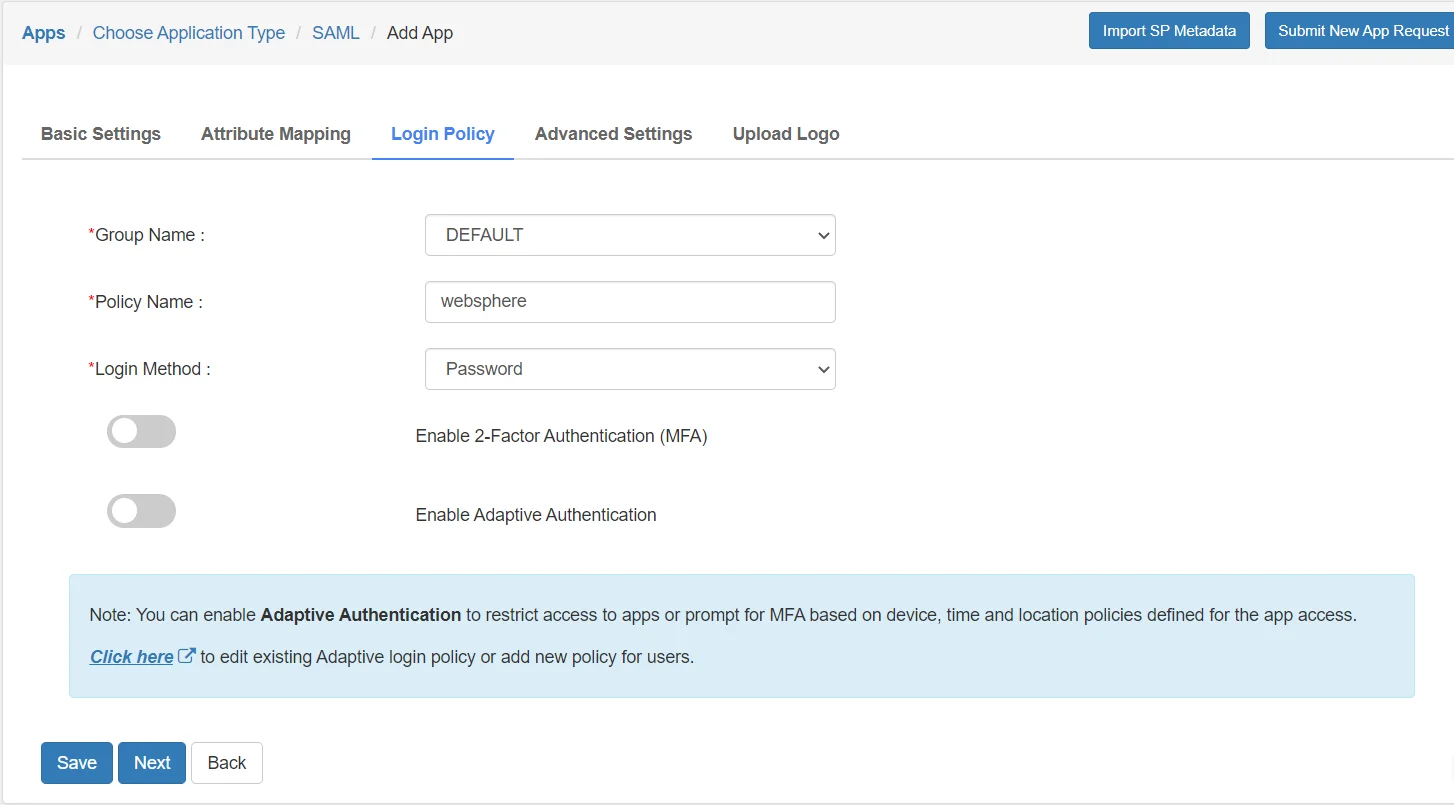
- Go to the Login Policy and select DEFAULT from the Group Name dropdown.
- Now enter the name for your app authentication policy in the Policy Name field.
- Select PASSWORD from the First Factor Type dropdown.
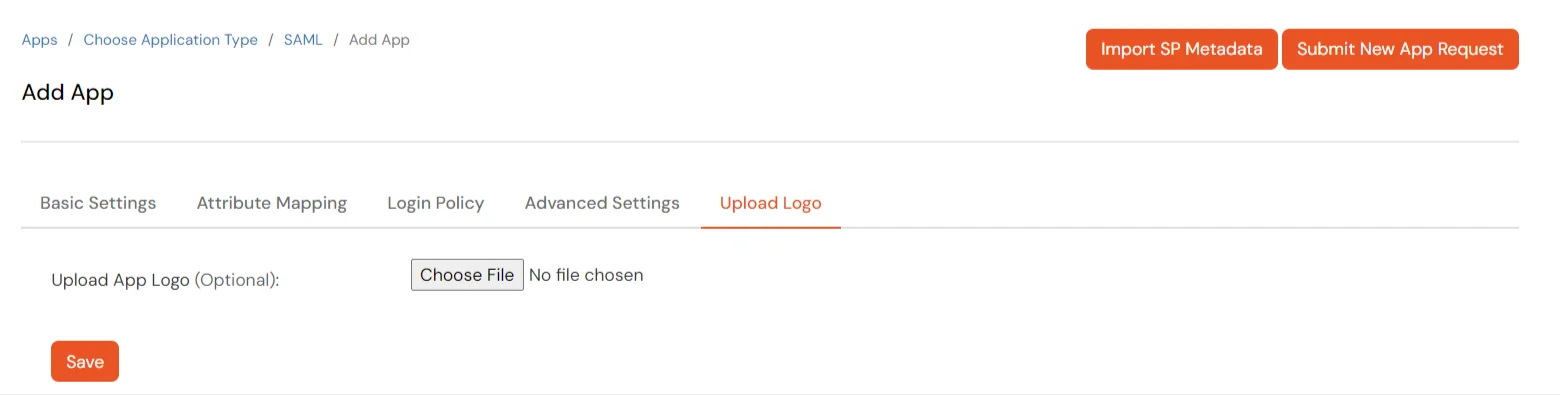
- To upload respective app logo for a Custom SAML App, click on Upload Logo tab.
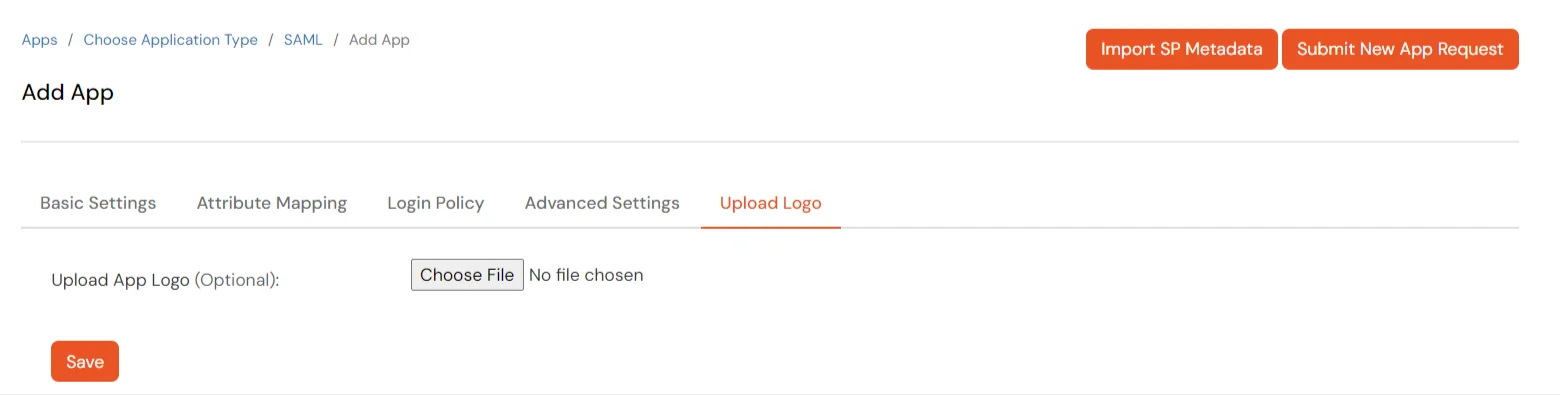
- Click on Save.
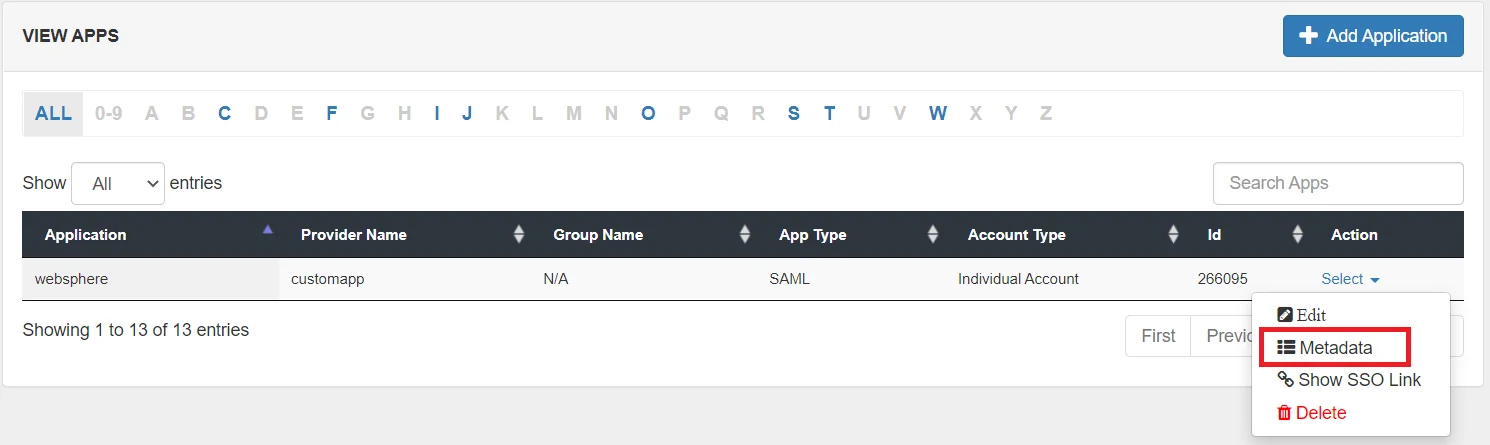
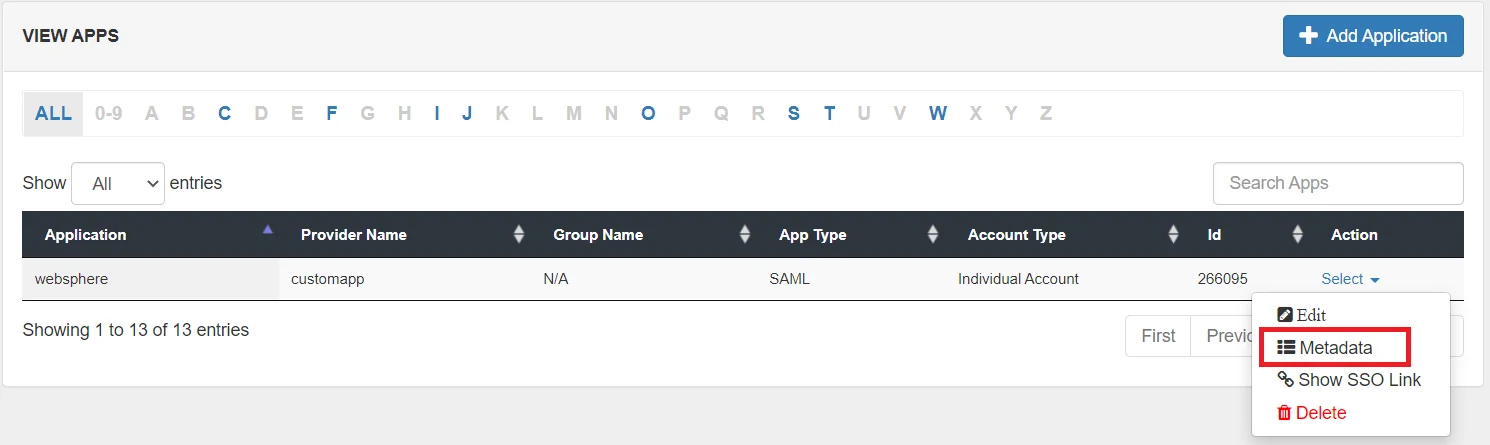
- Your application is saved successfully. Now click on the Select button against your newly created application. Go to Metadata.
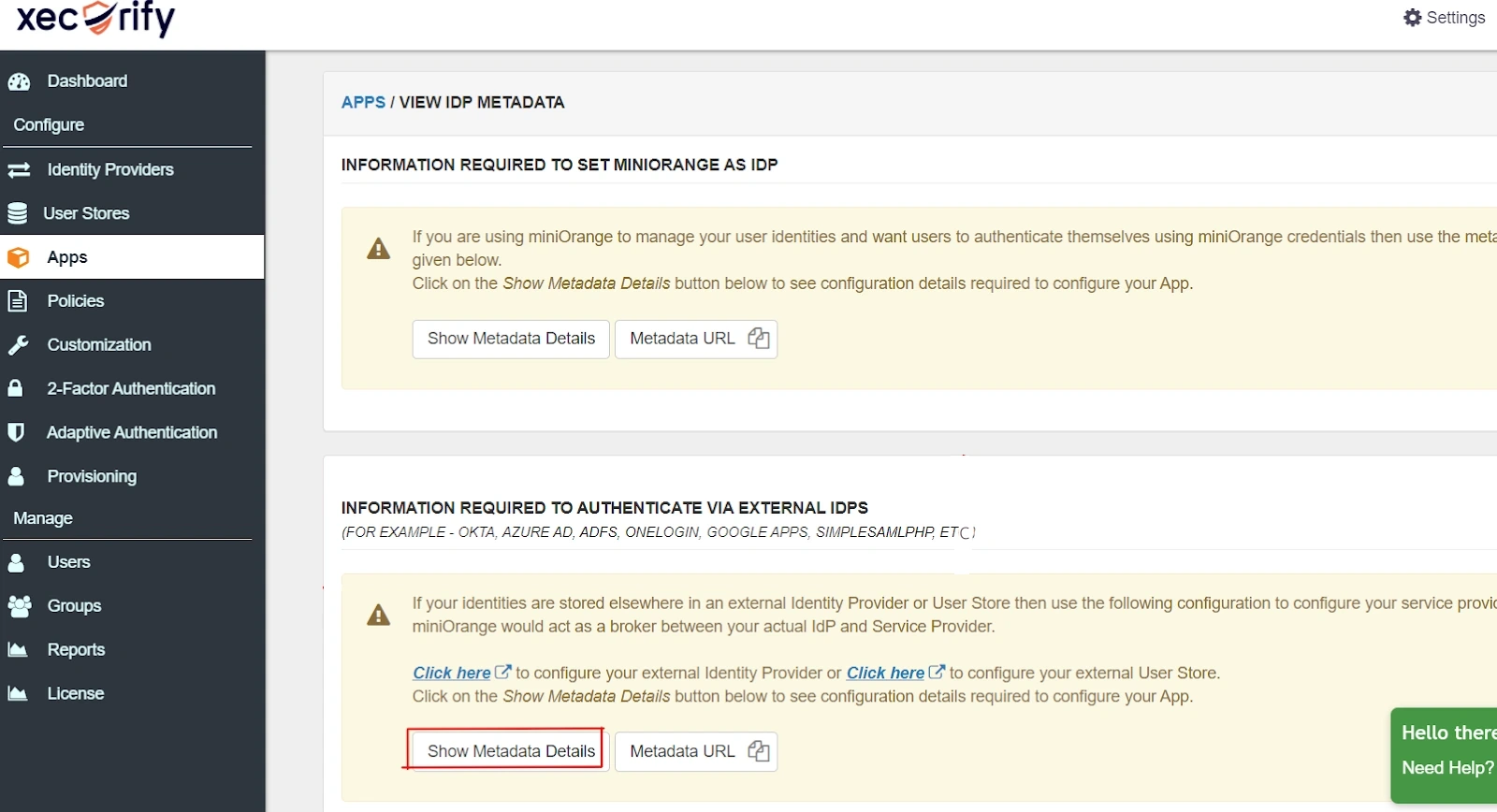
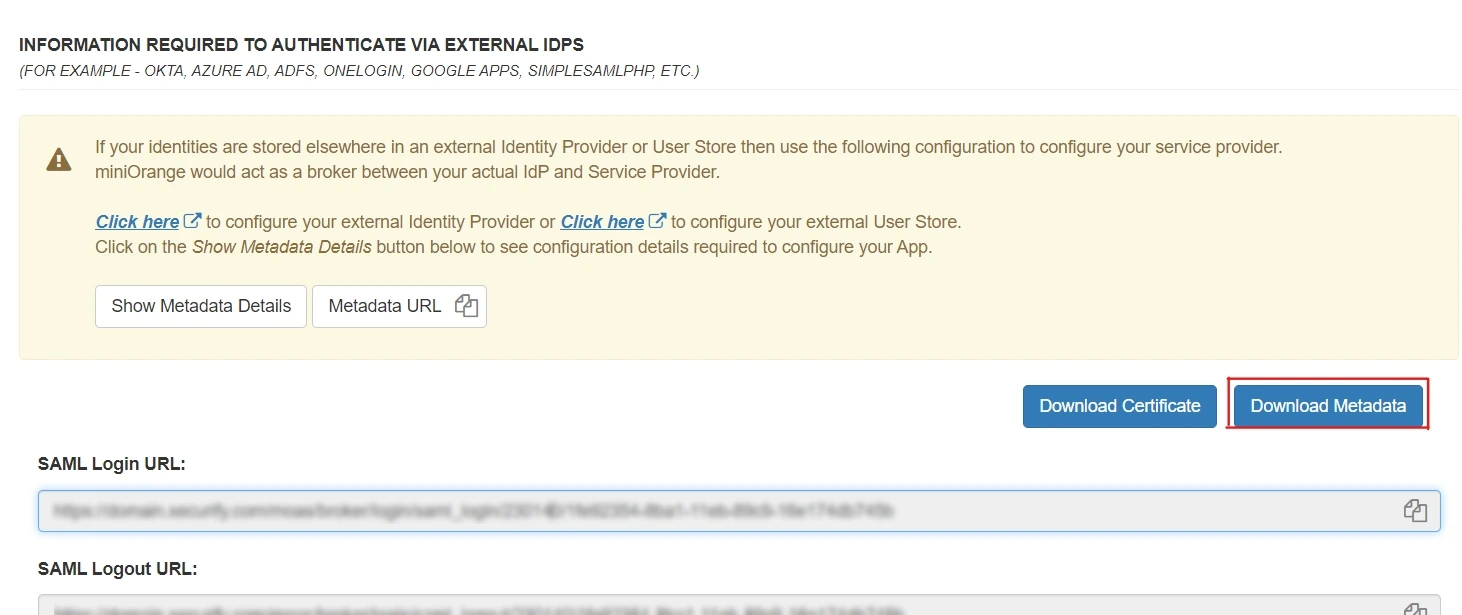
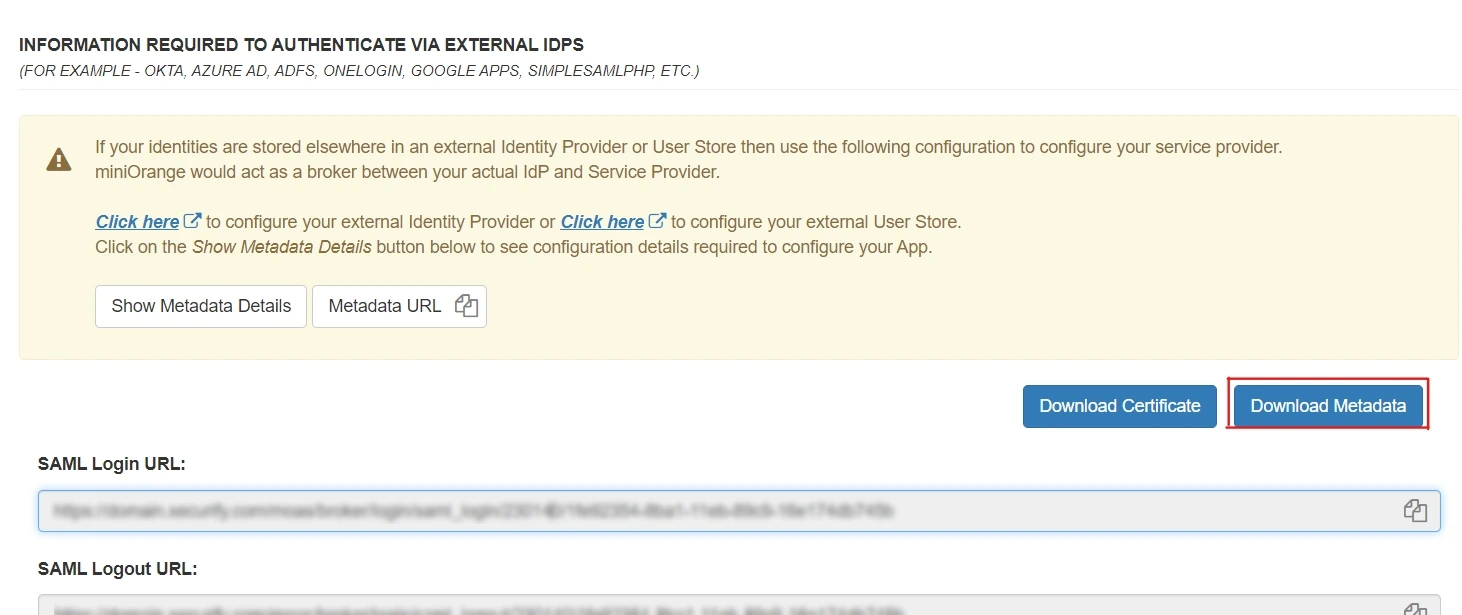
- On the Metadata page -
1. If you want to use miniOrange as User-Store i.e., your user identities will be stored in miniOrange then download the metadata file under the heading 'INFORMATION REQUIRED TO SET MINIORANGE AS IDP'.
2. If you want to authenticate your users via any external Identity Provider like Active Directory, Okta, OneLogin, Google, Apple ID, etc then download the Metadata file under the heading 'INFORMATION REQUIRED TO AUTHENTICATE VIA EXTERNAL IDPS'.
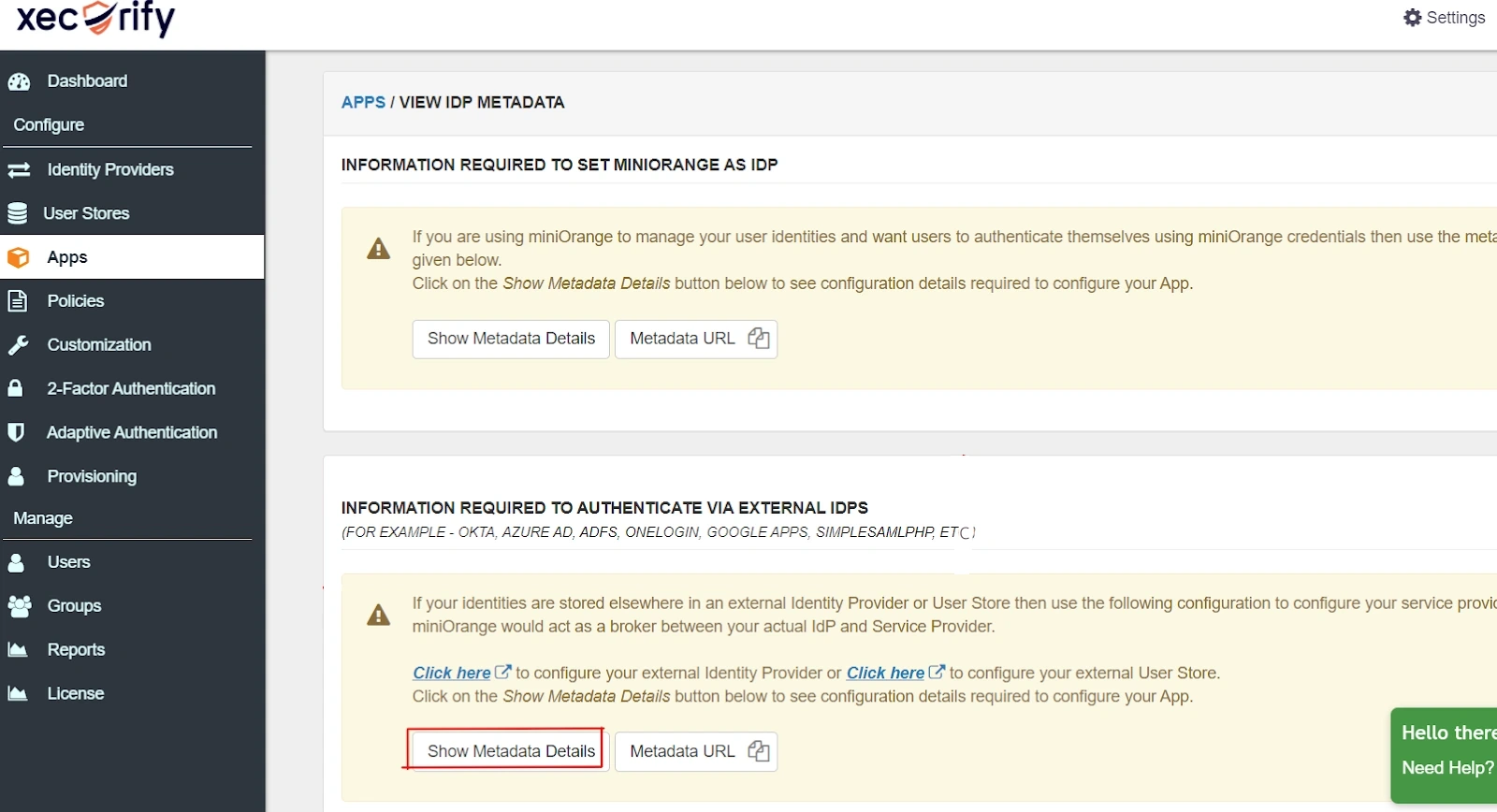
- Then click on Download Metadata.
2. Configure SSO in WebSphere SAML TAI
- Installing SAML ACS application:
- A new Enterprise Application has to be installed. On the WAS Admin console do the following steps.
- Open Applications > New Application > New Enterprise Application.
- Flag Remote file system and choose the following EAR
- /opt/IBM/WebSphere/AppServer/installableApps/WebSphereSamlSP.ear
- Enable SAML TAI using the administrative console.
- Log on to the WebSphere Application Server administrative console.
- Click SecurityGlobal security.
- Expand Web and SIP security and click Trust association.
- Under the General Properties heading, select the Enable trust association check box and click Interceptors.
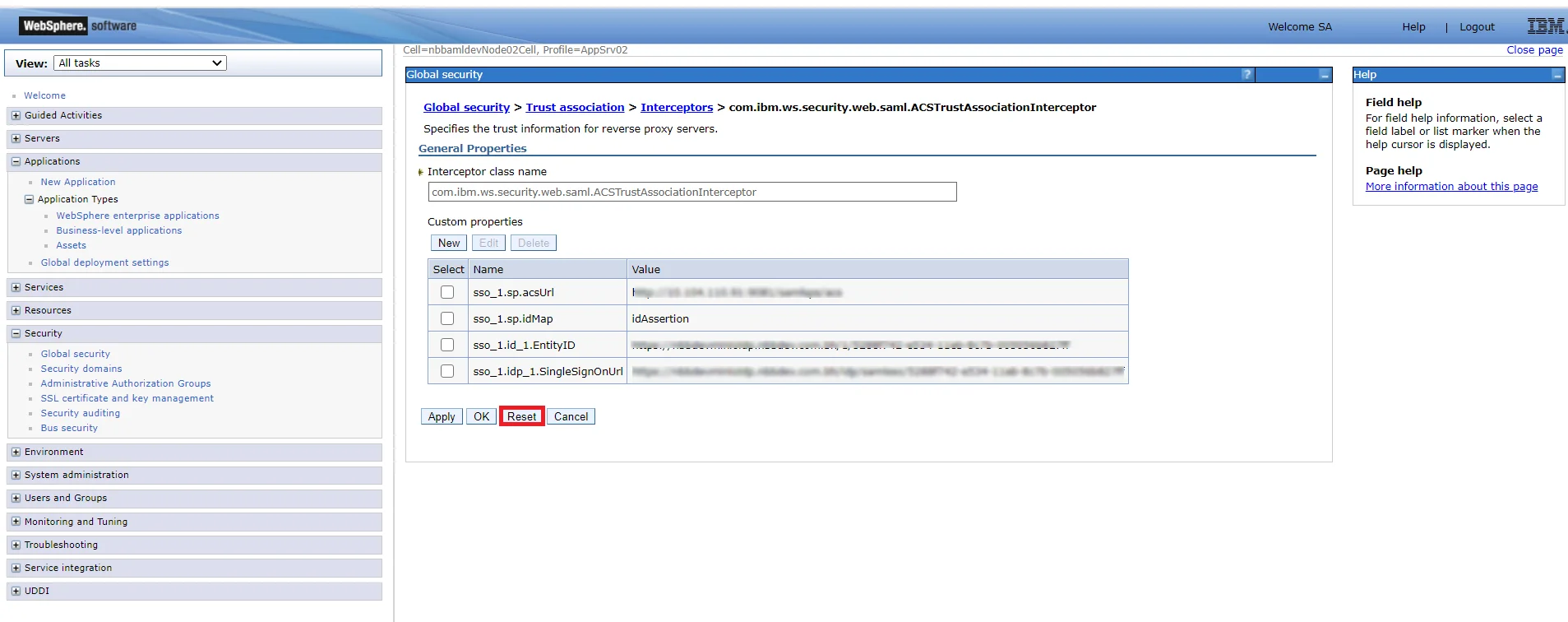
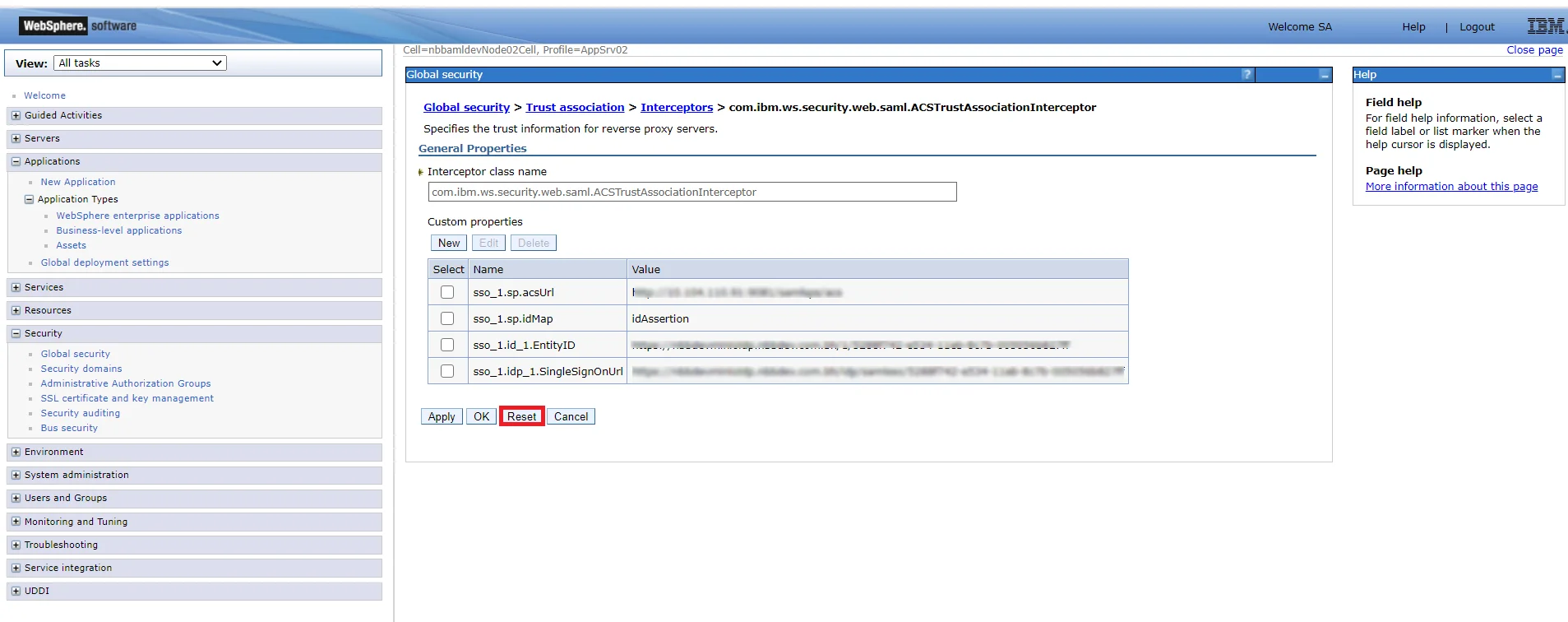
- Click New and enter com.ibm.ws.security.web.saml.ACSTrustAssociationInterceptor in the Interceptor class name field.
- Under Custom properties, fill in the following custom property information:
Name: sso_1.sp.acsUrl and Value: https://<hostname>:<sslport>/samlsps/<any URI pattern string> where hostname is the host name of the system where WebSphere Application is installed and sslport is the Web server SSL port number (WC_defaulthost_secure).
Note: If you need to have multiple, similar entry points for your SAML workflows, you can specify a wildcard value instead of a specific URI pattern string at the end of the URL specified as the value of this property. Specifying a wildcard as part of the value of this property eliminates the need to separately configure each of the similar entry points.
- Click New and enter the following custom property information:
Name: sso_1.sp.idMap and Value: idAssertion.
- Click OK.
- Go back to SecurityGlobal security and click Custom properties.
- Click New and define the following custom property information under General properties: Name:
com.ibm.websphere.security.DeferTAItoSSO and Value:
com.ibm.ws.security.web.saml.ACSTrustAssociationInterceptor.
Note: The property com.ibm.websphere.security.DeferTAItoSSO, was previously used in the default configuration of all installed servers. Now it is only used as part of the SAML configuration. Therefore, even if this property already exists in your system configuration, you must change its value to com.ibm.ws.security.web.saml.ACSTrustAssociationInterceptor. Multiple values, separated with commas, cannot be specified for this property. It must be set to a single SAML TAI.
- Click New and define the following custom property information under General properties: Name:
com.ibm.websphere.security.InvokeTAIbeforeSSO and Value:
com.ibm.ws.security.web.saml.ACSTrustAssociationInterceptor.
- Click OK.
- Restart WebSphere Application Server.
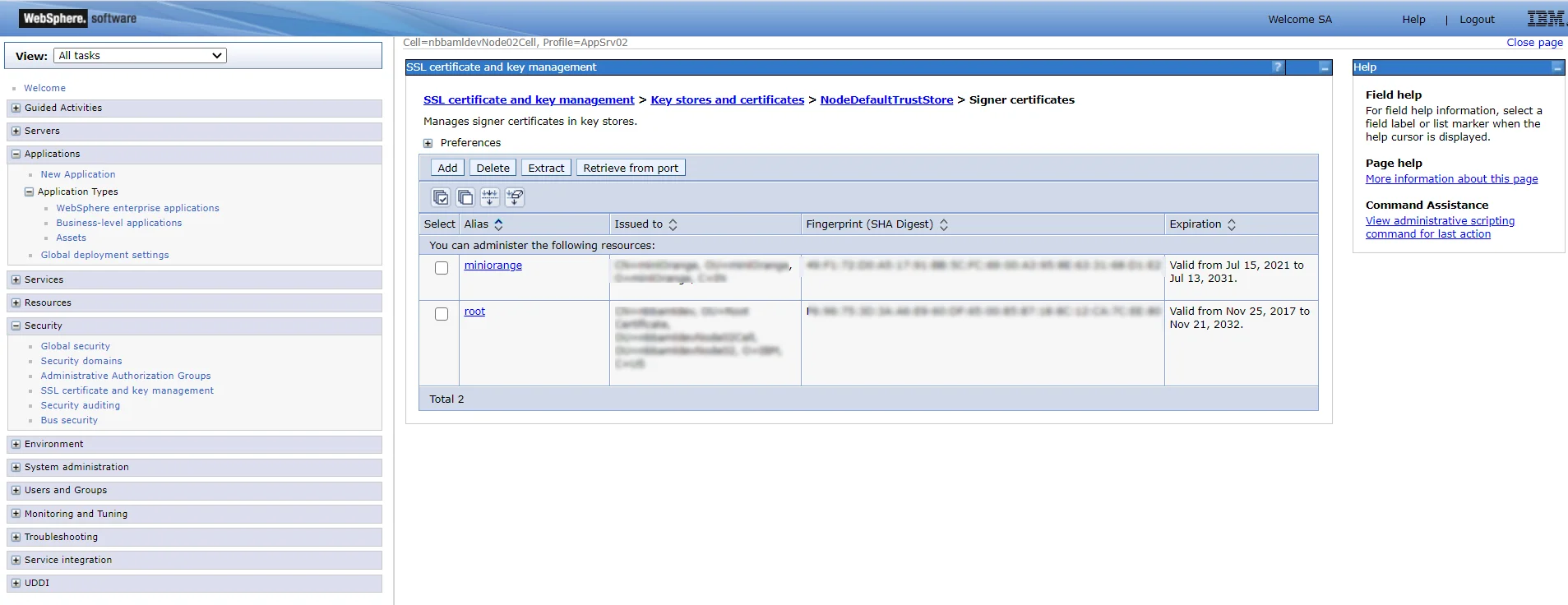
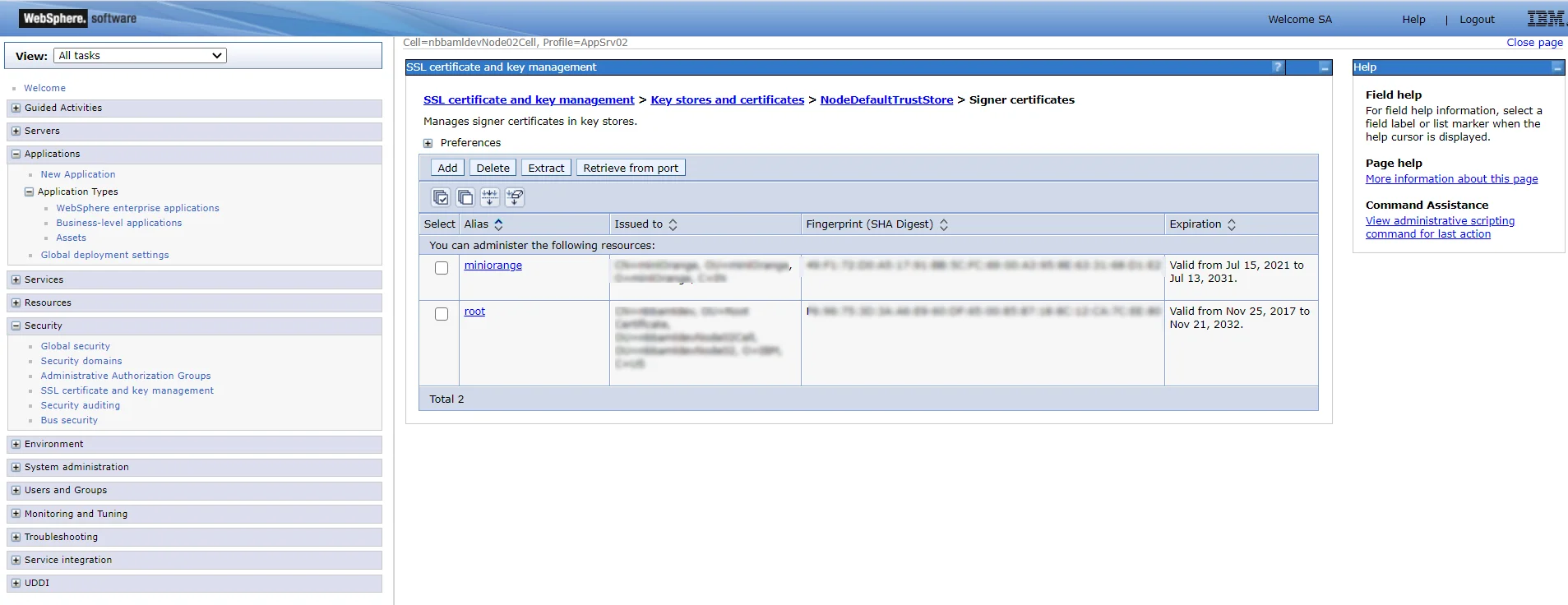
- Import the SAML token signer certificate using the administrative console:
- Log on to the WebSphere Application Server administrative console.
- Click Security > SSL certificate and key management > Key stores and certificates > NodeDefaultTrustStore > Signer certificates Use CellDefaultTrustStore instead of NodeDefaultTrustStore for a deployment manager.
- Click Add.
- Fill in the certificate information from the certificate downloaded from miniOrange metadata.
- Click Apply.
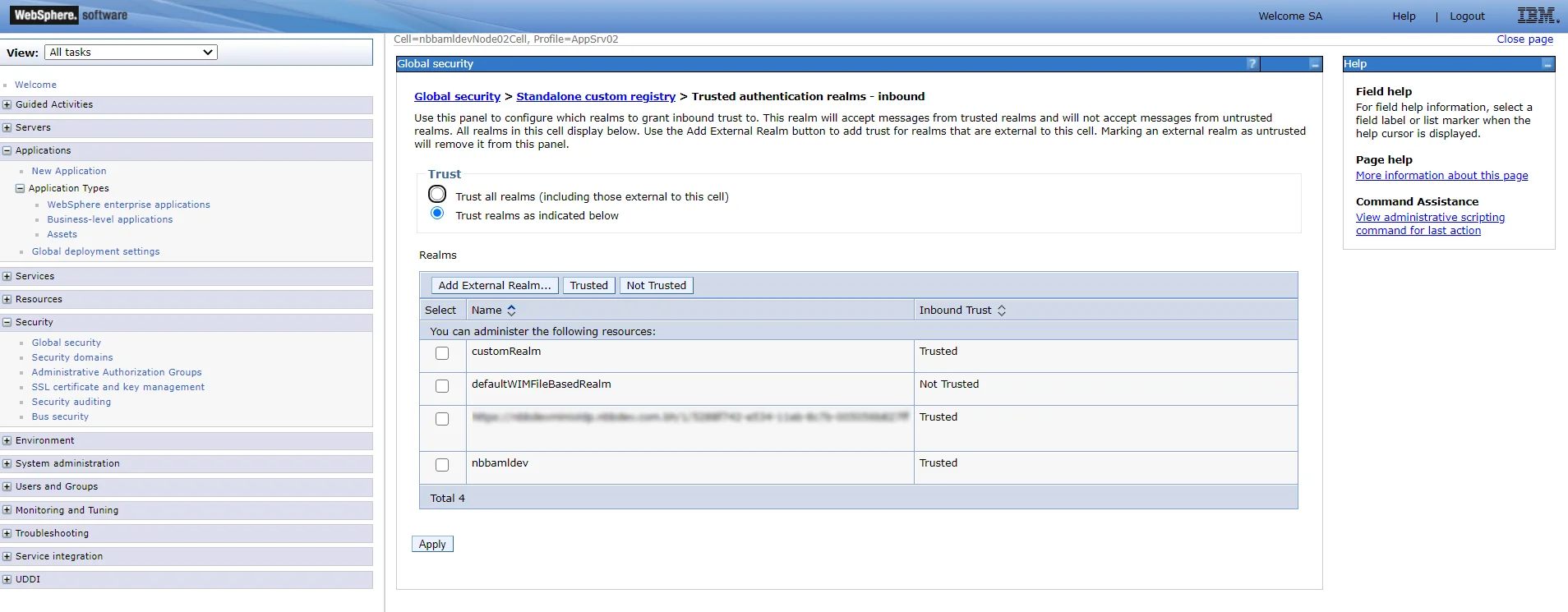
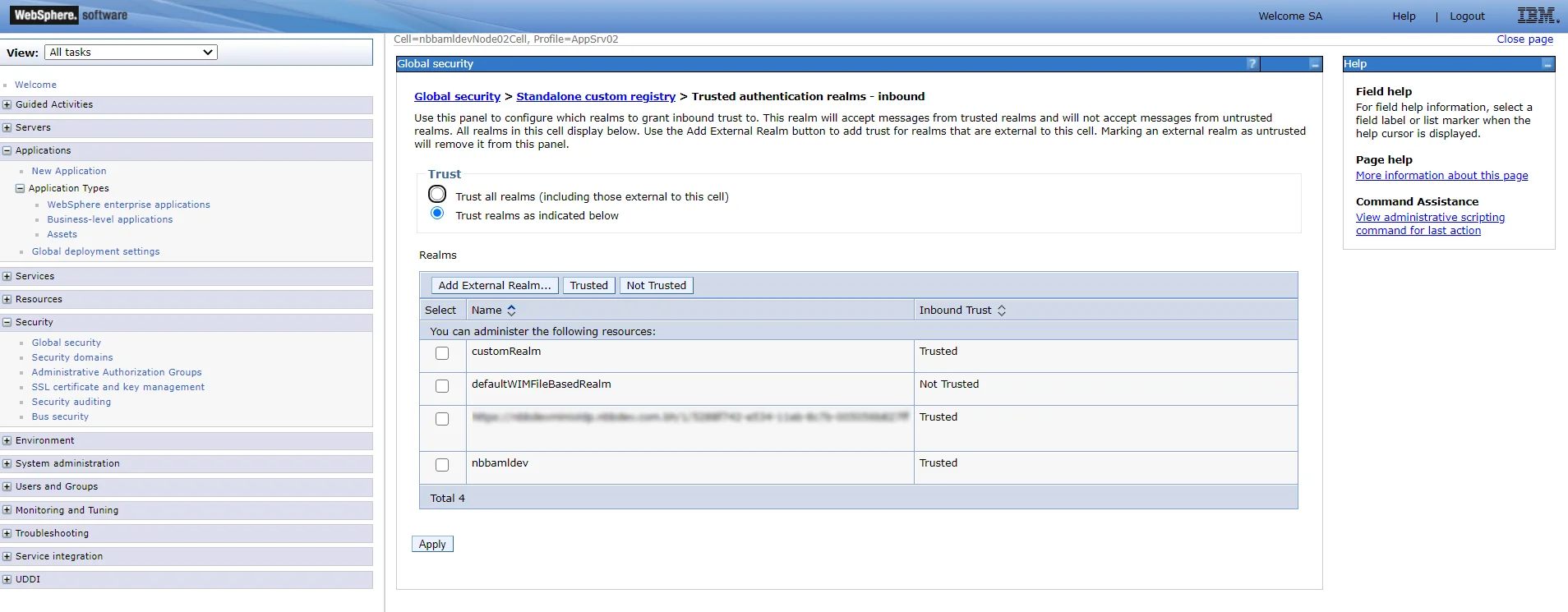
- Add IdP realms to the list of inbound trusted realms: Add inbound trust using the administrative console.
- Click Global security.
- Under the user account repository, click Configure.
- Click Trusted authentication realms - inbound.
- Click Add External Realm.
- Fill in the external realm name.
- Click OK and Save changes to the master configuration.
Your WebSphere Application Server is now configured as a service provider partner for IdP-initiated SSO.
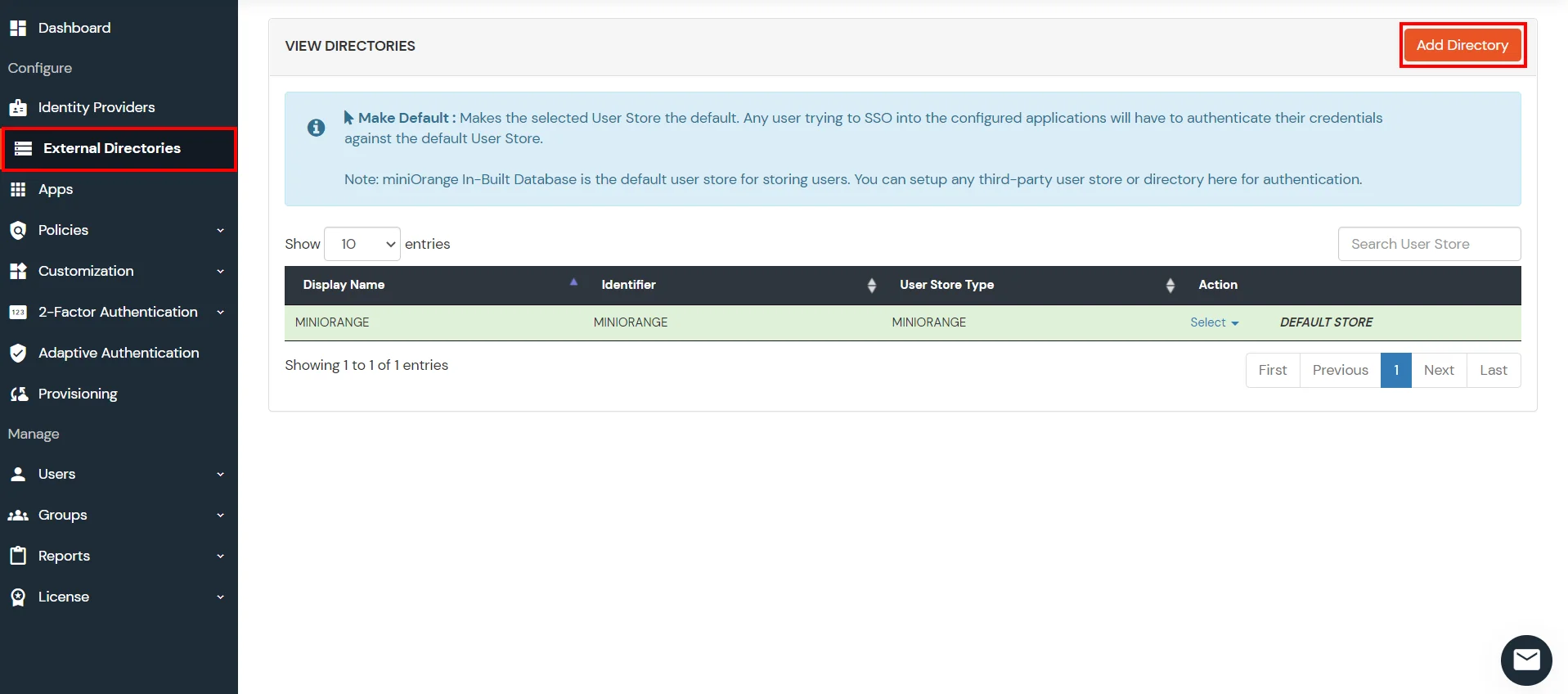
3. Configure Your User Directory (Optional)
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Microsoft Entra ID, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
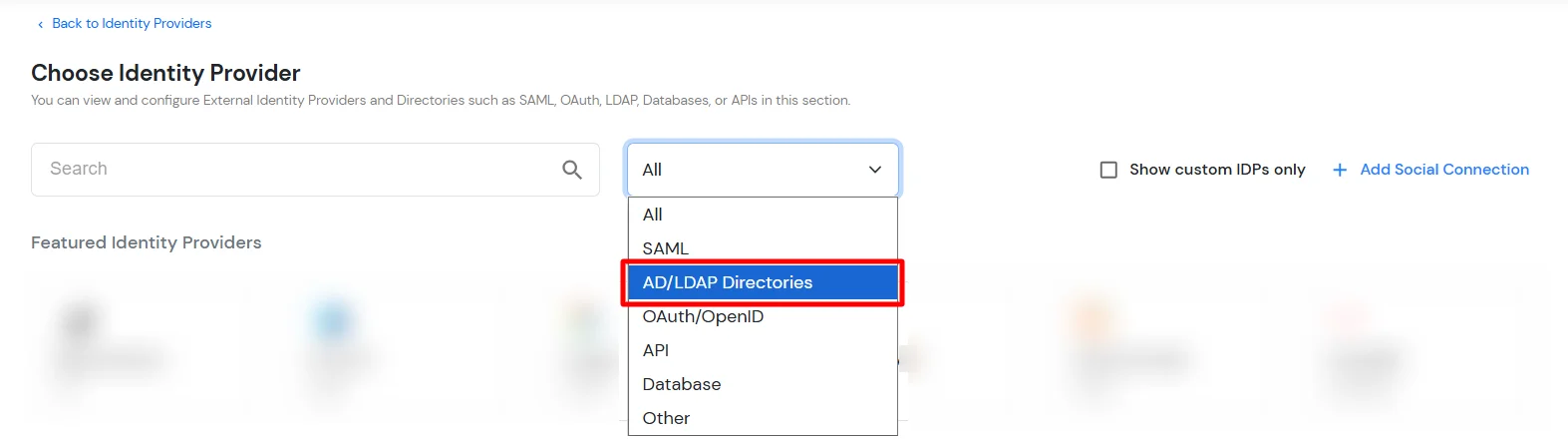
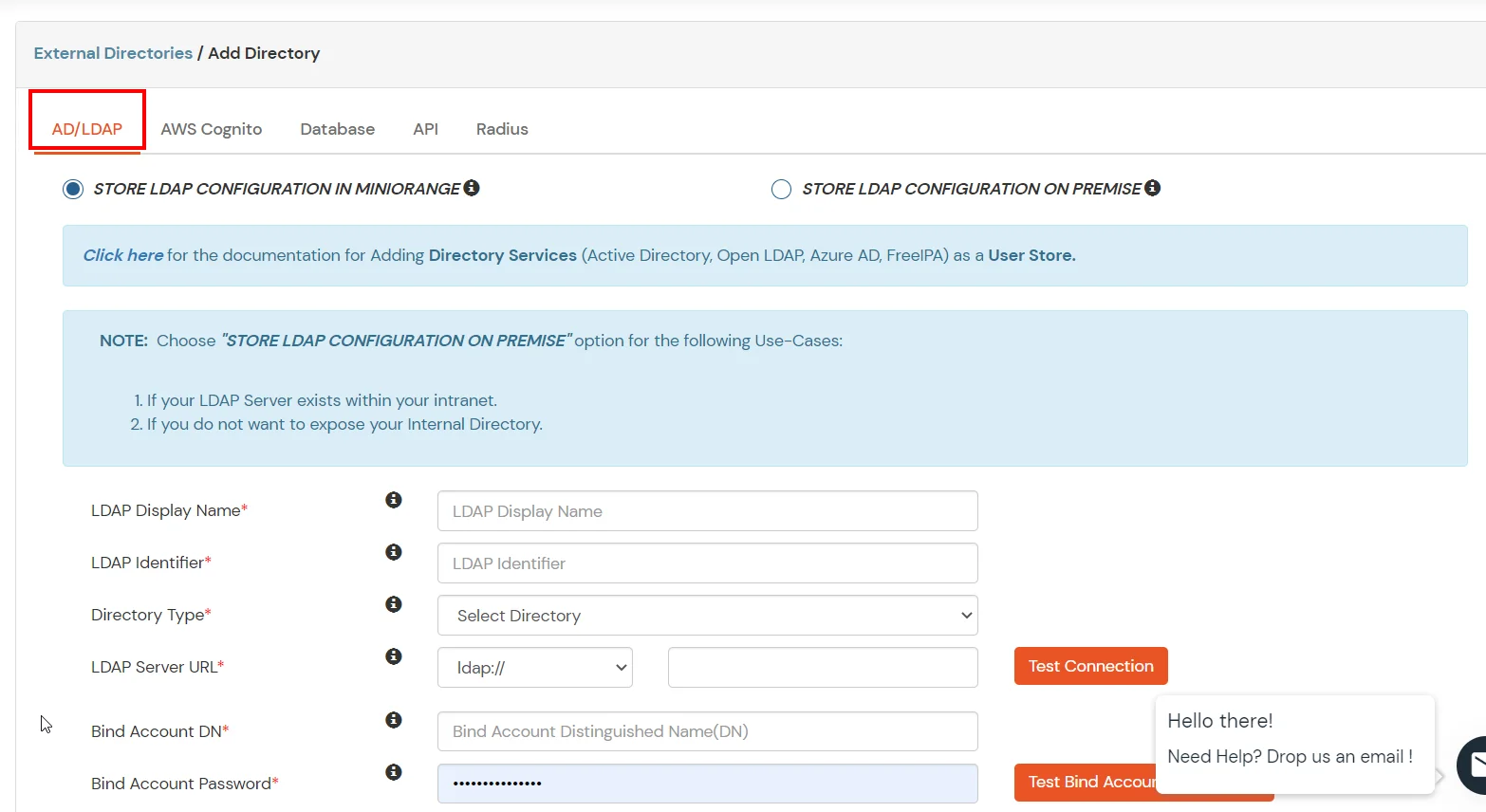
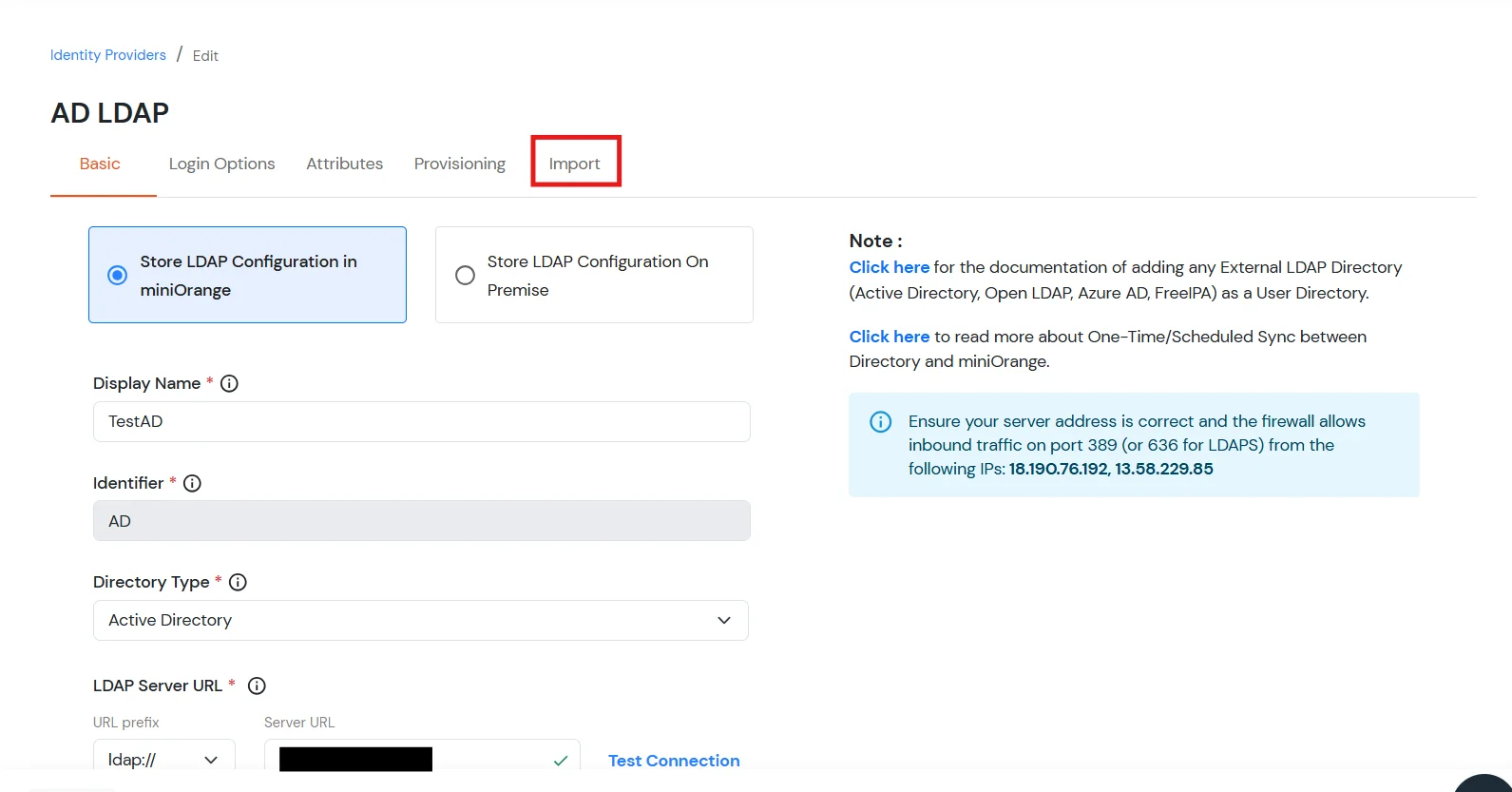
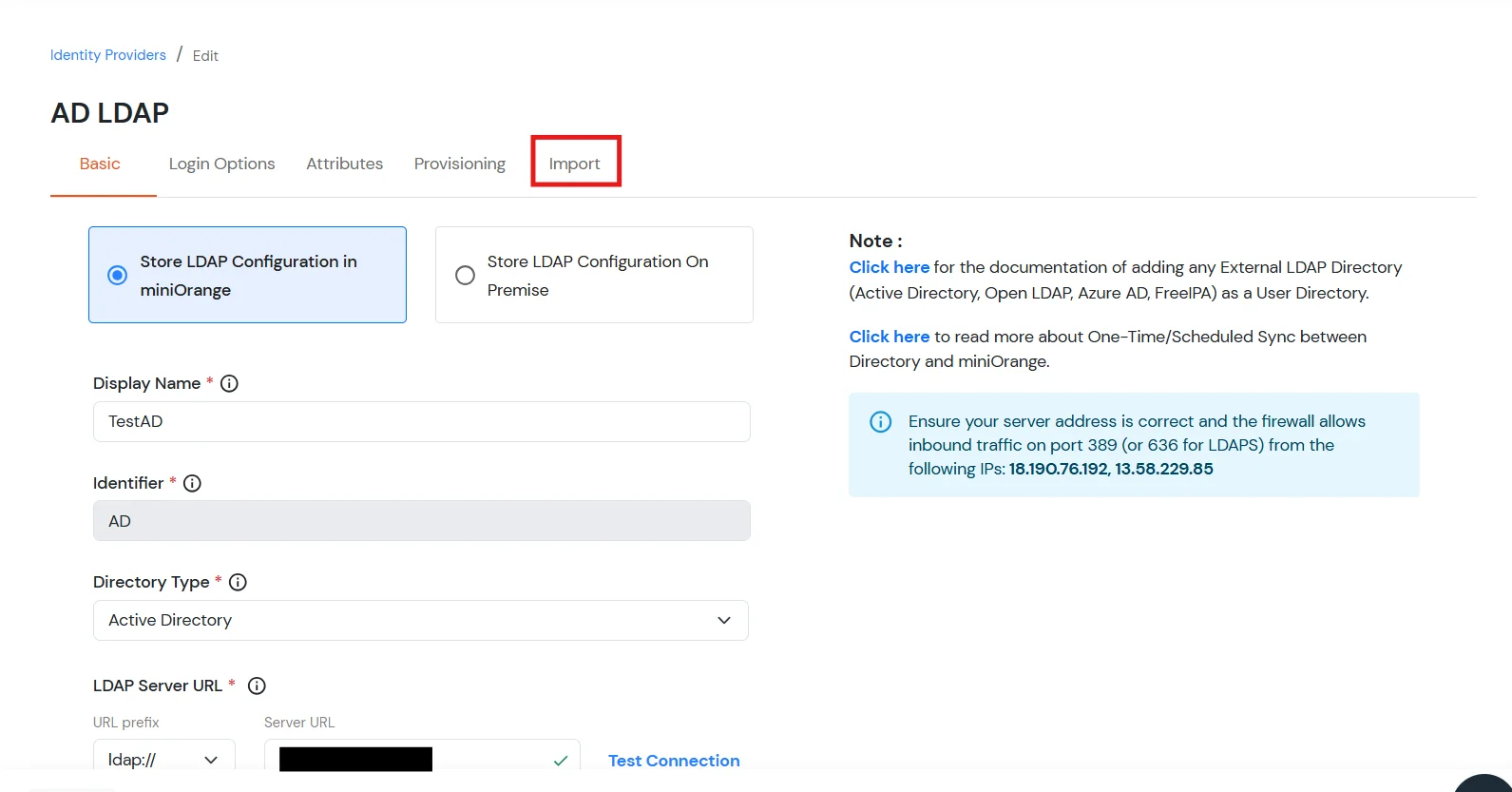
- Click on Identity Providers >> Add Identity Provider in the left menu of the dashboard
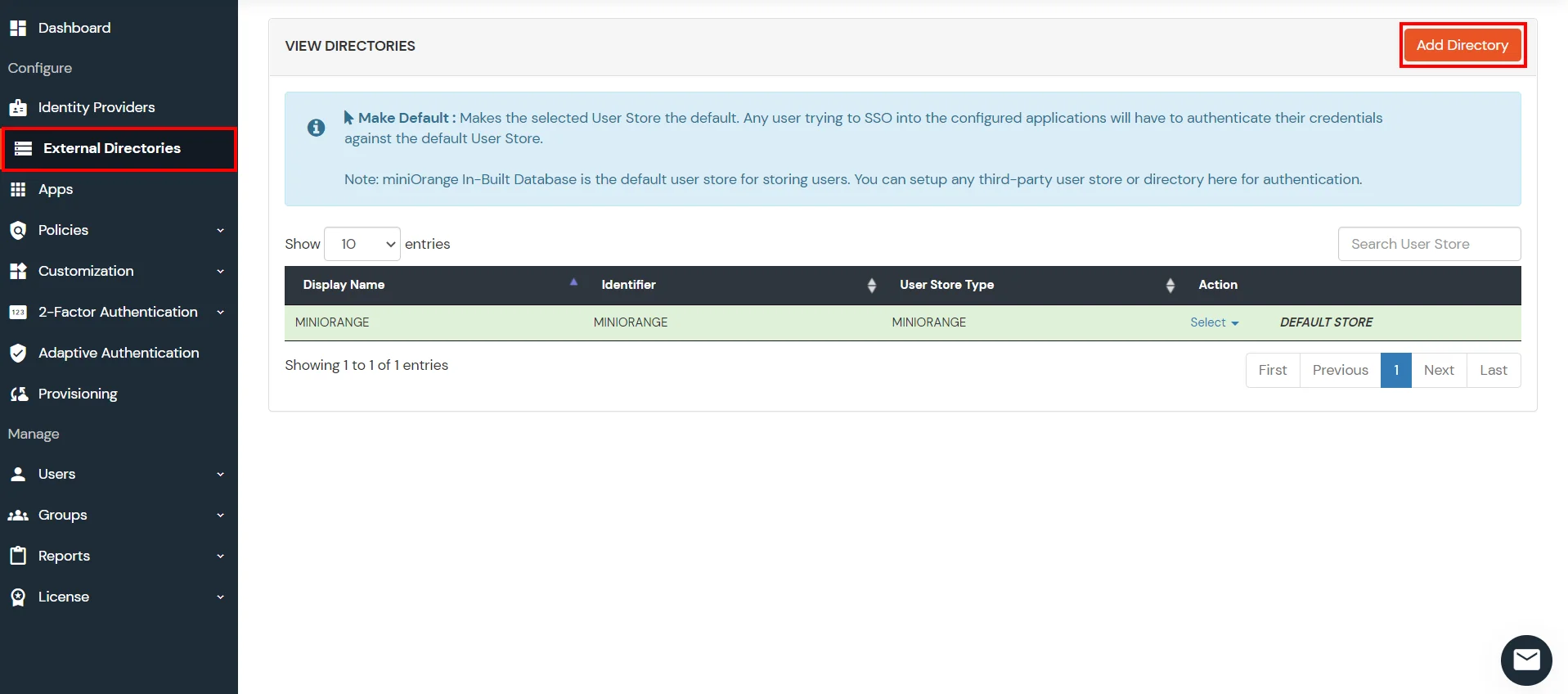
- In Choose Identity Provider, select AD/LDAP Directories from the dropdown.
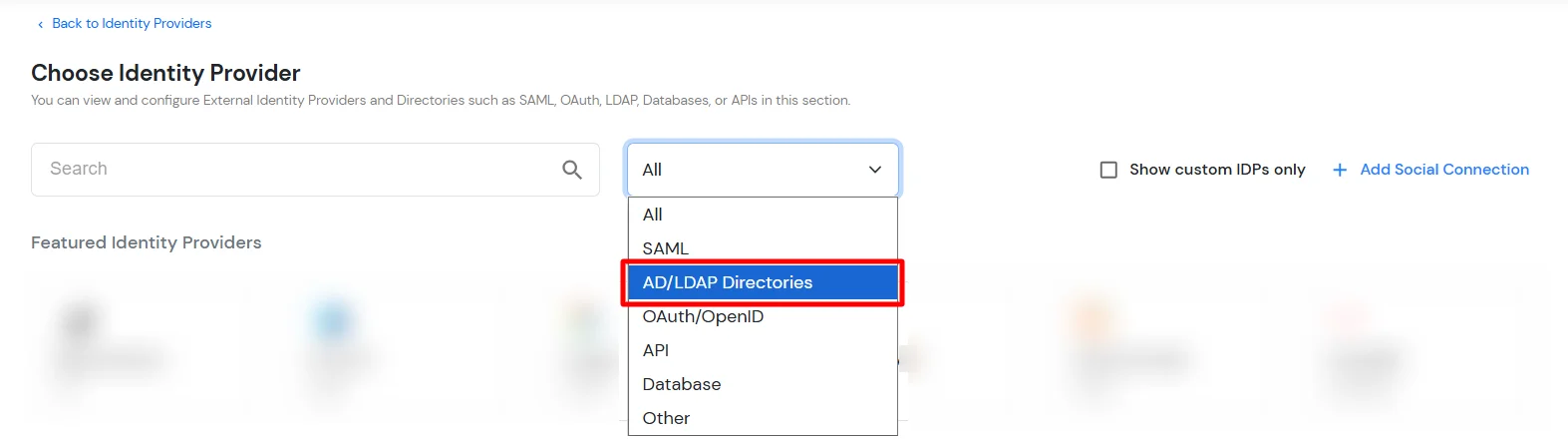
- Then search for AD/LDAP and click it.
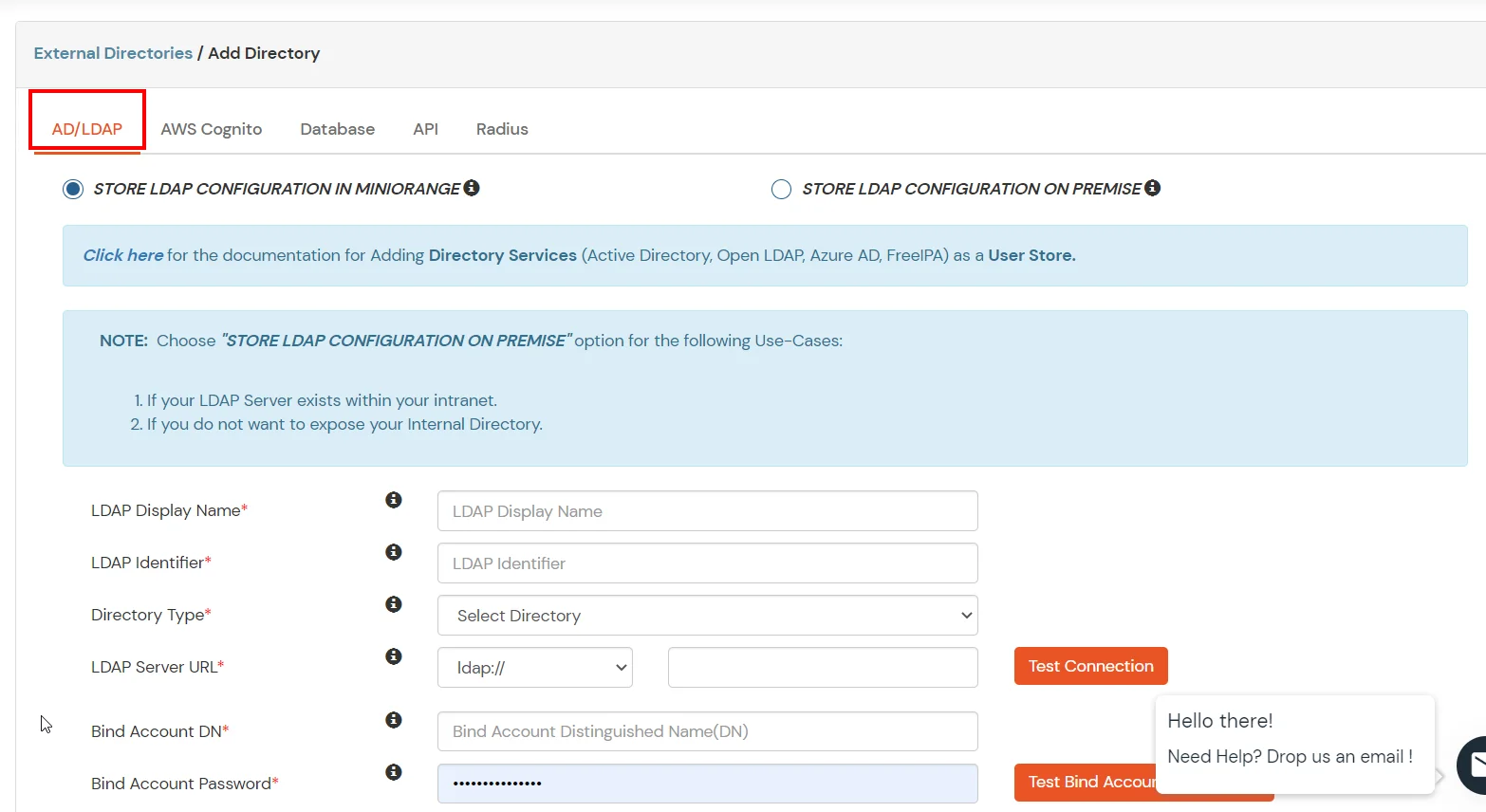
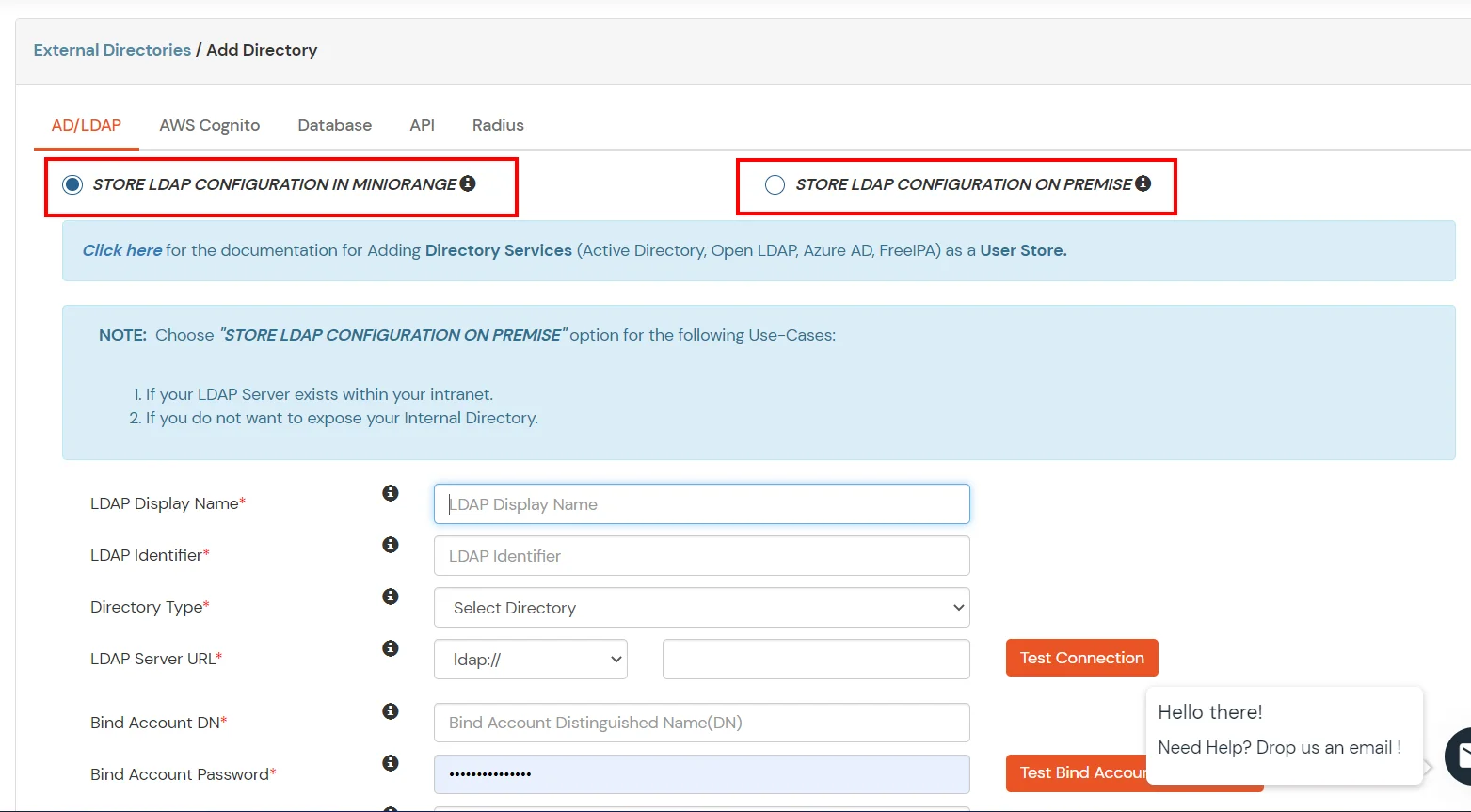
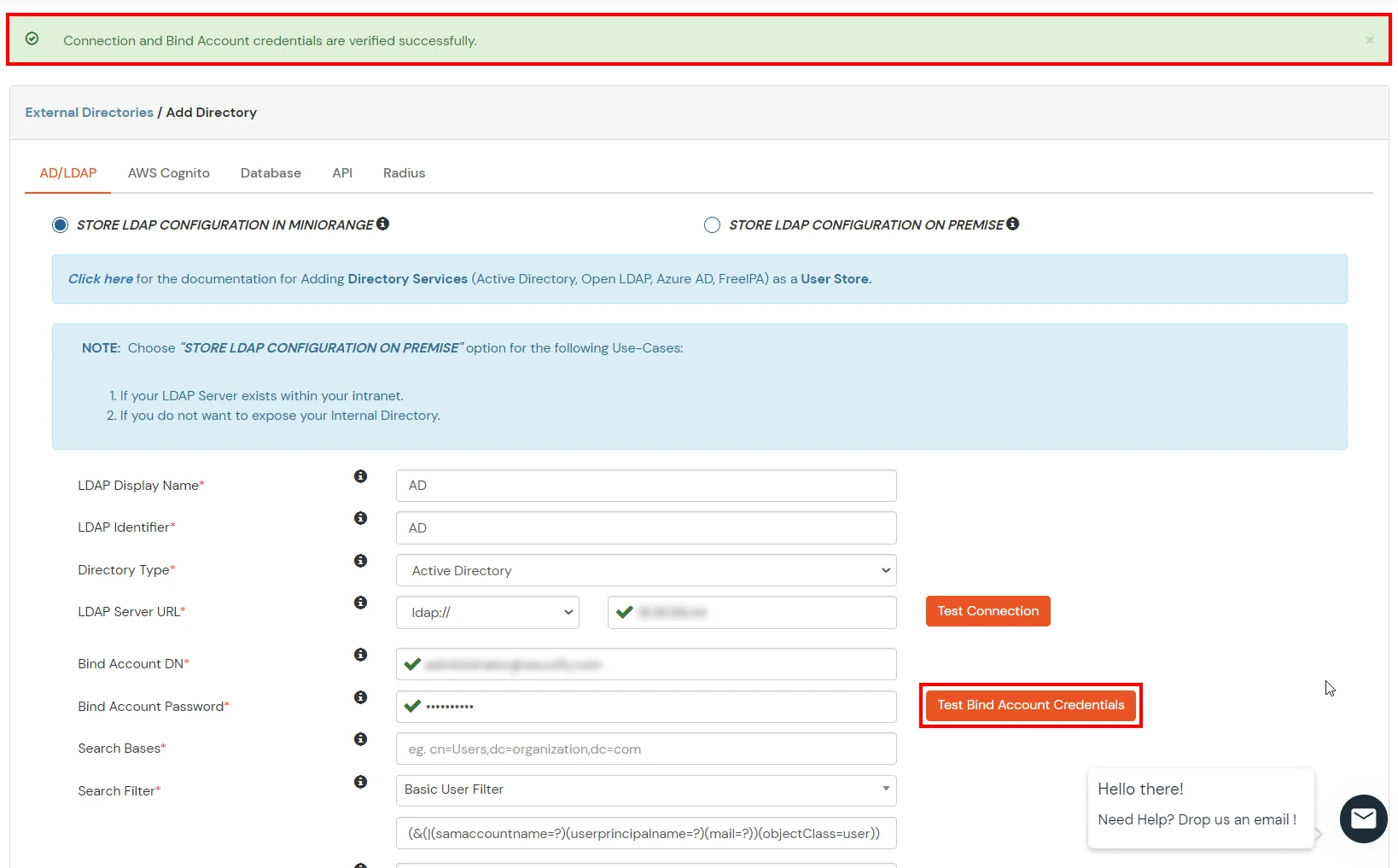
- STORE LDAP CONFIGURATION IN MINIORANGE: Choose this option if you want to keep your configuration in miniOrange. If the active directory is behind a firewall, you will need to open the firewall to allow incoming requests to your AD.
- STORE LDAP CONFIGURATION ON PREMISE: Choose this option if you want to keep your configuration in your premise and only allow access to AD inside premises. You will have to download and install miniOrange gateway on your premise.
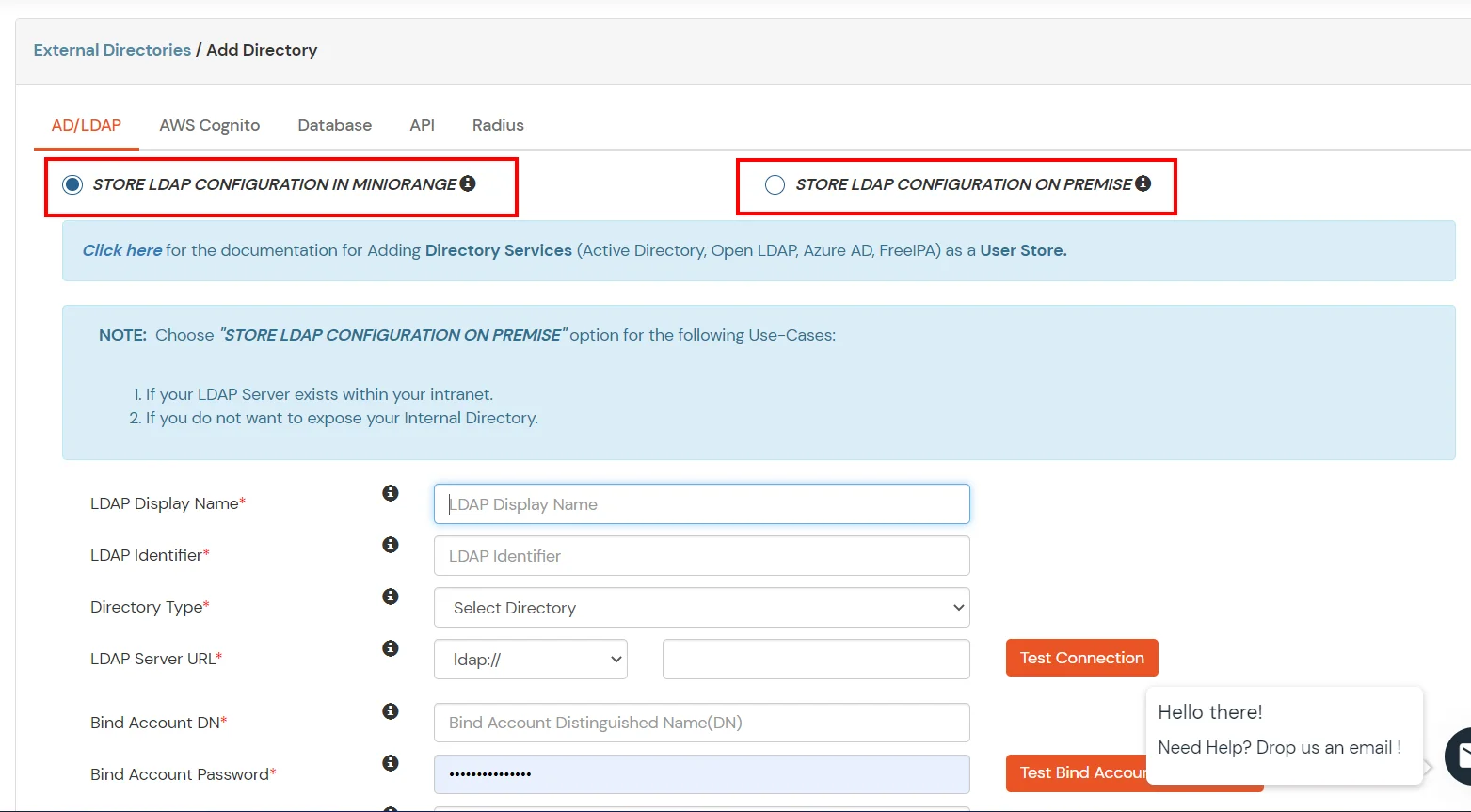
- Enter AD/LDAP Display Name and Identifier name.
- Select Directory Type as Active Directory.
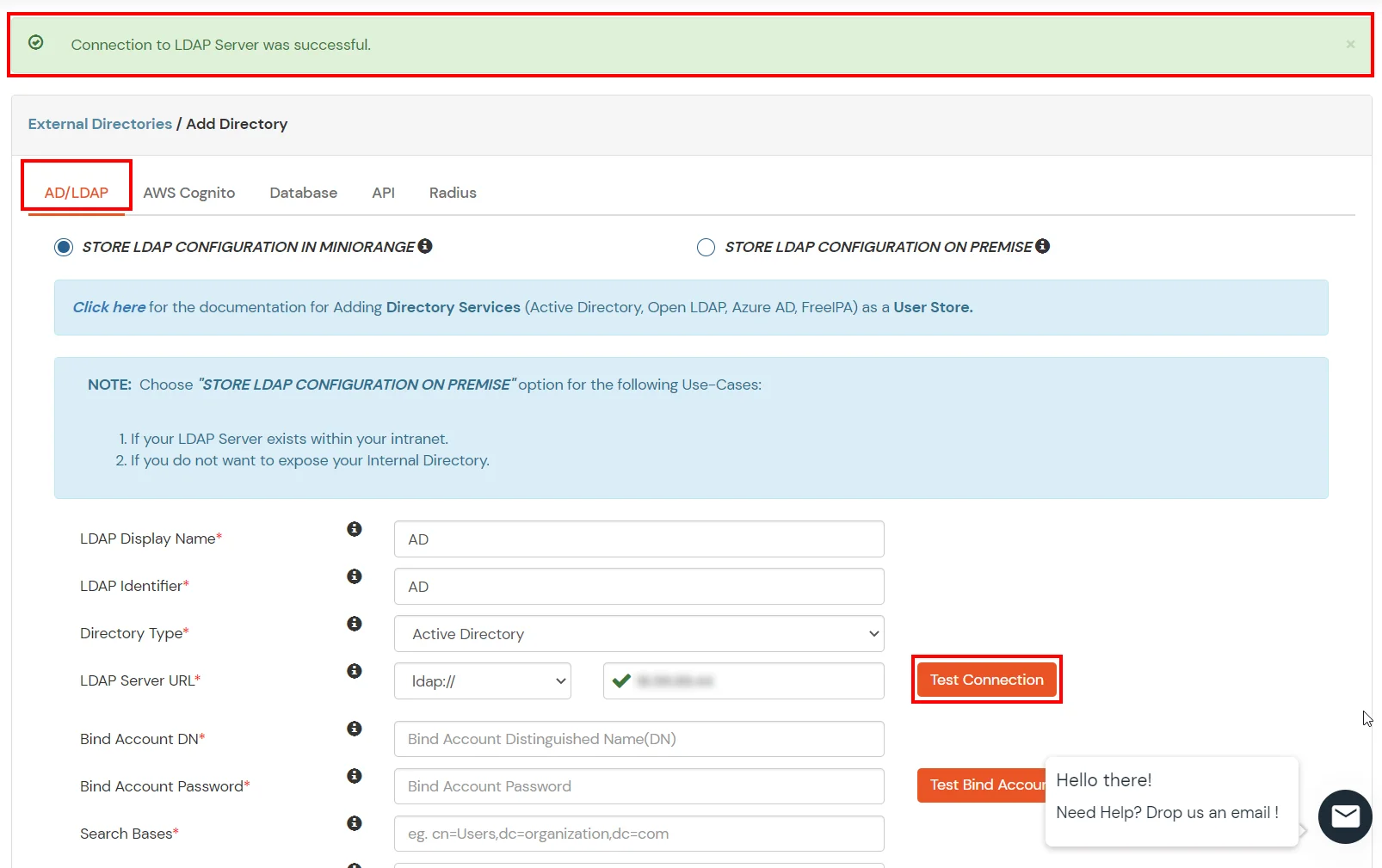
- Enter the LDAP Server URL or IP Address against the LDAP Server URL field.
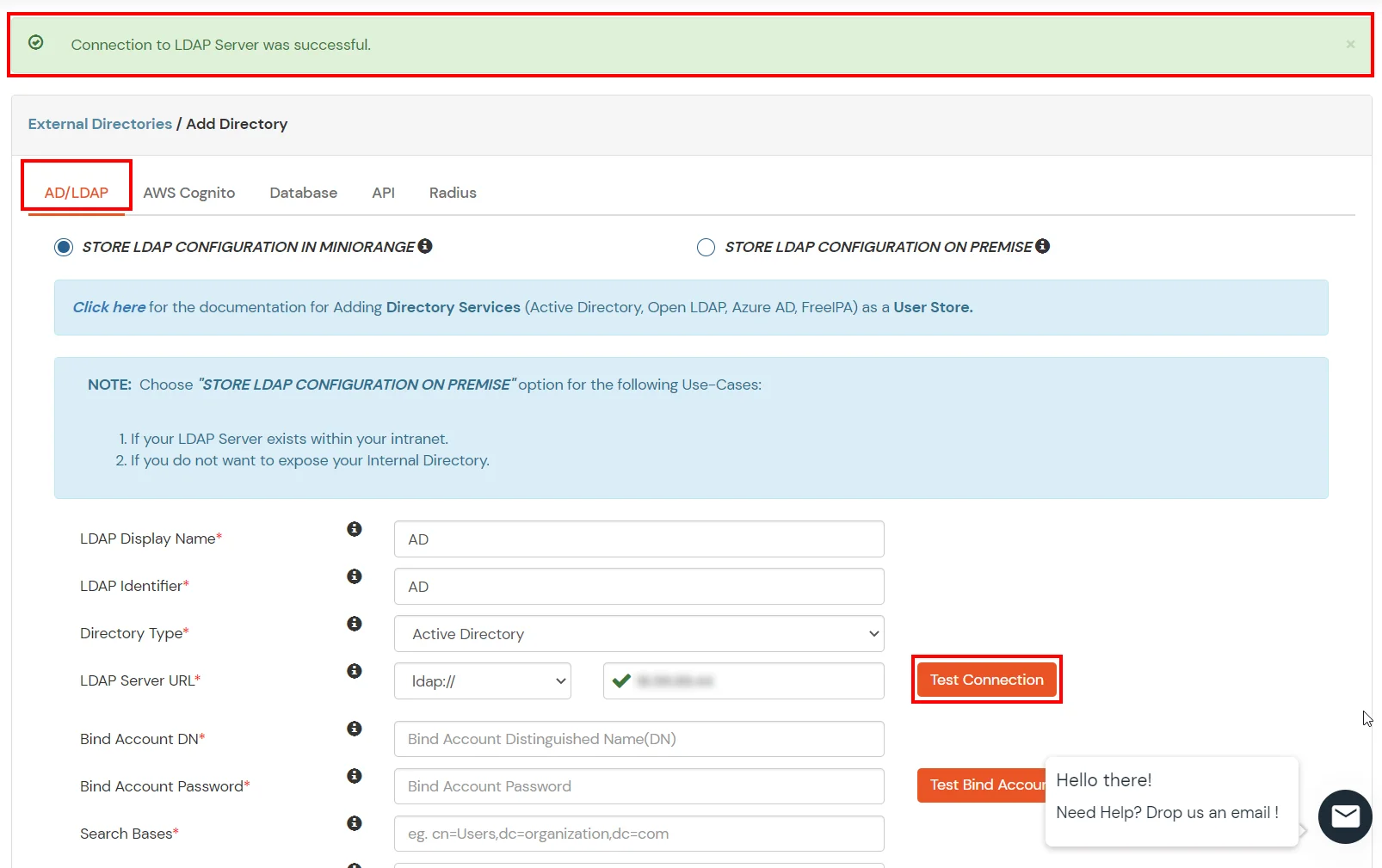
- Click on the Test Connection button to verify if you have made a successful connection with your LDAP server.
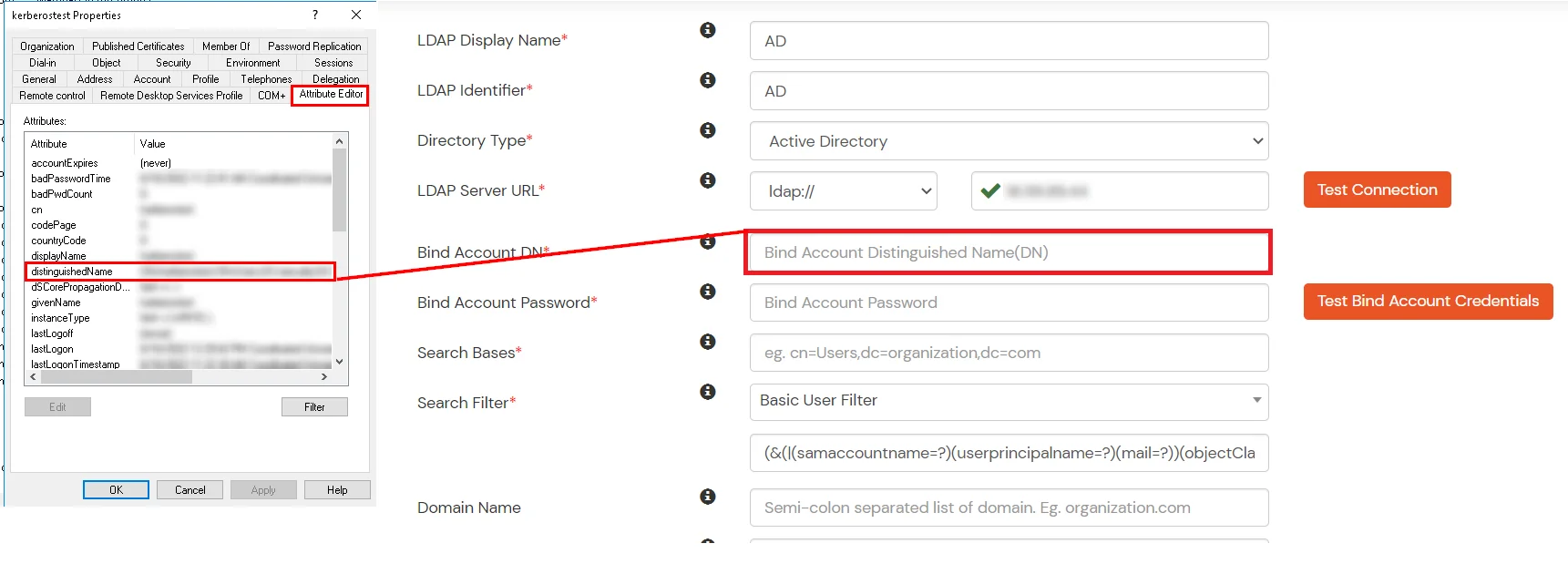
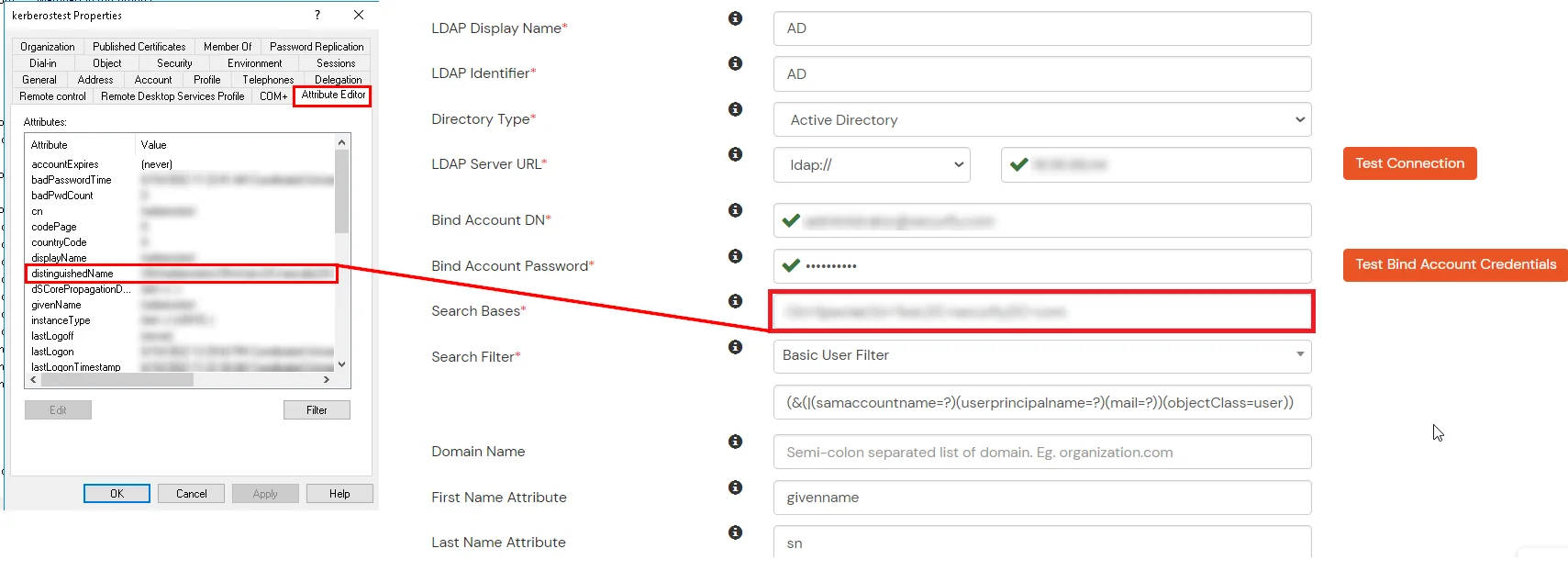
- In Active Directory, go to the properties of user containers/OU's and search for the Distinguished Name attribute. The bind account should have minimum required read privileges in Active Directory to allow directory lookups. If the use case involves provisioning (such as creating, updating, or deleting users or groups), the account must also be granted appropriate write permissions.
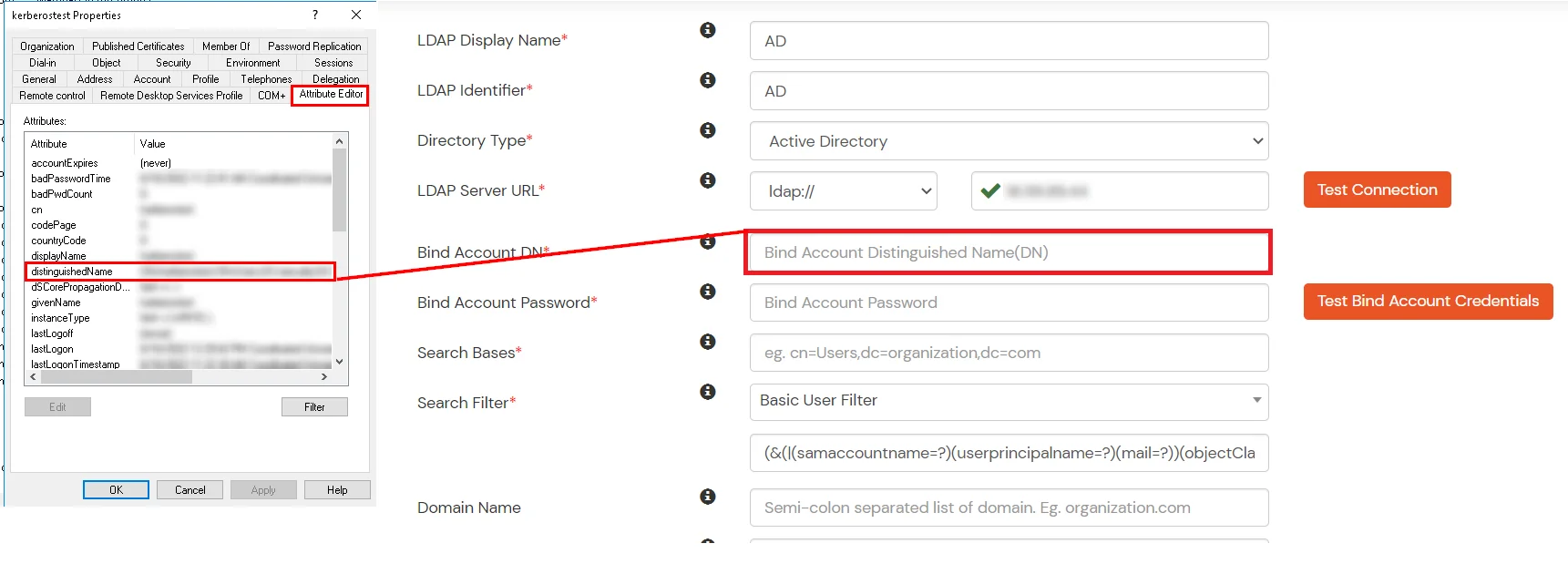
- Enter the valid Bind account Password.
- Click on the Test Bind Account Credentials button to verify your LDAP Bind credentials for LDAP connection.
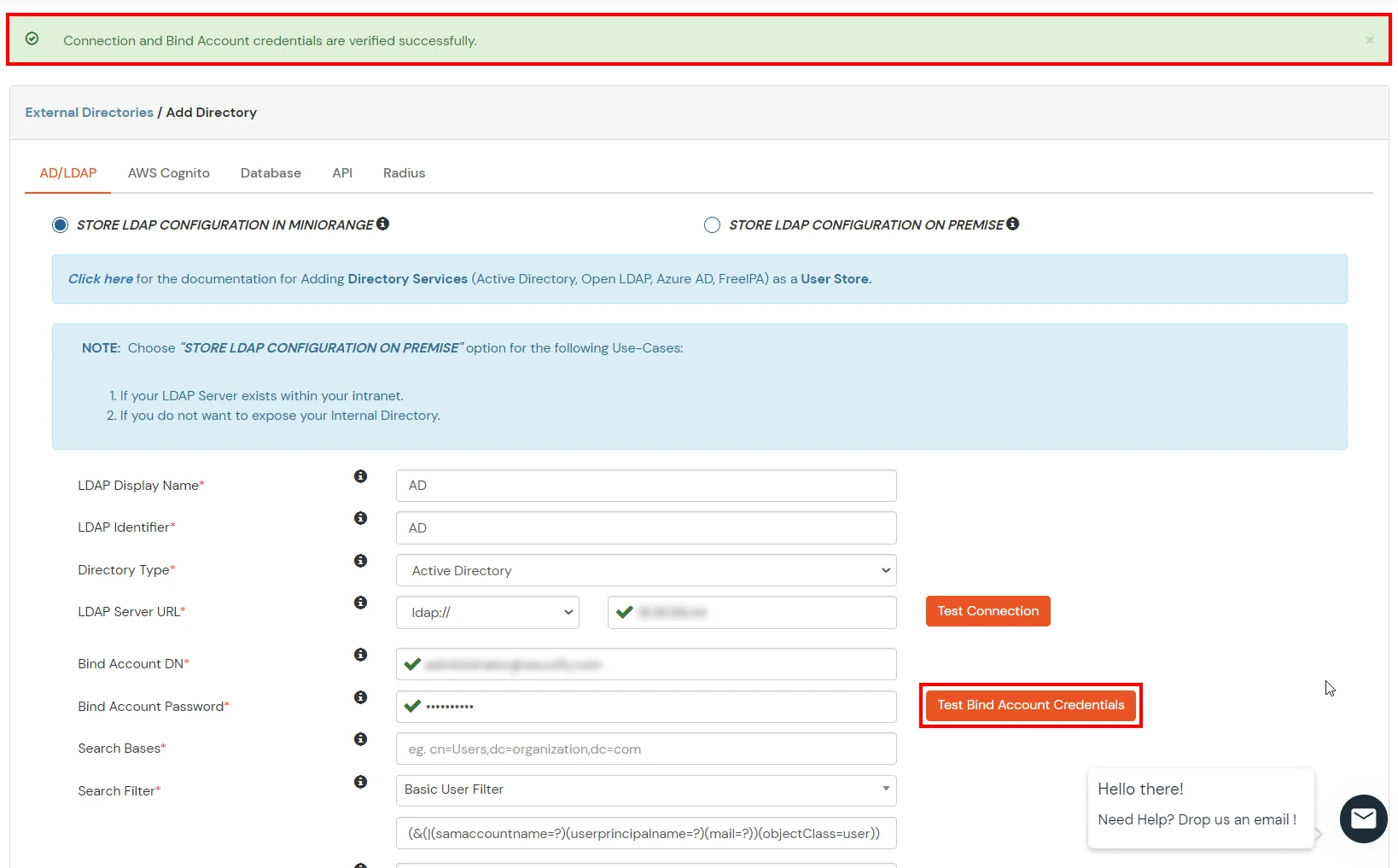
- Search Base is the location in the directory where the search for a user begins. You will get this from the same place you got your Distinguished name.
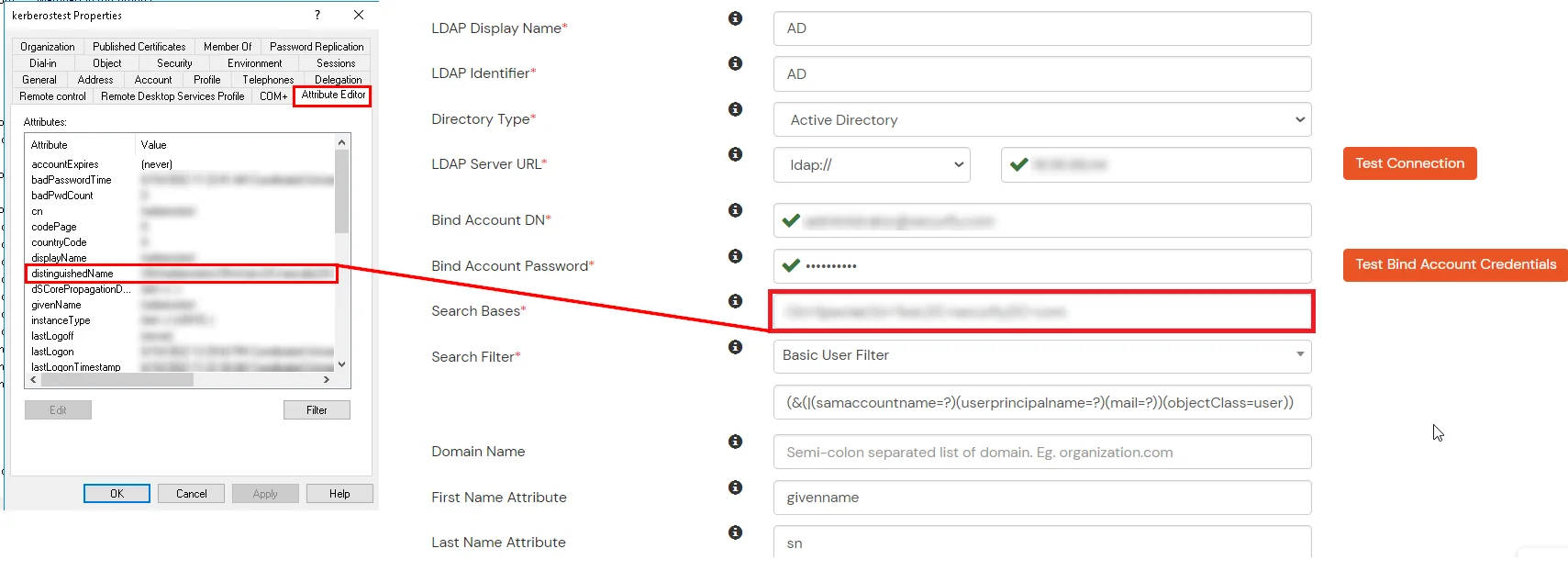
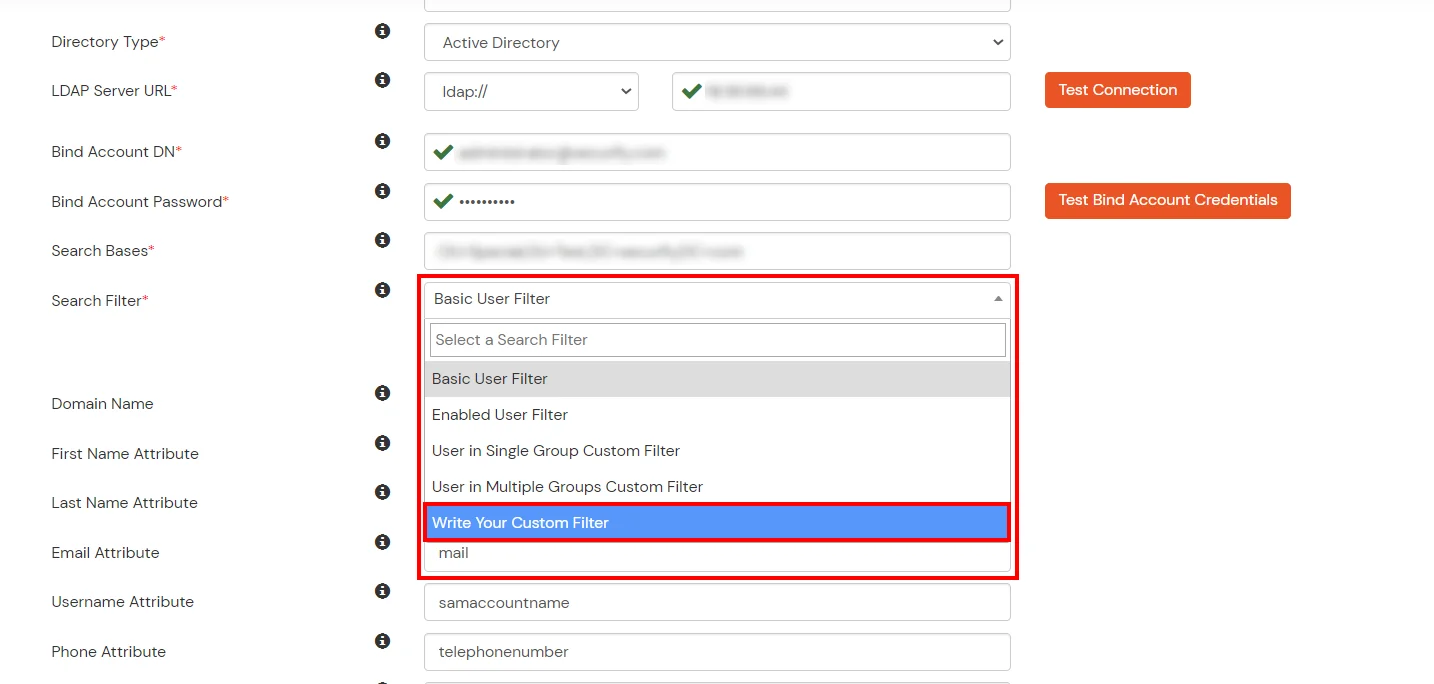
- Select a suitable Search filter from the drop-down menu. If you use User in Single Group Filter or User in Multiple Group Filter, replace the <group-dn> in the search filter with the distinguished name of the group in which your users are present. To use custom Search Filter select "Write your Custom Filter" option and customize it accordingly.
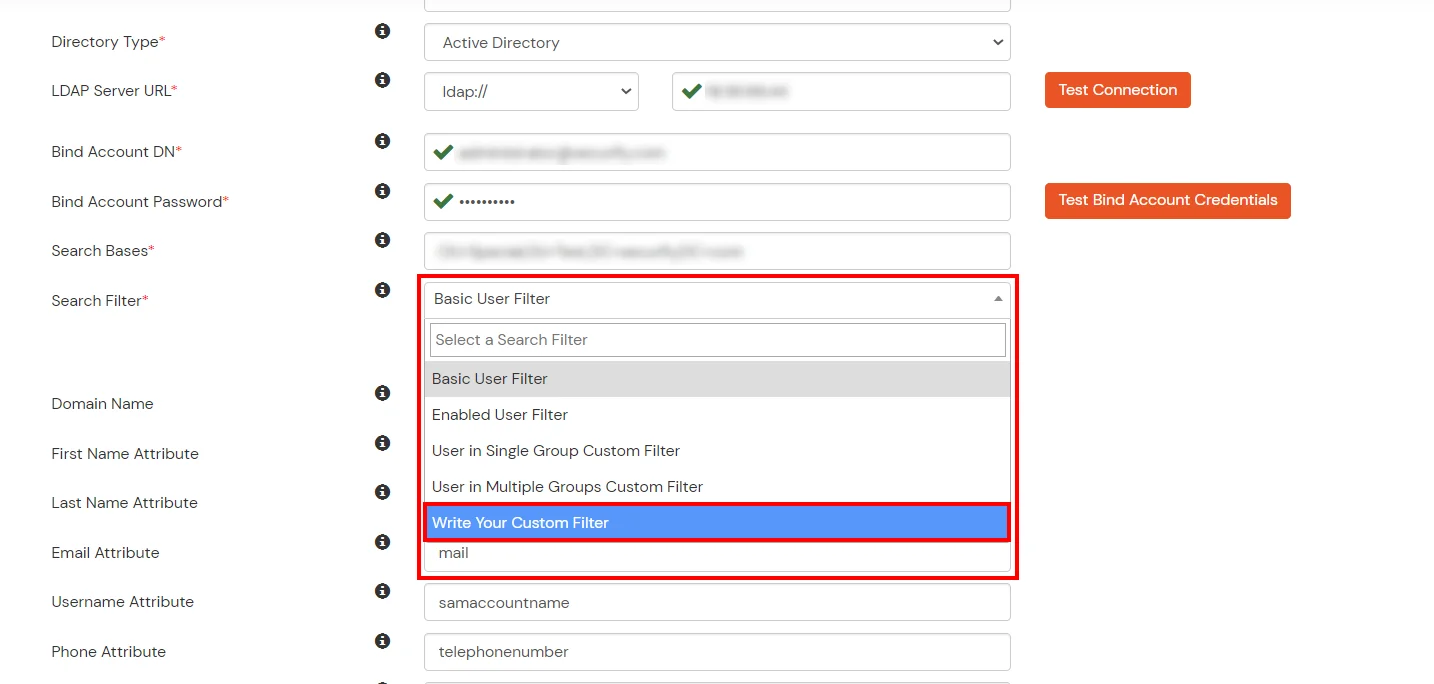
- Click on the Next button, or go to the Login Options tab.
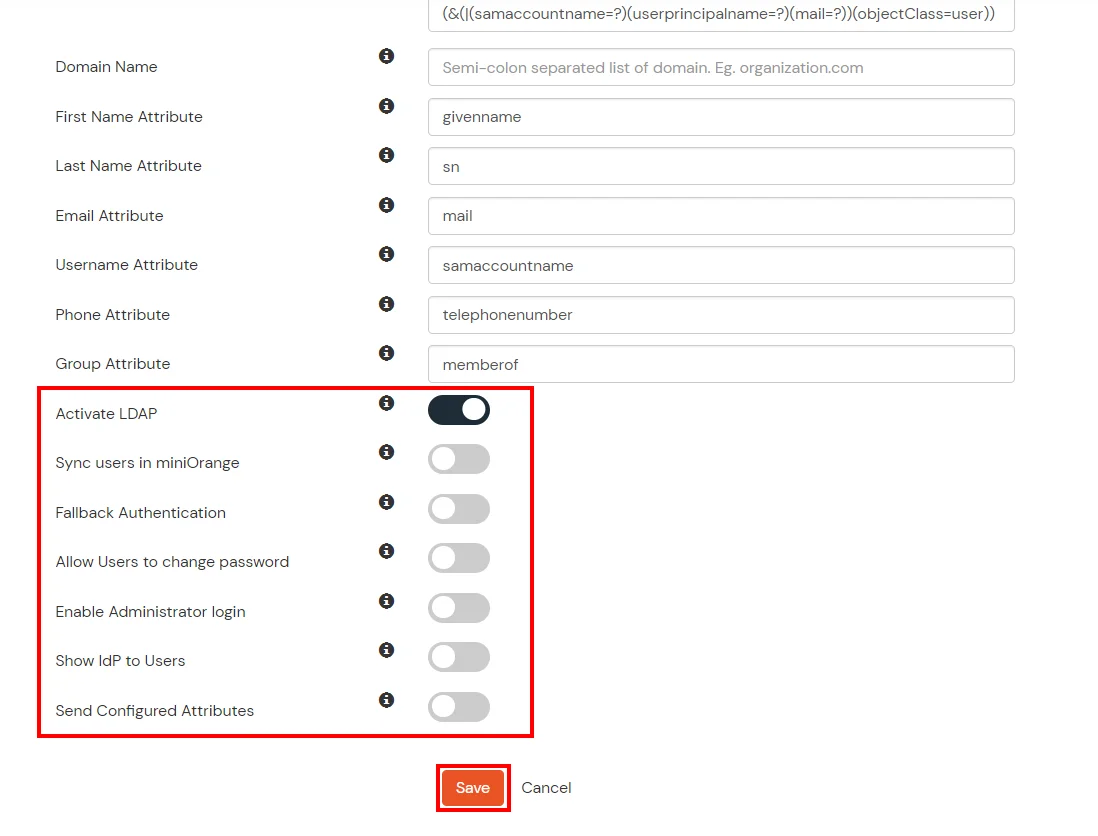
- You can also configure following options while setting up AD. Enable Activate LDAP in order to authenticate users from AD/LDAP. Click on the Next button to add user store.
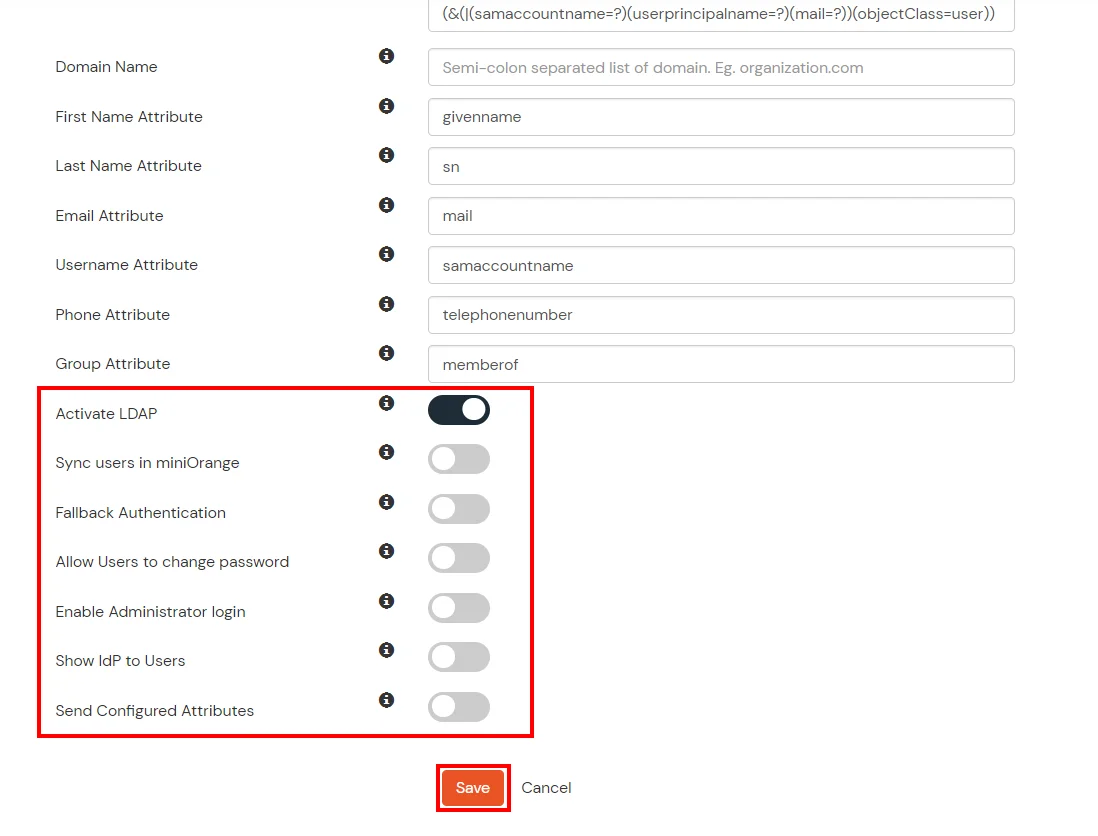
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute |
Description |
| Activate LDAP |
All user authentications will be done with LDAP credentials if you Activate it |
| Fallback Authentication |
If LDAP credentials fail then user will be authenticated through miniOrange |
| Enable administrator login |
On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users |
If you enable this option, this IdP will be visible to users |
| Sync users in miniOrange |
Users will be created in miniOrange after authentication with LDAP |
- Click on the Next button, or go to the Attributes tab.
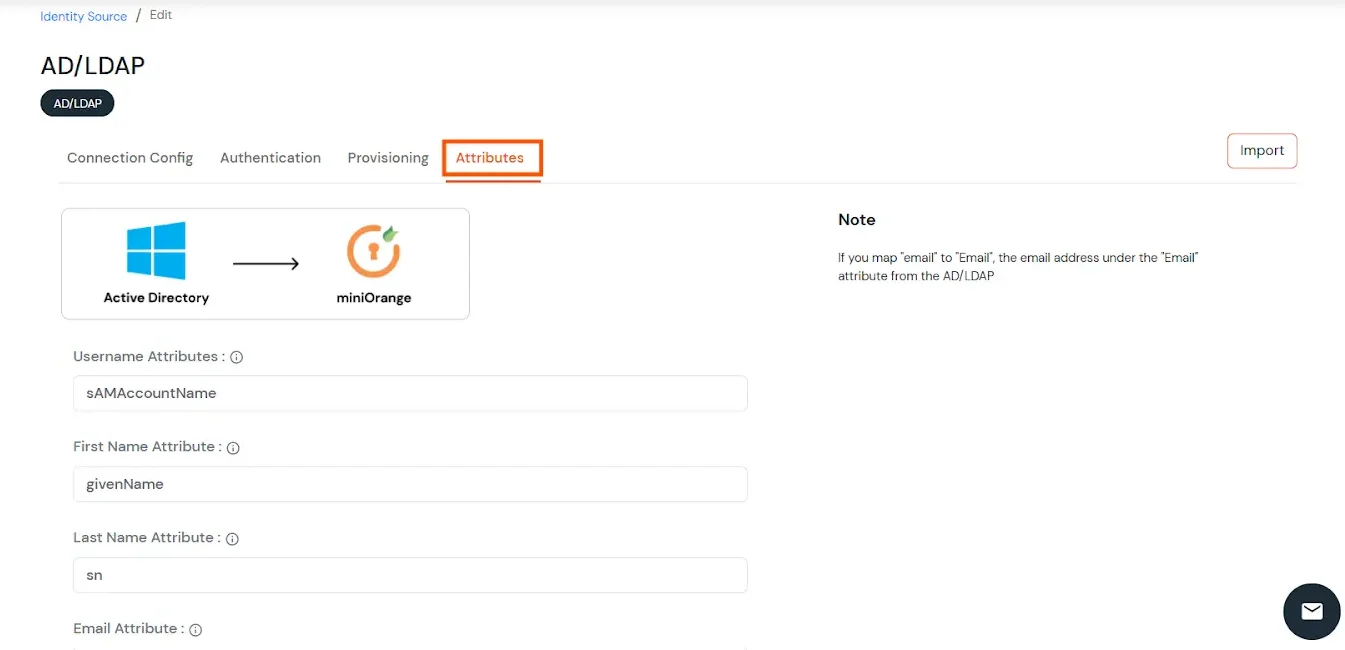
Attributes Mapping from AD
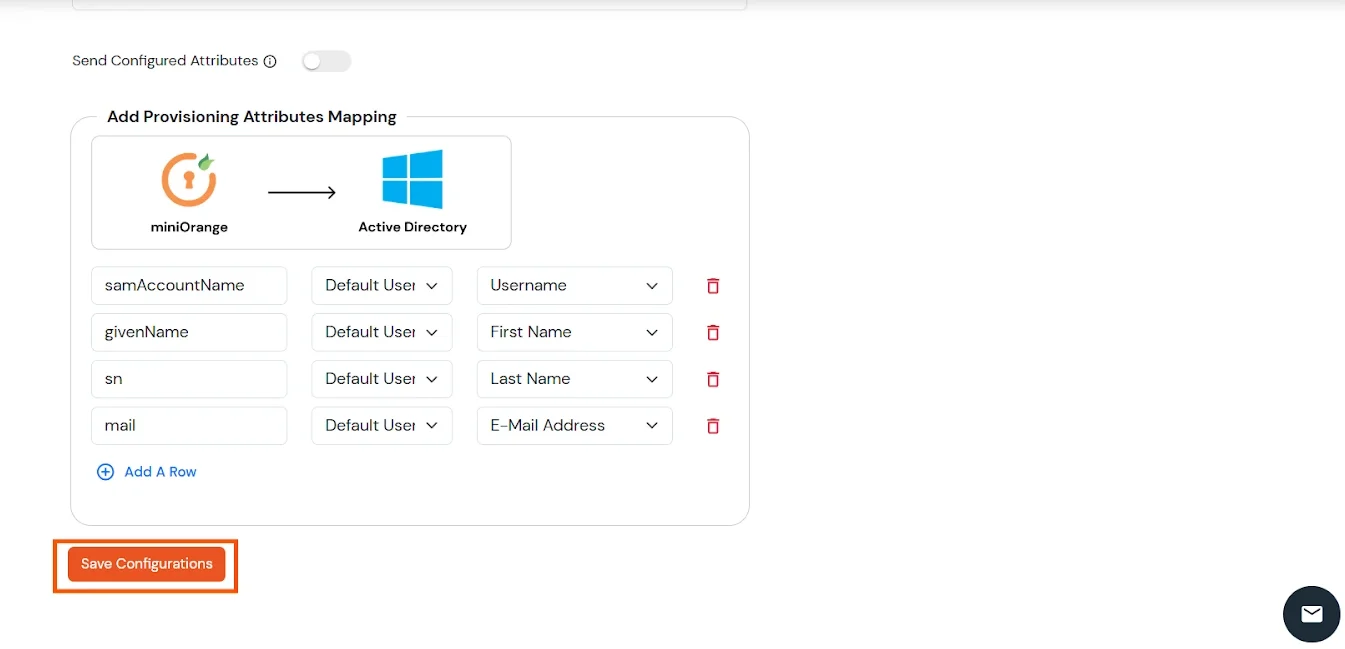
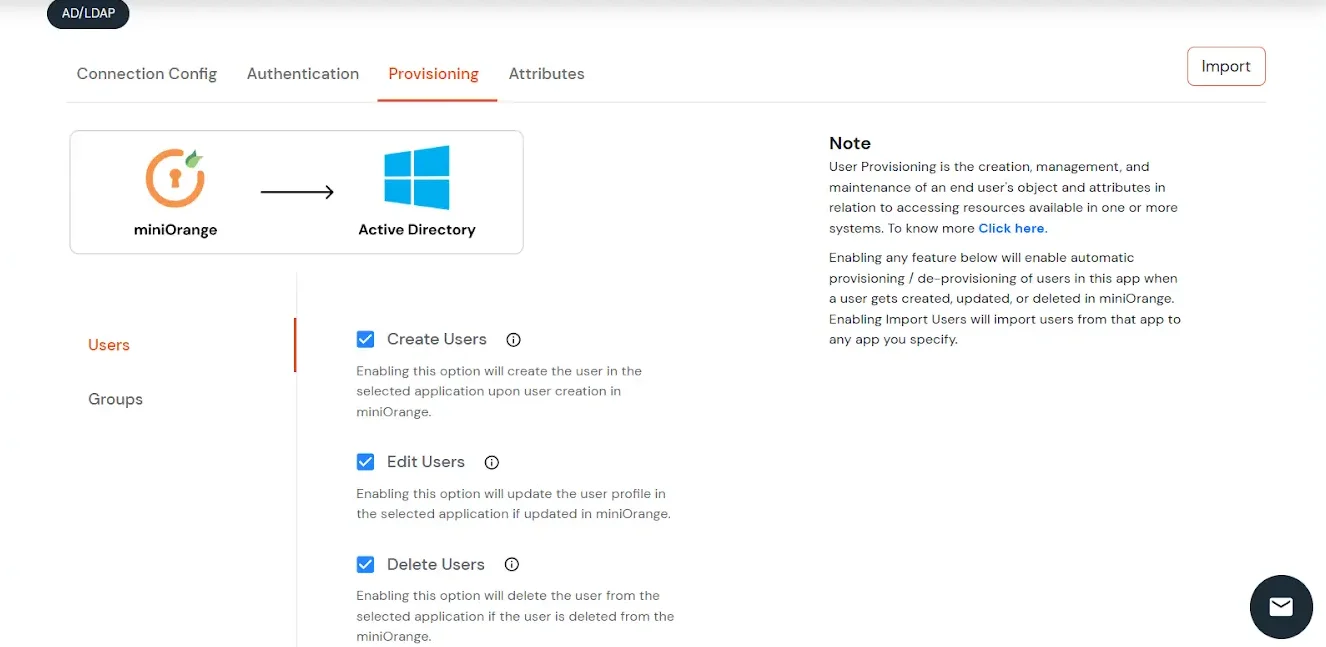
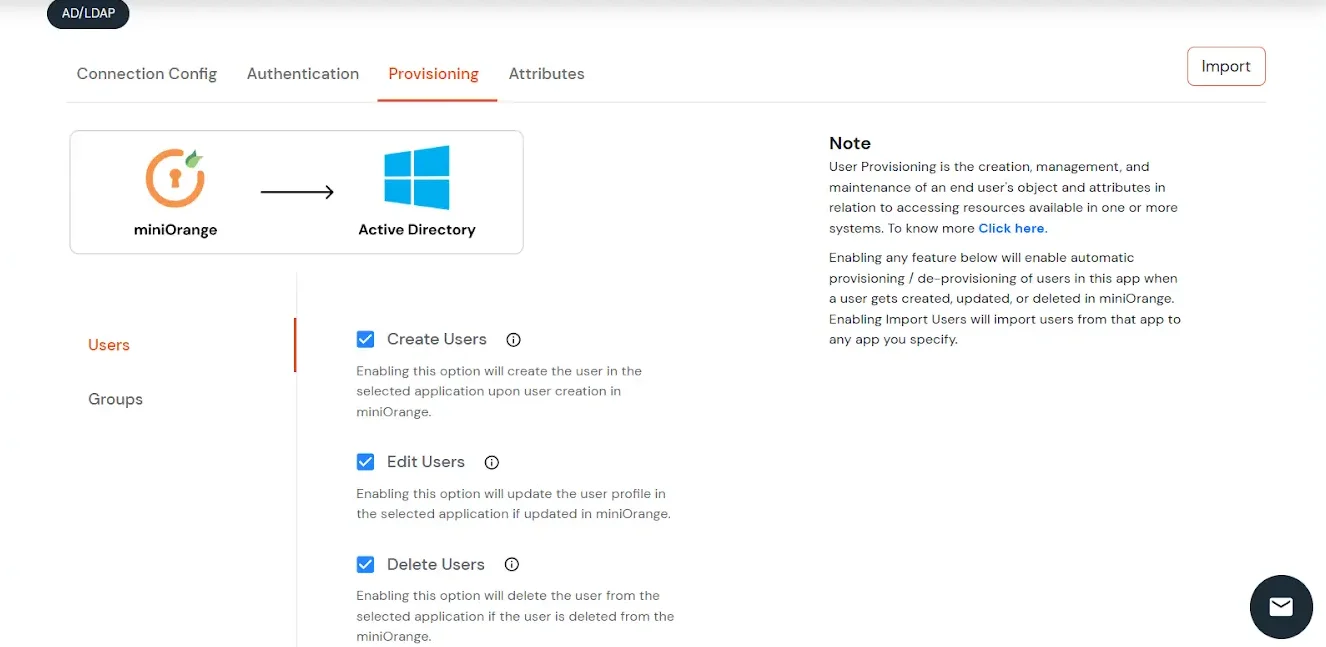
User Import and Provisioning from AD
- If you want to set up provisioning, click here for detailed information. We will skip this step for now.
Import Password Policy from AD
- If you want to import your Active Directory password policy into miniOrange, click here for detailed information. We will skip this step for now.
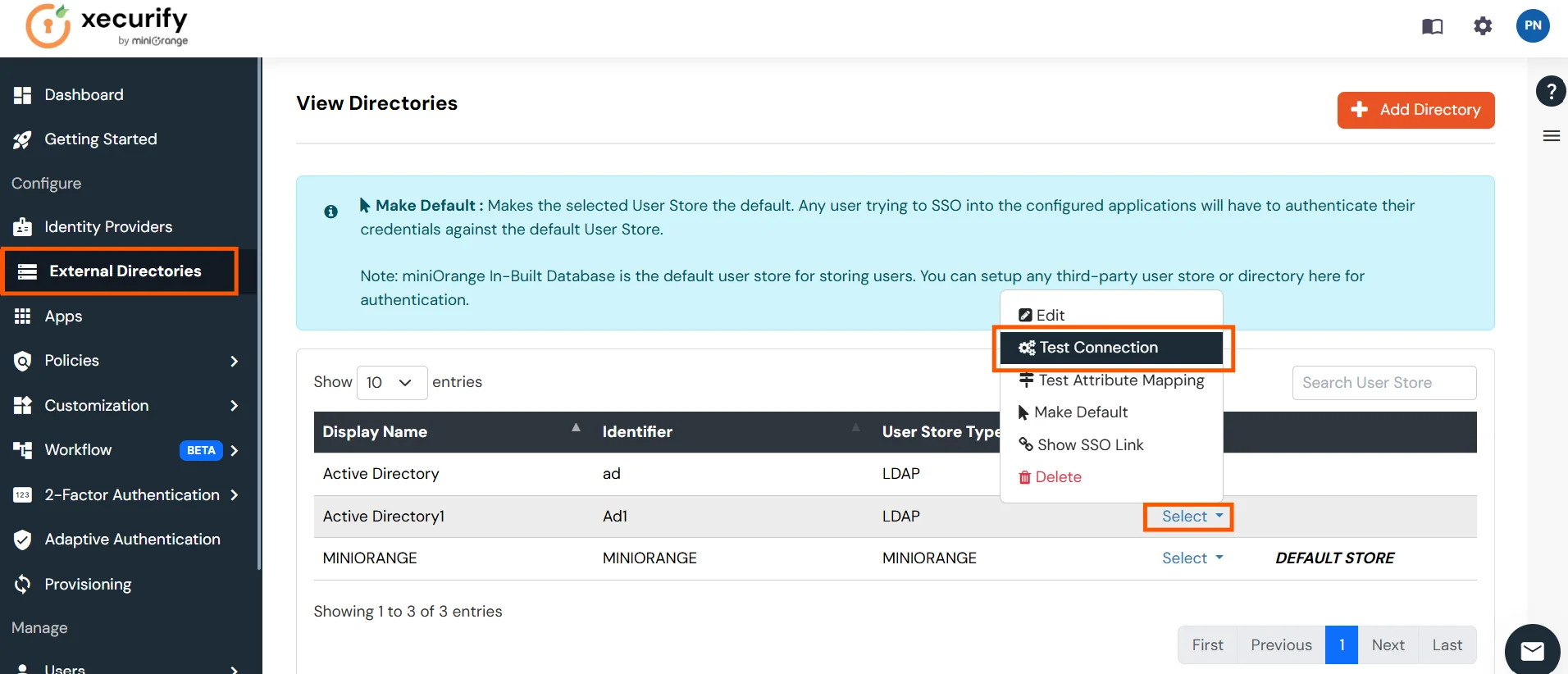
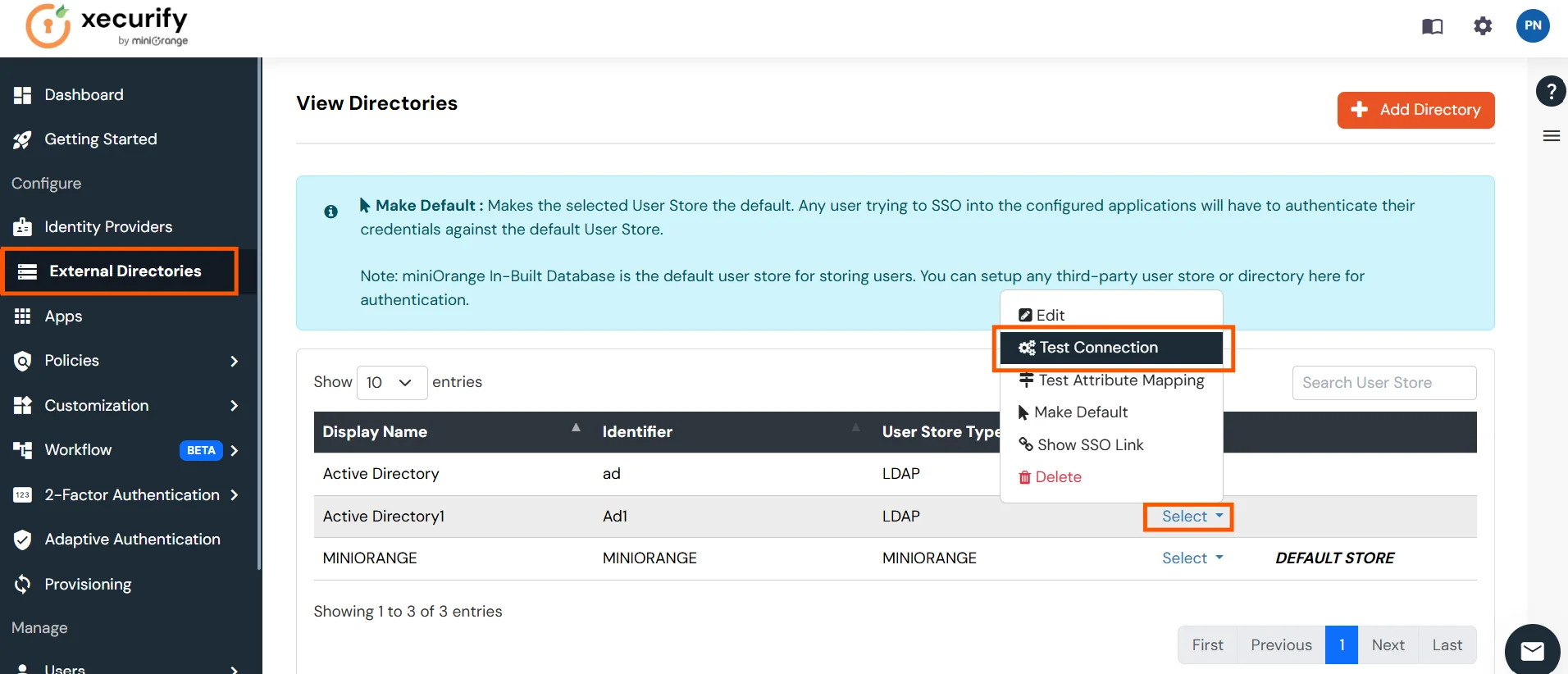
Test Connections
- You will see a list of directories under Identity Providers. From the dropdown, select AD/LDAP Directories, search for your configured directory, click the three dots next to it, and select Test Connection.
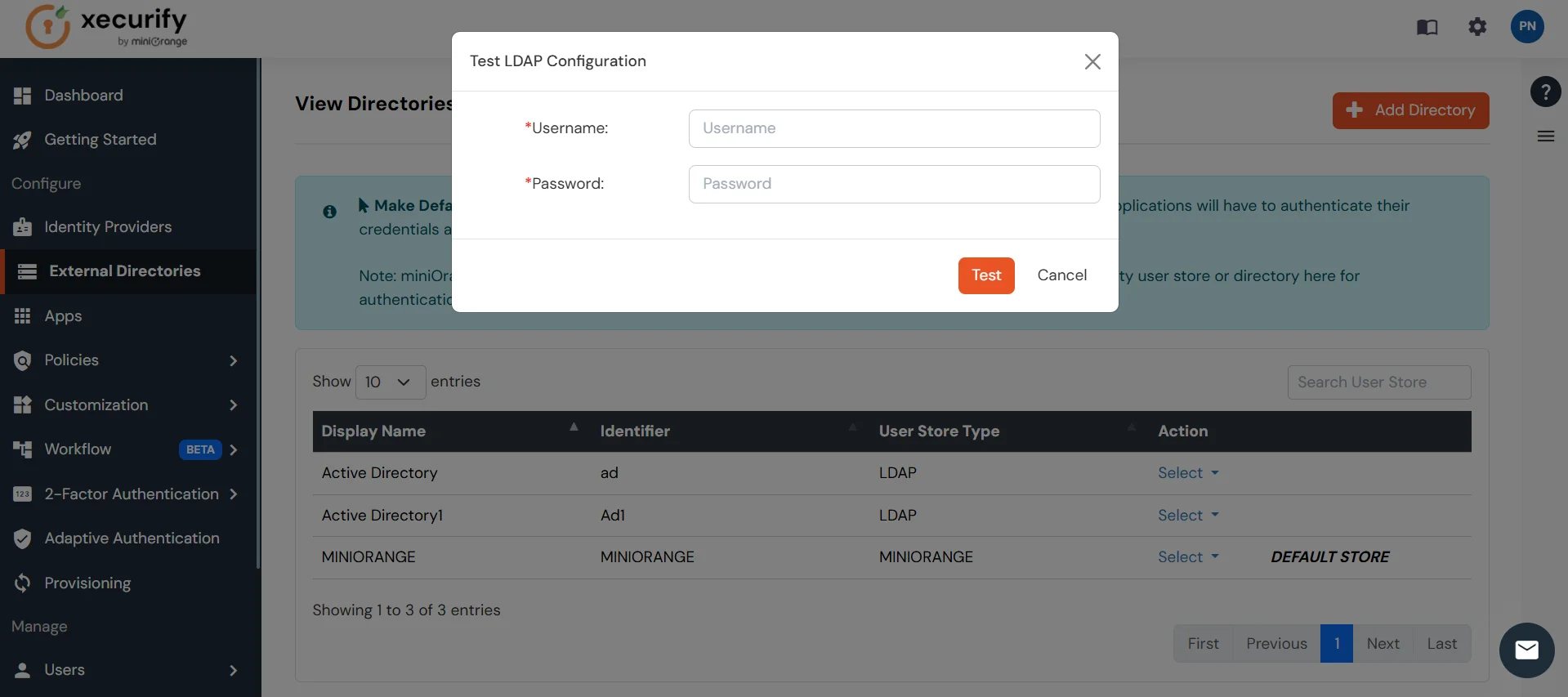
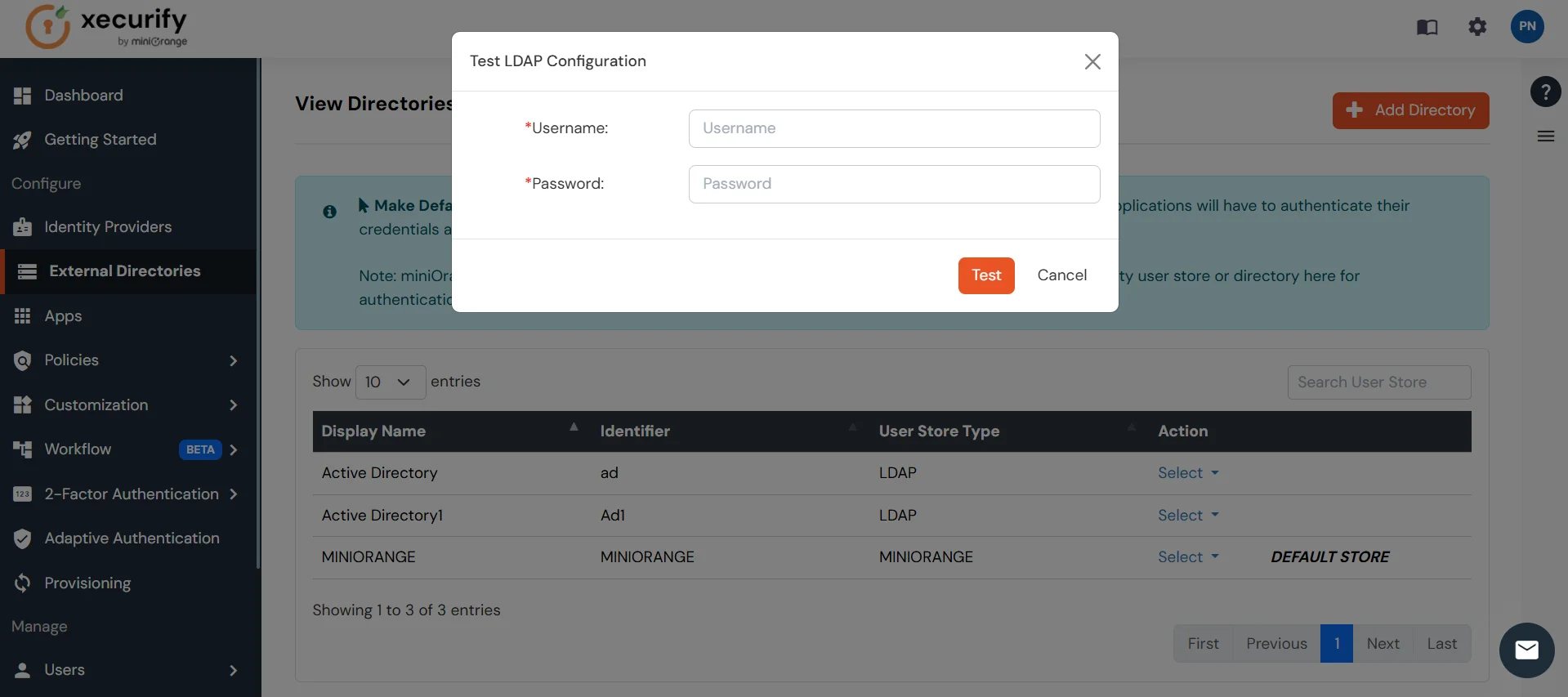
- A pop-up appears prompting you to enter a username and password to verify your LDAP configuration.
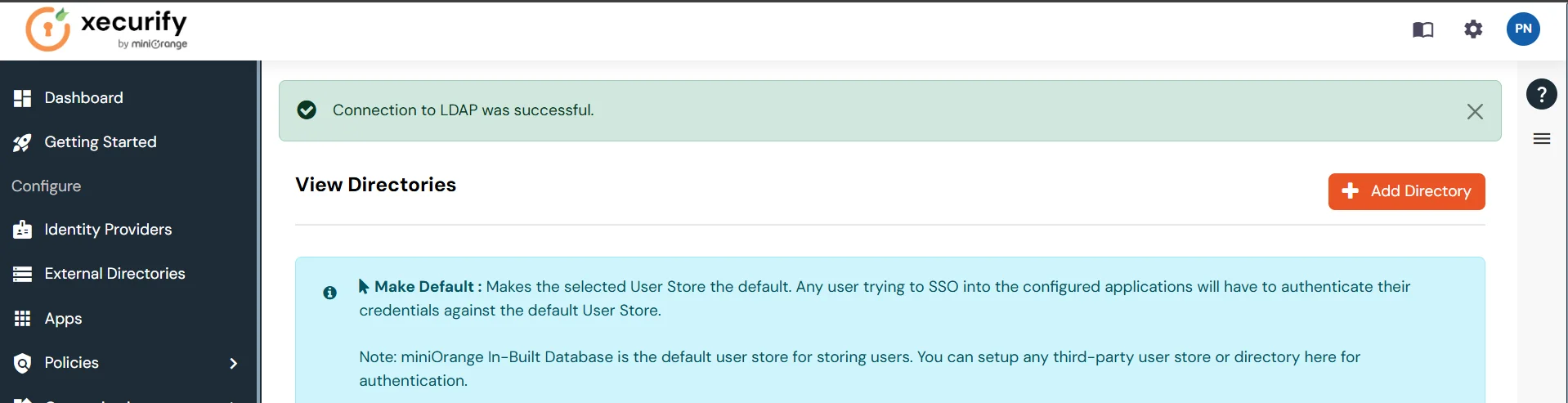
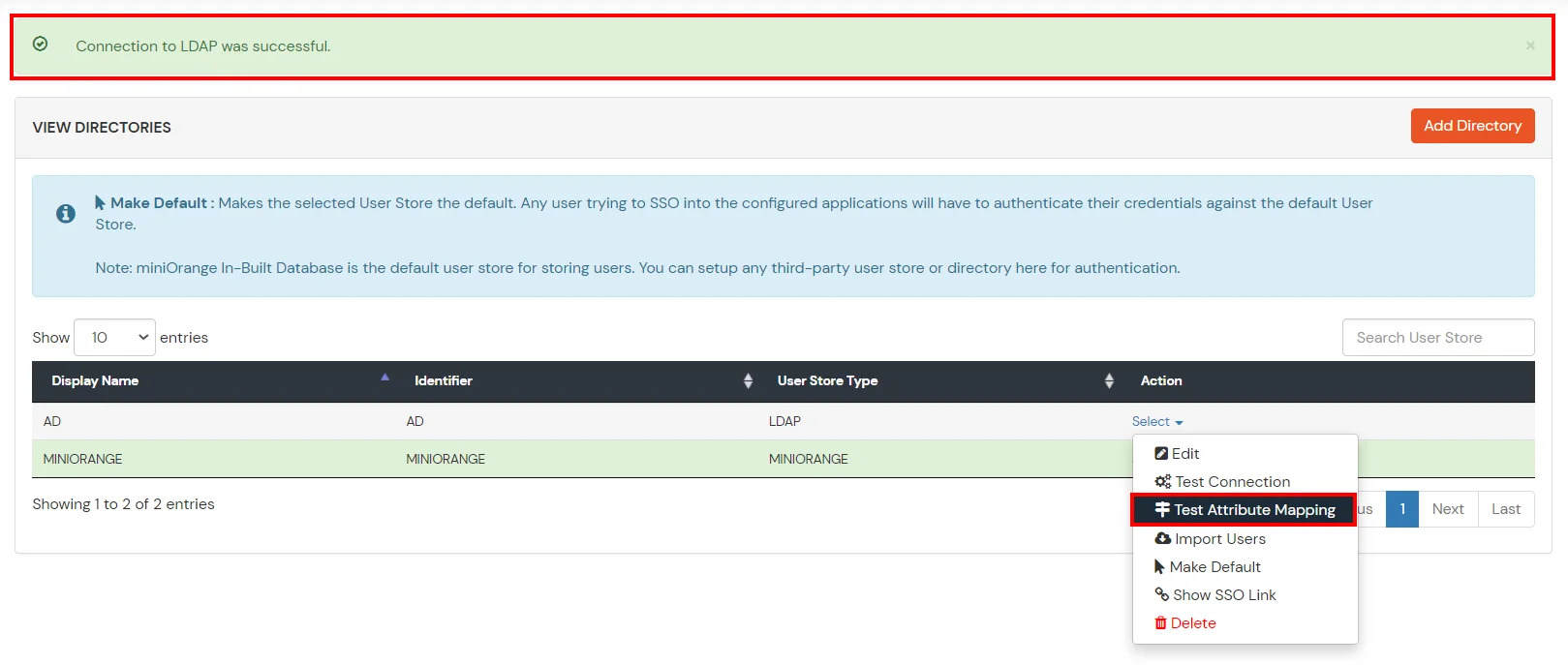
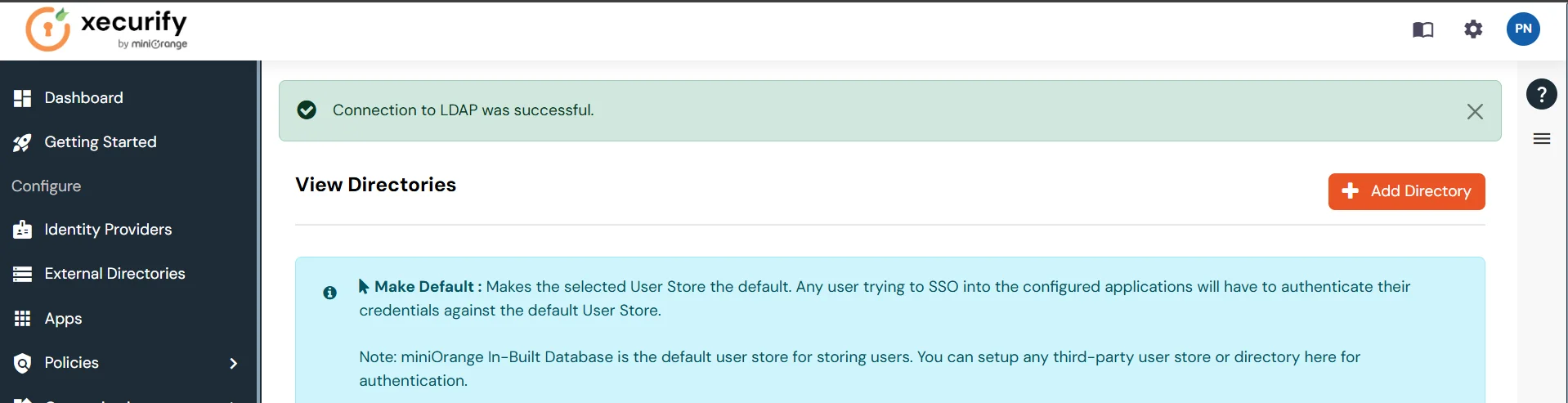
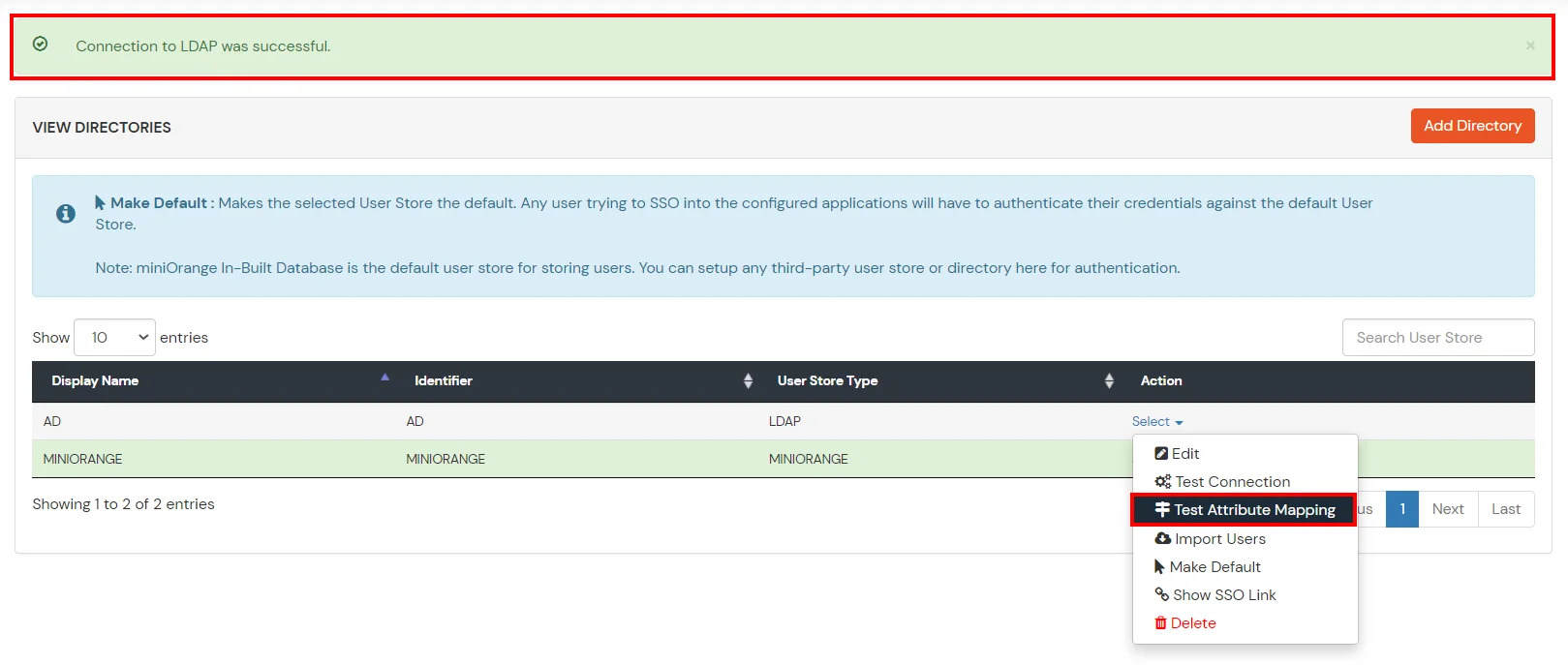
- On Successful connection with LDAP Server, a success message is shown.
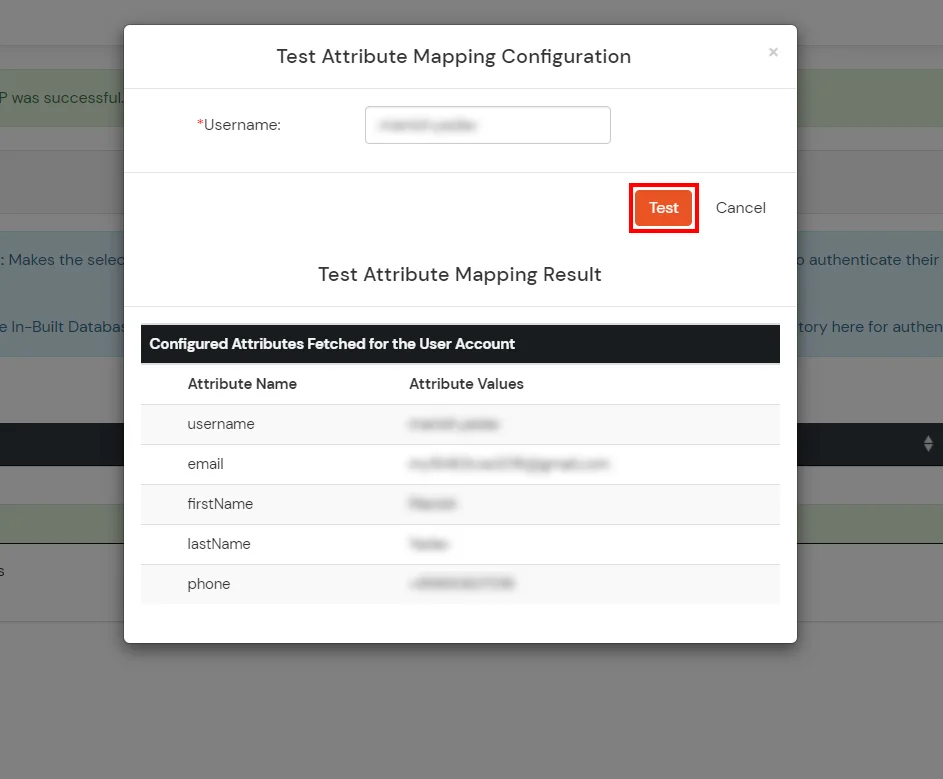
Test Attribute Mapping
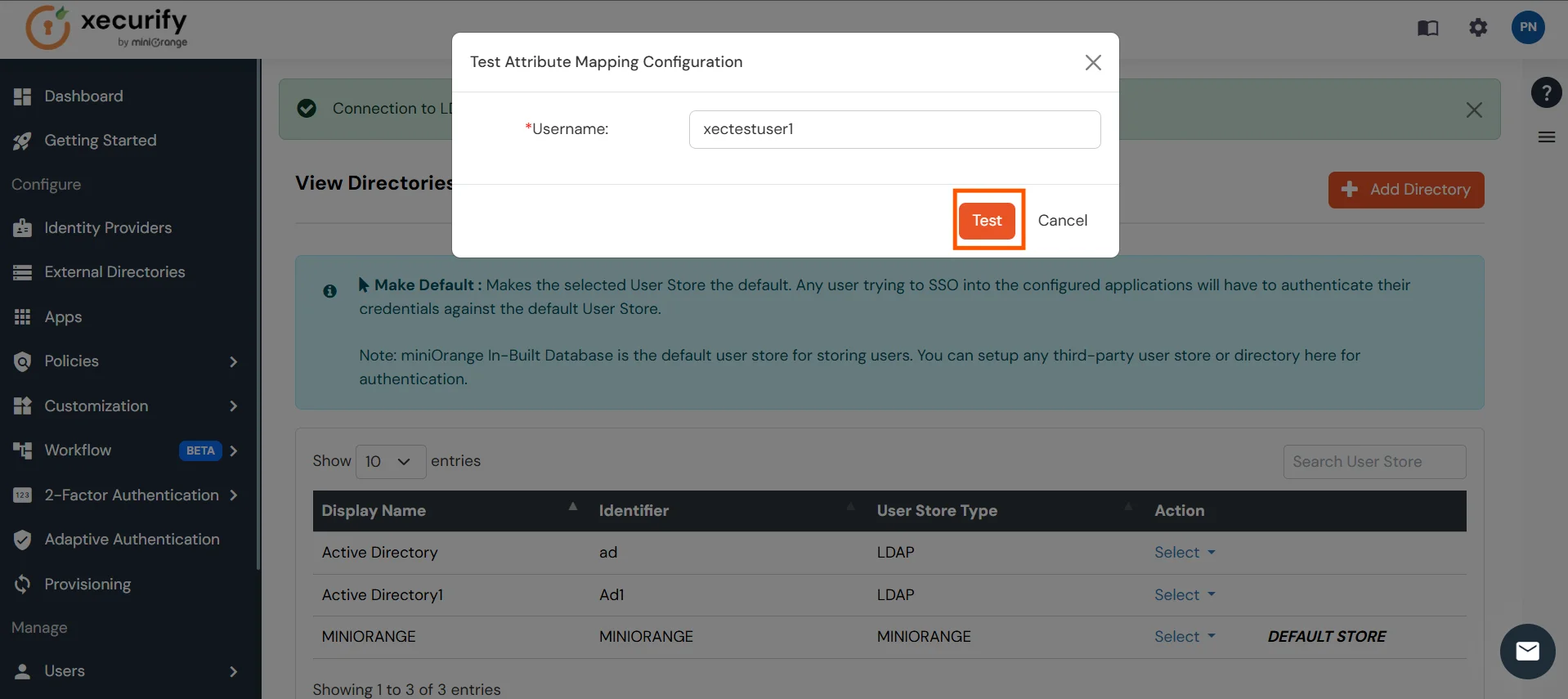
- You will see a list of directories under Identity Providers. From the dropdown, select AD/LDAP Directories, search for your configured directory, click the three dots next to it, and select Test Attribute Mapping.
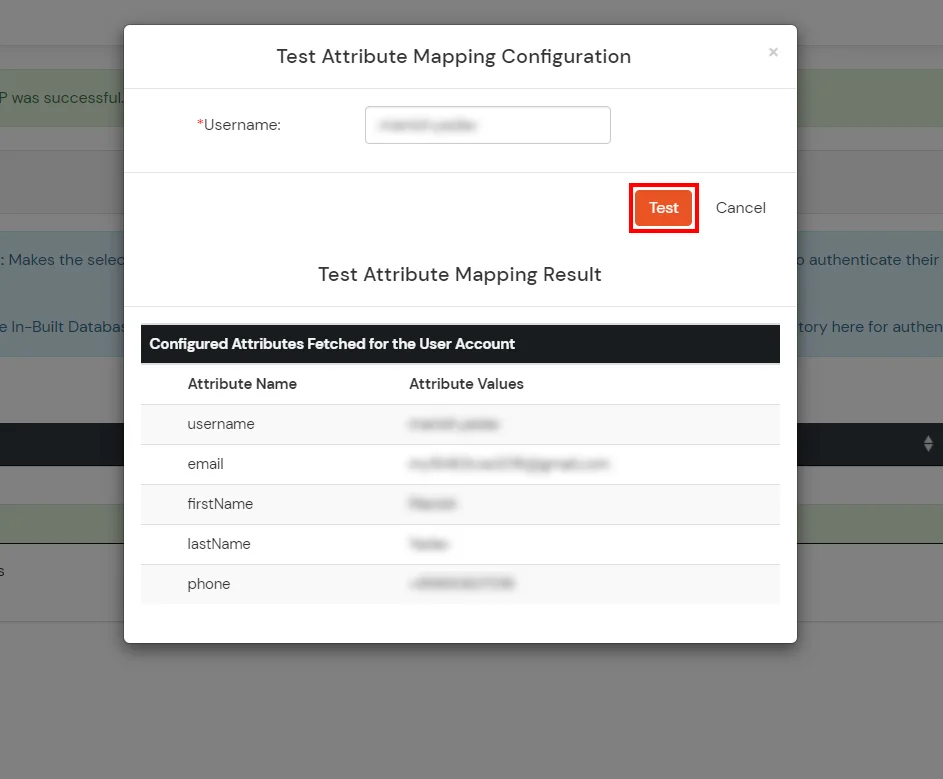
- A pop‑up appears to enter a username and click Test.
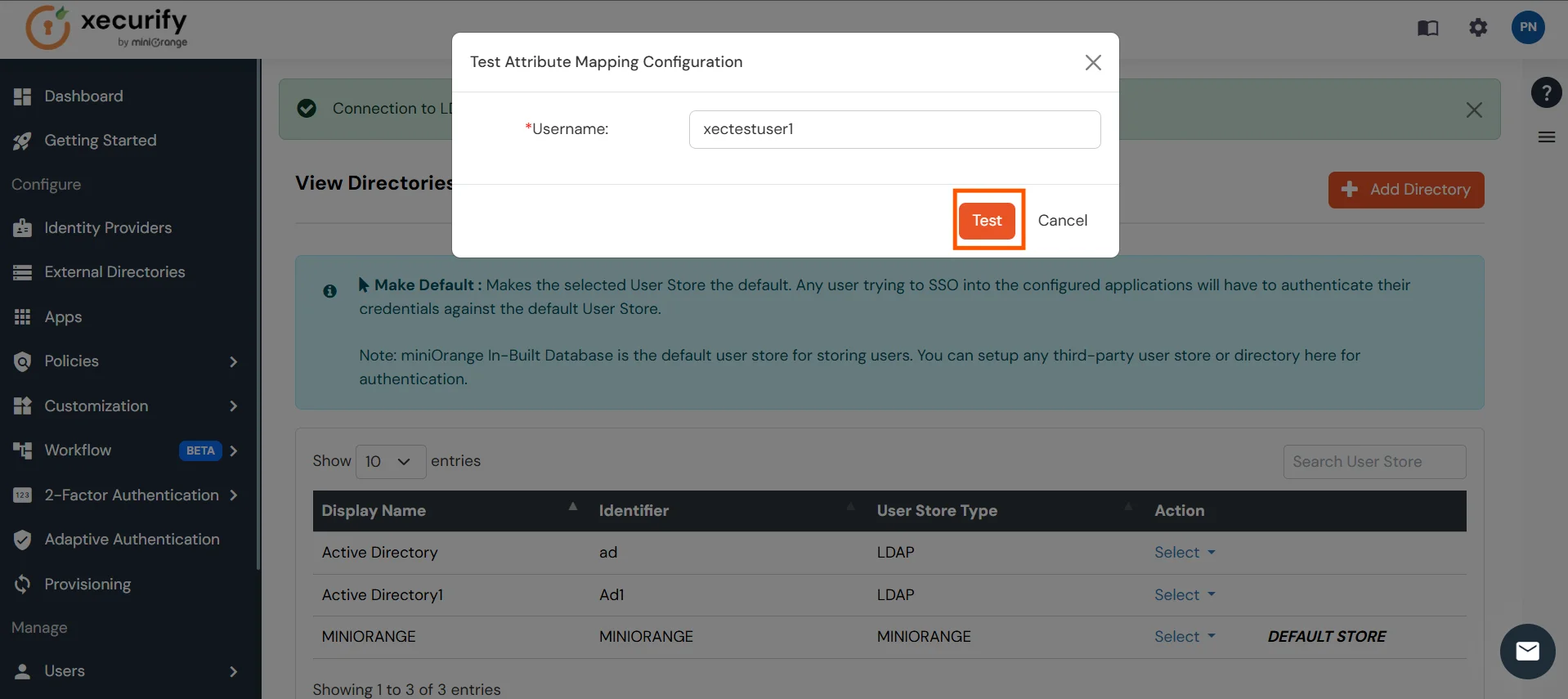
- The Test Attribute Mapping Result will be displayed.
Set up AD as External Directory configuration is complete.
Note: Refer our guide to setup LDAP on windows server.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
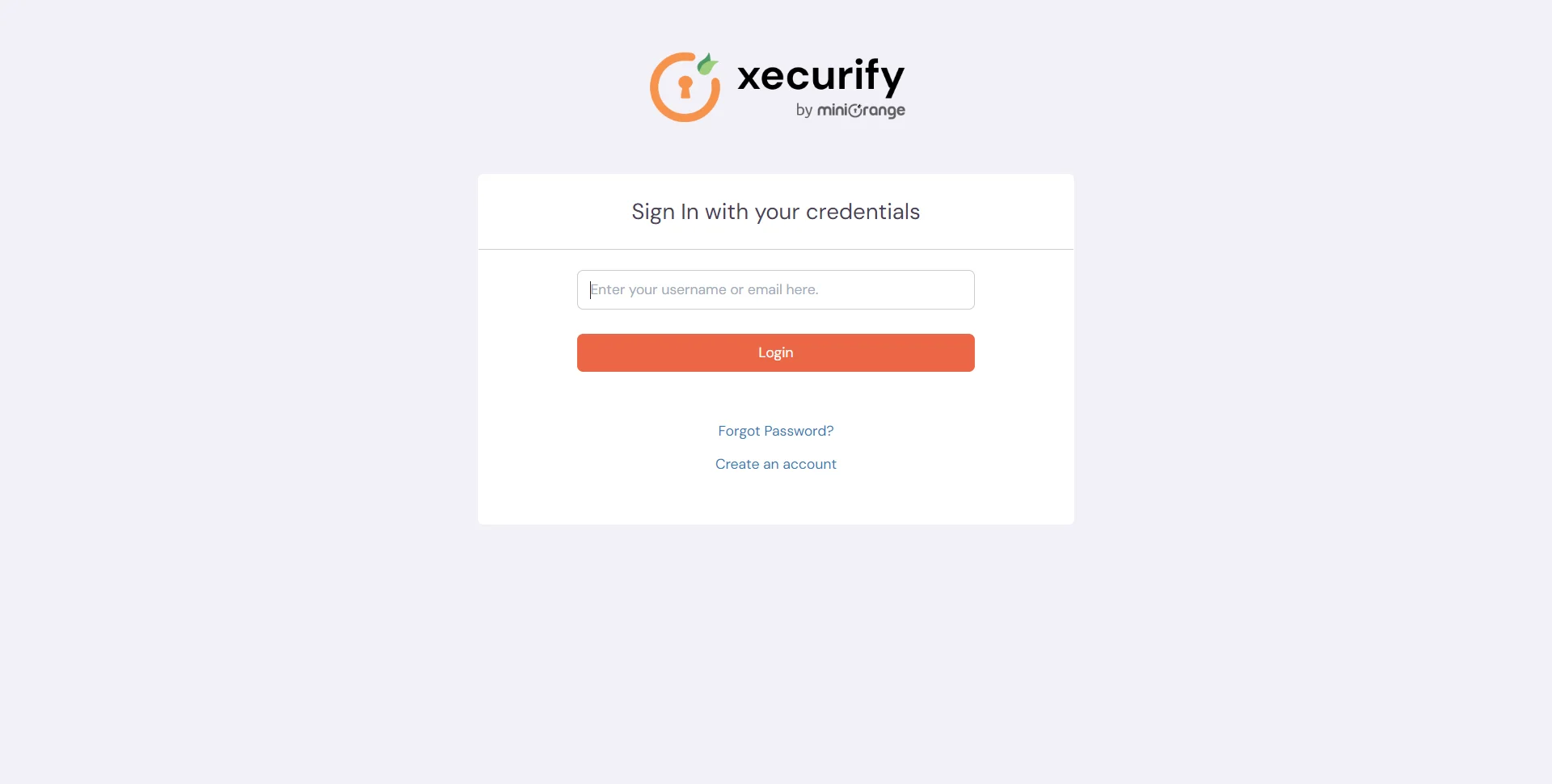
4. Test SSO Configuration
Test SSO login to your Websphere account with miniOrange IdP:
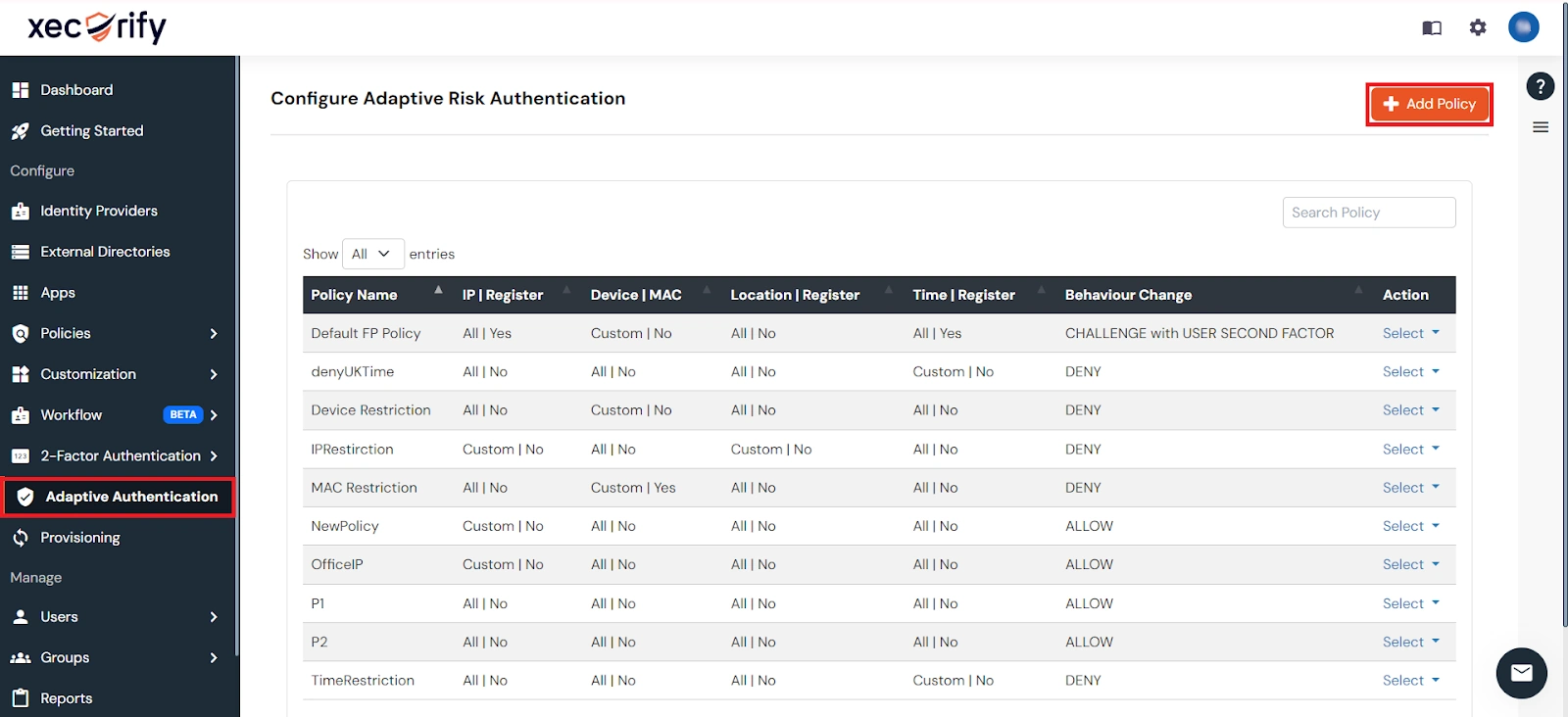
5. Adaptive Authentication with Websphere
A. Restricting access to Websphere with IP Configuration
You can use adaptive authentication with Websphere Single Sign-On (SSO) to improve the security and functionality of Single Sign-On. You can allow a IP Address in certain range for SSO or you can deny it based your requirements and you can also challenge the user to verify his authenticity. Adaptive authentication manages the user authentication bases on different factors such as Device ID, Location, Time of Access, IP Address and many more.
You can configure Adaptive Authentication with IP Blocking in following way :
- Login to Self Service Console >> Adaptive Authentication >> Add Policy.
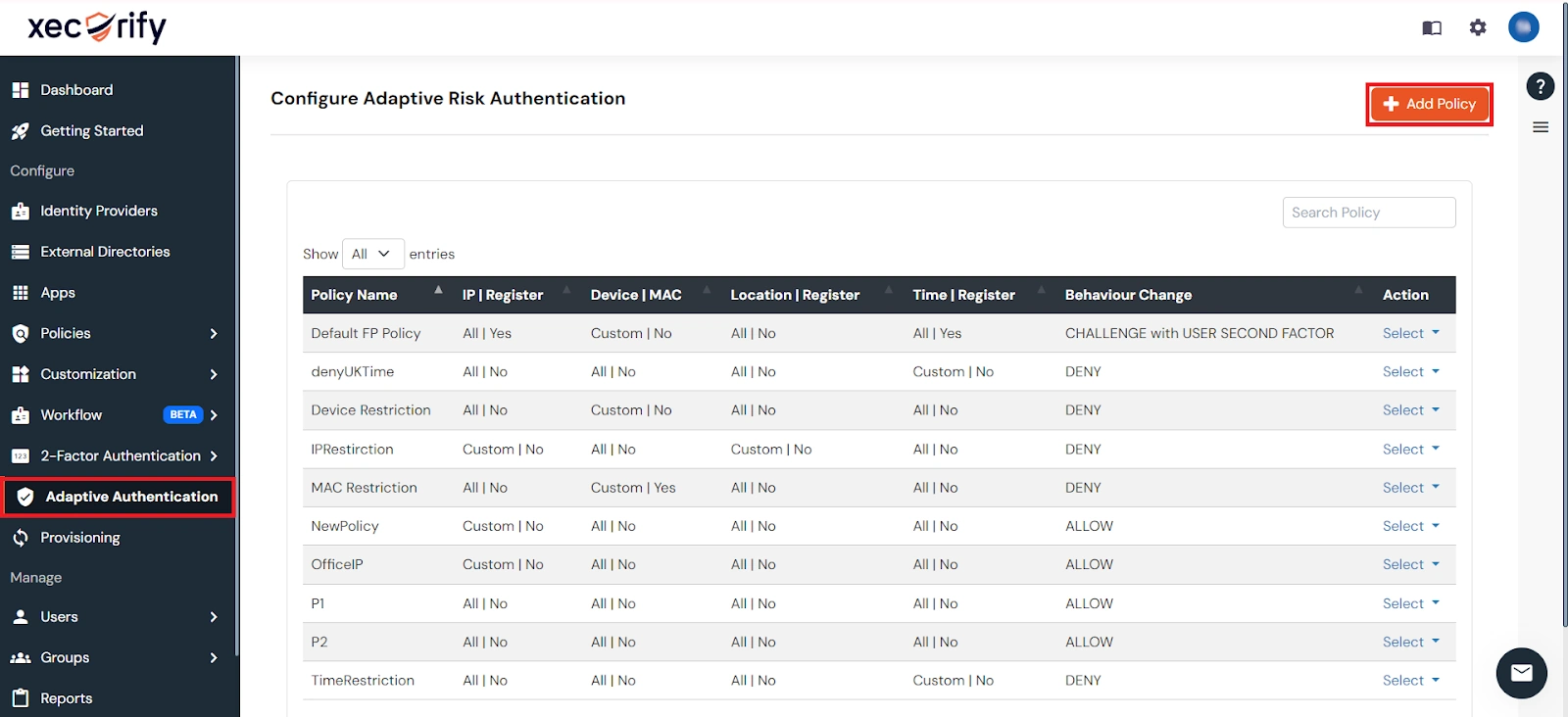
- Add a Policy Name for your Adative Authentication Policy.
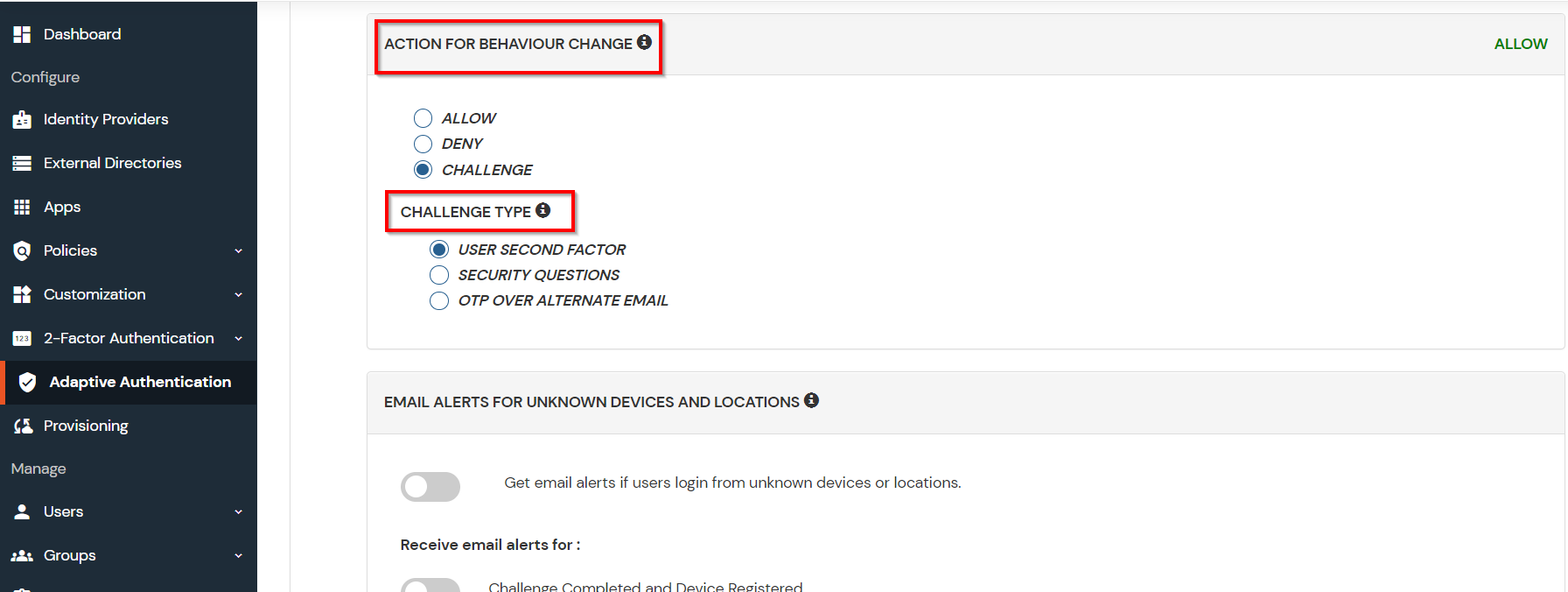
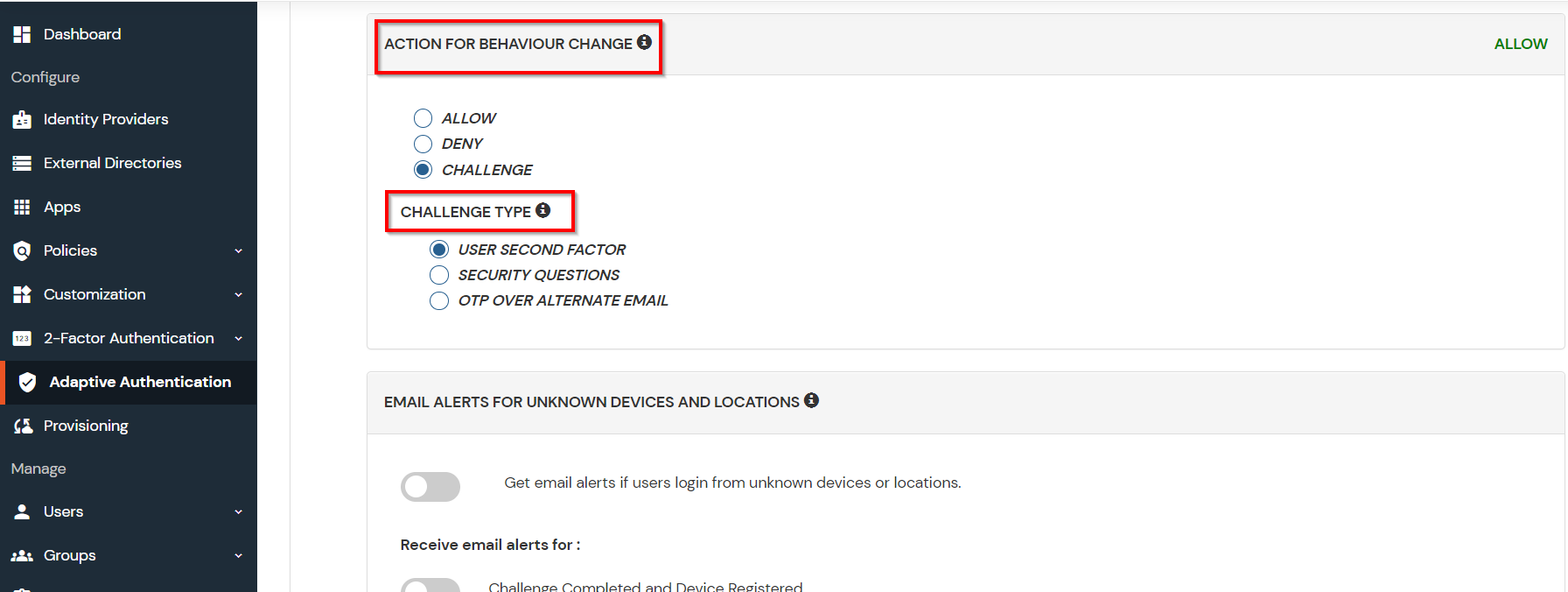
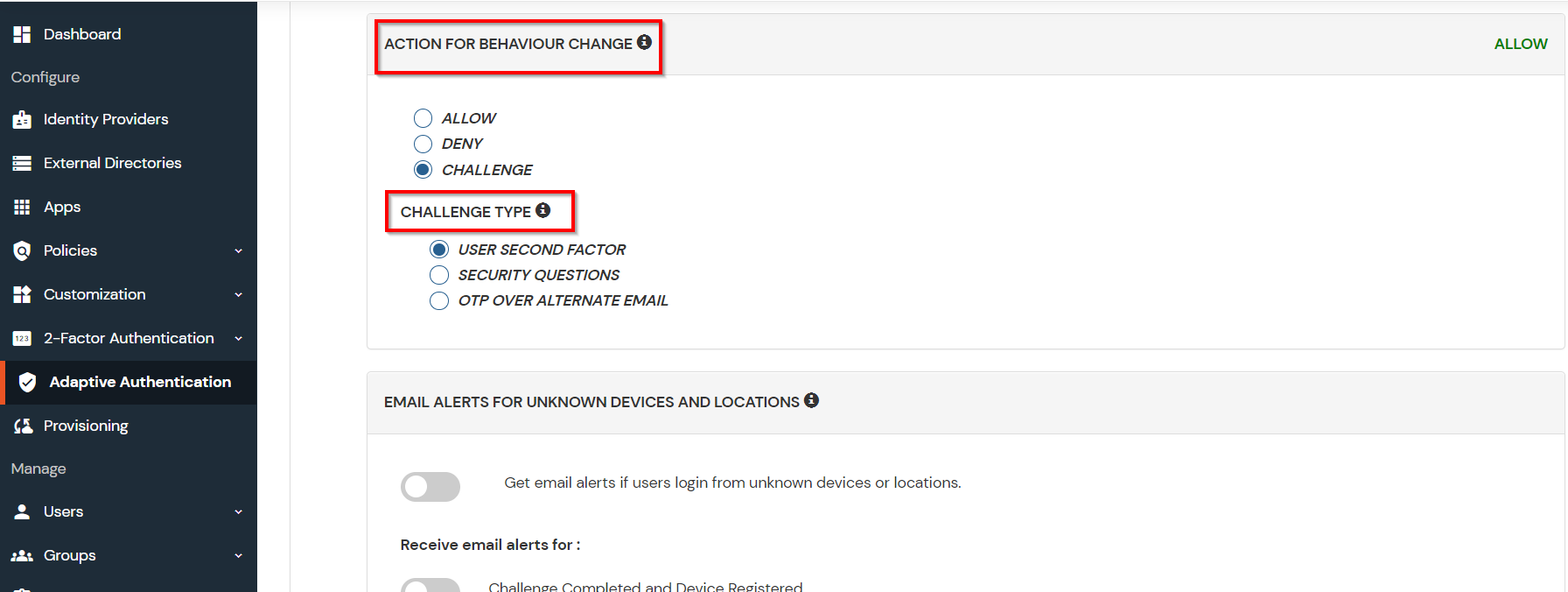
- Select Action for Behavior Change, click the Edit link, and then choose the appropriate Action and Challenge Type for the user from that section.
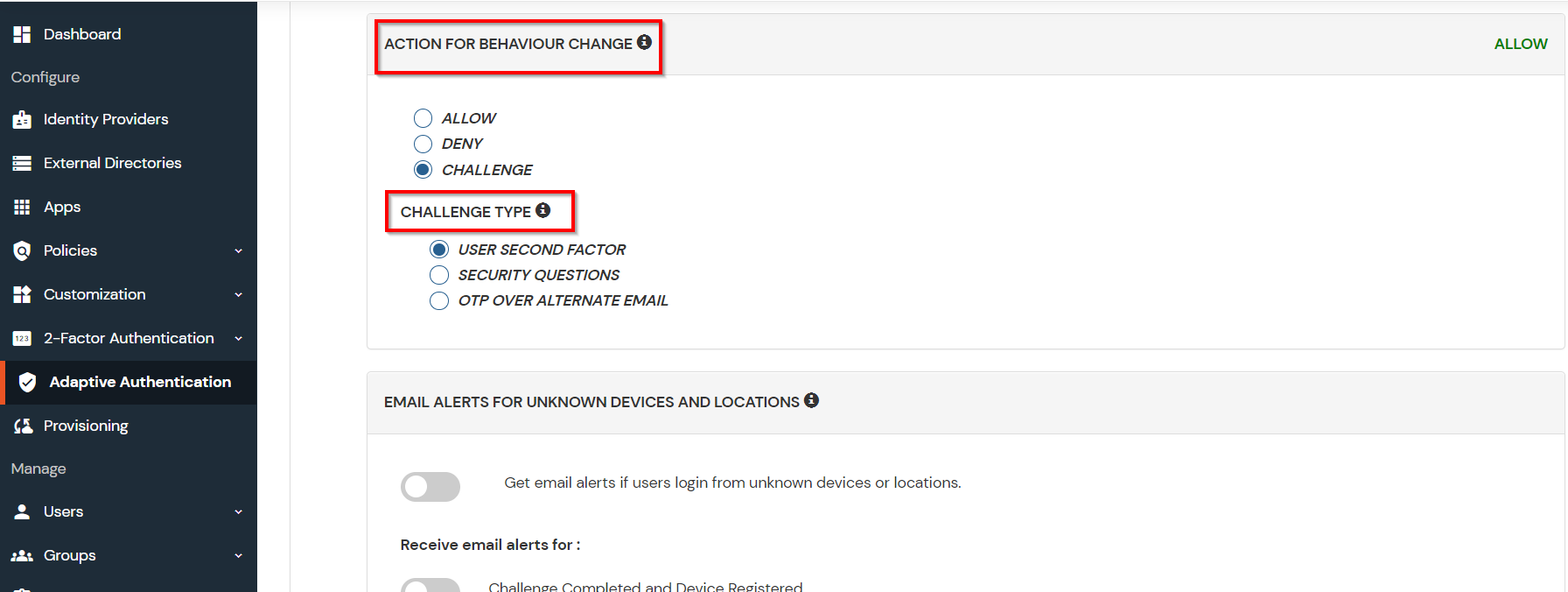
Action for behavior Change Options :
| Attribute |
Description |
| Allow |
Allow users to authenticate and use services if Adaptive authentication condition is true. |
| Deny |
Deny user authentications and access to services if Adaptive authentication condition is true. |
| Challenge |
Challenge users with one of the three methods mentioned below for verifying user authenticity. |
Challenge Type Options :
| Attribute |
Description |
| User second Factor |
The User needs to authenticate using the second factor he has opted or assigned for such as
- OTP over SMS
- PUSH Notification
- OTP over Email and, many more.
|
| KBA (Knowledge-based authentication) |
The System will ask the user for 2 of 3 questions he has configured in his Self-Service Console. Only after the right answer to both questions is the user allowed to proceed further. |
| OTP over Alternate Email |
User will receive an OTP on the alternate email they have configured through the Self Service Console. Once the user provides the correct OTP, they are allowed to proceed further. |
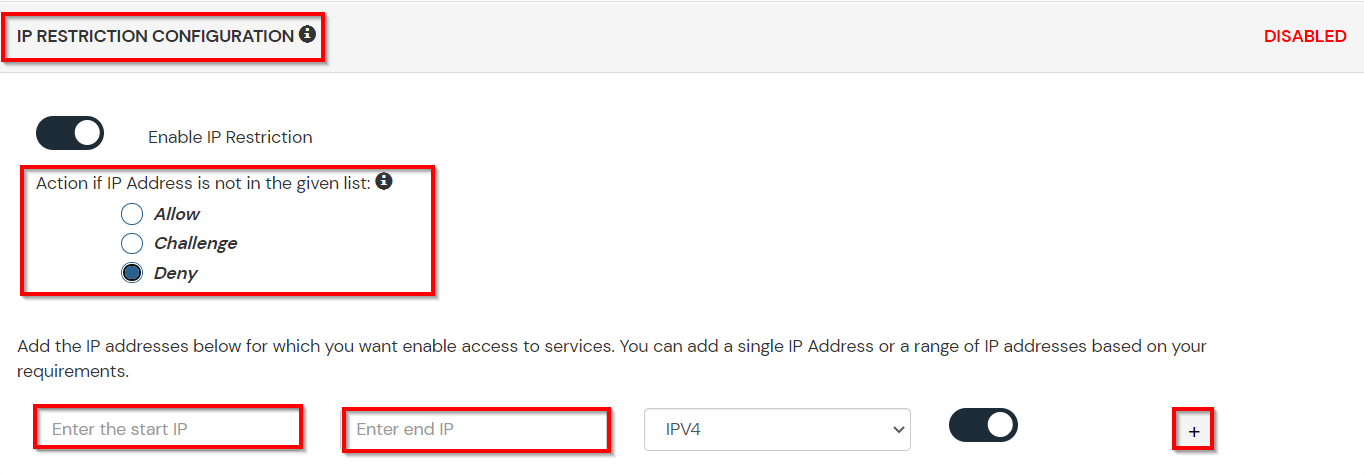
- Now click Edit option from the IP Configuration section to configure custom IP range.
- Select Add IP if the User's IP Address is not in the configured list.
- Specify the IP Address that you want to whitelist. For the IP Range other than the whitelisted one, you can select the above setting to reflect.
- Choose either allow or deny by selecting the corresponding option from the dropdown.
- If a user tries to login with the whitelisted IP address, they will always be allowed access.
- We support IP address range in three formats i.e., IPv4, IPv4 CIDR, and IPv6 CIDR. You can choose whichever is suitable for you from the dropdown menu.
- You can add multiple IPs or IP ranges by clicking the + Add IP button.
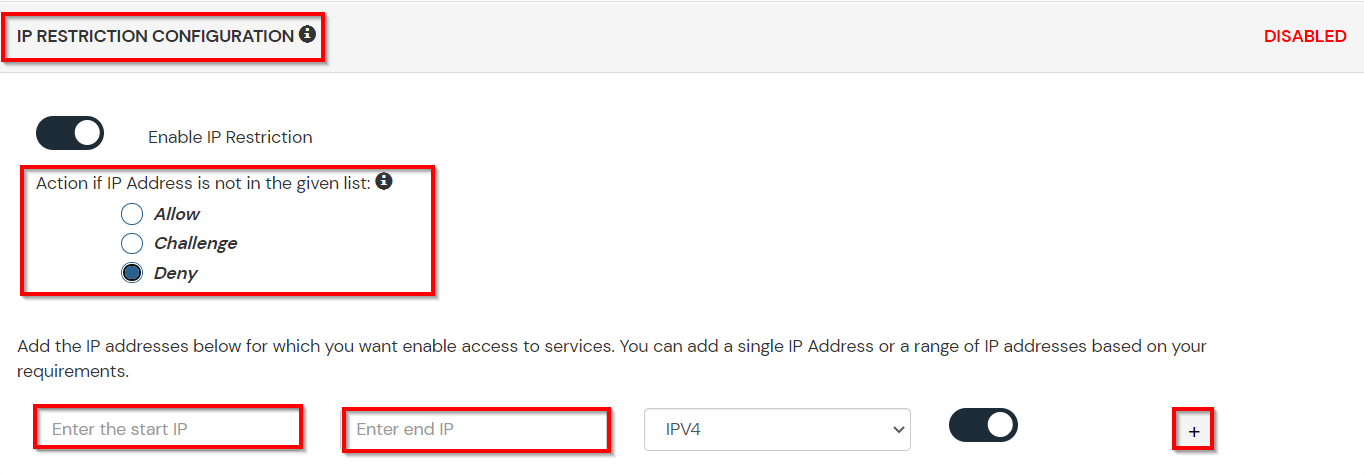
- Once the changes are made, scroll down to the end and click on Save.
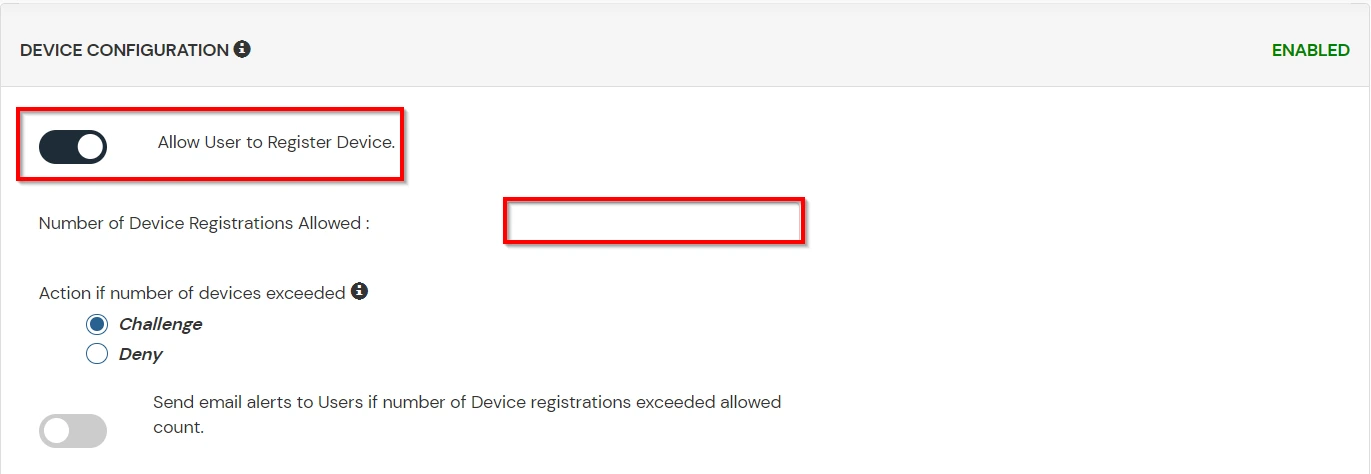
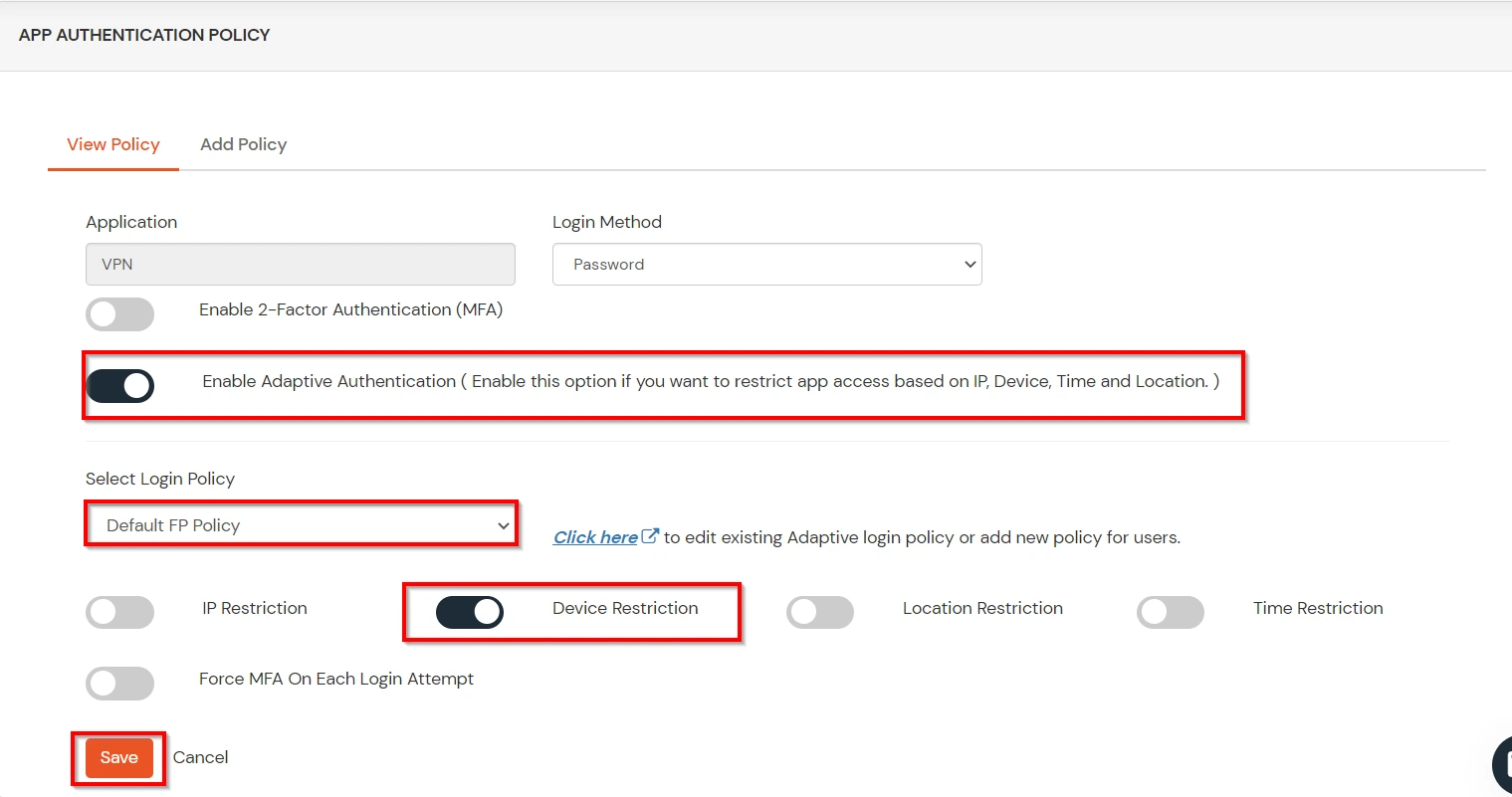
B. Adaptive Authentication with Limiting number of devices
Using Adaptive Authentication you can also restrict the number of devices the end user can access the Services on. You can allow end users to access services on a fixed no. of devices. The end users will be able to access services provided by us on this fixed no. of devices.
You can configure Adaptive Authentication with Device Restriction in following way
- Login to Self Service Console >> Adaptive Authentication >> Add Policy.
- Add a Policy Name for your Adaptive Authentication Policy.
- Select your Action for behavior Change and Challenge Type for user from the Action for behavior Change Section.
- On the Add Policy tab, go to the Device Configuration section and click the Edit button.
- Enter the Number of Device Registrations Allowed as per your requirement. (2-3 devices are recommended.)
- Choose Action if number of devices exceeded (This will override your setting for Action for behavior Change.)
- Challenge: The user needs to verify himself using any of the three methods mentioned in table in step 5.1
- Deny : Deny users access to the system
- Enable Mobile Device Restriction to block logins from mobile devices. This ensures all login attempts from mobile devices will be declined.
- Enable MAC Address Based Restriction if you want to restrict access based on device MAC address.
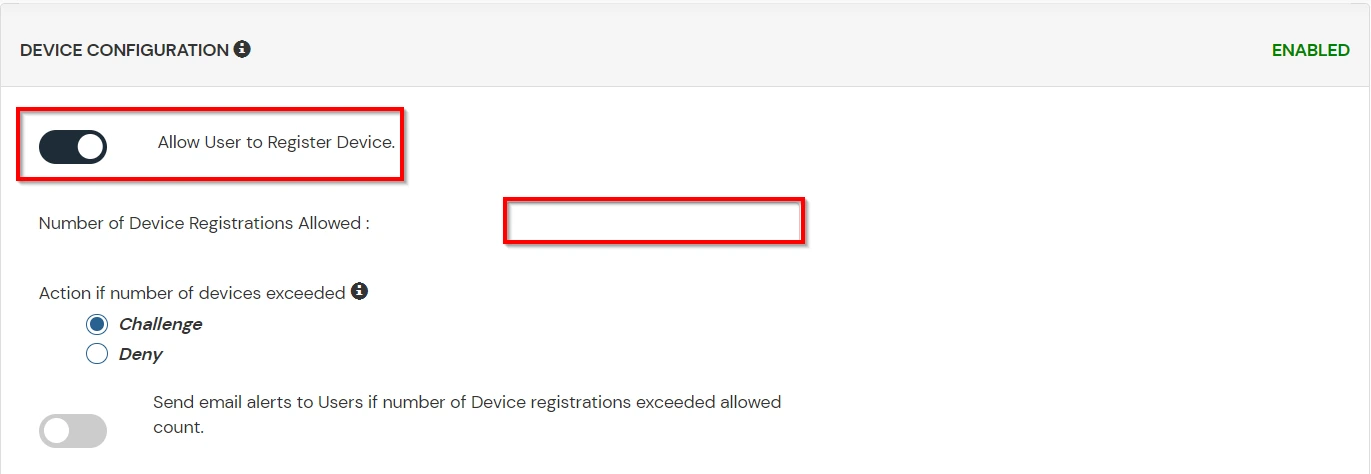
- Scroll down to the bottom of the page and click on Save.
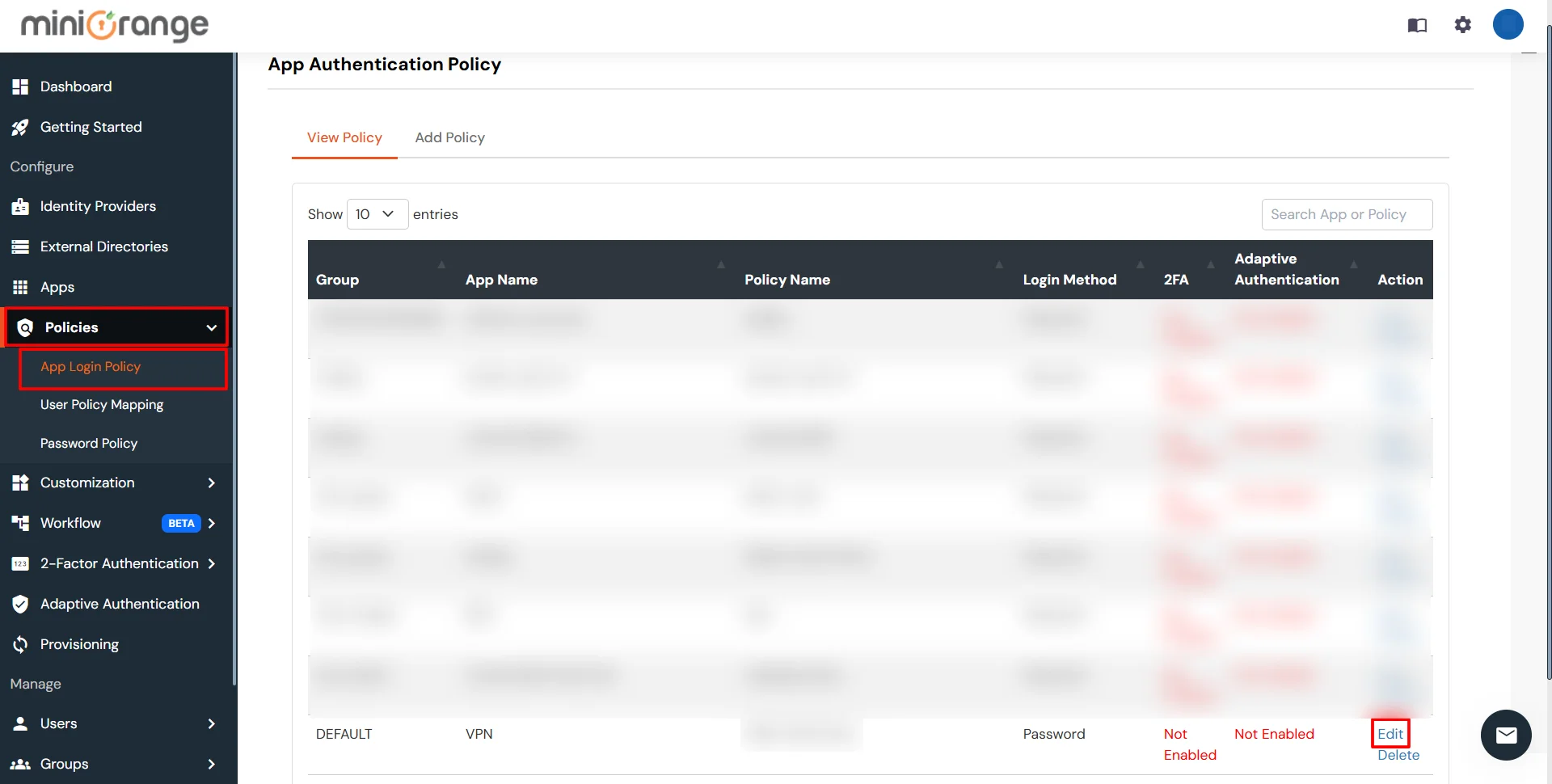
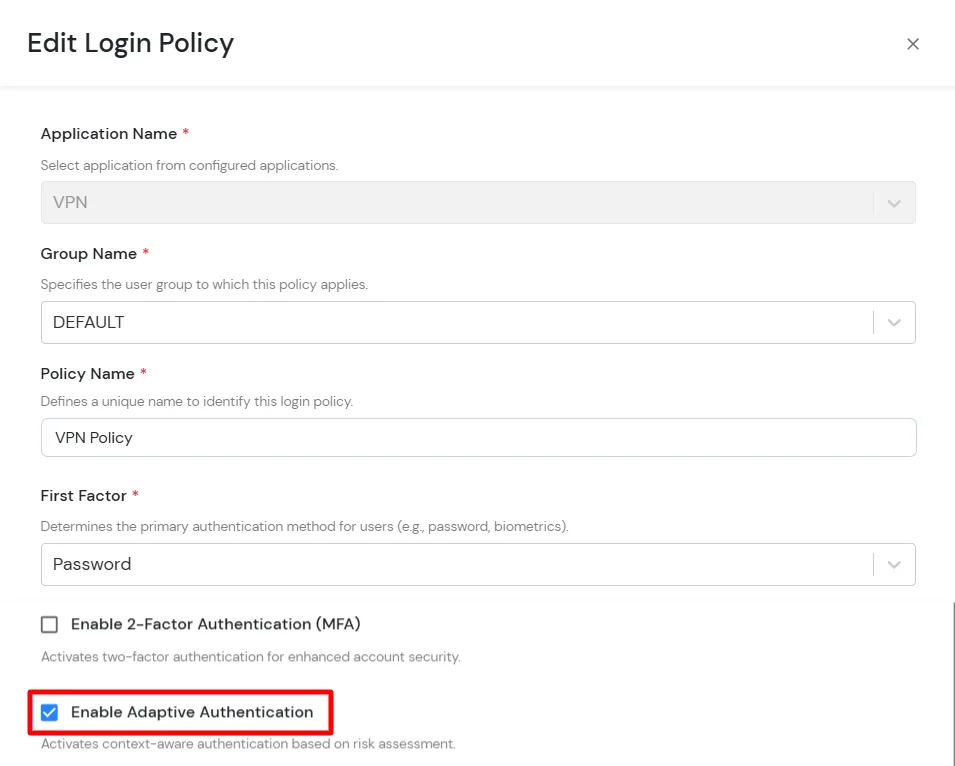
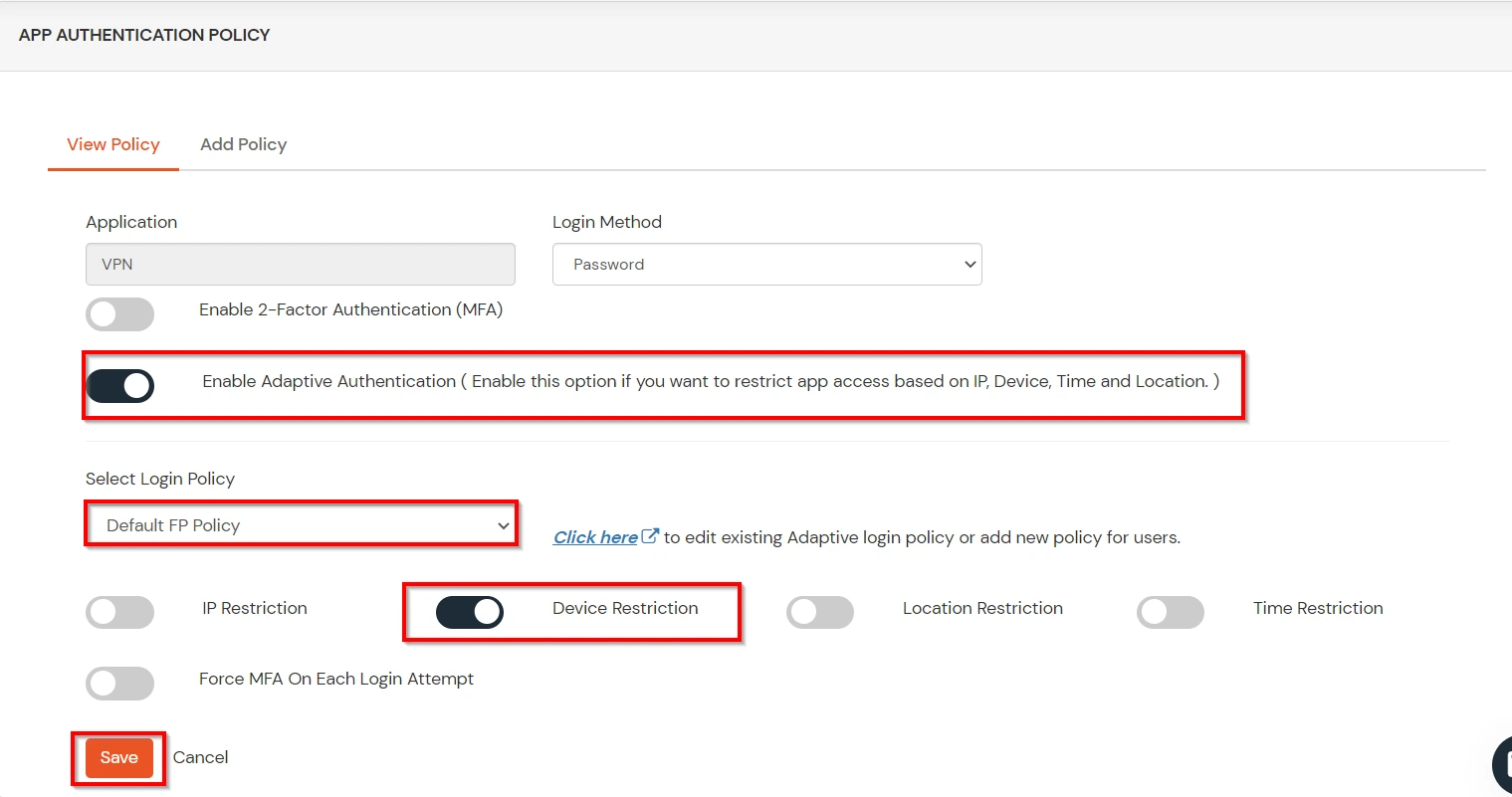
C. Add Adaptive Authentication policy to Websphere
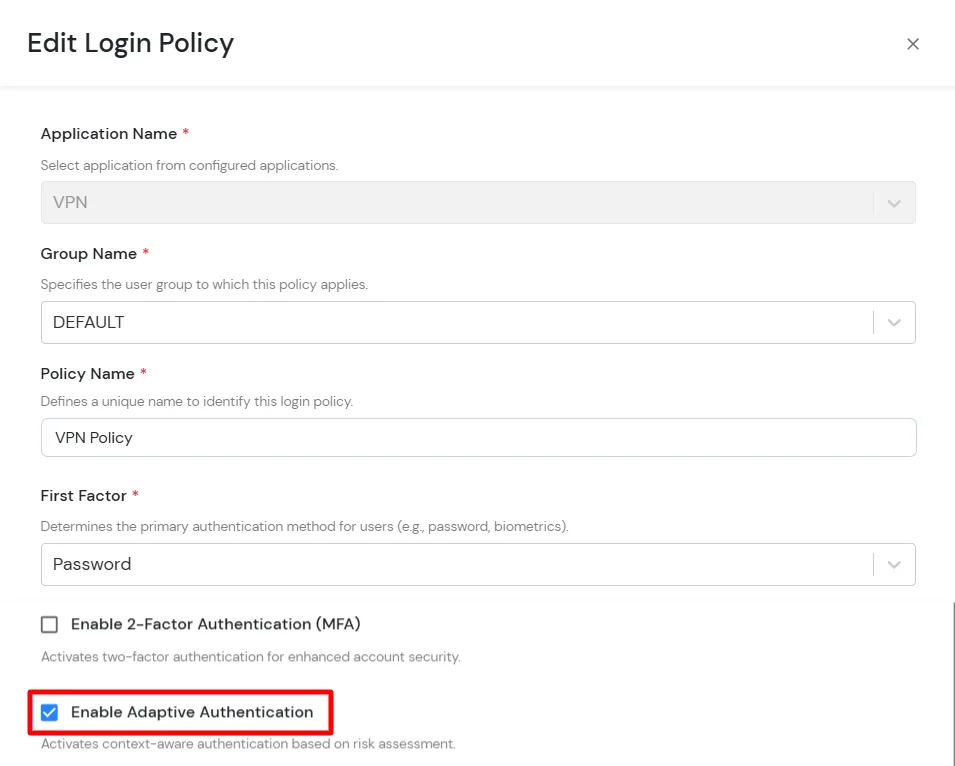
- Login to Self Service Console >> Policies >> Add Login Policy.
- Click on Edit icon option for predefined app policy.
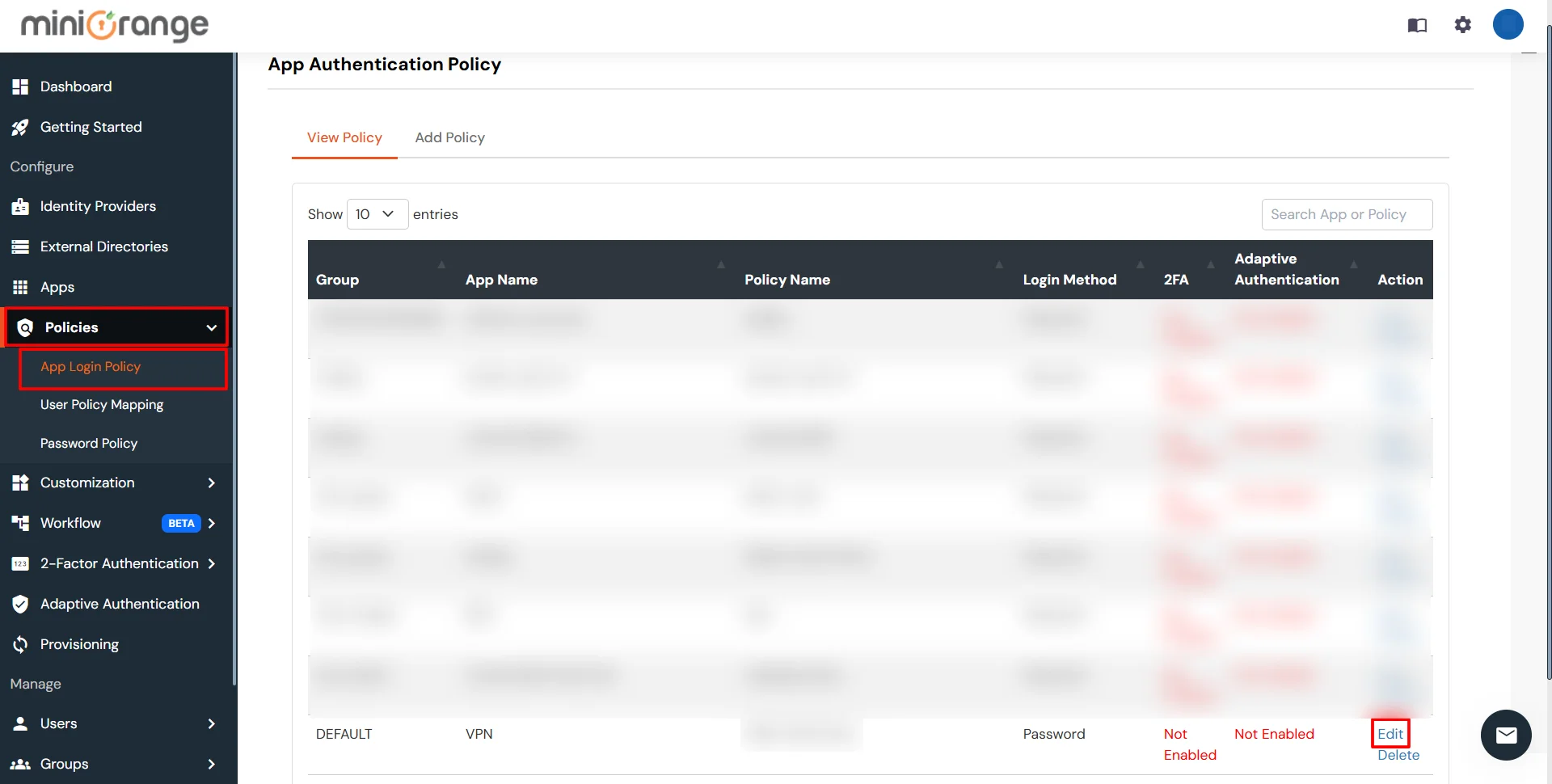
- Set your policy in the Policy Name and select Password as First Factor.
- Enable Adaptive Authentication on Edit Login Policy page and select the required restriction method as an option.
- From Select Login Policy dropdown select the policy we created in last step and click on Submit.
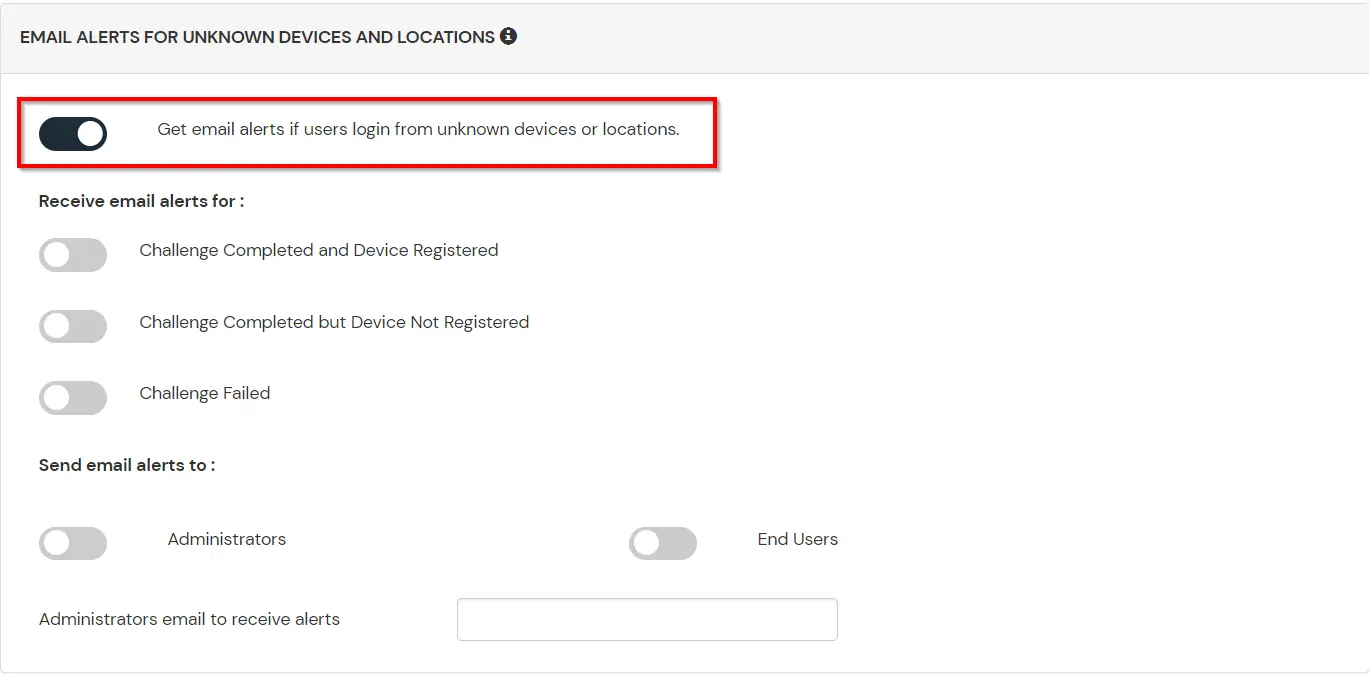
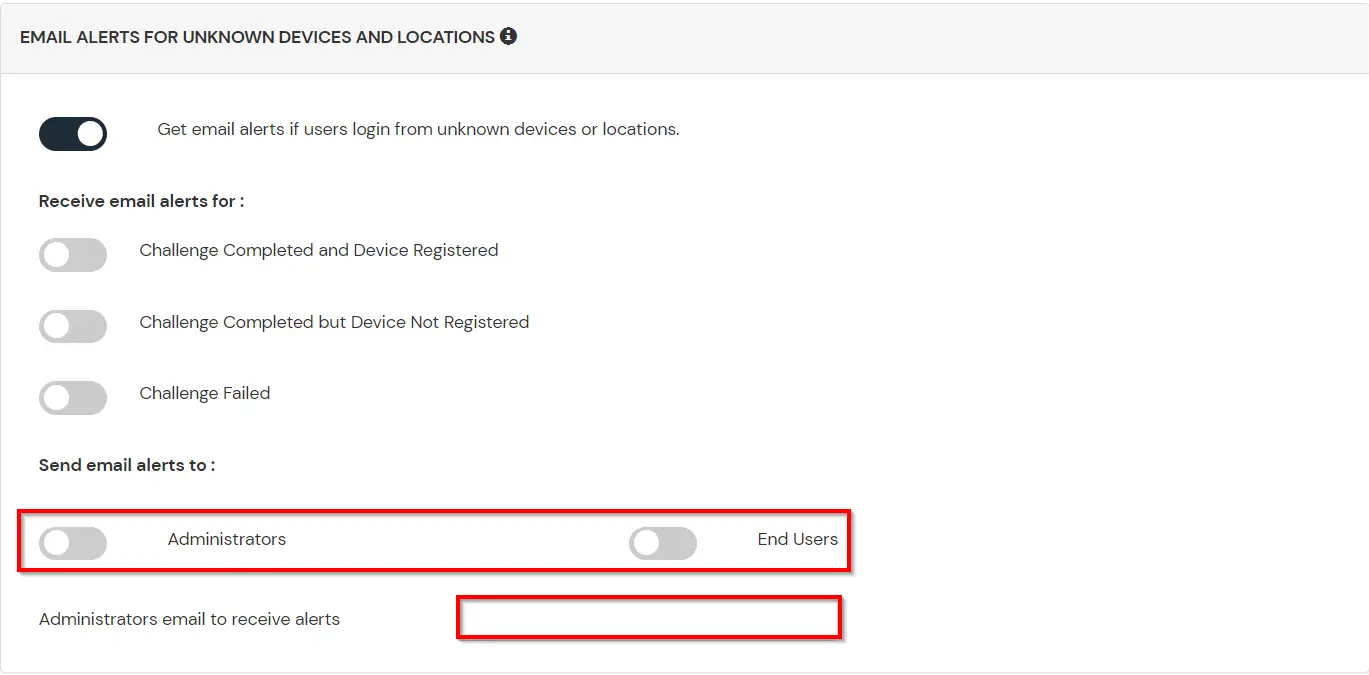
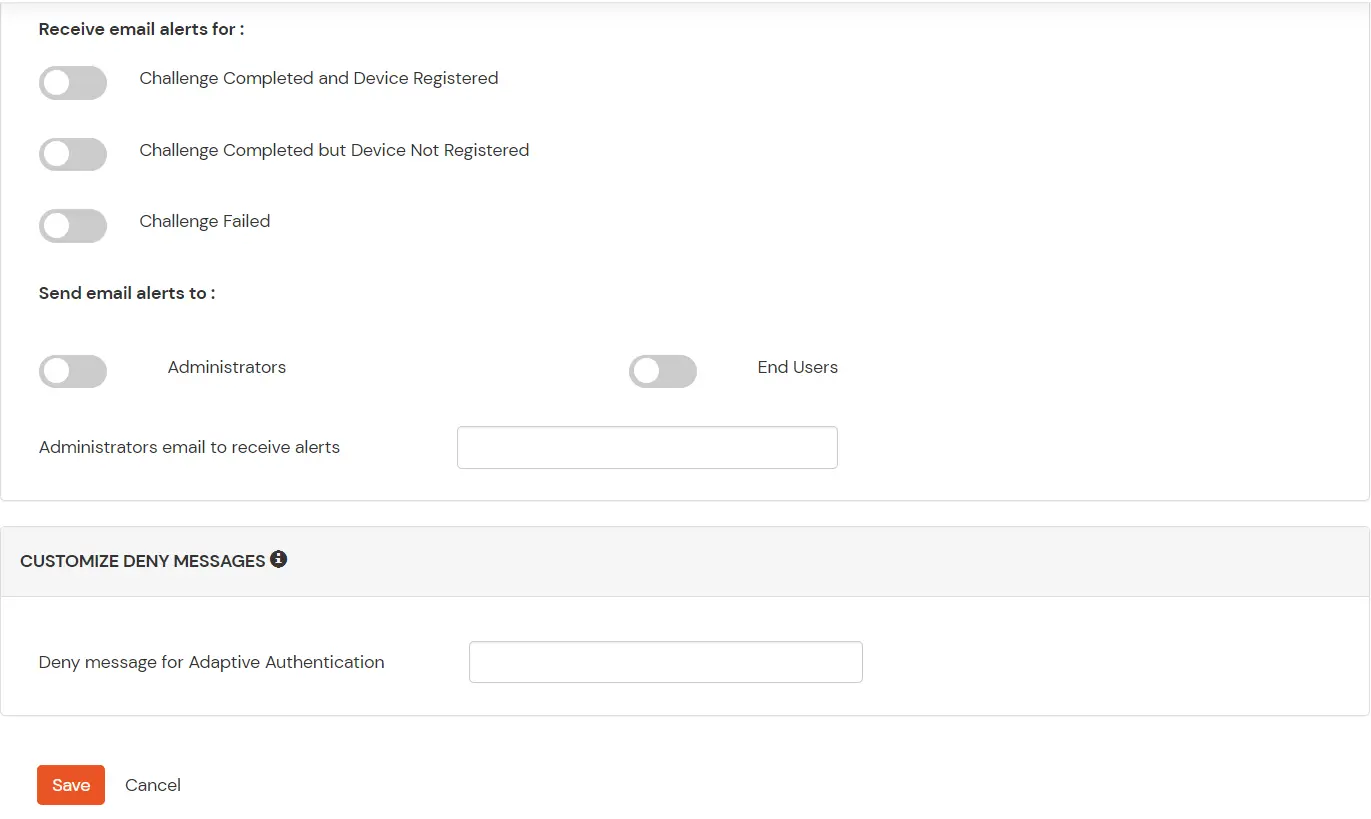
D. Notification and Alert Message.
How to add a trusted Device
- When End-user log in to the self service console after the policy for device restriction is on, he is provided the option to add the current device as a trusted device.
External References